Steganography the practice of concealing messages or information

- Slides: 22
Steganography …the practice of concealing messages or information within other non-secret text or data
Steganography › The origin of the word is from the Greek word “steganos, ” meaning “covered” › And the Greek word “graphie, ” meaning “writing” › Steganography means “covered writing”

Can you detect the hidden image?
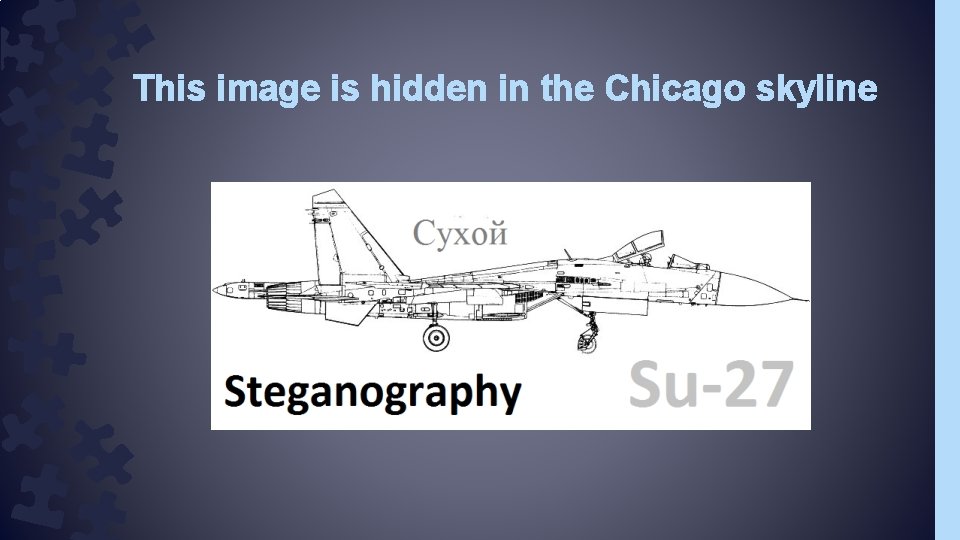
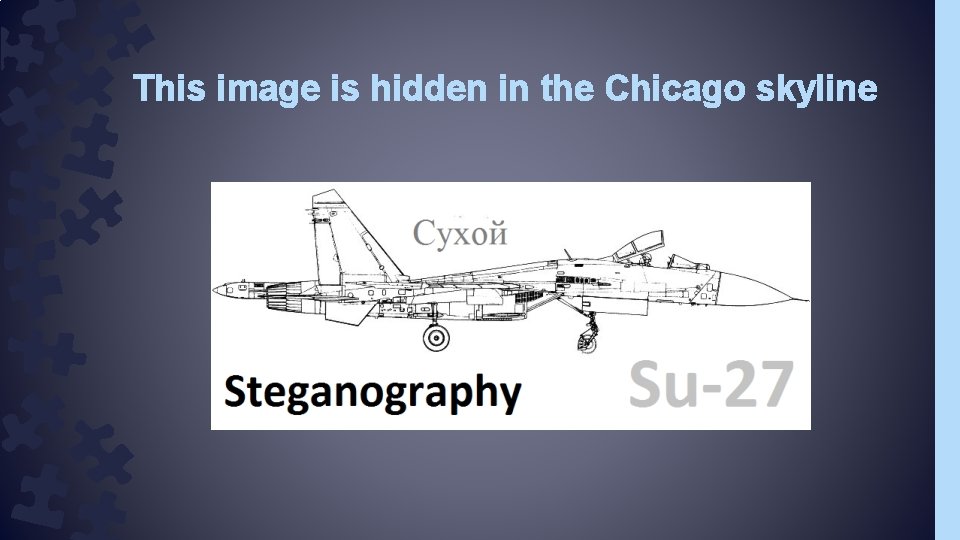
This image is hidden in the Chicago skyline
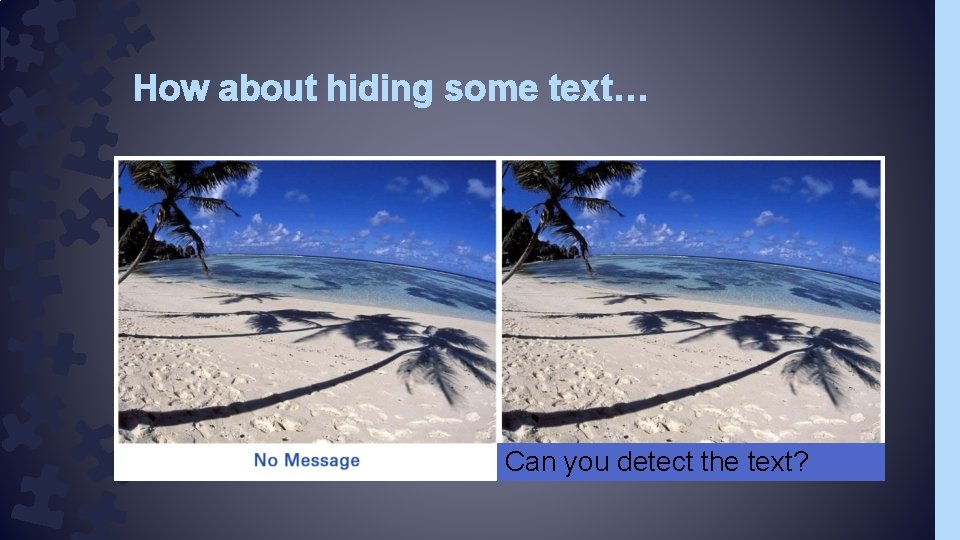
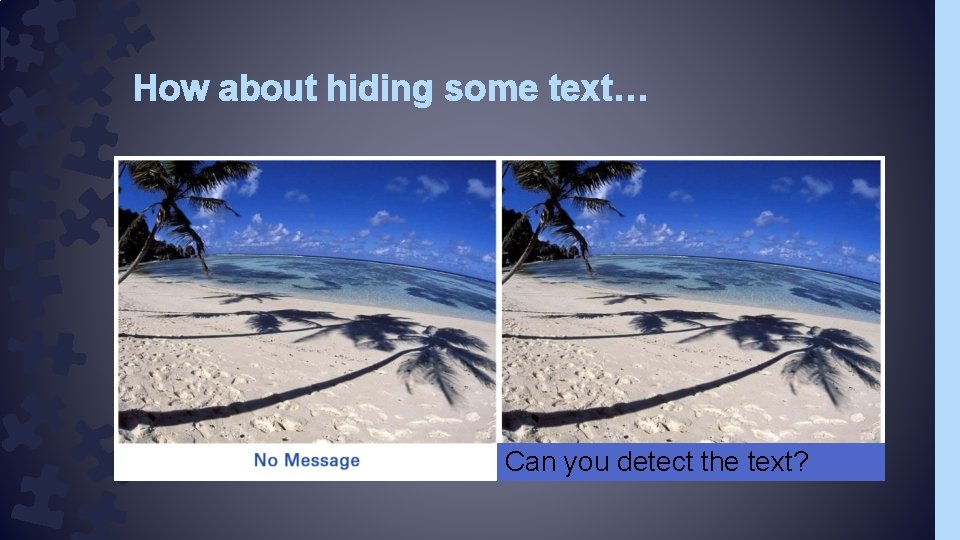
How about hiding some text… Can you detect the text?
We will come back to how items are hidden in images › But first… – A little bit of history of steganography
Early Examples › Ancient Greece: – Shaved the head of a messenger, – tattooed the message, – and waited for the hair to grow back. – Demeratus wanted to advise Sparta that Xerxes was planning on invading Greece – He wrote it on the wood – Covered it in wax – To guards, the tablet appeared to be blank.
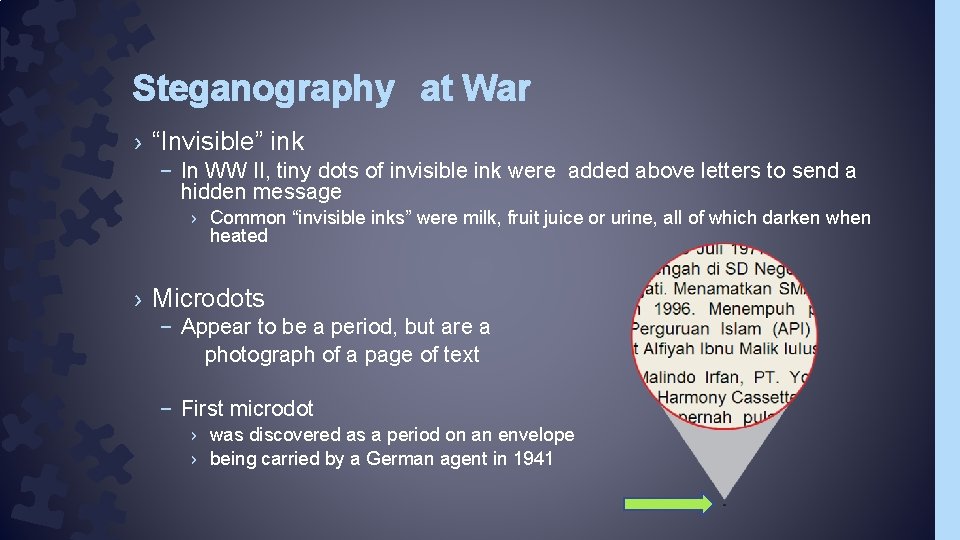
Steganography at War › “Invisible” ink – In WW II, tiny dots of invisible ink were added above letters to send a hidden message › Common “invisible inks” were milk, fruit juice or urine, all of which darken when heated › Microdots – Appear to be a period, but are a photograph of a page of text – First microdot › was discovered as a period on an envelope › being carried by a German agent in 1941
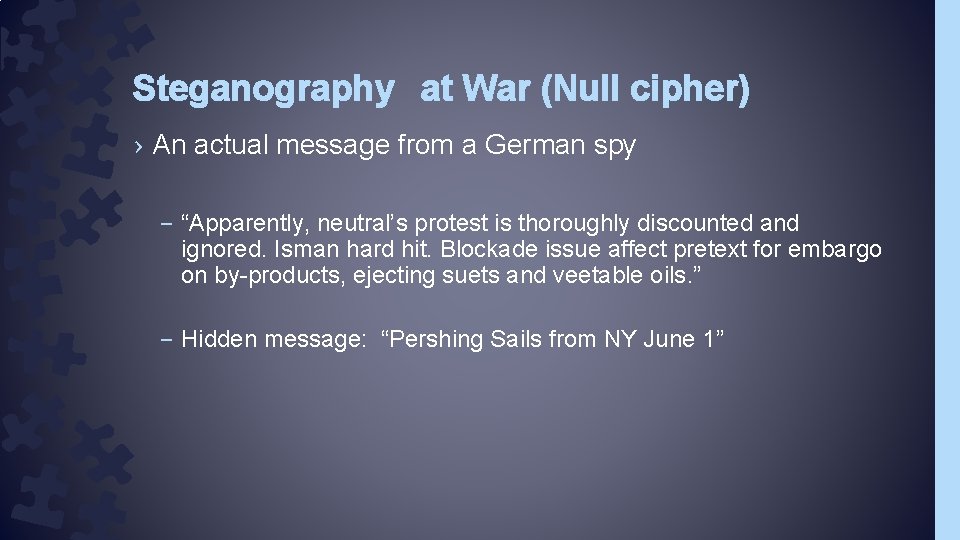
Steganography at War (Null cipher) › An actual message from a German spy – “Apparently, neutral’s protest is thoroughly discounted and ignored. Isman hard hit. Blockade issue affect pretext for embargo on by-products, ejecting suets and veetable oils. ” – Hidden message: “Pershing Sails from NY June 1”
Null Ciphers (non-encrypted text) › Fishing freshwater bends and saltwater coasts rewards anyone feeling stressed. Resourceful anglers usually find masterful leapers fun and admit swordsish rank overwhelming anyday. › Secret message: – Send Lawyers, Guns and Money
Simple Null Cipher (non-encrypted text) › Frank is not doing my editing – Hidden message: Find me
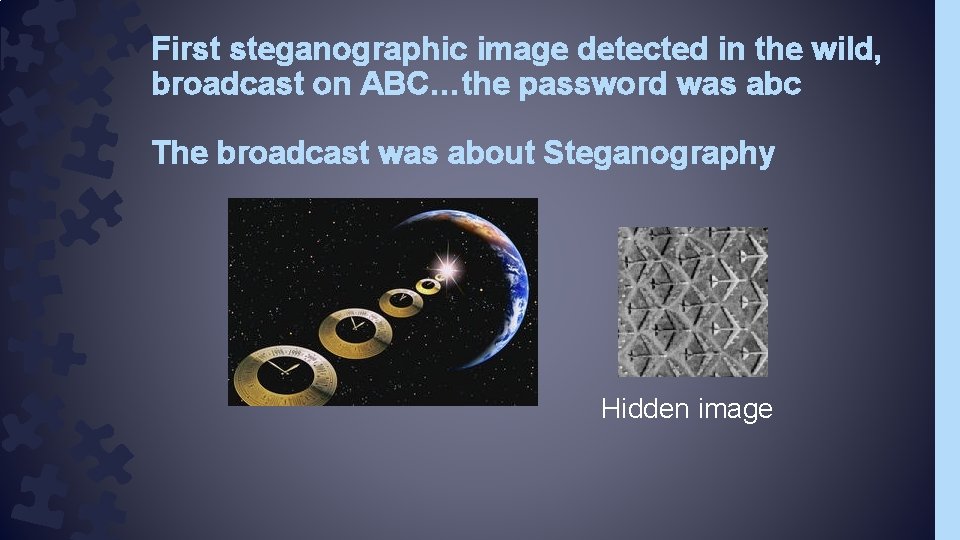
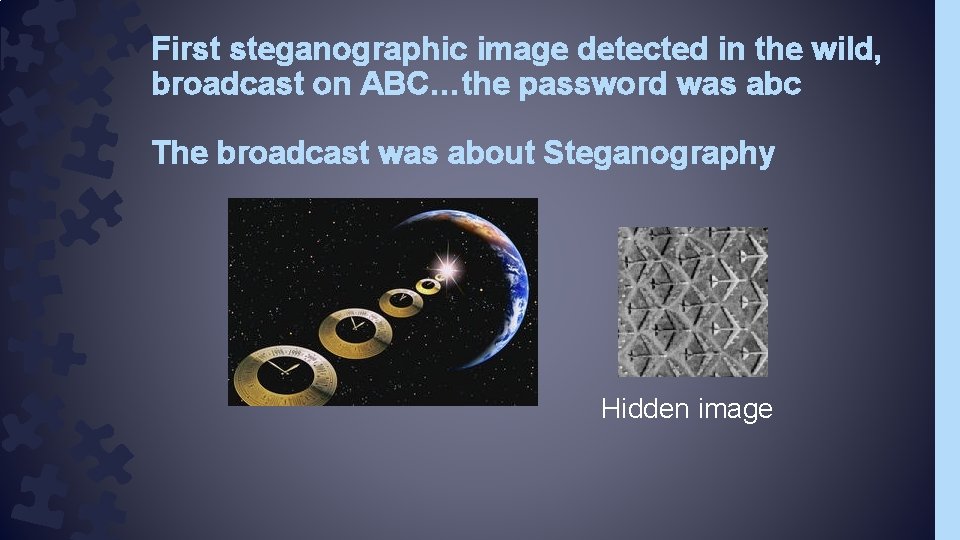
First steganographic image detected in the wild, broadcast on ABC…the password was abc The broadcast was about Steganography Hidden image
“Good” uses of Steganography › Digital watermarking – Visible watermarks – Invisible watermarks › Ability to transmit trade secrets without fear of interception of critical data
“Bad” uses of steganography › Corporate espionage › Spies and Terrorists › Hackers › Transmission of child porn
You be the judge – World of Warcraft watermarks every screenshot with: › › User ID Time of screenshot capture Version IP Address of the server › Apparently used to determine origin of exploits/hacks › Also used to track early release review violations of a Non-Disclosure Agreement
2 Main types of Digital Steganography › Least Significant Bit (LSB) › Discrete Cosine Transform (DCT)
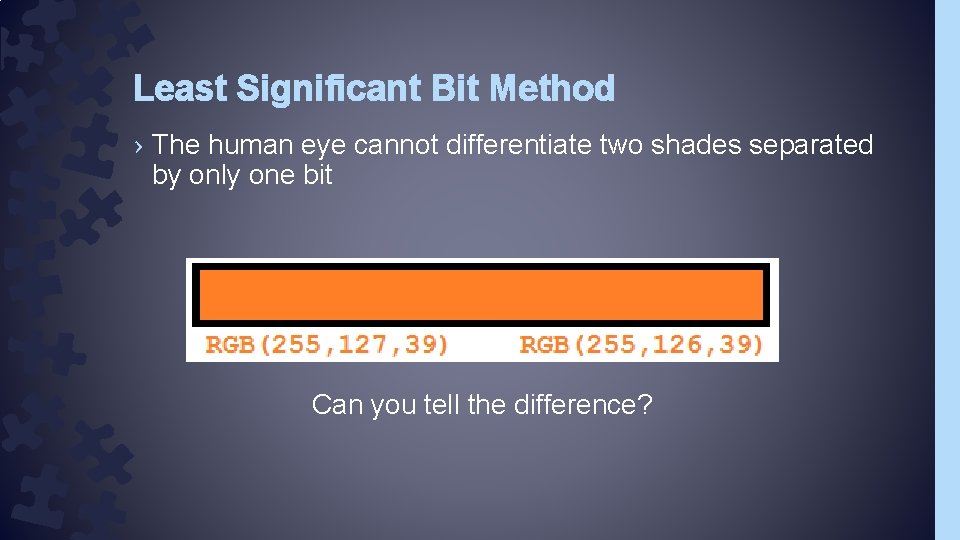
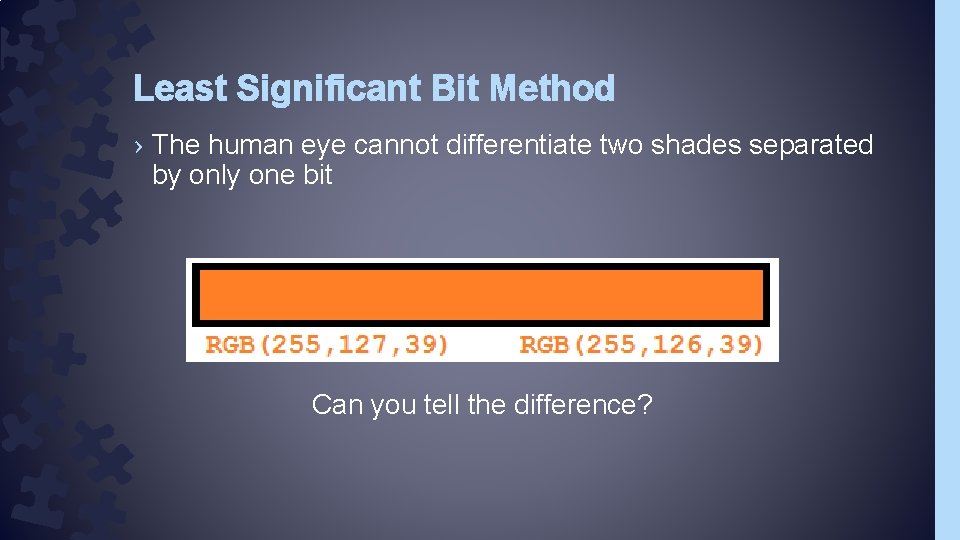
Least Significant Bit Method › The human eye cannot differentiate two shades separated by only one bit Can you tell the difference?
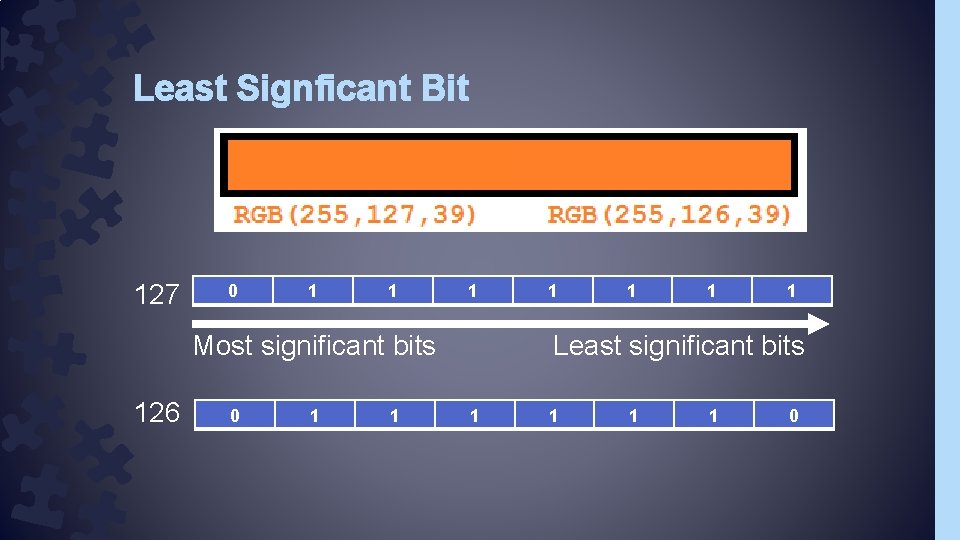
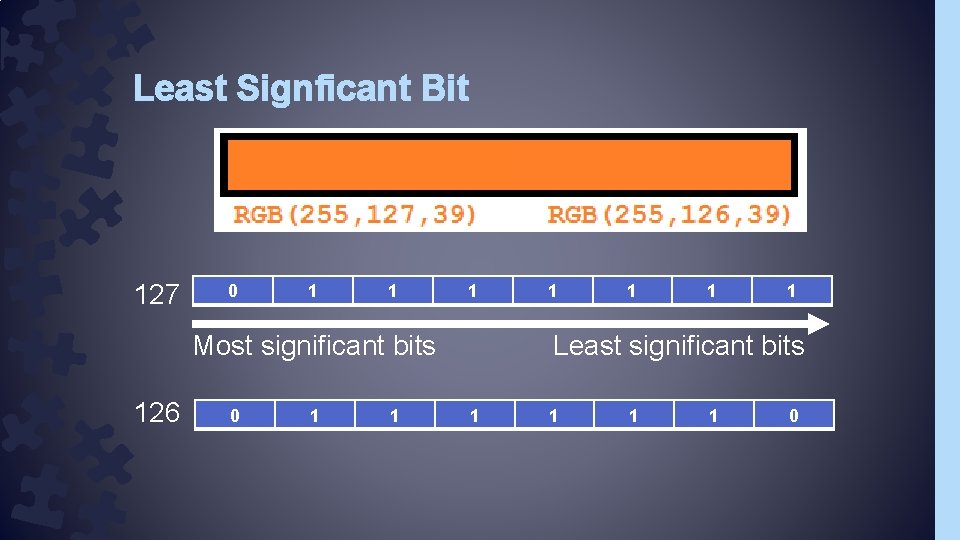
Least Signficant Bit 127 0 1 1 1 Most significant bits 126 0 1 1 1 Least significant bits 1 1 0
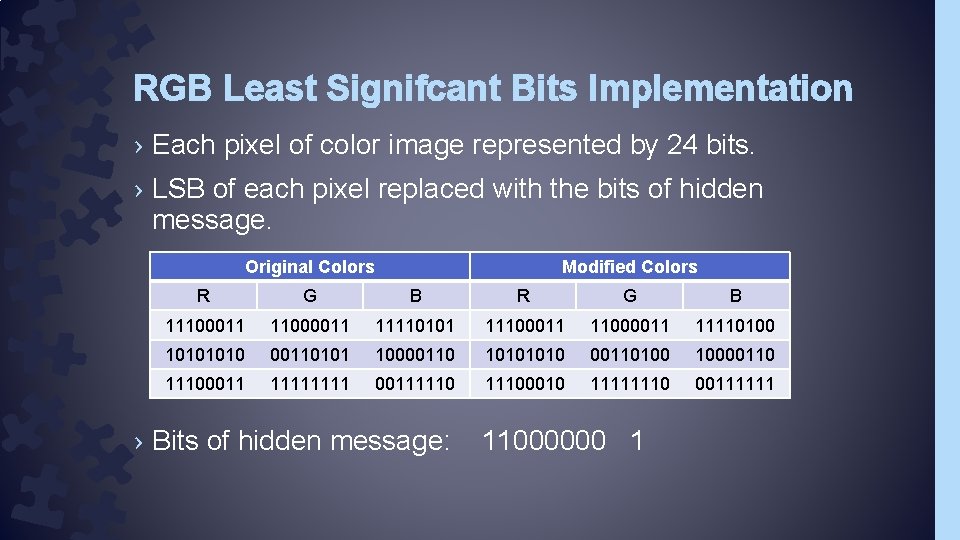
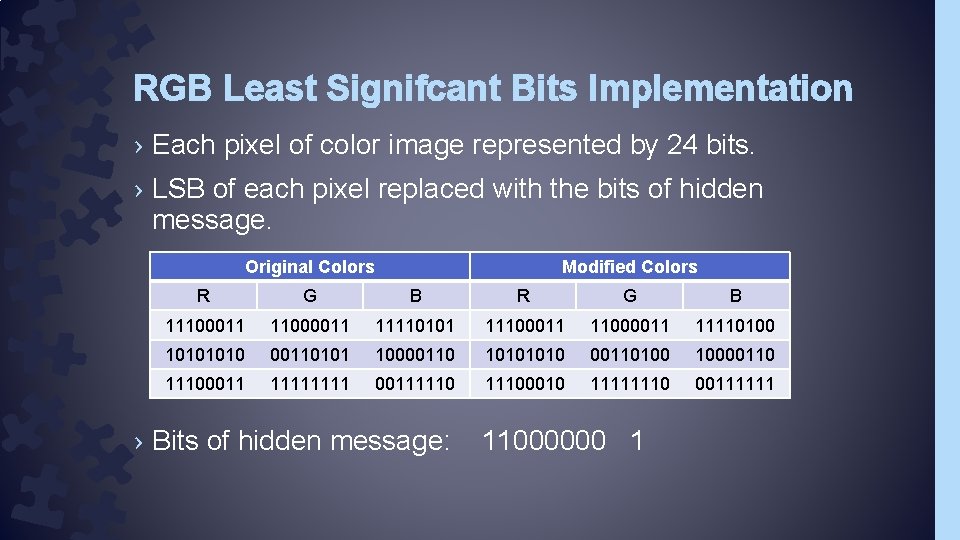
RGB Least Signifcant Bits Implementation › Each pixel of color image represented by 24 bits. › LSB of each pixel replaced with the bits of hidden message. Original Colors Modified Colors R G B 11100011 11000011 11110101 11100011 11000011 11110100 1010 00110101 10000110 1010 00110100 10000110 11100011 1111 001111100010 11111110 00111111 › Bits of hidden message: 11000000 1
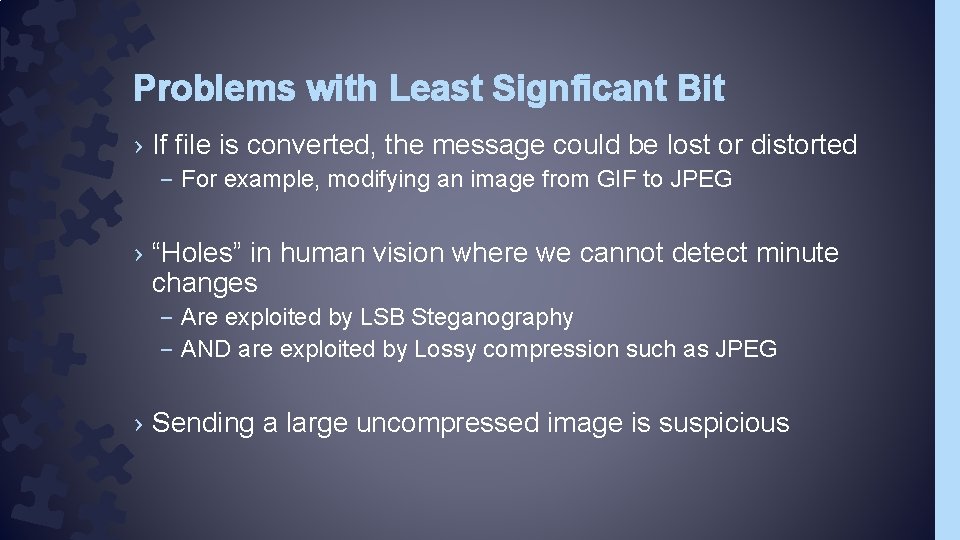
Problems with Least Signficant Bit › If file is converted, the message could be lost or distorted – For example, modifying an image from GIF to JPEG › “Holes” in human vision where we cannot detect minute changes – Are exploited by LSB Steganography – AND are exploited by Lossy compression such as JPEG › Sending a large uncompressed image is suspicious
Discrete Cosine Transform Steganography › Recall that JPEG uses Cosine Transformation to determine the overall image shades in an 8 pixel x 8 pixel block. › It then generates Coefficients for the Cosine function that most closely approximates the block › Discrete Cosine Transform Steganography modifies the coefficients slightly, therefore it is not affected by compression such as JPEG
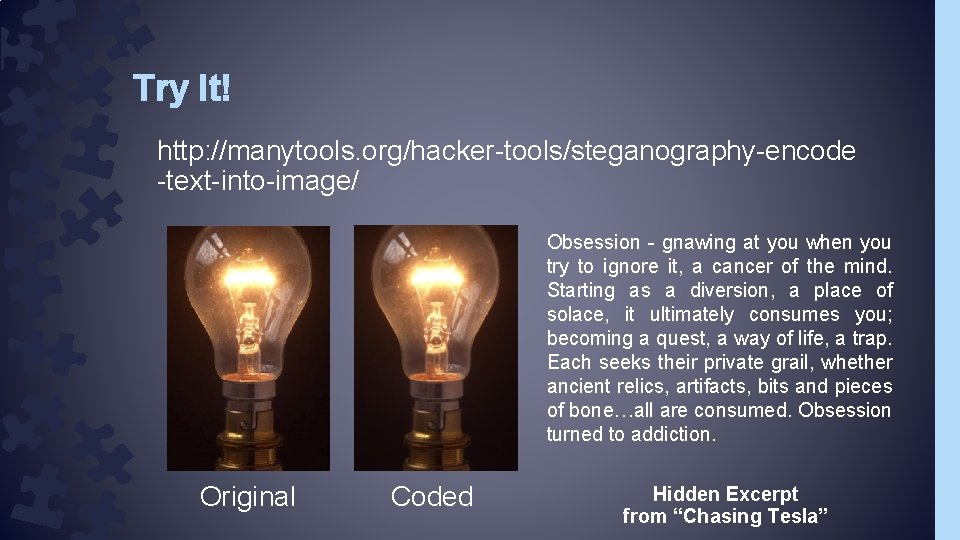
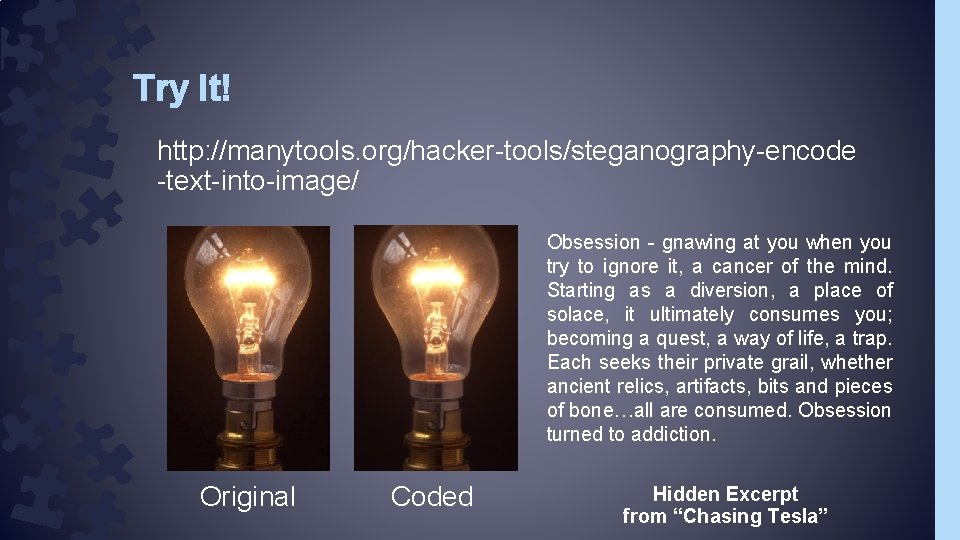
Try It! http: //manytools. org/hacker-tools/steganography-encode -text-into-image/ Obsession - gnawing at you when you try to ignore it, a cancer of the mind. Starting as a diversion, a place of solace, it ultimately consumes you; becoming a quest, a way of life, a trap. Each seeks their private grail, whether ancient relics, artifacts, bits and pieces of bone…all are consumed. Obsession turned to addiction. Original Coded Hidden Excerpt from “Chasing Tesla”