SNMPv 3 Wes Hardaker Network Associates Laboratories 6
SNMPv 3 Wes Hardaker Network Associates Laboratories 6 August 2002 Wes_Hardaker@nai. com
Overview • About SNMP in General • SNMPv 3 Architecture Breakdown • User Based Security • View Based Access Control • Future of SNMP • Summary & Questions 1 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Author’s Background • Past: – Lead developer of the Net-SNMP open source project – Developer of the Open. SNMP toolkit • Present: – Project lead in a scalable IPSec policy management system build on top of SNMPv 3. • Future: – Participating in various IETF working groups responsible for continuing development of SNMP technologies. • Apologetic: – Not all the slides in this presentation are in your hand out. – http: //www. net-snmp. org/presentations/snmpv 3/ 2 Aug 6, 2002 CERT Conference 2002: SNMPv 3
About SNMP “Simple Network Management Protocol” -- RFC 1157 “SNMP: Can I buy a vowel? ” --Harrie Hazewinkel 3 Aug 6, 2002 CERT Conference 2002: SNMPv 3
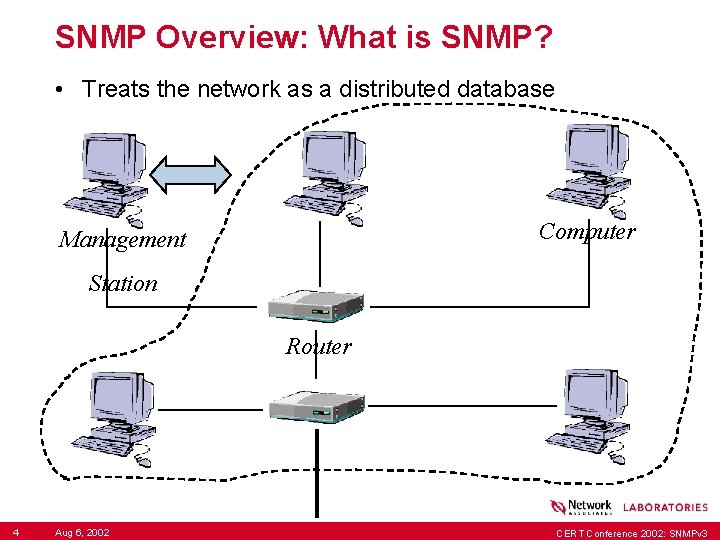
SNMP Overview: What is SNMP? • Treats the network as a distributed database Computer Management Station Router 4 Aug 6, 2002 CERT Conference 2002: SNMPv 3
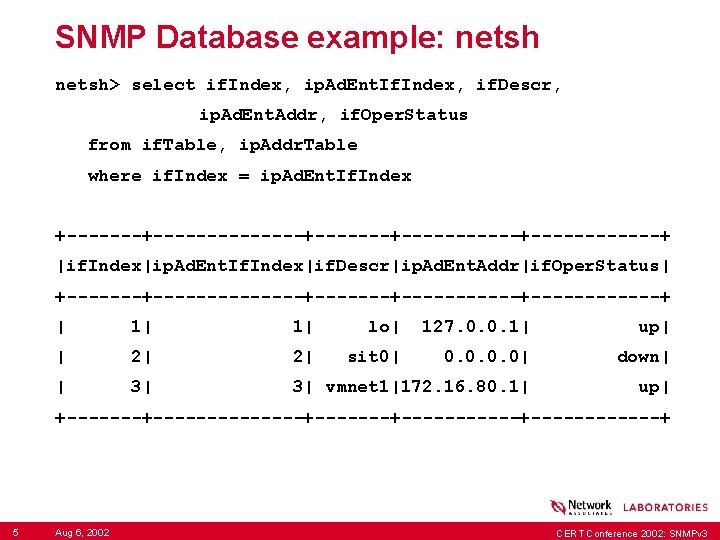
SNMP Database example: netsh> select if. Index, ip. Ad. Ent. If. Index, if. Descr, ip. Ad. Ent. Addr, if. Oper. Status from if. Table, ip. Addr. Table where if. Index = ip. Ad. Ent. If. Index +--------------+------+------+ |if. Index|ip. Ad. Ent. If. Index|if. Descr|ip. Ad. Ent. Addr|if. Oper. Status| +--------------+------+------+ | 1| lo| 127. 0. 0. 1| up| | 2| sit 0| 0. 0| down| | 3| vmnet 1|172. 16. 80. 1| up| +--------------+------+------+ 5 Aug 6, 2002 CERT Conference 2002: SNMPv 3
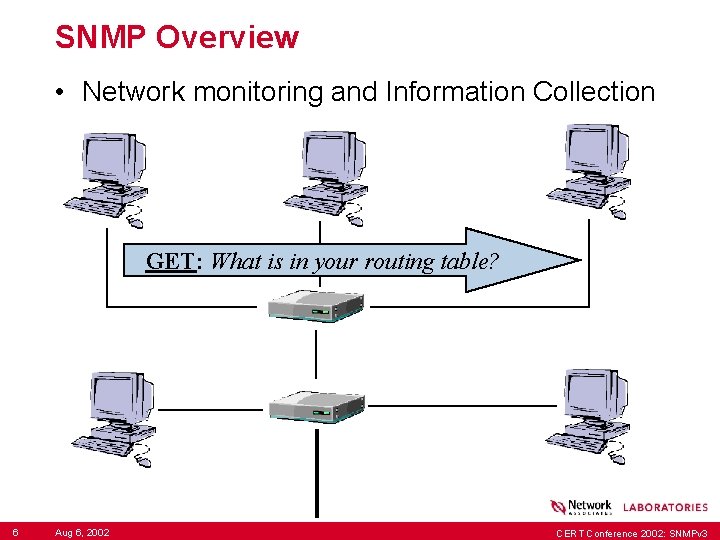
SNMP Overview • Network monitoring and Information Collection GET: What is in your routing table? 6 Aug 6, 2002 CERT Conference 2002: SNMPv 3
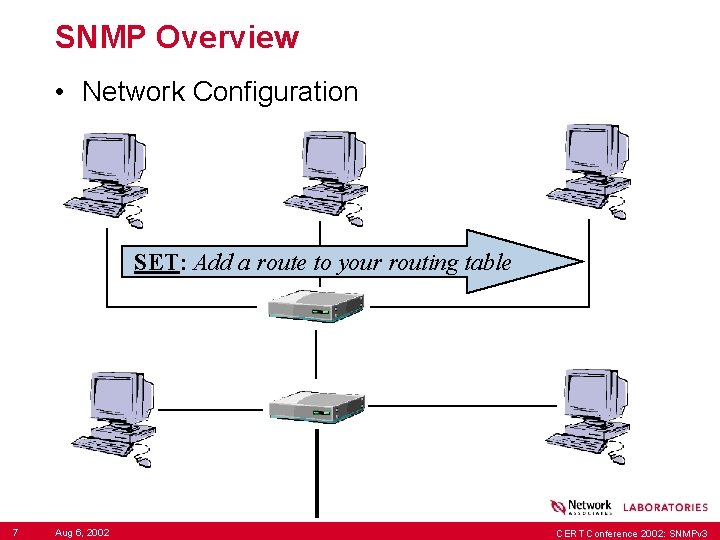
SNMP Overview • Network Configuration SET: Add a route to your routing table 7 Aug 6, 2002 CERT Conference 2002: SNMPv 3
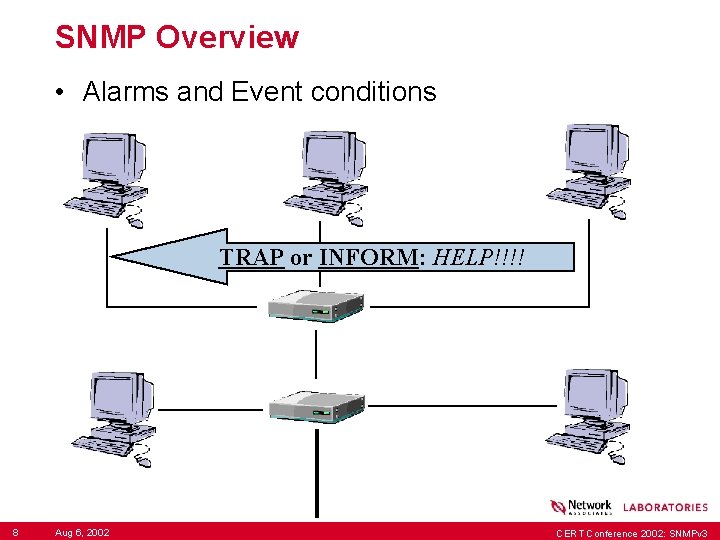
SNMP Overview • Alarms and Event conditions TRAP or INFORM: HELP!!!! 8 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Terminology • SNMP: the protocol itself • MIB: the specification defining a particular piece of data to be transferred over SNMP • SMI: the language a MIB is written in – It is not ASN. 1, contrary to what many people think. • OID / “Object Identifier”: A hierarchical naming scheme using number assignment. –. 1. 3. 6. 1. 2. 1. 1. 4. 0 = You (the system contact for a device) –. iso. org. dod. internet. mgmt. mib-2. system. sys. Contact. 0 9 Aug 6, 2002 CERT Conference 2002: SNMPv 3
SNMP Standards Timeline • SNMPv 1 created in 1988 – Officially a “Full Standard” • SNMPv 2 c added a few things in 1996 – SNMPv 2 c MSG Format classified as experimental – PDUs, etc, classified as a “FULL Standard” • SNMPv 3 added security in 1999 – Currently a “Draft” standard – Approved as a “Full Standard”, but not published yet • SNMPv 2 p, SNMPv 2 u, SNMPv 2*: – secure protocol versions that didn’t make the cut. 10 Aug 6, 2002 CERT Conference 2002: SNMPv 3
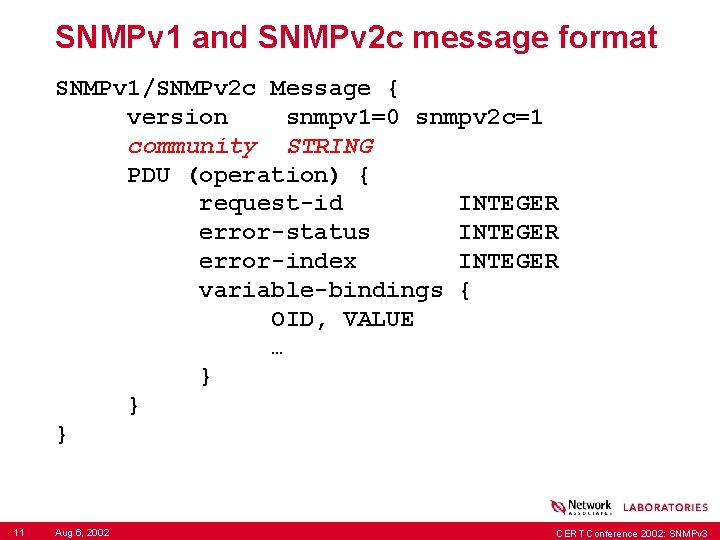
SNMPv 1 and SNMPv 2 c message format SNMPv 1/SNMPv 2 c Message { version snmpv 1=0 snmpv 2 c=1 community STRING PDU (operation) { request-id INTEGER error-status INTEGER error-index INTEGER variable-bindings { OID, VALUE … } } } 11 Aug 6, 2002 CERT Conference 2002: SNMPv 3
SNMPv 1 and SNMPv 2 c problems • Community strings for authentication == Clear Text Passwords • Community strings also used for “context” – Accessing data in a certain “context” is difficult • No Standardized Method for Access Control – No consistent method to configure communities across a network of many devices. – Most were devices manually configured, or worse, left with their default settings intact. - kingdom keys: “public”, “private” 12 Aug 6, 2002 CERT Conference 2002: SNMPv 3
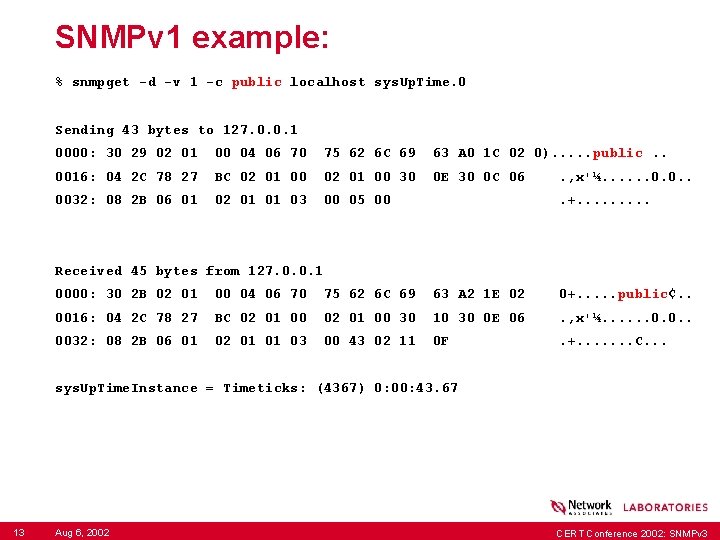
SNMPv 1 example: % snmpget -d -v 1 -c public localhost sys. Up. Time. 0 Sending 43 bytes to 127. 0. 0. 1 0000: 30 29 02 01 00 04 06 70 75 62 6 C 69 63 A 0 1 C 02 0). . . public. . 0016: 04 2 C 78 27 BC 02 01 00 30 0 E 30 0 C 06 . , x'¼. . . 0. 0. . 0032: 08 2 B 06 01 02 01 01 03 00 05 00 . +. . Received 45 bytes from 127. 0. 0. 1 0000: 30 2 B 02 01 00 04 06 70 75 62 6 C 69 63 A 2 1 E 02 0+. . . public¢. . 0016: 04 2 C 78 27 BC 02 01 00 30 10 30 0 E 06 . , x'¼. . . 0. 0. . 0032: 08 2 B 06 01 02 01 01 03 00 43 02 11 0 F . +. . . . C. . . sys. Up. Time. Instance = Timeticks: (4367) 0: 00: 43. 67 13 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Goals behind SNMPv 3 • Security • Provide modularity in the architecture – Replacing new elements in the future should be easier. – Modularity = many IETF RFCs • Separate “context” of the request from the authentication 14 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Aside: CERT Advisery CA-2002 -03 • SNMP uses BER encoded packets. • BER has a bunch of flexible rules which allow strangely encoded, but legal packets. • The failing was in the parsing of the BER encoding, NOT in the SNMP protocol. – SNMPv 1 was the only packet format tested. – It’s likely most vendors also fixed SNMPv 3 parsing too. – The university that produced the results has been testing various BER-based protocols. - Started with LDAP. - Next? Only they know. Kerberos? 15 Aug 6, 2002 CERT Conference 2002: SNMPv 3
SNMPv 3 Architecture “The architecture is designed to be modular to allow the evolution of the Framework over time. ” -- RFC 2570 & RFC 2571 16 Aug 6, 2002 CERT Conference 2002: SNMPv 3
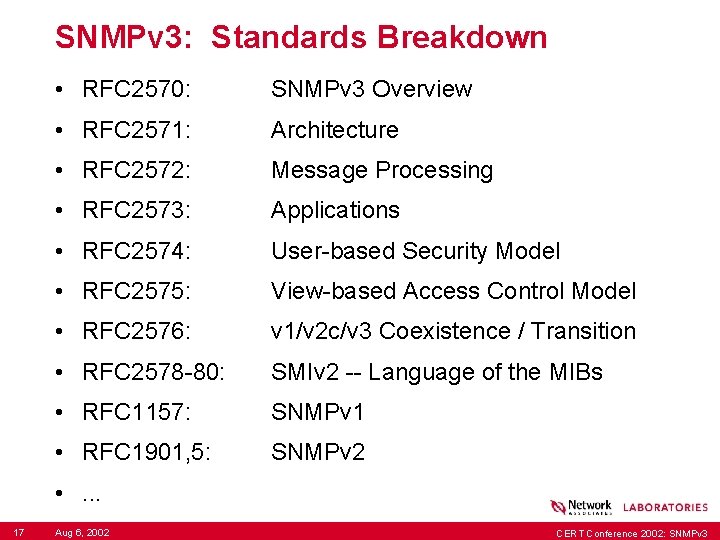
SNMPv 3: Standards Breakdown • RFC 2570: SNMPv 3 Overview • RFC 2571: Architecture • RFC 2572: Message Processing • RFC 2573: Applications • RFC 2574: User-based Security Model • RFC 2575: View-based Access Control Model • RFC 2576: v 1/v 2 c/v 3 Coexistence / Transition • RFC 2578 -80: SMIv 2 -- Language of the MIBs • RFC 1157: SNMPv 1 • RFC 1901, 5: SNMPv 2 • . . . 17 Aug 6, 2002 CERT Conference 2002: SNMPv 3
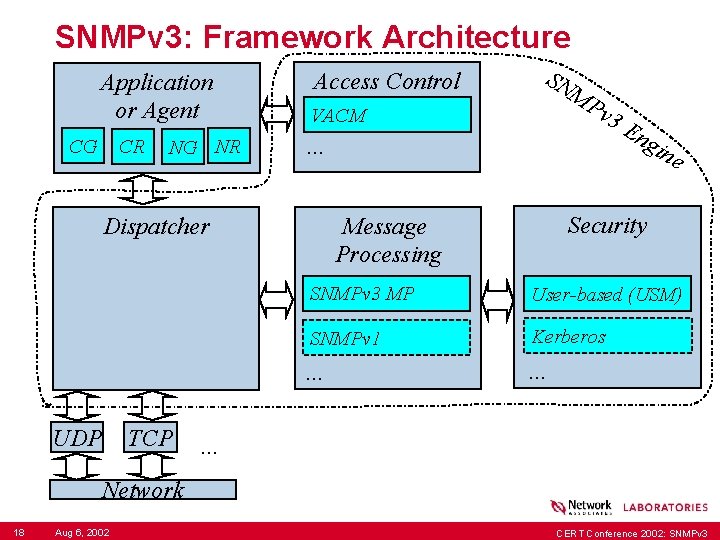
SNMPv 3: Framework Architecture Application or Agent CG CR NG NR Access Control TCP MP v 3 VACM . . . En gin e Security Message Processing Dispatcher UDP SN SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 18 Aug 6, 2002 CERT Conference 2002: SNMPv 3
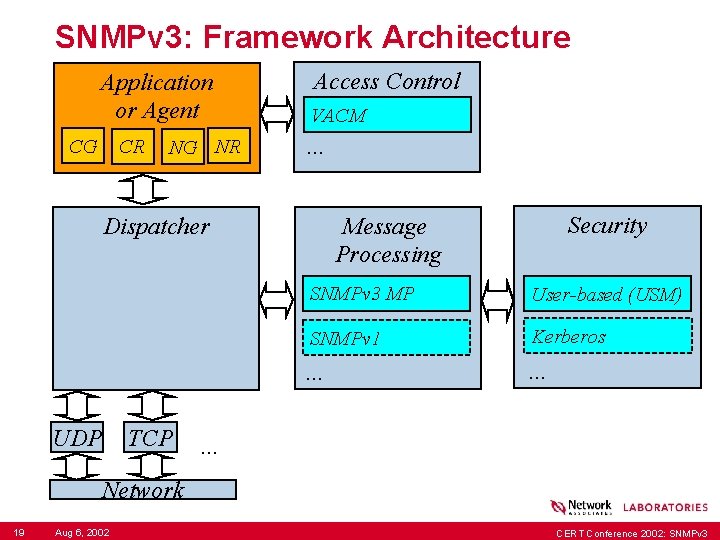
SNMPv 3: Framework Architecture Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processing Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 19 Aug 6, 2002 CERT Conference 2002: SNMPv 3
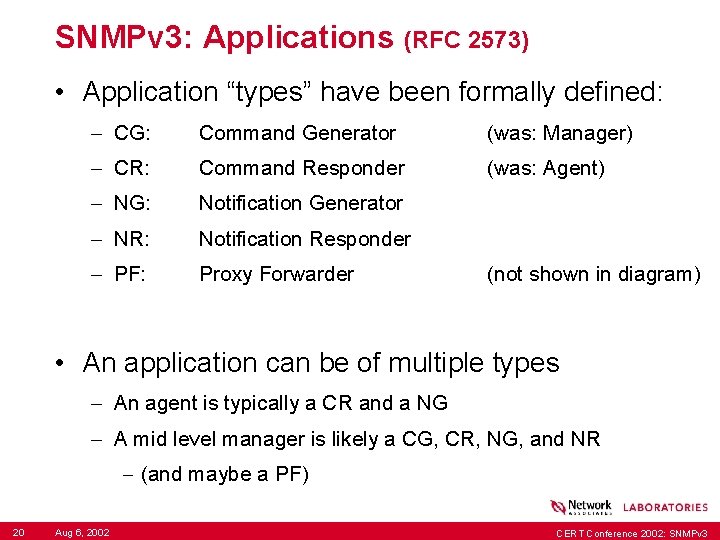
SNMPv 3: Applications (RFC 2573) • Application “types” have been formally defined: – CG: Command Generator (was: Manager) – CR: Command Responder (was: Agent) – NG: Notification Generator – NR: Notification Responder – PF: Proxy Forwarder (not shown in diagram) • An application can be of multiple types – An agent is typically a CR and a NG – A mid level manager is likely a CG, CR, NG, and NR - (and maybe a PF) 20 Aug 6, 2002 CERT Conference 2002: SNMPv 3
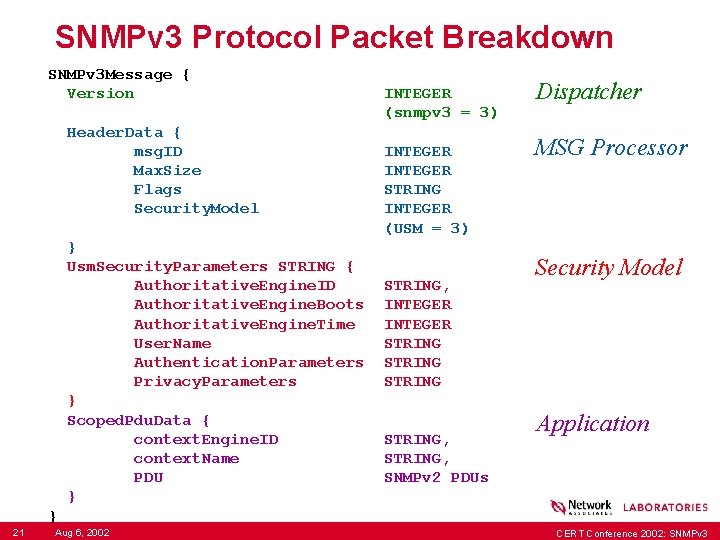
SNMPv 3 Protocol Packet Breakdown SNMPv 3 Message { Version INTEGER (snmpv 3 = 3) Header. Data { msg. ID INTEGER Max. Size INTEGER Flags STRING Security. Model INTEGER (USM = 3) } Usm. Security. Parameters STRING { Authoritative. Engine. ID STRING, Authoritative. Engine. Boots INTEGER Authoritative. Engine. Time INTEGER User. Name STRING Authentication. Parameters STRING Privacy. Parameters STRING } Scoped. Pdu. Data { context. Engine. ID STRING, context. Name STRING, PDU SNMPv 2 PDUs } } 21 Aug 6, 2002 Dispatcher MSG Processor Security Model Application CERT Conference 2002: SNMPv 3
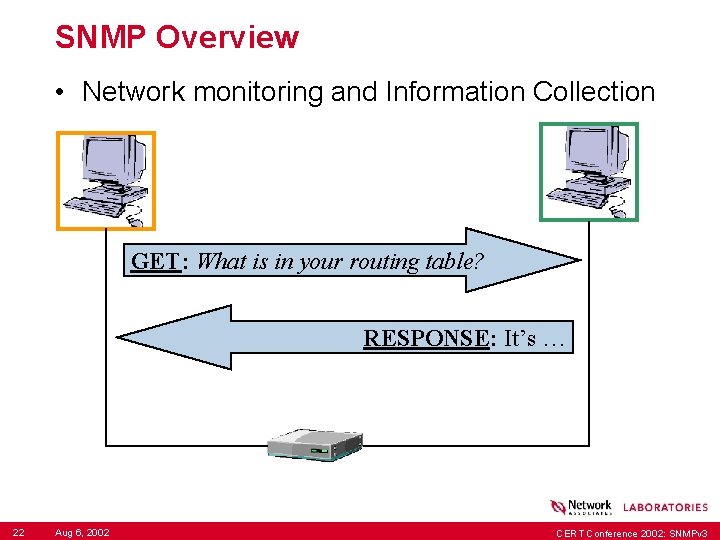
SNMP Overview • Network monitoring and Information Collection GET: What is in your routing table? RESPONSE: It’s … 22 Aug 6, 2002 CERT Conference 2002: SNMPv 3
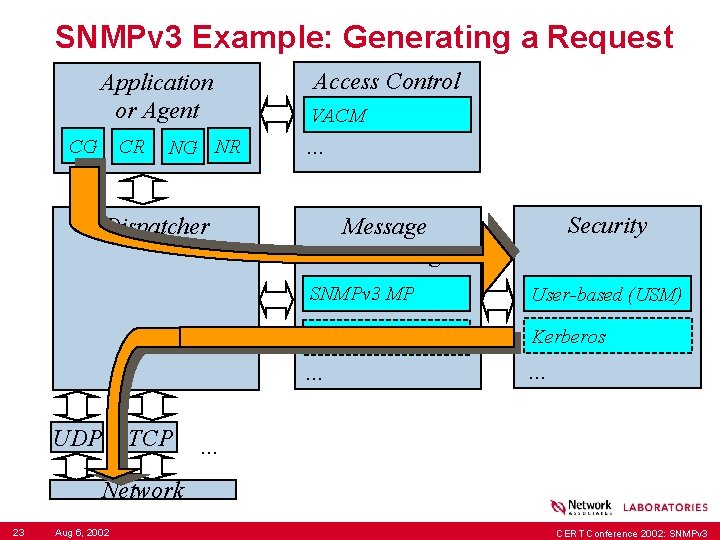
SNMPv 3 Example: Generating a Request Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processing Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 23 Aug 6, 2002 CERT Conference 2002: SNMPv 3
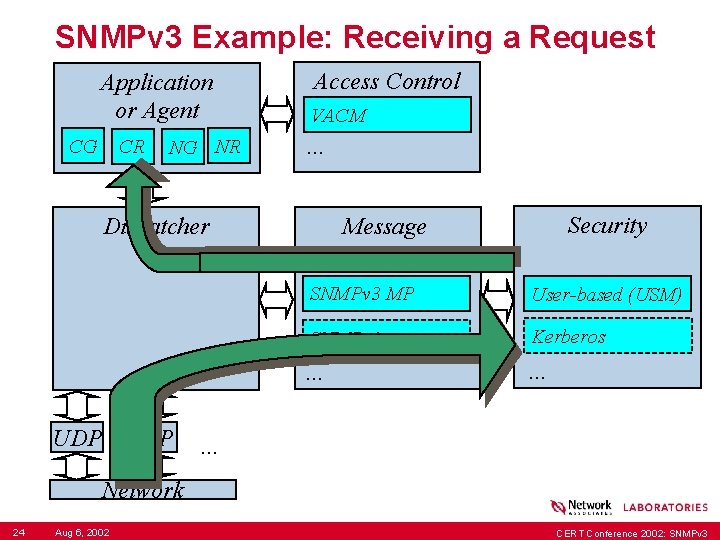
SNMPv 3 Example: Receiving a Request Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processing Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 24 Aug 6, 2002 CERT Conference 2002: SNMPv 3
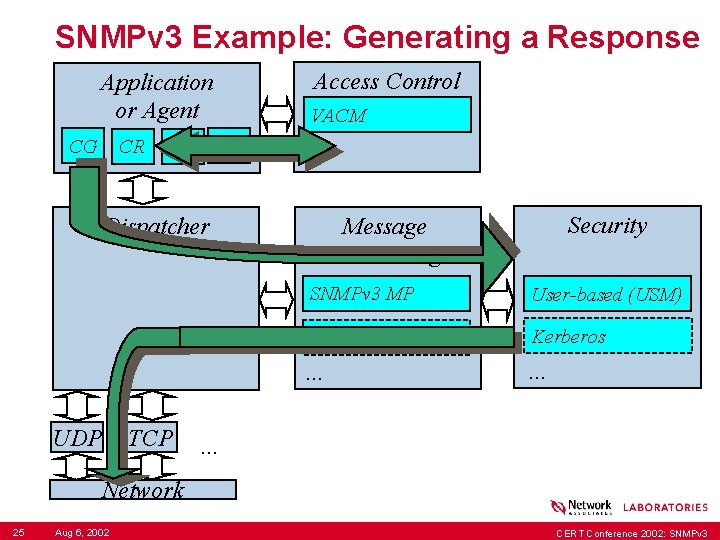
SNMPv 3 Example: Generating a Response Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processing Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 25 Aug 6, 2002 CERT Conference 2002: SNMPv 3
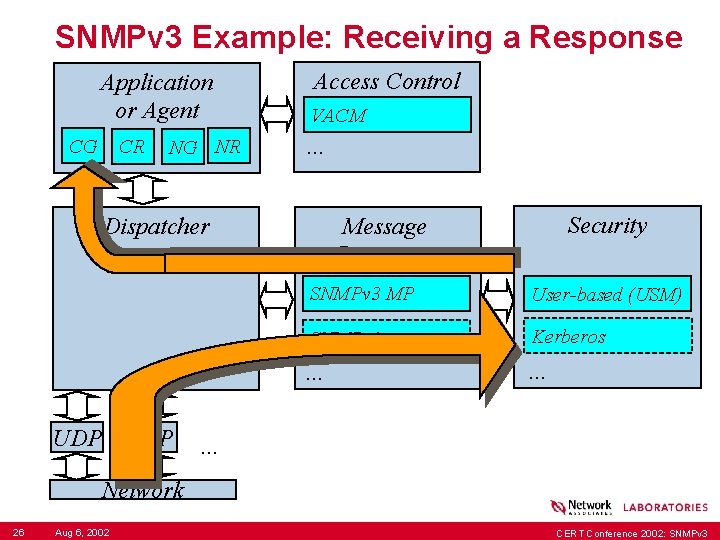
SNMPv 3 Example: Receiving a Response Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processing Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 26 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Architecture Components “The major portions of the architecture an SNMP engine containing a Message Processing Subsystem, a Security Subsystem and an Access Control Subsystem, and possibly multiple SNMP applications which provide specific functional processing of management data. . ” -- RFC 2571 27 Aug 6, 2002 CERT Conference 2002: SNMPv 3
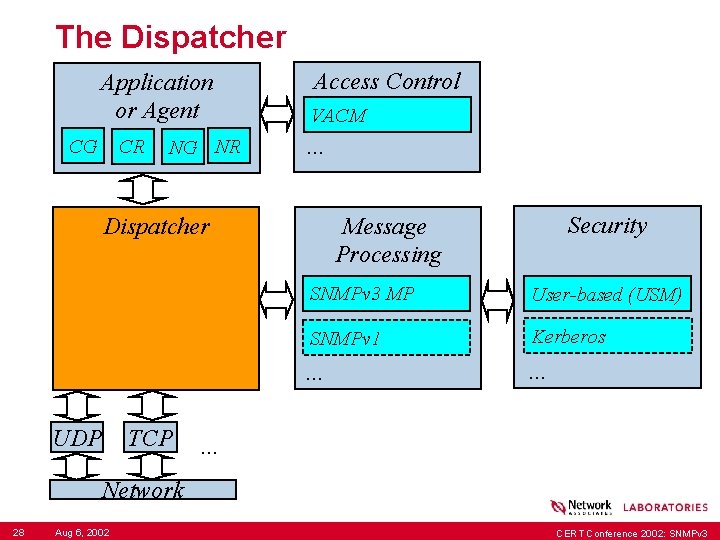
The Dispatcher Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processing Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 28 Aug 6, 2002 CERT Conference 2002: SNMPv 3
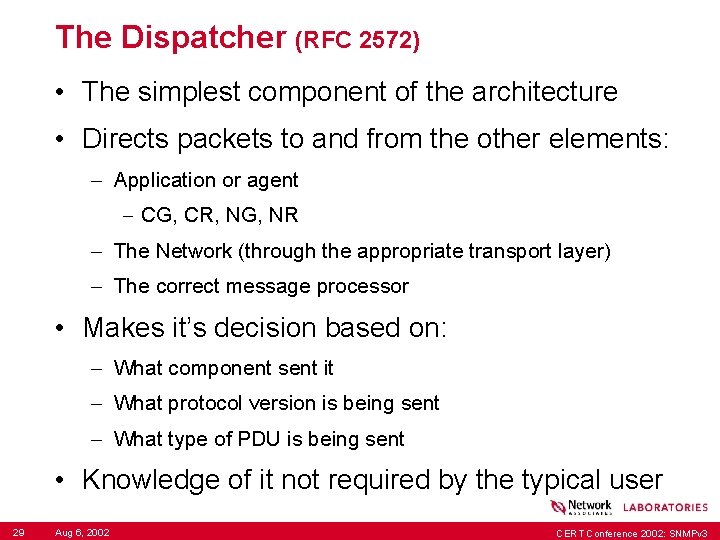
The Dispatcher (RFC 2572) • The simplest component of the architecture • Directs packets to and from the other elements: – Application or agent - CG, CR, NG, NR – The Network (through the appropriate transport layer) – The correct message processor • Makes it’s decision based on: – What component sent it – What protocol version is being sent – What type of PDU is being sent • Knowledge of it not required by the typical user 29 Aug 6, 2002 CERT Conference 2002: SNMPv 3
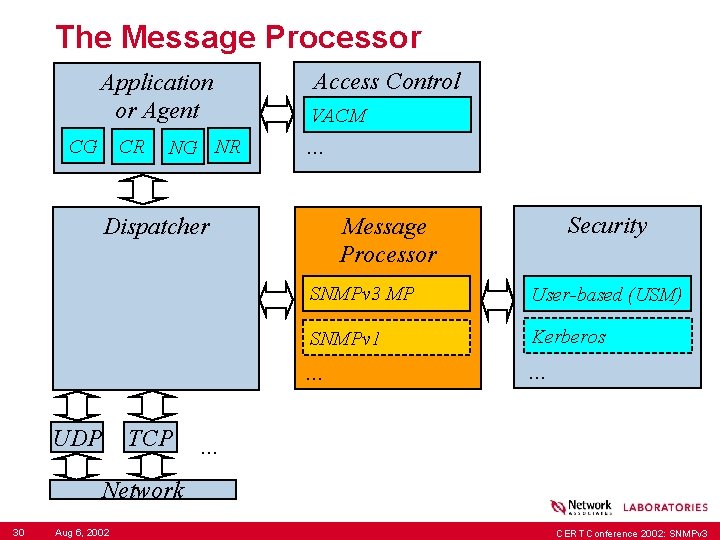
The Message Processor Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processor Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 30 Aug 6, 2002 CERT Conference 2002: SNMPv 3
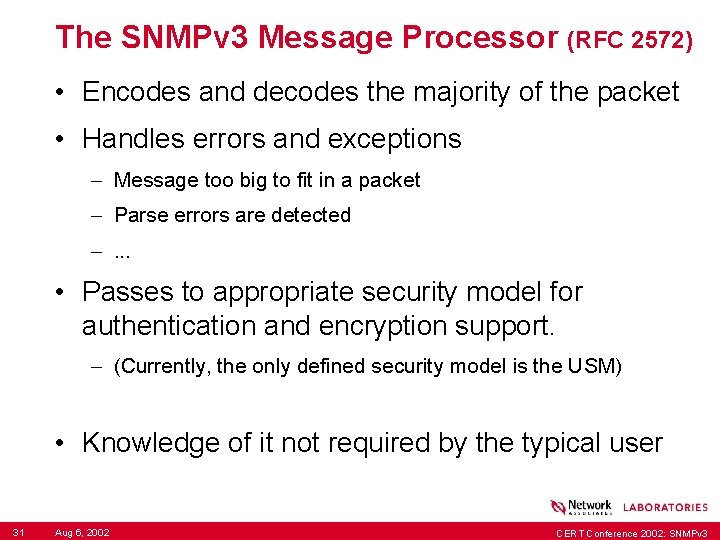
The SNMPv 3 Message Processor (RFC 2572) • Encodes and decodes the majority of the packet • Handles errors and exceptions – Message too big to fit in a packet – Parse errors are detected –. . . • Passes to appropriate security model for authentication and encryption support. – (Currently, the only defined security model is the USM) • Knowledge of it not required by the typical user 31 Aug 6, 2002 CERT Conference 2002: SNMPv 3
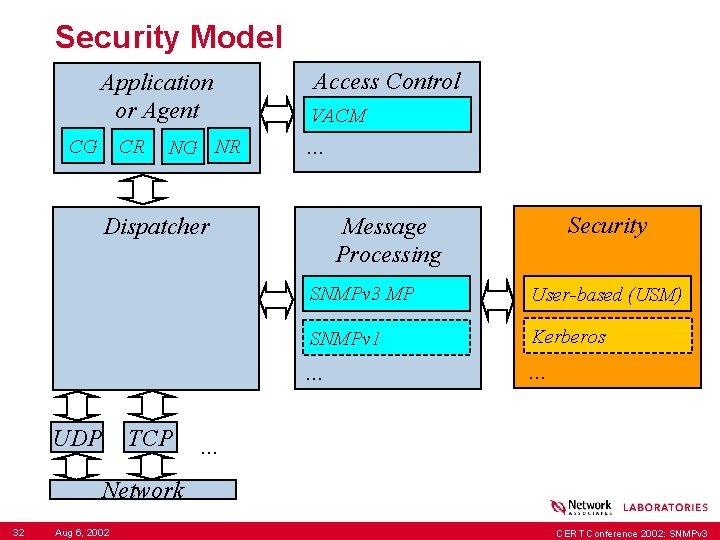
Security Model Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processing Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 32 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Security Model • Authenticates packets to ensure/verify origin – Current authentication methods • Provides message encryption/decryption support – The Scoped. PDU can be protected by encryption • Makes it’s decisions based on packet data: – Engine. ID, Engine Boots, Engine Time – User Name – Authentication field – Privacy field • Currently one standard security model exists – The “User Based Security Model”, or USM 33 Aug 6, 2002 CERT Conference 2002: SNMPv 3
User Based Security: USM (RFC 2574) • The User Based Security model provides: – Authentication via MD 5 or SHA 1 hash - The hash verifies the authenticity of the entire v 3 message. - Modified or forged packets will be rejected – Encryption via DES encryption - The Scoped. PDU is encrypted (basically, the payload) – 3 levels of security: no. Auth. No. Priv, auth. Priv • It does not provide protection against: – Denial of Service – Traffic Analysis 34 Aug 6, 2002 CERT Conference 2002: SNMPv 3
USM: About Engine. IDs, etc. . . • Engine. IDs are: – A unique “string” of data – Generally defined from one of: - IPv 4 address - IPv 6 address - MAC address - Administratively defined strings - Implementation dependent • Engine. Boots: number of reboots • Engine. Time: Time since last initialized • Information is automatically probed by protocol. 35 Aug 6, 2002 CERT Conference 2002: SNMPv 3
USM: A User is. . . • A USM User is defined by: – The Engine. ID of the authoritative engine – The Security. Name of the user (i. e. , user name) – The authentication type (MD 5 or SHA 1) and key – The privacy type (DES) and key • A user is modifiable via SNMP SET operations: – Authentication and privacy keys can be changed. – Encryption types and authentication types can not be changed without deleting and recreating the user 36 Aug 6, 2002 CERT Conference 2002: SNMPv 3
USM: The Authoritative Engine • Only one side of a transaction is “authoritative” – Authoritative side == where the master user key exists – Typically this means: the SNMP agents are authoritative – The authoritative side is defined by whether the packet being sent is expecting a response or not. - An odd effect of this is: - The engine receiving SNMPv 3 INFORMs, which expect a “I got it” response, are authoritative. - The engine sending SNMPv 3 TRAPs, which don’t require a response, are authoritative. - Ick. 37 Aug 6, 2002 CERT Conference 2002: SNMPv 3
USM: Keys • USM Keys used to authenticate and encrypt messages are generated: – A password hashed using the authentication algorithm (maybe) – The resulting hash is then re-hashed after mixing it with the authoritative engine. ID. • This means: – All user keys are different on each host – Pro: A cracked system’s keys can’t be used to gain access to other systems. – Con: Distributing keys to many systems is difficult 38 Aug 6, 2002 CERT Conference 2002: SNMPv 3
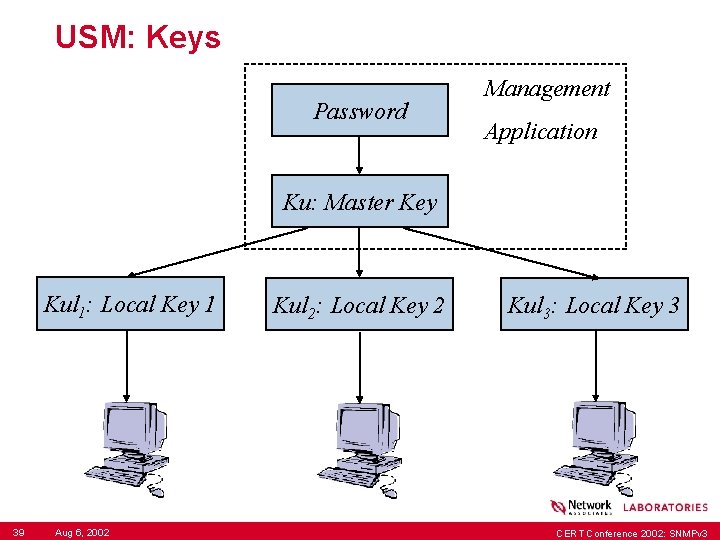
USM: Keys Password Management Application Ku: Master Key Kul 1: Local Key 1 39 Aug 6, 2002 Kul 2: Local Key 2 Kul 3: Local Key 3 CERT Conference 2002: SNMPv 3
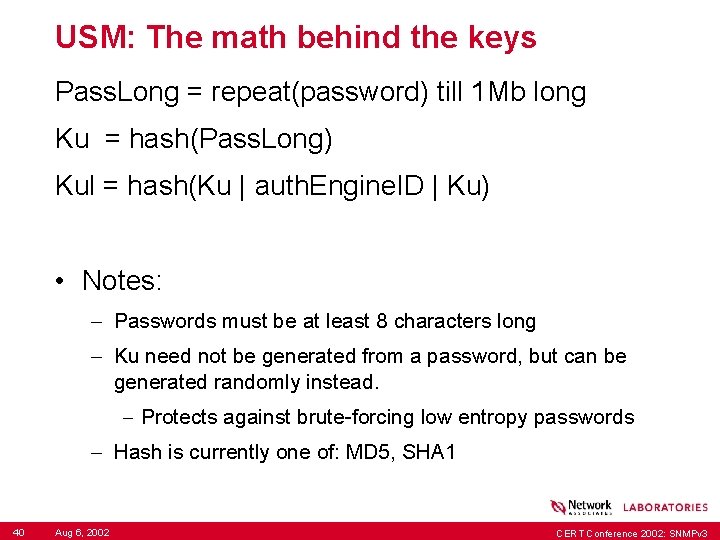
USM: The math behind the keys Pass. Long = repeat(password) till 1 Mb long Ku = hash(Pass. Long) Kul = hash(Ku | auth. Engine. ID | Ku) • Notes: – Passwords must be at least 8 characters long – Ku need not be generated from a password, but can be generated randomly instead. - Protects against brute-forcing low entropy passwords – Hash is currently one of: MD 5, SHA 1 40 Aug 6, 2002 CERT Conference 2002: SNMPv 3
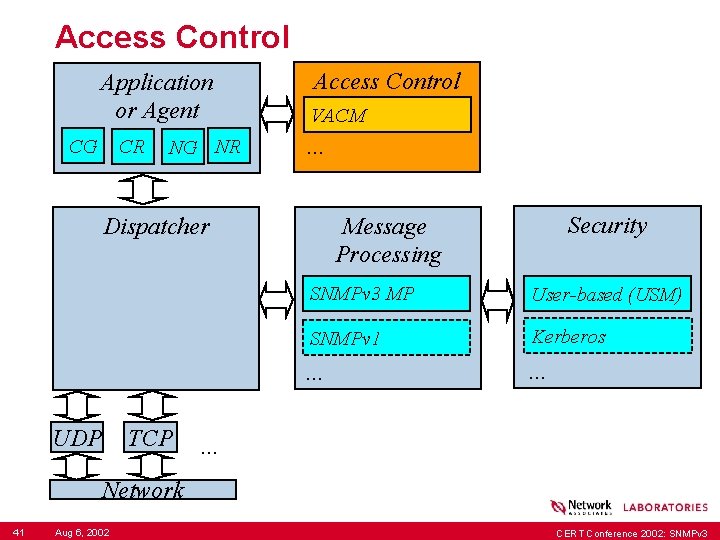
Access Control Application or Agent CG CR NG NR Access Control VACM . . . UDP TCP Security Message Processing Dispatcher SNMPv 3 MP User-based (USM) SNMPv 1 Kerberos . . Network 41 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Access Control • Decides if a particular “object instance” may be accessed or not. • Consulted by the CR and NG application types • Currently, only one access control model exists: – The View-Based Access Control Module (VACM) 42 Aug 6, 2002 CERT Conference 2002: SNMPv 3
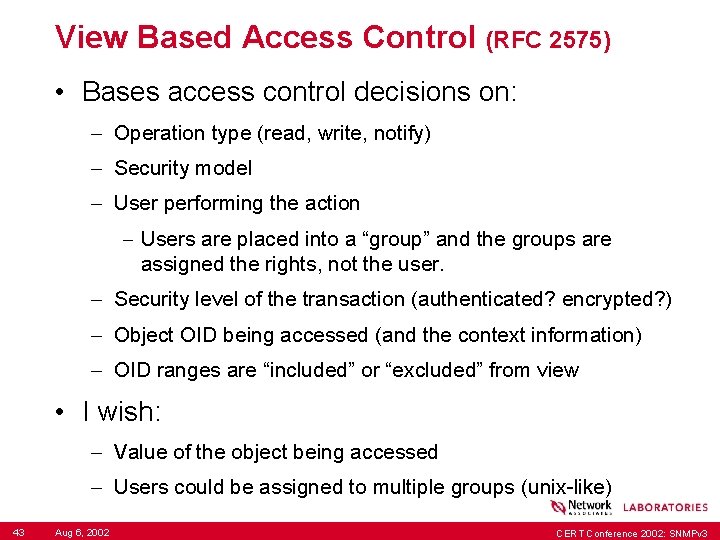
View Based Access Control (RFC 2575) • Bases access control decisions on: – Operation type (read, write, notify) – Security model – User performing the action - Users are placed into a “group” and the groups are assigned the rights, not the user. – Security level of the transaction (authenticated? encrypted? ) – Object OID being accessed (and the context information) – OID ranges are “included” or “excluded” from view • I wish: – Value of the object being accessed – Users could be assigned to multiple groups (unix-like) 43 Aug 6, 2002 CERT Conference 2002: SNMPv 3
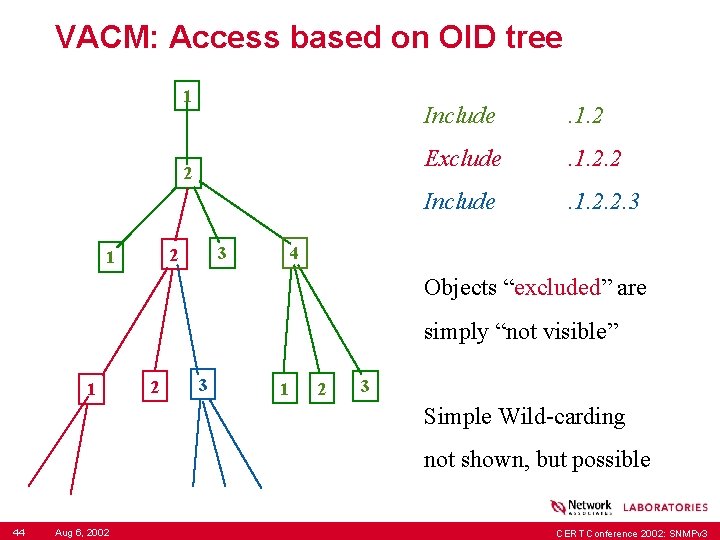
VACM: Access based on OID tree 1 2 3 2 1 Include . 1. 2 Exclude . 1. 2. 2 Include . 1. 2. 2. 3 4 Objects “excluded” are simply “not visible” 1 2 3 Simple Wild-carding not shown, but possible 44 Aug 6, 2002 CERT Conference 2002: SNMPv 3
The Future of SNMP • Other security work: – AES encryption for the USM – USM alternatives: kerberos, … • New protocol PDU operations (Eo. S WG): – Better bulk retrieval – Better write transaction handling – Better data compression – Easier row operations (creation, deletion, …) • A new SMI (SMIng WG): – Hierarchical Data Definition Language – Easier to write – Easier to read 45 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Summary • SNMPv 1, v 2 c: bad, no security • SNMPv 3: better, has security • Start switching to SNMPv 3 now. – Almost FULL standard – Most vendors support it • SNMPv 3 is modular in design 46 Aug 6, 2002 CERT Conference 2002: SNMPv 3
Conclusion Questions? Wes Hardaker <Wes_Hardaker@nai. com> 47 Aug 6, 2002 CERT Conference 2002: SNMPv 3
- Slides: 48