Somos Sequences and Cryptographic Applications Richard Schroeppel Hilarie
![Alice and Bob and Somos 4 over F[p] Alice chooses A from [1, p-1] Alice and Bob and Somos 4 over F[p] Alice chooses A from [1, p-1]](https://slidetodoc.com/presentation_image/cfb913e9569b5633c47bb92eb6f467e4/image-11.jpg)
- Slides: 17
Somos Sequences and Cryptographic Applications Richard Schroeppel Hilarie Orman R. Wm. Gosper
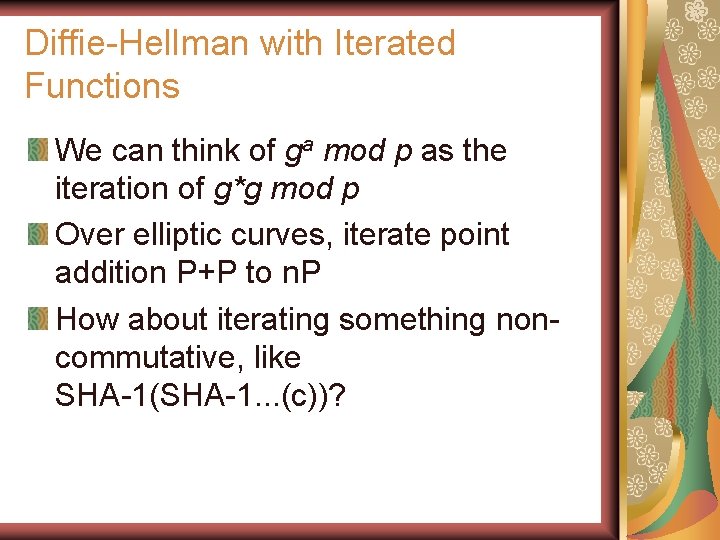
Diffie-Hellman with Iterated Functions We can think of ga mod p as the iteration of g*g mod p Over elliptic curves, iterate point addition P+P to n. P How about iterating something noncommutative, like SHA-1(SHA-1. . . (c))?
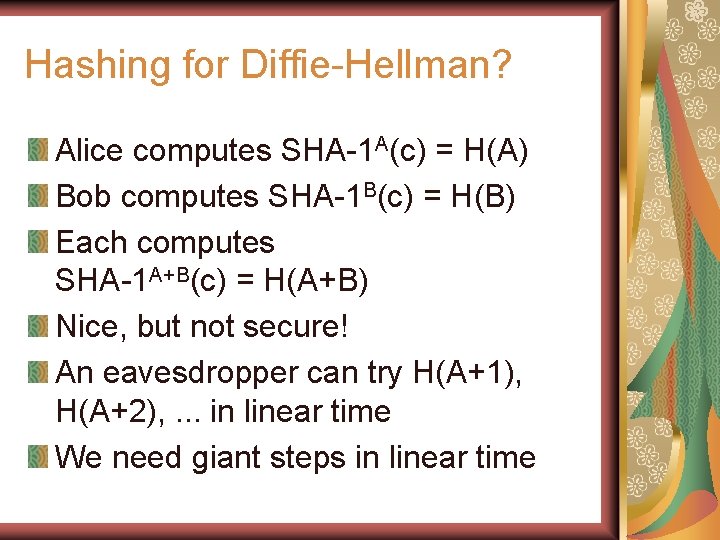
Hashing for Diffie-Hellman? Alice computes SHA-1 A(c) = H(A) Bob computes SHA-1 B(c) = H(B) Each computes SHA-1 A+B(c) = H(A+B) Nice, but not secure! An eavesdropper can try H(A+1), H(A+2), . . . in linear time We need giant steps in linear time
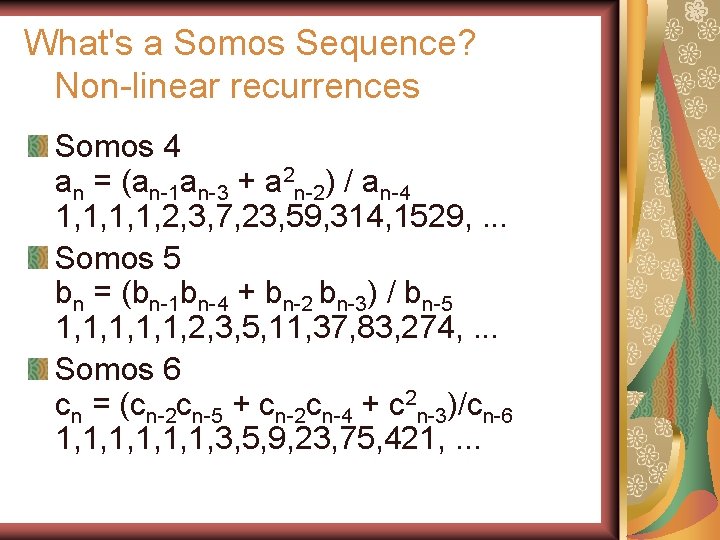
What's a Somos Sequence? Non-linear recurrences Somos 4 an = (an-1 an-3 + a 2 n-2) / an-4 1, 1, 2, 3, 7, 23, 59, 314, 1529, . . . Somos 5 bn = (bn-1 bn-4 + bn-2 bn-3) / bn-5 1, 1, 1, 2, 3, 5, 11, 37, 83, 274, . . . Somos 6 cn = (cn-2 cn-5 + cn-2 cn-4 + c 2 n-3)/cn-6 1, 1, 1, 3, 5, 9, 23, 75, 421, . . .
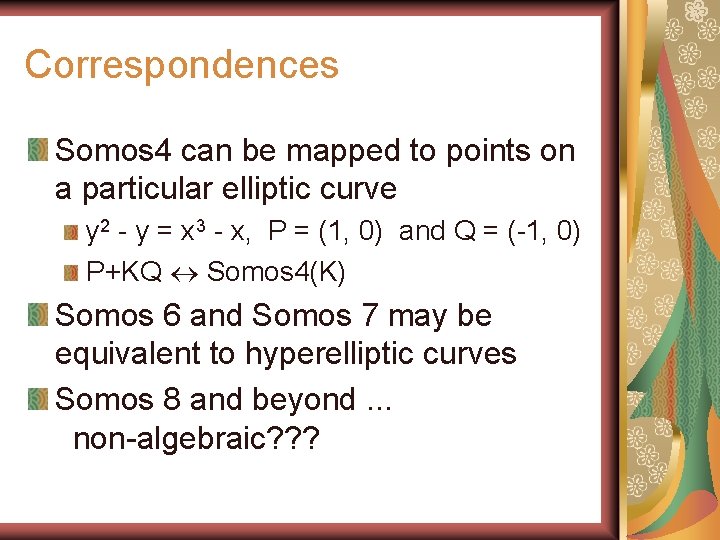
Apparent Mysteries. . . There's a quotient in the formulas, how come the values are integers? Somos 8 and beyond are not! Are these equivalent to some previously known sequences? Can you do anything interesting with them? Let's interpret them over finite fields
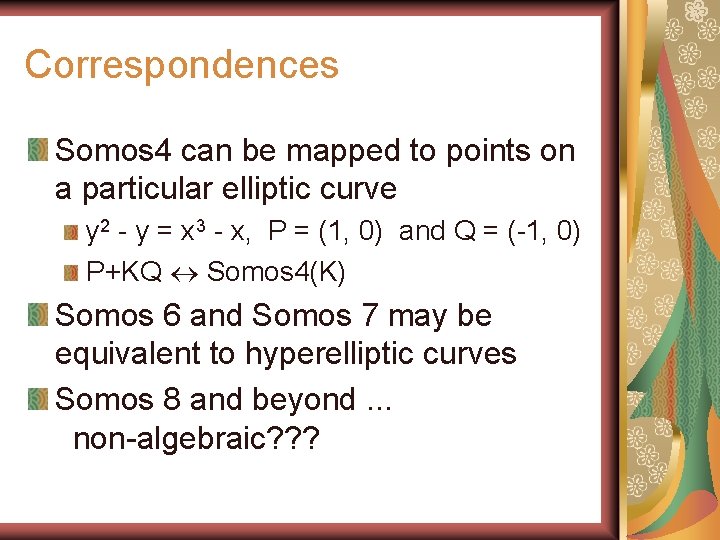
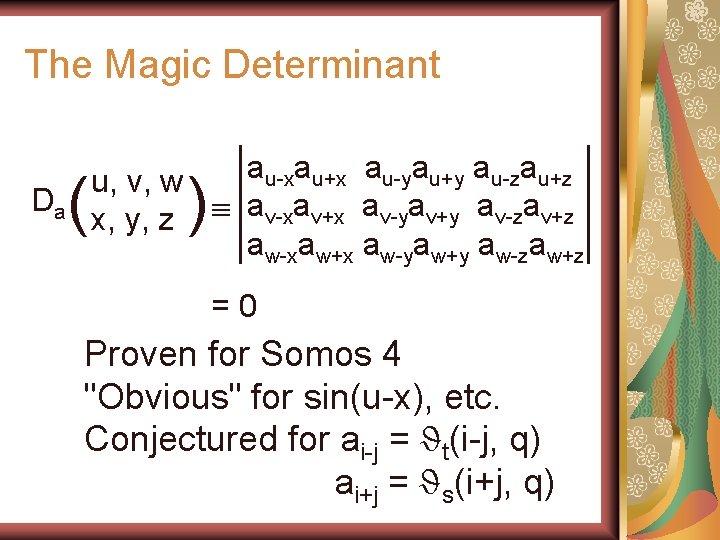
Correspondences Somos 4 can be mapped to points on a particular elliptic curve y 2 - y = x 3 - x, P = (1, 0) and Q = (-1, 0) P+KQ Somos 4(K) Somos 6 and Somos 7 may be equivalent to hyperelliptic curves Somos 8 and beyond. . . non-algebraic? ? ?
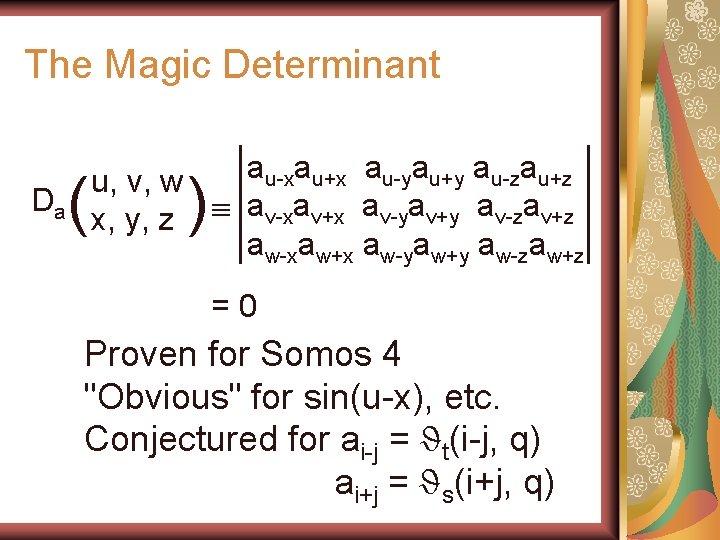
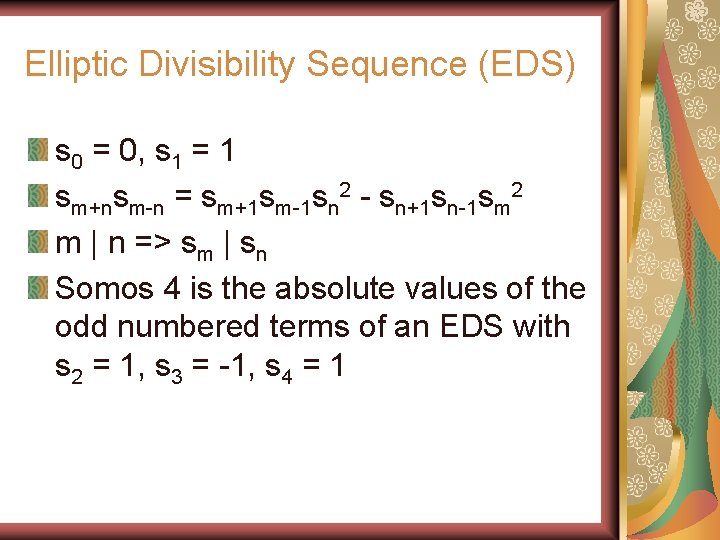
The Magic Determinant Da ( au-xau+x au-yau+y au-zau+z u, v, w x, y, z av-xav+x av-yav+y av-zav+z aw-xaw+x aw-yaw+y aw-zaw+z ) =0 Proven for Somos 4 "Obvious" for sin(u-x), etc. Conjectured for ai-j = ϑt(i-j, q) ai+j = ϑs(i+j, q)
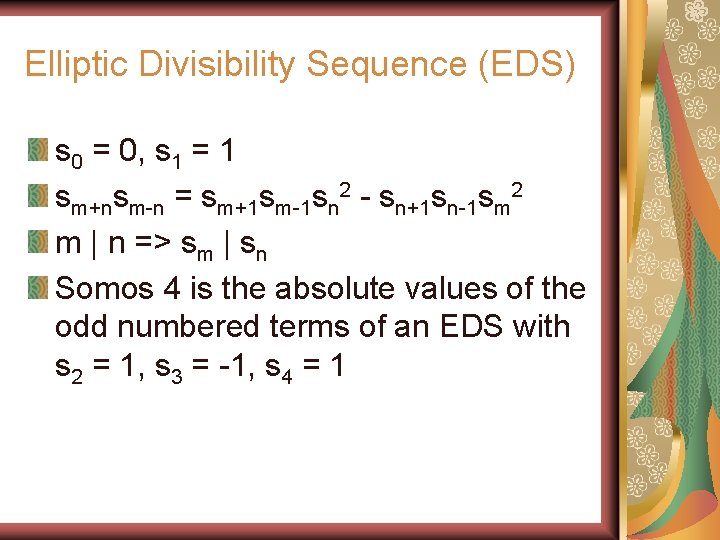
Elliptic Divisibility Sequence (EDS) s 0 = 0, s 1 = 1 sm+nsm-n = sm+1 sm-1 sn 2 - sn+1 sn-1 sm 2 m | n => sm | sn Somos 4 is the absolute values of the odd numbered terms of an EDS with s 2 = 1, s 3 = -1, s 4 = 1
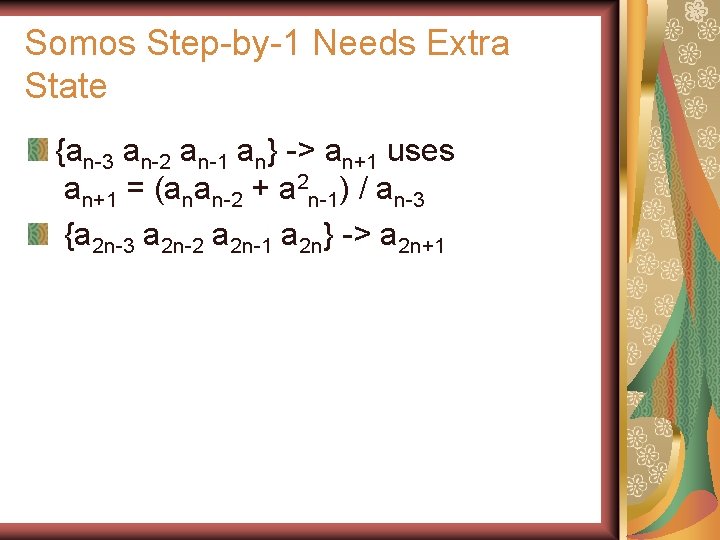
Near Addition Formula for Somos 4 Derived from the magic determinant u = k+1, v = 0, w =1 x = k-1, y = 0 , z = 1 a 2 k = 2 akak+13 + ak-1 akak+22 - ak-1 ak+12 ak+2 - ak 2 ak+1 ak+2 This is our Diffie-Hellman "giant step" NB, normally DH goes from k to k 2 for the "giant step", but Somos is secure for k -> 2 k !! (as we will show)
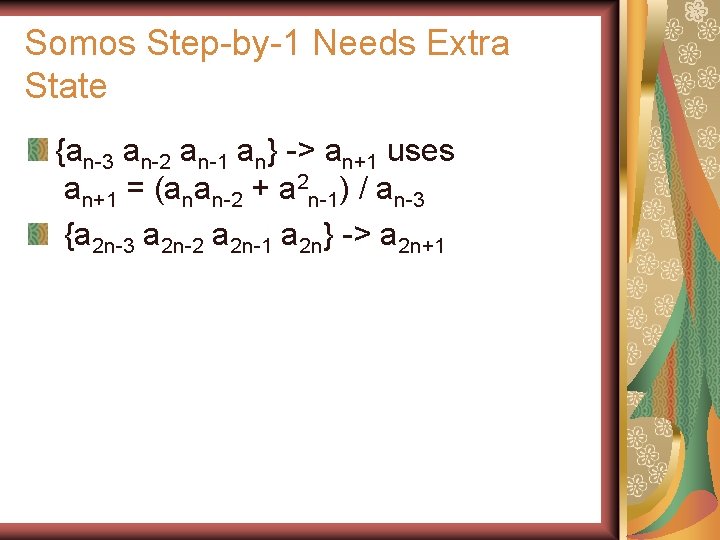
Somos Step-by-1 Needs Extra State {an-3 an-2 an-1 an} -> an+1 uses an+1 = (anan-2 + a 2 n-1) / an-3 {a 2 n-3 a 2 n-2 a 2 n-1 a 2 n} -> a 2 n+1
![Alice and Bob and Somos 4 over Fp Alice chooses A from 1 p1 Alice and Bob and Somos 4 over F[p] Alice chooses A from [1, p-1]](https://slidetodoc.com/presentation_image/cfb913e9569b5633c47bb92eb6f467e4/image-11.jpg)
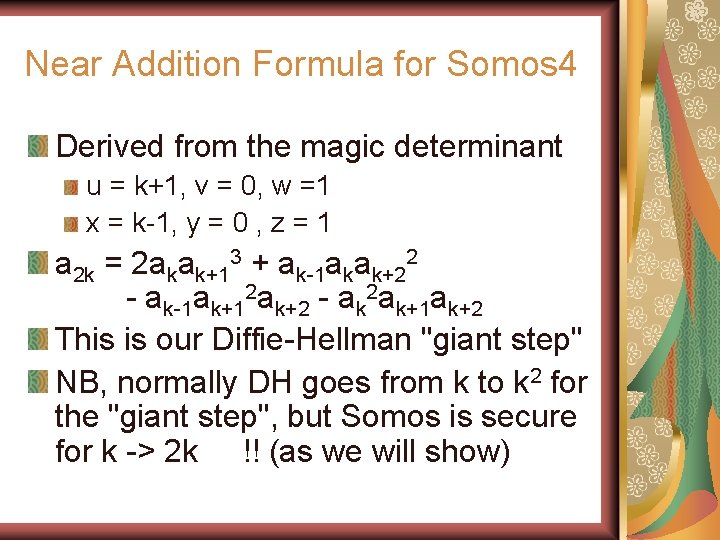
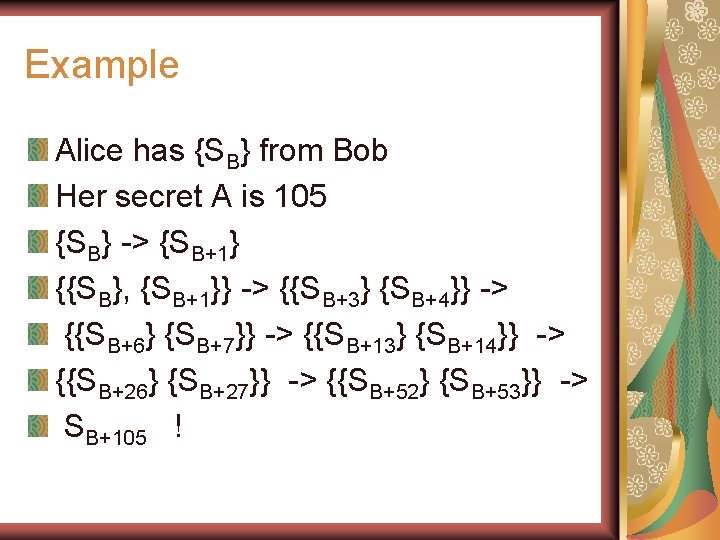
Alice and Bob and Somos 4 over F[p] Alice chooses A from [1, p-1] Alice calculates Somos 4(A) mod p Uses doubling formula and step-by-one formula Bob does the same with B Alice sends {Somos 4(A) }= {SA-3, SA-2, SA-1, SA } to Bob sends {Somos 4(B)} = {SB} to Alice steps SB to SB+A mod p Uses double and step-by-one Bob steps SA to SA+B
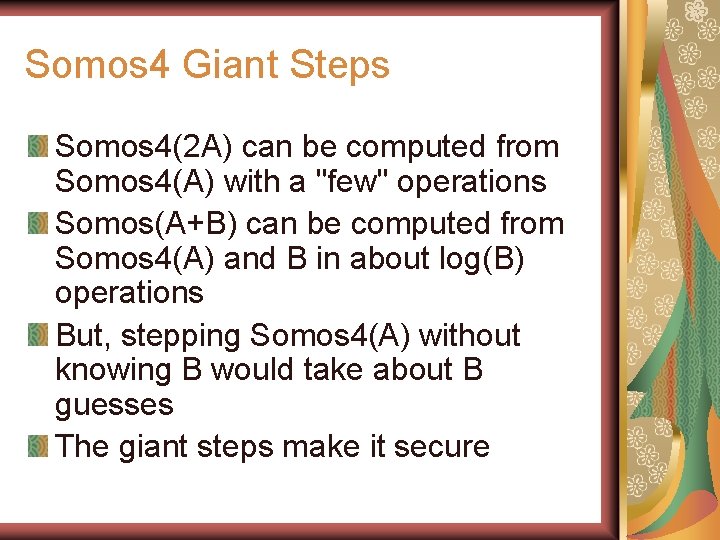
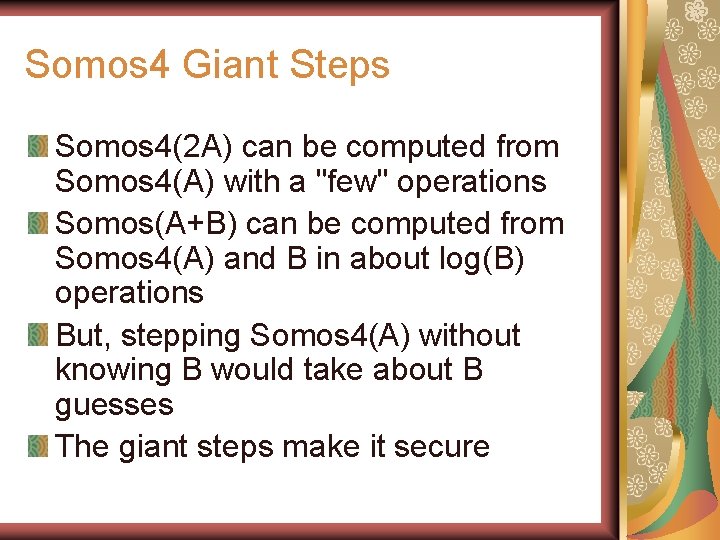
Somos 4 Giant Steps Somos 4(2 A) can be computed from Somos 4(A) with a "few" operations Somos(A+B) can be computed from Somos 4(A) and B in about log(B) operations But, stepping Somos 4(A) without knowing B would take about B guesses The giant steps make it secure
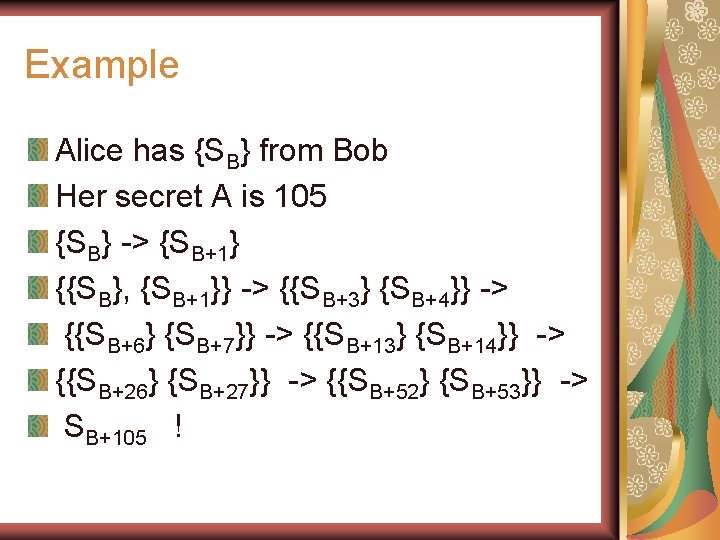
Example Alice has {SB} from Bob Her secret A is 105 {SB} -> {SB+1} {{SB}, {SB+1}} -> {{SB+3} {SB+4}} -> {{SB+6} {SB+7}} -> {{SB+13} {SB+14}} -> {{SB+26} {SB+27}} -> {{SB+52} {SB+53}} -> SB+105 !
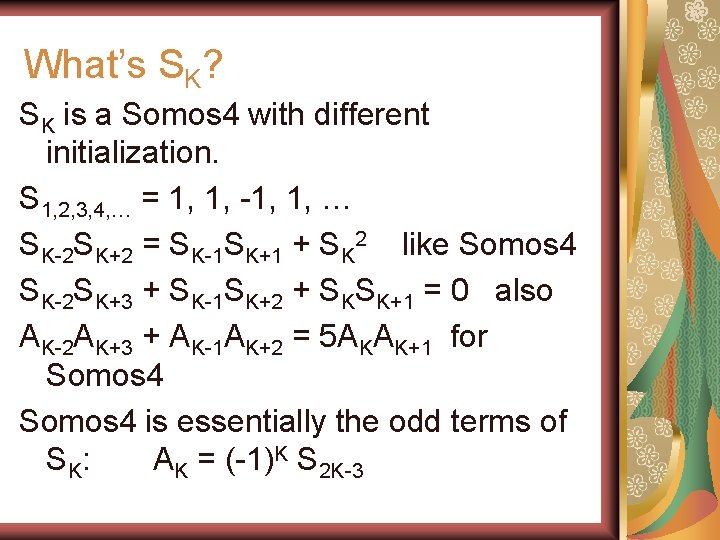
Somos 4 & Elliptic Curves Curve: Y(Y-1) = X(X-1)(X+1) Point: P = (0, 0) Multiples KP: O, (0, 0), (1, 0), (-1, 1), (2, 3), (1/4, 5/8), (6, -14), (-5/9, -8/27), (21/25, 69/125), (-20/49, 435/343), … KP = (XK, YK) = ( -SK-1 SK+1/SK 2, SK-2 SK-1 SK+3/SK 3 ) SK = 0, 1, 1, -1, 1, 2, -1, -3, -5, 7, -4, -23, 29, 59, …
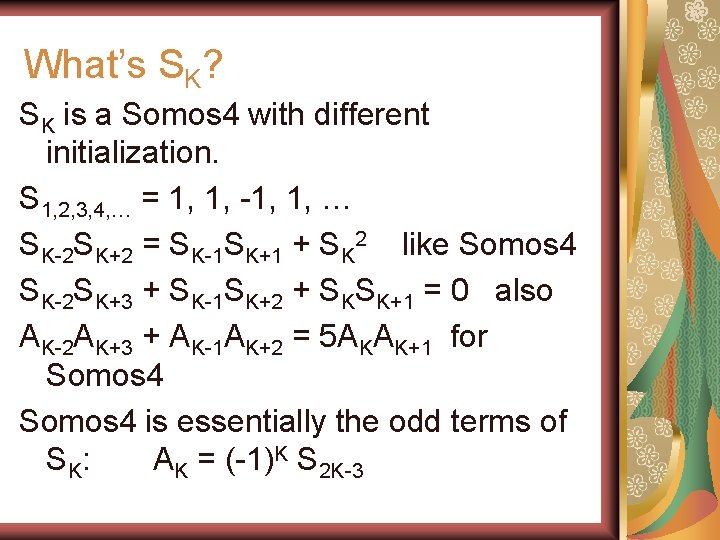
What’s SK? SK is a Somos 4 with different initialization. S 1, 2, 3, 4, … = 1, 1, -1, 1, … SK-2 SK+2 = SK-1 SK+1 + SK 2 like Somos 4 SK-2 SK+3 + SK-1 SK+2 + SKSK+1 = 0 also AK-2 AK+3 + AK-1 AK+2 = 5 AKAK+1 for Somos 4 is essentially the odd terms of S K: AK = (-1)K S 2 K-3
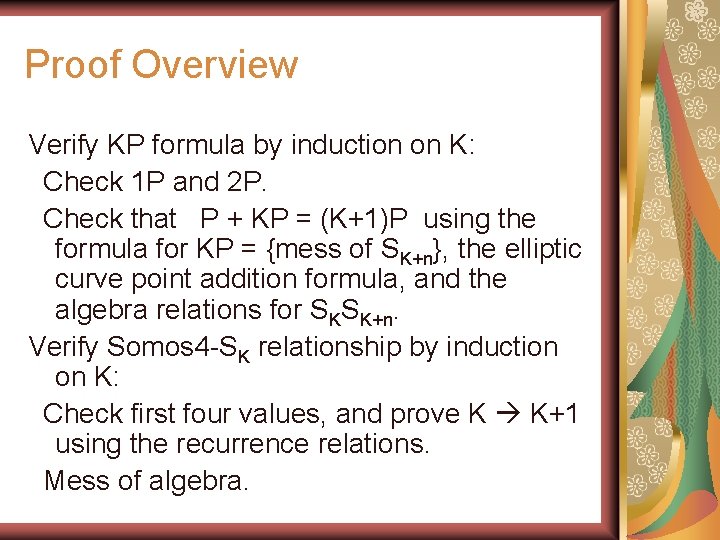
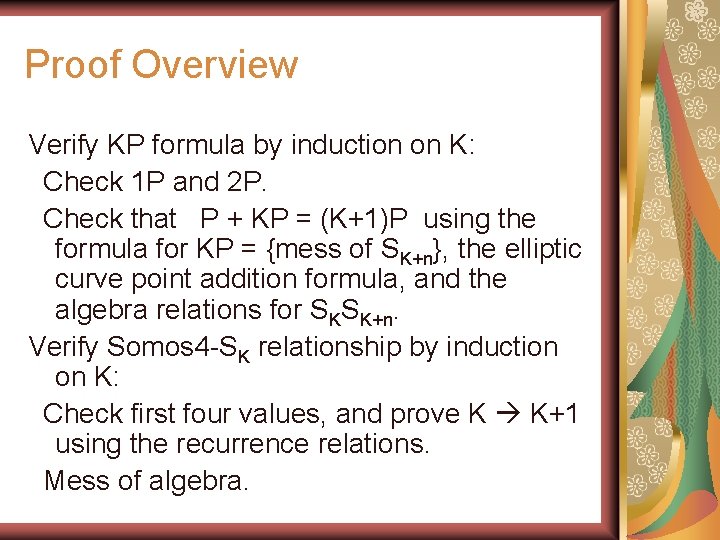
Proof Overview Verify KP formula by induction on K: Check 1 P and 2 P. Check that P + KP = (K+1)P using the formula for KP = {mess of SK+n}, the elliptic curve point addition formula, and the algebra relations for SKSK+n. Verify Somos 4 -SK relationship by induction on K: Check first four values, and prove K K+1 using the recurrence relations. Mess of algebra.
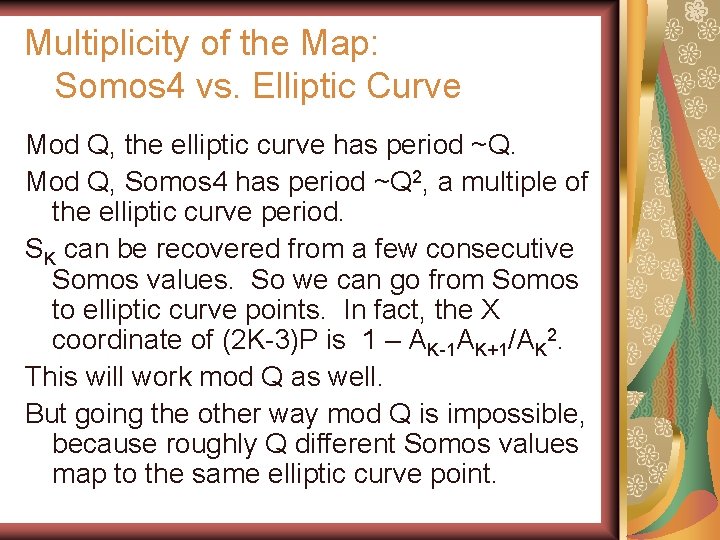
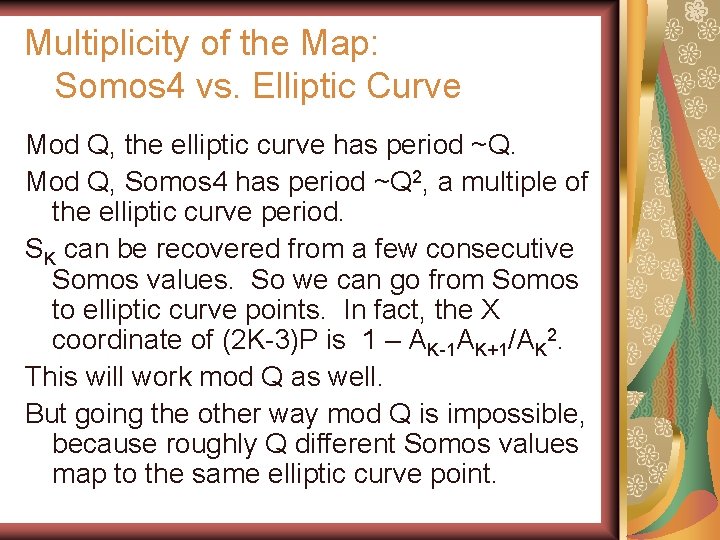
Multiplicity of the Map: Somos 4 vs. Elliptic Curve Mod Q, the elliptic curve has period ~Q. Mod Q, Somos 4 has period ~Q 2, a multiple of the elliptic curve period. SK can be recovered from a few consecutive Somos values. So we can go from Somos to elliptic curve points. In fact, the X coordinate of (2 K-3)P is 1 – AK-1 AK+1/AK 2. This will work mod Q as well. But going the other way mod Q is impossible, because roughly Q different Somos values map to the same elliptic curve point.