Sophisticated attack against VLE bank real case investigation

Sophisticated attack against VLE bank – real case investigation
Short introduction – victim profile • • 2 About 40 k seats in total Strong SOC team 3 rd party investigators/TIS All required ITSec systems are in place & in the right hands Copyright 2016 Trend Micro Inc.
Most prevalent attack types in bank 3 Copyright 2016 Trend Micro Inc.
Used tools/channels • • • 4 Cobalt Strike Mimikatz PS Keylogger Some RC tools + some more undiscovered stuff… Copyright 2016 Trend Micro Inc. HTTP/DNS/UDP/SMB/Proxy
First detected suspicious activity /> Payload /> URL /> C&C callback /> Lateral movement 5 Copyright 2016 Trend Micro Inc.
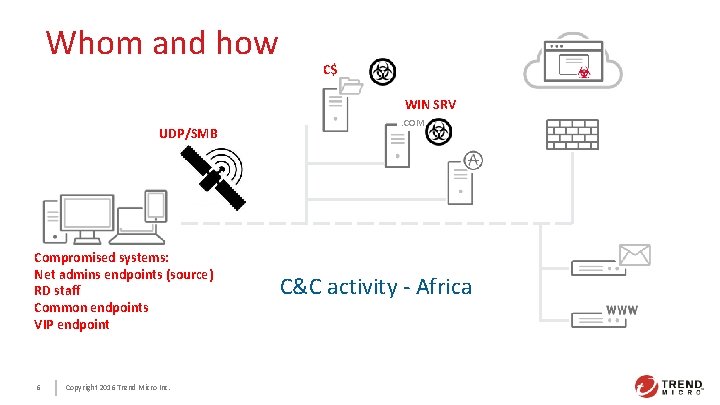
Whom and how C$ WIN SRV UDP/SMB Compromised systems: Net admins endpoints (source) RD staff Common endpoints VIP endpoint 6 Copyright 2016 Trend Micro Inc. . COM C&C activity - Africa
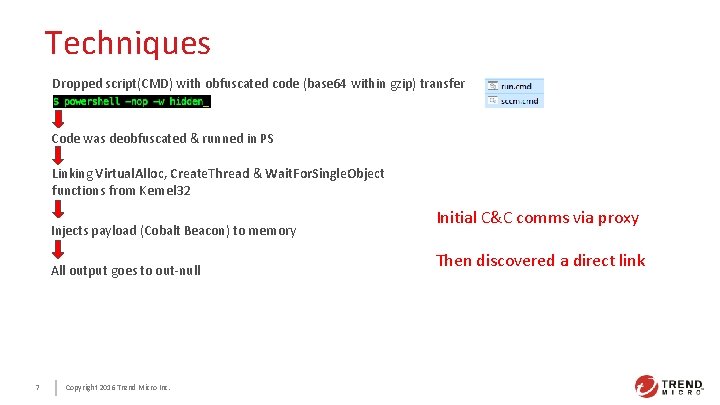
Techniques Dropped script(CMD) with obfuscated code (base 64 within gzip) transfer Code was deobfuscated & runned in PS Linking Virtual. Alloc, Create. Thread & Wait. For. Single. Object functions from Kernel 32 Injects payload (Cobalt Beacon) to memory All output goes to out-null 7 Copyright 2016 Trend Micro Inc. Initial C&C comms via proxy Then discovered a direct link
Probable goals of attack • Access to money-transfer related systems But detected at reconnaissance stage 8 Copyright 2016 Trend Micro Inc.
Lessons learned • More strict control on RD systems usage • More strict control on east-west communications • More closer interaction between the IT & ITSec depts 9 Copyright 2016 Trend Micro Inc.

Thank you 10 Copyright 2016 Trend Micro Inc.
- Slides: 10