SOCIAL ENGINEERING Dana Leonard CSPC 620 Overview What
- Slides: 9
SOCIAL ENGINEERING Dana Leonard CSPC 620
Overview What is Social Engineering? Techniques Targets Why does it work? Kevin Mitnick Defenses
What is Social Engineering collection of techniques used to manipulate people into performing actions or divulging confidential information
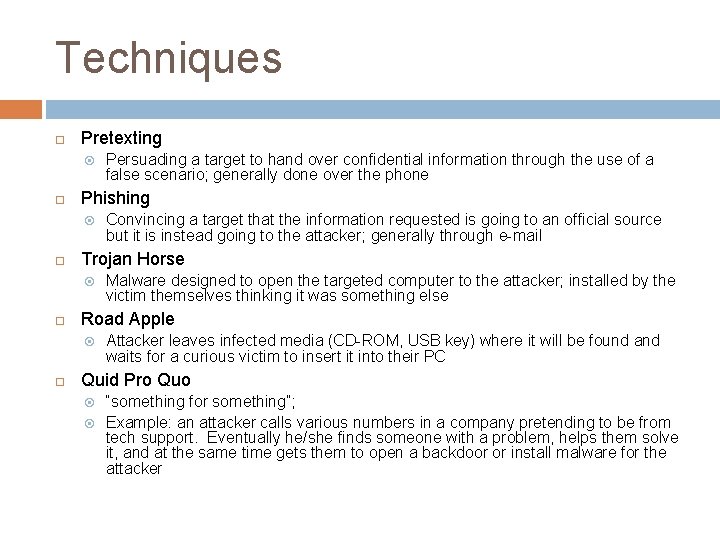
Techniques Pretexting Phishing Malware designed to open the targeted computer to the attacker; installed by the victim themselves thinking it was something else Road Apple Convincing a target that the information requested is going to an official source but it is instead going to the attacker; generally through e-mail Trojan Horse Persuading a target to hand over confidential information through the use of a false scenario; generally done over the phone Attacker leaves infected media (CD-ROM, USB key) where it will be found and waits for a curious victim to insert it into their PC Quid Pro Quo “something for something”; Example: an attacker calls various numbers in a company pretending to be from tech support. Eventually he/she finds someone with a problem, helps them solve it, and at the same time gets them to open a backdoor or install malware for the attacker
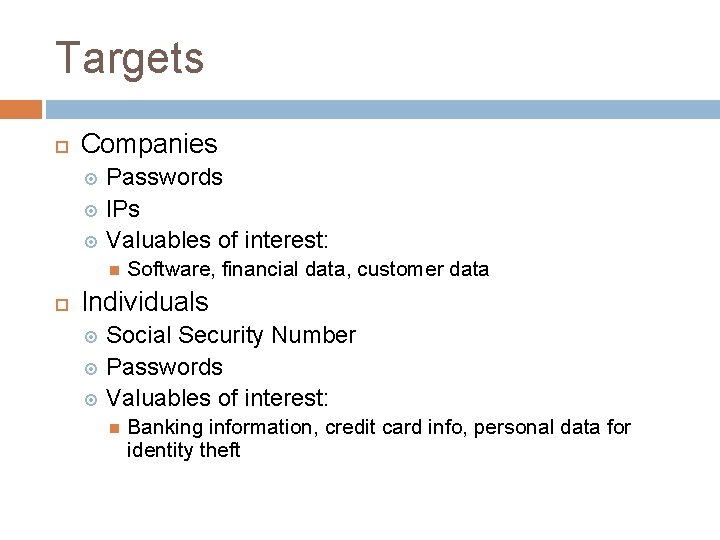
Targets Companies Passwords IPs Valuables of interest: Software, financial data, customer data Individuals Social Security Number Passwords Valuables of interest: Banking information, credit card info, personal data for identity theft
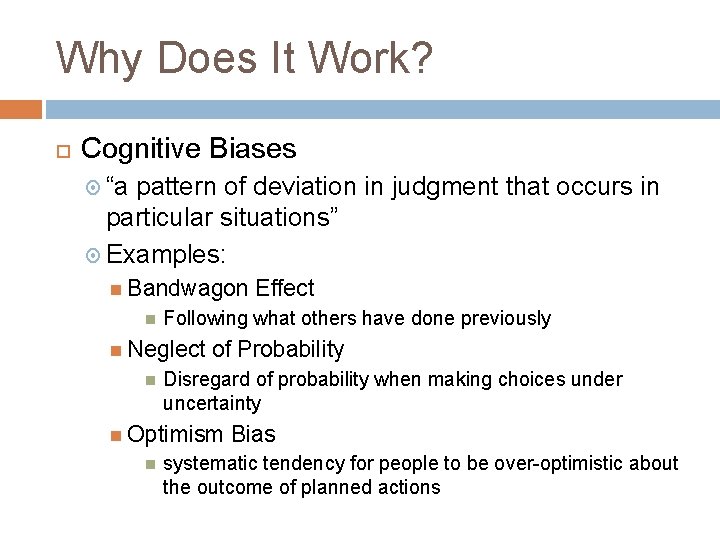
Why Does It Work? Cognitive Biases “a pattern of deviation in judgment that occurs in particular situations” Examples: Bandwagon Following what others have done previously Neglect of Probability Disregard of probability when making choices under uncertainty Optimism Effect Bias systematic tendency for people to be over-optimistic about the outcome of planned actions
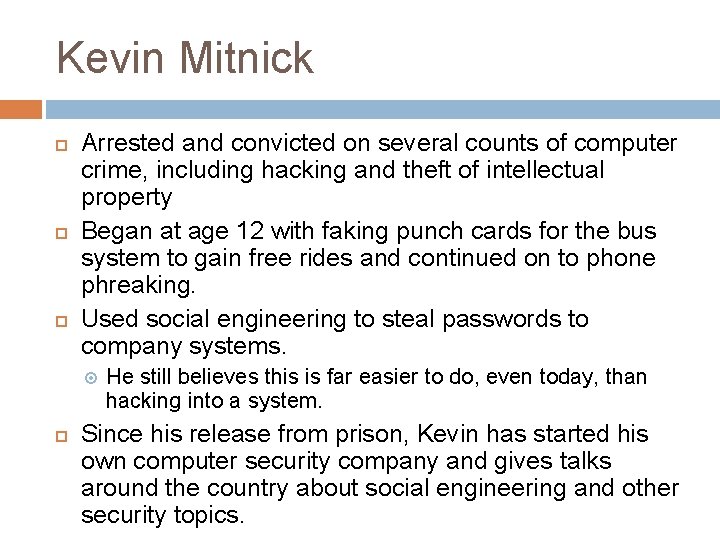
Kevin Mitnick Arrested and convicted on several counts of computer crime, including hacking and theft of intellectual property Began at age 12 with faking punch cards for the bus system to gain free rides and continued on to phone phreaking. Used social engineering to steal passwords to company systems. He still believes this is far easier to do, even today, than hacking into a system. Since his release from prison, Kevin has started his own computer security company and gives talks around the country about social engineering and other security topics.
Defenses Education Speakers like Kevin Mitnick Books like “The Art of Deception” Policies Strict policies at the workplace about divulging information Well known procedures for things like resetting passwords
Questions and Discussion