SRV RR other Name Stefan Santesson Microsoft The
- Slides: 8
SRV RR other. Name Stefan Santesson Microsoft
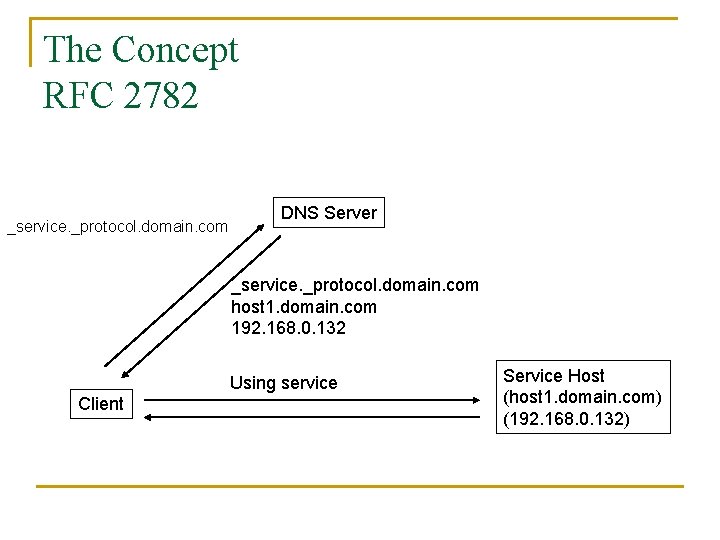
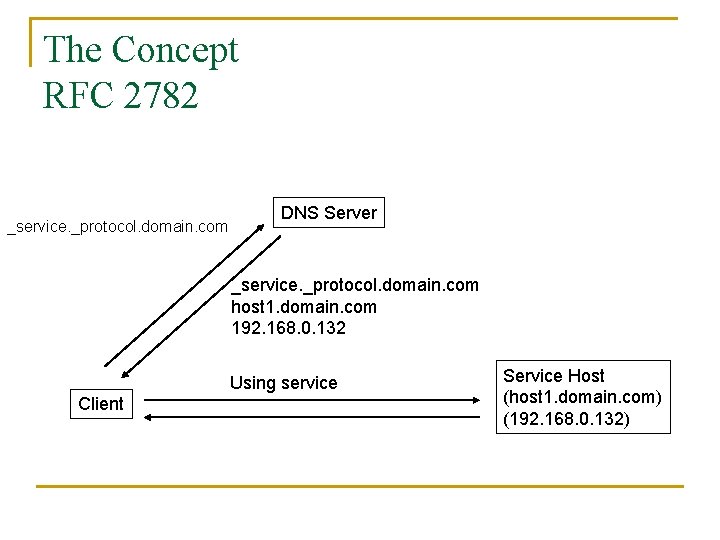
The Concept RFC 2782 _service. _protocol. domain. com DNS Server _service. _protocol. domain. com host 1. domain. com 192. 168. 0. 132 Using service Client Service Host (host 1. domain. com) (192. 168. 0. 132)
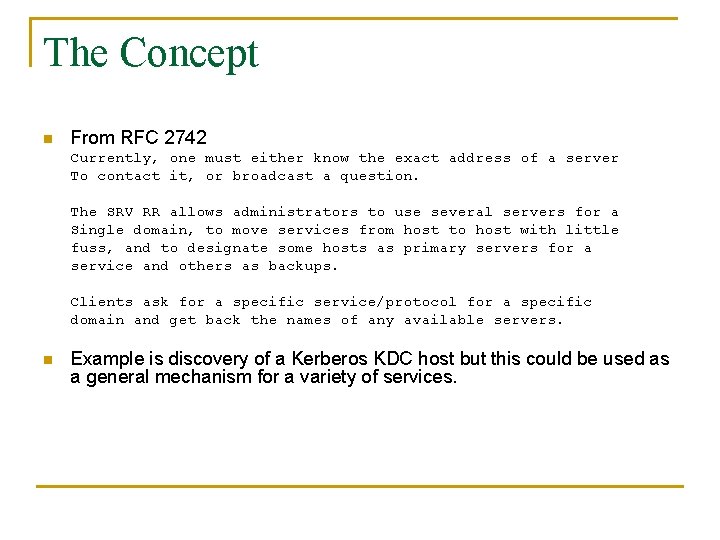
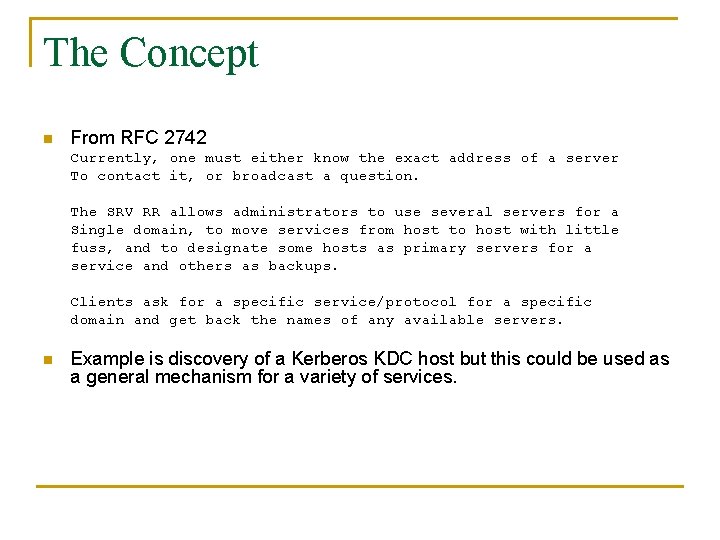
The Concept n From RFC 2742 Currently, one must either know the exact address of a server To contact it, or broadcast a question. The SRV RR allows administrators to use several servers for a Single domain, to move services from host to host with little fuss, and to designate some hosts as primary servers for a service and others as backups. Clients ask for a specific service/protocol for a specific domain and get back the names of any available servers. n Example is discovery of a Kerberos KDC host but this could be used as a general mechanism for a variety of services.
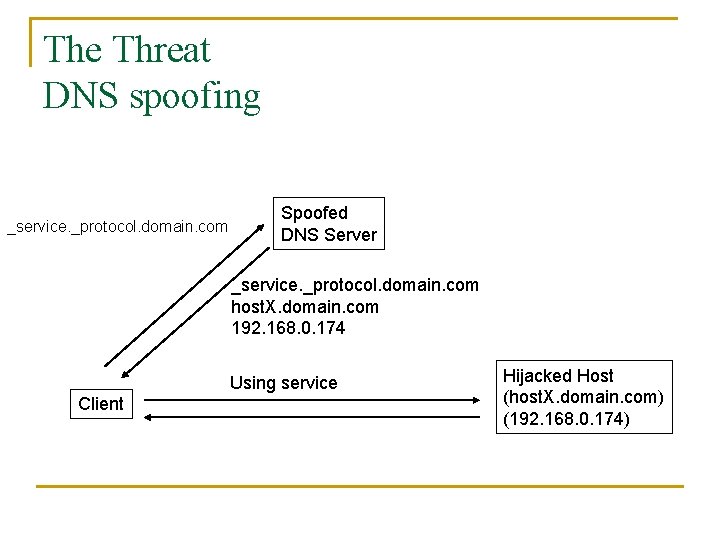
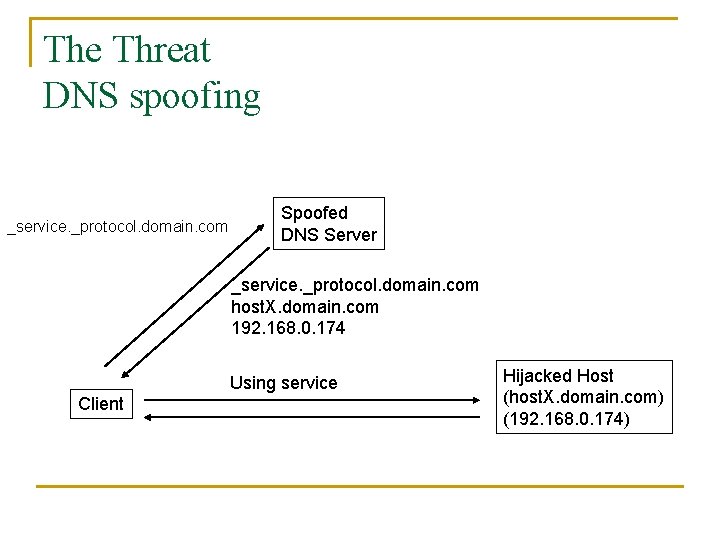
The Threat DNS spoofing _service. _protocol. domain. com Spoofed DNS Server _service. _protocol. domain. com host. X. domain. com 192. 168. 0. 174 Using service Client Hijacked Host (host. X. domain. com) (192. 168. 0. 174)
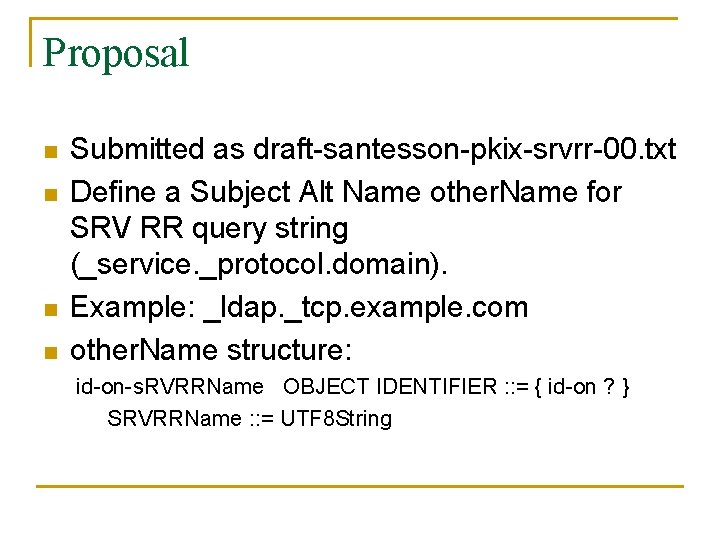
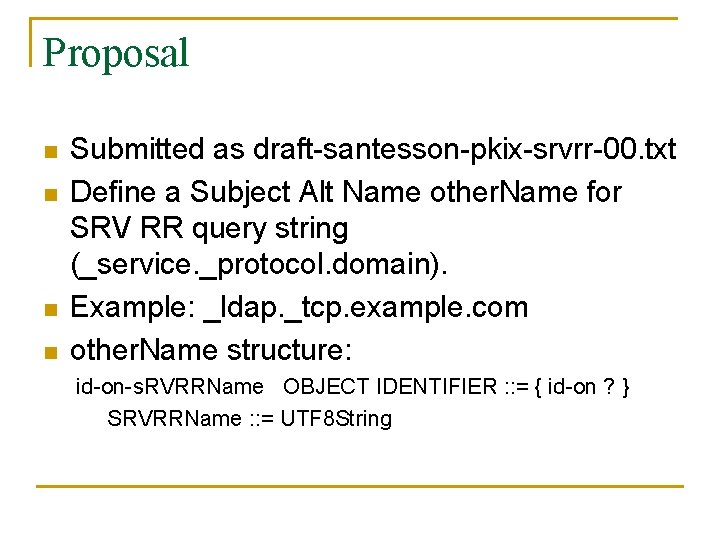
Proposal n n Submitted as draft-santesson-pkix-srvrr-00. txt Define a Subject Alt Name other. Name for SRV RR query string (_service. _protocol. domain). Example: _ldap. _tcp. example. com other. Name structure: id-on-s. RVRRName OBJECT IDENTIFIER : : = { id-on ? } SRVRRName : : = UTF 8 String
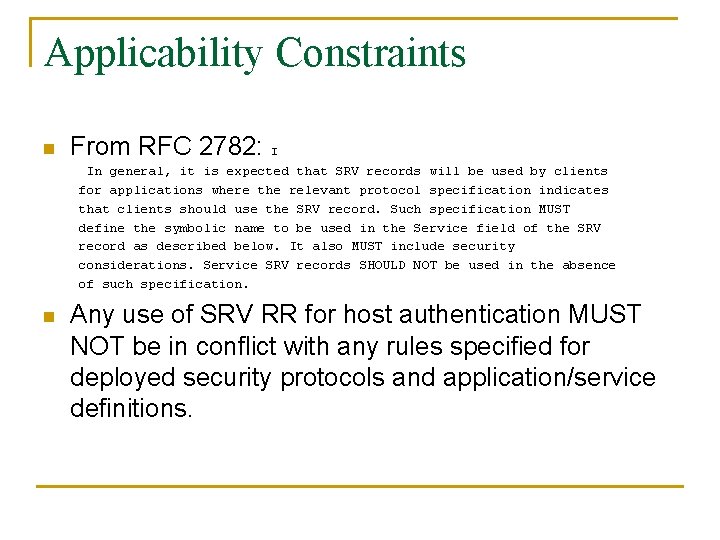
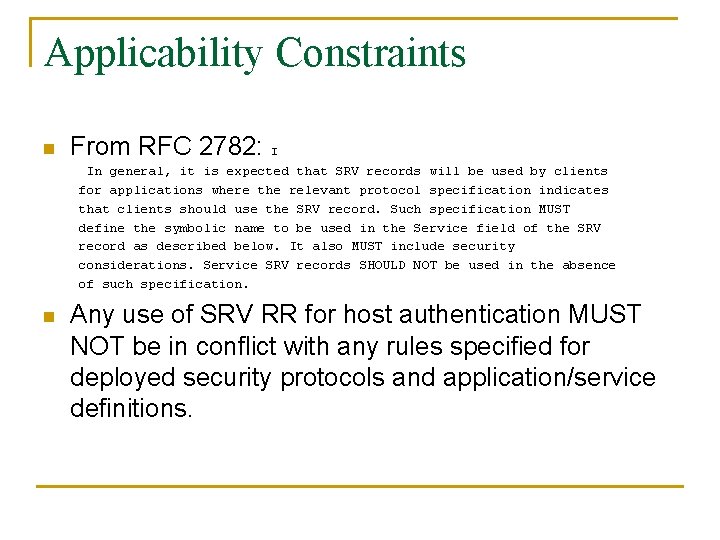
Applicability Constraints n From RFC 2782: I In general, it is expected that SRV records will be used by clients for applications where the relevant protocol specification indicates that clients should use the SRV record. Such specification MUST define the symbolic name to be used in the Service field of the SRV record as described below. It also MUST include security considerations. Service SRV records SHOULD NOT be used in the absence of such specification. n Any use of SRV RR for host authentication MUST NOT be in conflict with any rules specified for deployed security protocols and application/service definitions.
Request n Request that PKIX accept the task to define this SAN other. Name so it can be referenced and used by other protocol specifications to support host authentication where applicable.
Path forward n n n Correct known errors (IA 5 String -> UTF 8 String) Submit as first pkix draft (00) Define appropriate constraints and security considerations Proceed as standards track WG last call after Vancouver IETF