Social Networking Risks and realities Nick Barron nick
Social Networking: Risks and realities Nick Barron nick. barron@pennantplc. co. uk
Who am I? • Day job – Employed by Pennant Plc www. pennantplc. co. uk – Head of Group IT, Security controller, software developer • Meanwhile. . . – Freelance security consultant/researcher – SC magazine columnist – IT advisor to DISA • Disclaimers – Views expressed are my own, not those of my employer – Don’t try this at work without consent – Check legal aspects 2
What am I talking about? • What information can be obtained from online social networks? • How can it be (ab)used? • What can you do to address the risks • Focus on corporate liabilities/risks • Mainly about risks of online social networks, but many apply equally to old fashioned ones too! 3
The usual suspects 4
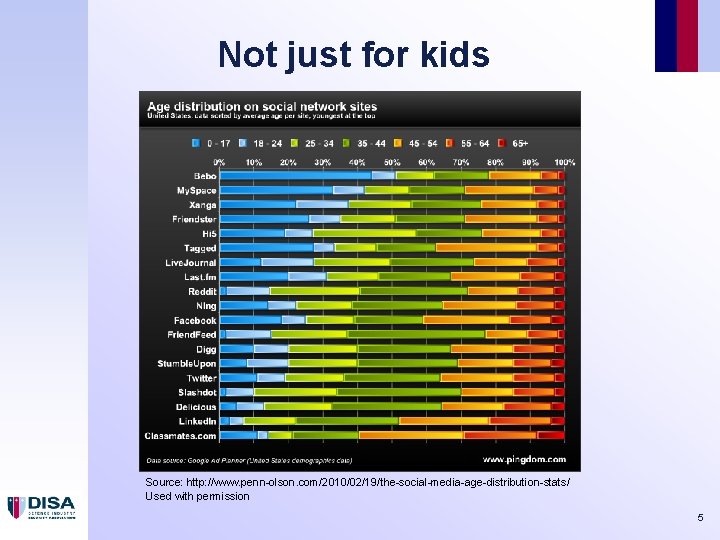
Not just for kids Source: http: //www. penn-olson. com/2010/02/19/the-social-media-age-distribution-stats/ Used with permission 5
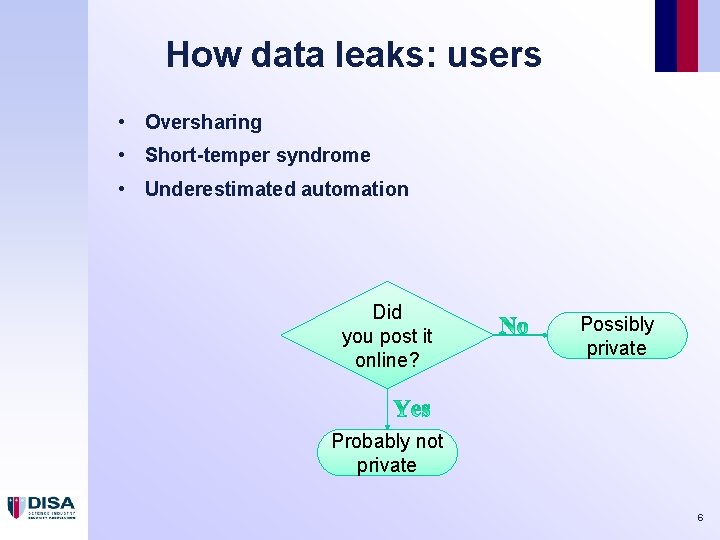
How data leaks: users • Oversharing • Short-temper syndrome • Underestimated automation Did you post it online? Possibly private Probably not private 6
How data leaks: hacks 7
How data leaks: loose lips 8
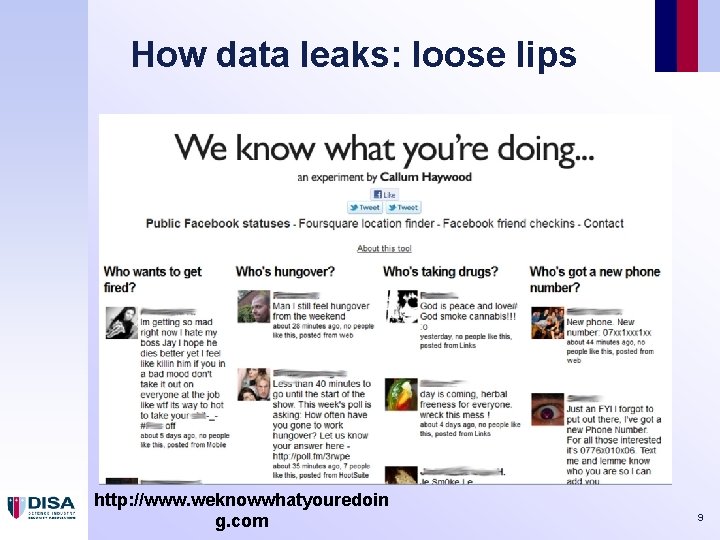
How data leaks: loose lips http: //www. weknowwhatyouredoin g. com 9
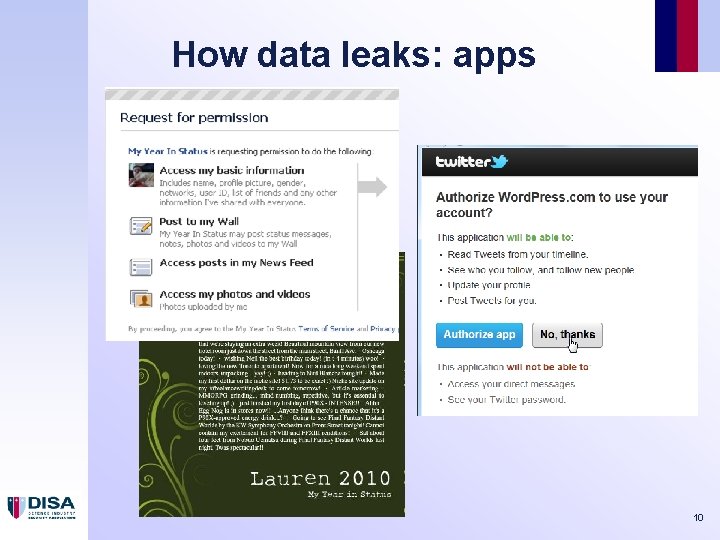
How data leaks: apps 10
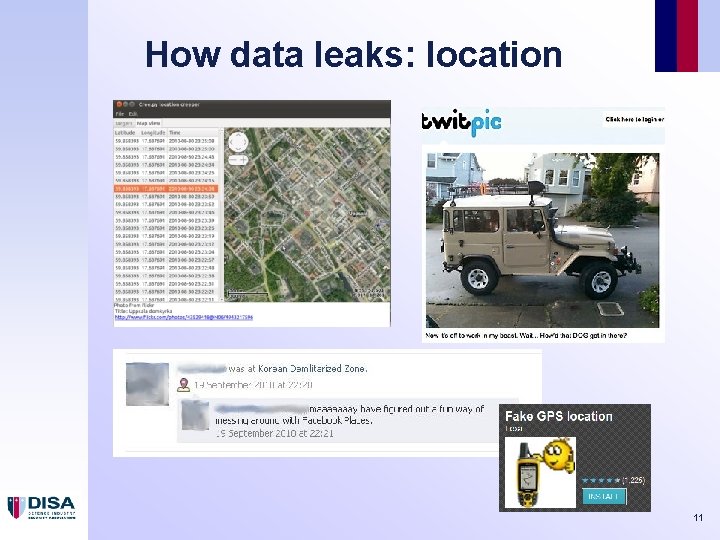
How data leaks: location 11
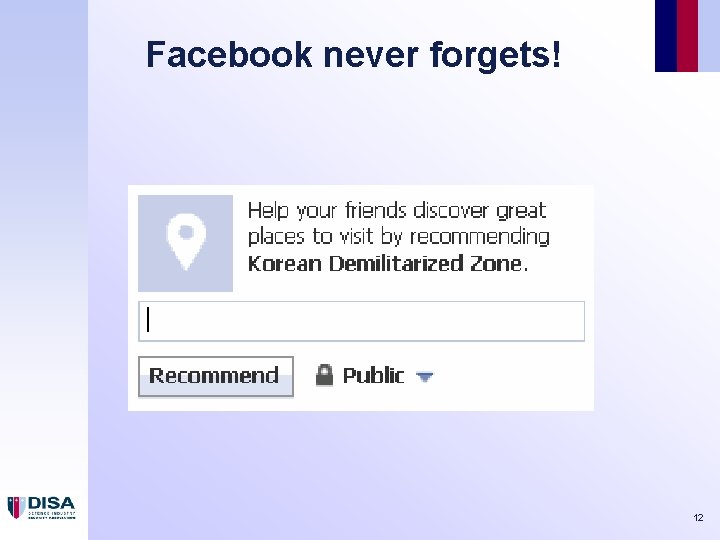
Facebook never forgets! 12
Feature creep 13

Risks are real… http: //news. bbc. co. uk/1/hi/8134807. stm 14

Risks are real… (2) https: //www. zdnet. com/blog/facebook/chinese-spies-used-fake-facebook-profile-to-friendnato-officials/10389 15
Risks are real (3) 16
Risks are real (4) 17
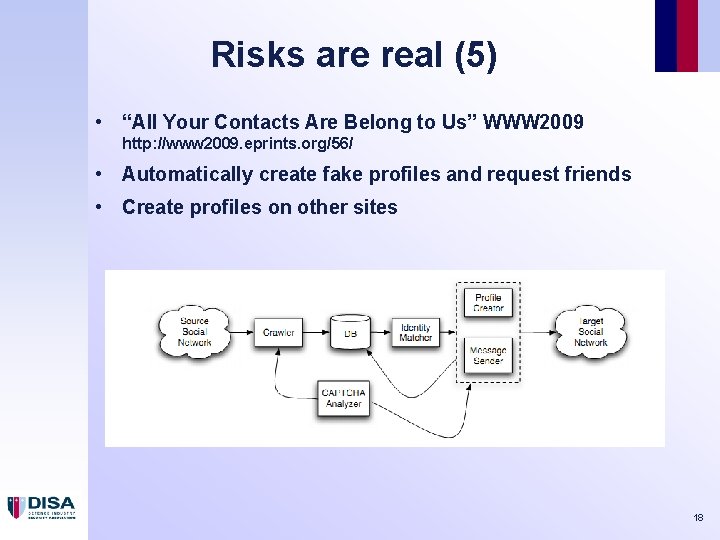
Risks are real (5) • “All Your Contacts Are Belong to Us” WWW 2009 http: //www 2009. eprints. org/56/ • Automatically create fake profiles and request friends • Create profiles on other sites 18
Risks are real (6) http: //thecaucus. blogs. nytimes. com/2009/02/09/in-iraq-to-twitter-or-notto-twitter/ 19

Who cares? 20
Using the data (1) 21
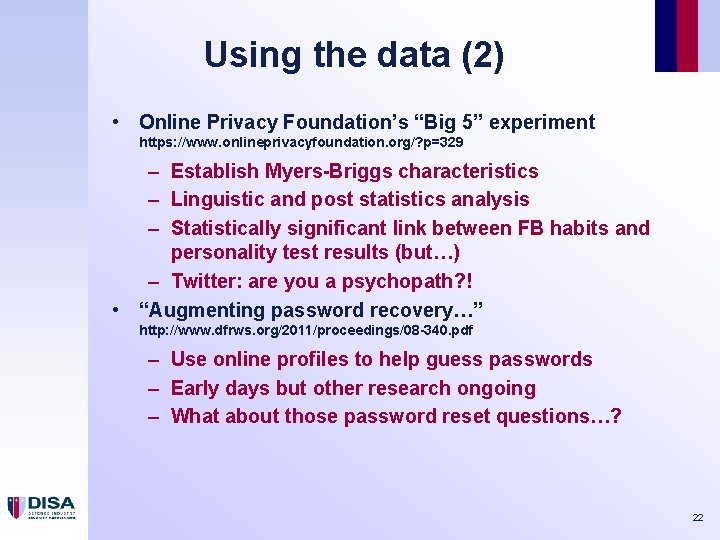
Using the data (2) • Online Privacy Foundation’s “Big 5” experiment https: //www. onlineprivacyfoundation. org/? p=329 – Establish Myers-Briggs characteristics – Linguistic and post statistics analysis – Statistically significant link between FB habits and personality test results (but…) – Twitter: are you a psychopath? ! • “Augmenting password recovery…” http: //www. dfrws. org/2011/proceedings/08 -340. pdf – Use online profiles to help guess passwords – Early days but other research ongoing – What about those password reset questions…? 22
Using the data (3) • Facebook analysis to determine Nigerian scammers http: //preview. tinyurl. com/specops-paper (PDF) http: //preview. tinyurl. com/specops-vid (video) 23
Sanity check • Your employees will use Facebook etc – Even if blocked at work – Use takes place outside corporate network perimeter • Social network users are not customers, they are product • It is not in social network vendors’ commercial interests to make your privacy a priority – Long record of truly awful security – Commercialisation is an incentive for more intrusion 24
Defences 25
Guidance http: //www. cpni. gov. uk/documents/publications/2010032 -gpg_online_social_networking. pdf http: //preview. tinyurl. com/gpg 27 26
Guidance (2) http: //preview. tinyurl. com/sophossmt 27
Countermeasures • Education, educations – Most users don’t actually want to breach privacy – Usually unaware of how much is available – Better privacy awareness increases personal security as well as business security Used with kind permission of Scott Hampson, www. agent-x. com. au 28
Countermeasures (2) • Snoop yourself (Google, Node. XL, Maltego etc) • Check exposure of key staff • Include social networks in scope for penetration tests (but check with ethics/legal departments) 29
Countermeasures (3) • Blur data where possible – Your friends will already know most of the useful info – Minimise what goes into profile – Seed a few bogus “facts” – Turn off location features – Check password reset policies • But…. – Not having DOB no help when people say “Happy Birthday” on your Facebook wall! – May be breach of terms of service to lie 30
Countermeasures (4) • Weed old accounts – Friends. Reunited, My. Space etc • Compartmentation where possible – Facebook for home stuff – Linked. In for business – Flickr for pictures • Email – Avoid the use of corporate mail addresses for social networking sites – High value targets should consider use different email addresses 31
Countermeasures (5) • “Placeholder” profiles on unused systems • Look at ‘privacy’ settings – KISS, don’t have too many options – Assume privacy controls will fail, and consider impact – If in doubt, don’t post Used with kind permission of Scott Hampson, www. agent-x. com. au 32
Summary • Online social networks are not going away any time soon • There are real benefits to their use for many staff • OSN vendors cannot be trusted to implement strong security • Education and defensive monitoring are the best protections • The risks apply to non-electronic social networks as well! 33

Links… • www. 44 con. com (Sept 2012, lots of business level info too) • www. agent-x. com. au for great cartoons! • www. securityg 33 k. com • www. facecrooks. com • www. onlineprivacyfoundation. org • harmonyguy. com • www. social-engineer. org • nodexl. codeplex. com (free Excel plugin for social network analysis) • www. paterva. com (industry standard tool for network analysis) 34
Questions? 35
- Slides: 35