Smart Phone Security Privacy What Should We Teach





- Slides: 49

Smart Phone Security & Privacy: What Should We Teach Our Users? Norman M. Sadeh Professor, School of Computer Science Director, Mobile Commerce Lab. Carnegie Mellon University www. cs. cmu. edu/~sadeh
Outline o Smart phone security and privacy awareness: unique challenges o Phishing: much worse with smart phone users n What can we do? o Mobile Apps and Social Networking n What we can we teach users? o Concluding remarks o Q&A Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 2
SMART PHONE SECURITY and PRIVACY AWARENESS: UNIQUE CHALLENGES Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 3

Cyber Security Training Awareness …Has been compared to trying to nail Jell-O to a wall Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 4
Yet… o Filters, firewalls, IDS etc. have their limitations o Users are the last line of defense o Universities: A Dual Objective n Protect the university’s infrastructure and sensitive data n Educational mission Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 5

Universities o Diversity of users n Faculty, staff, students o Diversity of cultures and environments n Fragmented administration o Diversity of needs n Research vs. education vs. admin o Diversity of devices n Some managed & some not o. . . Yet the price of security breaches can be dire… Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 6
Smart Phones: The New Frontier Smart Phone Adoption to Approach 50% in the US in 2011 Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 7

…Along the Way… o Our cell phones are now coming with the same vulnerabilities we have on our computers… …and more… Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 8
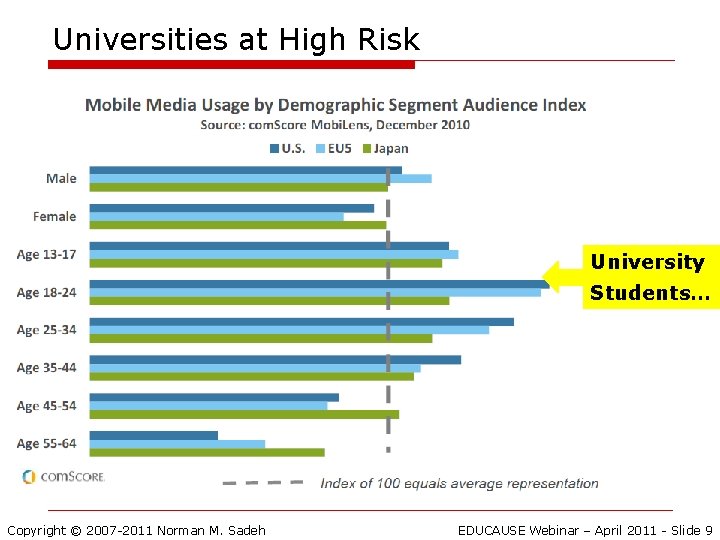
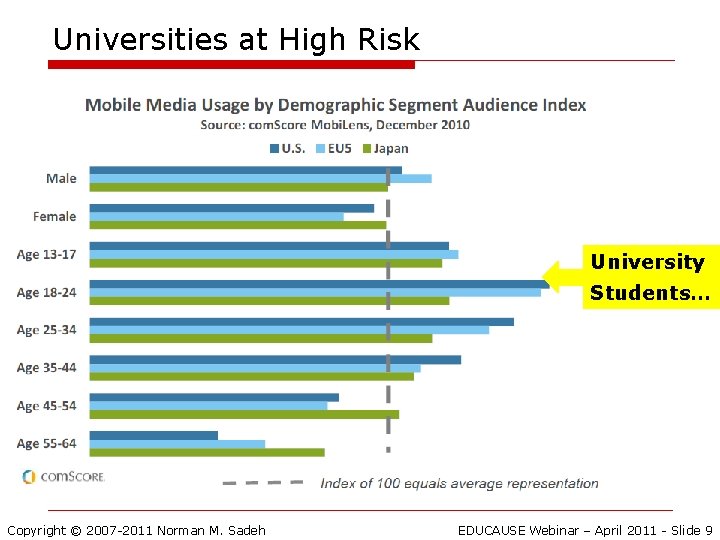
Universities at High Risk University Students… Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 9
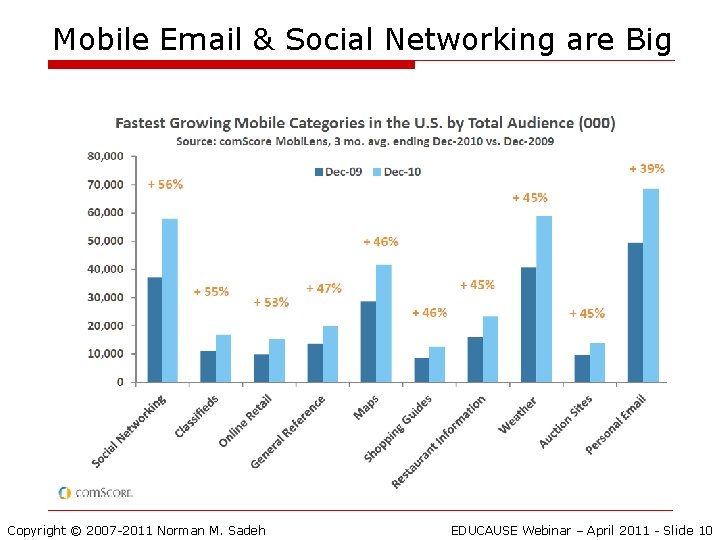
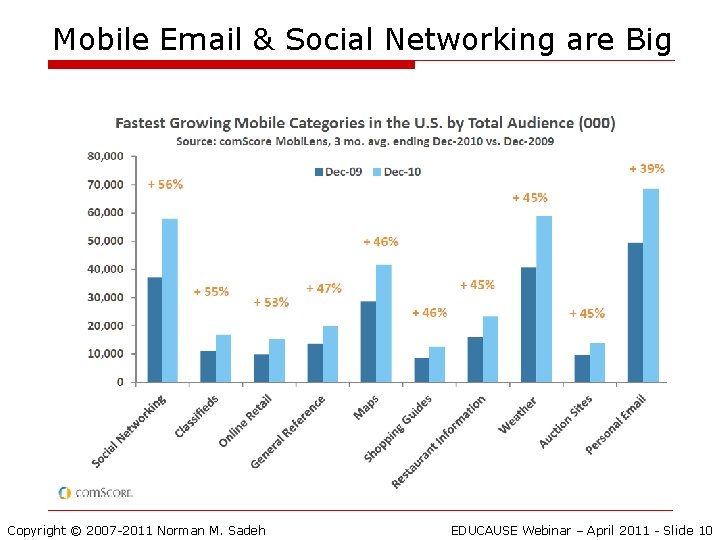
Mobile Email & Social Networking are Big Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 10
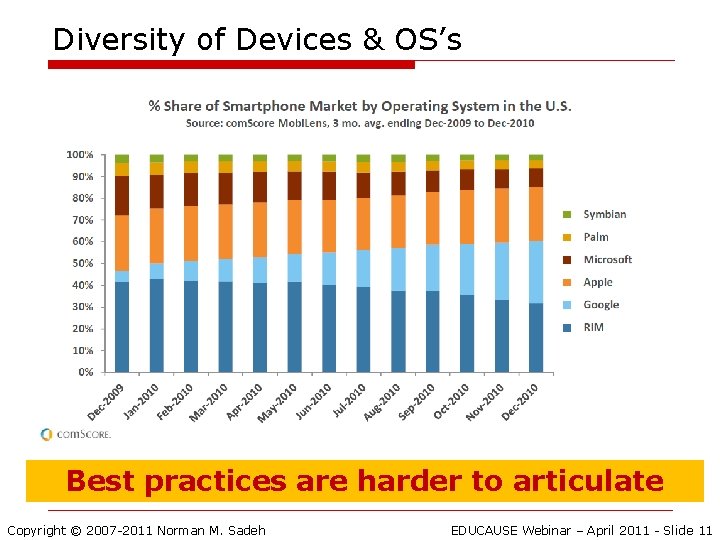
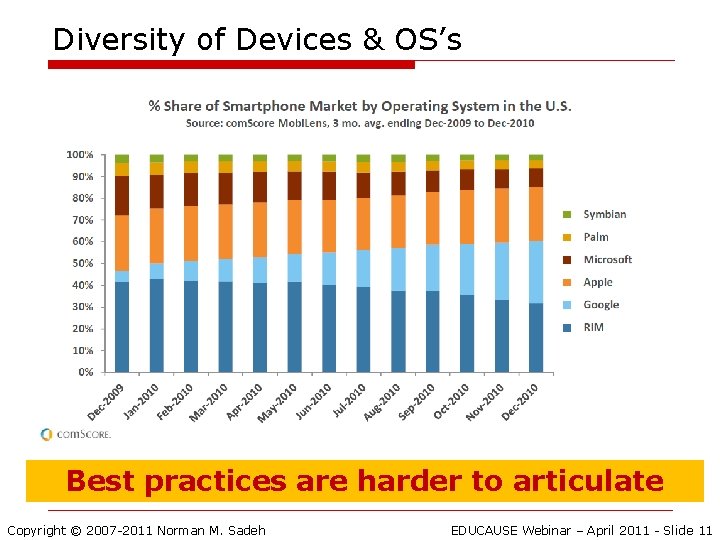
Diversity of Devices & OS’s Best practices are harder to articulate Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 11
The Biggest Security Risk? Millions of cell phones lost or stolen each year Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 12
Lost or Stolen Phone…. o Private data & sensitive apps n e. g. contacts list, pictures, phone calls, messages, email, calendar, apps, etc o Risk of someone using your phone n Impersonating you – SMS, voice, email, social networks, etc. n Placing expensive international calls o Reselling your phone o etc. Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 13
What Can We Teach? o Don’t leave your phone unattended n Goes beyond theft and loss: malware is easy to install o Use a PIN to protect your cell phone n Different options (e. g. i. Phone) o Write down your IMEI number as well as phone make and model and cell phone number o Quickly report lost/stolen phone Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 14
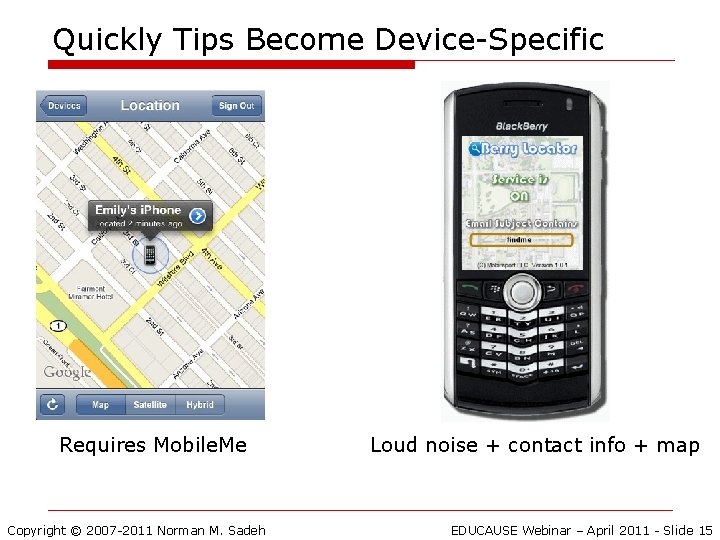
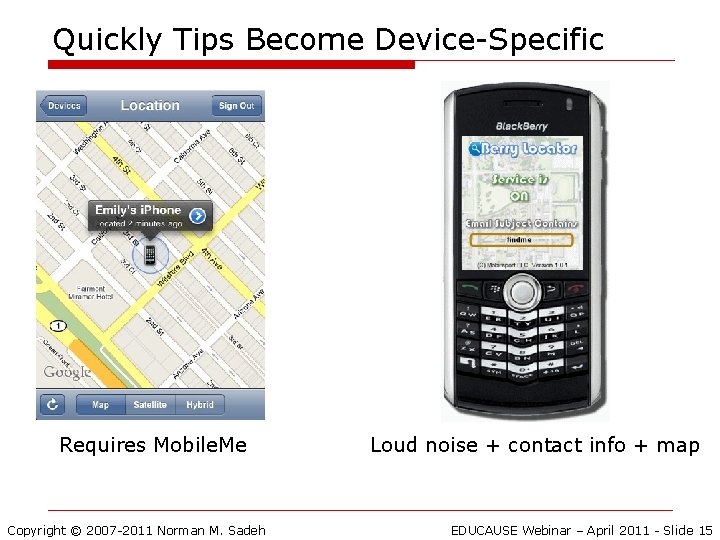
Quickly Tips Become Device-Specific Requires Mobile. Me Copyright © 2007 -2011 Norman M. Sadeh Loud noise + contact info + map EDUCAUSE Webinar – April 2011 - Slide 15
Remote Erase o A number of solutions… o …Hopefully you’ve backed up your data o …Some products combine both back up and “remote wipe” o Watch out for malware - read reviews and select reputable solutions… Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 16
Dangers of Multi-Tasking o Phone call, SMS, email, etc. o While driving, crossing the street. . • Illegal in some places • Not wise elsewhere Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 17
Understanding the risks… o Even more challenging than on a computer o Cell phones are highly personal devices with access to lots of sensitive information o …yet fewer people understand the risks o Lots of different cell phone models n Not all with the same functionality or settings… o Users need to invest time in understanding and tweaking their security settings Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 18
Different Activities Lead to Different Risks n Voice n Email n SMS n Bluetooth n Browsing n Wi. Fi n Location …A rather daunting task… n App Downloads n Social networks n …and more Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 19
PHISHING: MUCH WORSE ON SMART PHONES Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 20
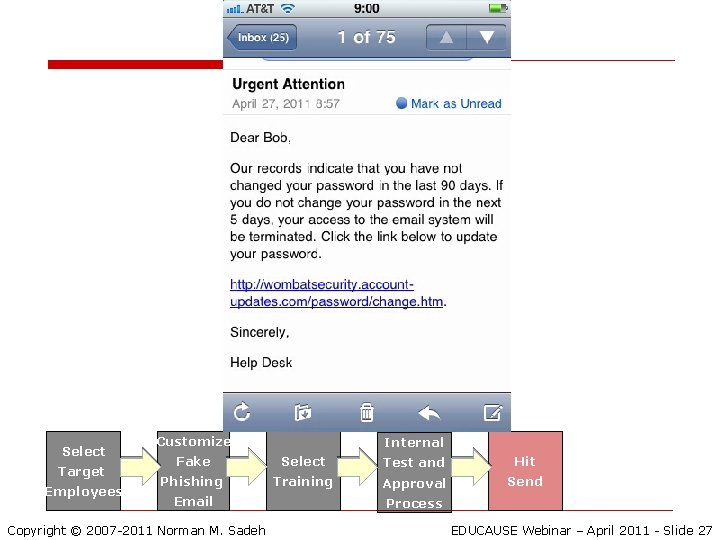
E-Mail Phishing: Worse on Mobile Phones o Trusteer – Jan 2011: n Mobile users are first to arrive at phishing websites n Mobile users 3 x more likely to submit credentials than desktop users Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 21
Beyond e-mail Phishing o SMS-ishing o Vishing o IM phishing o Phishing via social networks o Phishing apps Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 22
What To Do? o Better filters can help n Most spam filters rely on manually maintained blacklists that are several hours behind n Example: Wombat’s Phish. Patrol o Teach people to recognize traps in phishing emails Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 23
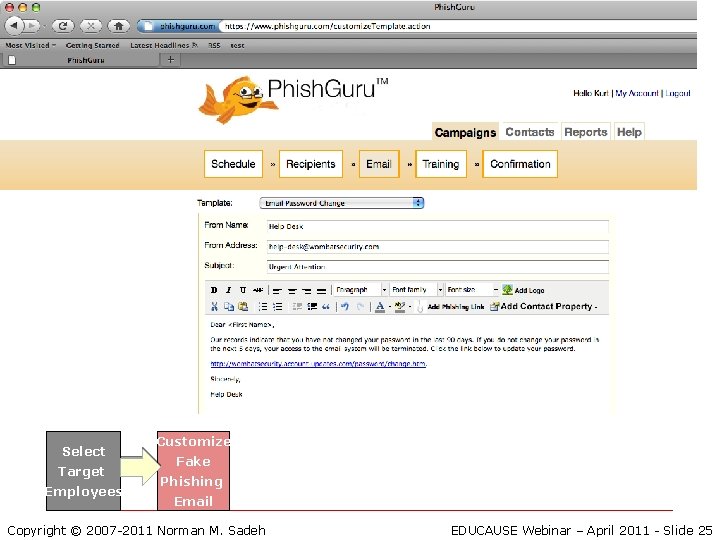
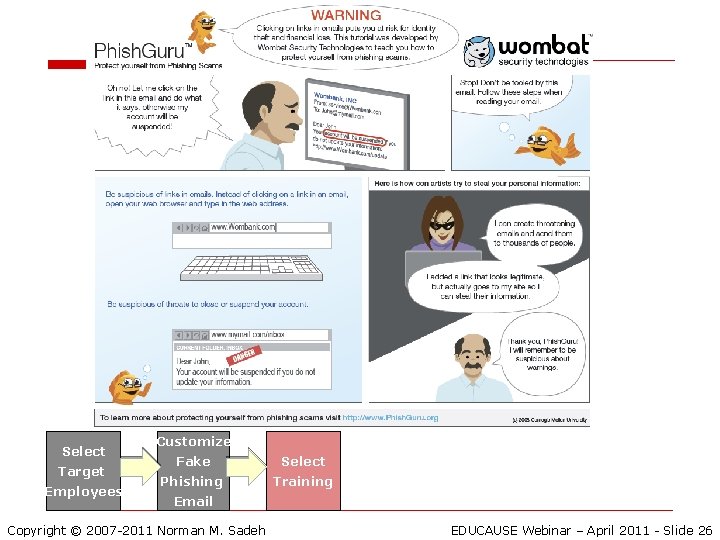
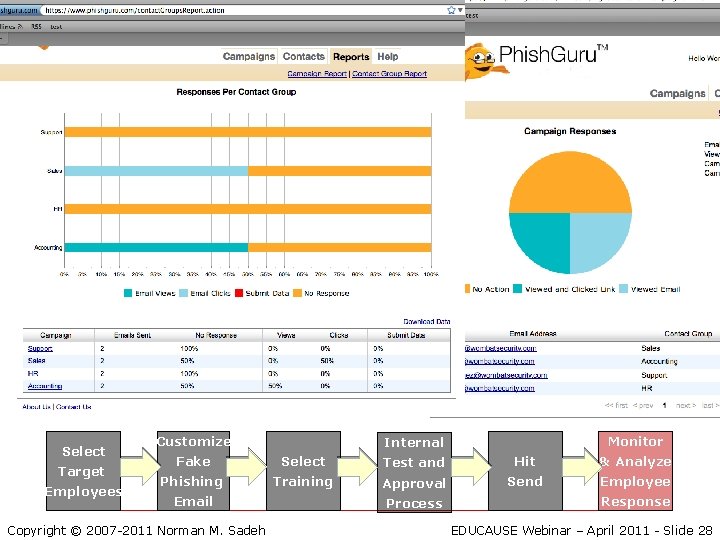
Training via Mock Attacks: Phish. Guru n Teach people in the context they would be attacked n If a person falls for simulated phish, then show intervention as to what just happened n Unique “teachable moment” Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 24
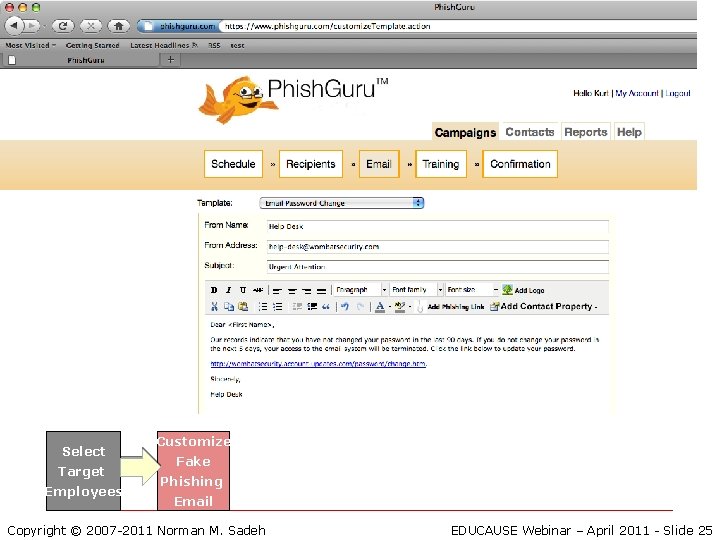
Select Target Employees Customize Fake Phishing Email Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 25
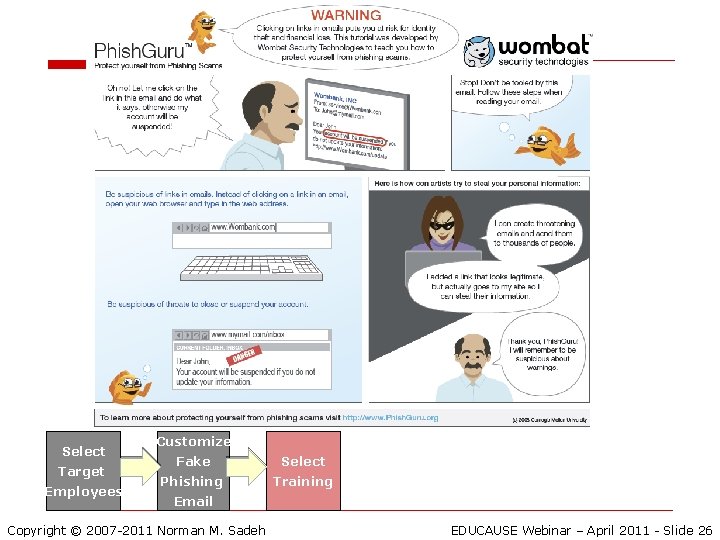
Select Target Employees Customize Fake Select Phishing Training Email Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 26
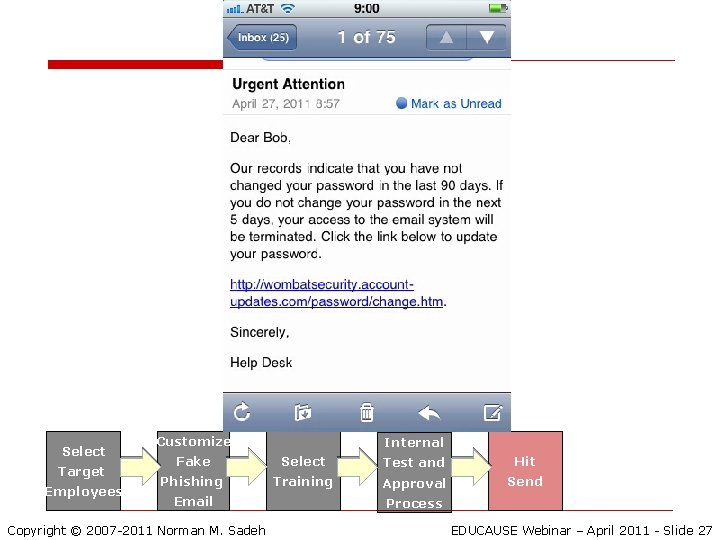
Select Target Employees Customize Internal Fake Select Test and Hit Phishing Training Approval Send Email Copyright © 2007 -2011 Norman M. Sadeh Process EDUCAUSE Webinar – April 2011 - Slide 27
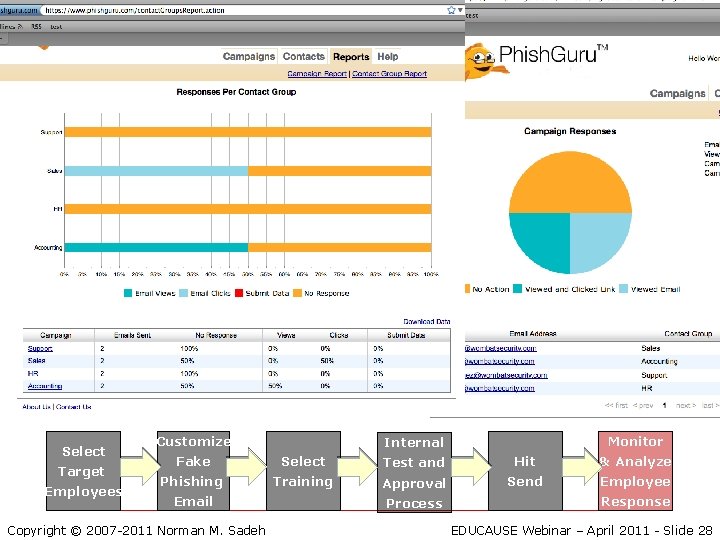
Select Target Employees Customize Monitor Internal Fake Select Test and Hit & Analyze Phishing Training Approval Send Employee Email Copyright © 2007 -2011 Norman M. Sadeh Process Response EDUCAUSE Webinar – April 2011 - Slide 28
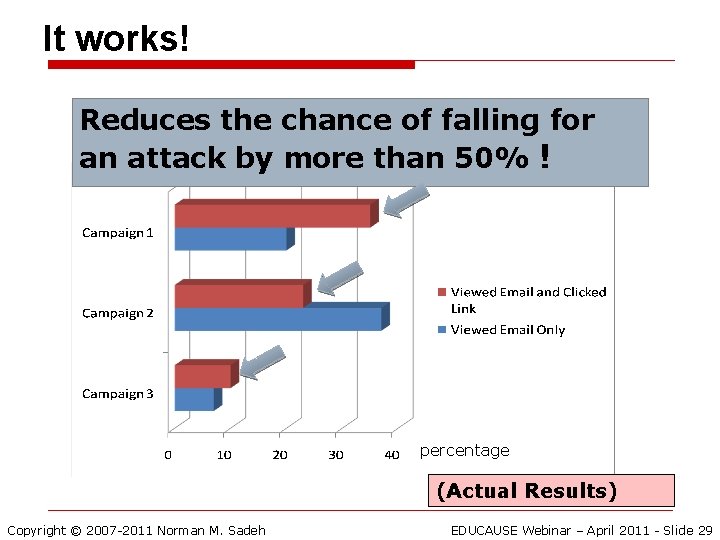
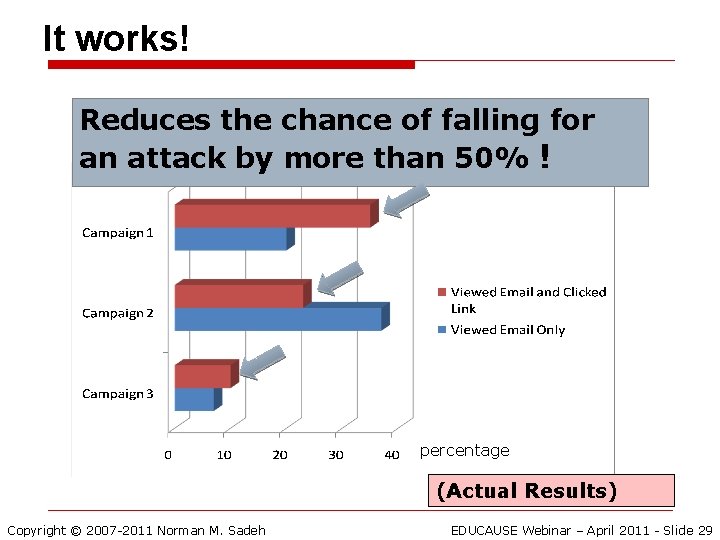
It works! Reduces the chance of falling for an attack by more than 50% ! percentage (Actual Results) Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 29
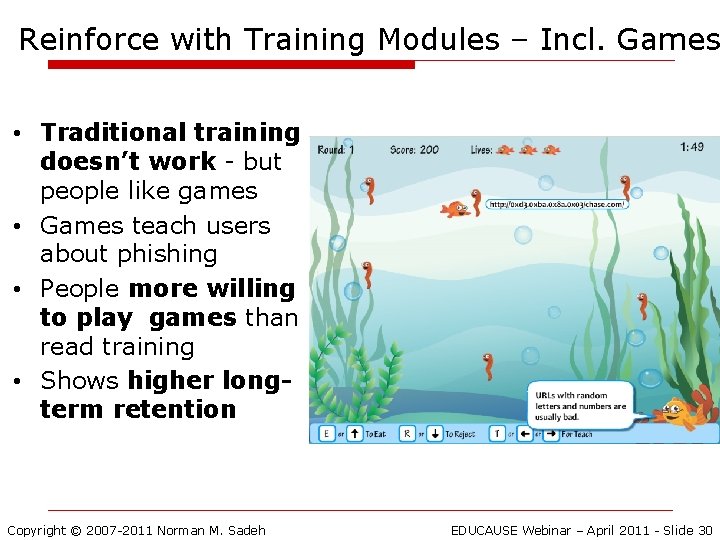
Reinforce with Training Modules – Incl. Games • Traditional training doesn’t work - but people like games • Games teach users about phishing • People more willing to play games than read training • Shows higher longterm retention Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 30
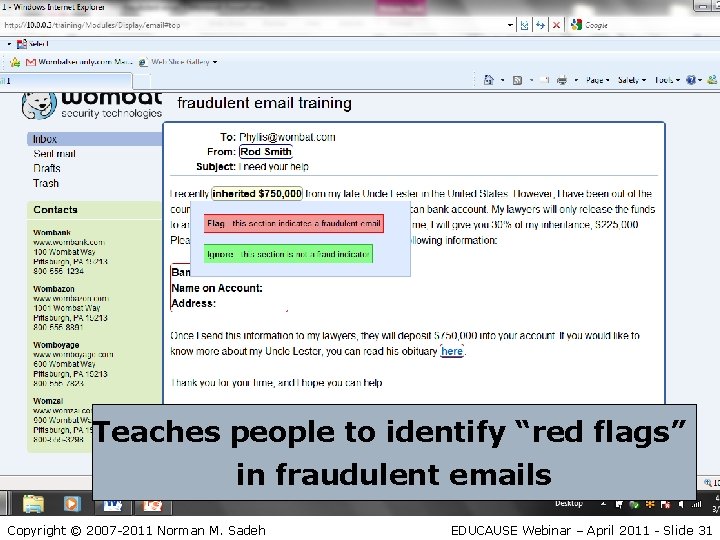
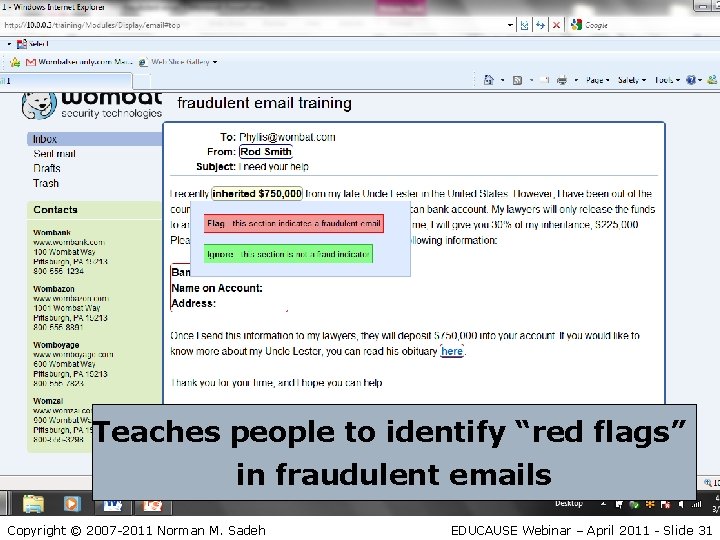
Teaches people to identify “red flags” in fraudulent emails Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 31
Phishing is a Generic Threat o It is possible to identify deviceindependent tips and strategies o It is possible to teach these tips and strategies in a matter of minutes o Universities like CMU are using Phish. Guru and training games (Phil and Phyllis training games) to train staff, faculty and students o A dedicated anti-phishing email filter can also make a difference (e. g. Phish. Patrol) Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 32
MOBILE APPS & SOCIAL NETWORKING: WHAT CAN WE TEACH USERS? Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 33
Social Networking – Facebook, Twitter & Co. o Sharing is wonderful… o …until you regret you did it o Think and ask yourself whether: n You really know who you are sharing with n A week or a year from now, you’ll still be happy you did o Colleagues, friends, new acquaintances… o Beware of pictures and links that seem to come from friends…. Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 34
All Those Great Apps Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 35
Malicious Apps o In January of 2010, the first malicious mobile banking app was detected n Stole your banking credentials o Android doesn’t review applications o Apple does, but that’s no guarantee o Many apps collect a lot more information than they need to – e. g. location Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 36
Some Recommendations o Research apps before you download them o Best to wait until enough other people have tried them o Check ratings – but do not rely entirely on them o If you are courageous, take time to review privacy provisions o Possibly create a Google alert for apps you download Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 37
Location Sharing Apps. Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 38
Also referred to by some as… Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 39
If you are going to share your location, at least do it under conditions you control Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 40
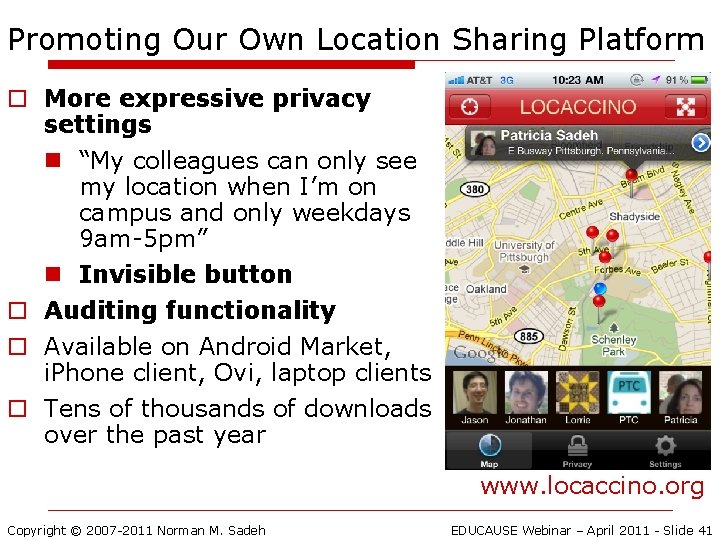
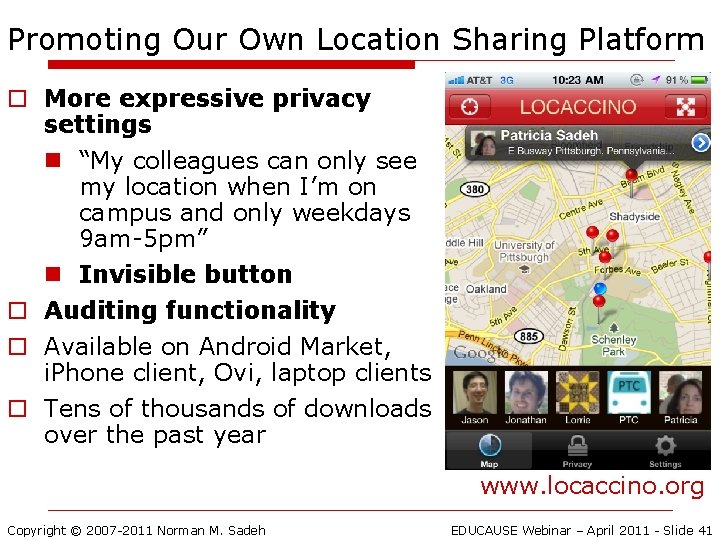
Promoting Our Own Location Sharing Platform o More expressive privacy settings n “My colleagues can only see my location when I’m on campus and only weekdays 9 am-5 pm” n Invisible button o Auditing functionality o Available on Android Market, i. Phone client, Ovi, laptop clients o Tens of thousands of downloads over the past year www. locaccino. org Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 41
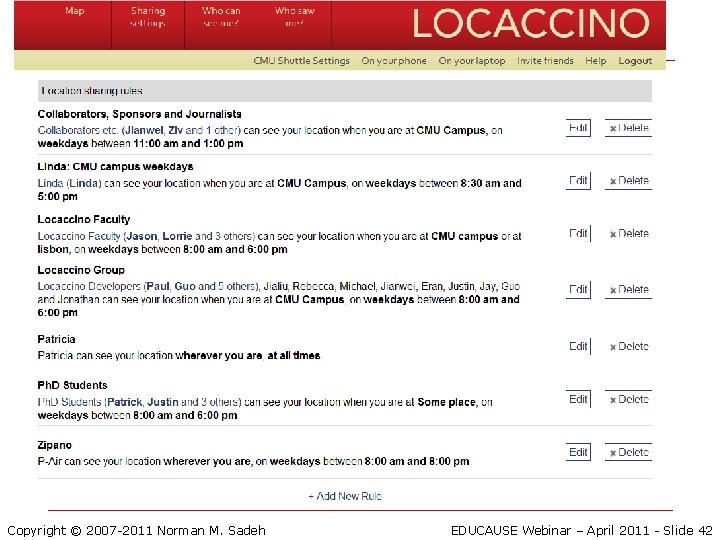
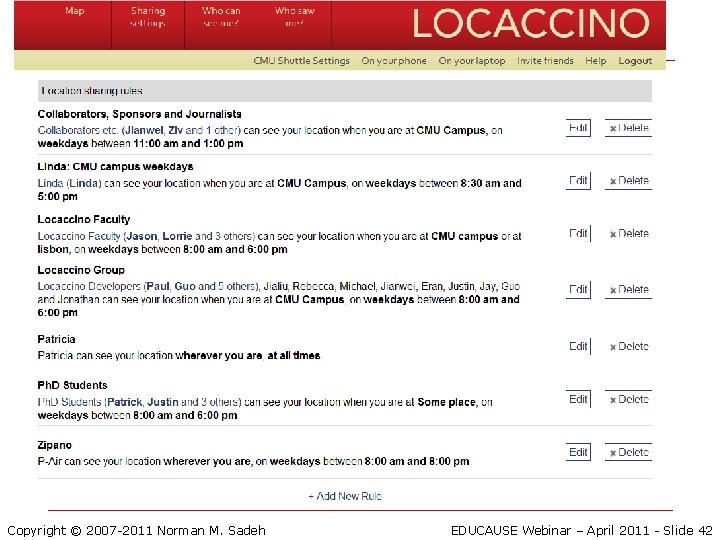
Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 42
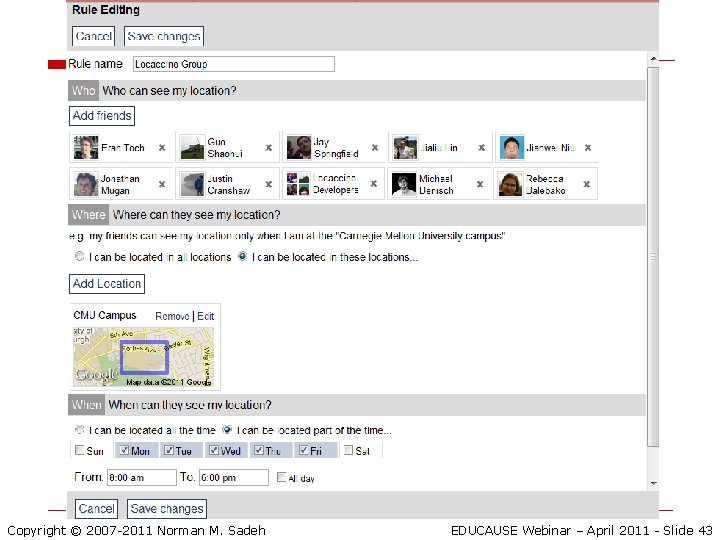
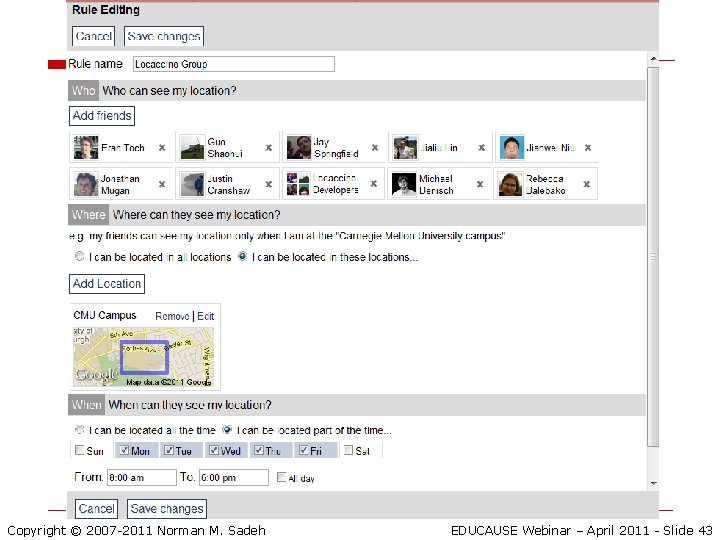
Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 43

Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 44
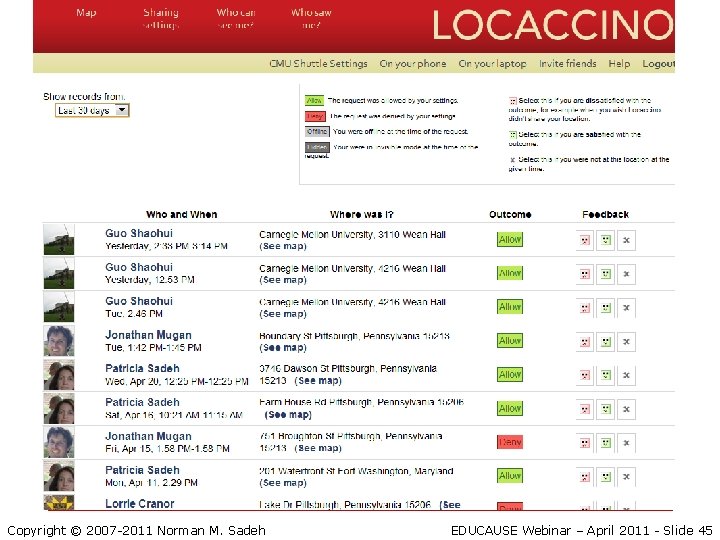
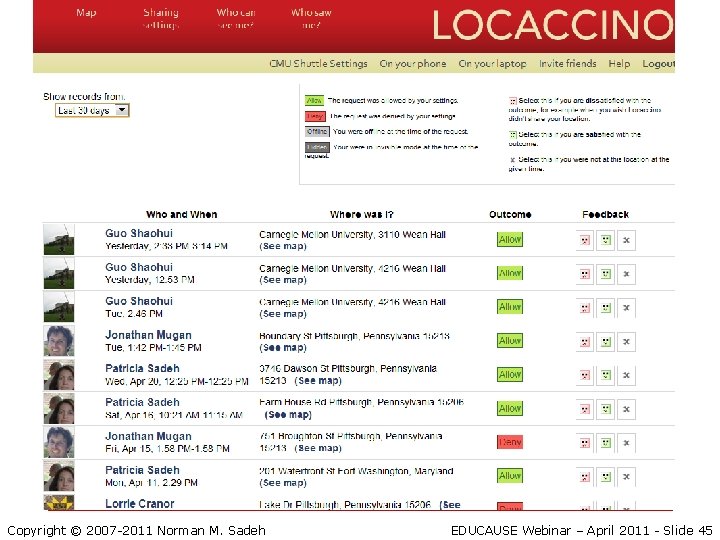
Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 45
CONCLUDING REMARKS Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 46
Concluding Remarks o Cell phones are wonderful devices … o Most of us can’t even remember how we could operate without them o …Yet they come with many risks o …General guidelines are difficult to articulate n Diversity of cell phones and usage scenarios o Yet in some areas such as phishing, results indicate that training can make a difference o We are extending this approach to mobile security at large Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 47
Q&A http: //mcom. cs. cmu. edu http: //wombatsecurity. com Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 48
References o o Scientific References n How to Foil “Phishing Scams”, Scientific American, L. Cranor n Teaching Johnny Not to Fall for Phish P. Kumaraguru, S. Sheng, A. Acquisti, L. Cranor, and J. Hong. ACM Transactions on Internet Technology, Vol. V, No. N, September 2009, Pages 1– 31. n Learning to Detect Phishing Emails I. Fette, N. Sadeh, and A. Tomasic. In Proceedings of the 16 th International Conference on World Wide Web, Banff, Alberta, Canada, May 8 -12, 2007. n Locaccino scientific publications: www. locaccino. org/science Case Studies & White Papers n “A Multi-Pronged Approach to Combat Phishing (Carnegie Mellon University case study)” n “Empirical Evaluation of Phish. Guru Embedded Training”, n “Cyber Security Training Game Teaches People to Avoid Phishing Attacks” Copyright © 2007 -2011 Norman M. Sadeh EDUCAUSE Webinar – April 2011 - Slide 49