Software as a ServiceSaa S Public Cloud AWS
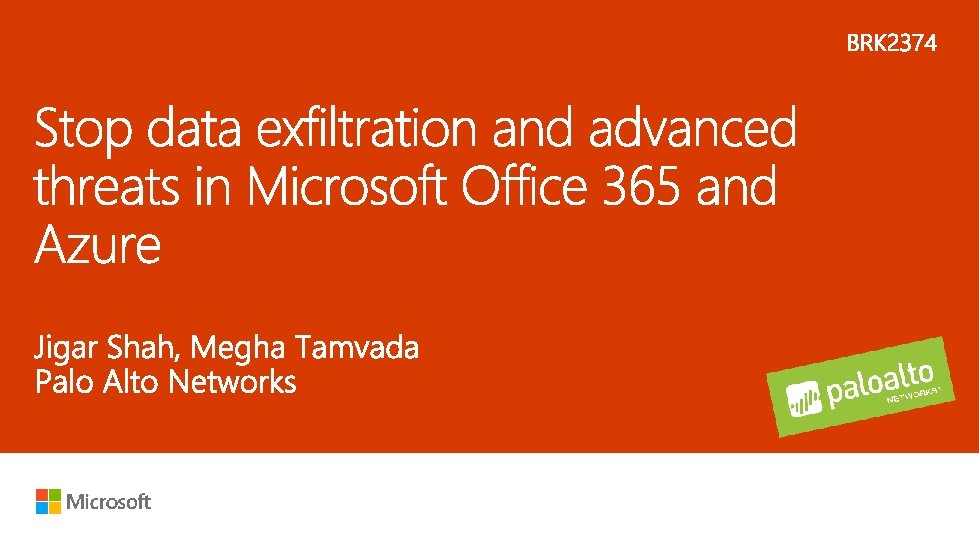
Software as a Service(Saa. S) Public Cloud (AWS, Azure) Private Cloud (Hyper-V, NSX, KVM, Open. Stack)

MALICIOUS OUTSIDER ACCIDENTAL DATA EXPOSURE MALICIOUS INSIDER 59% 23% 14% SOURCE OF BREACH DATA – 2013 -2017 – breachlevelindex. com
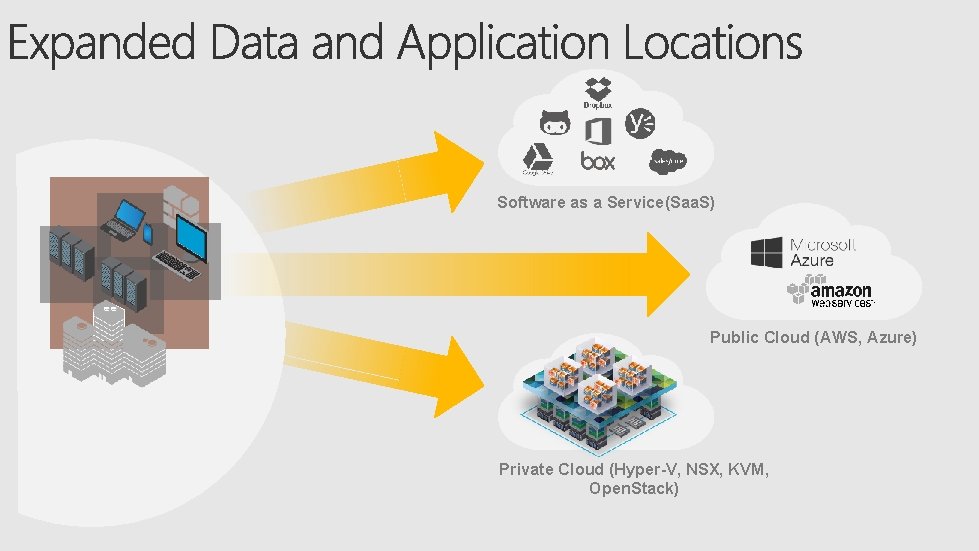
INFECT USER/WORKLOAD MOVE ACROSS THE NETWORK INFECT THE DATA CENTER or EXPLOIT KIT $ CREDENTIAL THEFT, PHISHING ADVERSARY COMMANDS STEAL BUILD DATA BOTNETS HARVEST BITCOIN

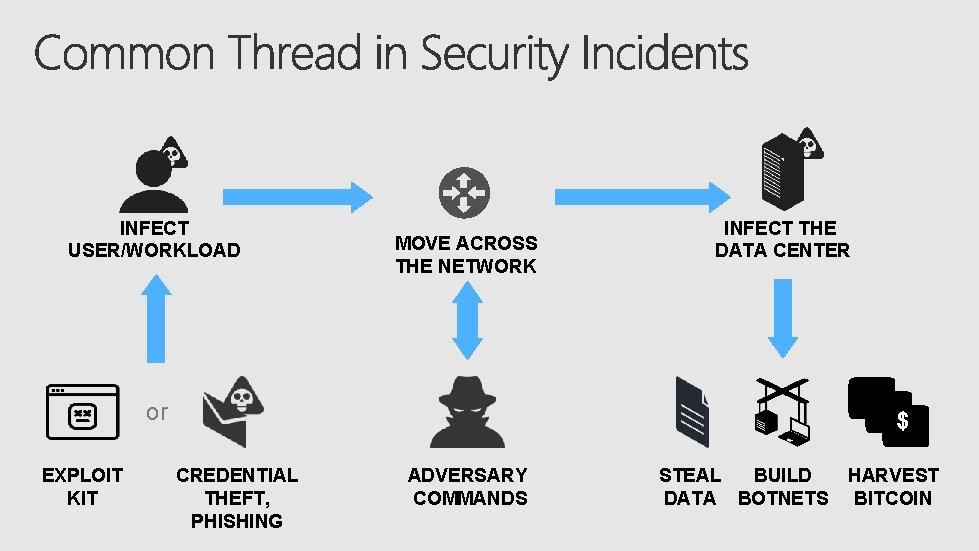
• • All applications All users All content Encrypted traffic Saa. S Cloud Mobile • Enable business apps • Block “bad” apps • Limit app functions • Limit file types • Block websites • Exploits • Malware • Command & control • Malicious websites • Bad domains • Stolen credentials • Dynamic analysis • Static analysis • Attack techniques • Anomaly detection • Analytics
Azure AWS NSX KVM ESXi Hyper-V Consistent security across the organization Diversity of clouds Cloud scalability Operational/ orchestration integration


Segmentation (subnet, VNET, resource group) Improved security and compliance Inspect all traffic Visibility and control Whitelist applications Control Restrict destinations (east-west, north-south) Block C 2, prevent exfiltration and attacks Scale out Elastic, cloud-friendly architectures

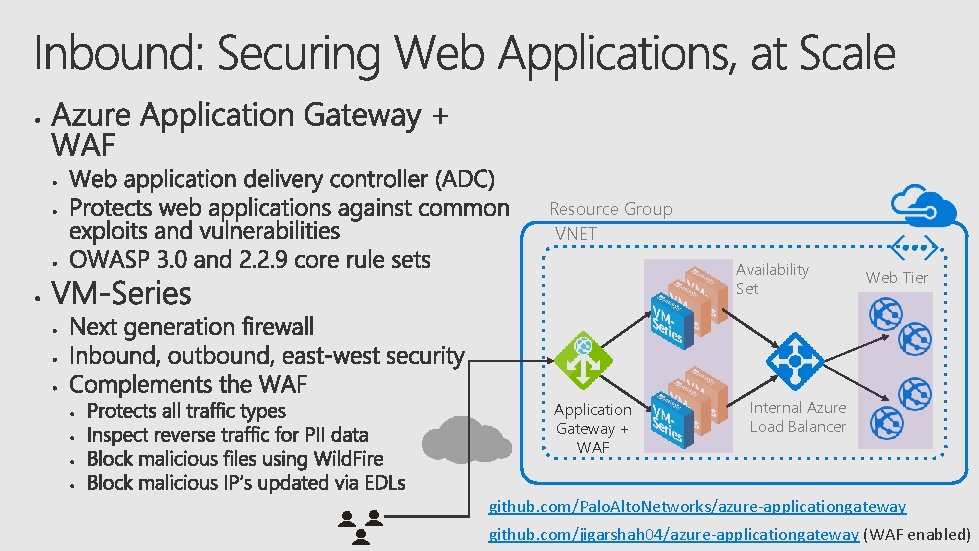
Resource Group VNET Availability Set Application Gateway + WAF Web Tier Internal Azure Load Balancer github. com/Palo. Alto. Networks/azure-applicationgateway github. com/jigarshah 04/azure-applicationgateway (WAF enabled)
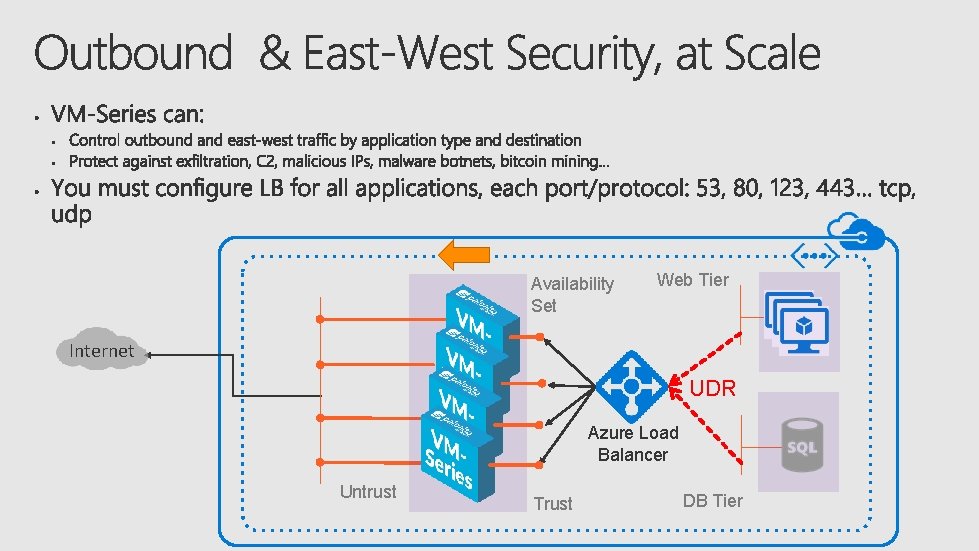
Availability Set Web Tier Internet UDR Azure Load Balancer Untrust Trust DB Tier
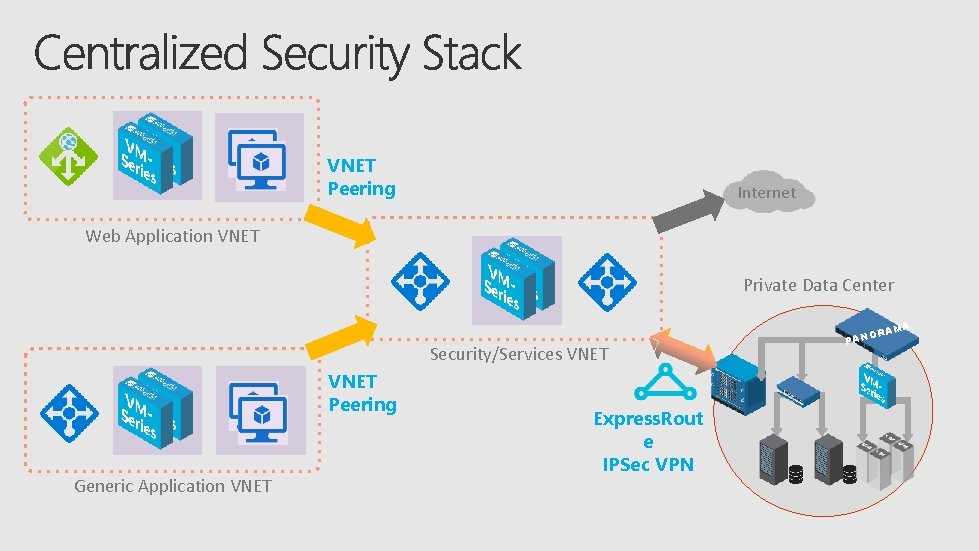
VNET Peering Internet Web Application VNET Private Data Center A RAM Security/Services VNET Peering Generic Application VNET Express. Rout e IPSec VPN O PAN
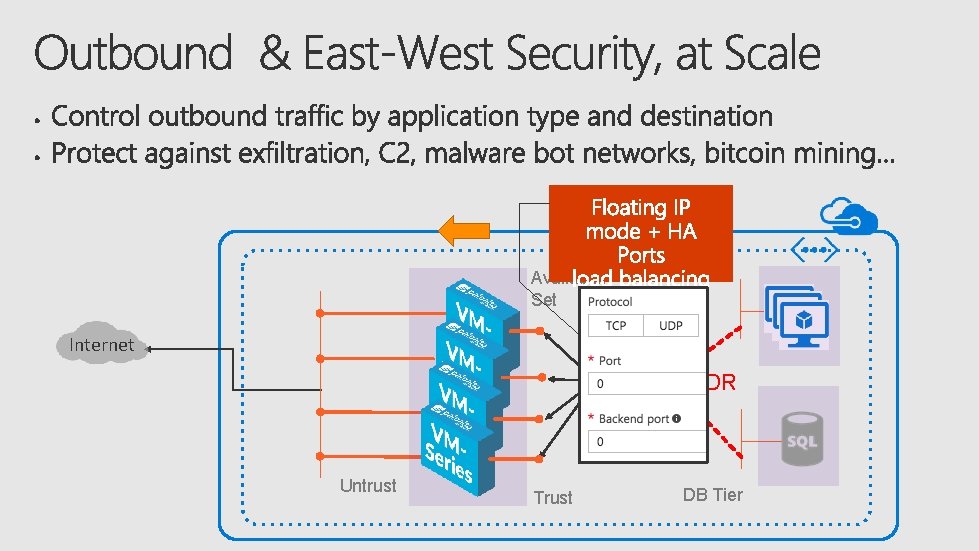
Availability Set Web Tier Internet UDR Azure Load Balancer Untrust Trust DB Tier



VNET Peering Internet Web Application VNET Private Data Center A RAM Security/Services VNET Peering Generic Application VNET Express. Rout e IPSec VPN O PAN
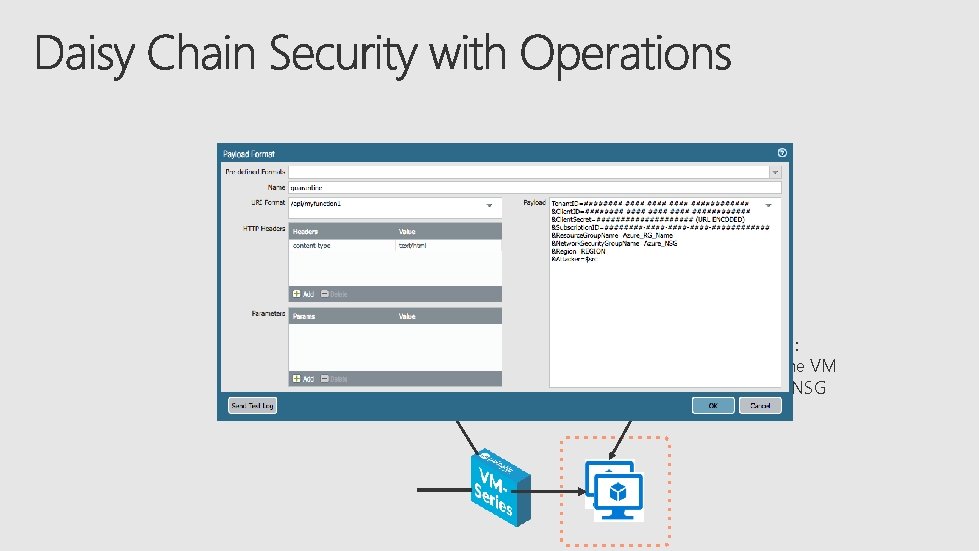
Found a critical threat in logs: Trigger an Azure Function Make an API call to VMSeries Enable: Action-Oriented Log Forwarding in VM-Series Azure API call: Quarantine the VM Close off the NSG
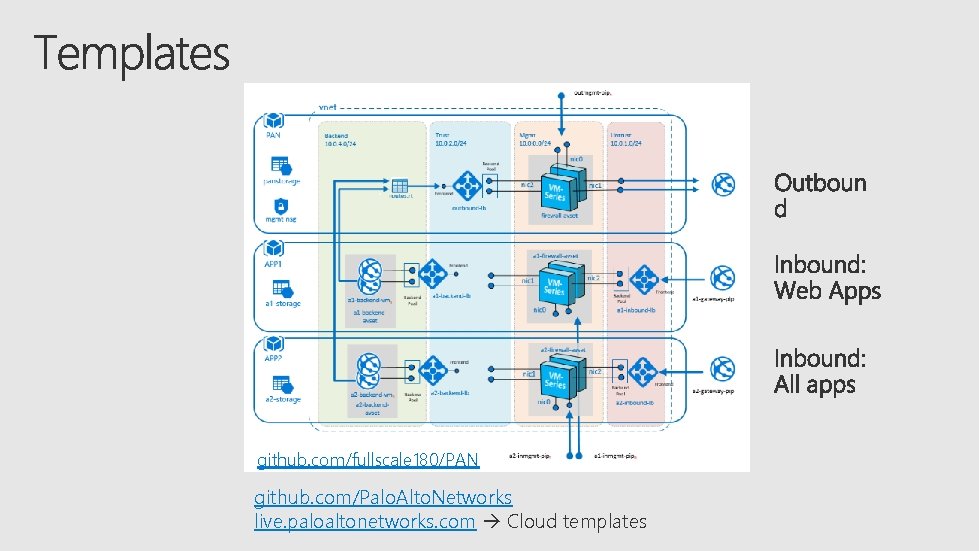
github. com/fullscale 180/PAN github. com/Palo. Alto. Networks live. paloaltonetworks. com Cloud templates

Software as a Service(Saa. S) Public Cloud (AWS, Azure) Private Cloud (NSX, Open. Stack)
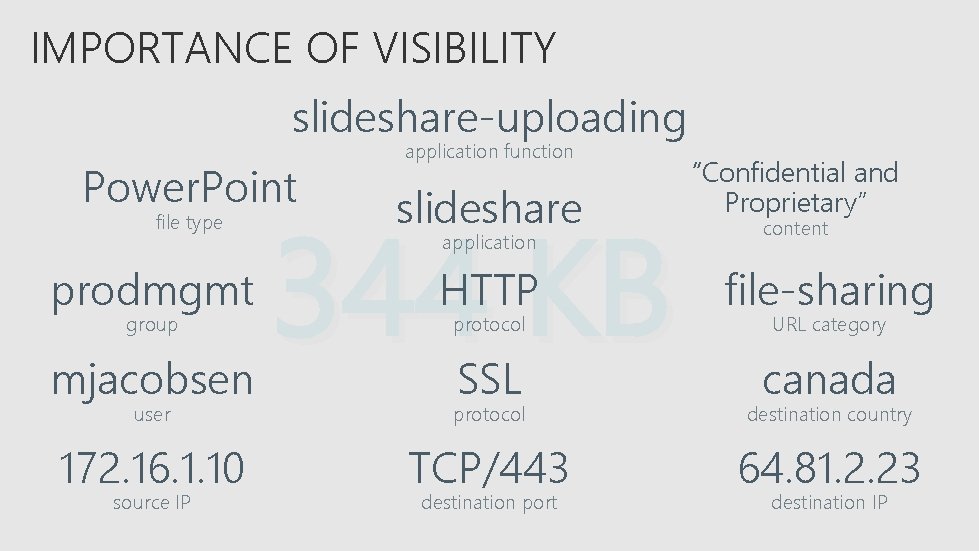
IMPORTANCE OF VISIBILITY slideshare-uploading Power. Point file type prodmgmt group mjacobsen application function slideshare 344 KB application “Confidential and Proprietary” content HTTP file-sharing SSL canada protocol URL category user protocol destination country 172. 16. 1. 10 TCP/443 64. 81. 2. 23 source IP destination port destination IP
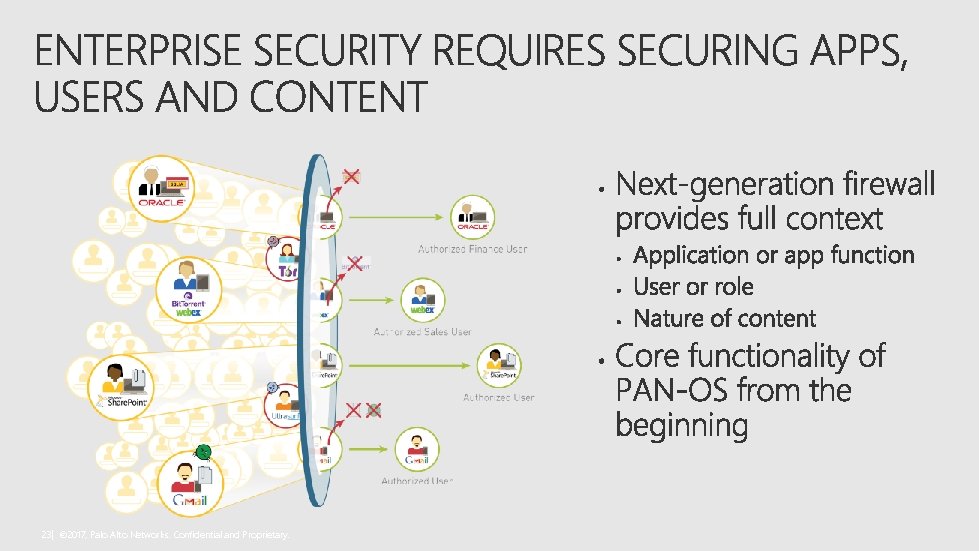
23| © 2017, Palo Alto Networks. Confidential and Proprietary.
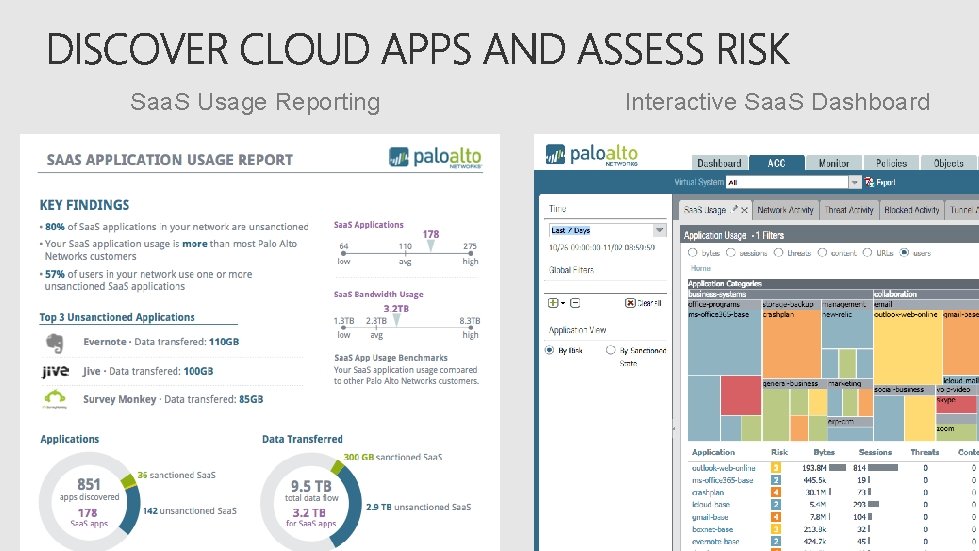
Saa. S Usage Reporting Interactive Saa. S Dashboard
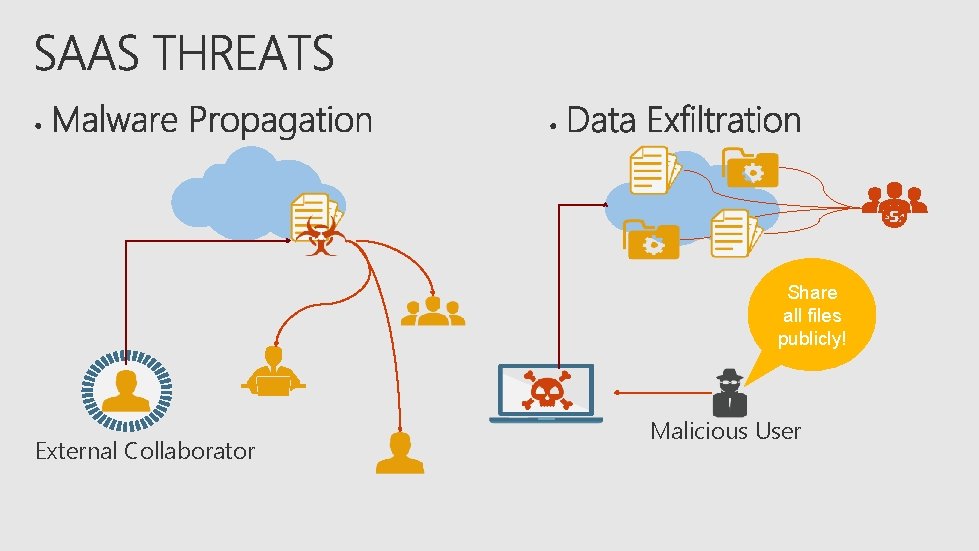
Share all files publicly! External Collaborator Malicious User
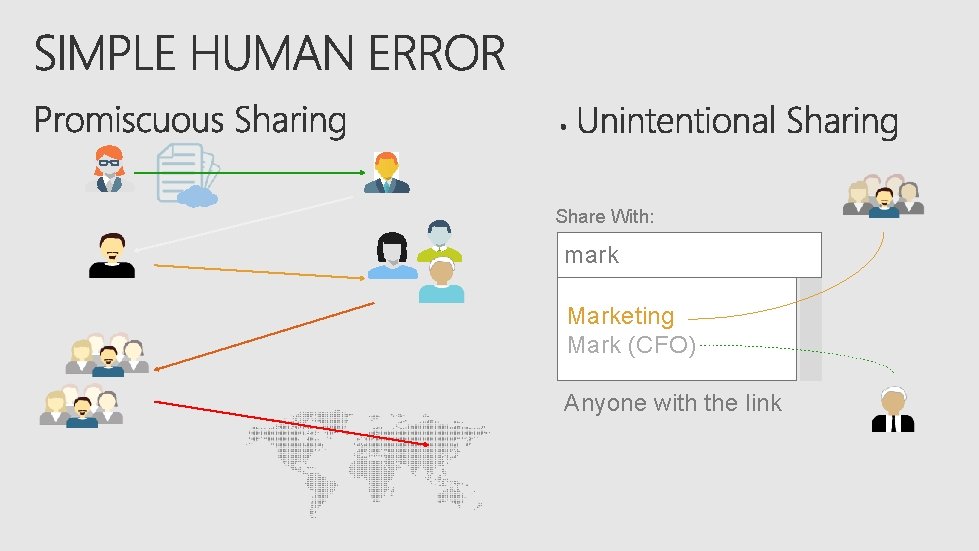
Share With: mark Marketing Mark (CFO) Anyone with the link


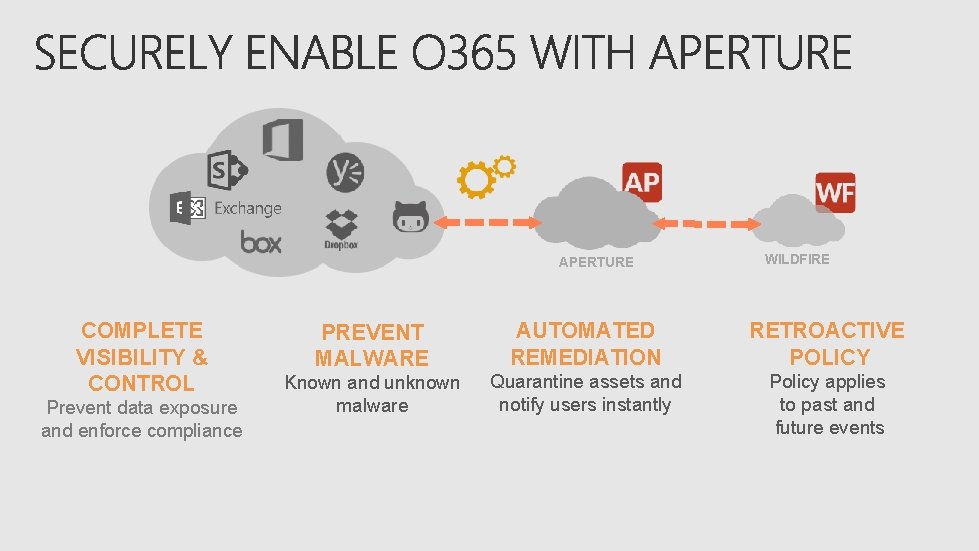
APERTURE COMPLETE VISIBILITY & CONTROL Prevent data exposure and enforce compliance WILDFIRE PREVENT MALWARE AUTOMATED REMEDIATION RETROACTIVE POLICY Known and unknown malware Quarantine assets and notify users instantly Policy applies to past and future events
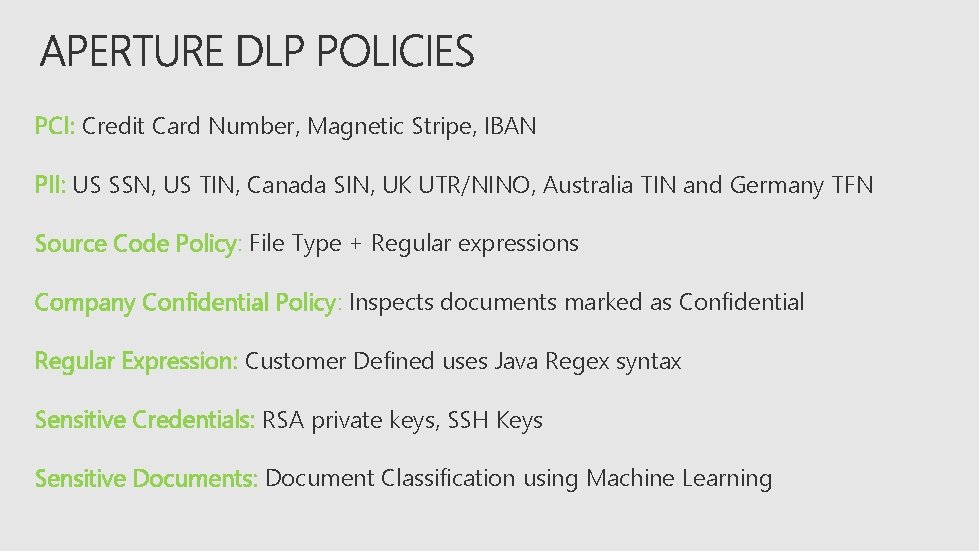
PCI: Credit Card Number, Magnetic Stripe, IBAN PII: US SSN, US TIN, Canada SIN, UK UTR/NINO, Australia TIN and Germany TFN Source Code Policy: File Type + Regular expressions Company Confidential Policy: Inspects documents marked as Confidential Regular Expression: Customer Defined uses Java Regex syntax Sensitive Credentials: RSA private keys, SSH Keys Sensitive Documents: Document Classification using Machine Learning
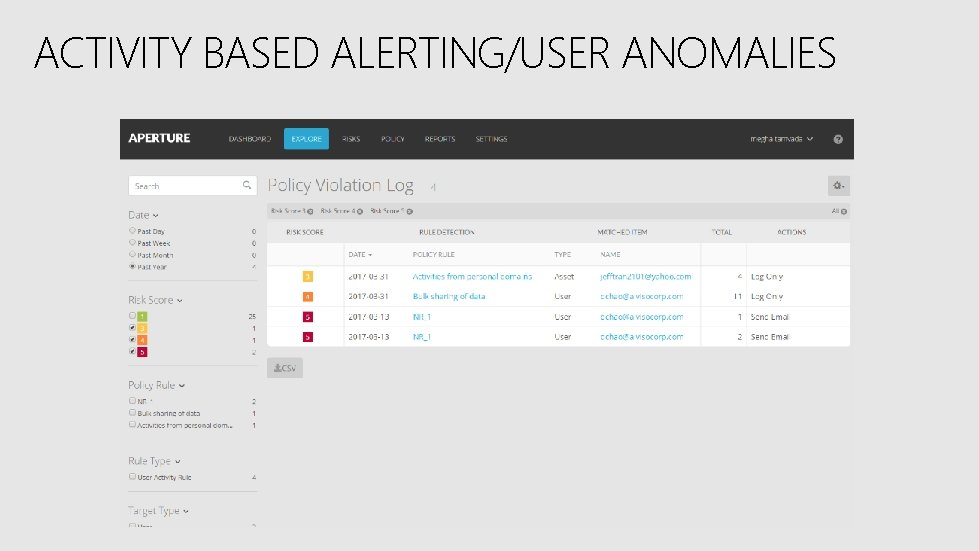
ACTIVITY BASED ALERTING/USER ANOMALIES

• Share. Point and One. Drive • Exchange Online • Yammer
APERTURE Email Security Threat Prevention and DLP 0 -Day Malware detection tied to Wild. Fire Detection of sensitive content and exposure Activity monitoring and anomalies Email Controls Monitoring THREAT INTELLIGENCE CLOUD
• Protect against Data exfiltration • Detection of sensitive content • Activity monitoring and anomalies • Monitor Share. Point Sites • Users One. Drive Folders • Remediate accidental exposure • Stop Malware Propagation • Detect Malware • Quarantine APERTURE THREAT INTELLIGENCE CLOUD
APERTURE • Protect against Data exfiltration • Detection of sensitive content • Yammer Networks • Remediate accidental exposure • Stop Malware Propagation • Detect Malware THREAT INTELLIGENCE CLOUD
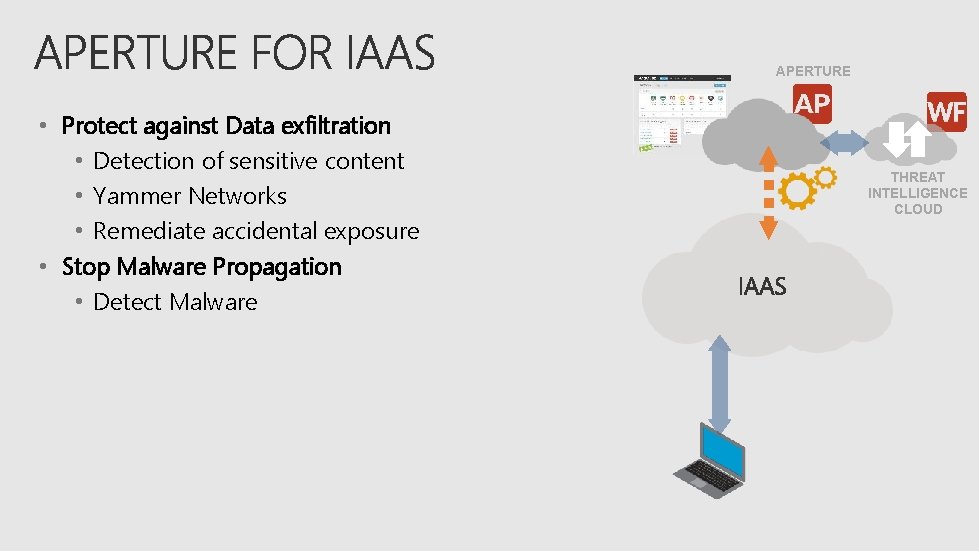
APERTURE • Protect against Data exfiltration • Detection of sensitive content • Yammer Networks • Remediate accidental exposure • Stop Malware Propagation • Detect Malware THREAT INTELLIGENCE CLOUD
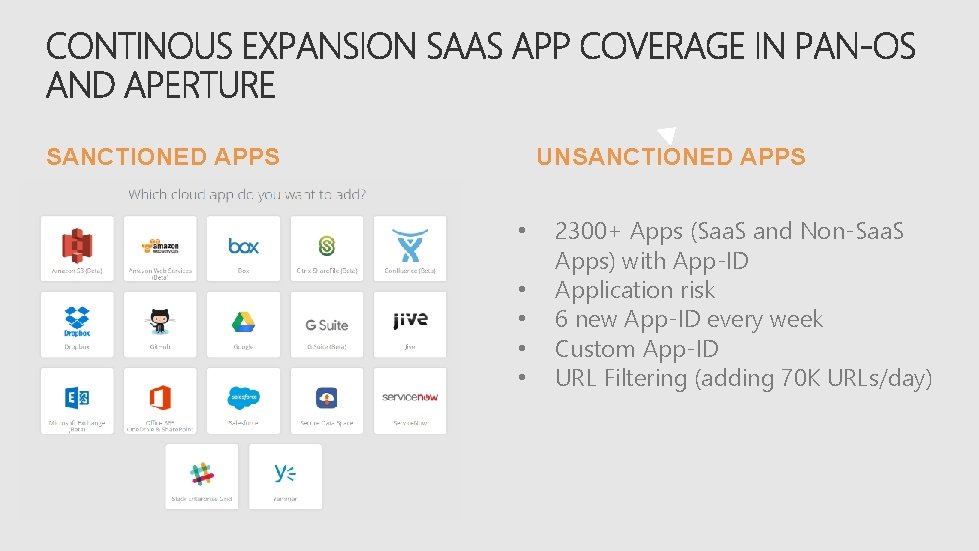
UNSANCTIONED APPS • • • 2300+ Apps (Saa. S and Non-Saa. S Apps) with App-ID Application risk 6 new App-ID every week Custom App-ID URL Filtering (adding 70 K URLs/day)

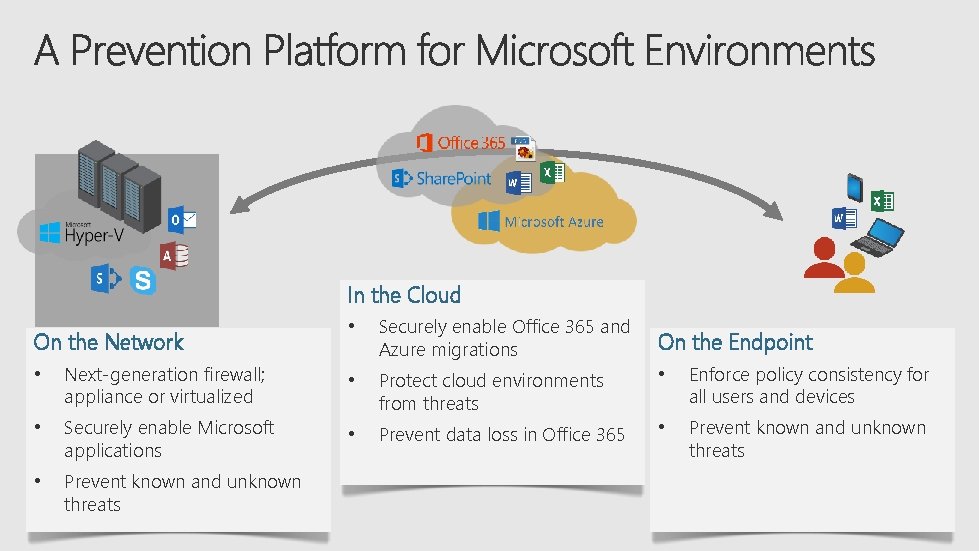
In the Cloud On the Network • Securely enable Office 365 and Azure migrations On the Endpoint • Next-generation firewall; appliance or virtualized • • Enforce policy consistency for all users and devices • Securely enable Microsoft applications Protect cloud environments from threats • Prevent data loss in Office 365 • Prevent known and unknown threats
https: //myignite. microsoft. com/evaluations https: //aka. ms/ignite. mobileapp

- Slides: 42