Society of Risk Management Consultants Annual Conference October
Society of Risk Management Consultants Annual Conference October 17, 2013 Text Goes Here 00/00/00 Presented by: Kurtis E. Suhs, Vice President National Practice Leader for Privacy and Technology Kurtis. Suhs@Ironshore. com / (404) 845 -7549 www. Ironshore. com
The Underwriting Process Non-binding indication Consultative discussion with Risk Management, Information Security, Human Resource, Records Management and Company Underwriter Formal quote Premiums based upon the following: Annual revenue of applicant Industry class Type of coverage Limits, sub-limits, retentions, terms and conditions Risk profile 2
Privacy and Network Security Coverage Third Party Coverage • • • Side A Excess D&O Liability Coverage Network Security Liability Coverage Privacy Liability Coverage Regulatory Proceeding Coverage Internet Media Liability Coverage First Party Coverage • • • Digital Asset Loss Coverage Business Interruption Loss and Dependent Business Interruption Income Loss Coverage Network Extortion Threat and Reward Payments Coverage • Privacy Breach Expenses Coverage 3
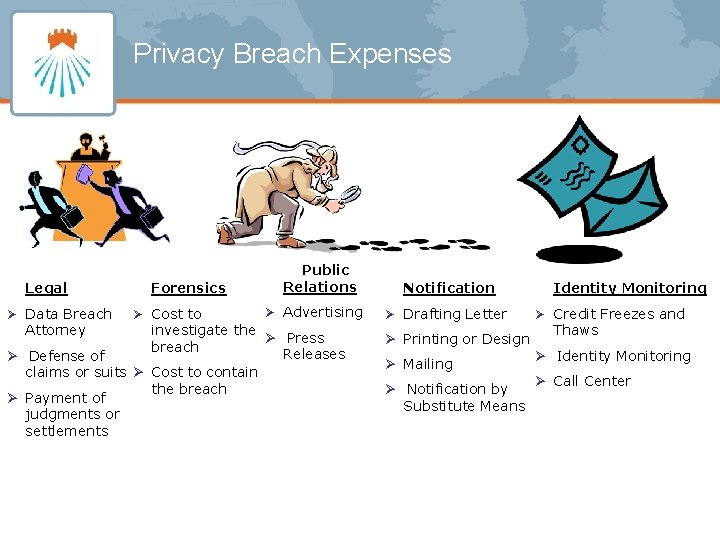
Privacy Breach Expenses Legal Ø Data Breach Attorney Forensics Ø Cost to Public Relations Ø Advertising investigate the Ø Press breach Releases Ø Defense of claims or suits Ø Cost to contain the breach Ø Payment of judgments or settlements Notification Ø Drafting Letter Ø Printing or Design Ø Mailing Ø Notification by Substitute Means Identity Monitoring Ø Credit Freezes and Thaws Ø Identity Monitoring Ø Call Center

Pre-Loss Control Services 5
Key Terms and Conditions Ø Separate Network Security and Privacy Liability coverage grant; Ø Privacy coverage includes non-public personal information and confidential corporate information in any format; Ø PII not defined as Last Name, First Name in combination with SS# etc. Ø Identity Monitoring versus Credit Monitoring Ø Regulatory Proceedings Coverage extends to both Privacy and Network Security; Ø Privacy breach expenses including notification, legal, public relations, forensics, identity monitoring and call center services; Ø Coverage for the insured’s liability arising from the actions of independent contractors and third party service providers; Ø Severability of application for individual insured persons, with only the knowledge of specified executives imputed to other insureds; Ø Carve backs in exclusion such as Dishonesty, Insured versus Insured, ERISA and EPLI. 6
Losses in the marketplace Health. Net $10 M limit with a $1 M SIR for $485 K in premium March 2011 - Nine unaccounted server drives with personal information for 24, 599 CT residents $6. 6 M total incurred. TRICARE/ SAIC $15 M limit. Premium unknown. Open Claim September 2011 – Theft of unencrypted back up tapes containing information on 4. 9 M TRICARE members stolen from the car of an SAIC employee. Eight class actions filed demanding $4 B against TRICARE and SAIC. Heartland Payment Systems $20 M limit with a $1 M SIR. Premium unknown May 2008– Third party hacker gains access to 130 million credit and debit card accounts. Full limit loss. 7
Losses in the marketplace Steven Hutchins Architects, Inc. No cyber coverage in force. January 2008 – Office Manager destroys 7 years’ worth of architectural drawings and blueprints estimated at $2. 5 M in value. Aereo $1 M limit with a $50 K SIR for $14 K in premium. March 2012 – Start-up company that streams the broadcast of television through a browser and DVR in the cloud is sued by several networks for copyright infringement. Full limit loss. Strategic Forecasting No cyber coverage in force. December 2011 – Third party hacker gain s access to 75 K credit cards, 860 K passwords and 5 million emails. In June 2012, Stratfor settled a class action lawsuit for $1. 75 M 8
Questions 9
- Slides: 9