Spring 2008 CS 155 Network Protocols and Vulnerabilities
Spring 2008 CS 155 Network Protocols and Vulnerabilities John Mitchell
Outline Basic Networking Network attacks n Attacking host-to-host datagram protocols w SYN flooding, TCP Spoofing, … n Attacking network infrastructure w Routing w Domain Name System This lecture is about the way things work now and how they are not perfect. Next lecture – some security improvements (still not perfect)

Internet Infrastructure ISP Backbone ISP Local and interdomain routing n n TCP/IP for routing, connections BGP for routing announcements Domain Name System n Find IP address from symbolic name (www. cs. stanford. edu)
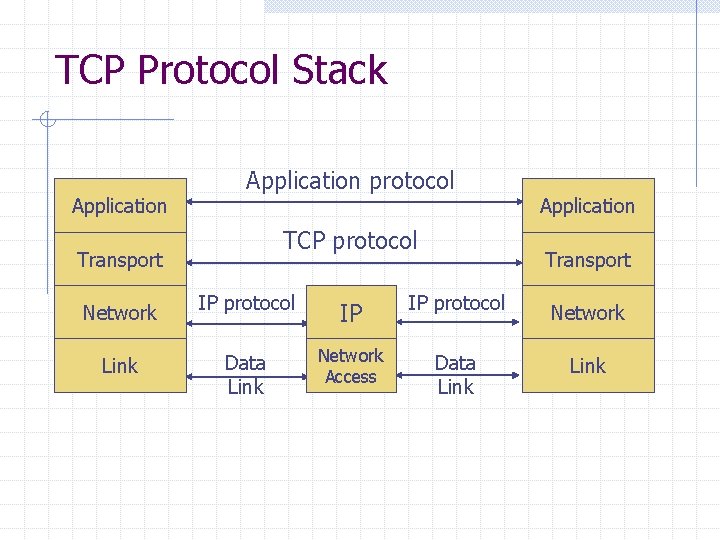
TCP Protocol Stack Application protocol TCP protocol Transport Application Transport Network IP protocol IP IP protocol Network Link Data Link Network Access Data Link
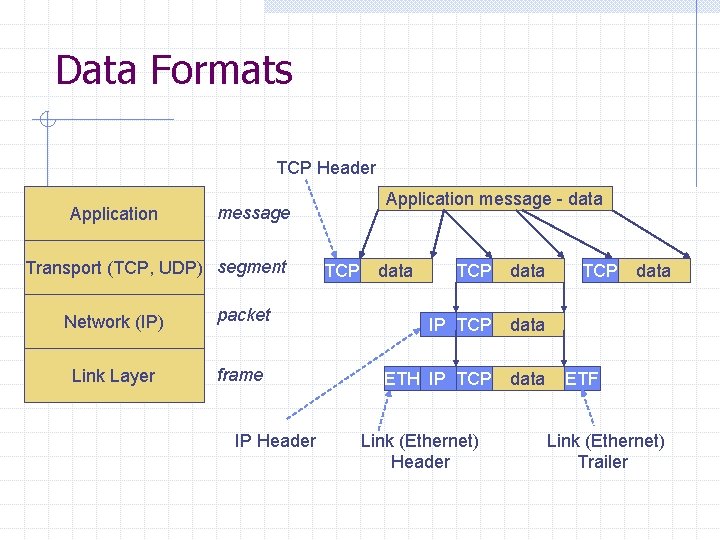
Data Formats TCP Header Application message - data message Transport (TCP, UDP) segment Network (IP) packet Link Layer frame IP Header TCP data IP TCP data ETH IP TCP data Link (Ethernet) Header TCP data ETF Link (Ethernet) Trailer
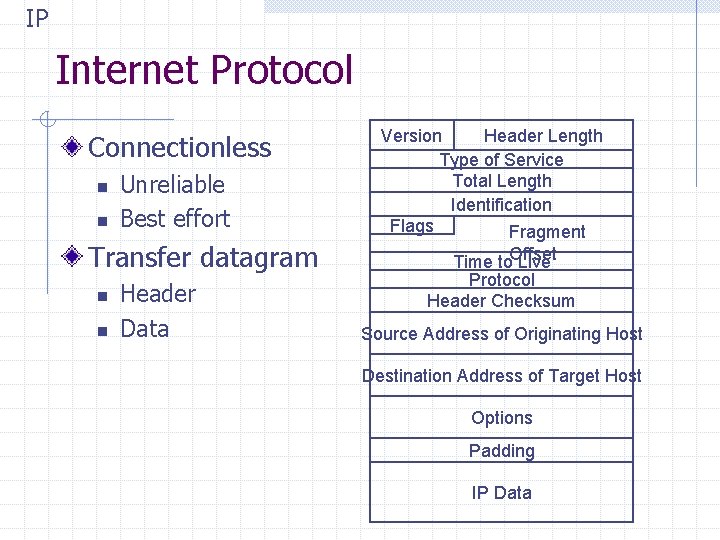
IP Internet Protocol Connectionless n n Unreliable Best effort Transfer datagram n n Header Data Version Header Length Type of Service Total Length Identification Flags Fragment Time to. Offset Live Protocol Header Checksum Source Address of Originating Host Destination Address of Target Host Options Padding IP Data
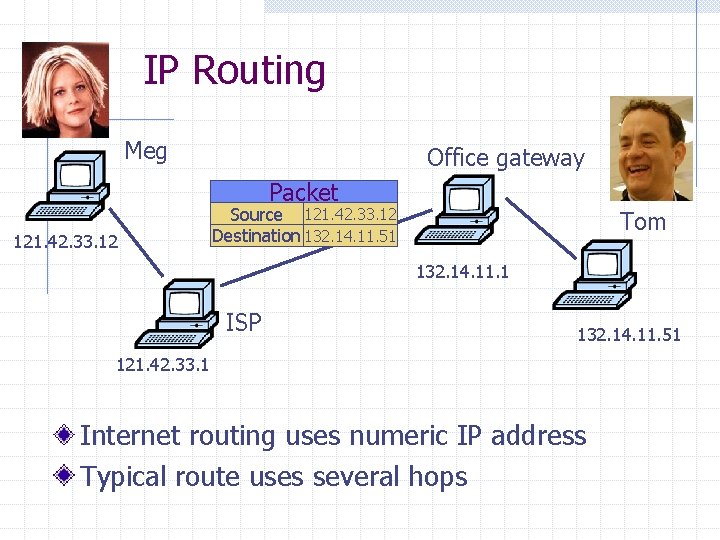
IP Routing Meg Office gateway Packet 121. 42. 33. 12 Source 121. 42. 33. 12 Destination 132. 14. 11. 51 Tom 132. 14. 11. 1 ISP 132. 14. 11. 51 121. 42. 33. 1 Internet routing uses numeric IP address Typical route uses several hops
IP Protocol Functions (Summary) Routing n n IP host knows location of router (gateway) IP gateway must know route to other networks Fragmentation and reassembly n If max-packet-size less than the user-data-size Error reporting n ICMP packet to source if packet is dropped

UDP User Datagram Protocol IP provides routing n IP address gets datagram to a specific machine UDP separates traffic by port n n Destination port number gets UDP datagram to particular application process, e. g. , 128. 3. 23. 3, 53 Source port number provides return address Minimal guarantees n n n No acknowledgment No flow control No message continuation
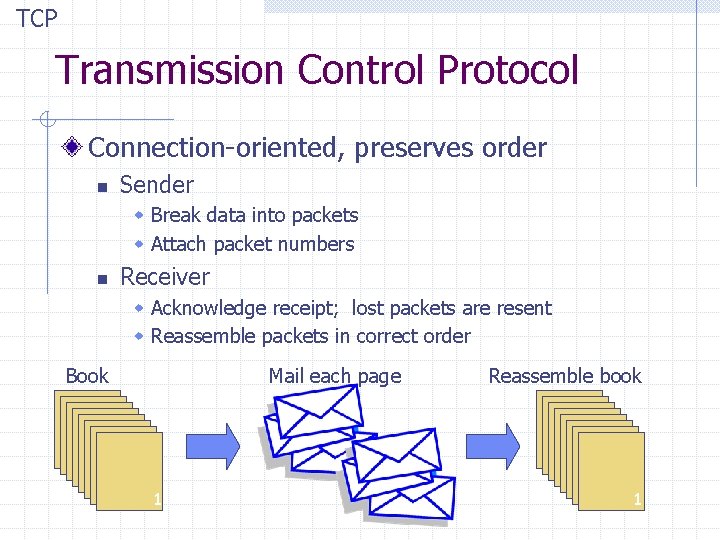
TCP Transmission Control Protocol Connection-oriented, preserves order n Sender w Break data into packets w Attach packet numbers n Receiver w Acknowledge receipt; lost packets are resent w Reassemble packets in correct order Book Mail each page Reassemble book 1 19 1 5 1

ICMP Internet Control Message Protocol Provides feedback about network operation n Error reporting Reachability testing Congestion Control Example message types n n n Destination unreachable Time-to-live exceeded Parameter problem Redirect to better gateway Echo/echo reply - reachability test Timestamp request/reply - measure transit delay
Basic Security Problems Network packets pass by untrusted hosts n Eavesdropping, packet sniffing (e. g. , “ngrep”) IP addresses are public n Smurf TCP connection requires state n SYN flooding attack TCP state can be easy to guess n TCP spoofing attack
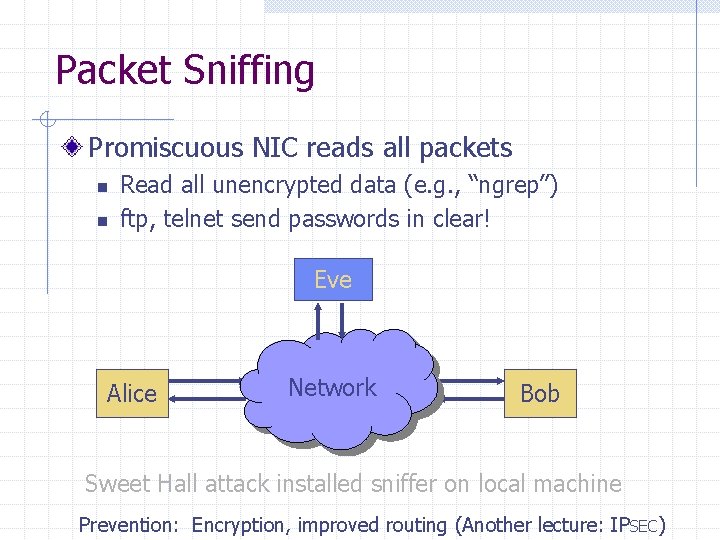
Packet Sniffing Promiscuous NIC reads all packets n n Read all unencrypted data (e. g. , “ngrep”) ftp, telnet send passwords in clear! Eve Alice Network Bob Sweet Hall attack installed sniffer on local machine Prevention: Encryption, improved routing (Another lecture: IP SEC)
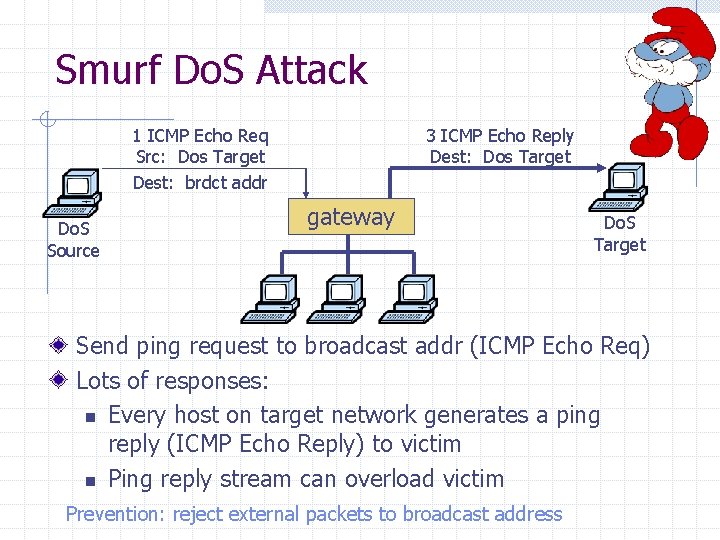
Smurf Do. S Attack 1 ICMP Echo Req Src: Dos Target Dest: brdct addr Do. S Source 3 ICMP Echo Reply Dest: Dos Target gateway Do. S Target Send ping request to broadcast addr (ICMP Echo Req) Lots of responses: n Every host on target network generates a ping reply (ICMP Echo Reply) to victim n Ping reply stream can overload victim Prevention: reject external packets to broadcast address
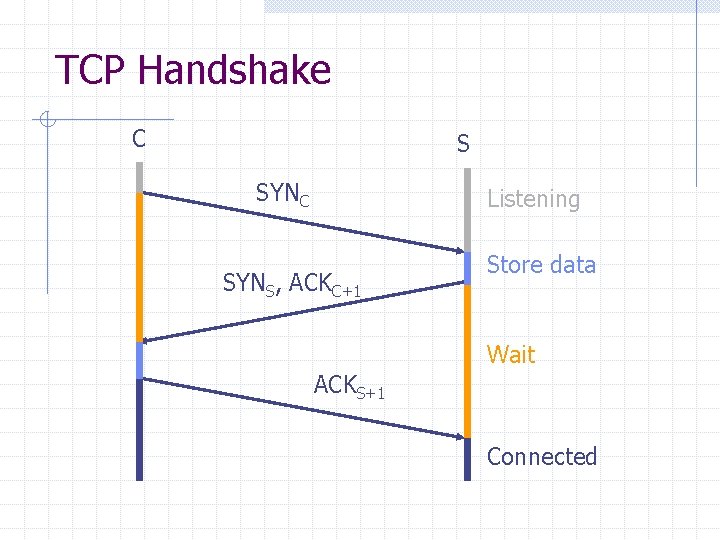
TCP Handshake C S SYNC Listening SYNS, ACKC+1 Store data Wait ACKS+1 Connected
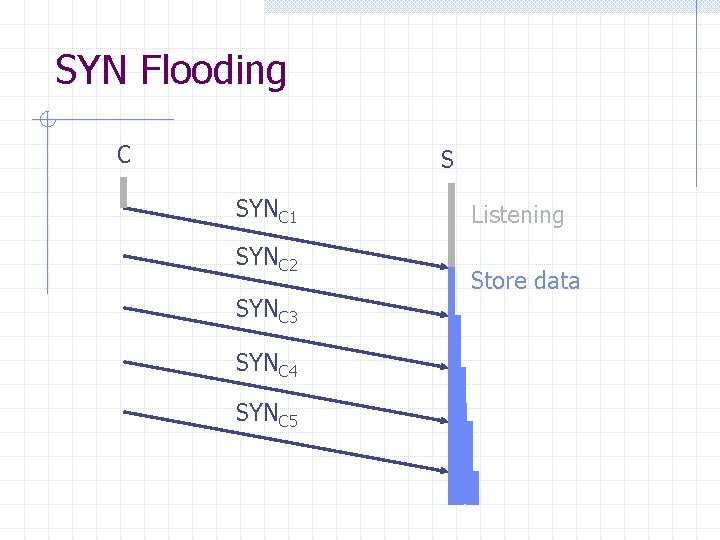
SYN Flooding C S SYNC 1 SYNC 2 SYNC 3 SYNC 4 SYNC 5 Listening Store data
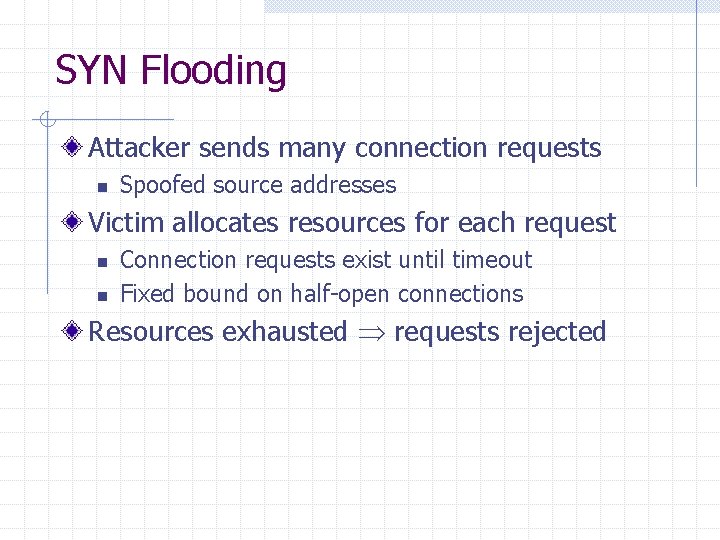
SYN Flooding Attacker sends many connection requests n Spoofed source addresses Victim allocates resources for each request n n Connection requests exist until timeout Fixed bound on half-open connections Resources exhausted requests rejected
![Protection against SYN Attacks [Bernstein, Schenk] Client sends SYN Server responds to Client with Protection against SYN Attacks [Bernstein, Schenk] Client sends SYN Server responds to Client with](http://slidetodoc.com/presentation_image_h2/0413549704b69b986a26365fe9c6cf55/image-18.jpg)
Protection against SYN Attacks [Bernstein, Schenk] Client sends SYN Server responds to Client with SYN-ACK cookie n n sqn = f(src addr, src port, dest addr, dest port, rand) Normal TCP response but server does not save state Honest client responds with ACK(sqn) Server checks response n If matches SYN-ACK, establishes connection w “rand” is top 5 bits of 32 -bit time counter w Server checks client response against recent values See http: //cr. yp. to/syncookies. html
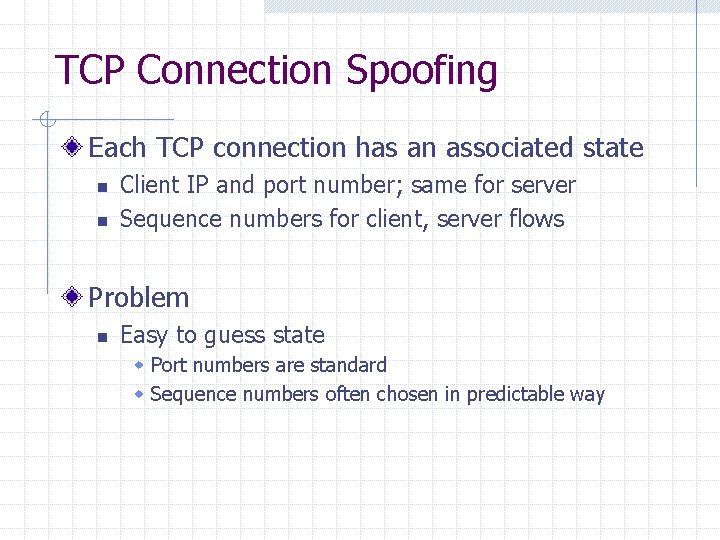
TCP Connection Spoofing Each TCP connection has an associated state n n Client IP and port number; same for server Sequence numbers for client, server flows Problem n Easy to guess state w Port numbers are standard w Sequence numbers often chosen in predictable way
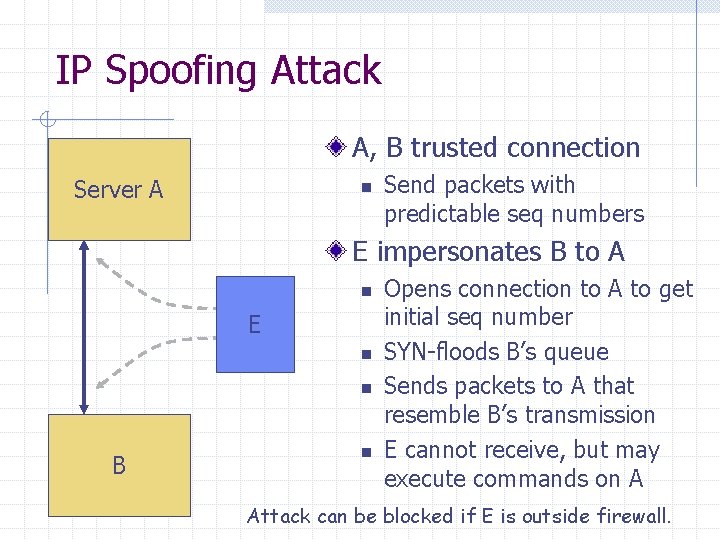
IP Spoofing Attack A, B trusted connection Server A n Send packets with predictable seq numbers E impersonates B to A n E n n B n Opens connection to A to get initial seq number SYN-floods B’s queue Sends packets to A that resemble B’s transmission E cannot receive, but may execute commands on A Attack can be blocked if E is outside firewall.
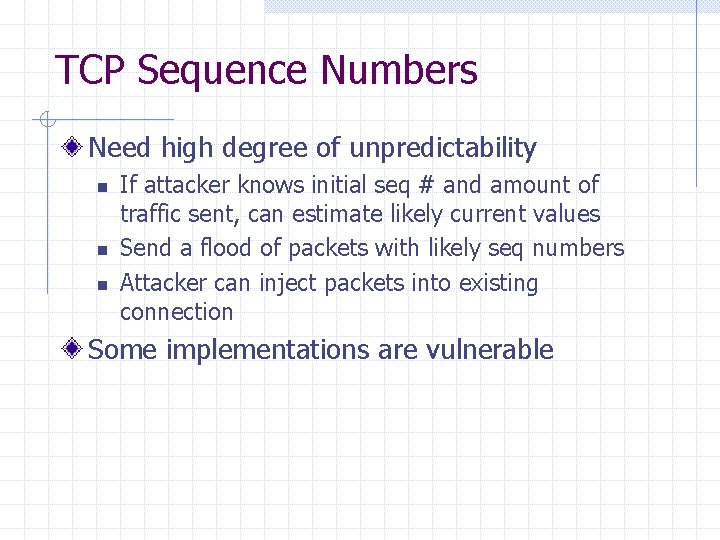
TCP Sequence Numbers Need high degree of unpredictability n n n If attacker knows initial seq # and amount of traffic sent, can estimate likely current values Send a flood of packets with likely seq numbers Attacker can inject packets into existing connection Some implementations are vulnerable
![Recent Do. S vulnerability [Watson’ 04] Suppose attacker can guess seq. number for an Recent Do. S vulnerability [Watson’ 04] Suppose attacker can guess seq. number for an](http://slidetodoc.com/presentation_image_h2/0413549704b69b986a26365fe9c6cf55/image-22.jpg)
Recent Do. S vulnerability [Watson’ 04] Suppose attacker can guess seq. number for an existing connection: n n n Attacker can send Reset packet to close connection. Results in Do. S. Naively, success prob. is 1/232 (32 -bit seq. #’s). Most systems allow for a large window of acceptable seq. #’s w Much higher success probability. Attack is most effective against long lived connections, e. g. BGP.
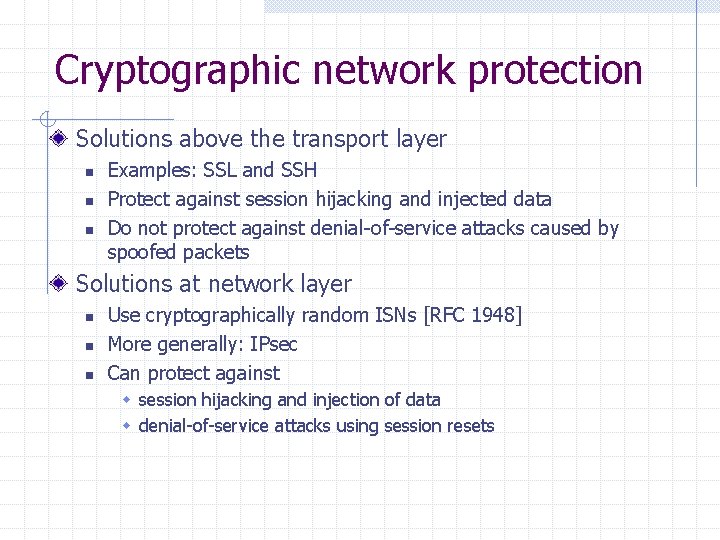
Cryptographic network protection Solutions above the transport layer n n n Examples: SSL and SSH Protect against session hijacking and injected data Do not protect against denial-of-service attacks caused by spoofed packets Solutions at network layer n n n Use cryptographically random ISNs [RFC 1948] More generally: IPsec Can protect against w session hijacking and injection of data w denial-of-service attacks using session resets
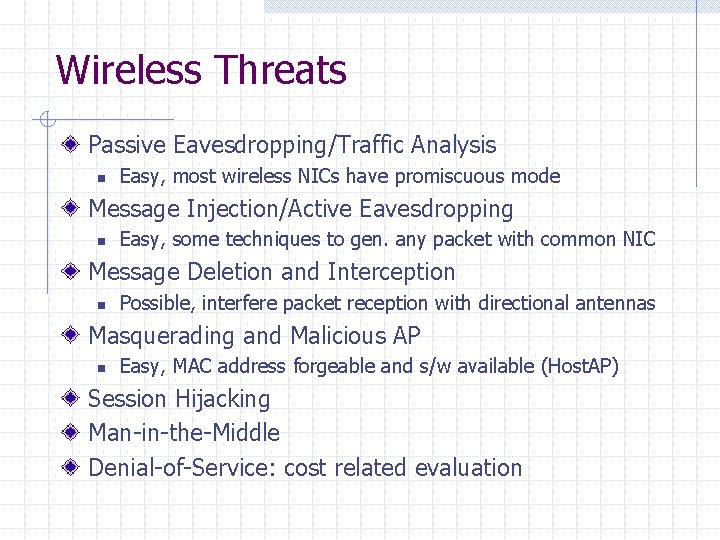
Wireless Threats Passive Eavesdropping/Traffic Analysis n Easy, most wireless NICs have promiscuous mode Message Injection/Active Eavesdropping n Easy, some techniques to gen. any packet with common NIC Message Deletion and Interception n Possible, interfere packet reception with directional antennas Masquerading and Malicious AP n Easy, MAC address forgeable and s/w available (Host. AP) Session Hijacking Man-in-the-Middle Denial-of-Service: cost related evaluation
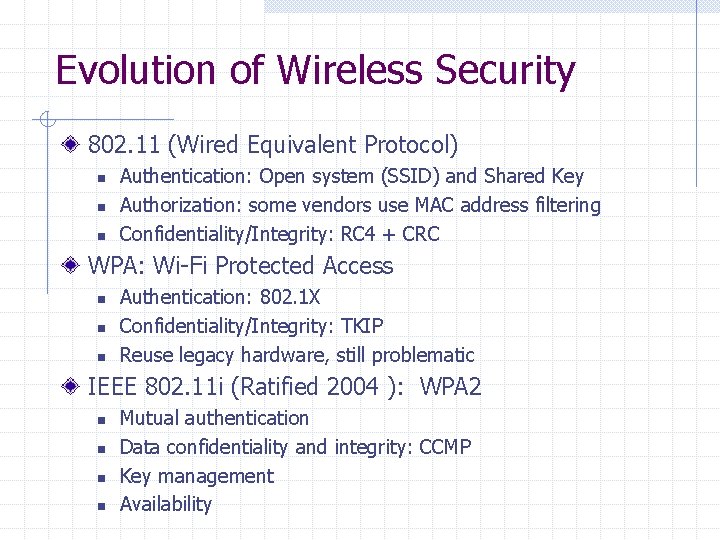
Evolution of Wireless Security 802. 11 (Wired Equivalent Protocol) n n n Authentication: Open system (SSID) and Shared Key Authorization: some vendors use MAC address filtering Confidentiality/Integrity: RC 4 + CRC WPA: Wi-Fi Protected Access n n n Authentication: 802. 1 X Confidentiality/Integrity: TKIP Reuse legacy hardware, still problematic IEEE 802. 11 i (Ratified 2004 ): WPA 2 n n Mutual authentication Data confidentiality and integrity: CCMP Key management Availability
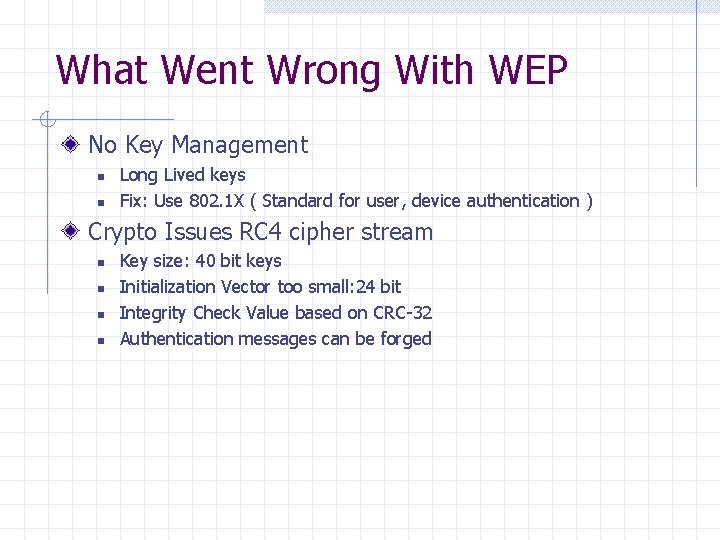
What Went Wrong With WEP No Key Management n n Long Lived keys Fix: Use 802. 1 X ( Standard for user, device authentication ) Crypto Issues RC 4 cipher stream n n Key size: 40 bit keys Initialization Vector too small: 24 bit Integrity Check Value based on CRC-32 Authentication messages can be forged
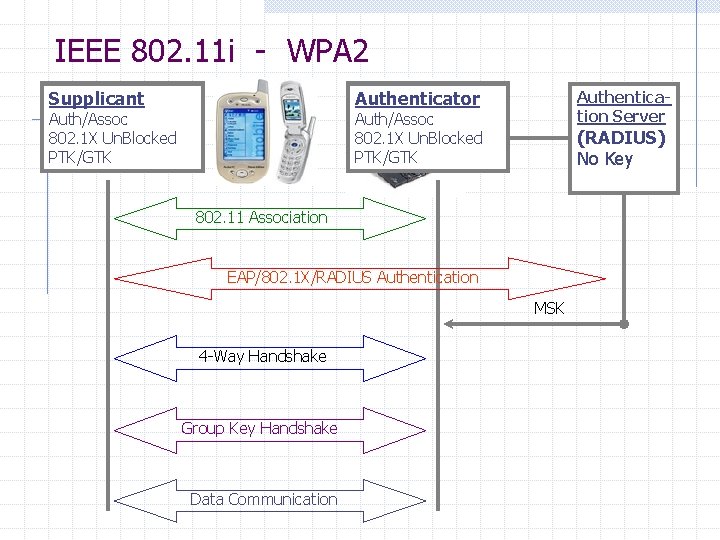
IEEE 802. 11 i - WPA 2 Supplicant Un. Auth/Un. Assoc Auth/Assoc 802. 1 X Blocked Un. Blocked PMK No MSKKey New GTK PTK/GTK Authenticator Un. Auth/Un. Assoc Auth/Assoc Blocked 802. 1 X Un. Blocked PMK No Key New GTK PTK/GTK Authentication Server (RADIUS) MSK No No Key 802. 11 Association EAP/802. 1 X/RADIUS Authentication MSK 4 -Way Handshake Group Key Handshake Data Communication
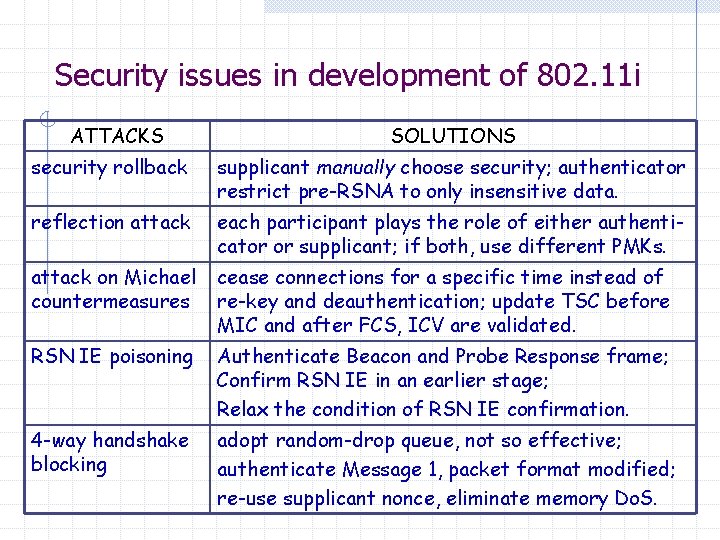
Security issues in development of 802. 11 i ATTACKS SOLUTIONS security rollback supplicant manually choose security; authenticator restrict pre-RSNA to only insensitive data. reflection attack each participant plays the role of either authenticator or supplicant; if both, use different PMKs. attack on Michael countermeasures cease connections for a specific time instead of re-key and deauthentication; update TSC before MIC and after FCS, ICV are validated. RSN IE poisoning Authenticate Beacon and Probe Response frame; Confirm RSN IE in an earlier stage; Relax the condition of RSN IE confirmation. 4 -way handshake blocking adopt random-drop queue, not so effective; authenticate Message 1, packet format modified; re-use supplicant nonce, eliminate memory Do. S.

TCP Congestion Control Source Destination If packets are lost, assume congestion Reduce transmission rate by half, repeat n If loss stops, increase rate very slowly Design assumes routers blindly obey this policy n
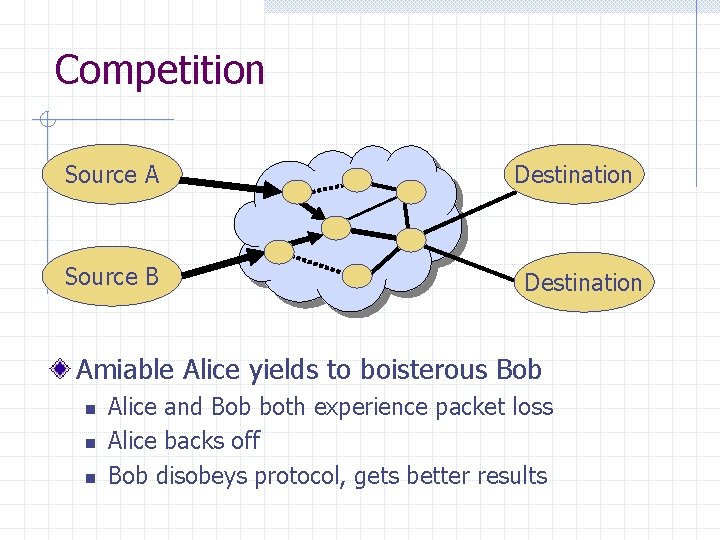
Competition Source A Source B Destination Amiable Alice yields to boisterous Bob n n n Alice and Bob both experience packet loss Alice backs off Bob disobeys protocol, gets better results
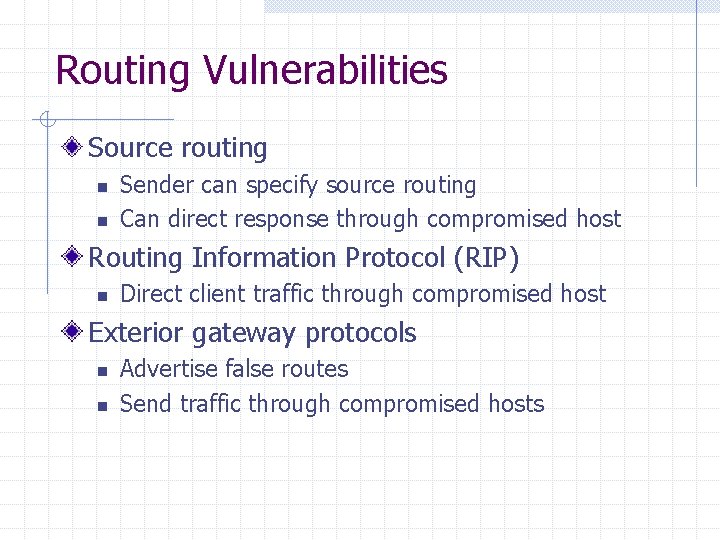
Routing Vulnerabilities Source routing n n Sender can specify source routing Can direct response through compromised host Routing Information Protocol (RIP) n Direct client traffic through compromised host Exterior gateway protocols n n Advertise false routes Send traffic through compromised hosts
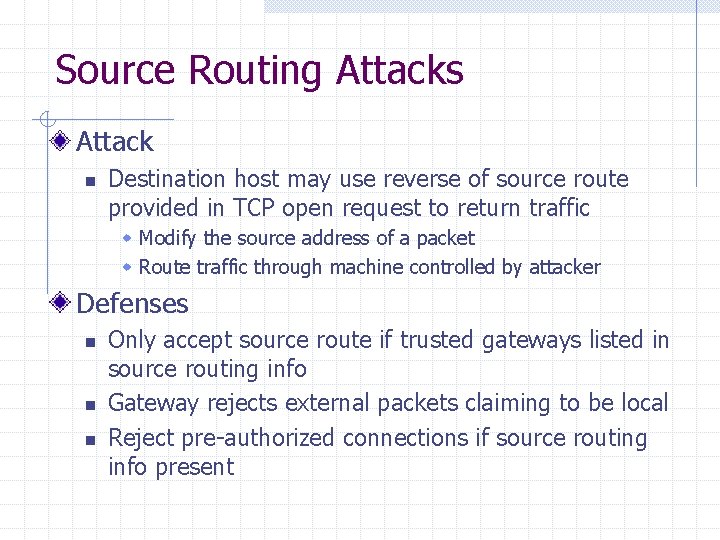
Source Routing Attacks Attack n Destination host may use reverse of source route provided in TCP open request to return traffic w Modify the source address of a packet w Route traffic through machine controlled by attacker Defenses n n n Only accept source route if trusted gateways listed in source routing info Gateway rejects external packets claiming to be local Reject pre-authorized connections if source routing info present
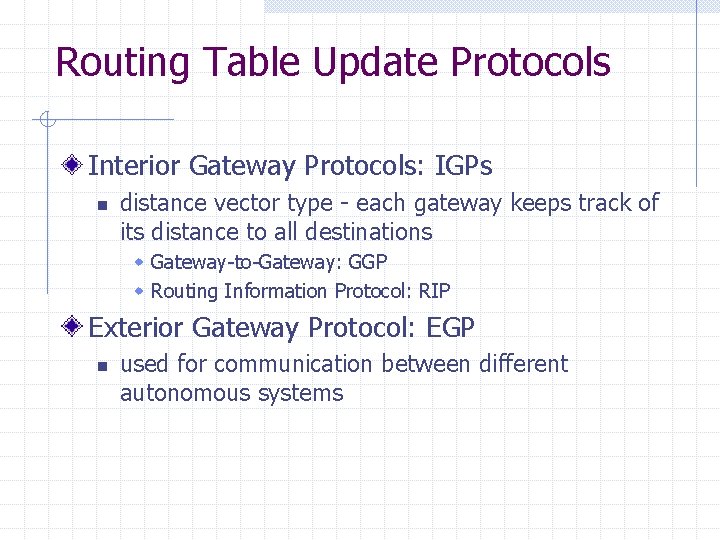
Routing Table Update Protocols Interior Gateway Protocols: IGPs n distance vector type - each gateway keeps track of its distance to all destinations w Gateway-to-Gateway: GGP w Routing Information Protocol: RIP Exterior Gateway Protocol: EGP n used for communication between different autonomous systems
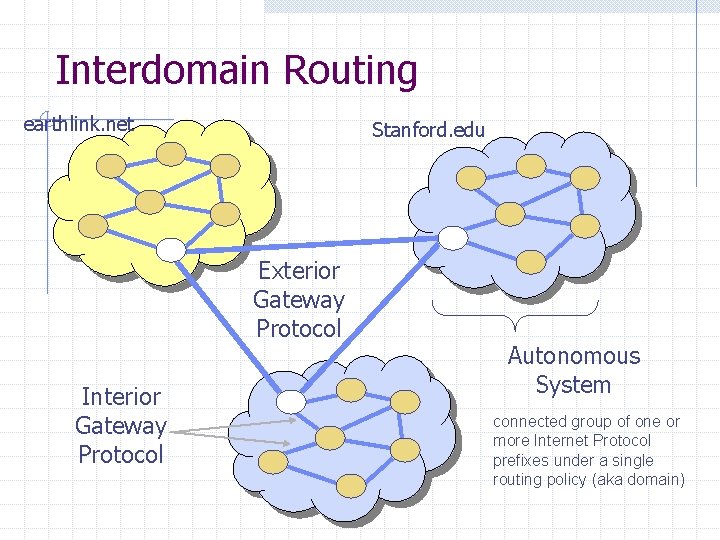
Interdomain Routing earthlink. net Stanford. edu Exterior Gateway Protocol Interior Gateway Protocol Autonomous System connected group of one or more Internet Protocol prefixes under a single routing policy (aka domain)
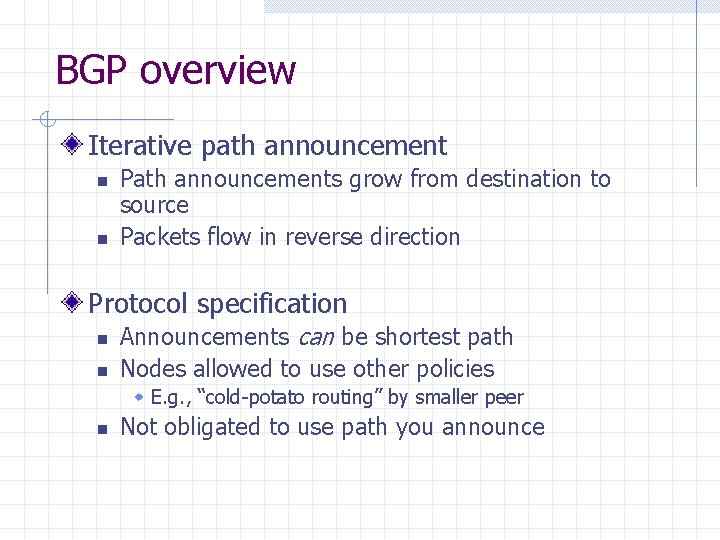
BGP overview Iterative path announcement n n Path announcements grow from destination to source Packets flow in reverse direction Protocol specification n n Announcements can be shortest path Nodes allowed to use other policies w E. g. , “cold-potato routing” by smaller peer n Not obligated to use path you announce
![BGP example 1 [D. Wetherall] 27 265 8 2 7265 7 7 7 265 BGP example 1 [D. Wetherall] 27 265 8 2 7265 7 7 7 265](http://slidetodoc.com/presentation_image_h2/0413549704b69b986a26365fe9c6cf55/image-36.jpg)
BGP example 1 [D. Wetherall] 27 265 8 2 7265 7 7 7 265 327 3 3265 27 6 4 627 5 5 5 Transit: 2 provides transit for 7 Algorithm seems to work OK in practice n BGP is does not respond well to frequent node outages
Issues Security problems n n Potential for disruptive attacks BGP packets are un-authenticated Incentive for dishonesty n ISP pays for some routes, others free
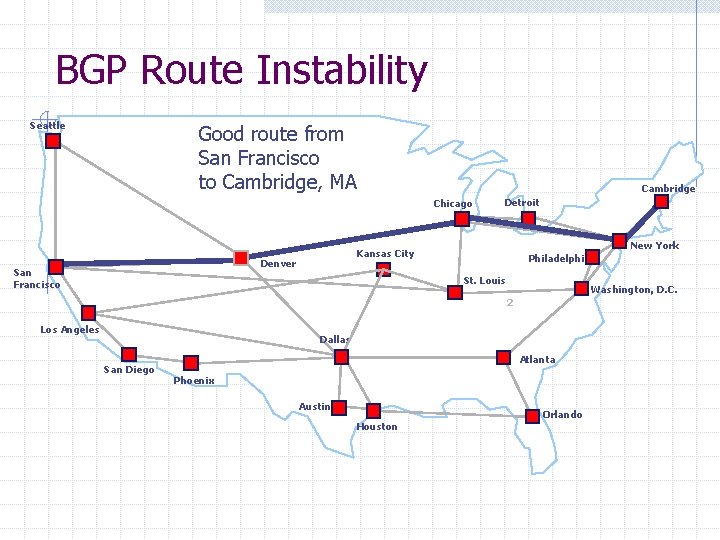
BGP Route Instability Seattle Good route from San Francisco to Cambridge, MA Cambridge Chicago New York Kansas City Denver San Francisco Detroit Philadelphia St. Louis Washington, D. C. 2 Los Angeles Dallas San Diego Atlanta Phoenix Austin Houston Orlando
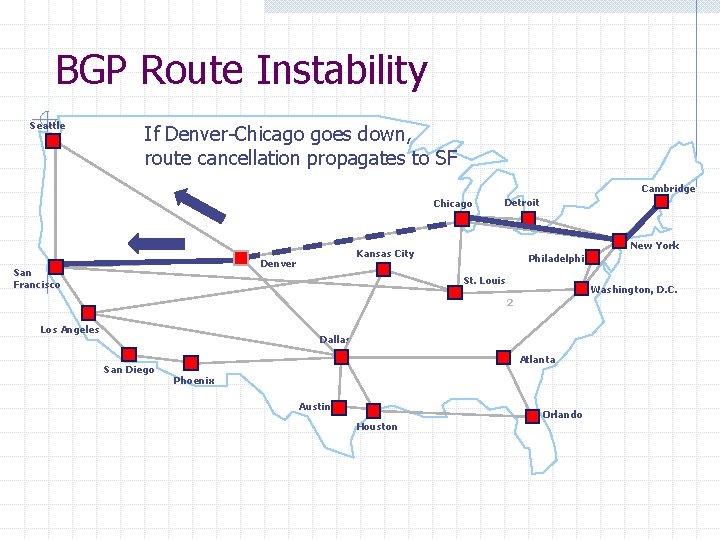
BGP Route Instability Seattle If Denver-Chicago goes down, route cancellation propagates to SF Cambridge Chicago New York Kansas City Denver San Francisco Detroit Philadelphia St. Louis Washington, D. C. 2 Los Angeles Dallas San Diego Atlanta Phoenix Austin Houston Orlando
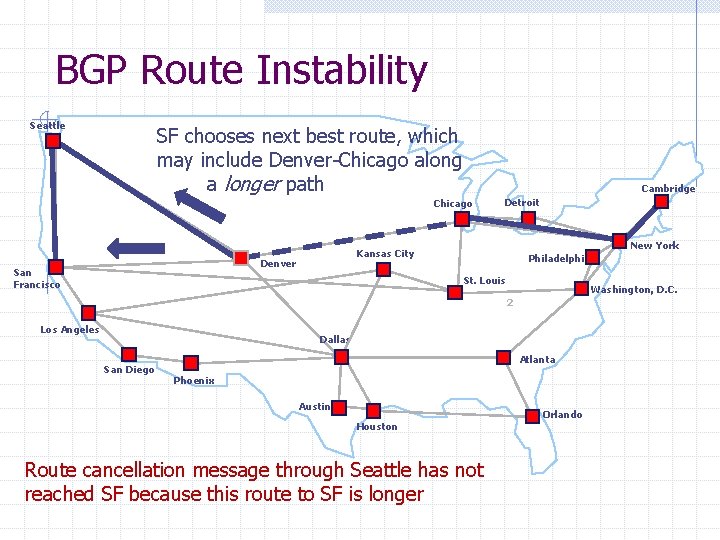
BGP Route Instability Seattle SF chooses next best route, which may include Denver-Chicago along a longer path Cambridge Chicago New York Kansas City Denver San Francisco Detroit Philadelphia St. Louis Washington, D. C. 2 Los Angeles Dallas San Diego Atlanta Phoenix Austin Houston Route cancellation message through Seattle has not reached SF because this route to SF is longer Orlando
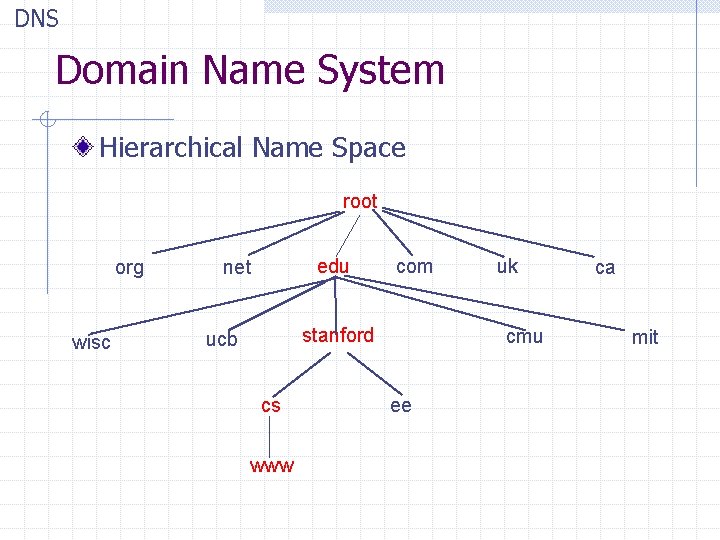
DNS Domain Name System Hierarchical Name Space root org wisc edu net com stanford ucb cs www uk cmu ee ca mit
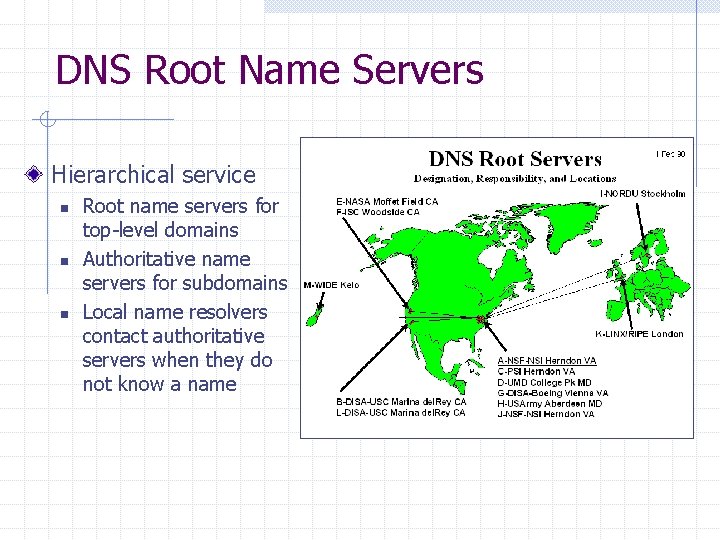
DNS Root Name Servers Hierarchical service n n n Root name servers for top-level domains Authoritative name servers for subdomains Local name resolvers contact authoritative servers when they do not know a name
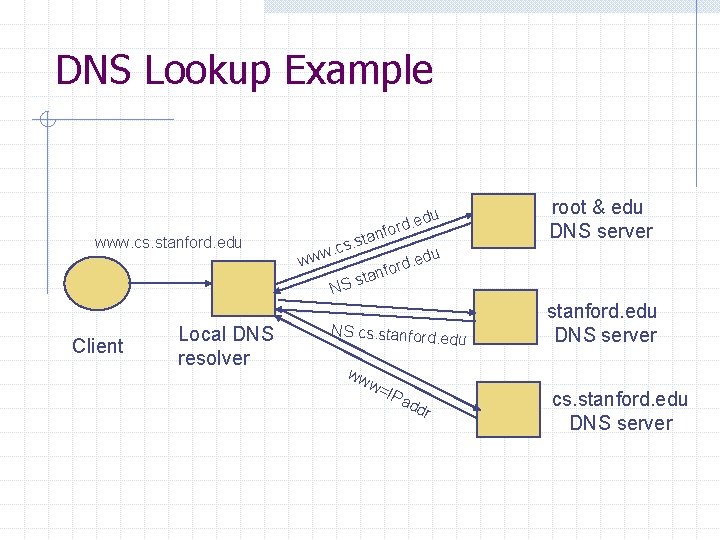
DNS Lookup Example nfo . sta s c. ww www. cs. stanford. edu w Client Local DNS resolver root & edu DNS server du rd. e du d. e nfor a st NS NS cs. stanford. e du ww w= IPa dd r stanford. edu DNS server cs. stanford. edu DNS server
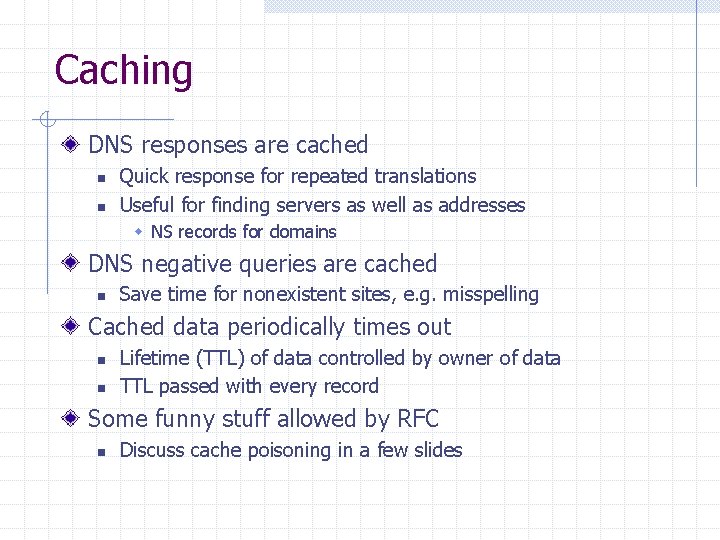
Caching DNS responses are cached n n Quick response for repeated translations Useful for finding servers as well as addresses w NS records for domains DNS negative queries are cached n Save time for nonexistent sites, e. g. misspelling Cached data periodically times out n n Lifetime (TTL) of data controlled by owner of data TTL passed with every record Some funny stuff allowed by RFC n Discuss cache poisoning in a few slides
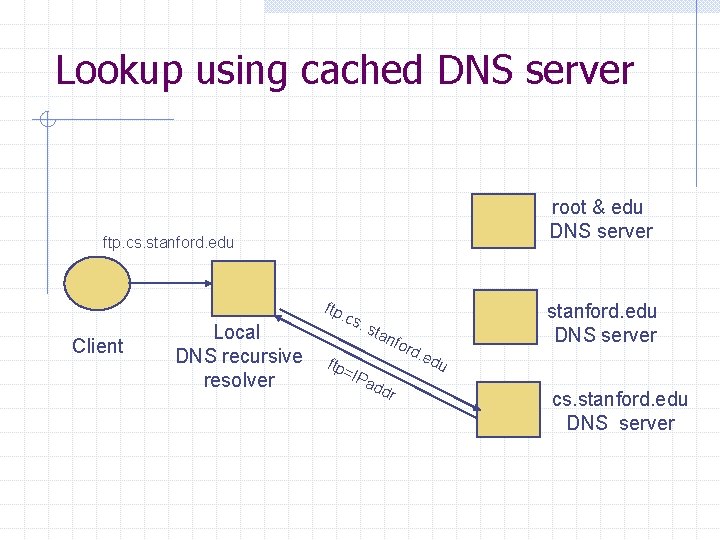
Lookup using cached DNS server root & edu DNS server ftp. cs. stanford. edu Client Local DNS recursive resolver ftp. cs. ftp = sta nfo rd. ed stanford. edu DNS server u IPa dd r cs. stanford. edu DNS server
DNS Implementation Vulnerabilities DNS implementations have had same kinds of vulnerabilities as other software n Reverse query buffer overrun in BIND Releases 4. 9 (4. 9. 7 prior) and Releases 8 (8. 1. 2 prior) w gain root access w abort DNS service n MS DNS for NT 4. 0 (service pack 3 and prior) w crashes on chargen stream w telnet ntbox 19 | telnet ntbox 53 Moral n n Better software quality is important Defense in depth!
Inherent DNS Vulnerabilities Users/hosts typically trust the host-address mapping provided by DNS Obvious problems n n Interception of requests or compromise of DNS servers can result in incorrect or malicious responses Solution – authenticated requests/responses Some funny stuff allowed by RFC n n Name server may delegate name to another NS (this is OK) If name is delegated, may also supply IP addr (this is trouble)
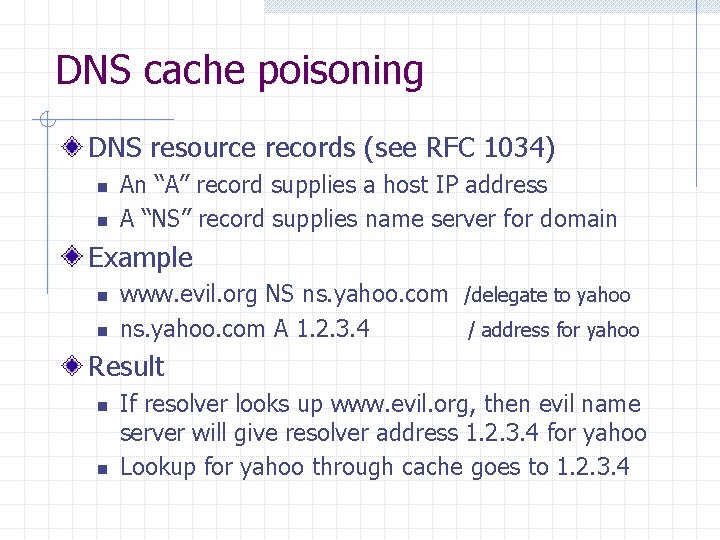
DNS cache poisoning DNS resource records (see RFC 1034) n n An “A” record supplies a host IP address A “NS” record supplies name server for domain Example n n www. evil. org NS ns. yahoo. com /delegate to yahoo ns. yahoo. com A 1. 2. 3. 4 / address for yahoo Result n n If resolver looks up www. evil. org, then evil name server will give resolver address 1. 2. 3. 4 for yahoo Lookup for yahoo through cache goes to 1. 2. 3. 4
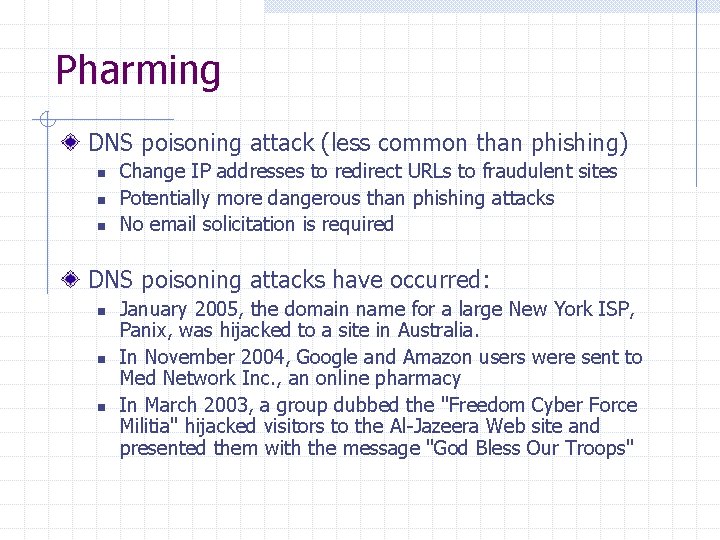
Pharming DNS poisoning attack (less common than phishing) n n n Change IP addresses to redirect URLs to fraudulent sites Potentially more dangerous than phishing attacks No email solicitation is required DNS poisoning attacks have occurred: n n n January 2005, the domain name for a large New York ISP, Panix, was hijacked to a site in Australia. In November 2004, Google and Amazon users were sent to Med Network Inc. , an online pharmacy In March 2003, a group dubbed the "Freedom Cyber Force Militia" hijacked visitors to the Al-Jazeera Web site and presented them with the message "God Bless Our Troops"
![[DWF’ 96, R’ 01] DNS Rebinding Attack <iframe src='data:image/svg+xml,%3Csvg%20xmlns=%22http://www.w3.org/2000/svg%22%20viewBox=%220%200%20760%20570%22%3E%3C/svg%3E' data-src="http: //www. evil. com"> DNS-SEC cannot [DWF’ 96, R’ 01] DNS Rebinding Attack <iframe src='data:image/svg+xml,%3Csvg%20xmlns=%22http://www.w3.org/2000/svg%22%20viewBox=%220%200%20760%20570%22%3E%3C/svg%3E' data-src="http: //www. evil. com"> DNS-SEC cannot](http://slidetodoc.com/presentation_image_h2/0413549704b69b986a26365fe9c6cf55/image-50.jpg)
[DWF’ 96, R’ 01] DNS Rebinding Attack <iframe src="http: //www. evil. com"> DNS-SEC cannot stop this attack www. evil. com? 171. 64. 7. 115 TTL = 0 Firewall corporate web server 192. 168. 0. 100 ns. evil. com DNS server 192. 168. 0. 100 www. evil. com web server 171. 64. 7. 115 Read permitted: it’s the “same origin”
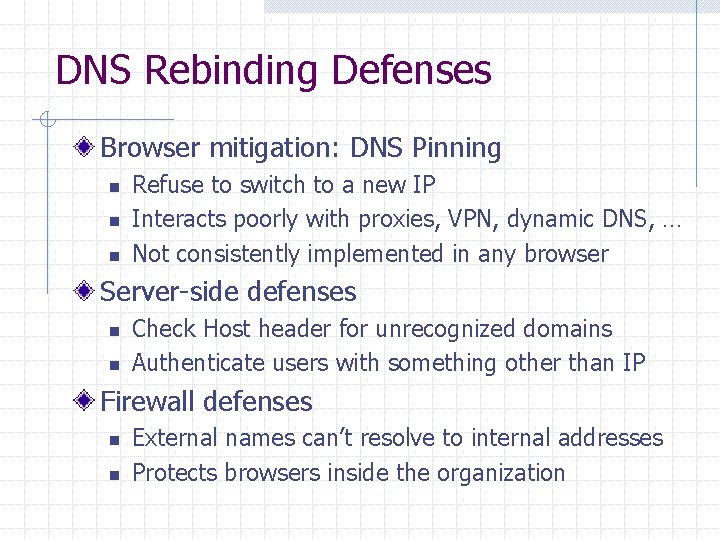
DNS Rebinding Defenses Browser mitigation: DNS Pinning n n n Refuse to switch to a new IP Interacts poorly with proxies, VPN, dynamic DNS, … Not consistently implemented in any browser Server-side defenses n n Check Host header for unrecognized domains Authenticate users with something other than IP Firewall defenses n n External names can’t resolve to internal addresses Protects browsers inside the organization
Summary (I) Eavesdropping n Encryption, improved routing Smurf n Drop external packets to brdcst address SYN Flooding n SYN Cookies IP spoofing n Use less predictable sequence numbers
Summary (II) Source routing attacks n Additional info in packets, tighter control over routing Interdomain routing n n Authenticate routing announcements Many other issues DNS attacks n n n Cache poisoning Pharming Rebinding
- Slides: 53