Sphere Shield Secure Skype for Business V 7

Sphere. Shield Secure Skype for Business V 7. 0

Solution Overview Sphere. Shield offers advanced compliance and security solutions for Unified Communication services including Skype for Business.

Targeted Services Skype for Business on premises Skype for Business online (conditional access only) Microsoft Teams Office 365 -Exchange, One. Drive, Share. Point Cisco Webex Teams (Spark) Slack = Released Zoom Microsoft Stream =Released Q 3, 2020 Ring Central
Sphere. Shield security features Secure Authentication Simple and secure TFA based on device as second factor. Protect Sf. B & Exchange EWS Device Access Control Manage which devices can connect using device enrolment process Network Account Lockout Protection Prevent Account lockout issues in DDo. S attacks through multiple UC channels
Sphere. Shield security features MDM Conditional Access Verify only devices that are managed by MDM and compliant with security policy can connect Credential Protection Prevent network password theft by using app specific credentials instead of domain credentials Ethical Wall Functional control Granular policy for all activities (IM, File sharing, presence etc. ) controlling external (Federation) and internal traffic
Sphere. Shield security features Application firewall Sanitize and validating all anonymous traffic requests in the DMZ before entering the network DLP Content Inspection Inspect content passing through Skype for Business by DLP (Data Loss Prevention) policy rules Risk Engine Define Geo location (Geo fencing) rules. Display live map of connections. Profile user behaviour and create security alerts events
Sphere. Shield security features Disclaimer Display disclaimers for internal and external users based on domains e. Discovery Advanced search export and modify dashboard for Skype for Business Archiving DB

Features in depth
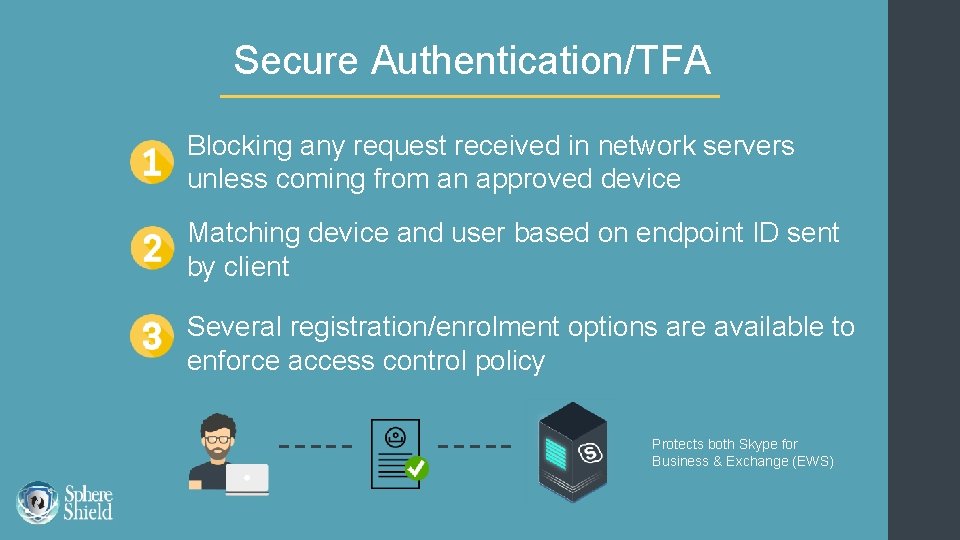
Secure Authentication/TFA Blocking any request received in network servers unless coming from an approved device Matching device and user based on endpoint ID sent by client Several registration/enrolment options are available to enforce access control policy Protects both Skype for Business & Exchange (EWS)
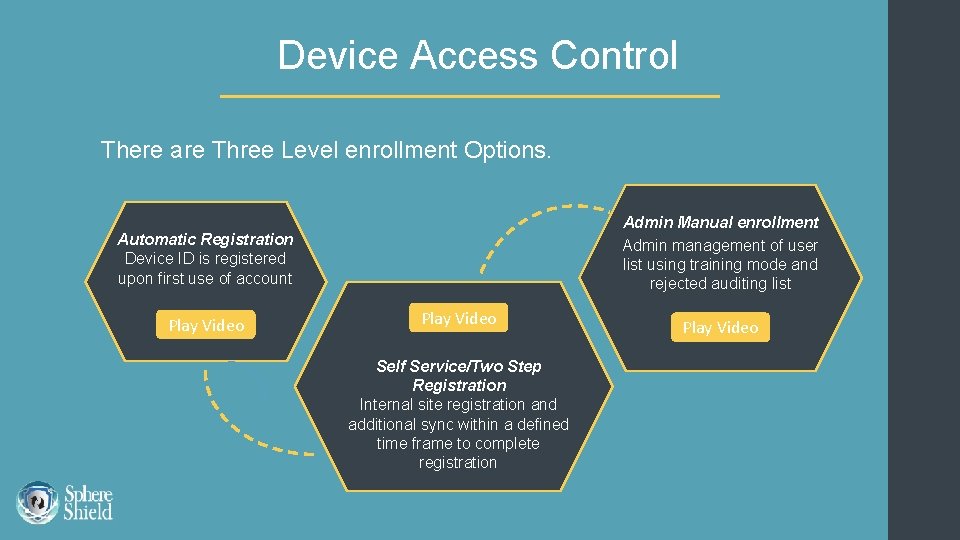
Device Access Control There are Three Level enrollment Options. Admin Manual enrollment Admin management of user list using training mode and rejected auditing list Automatic Registration Device ID is registered upon first use of account Play Video Self Service/Two Step Registration Internal site registration and additional sync within a defined time frame to complete registration Play Video
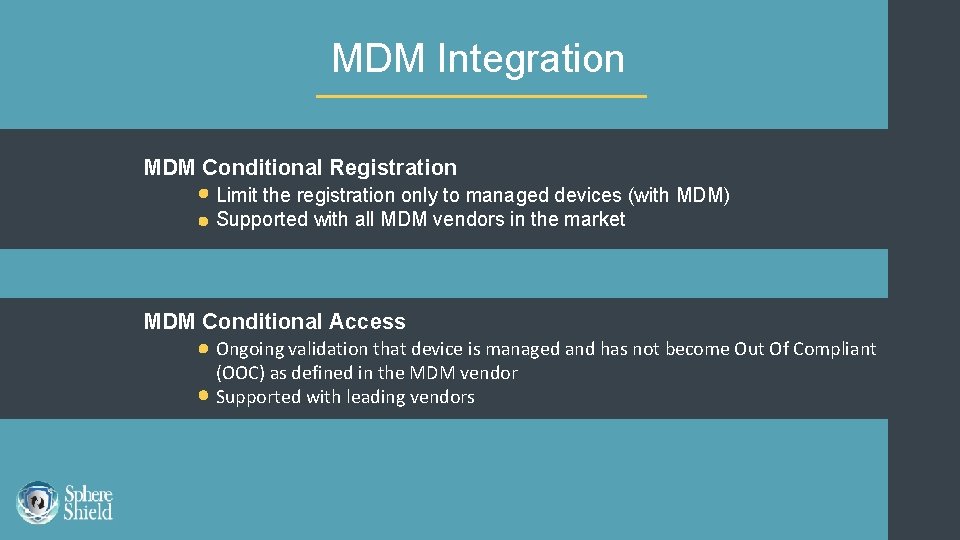
MDM Integration MDM Conditional Registration Limit the registration only to managed devices (with MDM) Supported with all MDM vendors in the market MDM Conditional Access Ongoing validation that device is managed and has not become Out Of Compliant (OOC) as defined in the MDM vendor Supported with leading vendors

MDM Conditional Registration Sphere. Shield can limit the registration of Sf. B to managed devices only. Compatible with any MDM solution supporting one of the following capabilities: WIFI access control Application management (MAM) VPN triggering / control Compatible with all MDM vendors in the market
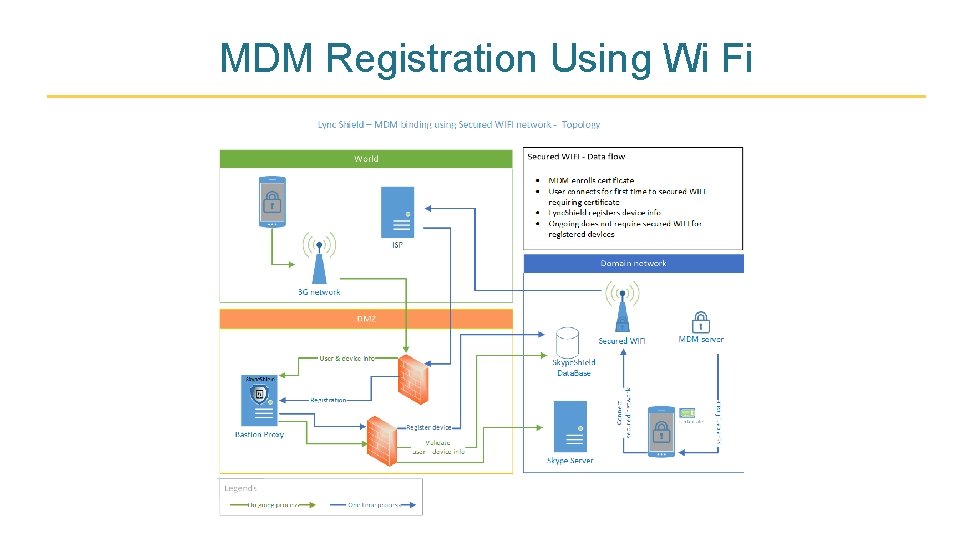
MDM Registration Using Wi Fi
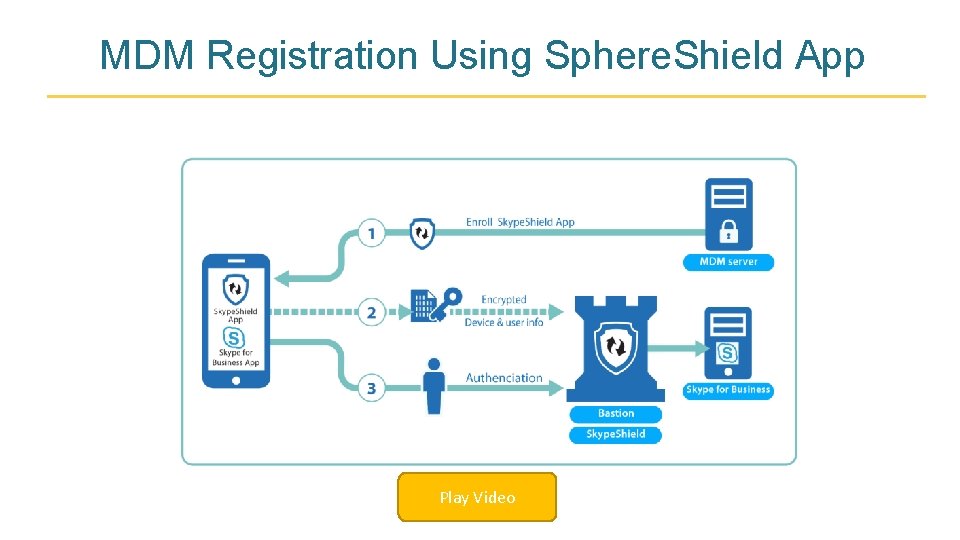
MDM Registration Using Sphere. Shield App Play Video
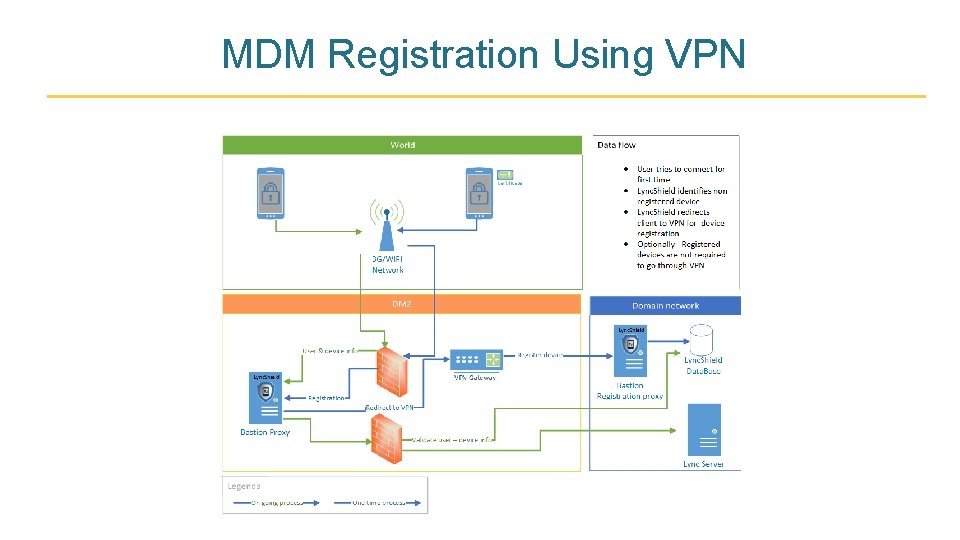
MDM Registration Using VPN
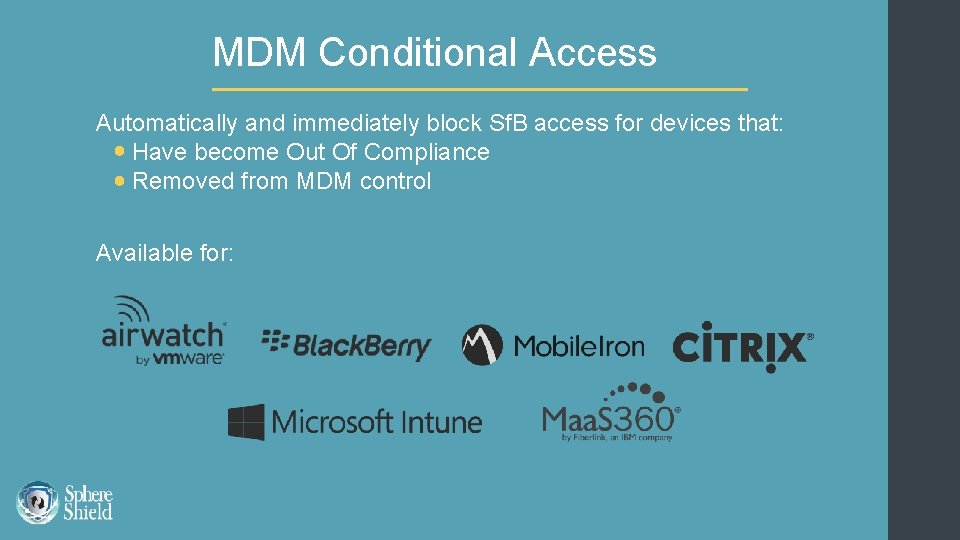
MDM Conditional Access Automatically and immediately block Sf. B access for devices that: Have become Out Of Compliance Removed from MDM control Available for:
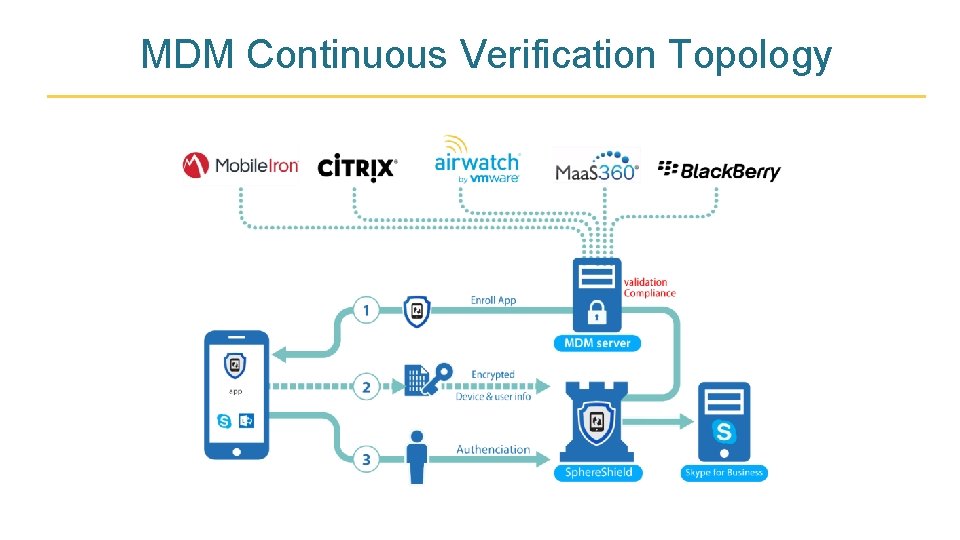
MDM Continuous Verification Topology
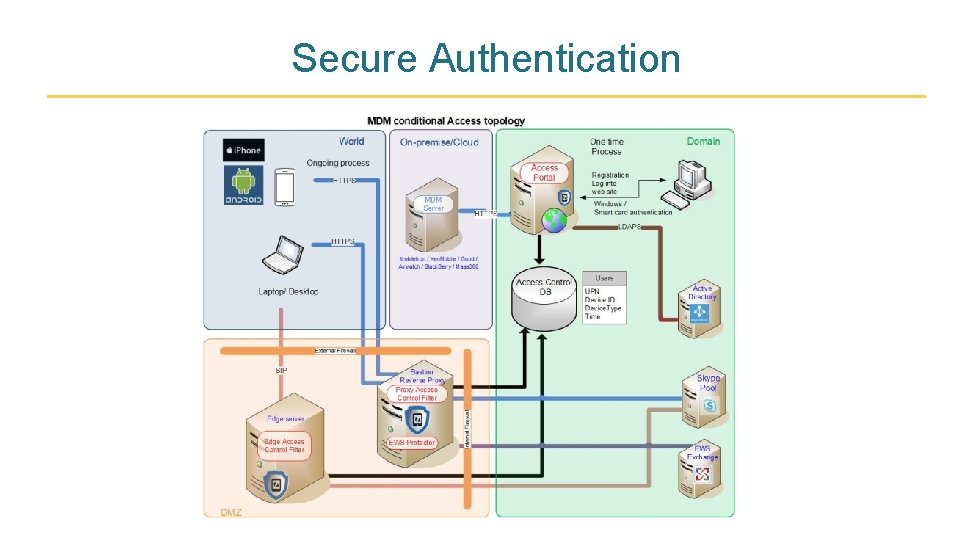
Secure Authentication
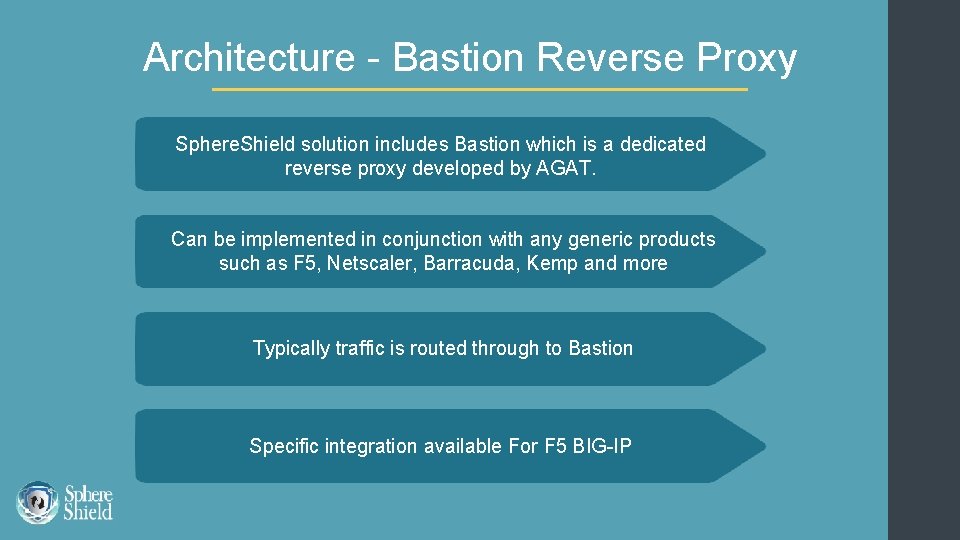
Architecture - Bastion Reverse Proxy Sphere. Shield solution includes Bastion which is a dedicated reverse proxy developed by AGAT. Can be implemented in conjunction with any generic products such as F 5, Netscaler, Barracuda, Kemp and more Typically traffic is routed through to Bastion Specific integration available For F 5 BIG-IP

Reverse Proxy Topology
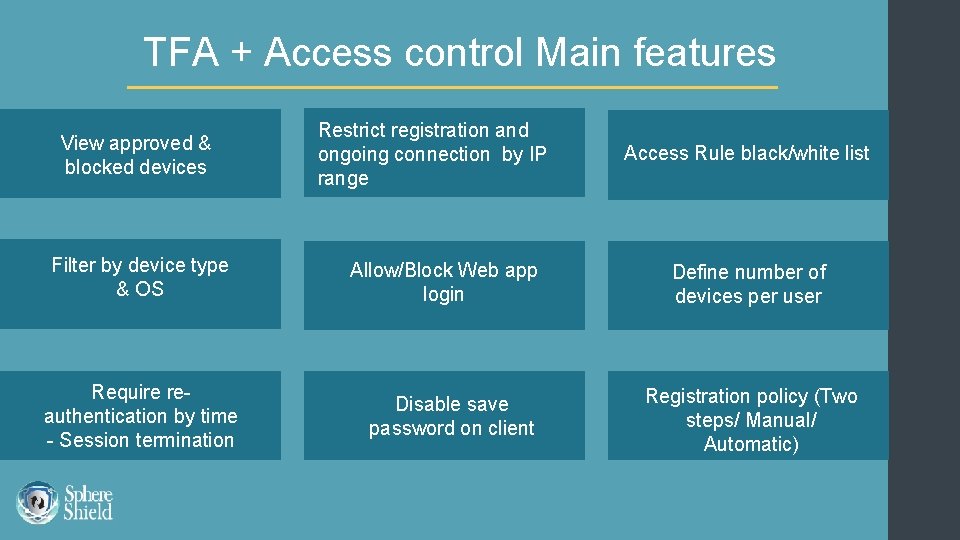
TFA + Access control Main features View approved & blocked devices Filter by device type & OS Require reauthentication by time - Session termination Restrict registration and ongoing connection by IP range Allow/Block Web app login Disable save password on client Access Rule black/white list Define number of devices per user Registration policy (Two steps/ Manual/ Automatic)
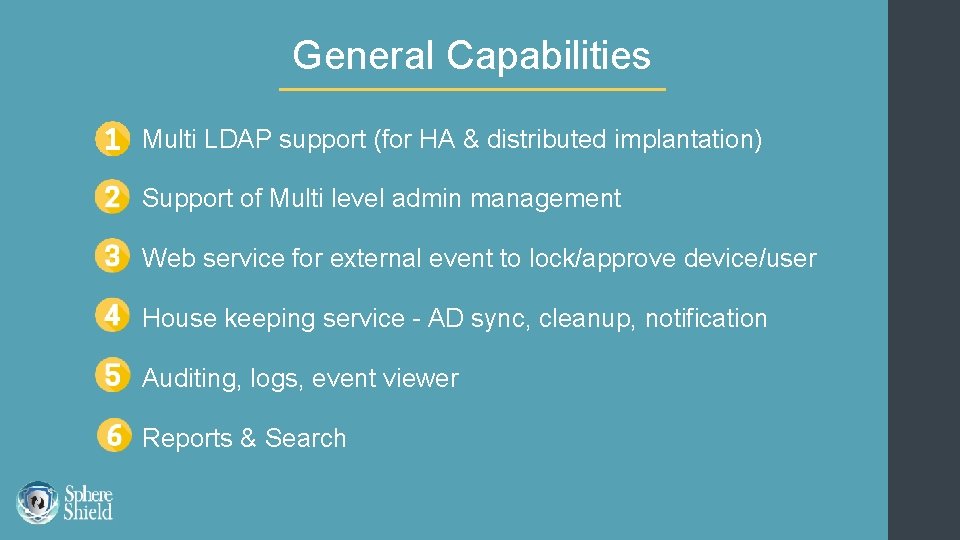
General Capabilities Multi LDAP support (for HA & distributed implantation) Support of Multi level admin management Web service for external event to lock/approve device/user House keeping service - AD sync, cleanup, notification Auditing, logs, event viewer Reports & Search
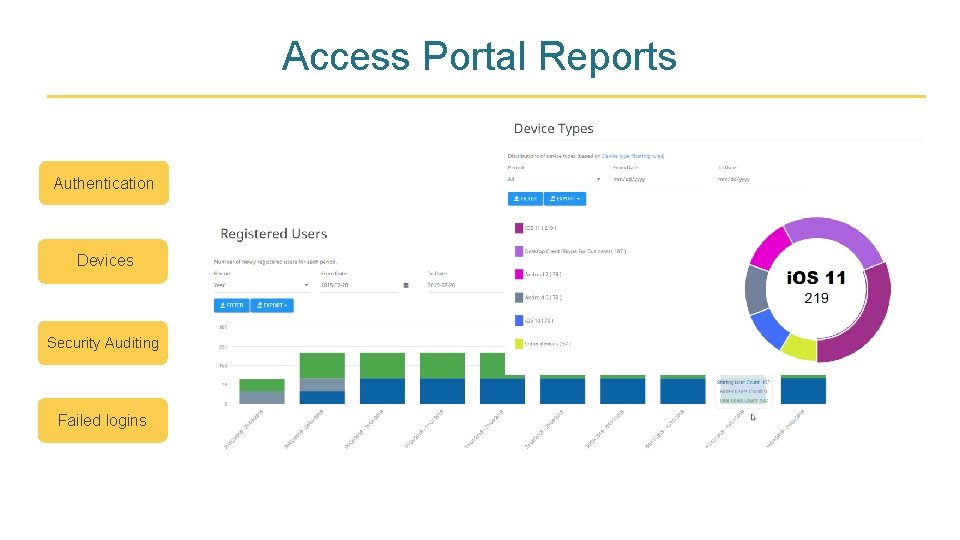
Access Portal Reports Authentication Devices Security Auditing Failed logins
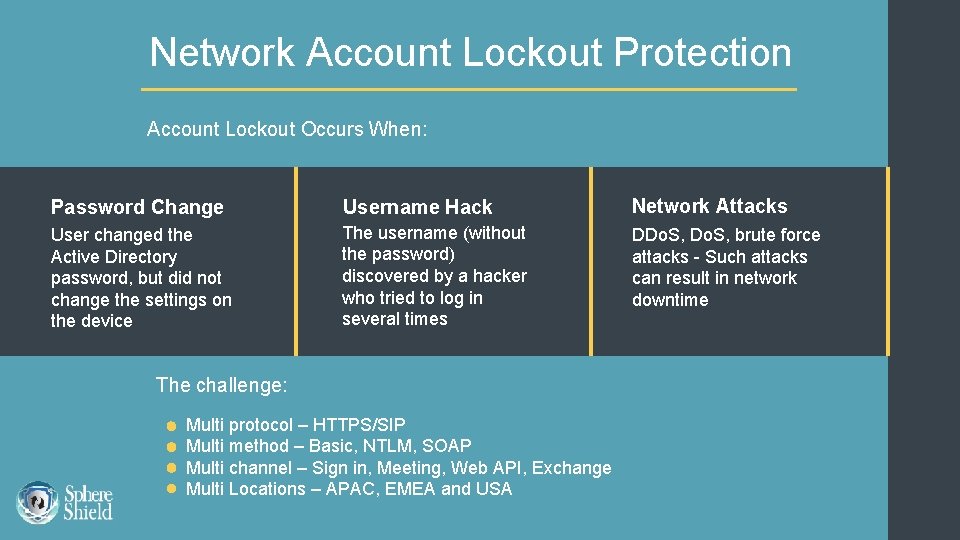
Network Account Lockout Protection Account Lockout Occurs When: Password Change Username Hack Network Attacks User changed the Active Directory password, but did not change the settings on the device The username (without the password) discovered by a hacker who tried to log in several times DDo. S, brute force attacks - Such attacks can result in network downtime The challenge: Multi protocol – HTTPS/SIP Multi method – Basic, NTLM, SOAP Multi channel – Sign in, Meeting, Web API, Exchange Multi Locations – APAC, EMEA and USA
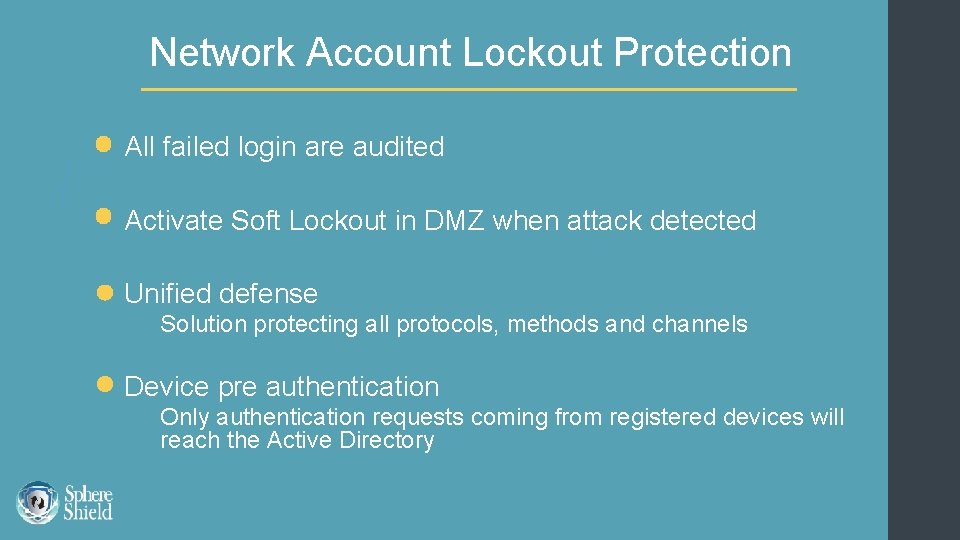
Network Account Lockout Protection All failed login are audited Activate Soft Lockout in DMZ when attack detected Unified defense Solution protecting all protocols, methods and channels Device pre authentication Only authentication requests coming from registered devices will reach the Active Directory
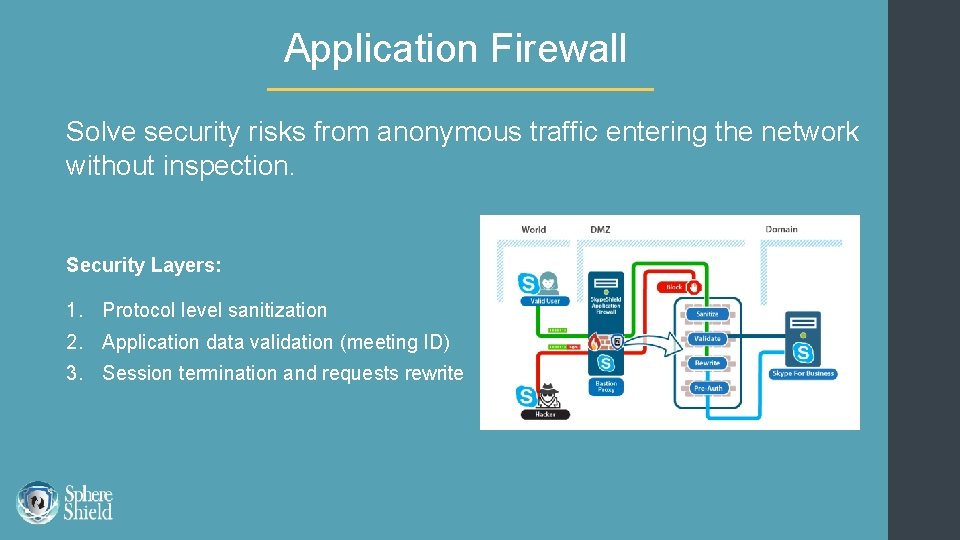
Application Firewall Solve security risks from anonymous traffic entering the network without inspection. Security Layers: 1. Protocol level sanitization 2. Application data validation (meeting ID) 3. Session termination and requests rewrite
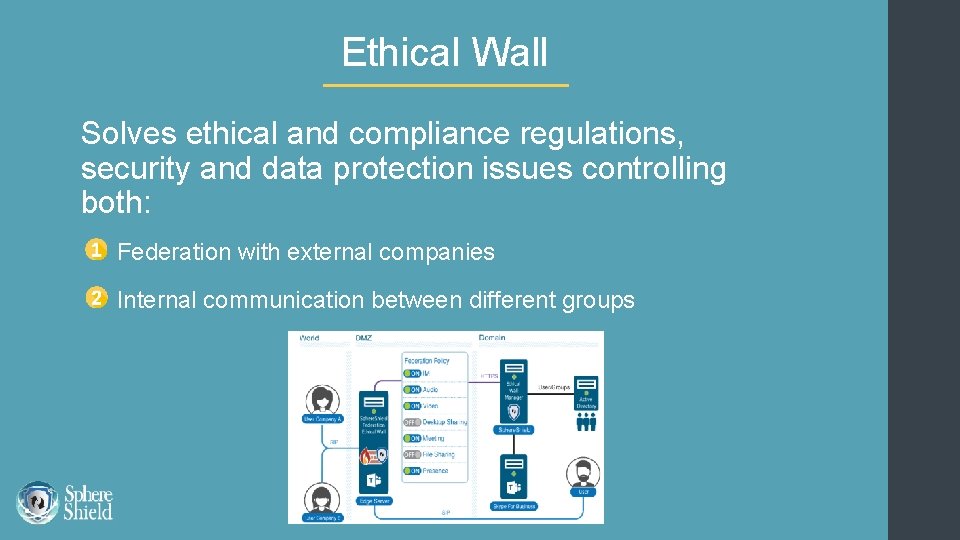
Ethical Wall Solves ethical and compliance regulations, security and data protection issues controlling both: Federation with external companies Internal communication between different groups
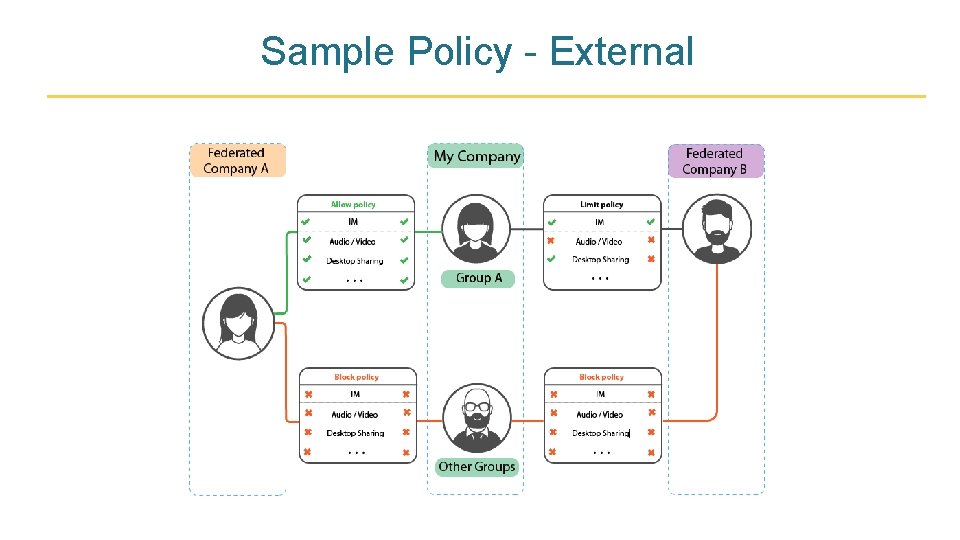
Sample Policy - External
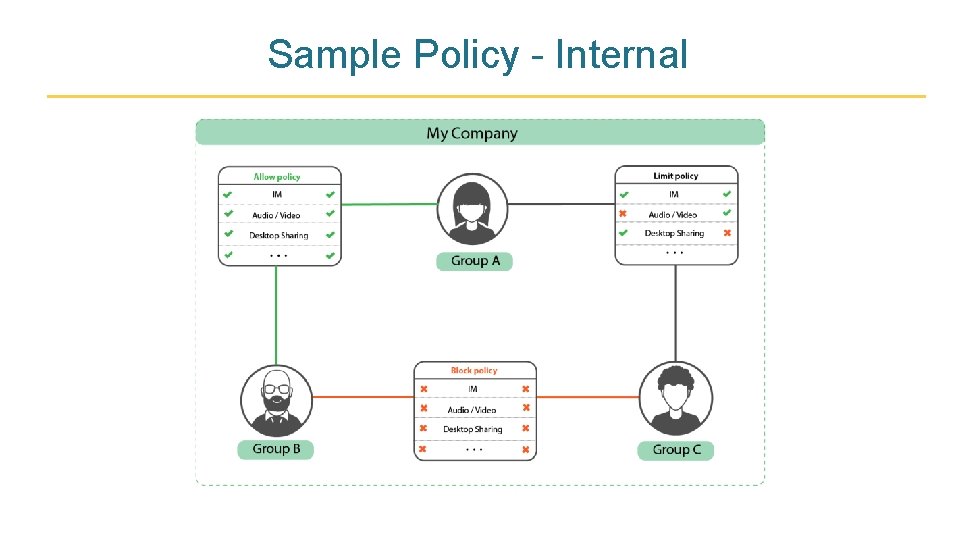
Sample Policy - Internal
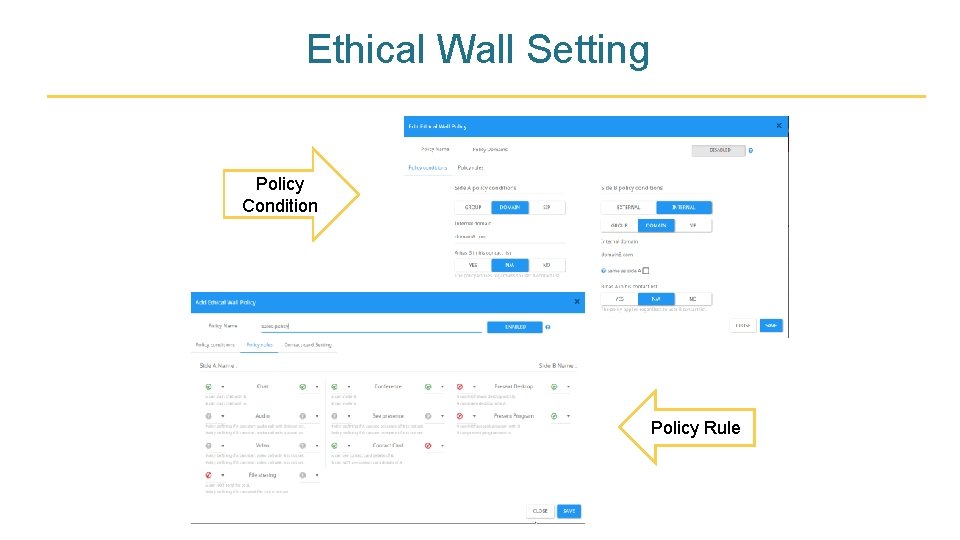
Ethical Wall Setting Policy Condition Policy Rule
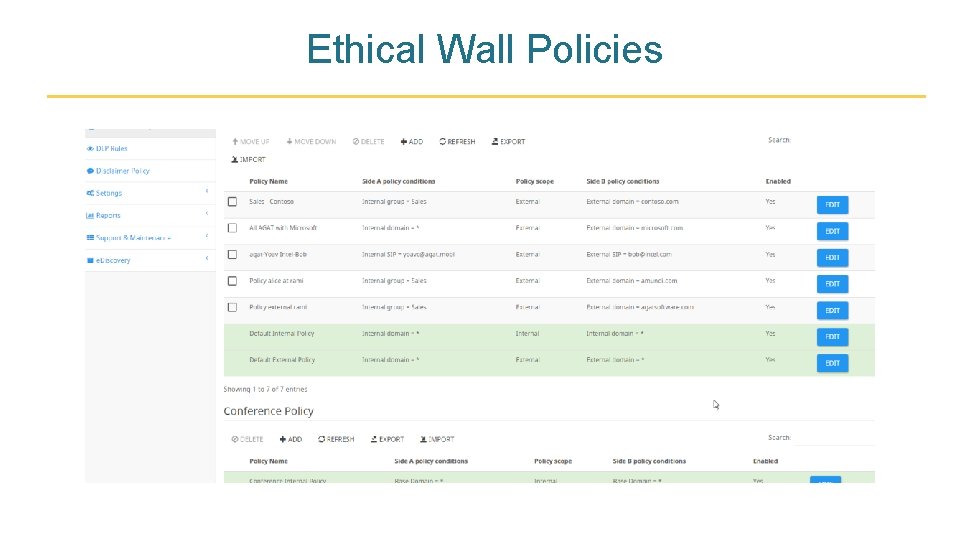
Ethical Wall Policies
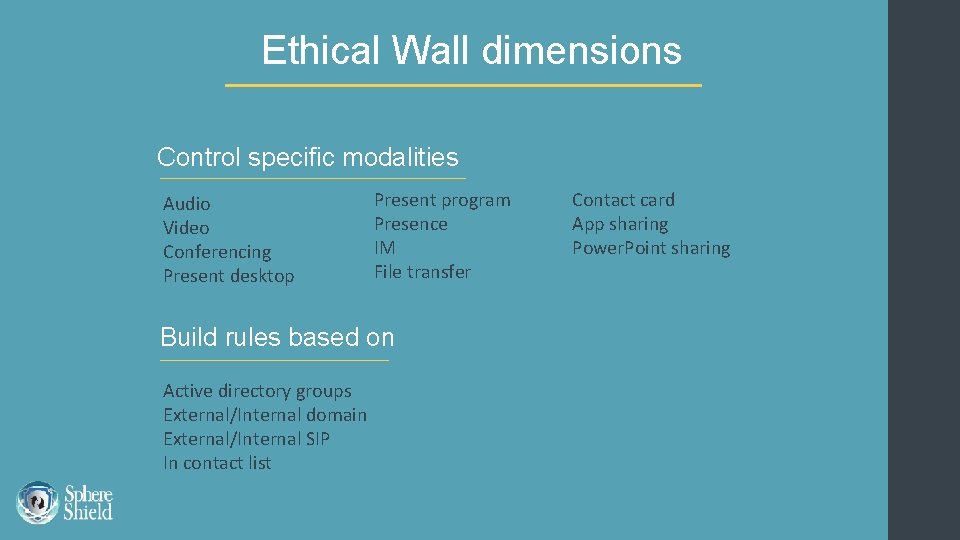
Ethical Wall dimensions Control specific modalities Audio Video Conferencing Present desktop Present program Presence IM File transfer Build rules based on Active directory groups External/Internal domain External/Internal SIP In contact list Contact card App sharing Power. Point sharing
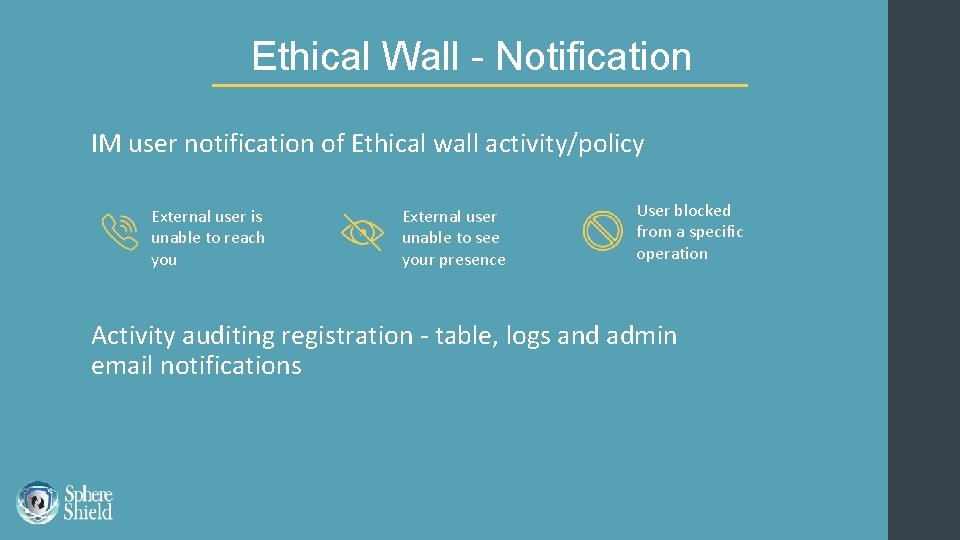
Ethical Wall - Notification IM user notification of Ethical wall activity/policy External user is unable to reach you External user unable to see your presence User blocked from a specific operation Activity auditing registration - table, logs and admin email notifications
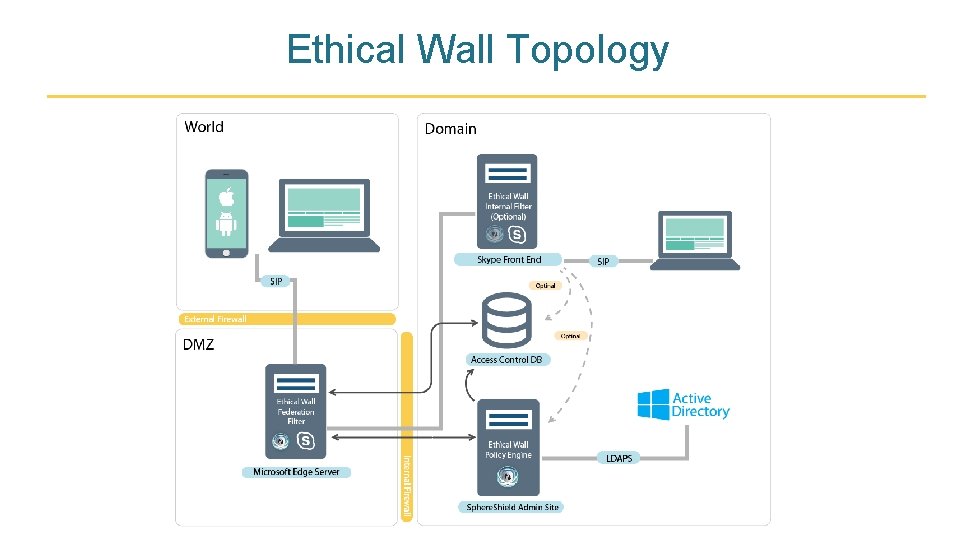
Ethical Wall Topology
DLP Engine Server side solution inspecting content passing through any channel. Sending messages to existing DLP vendors or Sphere. Shield DLP engine to meet existing policies.
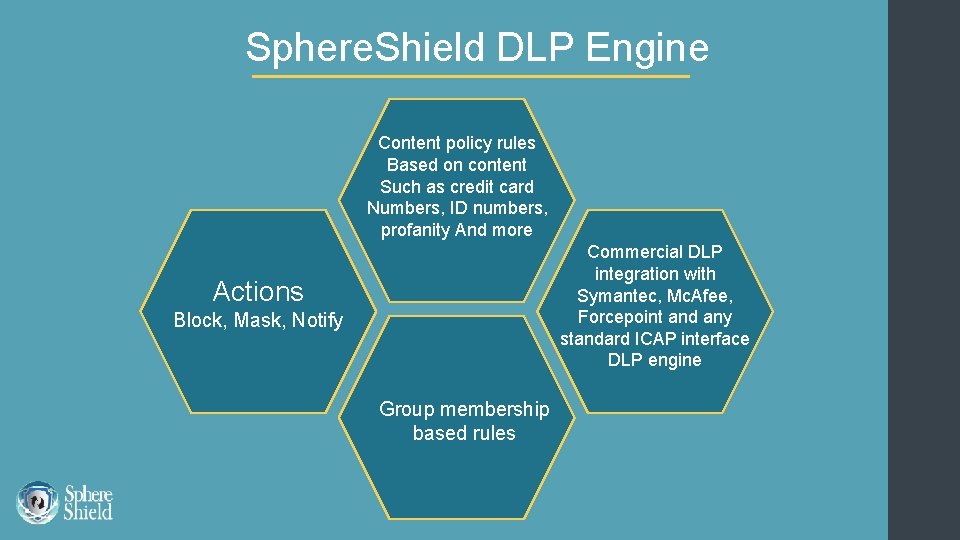
Sphere. Shield DLP Engine Content policy rules Based on content Such as credit card Numbers, ID numbers, profanity And more Commercial DLP integration with Symantec, Mc. Afee, Forcepoint and any standard ICAP interface DLP engine Actions Block, Mask, Notify Group membership based rules
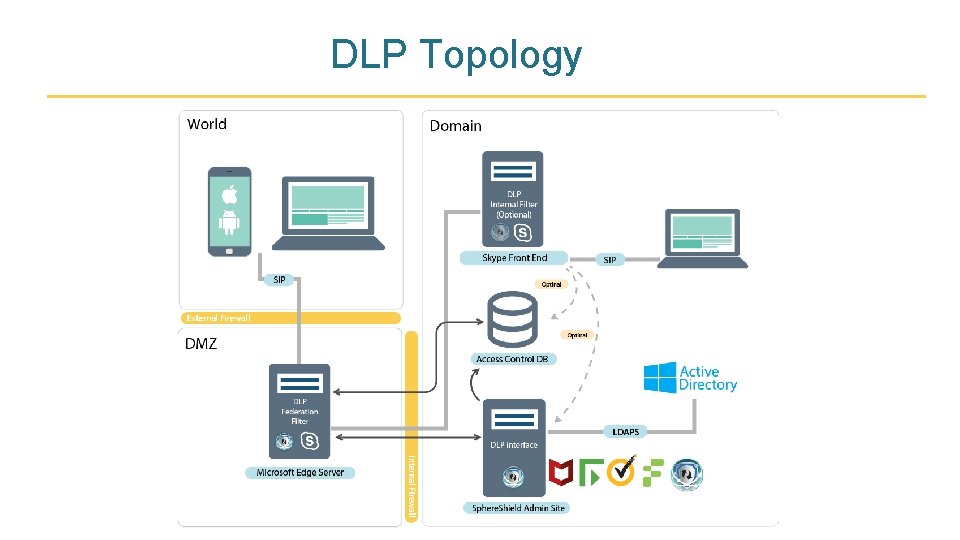
DLP Topology
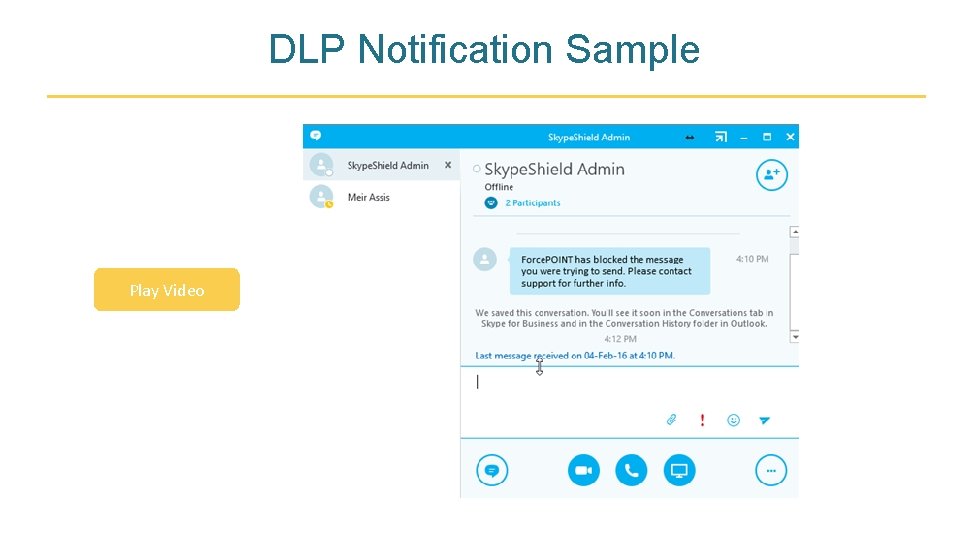
DLP Notification Sample Play Video
Active Directory Credential Protection A new approach in protecting the Active Directory credentials. Connect using App dedicated Skype credentials Eliminate risk of domain password theft No storage of Active Directory passwords on server or device Supports Exchange & Skype with one App credentials

Active Directory App login Creating dedicated Skype credential on a self service internal web site for use on the device, instead of Active Directory credentials. Play Video
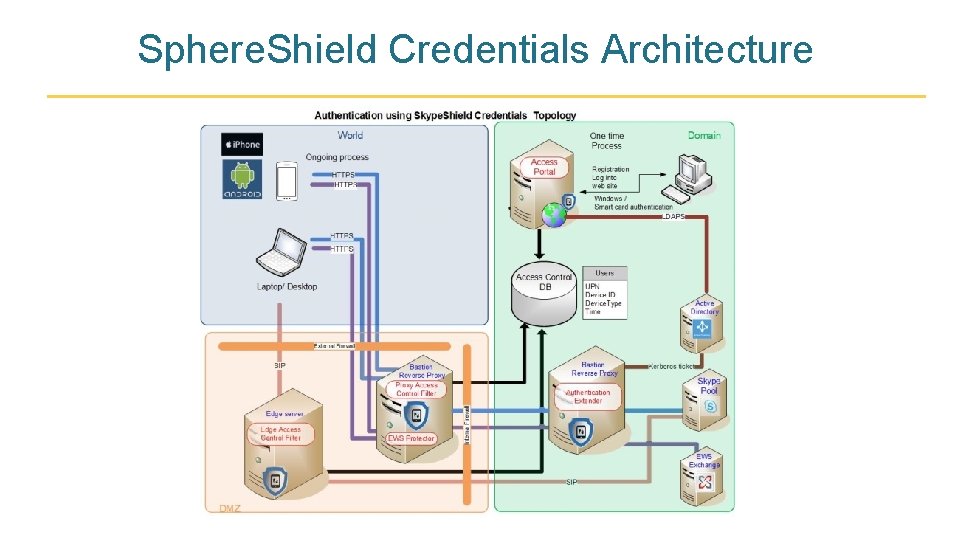
Sphere. Shield Credentials Architecture
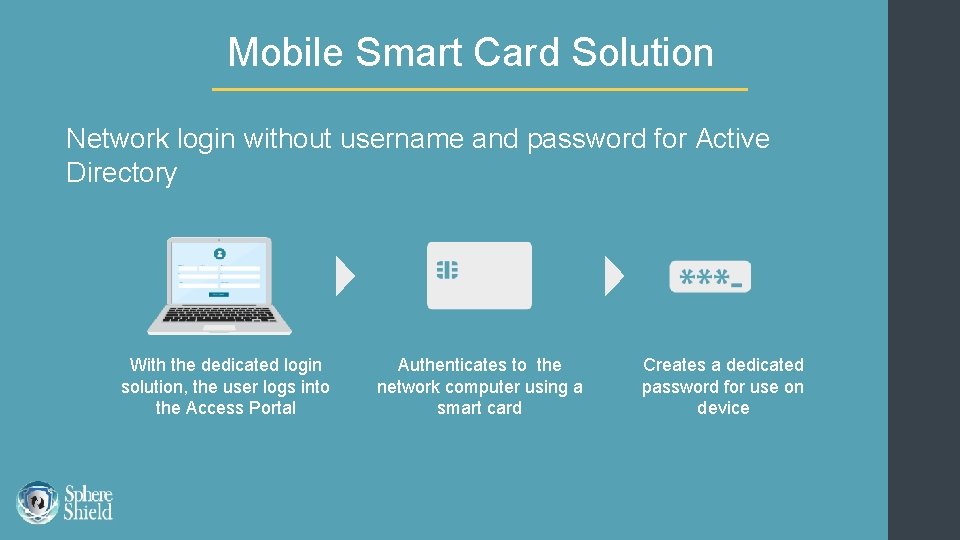
Mobile Smart Card Solution Network login without username and password for Active Directory With the dedicated login solution, the user logs into the Access Portal Authenticates to the network computer using a smart card Creates a dedicated password for use on device
RSA integration Strong TFA Avoid using domain credentials Users enter their RSA Token authentication code instead of Active Directory password Sphere. Shield verifies password against RSA Authentication Manager and impersonate user against Skype
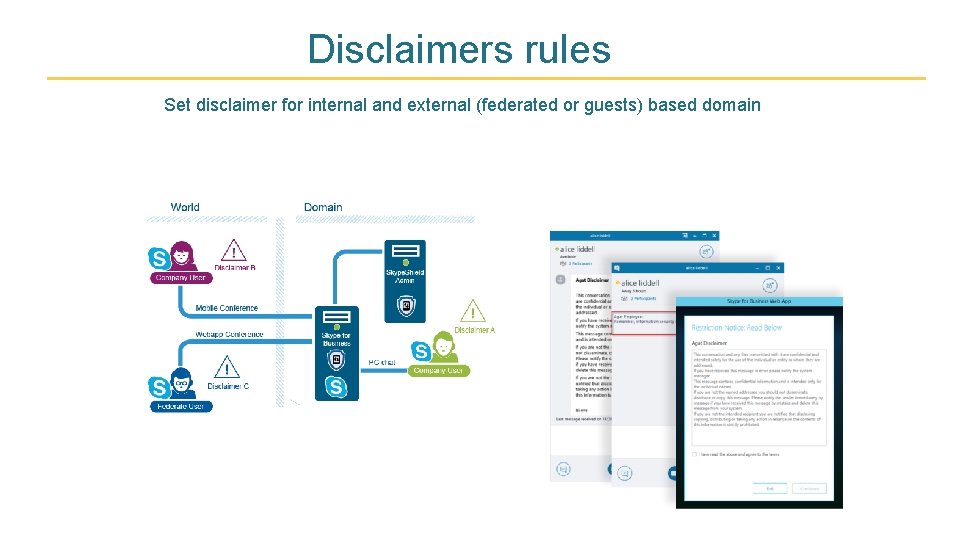
Disclaimers rules Set disclaimer for internal and external (federated or guests) based domain
Disclaimer types Internal User Client Invite To External Conference Presented to the internal user in the Sf. B client every time a new conversation/conference has started. Sent as IM to internal user when he was invited to an external conference. IM Conference Sent as IM once a user has joined the conference. IM Conversation Included with the first IM message sent while the communication is a conversation (one on one).
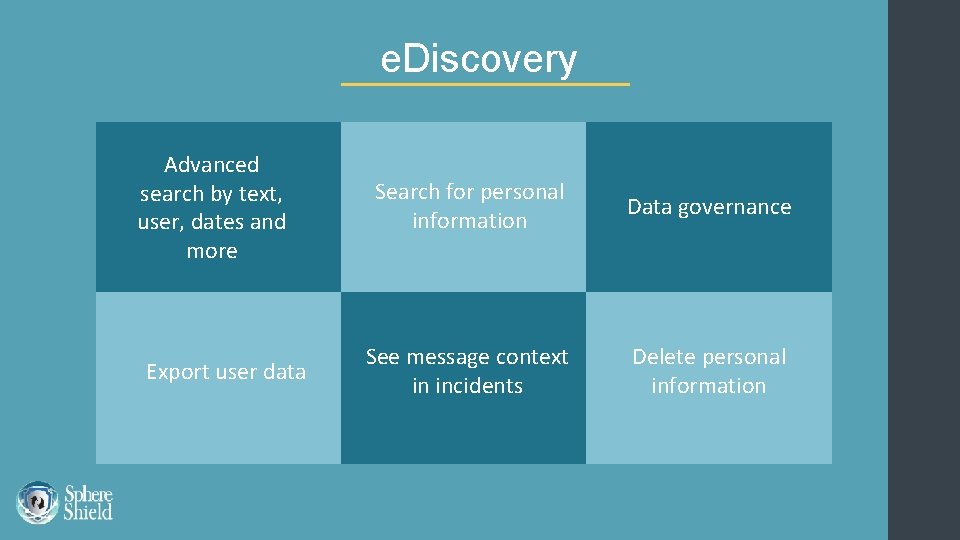
e. Discovery Advanced search by text, user, dates and more Export user data Search for personal information Data governance See message context in incidents Delete personal information
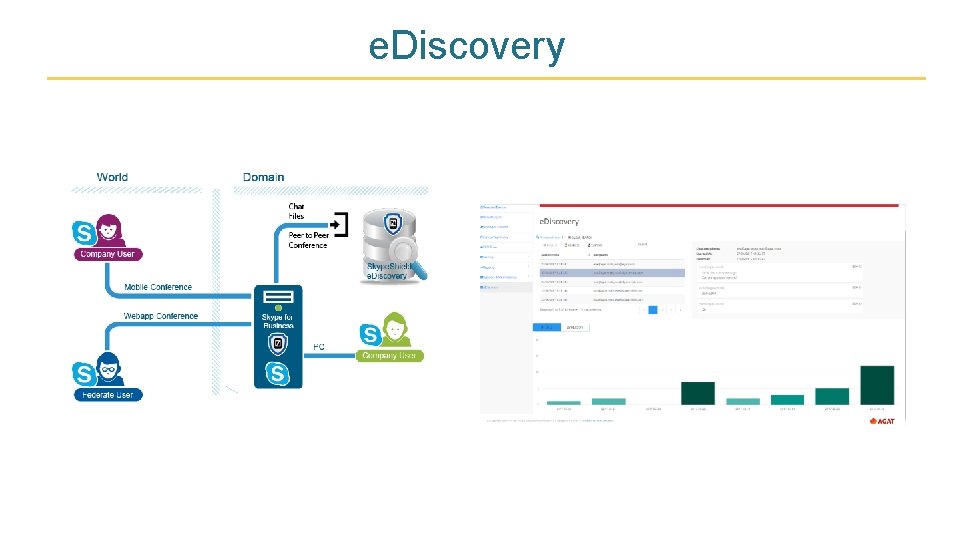
e. Discovery
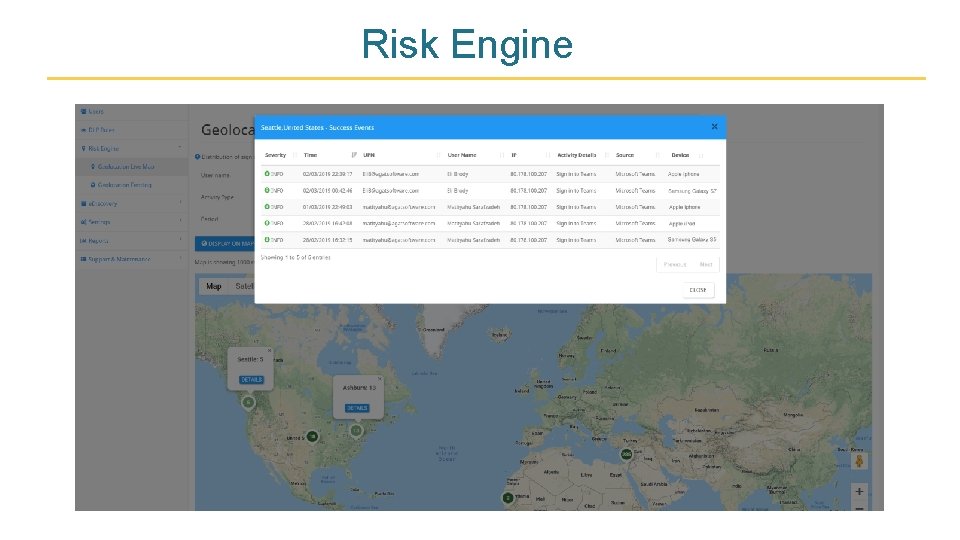
Risk Engine
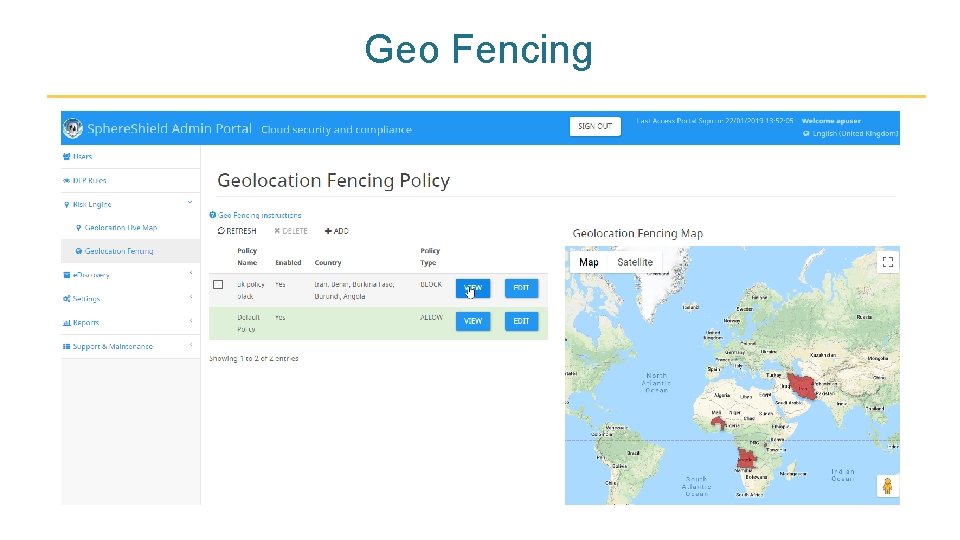
Geo Fencing
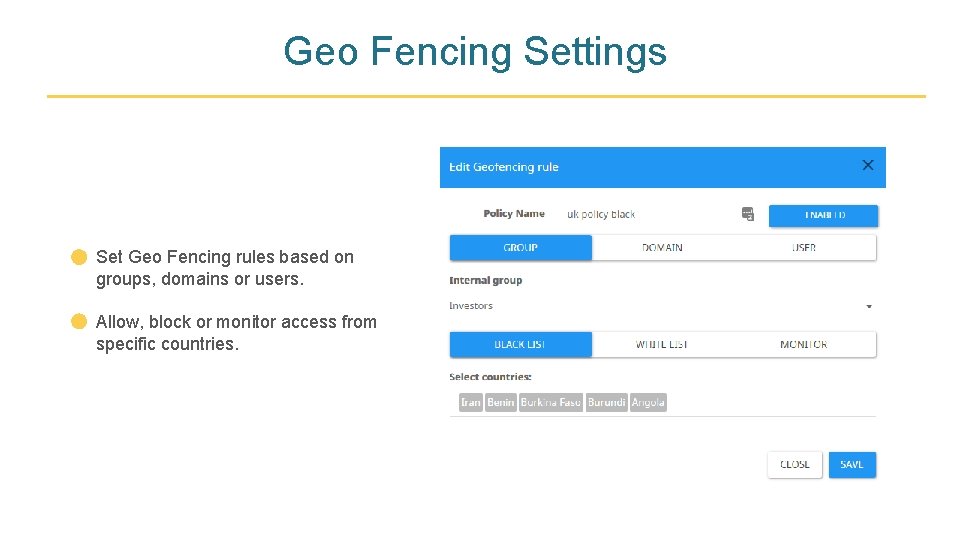
Geo Fencing Settings Set Geo Fencing rules based on groups, domains or users. Allow, block or monitor access from specific countries.
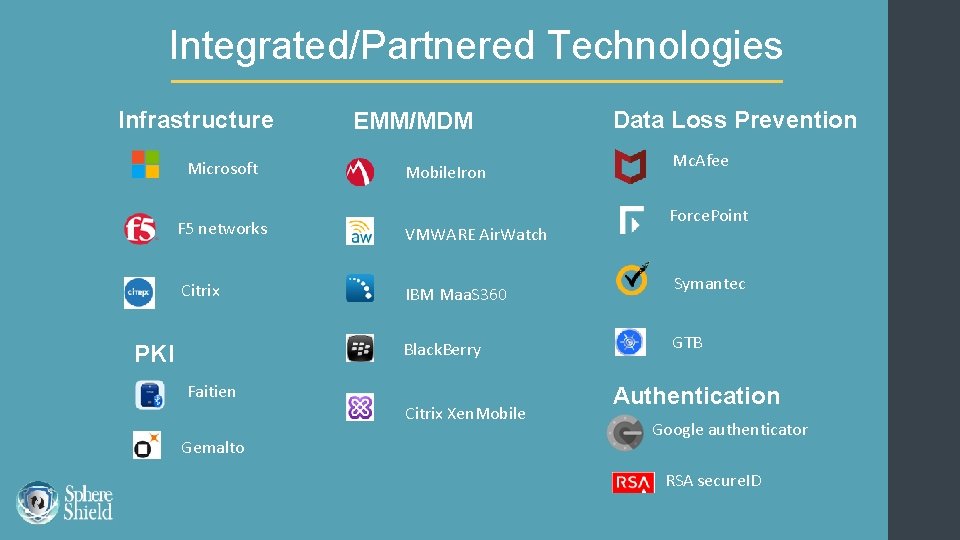
Integrated/Partnered Technologies Infrastructure Microsoft EMM/MDM Mobile. Iron F 5 networks VMWARE Air. Watch Citrix IBM Maa. S 360 Black. Berry PKI Faitien Gemalto Citrix Xen. Mobile Data Loss Prevention Mc. Afee Force. Point Symantec GTB Authentication Google authenticator RSA secure. ID
Product Documents Skype for Business Security Threats Sphere. Shield product page Sphere. Shield datasheet
More Info Visit our website AGAT Software Contact us info@agatsoftware. com +972 -525209860 Thank you
- Slides: 53