Social Ethical and Legal Issues in Technology Betsy
Social, Ethical, and Legal Issues in Technology Betsy Bitson

Social Issues • Digital Divide • Cyberbullying • Online social interaction
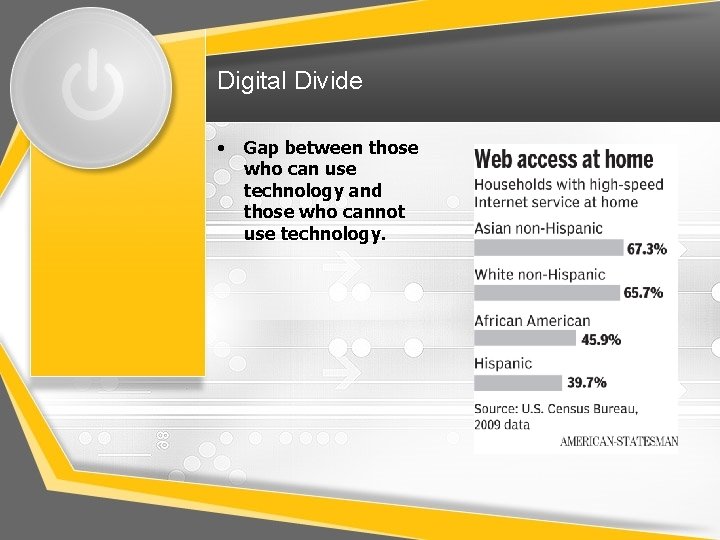
Digital Divide • Gap between those who can use technology and those who cannot use technology.
Cyberbullying • • Other people attack others over the internet verbally or through some visual aid Can lead to children or teens committing suicide
Social Interactions • • • Search Engines like Google, Yahoo, MSN, Bing, etc. Chat rooms Dating websites like e. Harmony Cell phones, i-pad, laptop, mp 3 players, television People can communicate or hang out using any of these options but safety is always a concern.
Ethical Issues • • Freedom of Speech Privacy Academic Dishonesty Plagiarism
Freedom of Speech Social websites are a great way to see the right to speak freely in action.
Privacy • Things are kept between only a certain group or certain amount of people • Ex: Facebook or other internet profiles, doctors files, important documentation for loans or other government paperwork
Academic Dishonesty • • Cheating and plagiarism http: //www. youtube. com/watch? v=LSMo_Ns-FUc http: //www. youtube. com/watch? v=2 q 0 Nl. Wc. Tq 1 Y These can lead to class failures, assignment failures, or even expulsion from the school that the student is attending.
Plagiarism • • Using someone else's work as your own instead of citing it properly. Whenever you use someone else’s work, it always needs to be cited so people know that it is not originally yours. This is just like stealing something that is not yours.
Legal Issues • • Copy right and fair use Privacy Acceptable use Software piracy

Copyright • http: //www. youtube. com/watch? v=Uiq 42 O 6 rh. W 4 • http: //www. loc. gov/teachers/copyrightmyste ry/#/reading/

Fair Use • http: //www. adec. edu/admin/papers/fair 10 -17. html
Privacy • Information is kept secret unless the person who’s information someone wants says that it is ok to release their information.
Acceptable Use • http: //www. youtube. com/watch? v=P 1 wew 3 t 3 SVs
Software Piracy • • Unauthorized copying of software Counterfeit software, OEM unbundling, softlifting, hard disk loading, corporate software piracy, and Internet software piracy
Safety • • If you see any of the activities that have been discussed about through words, videos, or pictures in previous slides, let an adult or appropriate officials know right away. It is important to keep everyone safe and if information leaks out then identity theft becomes a problem, suicide becomes a bigger risk, and losing education increases.
References for pictures • • • http: //www. copyrightblog. com/copyright-attorney. html http: //beyondclause 8. com/articlepost/youtubes-copyright-school/ http: //www. it. ojp. gov/privacy http: //www. statesman. com/news/technology/can-mobile-phonesnarrow-the-digital-divide-1/n. Rt 5 n/ http: //www. dosomething. org/tipsandtools/11 -facts-about-cyberbullying# https: //sts. stanford. edu/news/facebook-u http: //blogs. knoxnews. com/woodbery/2013/01/tennessee-coachesare-on-twitter-but-are-they-doing-their-own-tweeting. html http: //redbus 2 us. com/why-not-to-copy-homework-or-projects-inms-mba-in-us-plagiarism-academic-dishonesty/ http: //socialleena. blogspot. com/2012/07/privacy-is-dead-and-socialmedia-holds. html http: //dramatisdei. com/2011/06/16/acceptable-use/ http: //www. mygca. my/Software_Piracy_is_a_crime. h
- Slides: 18