SSL Prof Ravi Sandhu SECURE SOCKETS LAYER SSL





- Slides: 45
SSL Prof. Ravi Sandhu
SECURE SOCKETS LAYER (SSL) v layered on top of TCP v SSL versions 1. 0, 2. 0, 3. 1 v Netscape protocol v later refitted as IETF standard TLS (Transport Layer Security) v TLS 1. 0 very close to SSL 3. 1 © Ravi Sandhu 2002 2
SECURE SOCKETS LAYER (SSL) v application protocol independent v does not specify how application protocols add security with SSL Ø how to initiate SSL handshaking Ø how to interpret certificates v left to designers of upper layer protocols to figure out © Ravi Sandhu 2002 3
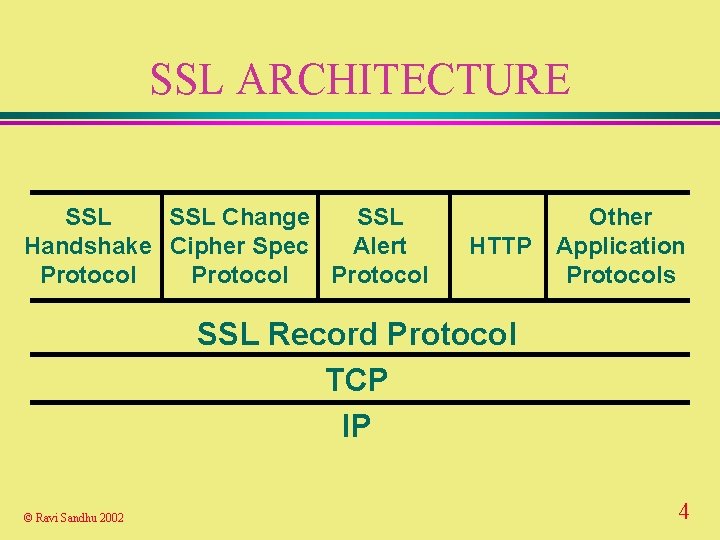
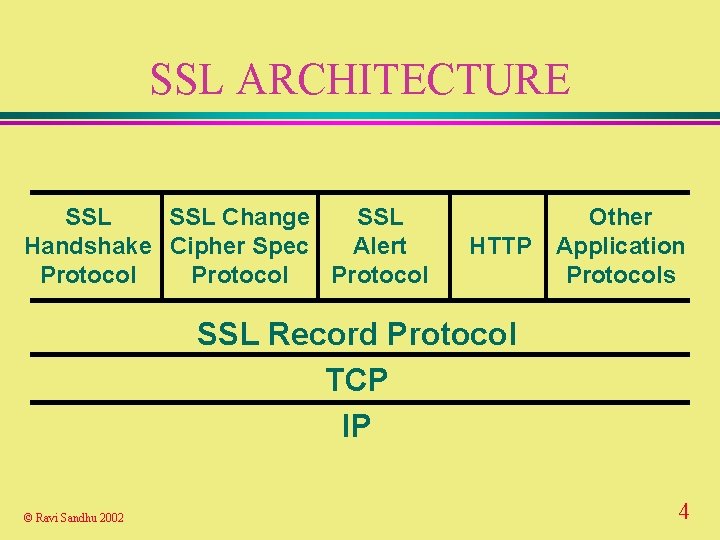
SSL ARCHITECTURE SSL Change SSL Handshake Cipher Spec Alert Protocol Other HTTP Application Protocols SSL Record Protocol TCP IP © Ravi Sandhu 2002 4
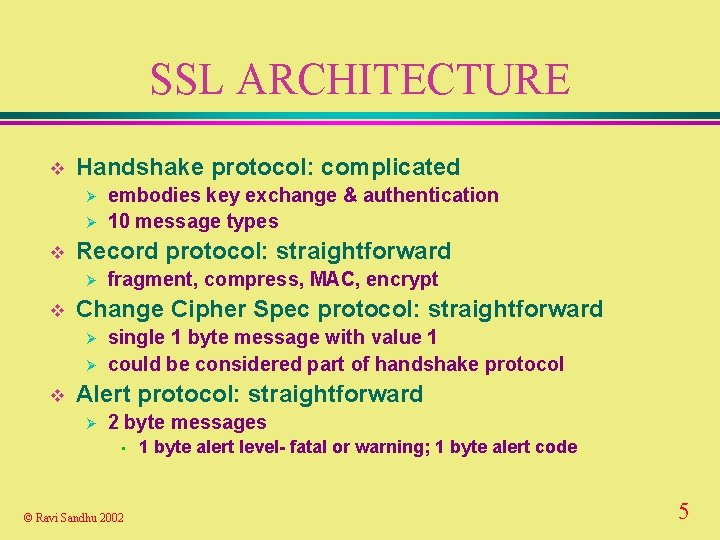
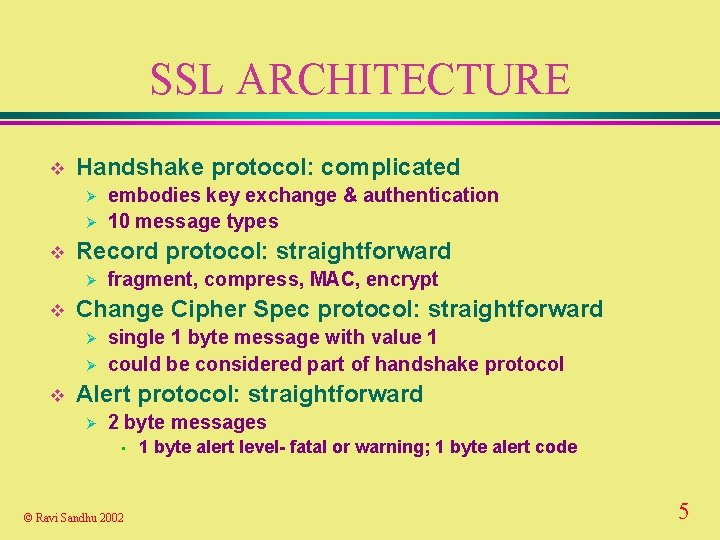
SSL ARCHITECTURE v Handshake protocol: complicated Ø Ø v Record protocol: straightforward Ø v fragment, compress, MAC, encrypt Change Cipher Spec protocol: straightforward Ø Ø v embodies key exchange & authentication 10 message types single 1 byte message with value 1 could be considered part of handshake protocol Alert protocol: straightforward Ø 2 byte messages • © Ravi Sandhu 2002 1 byte alert level- fatal or warning; 1 byte alert code 5
SSL/TLS DIFFERENCES TLS uses HMAC, SSL uses a precursor v TLS MAC covers compression version field in addition to what SSL MAC covers v TLS defines additional alert codes v other minor differences v TLS has a mode to fall back to SSL v © Ravi Sandhu 2002 6

SSL SERVICES v peer entity authentication v data confidentiality v data authentication and integrity v compression/decompression v generation/distribution of session keys Ø integrated v security © Ravi Sandhu 2002 into protocol parameter negotiation 7

SSL SESSIONS AND CONNECTIONS v Every connection is associated with one session v Session can be reused across multiple secure connections v Handshake protocol Ø establishes new session and connection together Ø uses existing session for new connection © Ravi Sandhu 2002 8
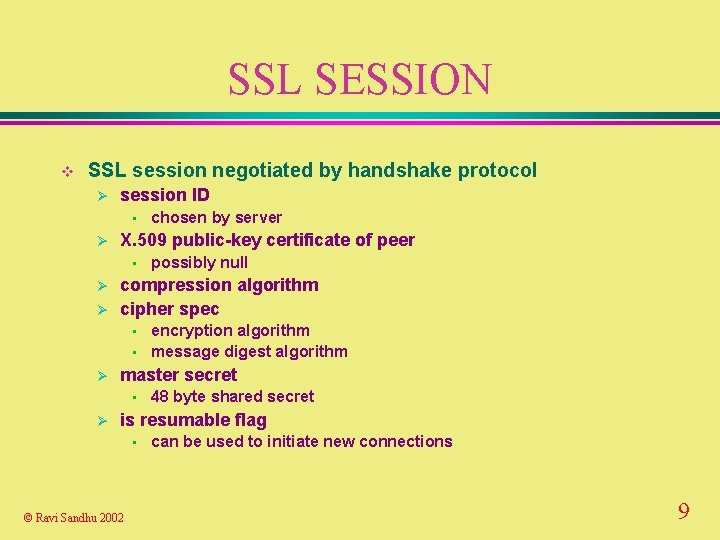
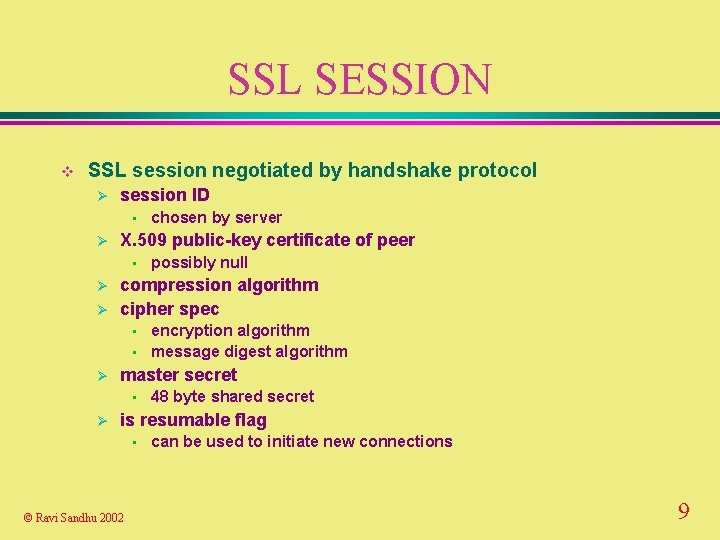
SSL SESSION v SSL session negotiated by handshake protocol Ø session ID • Ø X. 509 public-key certificate of peer • Ø Ø • encryption algorithm message digest algorithm master secret • Ø possibly null compression algorithm cipher spec • Ø chosen by server 48 byte shared secret is resumable flag • © Ravi Sandhu 2002 can be used to initiate new connections 9
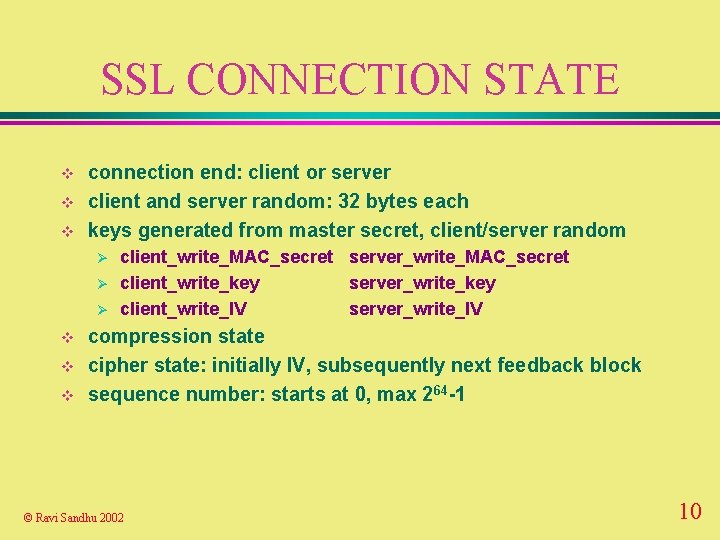
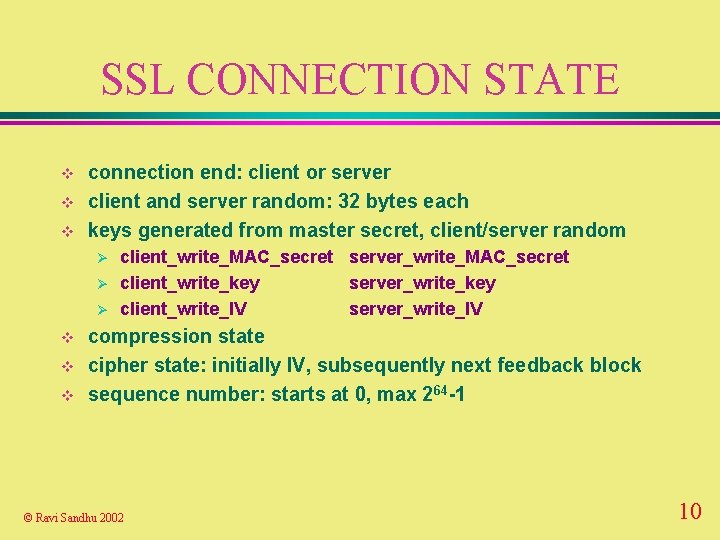
SSL CONNECTION STATE v v v connection end: client or server client and server random: 32 bytes each keys generated from master secret, client/server random Ø Ø Ø v v v client_write_MAC_secret server_write_MAC_secret client_write_key server_write_key client_write_IV server_write_IV compression state cipher state: initially IV, subsequently next feedback block sequence number: starts at 0, max 264 -1 © Ravi Sandhu 2002 10
SSL CONNECTION STATE v 4 parts to state Ø Ø v current read state current write state pending read state pending write state handshake protocol Ø Ø initially current state is empty either pending state can be made current and reinitialized to empty © Ravi Sandhu 2002 11
SSL RECORD PROTOCOL v 4 steps by sender (reversed by receiver) Ø Fragmentation Ø Compression Ø MAC Ø Encryption © Ravi Sandhu 2002 12
SSL RECORD PROTOCOL v each SSL record contains Ø content type: 8 bits, only 4 defined • • Ø Ø change_cipher_spec alert handshake application_data protocol version number: 8 bits major, 8 bits minor length: max 16 K bytes (actually 214+2048) data payload: optionally compressed and encrypted message authentication code (MAC) © Ravi Sandhu 2002 13
SSL HANDSHAKE PROTOCOL v initially SSL session has null compression and cipher algorithms v both are set by the handshake protocol at beginning of session v handshake protocol may be repeated during the session © Ravi Sandhu 2002 14
SSL HANDSHAKE PROTOCOL v Type: Ø 10 1 byte message types defined v length: 3 bytes v content © Ravi Sandhu 2002 15
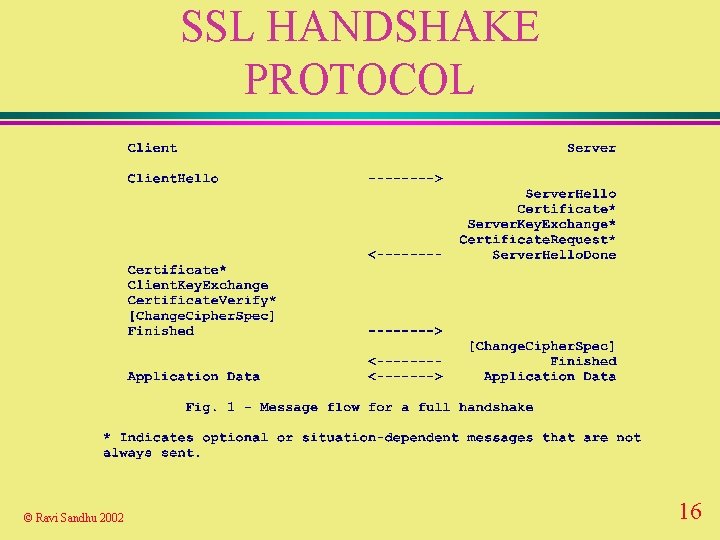
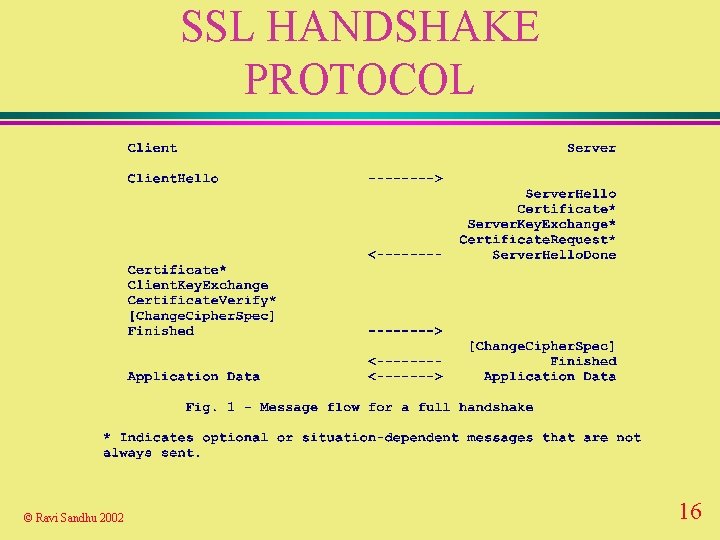
SSL HANDSHAKE PROTOCOL © Ravi Sandhu 2002 16
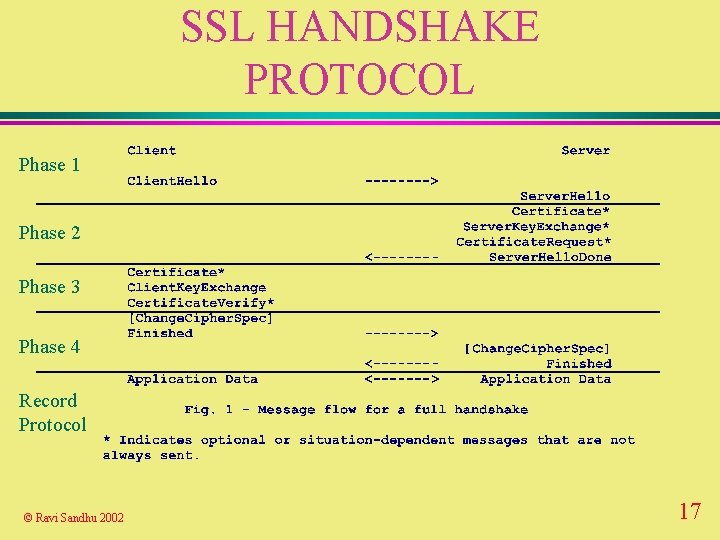
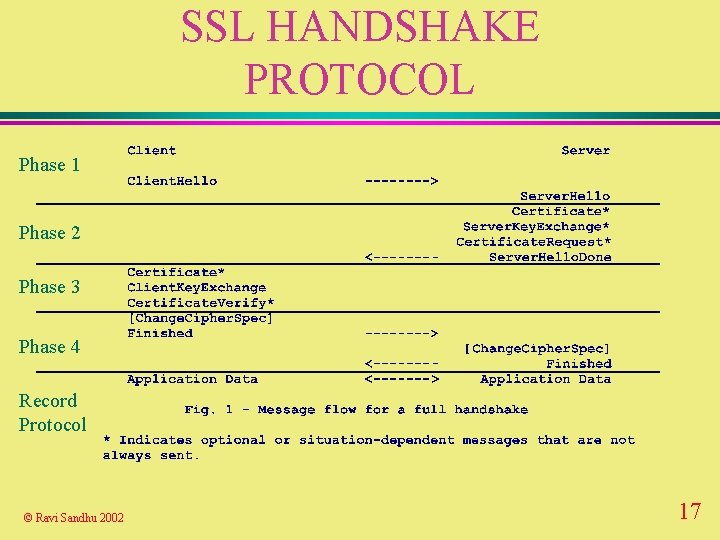
SSL HANDSHAKE PROTOCOL Phase 1 Phase 2 Phase 3 Phase 4 Record Protocol © Ravi Sandhu 2002 17
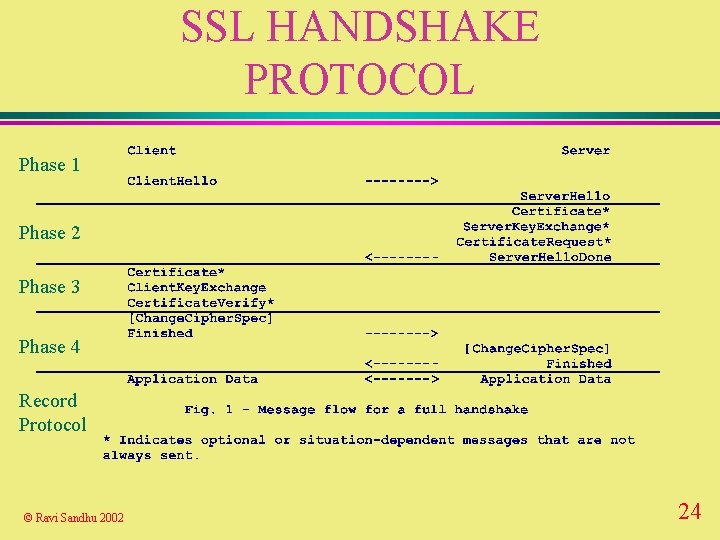
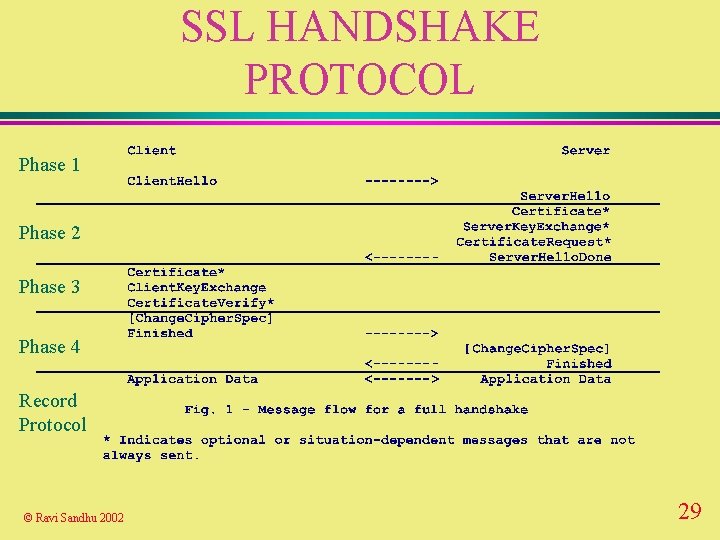
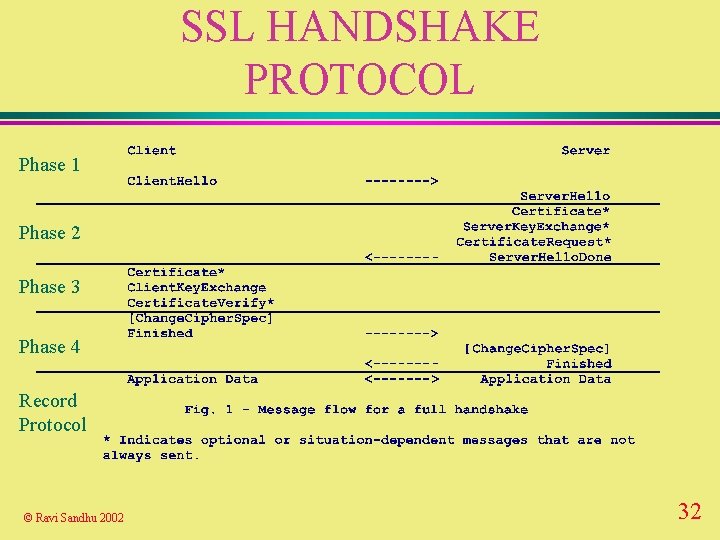
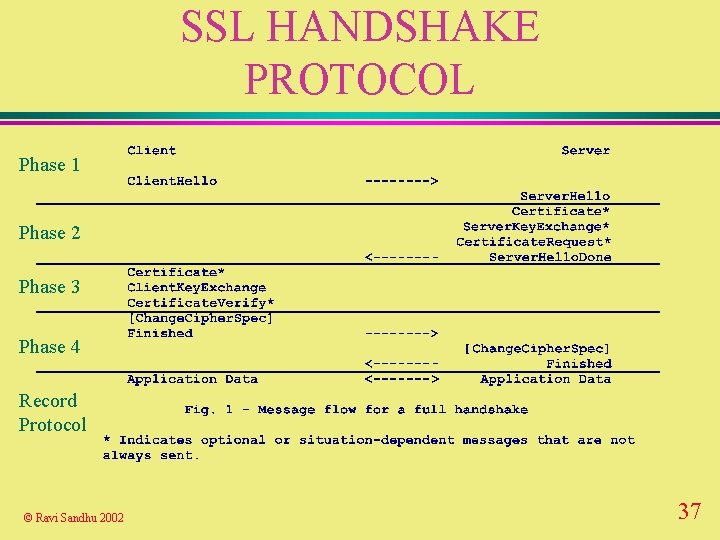
SSL HANDSHAKE PROTOCOL v Phase 1: Ø Establish v Phase 2: Ø Server v Phase authentication and key exchange 3: Ø Client v Phase security capabilities authentication and key exchange 4: Ø Finish © Ravi Sandhu 2002 18
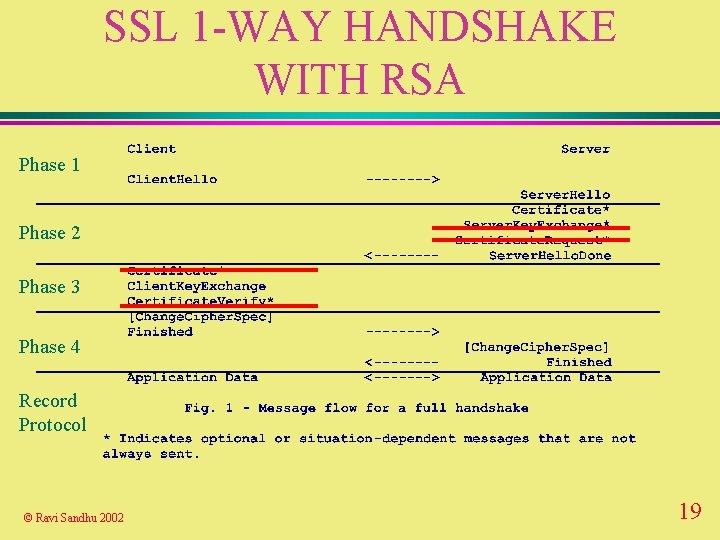
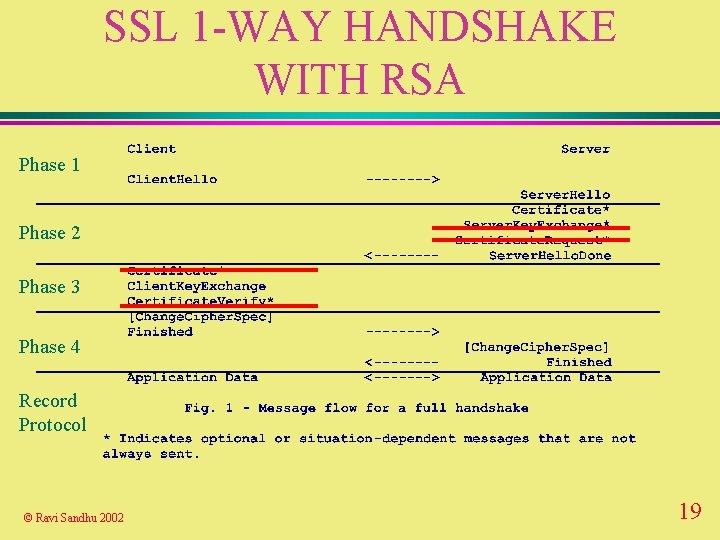
SSL 1 -WAY HANDSHAKE WITH RSA Phase 1 Phase 2 Phase 3 Phase 4 Record Protocol © Ravi Sandhu 2002 19
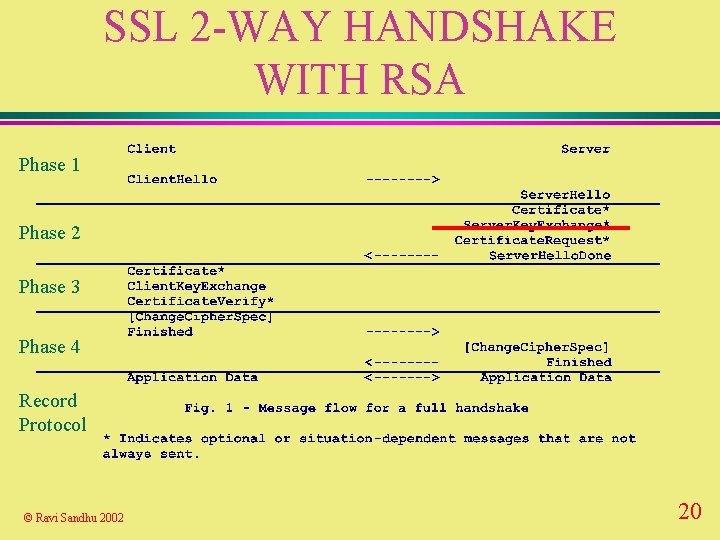
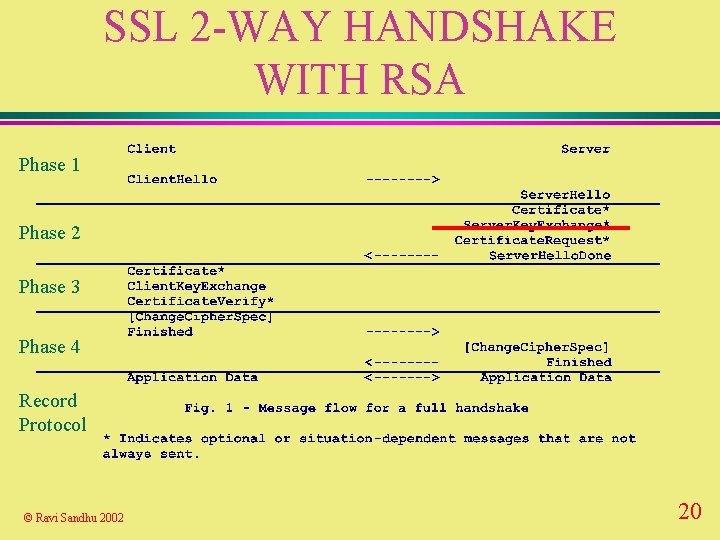
SSL 2 -WAY HANDSHAKE WITH RSA Phase 1 Phase 2 Phase 3 Phase 4 Record Protocol © Ravi Sandhu 2002 20
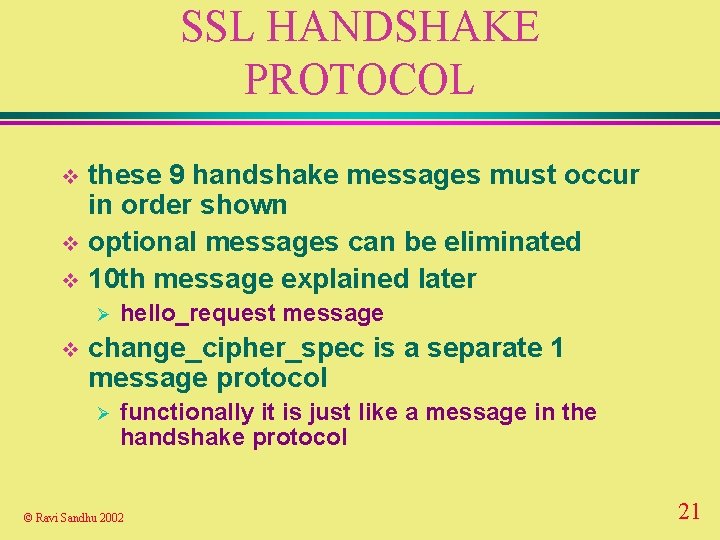
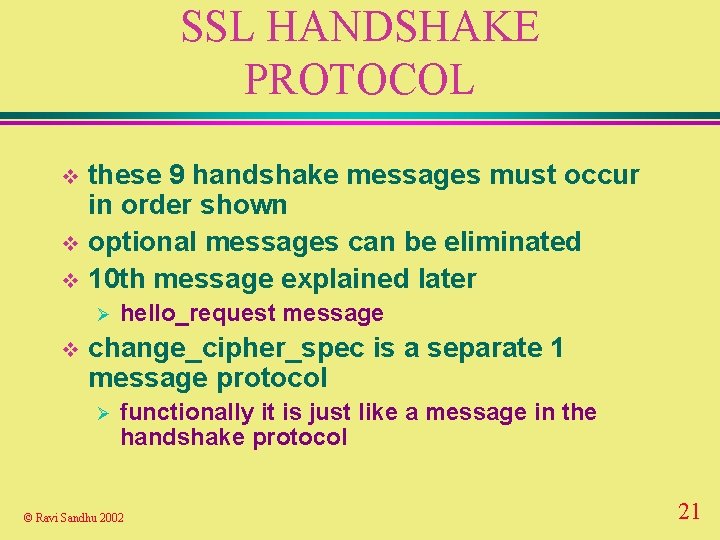
SSL HANDSHAKE PROTOCOL these 9 handshake messages must occur in order shown v optional messages can be eliminated v 10 th message explained later v Ø v hello_request message change_cipher_spec is a separate 1 message protocol Ø functionally it is just like a message in the handshake protocol © Ravi Sandhu 2002 21
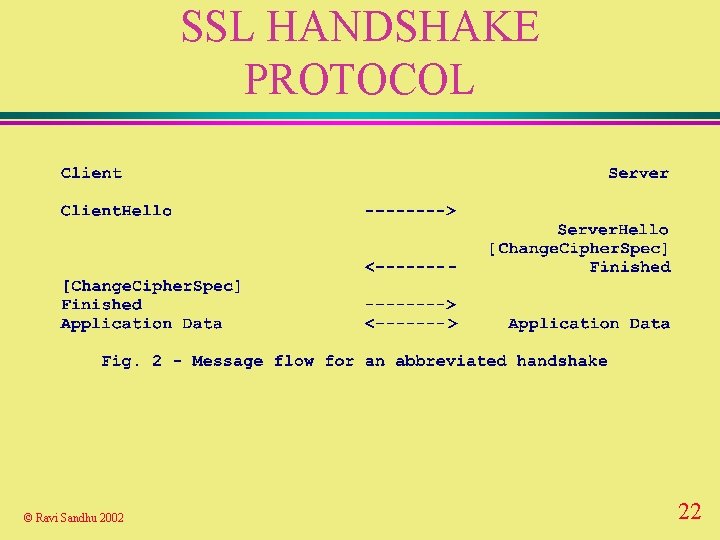
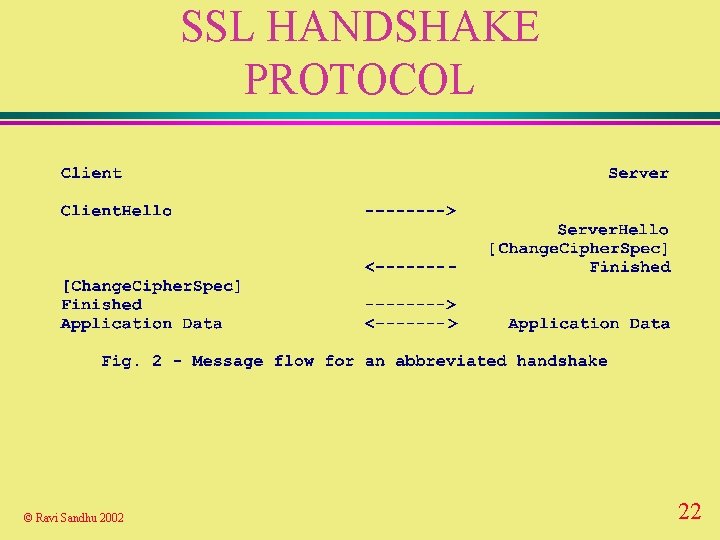
SSL HANDSHAKE PROTOCOL © Ravi Sandhu 2002 22
SSL HANDSHAKE PROTOCOL hello_request (not shown) can be sent anytime from server to client to request client to start handshake protocol to renegotiate session when convenient v can be ignored by client v Ø Ø if already negotiating a session don’t want to renegotiate a session • © Ravi Sandhu 2002 client may respond with a no_renegotiation alert 23
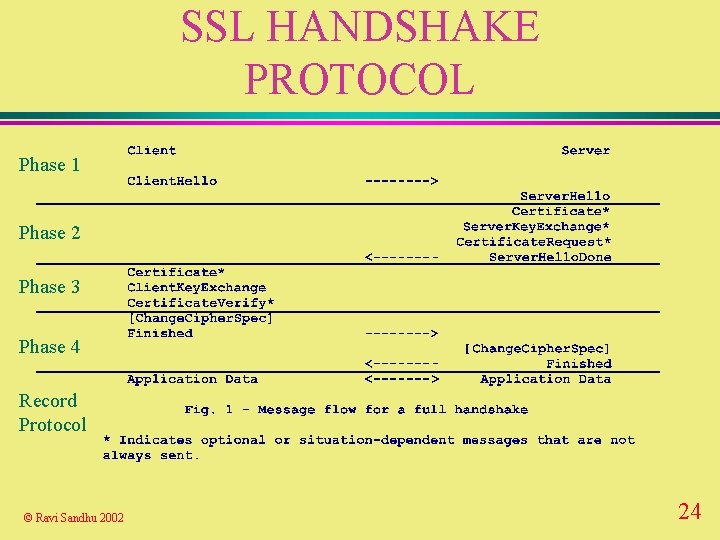
SSL HANDSHAKE PROTOCOL Phase 1 Phase 2 Phase 3 Phase 4 Record Protocol © Ravi Sandhu 2002 24

SSL HANDSHAKE: PHASE 1 ESTABLISH SECURITY CAPABILITIES v client hello Ø Ø 4 byte timestamp, 28 byte random value session ID: • non-zero for new connection on existing session zero for new connection on new session client version: highest version cipher_suite list: ordered list compression list: ordered list • Ø Ø Ø © Ravi Sandhu 2002 25

SSL HANDSHAKE: PHASE 1 ESTABLISH SECURITY CAPABILITIES v server hello Ø Ø 32 byte random value session ID: • Ø version • Ø Ø new or reuse lower of client suggested and highest supported cipher_suite list: single choice compression list: single choice © Ravi Sandhu 2002 26
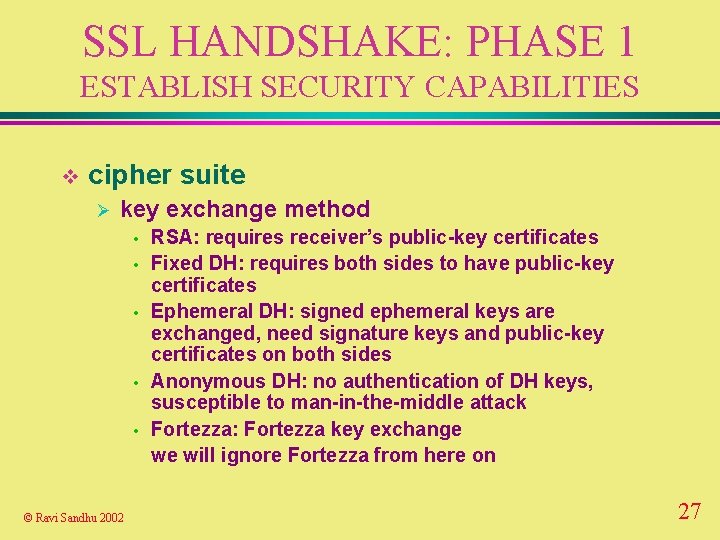
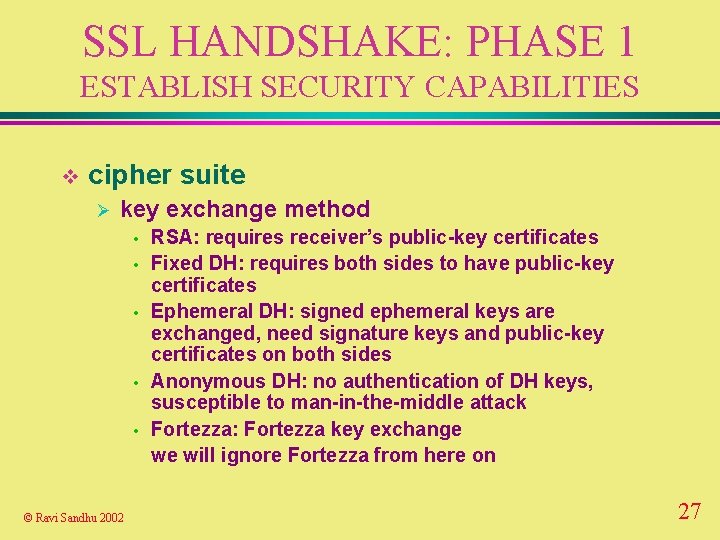
SSL HANDSHAKE: PHASE 1 ESTABLISH SECURITY CAPABILITIES v cipher suite Ø key exchange method • • • © Ravi Sandhu 2002 RSA: requires receiver’s public-key certificates Fixed DH: requires both sides to have public-key certificates Ephemeral DH: signed ephemeral keys are exchanged, need signature keys and public-key certificates on both sides Anonymous DH: no authentication of DH keys, susceptible to man-in-the-middle attack Fortezza: Fortezza key exchange we will ignore Fortezza from here on 27

SSL HANDSHAKE: PHASE 1 ESTABLISH SECURITY CAPABILITIES v cipher suite Ø cipher spec • • © Ravi Sandhu 2002 Cipher. Algorithm: RC 4, RC 2, DES, 3 DES, DES 40, IDEA, Fortezza MACAlgorithm: MD 5 or SHA-1 Cipher. Type: stream or block Is. Exportable: true or false Hash. Size: 0, 16 or 20 bytes Key Material: used to generate write keys IV Size: size of IV for CBC 28
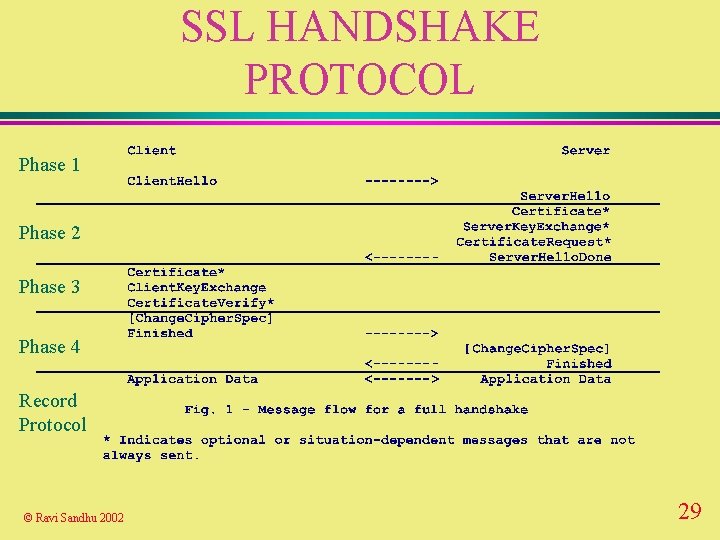
SSL HANDSHAKE PROTOCOL Phase 1 Phase 2 Phase 3 Phase 4 Record Protocol © Ravi Sandhu 2002 29
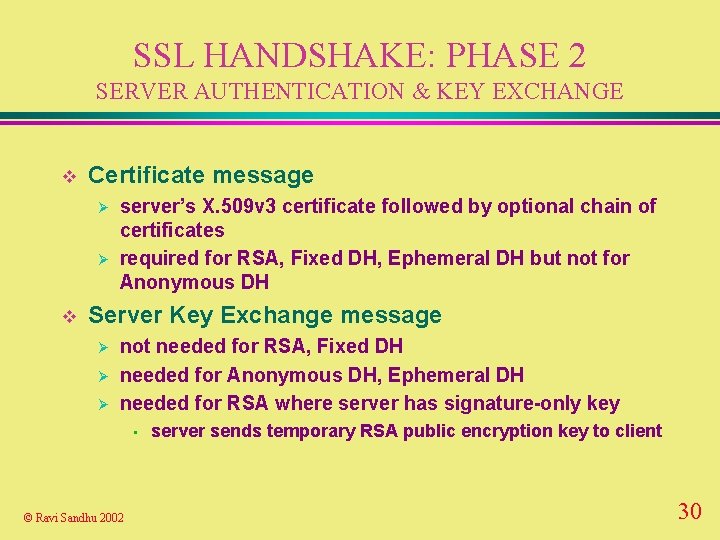
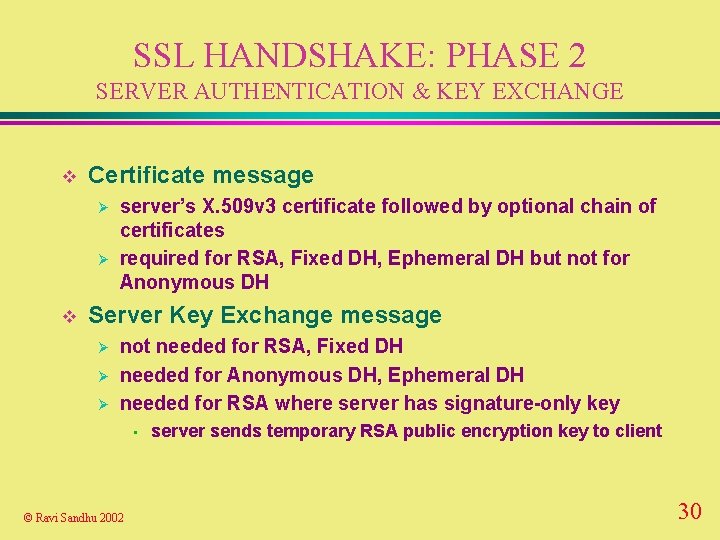
SSL HANDSHAKE: PHASE 2 SERVER AUTHENTICATION & KEY EXCHANGE v Certificate message Ø Ø v server’s X. 509 v 3 certificate followed by optional chain of certificates required for RSA, Fixed DH, Ephemeral DH but not for Anonymous DH Server Key Exchange message Ø Ø Ø not needed for RSA, Fixed DH needed for Anonymous DH, Ephemeral DH needed for RSA where server has signature-only key • © Ravi Sandhu 2002 server sends temporary RSA public encryption key to client 30
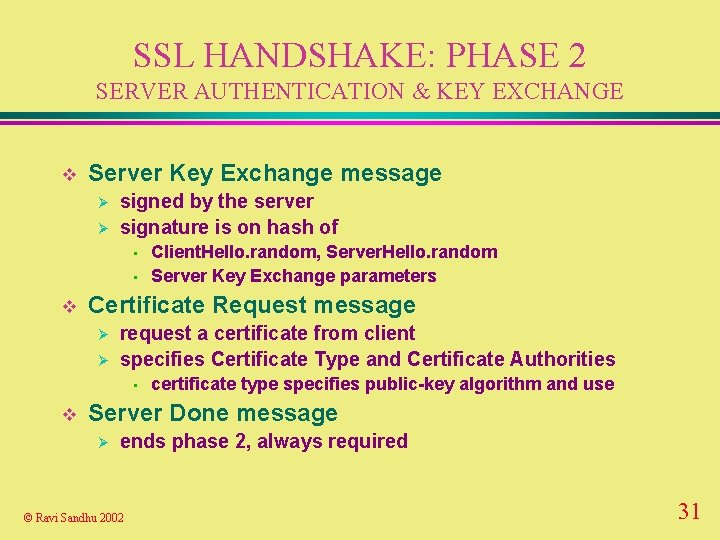
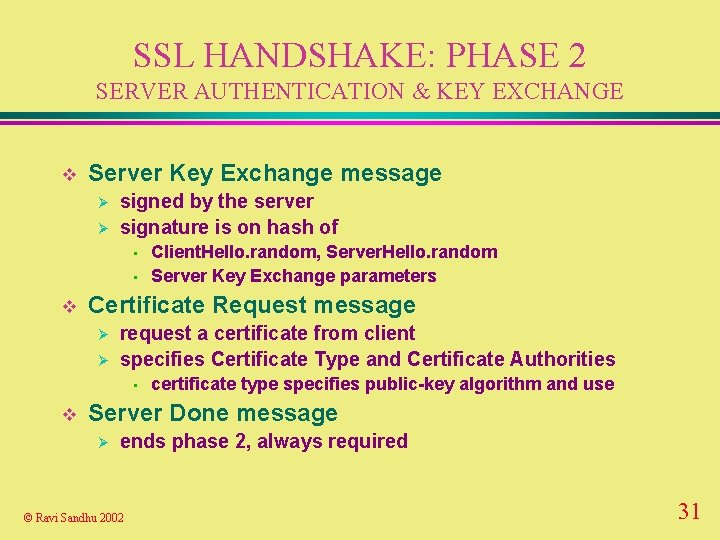
SSL HANDSHAKE: PHASE 2 SERVER AUTHENTICATION & KEY EXCHANGE v Server Key Exchange message Ø Ø signed by the server signature is on hash of • • v Certificate Request message Ø Ø request a certificate from client specifies Certificate Type and Certificate Authorities • v Client. Hello. random, Server. Hello. random Server Key Exchange parameters certificate type specifies public-key algorithm and use Server Done message Ø ends phase 2, always required © Ravi Sandhu 2002 31
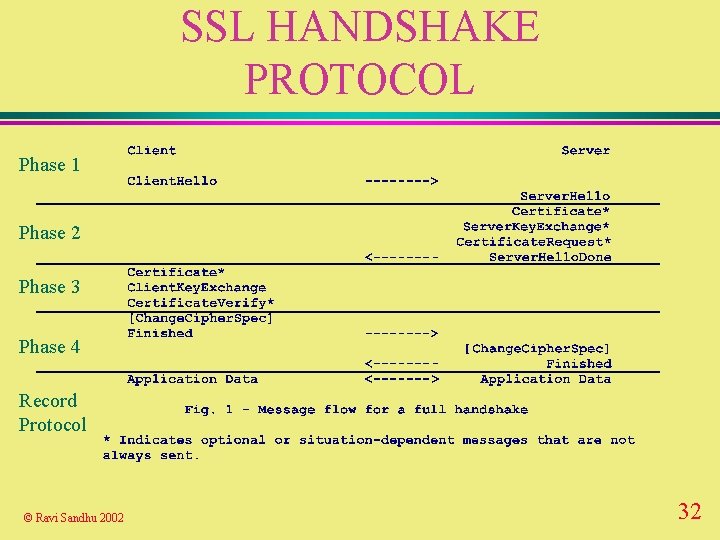
SSL HANDSHAKE PROTOCOL Phase 1 Phase 2 Phase 3 Phase 4 Record Protocol © Ravi Sandhu 2002 32
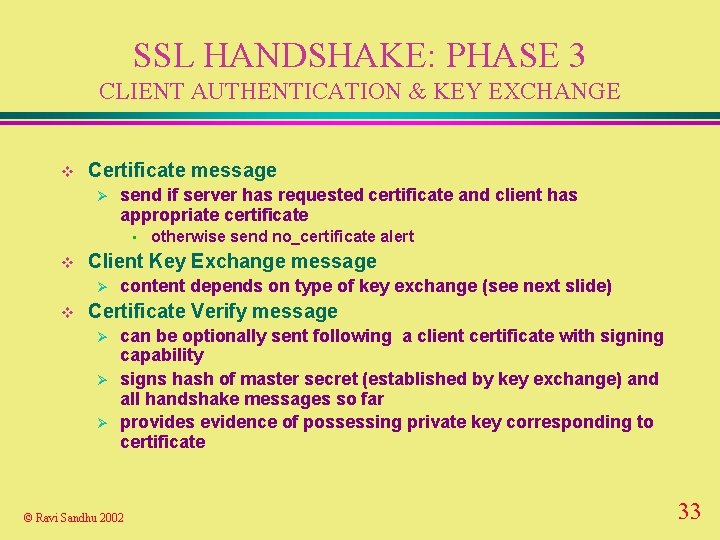
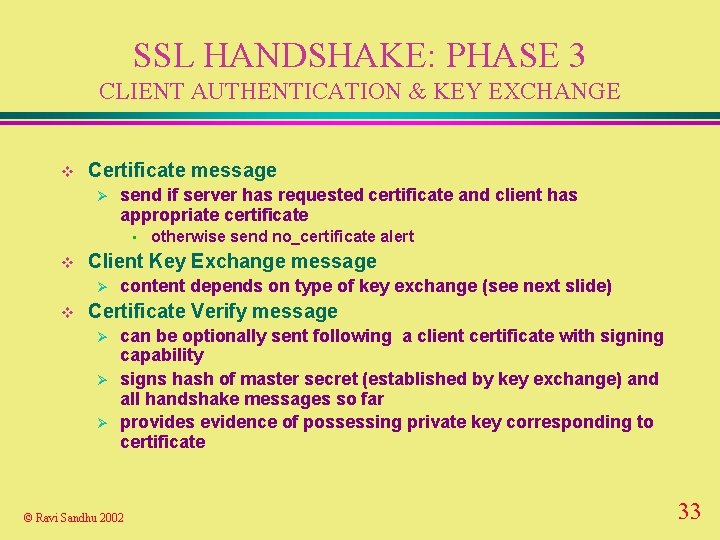
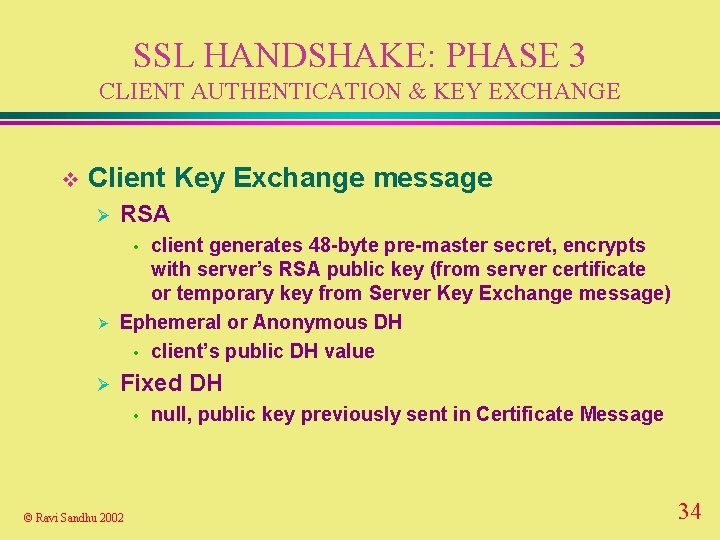
SSL HANDSHAKE: PHASE 3 CLIENT AUTHENTICATION & KEY EXCHANGE v Certificate message Ø send if server has requested certificate and client has appropriate certificate • v Client Key Exchange message Ø v otherwise send no_certificate alert content depends on type of key exchange (see next slide) Certificate Verify message Ø Ø Ø can be optionally sent following a client certificate with signing capability signs hash of master secret (established by key exchange) and all handshake messages so far provides evidence of possessing private key corresponding to certificate © Ravi Sandhu 2002 33
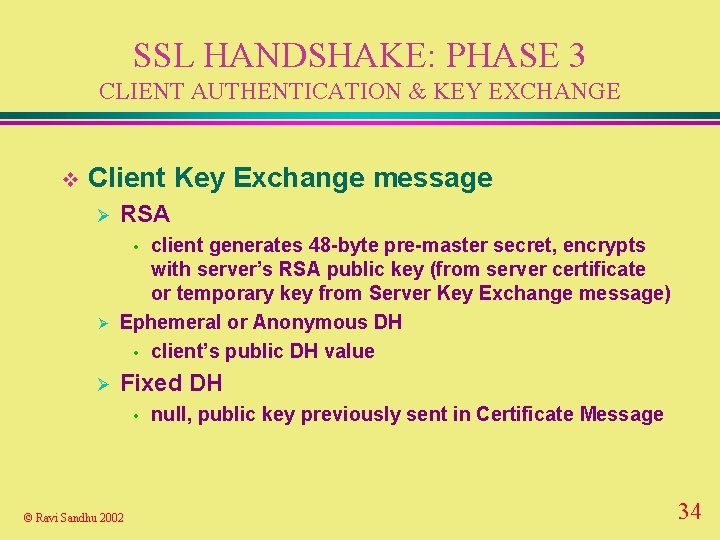
SSL HANDSHAKE: PHASE 3 CLIENT AUTHENTICATION & KEY EXCHANGE v Client Key Exchange message Ø RSA client generates 48 -byte pre-master secret, encrypts with server’s RSA public key (from server certificate or temporary key from Server Key Exchange message) Ephemeral or Anonymous DH • client’s public DH value • Ø Ø Fixed DH • © Ravi Sandhu 2002 null, public key previously sent in Certificate Message 34
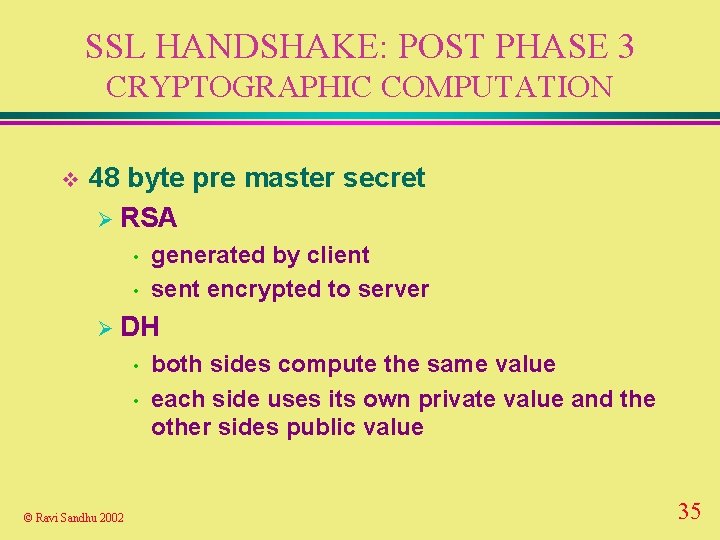
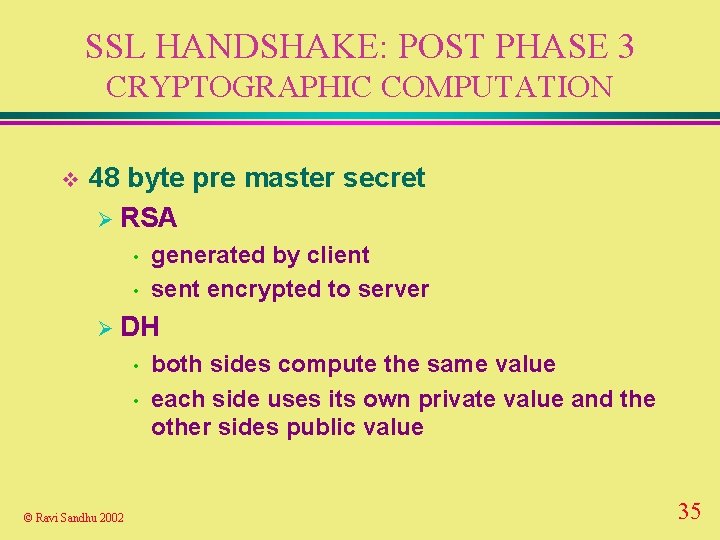
SSL HANDSHAKE: POST PHASE 3 CRYPTOGRAPHIC COMPUTATION v 48 byte pre master secret Ø RSA • • generated by client sent encrypted to server Ø DH • • © Ravi Sandhu 2002 both sides compute the same value each side uses its own private value and the other sides public value 35
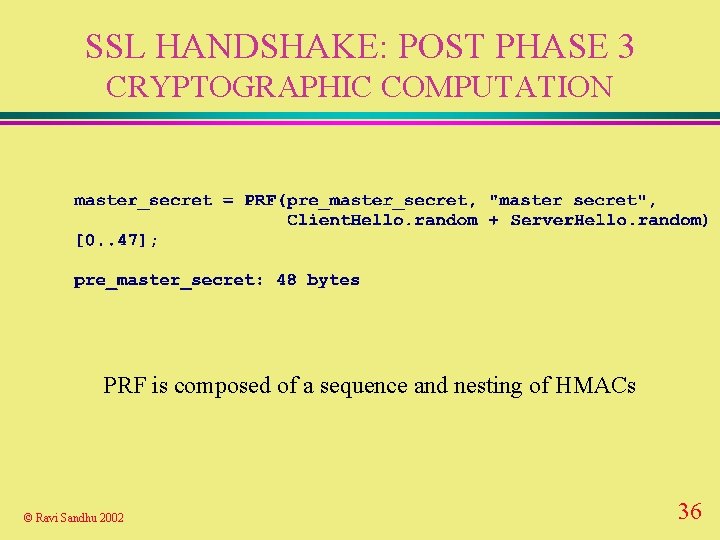
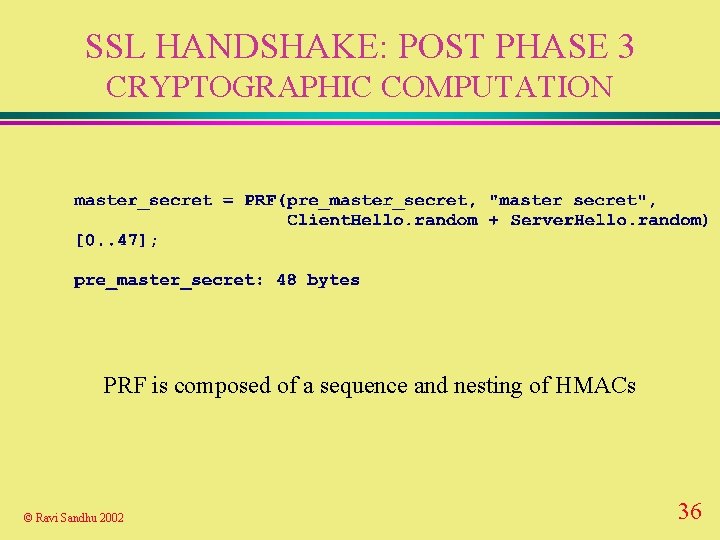
SSL HANDSHAKE: POST PHASE 3 CRYPTOGRAPHIC COMPUTATION PRF is composed of a sequence and nesting of HMACs © Ravi Sandhu 2002 36
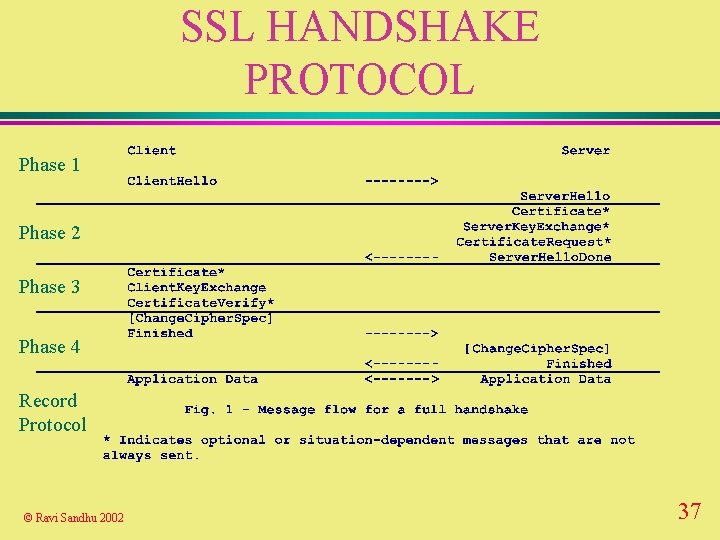
SSL HANDSHAKE PROTOCOL Phase 1 Phase 2 Phase 3 Phase 4 Record Protocol © Ravi Sandhu 2002 37
SSL HANDSHAKE: PHASE 4 FINISH v Change Cipher Spec message Ø not considered part of handshake protocol but in some sense is part of it v Finished message Ø sent under new algorithms and keys Ø content is hash of all previous messages and master secret © Ravi Sandhu 2002 38
SSL HANDSHAKE: PHASE 4 FINISH v Change Cipher Spec message Ø Ø 1 byte message protected by current state copies pending state to current state • • Ø sender copies write pending state to write current state receiver copies read pending state to read current state immediately send finished message under new current state © Ravi Sandhu 2002 39
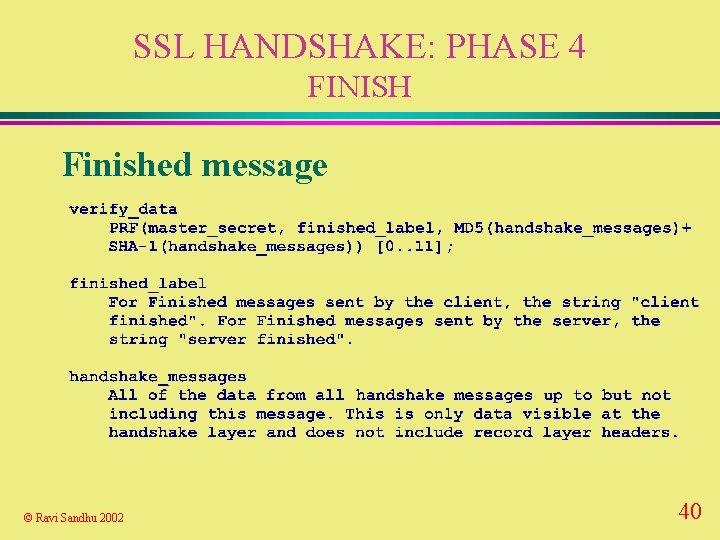
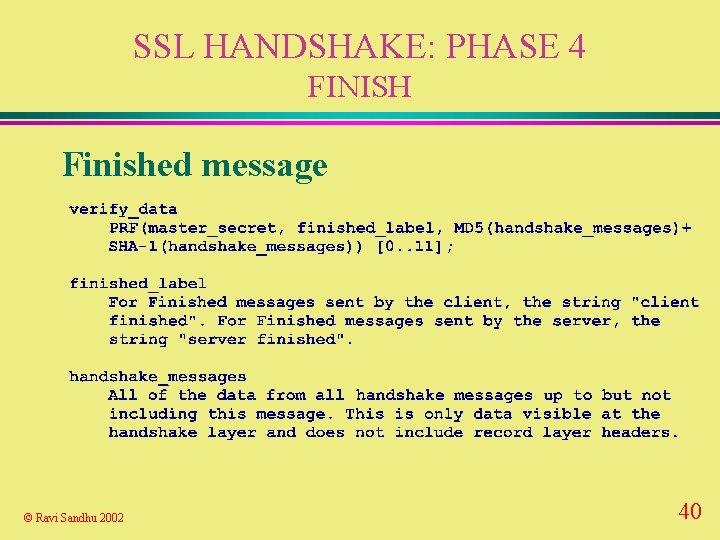
SSL HANDSHAKE: PHASE 4 FINISH Finished message © Ravi Sandhu 2002 40
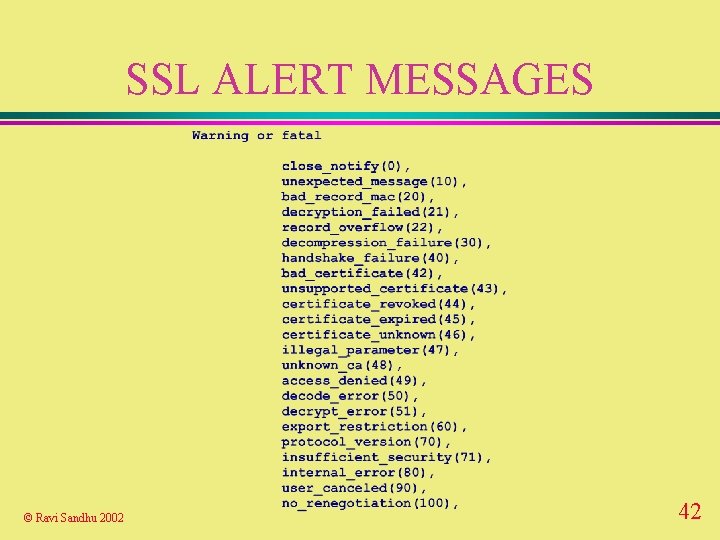
SSL ALERT PROTOCOL v 2 byte alert messages Ø 1 byte level • Ø 1 • © Ravi Sandhu 2002 fatal or warning byte alert code 41
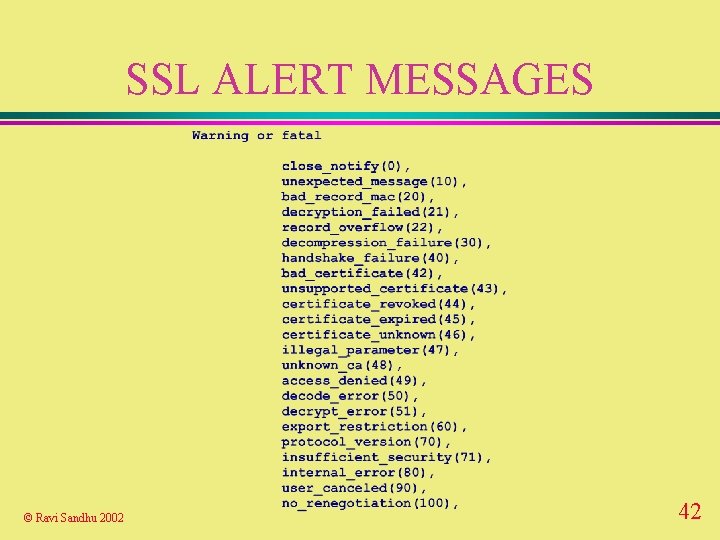
SSL ALERT MESSAGES © Ravi Sandhu 2002 42
SSL ALERT MESSAGES v always fatal Ø unexpected_message Ø bad_record_mac Ø decompression_failure Ø handshake_failure Ø illegal_parameter © Ravi Sandhu 2002 43
APPLICATIONS AND SSL v use dedicated port numbers for every application that uses SSL Ø de facto what is happening v use normal application port and negotiate security options as part of application protocol v negotiate use of SSL during normal TCP/IP connection establishment © Ravi Sandhu 2002 44
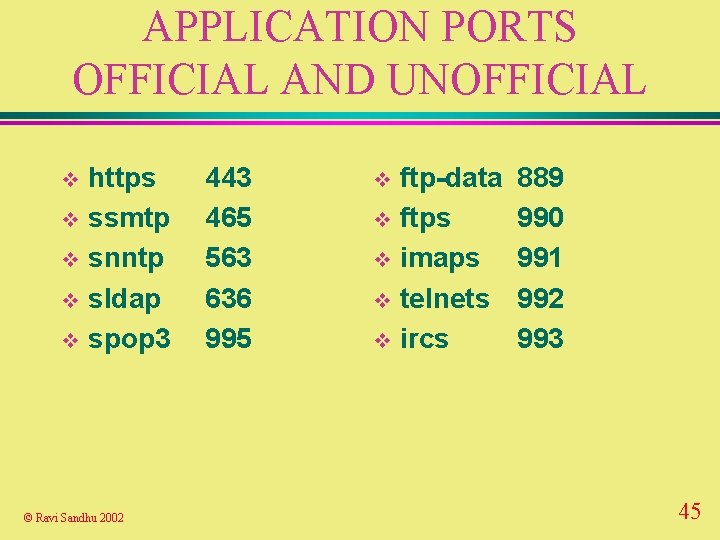
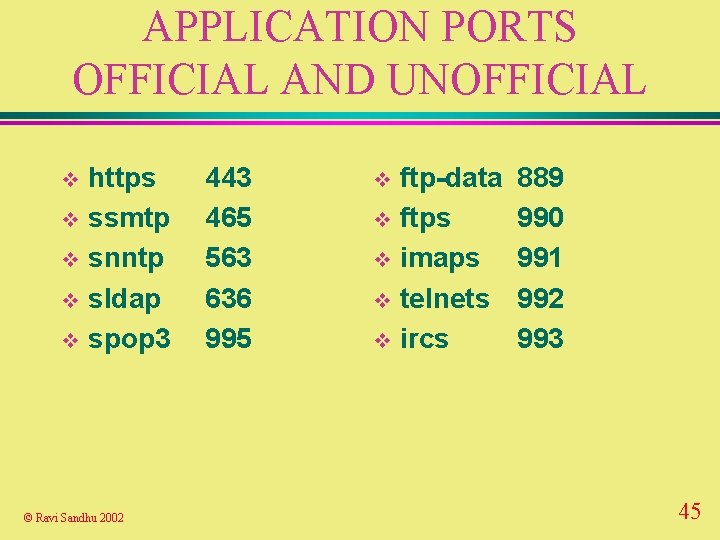
APPLICATION PORTS OFFICIAL AND UNOFFICIAL https v ssmtp v snntp v sldap v spop 3 v © Ravi Sandhu 2002 443 465 563 636 995 ftp-data v ftps v imaps v telnets v ircs v 889 990 991 992 993 45