Stealthy Video Capturer Video based Spyware in 3
Stealthy Video Capturer: Video‐ based Spyware in 3 G Smartphones Stefan Maurer Liz Ellis
Why secure Smartphones? • Increasing public usage – More people buying and using Smartphones – (insert statistic here) • Smartphones are incredibly mobile – Access to the most private moments – Intimate details about habits/lifestyle revealed
Introduction to SVC • Allows hackers to have control of camera • Records and sends video to a third party over an internet connection through the phone • Three phases: – Install SVC without device owner’s knowledge – Collect video – Send files to hacker
Infection • Trojan horse attached to tic‐tac‐toe game • Binary executable file of SVC attached as resource file of game • After compilation, creates executable codes of SVC • When game is executed, SVC attaches itself independently and continues running even after game is closed.
Application Layer • 3 modules • Video capture – Takes chare of camera • File sending – Sends data to hacker • Triggering algorithm – Dynamic control module – Determines the right time to run other modules
“Stealthiness” and acquiring info • Which is more important for the SVC intender • “Stealthiness” – term used by team – Device owner should not know program is running – Team focuses on this – 3 aspects: power, CPU usage, and memory • Information acquisition – Sometimes, more important to get all info than not get caught (crime scene/contracts signed) • Scenario decides triggering algorithm!
Triggering Algorithm • • 2 parts: capture and sending Should change based on practical application! Main challenge: when to capture/send? Ce. Set. User. Notification. Ex() – Allows spyware to record even when phone is idle • Uses Windows Mobile API to gather more info – Power, CPU status, phone dialing, etc. – Device owner should have little suspicion
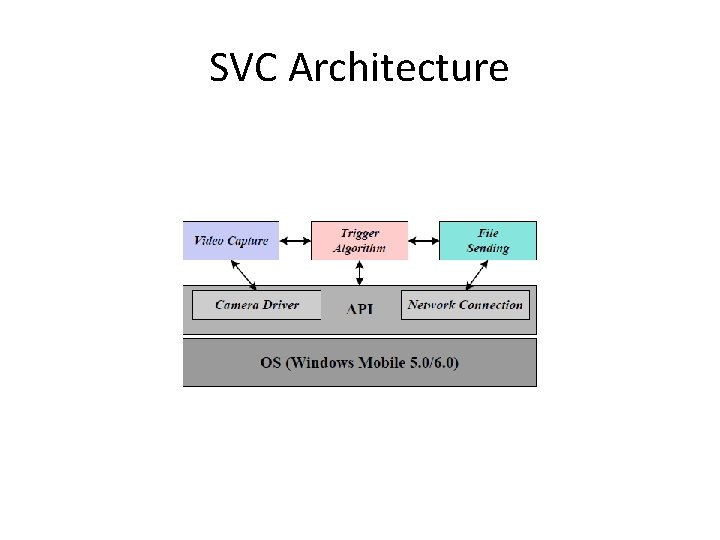
SVC Architecture
When to Capture/Send? • Both use specifications from API • Examples: – Power level between 20%‐ 80% – CPU usage should be no more than 50% – Device owner talking on phone: capture – Connection to internet (Wi. Fi/Bluetooth): sending • If there is knowledge about victim, can use living habits to determine when to record – Ex: businessman having important weekly conference
Video Capture Module • Called by triggering algorithm • Phases: – Open camera and take video – Determine whether images are static or dynamic – If dynamic images, compress and store • If images are static, process terminates – Pictures of inside of pocket are not useful • Files are hidden on the disk in hidden and unused folders
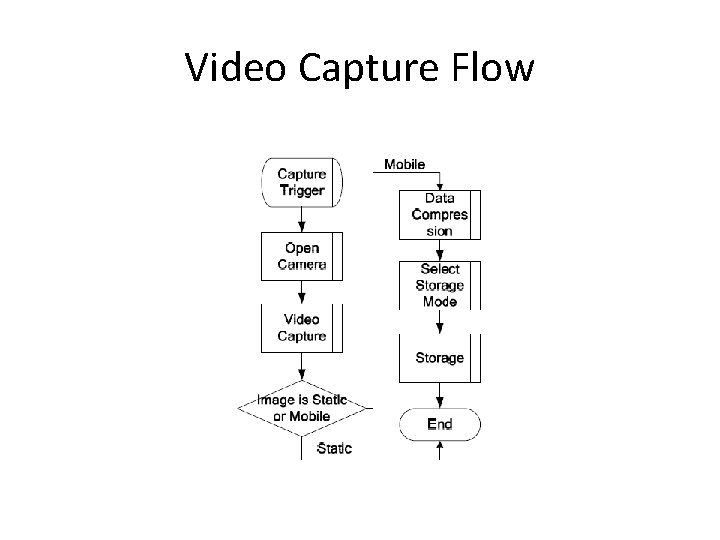
Video Capture Flow
How to Access Camera • Native API has little customizability – Can access camera, but no flexibility (frame rate, file format, etc. ) • Access and build filter manually with software • Several COM controllers developed – Enable modifications of encoding and file formats – Video Encoder and Custom Format File Render
Data Compression • Data compression: large files are easy to detect and hard to send • H. 263 is used to compress files – Many Smartphones use hardware for compression, which is inaccessible – Software compression is used instead – Lower compression rate but less CPU cycles than H. 264
File Sending • Need a wireless connection – Wi. Fi / Internet – Bluetooth – 3 G Network • Some delay between capture and sending is acceptable (real‐time not mandatory) • Use transmissions that are free of charge (unlike MMS) • Several methods considered: MMS, FTP, streaming
File Sending cont. • Prefer ability to use any wireless connections • Video files are generally large – Segment into portions, and send individually • Email is ideal – easily customizable, free, uniformly supported, flexible in syntax/size
Results • O 2 XDA Flame chosen for testing – Windows Mobile 5. 0 OS • Evaluation of stealthiness – CPU, memory, and power consumption • Four states – J 1: SVC running with backlight off – J 2: Camera operational, but recording – J 3: Recording Video and compression – J 4: Sending File to the intended viewer
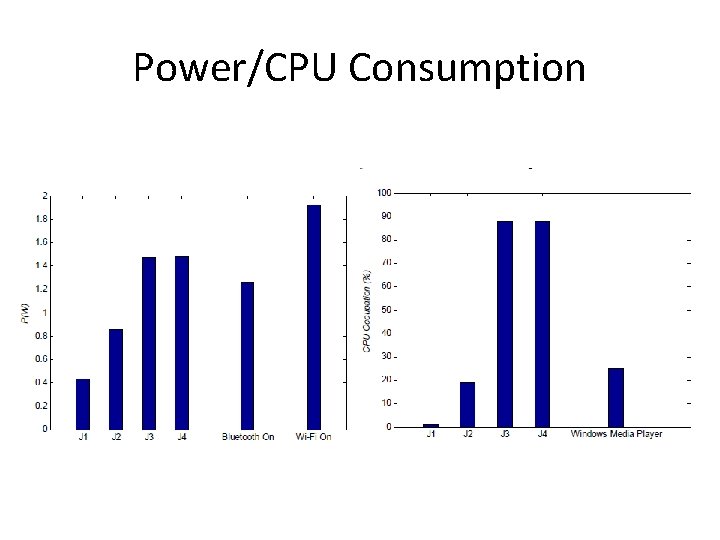
Power/CPU Consumption
Results cont. • Memory usage is almost constant – SVC uses less than WMP (relevance? ) • J 3 uses a large amount of power and CPU • Due primarily to the complexities of the compressions algorithm • Performance of SVC can be greatly improved using a better compression algorithm
Author's Opinions • Making SVC smarter – More intelligent triggering algorithm • Monitor user's living patterns – Exploit image recognition to capture video • Resistant to Anti‐Virus – AV is useless against new viruses/spyware • Security of Phones – Low default security settings on smartphones – Biggest Vulnerability: People are stupid
Our Opinions • Windows Media Player? • What if the user does not use Wi. Fi/Bluetooth frequently? • CPU consumption of J 3 • When does J 4 send the files? – Large CPU consumption
Work Cited • Xu, N. , Zhang, F. , Luo, Y. , Jia, W. , Xuan, D. , and Teng, J. 2009. Stealthy video capturer: a new video‐based spyware in 3 G smartphones. In Proceedings of the Second ACM Conference on Wireless Network Security (Zurich, Switzerland, March 16‐ 19, 2009). Wi. Sec '09. ACM, New York, NY, 69‐ ‐ 78.
- Slides: 21