Stages of Investigation Open an inquiry based on
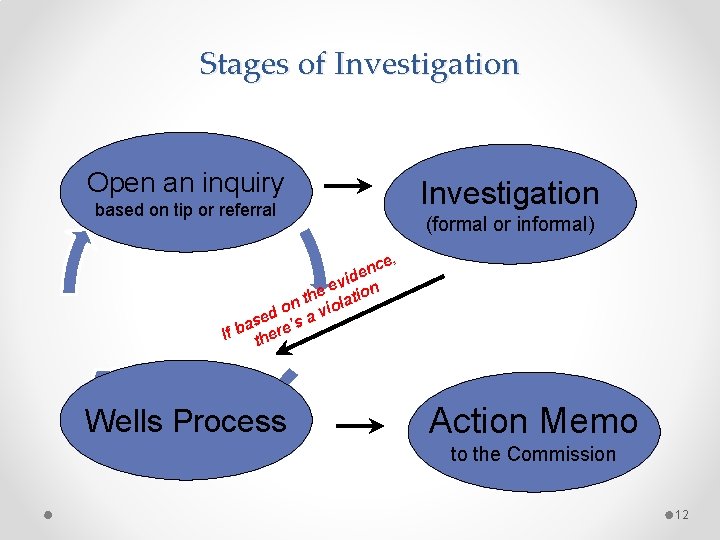
Stages of Investigation Open an inquiry based on tip or referral Investigation (formal or informal) e, c n de i v e he lation t on vio d e as re’s a b If the Wells Process Action Memo to the Commission 12
Ways an Investigation May Start • • • Investor complaint Company disclosure Tip from an informant Referral from inspection staff or another office Referral from other government source or a selfregulatory organization • Public sources such as newspaper articles or academic papers 13
First Steps • Create an investigative plan • Obtain relevant evidence o Documents o Witness statements or testimony • Analyze possible legal theories • Consider whether immediate action is necessary, appropriate, and effective 14
Investigation Plan • Written plan o o o Facts known so far Theory of the case and potential violations Potential defendants and witnesses Types of documents to obtain Issues (legal, evidentiary, practical) Timetable • Should be flexible and updated during investigation as things change and you learn more facts 15
Next Step – Fact Gathering • Documents o Obtain electronically if we can o Scan & load into an electronic database • allows us to search & tag • Witnesses • Other sources of information o o Internal investigations by company or regulated entity Informants Investigations by other agencies Publicly-available information (internet, press releases, regulator filings, public databases 16
Gather Written Information • Document Requests o Voluntary production? o Subpoenas? o Demand production of required records from entities registered with the relevant authority (broker-dealers, investment advisers) o Obtain records from other regulators (states, self-regulatory agencies, other federal agencies) o E-mails, e-mails!! Get the computer hard drive if needed o In some countries, obtain records through search and seizure • Consider requesting that company provide some types of information in summary form 17
Gather Oral Information • Decide how to get the information o Telephone interview? With notice? (take notes? ) o In person interview? (take notes? ) o Sworn voluntary testimony? o Sworn compelled testimony? (testimony following a subpoena) • Decide which witnesses and in what order o Consider - what is the role of the witness? Possible defendant? Third party? Investor? Uncertain? 18
Witness Interviews – Who First? ? • Two principal ways: “Bottom-Up” or “Top-Down” • The “bottom-up approach” – start from the least culpable witnesses and work up to the most culpable • Probably most common way - Learn as much as possible before you question the most critical parties in the case • But gives subsequent witnesses more time to prepare for their testimony or to communicate with others to develop a common version of events. • Sometimes want to lock in story of potential defendants early 19
TIPS FOR QUESTIONING WITNESSES • Have the witness tell the story o Let the witness tell the story in his/her own words o Remember the five “Ws” of any conversation or event • Who was there, what was said, when did it occur, where did it take place and why was it held. • Develop both sides of the story o Important to probe both areas that might help the prosecution and areas that might help the defense – avoids unpleasant surprises later on that may undermine your case. 20
TIPS FOR QUESTIONING WITNESSES • Ask the “ultimate” question: o Did you trade while in possession of inside information? - did you tip others? - did you alter those financial records? • May expect witness to lie, but at some point, make sure the witness has to confront the key question and their role o Better to know any possible defenses now 21
TIPS FOR QUESTIONING WITNESSES • Funnel approach - remember to ask the “closure questions” o When you’re finished with a topic, ask: Did anything else happen? – what else was said? – is that all that was said? -- was anybody else present? o Make sure you have gained all the relevant information in that area of inquiry (and locked witnesses into their story) 22
What’s Next? Follow the Evidence! • Develop and explore leads from the documents and testimony. • Review the documents and e-mails for internal inconsistencies and for inconsistencies with evidence provided by other people or documents. • Seek information from newly discovered relevant people or entities. • Consider bringing witnesses back in or gathering additional documents. 23
Next Step - Analyze Information • Organize the facts o Create chronologies, graphs, and other visual devices that will help explain the case. o Summarize the witness testimony and the key documents • Analyze the law o How do the facts fit under your legal theories? o Is there more information you still need to gather? • As you gather facts, continually re-analyze legal theories to see if you are developing the facts you need and if the facts you’ve developed fit your legal theory 24
Investigative Steps The following protocol was prepared to illustrate the tools and investigative steps necessary to successfully investigate and prosecute insider trading. These steps are based on SEC experience in filing approximately 50 insider trading cases each year. However, we also stress that such protocols should remain flexible so that investigators remain free to “follow the facts” wherever they may lead.
I. Identify the Material Non-public Information • • In most cases, the information will concern the following matters: o o o product announcements, earnings announcements, regulatory approvals or denials, mergers and acquisitions, and research reports. Identify the precise time at which the material information was made public. Assess the impact of the information on the market price of the stock.
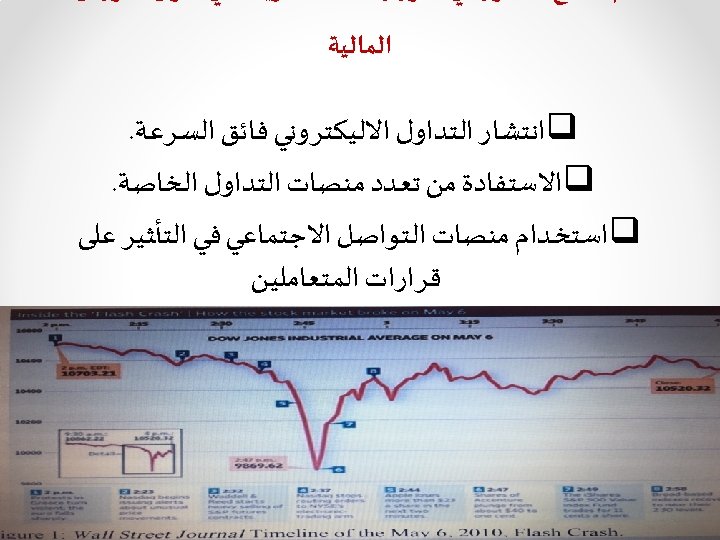
II. Evaluate Trading Records • • Obtain trading records to determine who conducted trading in the relevant stocks prior to the information becoming public. Analyze stock price and trading volume patterns in the stock over time to identify how unusual the trading is. Check publicly available information to see if there are other explanations for the unusual trading patterns. Public sources include: newspapers, websites, chat rooms, complaints, referrals, and filings with the securities authority and exchanges.
III. Maintain a Time-Line of Events Prepare a time line of events (also called a staff chronology).
IV. Question the Traders Consider calling the persons who conducted the trades to ask why they traded in the stock. These calls can be made informally at an early stage in the investigation. Ask: o o o Reasons for the trading? Whether they had knowledge of or access to the material nonpublic information? Whether they had contacts with any insiders of the companies involved? Whether they have prior trading in the stocks at issue? Did anyone else pay for all or a part of the transactions? Was there any agreement to share proceeds of the transaction with another person?
V. Request a Chronology Send a “chronology” request to the publicly traded companies whose stock was traded, or other companies associated with the traded companies in a way that relates to the material non-public information (such as merger partners). u The chronology should request the company to identify all steps, negotiations, discussions, conferences leading up to the event, and who was involved prior to the news release regarding the event. u This will show who was aware of the material nonpublic information, what they knew, and when they knew it.
VI. Brokerage Records 1. Obtain brokerage account records for those with significant or highly suspiciously timed trading in the stocks and review those records to determine how unusual the trading is. 2. New account forms should provide names, numbers, third party trading authorizations, net worth, locations of accounts, geographic location of individuals, employment and trade activity. 3. Evaluate other stocks the person has been trading and look for unusual patterns. 4. Recordings and communications with trader.
VII. Phone Records Compel production of phone records, email, and instant messaging from all relevant persons. Include cell, land, home, office phones. Phone records show contacts and the potential passage of information at critical times.
VIII. Corporate Records 1. 2. 3. All Documents that relate to the material non-public information including emails, board minutes and business records. Calendars and scheduling software of relevant individuals who may have had access to the material non-public information. Policies – request copies of policies and procedures for employees that cover insider trading and “quiet periods” If stock issuing companies are not required to maintain such policies, the securities authority may want to consider requiring such a practice.
IX. Bank Records • Compel production of bank records to trace proceeds of the trading. • Follow the money trail to see who benefits from the trading, whether it be gains or losses avoided from selling a stock while in possession of negative information. • Obtain monthly accounts statements, checks, deposits and wire transfers to identify the transfers of money between individuals, which may show a sharing of profits or payment for a profitable tip.
X. Recognition Letter • Compile a list of suspicious names (can be those that conducted the trades, family, friends, associates, etc…) and attach it to a “recognition letter” that the stock issuing company is requested to circulate and identify. • The issuer should identify any histories or relationships and contacts with the names on the list. • The responses may indicate who may be a “tippee” of an insider who has knowledge of material non-public information
XI. Taking Statements and Testimony Compel statements from broker that placed the trades regarding: o o Communications with client/trader Whether they have knowledge of or access to the material non-public information Whether they have any contacts and relationship with the trader or the tippee Whether they have any contacts or relationship with any company officers or those with knowledge of the material non-public information.

Thank you khaledserry@gmail. com
- Slides: 38