Software Vulnerability Examples SQL Injection Example Scenario Imagine

Software Vulnerability Examples
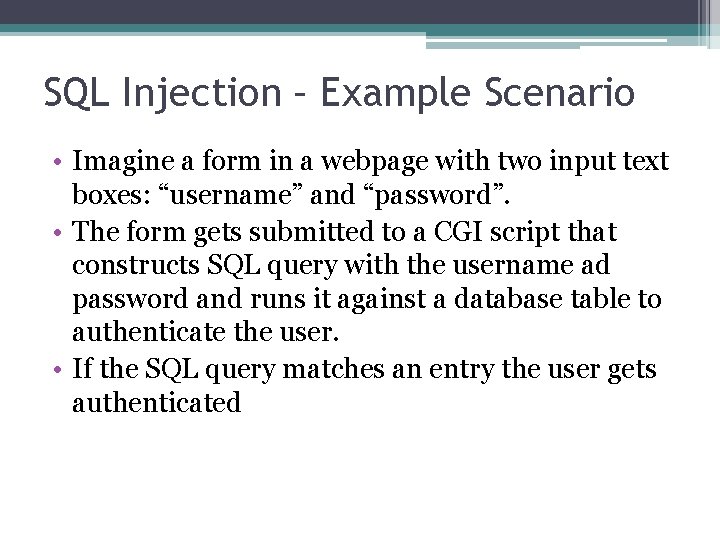
SQL Injection – Example Scenario • Imagine a form in a webpage with two input text boxes: “username” and “password”. • The form gets submitted to a CGI script that constructs SQL query with the username ad password and runs it against a database table to authenticate the user. • If the SQL query matches an entry the user gets authenticated
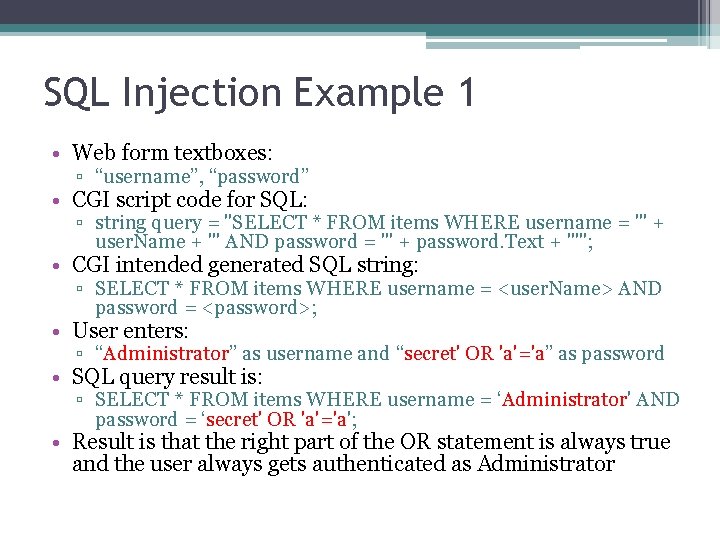
SQL Injection Example 1 • Web form textboxes: ▫ “username”, “password” • CGI script code for SQL: ▫ string query = "SELECT * FROM items WHERE username = '" + user. Name + "' AND password = '" + password. Text + "'"; • CGI intended generated SQL string: ▫ SELECT * FROM items WHERE username = <user. Name> AND password = <password>; • User enters: ▫ “Administrator” as username and “secret' OR 'a'='a” as password • SQL query result is: ▫ SELECT * FROM items WHERE username = ‘Administrator' AND password = ‘secret' OR 'a'='a'; • Result is that the right part of the OR statement is always true and the user always gets authenticated as Administrator
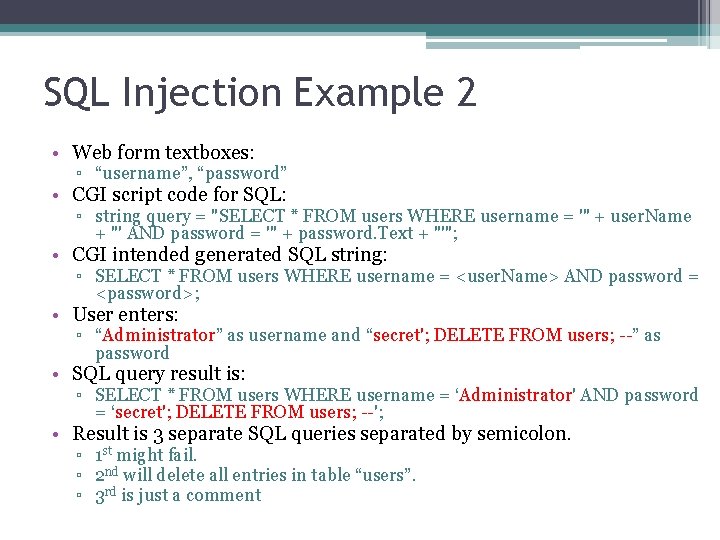
SQL Injection Example 2 • Web form textboxes: ▫ “username”, “password” • CGI script code for SQL: ▫ string query = "SELECT * FROM users WHERE username = '" + user. Name + "' AND password = '" + password. Text + "'"; • CGI intended generated SQL string: ▫ SELECT * FROM users WHERE username = <user. Name> AND password = <password>; • User enters: ▫ “Administrator” as username and “secret'; DELETE FROM users; --” as password • SQL query result is: ▫ SELECT * FROM users WHERE username = ‘Administrator' AND password = ‘secret'; DELETE FROM users; --'; • Result is 3 separate SQL queries separated by semicolon. ▫ 1 st might fail. ▫ 2 nd will delete all entries in table “users”. ▫ 3 rd is just a comment
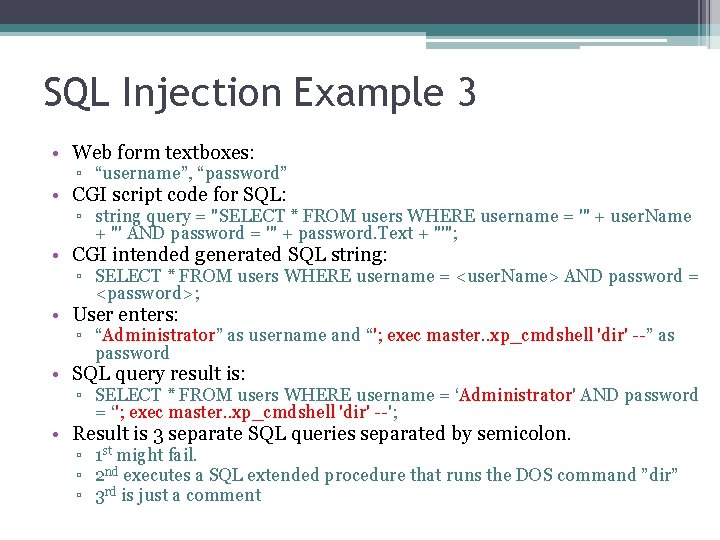
SQL Injection Example 3 • Web form textboxes: ▫ “username”, “password” • CGI script code for SQL: ▫ string query = "SELECT * FROM users WHERE username = '" + user. Name + "' AND password = '" + password. Text + "'"; • CGI intended generated SQL string: ▫ SELECT * FROM users WHERE username = <user. Name> AND password = <password>; • User enters: ▫ “Administrator” as username and “'; exec master. . xp_cmdshell 'dir' --” as password • SQL query result is: ▫ SELECT * FROM users WHERE username = ‘Administrator' AND password = ‘'; exec master. . xp_cmdshell 'dir' --'; • Result is 3 separate SQL queries separated by semicolon. ▫ 1 st might fail. ▫ 2 nd executes a SQL extended procedure that runs the DOS command ”dir” ▫ 3 rd is just a comment
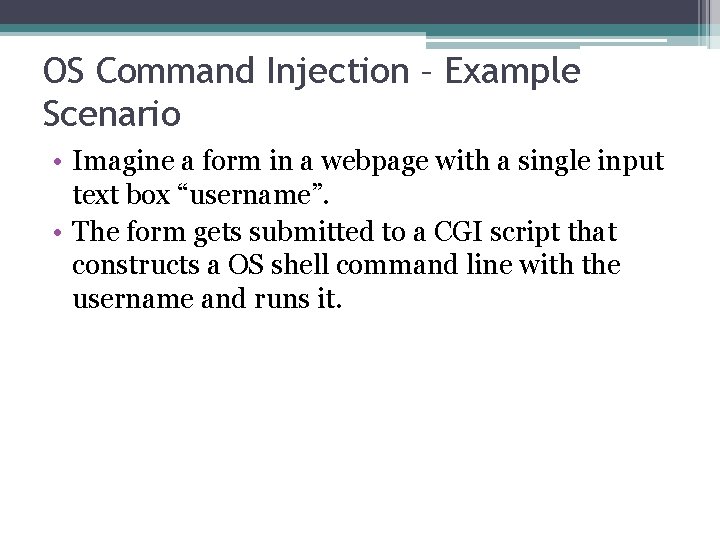
OS Command Injection – Example Scenario • Imagine a form in a webpage with a single input text box “username”. • The form gets submitted to a CGI script that constructs a OS shell command line with the username and runs it.
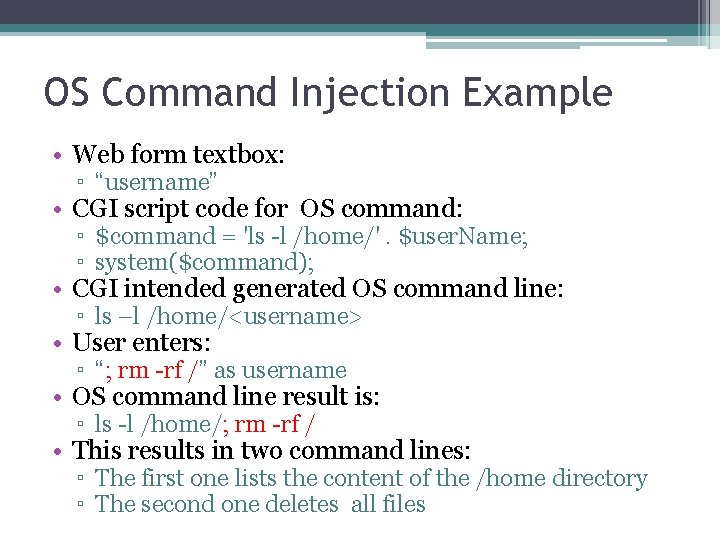
OS Command Injection Example • Web form textbox: ▫ “username” • CGI script code for OS command: ▫ $command = 'ls -l /home/'. $user. Name; ▫ system($command); • CGI intended generated OS command line: ▫ ls –l /home/<username> • User enters: ▫ “; rm -rf /” as username • OS command line result is: ▫ ls -l /home/; rm -rf / • This results in two command lines: ▫ The first one lists the content of the /home directory ▫ The second one deletes all files
![Classic Buffer Overflow Example • Example C code: char buf[24]; printf("Please enter your name Classic Buffer Overflow Example • Example C code: char buf[24]; printf("Please enter your name](http://slidetodoc.com/presentation_image/1ab76b0f3c3e42b2c56999c0bbdab0ff/image-8.jpg)
Classic Buffer Overflow Example • Example C code: char buf[24]; printf("Please enter your name n"); gets(buf); • Vulnerability ▫ The code uses gets() �which is inherently unsafe �blindly copies all input from STDIN to the buffer without restricting how much is copied �This allows the user to provide a string that is larger than the buffer size, resulting in an overflow condition. ▫ Strings like the below one can be used to exploit it: �"xebx 1 fx 5 ex 89x 76x 08x 31xc 0x 88x 46x 07x 89x 46x 0 cxb 0x 0 bx 89xf 3x 8 dx 4 ex 08x 8 dx 56x 0 cxcd x 80x 31xdbx 89xd 8x 40xcdx 80xe 8xdcxffxff/b in/sh"
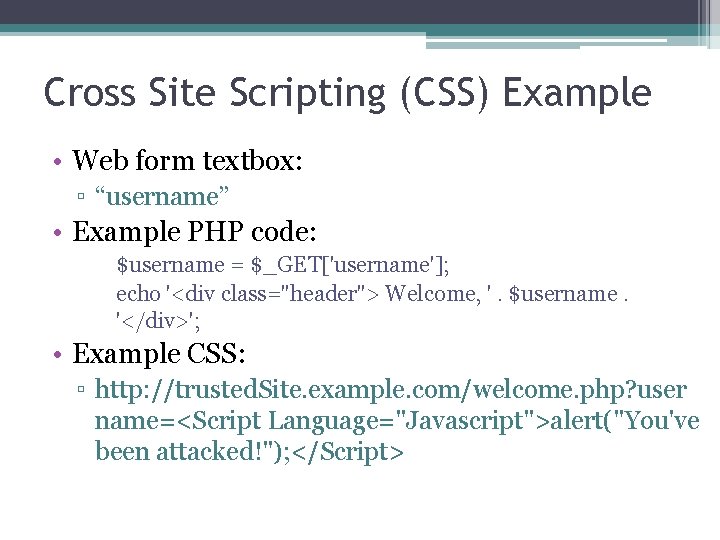
Cross Site Scripting (CSS) Example • Web form textbox: ▫ “username” • Example PHP code: $username = $_GET['username']; echo '<div class="header"> Welcome, '. $username. '</div>'; • Example CSS: ▫ http: //trusted. Site. example. com/welcome. php? user name=<Script Language="Javascript">alert("You've been attacked!"); </Script>
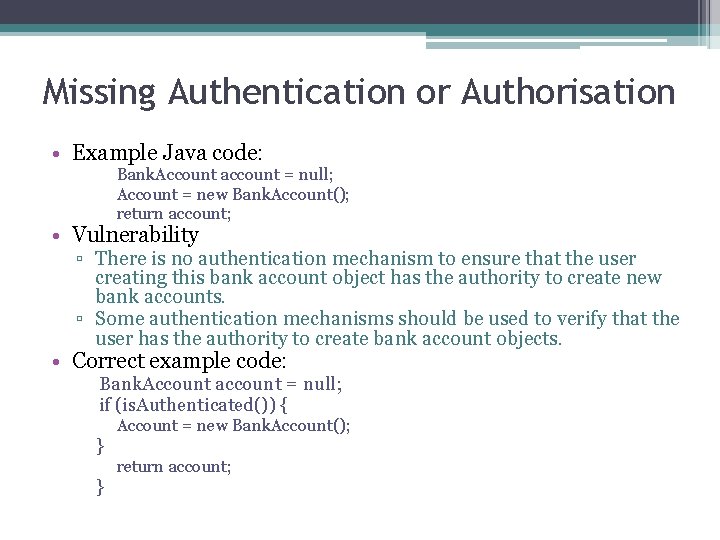
Missing Authentication or Authorisation • Example Java code: Bank. Account account = null; Account = new Bank. Account(); return account; • Vulnerability ▫ There is no authentication mechanism to ensure that the user creating this bank account object has the authority to create new bank accounts. ▫ Some authentication mechanisms should be used to verify that the user has the authority to create bank account objects. • Correct example code: Bank. Account account = null; if (is. Authenticated()) { } } Account = new Bank. Account(); return account;
Further Reading • “ 2011 CWE/SANS Top 25 Most Dangerous Software Errors” ▫ http: //cwe. mitre. org/top 25/
- Slides: 11