Sliding Windows Succumbs to Big Mac Attack Colin
Sliding Windows Succumbs to Big Mac Attack Colin D. Walter www. co. umist. ac. uk CHES 2001 C. D. Walter, UMIST
Aims • Re-think the power of DPA; • Use it on a single exponentiation; • Longer keys are more unsafe! CHES 2001 C. D. Walter, UMIST 2
DPA Attack on RSA Summary: Differential Power Analysis (DPA) is used to determine the secret exponent in an embedded RSA cryptosystem. Assumption: The implementation uses a small multiplier whose power consumption is data dependent and measurable. CHES 2001 C. D. Walter, UMIST 3
History • P. Kocher, J. Jaffe & B. Jun Introduction to Differential Power Analysis and Related Attacks Crypto 99 • T. S. Messerges, E. A. Dabbish & R. H. Sloan Power Analysis Attacks of Modular Exponentiation in Smartcards CHES 99 CHES 2001 C. D. Walter, UMIST 4
Multipliers • Switching a gate in the H/W requires more power than not doing so; • On average, a Mult-Acc opn a×b+c has data dependent contributions roughly linear in the Hamming weights of a and b; • Variation occurs because of the initial state set up by the previous mult-acc opn. CHES 2001 C. D. Walter, UMIST 5
First Results • This theory was checked by simulation and found to be broadly correct; • Refinements were made to this model (which will be reported elsewhere); • These give a more precise & detailed partial ordering. CHES 2001 C. D. Walter, UMIST 6
Combining Traces I • The long integer product A×B in an exponentiation contains a large number of small digit multiply-accumulates: ai×bj+ck • Identify the power subtraces of each ai×bj+ck from the power trace of A×B; • Average the power traces for fixed i as j varies: this gives a trace tri which depends on ai but only the average of the digits of B. CHES 2001 C. D. Walter, UMIST 7
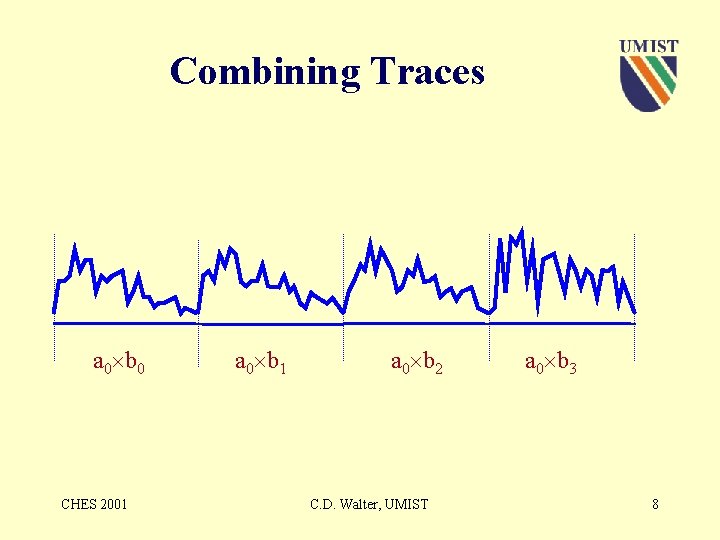
Combining Traces a 0 b 0 CHES 2001 a 0 b 2 C. D. Walter, UMIST a 0 b 3 8
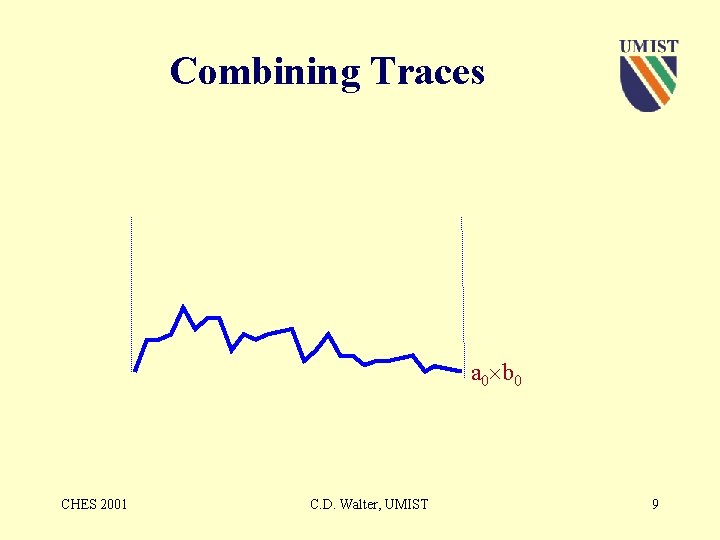
Combining Traces a 0 b 0 CHES 2001 C. D. Walter, UMIST 9
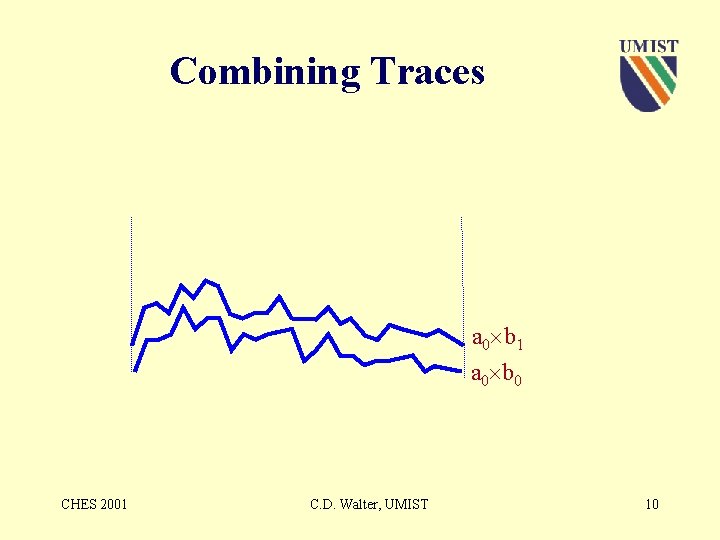
Combining Traces a 0 b 1 a 0 b 0 CHES 2001 C. D. Walter, UMIST 10
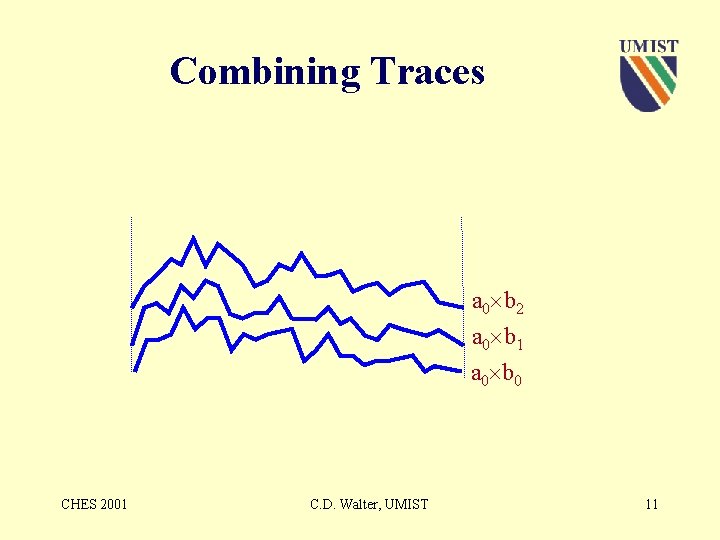
Combining Traces a 0 b 2 a 0 b 1 a 0 b 0 CHES 2001 C. D. Walter, UMIST 11
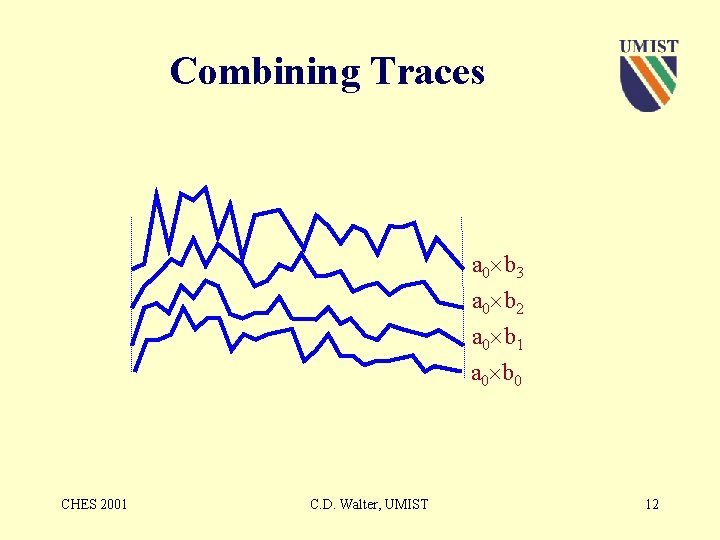
Combining Traces a 0 b 3 a 0 b 2 a 0 b 1 a 0 b 0 CHES 2001 C. D. Walter, UMIST 12
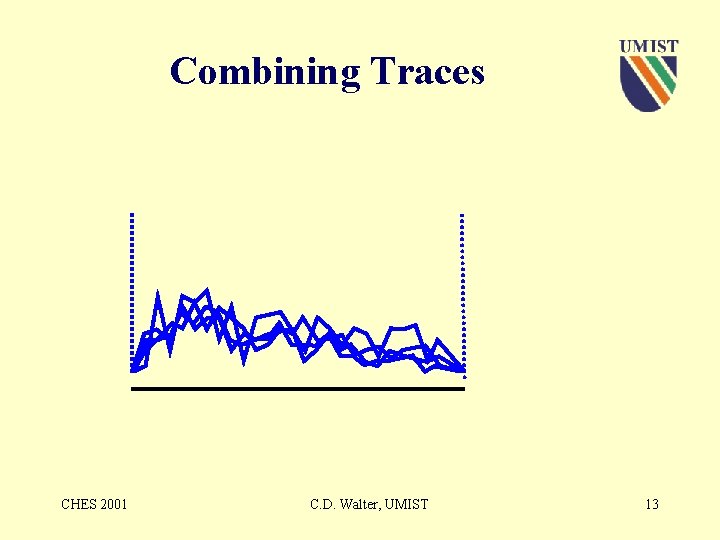
Combining Traces CHES 2001 C. D. Walter, UMIST 13
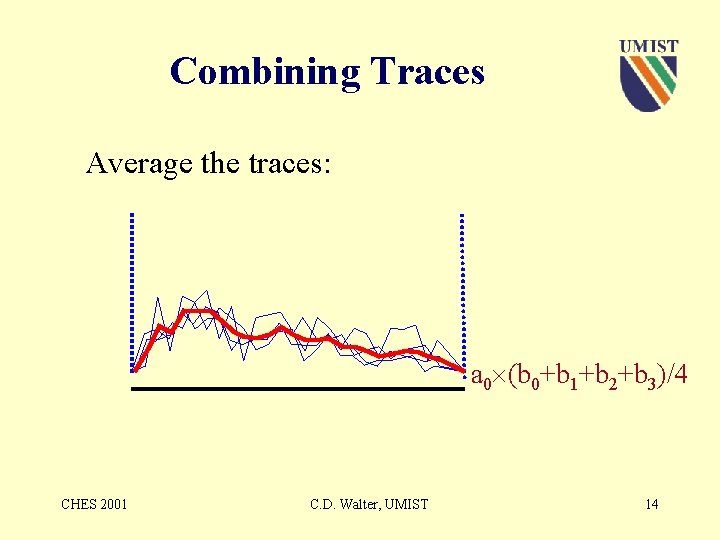
Combining Traces Average the traces: a 0 (b 0+b 1+b 2+b 3)/4 CHES 2001 C. D. Walter, UMIST 14
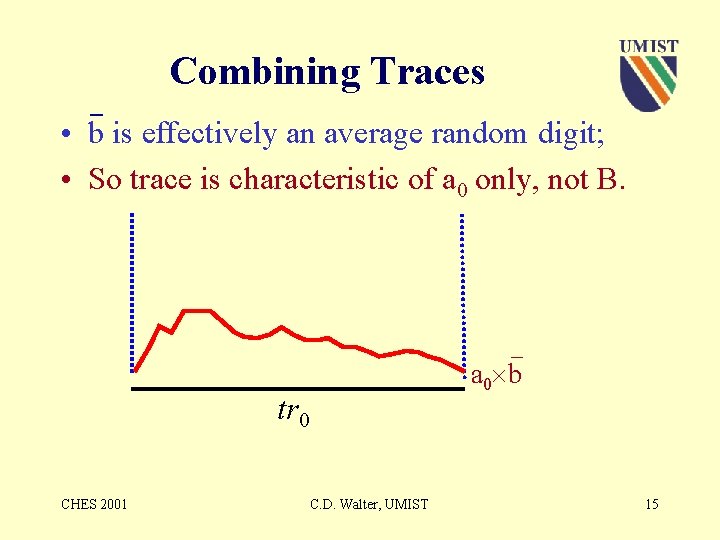
_ Combining Traces • b is effectively an average random digit; • So trace is characteristic of a 0 only, not B. _ a 0 b tr 0 CHES 2001 C. D. Walter, UMIST 15
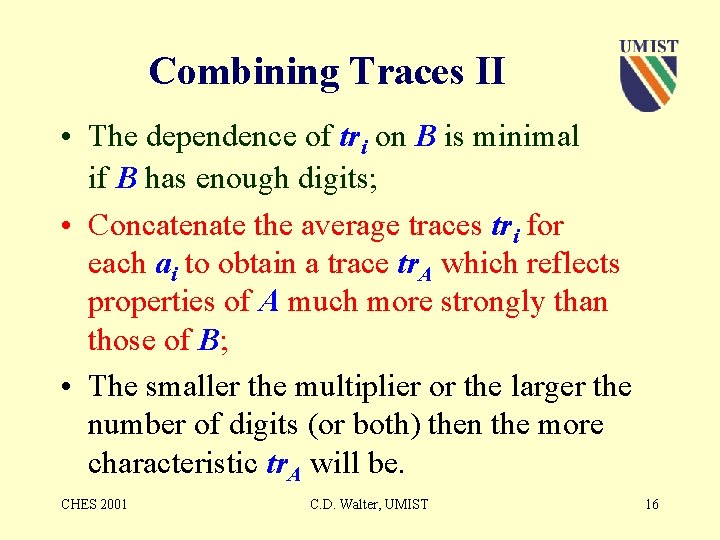
Combining Traces II • The dependence of tri on B is minimal if B has enough digits; • Concatenate the average traces tri for each ai to obtain a trace tr. A which reflects properties of A much more strongly than those of B; • The smaller the multiplier or the larger the number of digits (or both) then the more characteristic tr. A will be. CHES 2001 C. D. Walter, UMIST 16
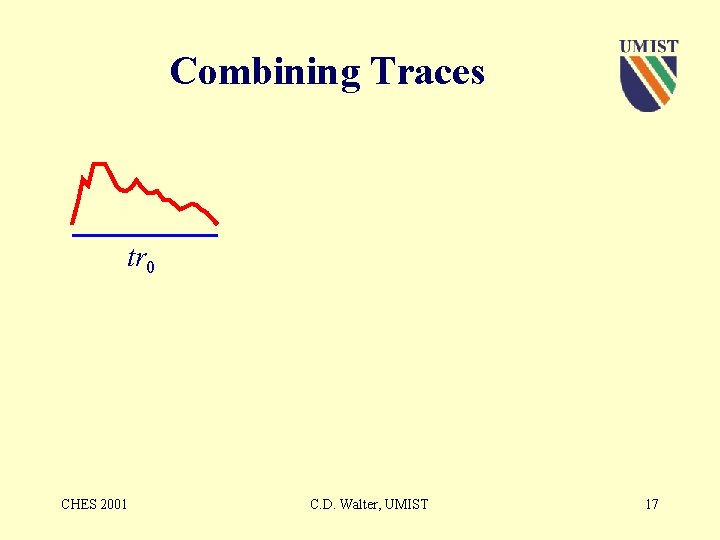
Combining Traces tr 0 CHES 2001 C. D. Walter, UMIST 17
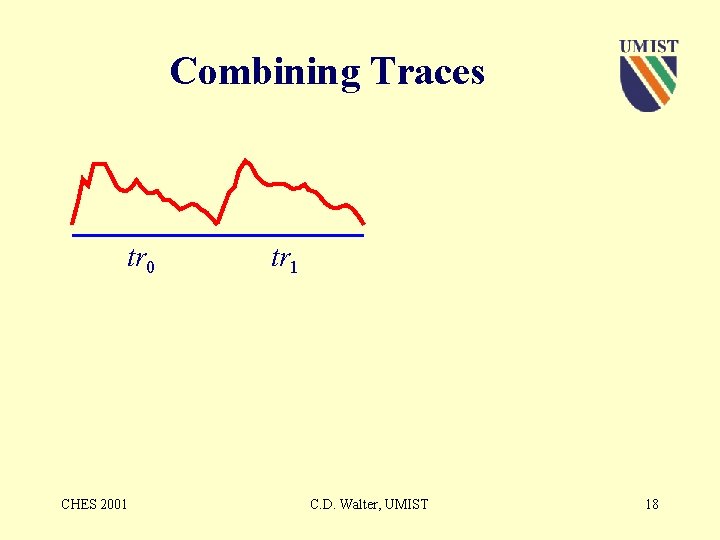
Combining Traces tr 0 CHES 2001 tr 1 C. D. Walter, UMIST 18
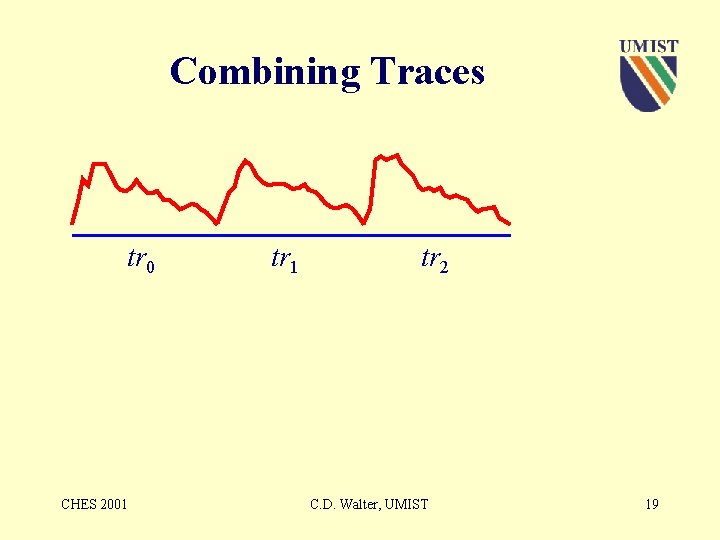
Combining Traces tr 0 CHES 2001 tr 2 C. D. Walter, UMIST 19
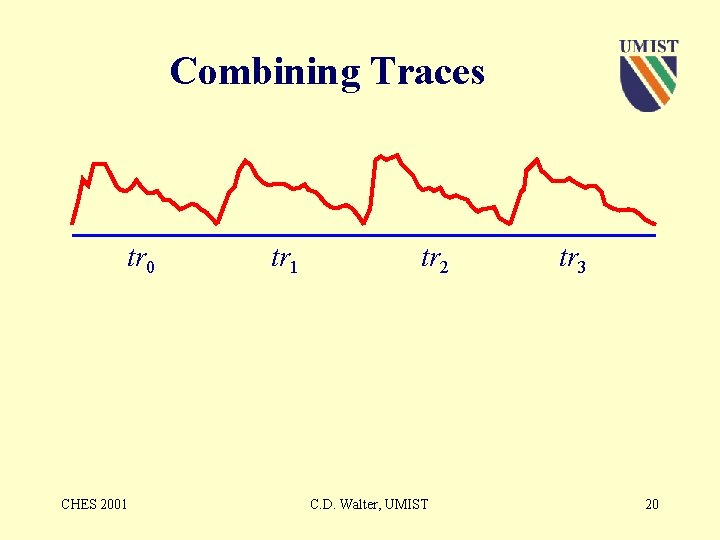
Combining Traces tr 0 CHES 2001 tr 2 C. D. Walter, UMIST tr 3 20
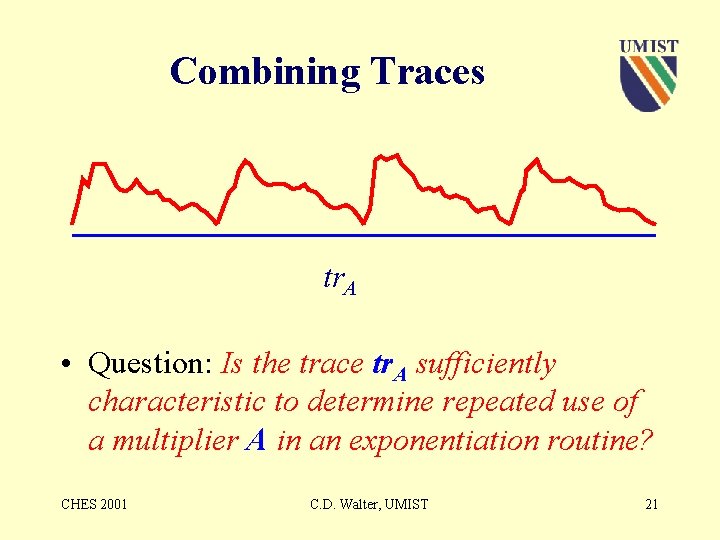
Combining Traces tr. A • Question: Is the trace tr. A sufficiently characteristic to determine repeated use of a multiplier A in an exponentiation routine? CHES 2001 C. D. Walter, UMIST 21
Distinguish Digits? • Averaging over the digits of B has reduced the noise level; • In m-ary exponentiation we only need to distinguish: – squares from multiplies – the multipliers A(1), A(2), A(3), …, A(m– 1) • For small enough m and large enough number of digits they can be distinguished in a simulation of clean data. CHES 2001 C. D. Walter, UMIST 22
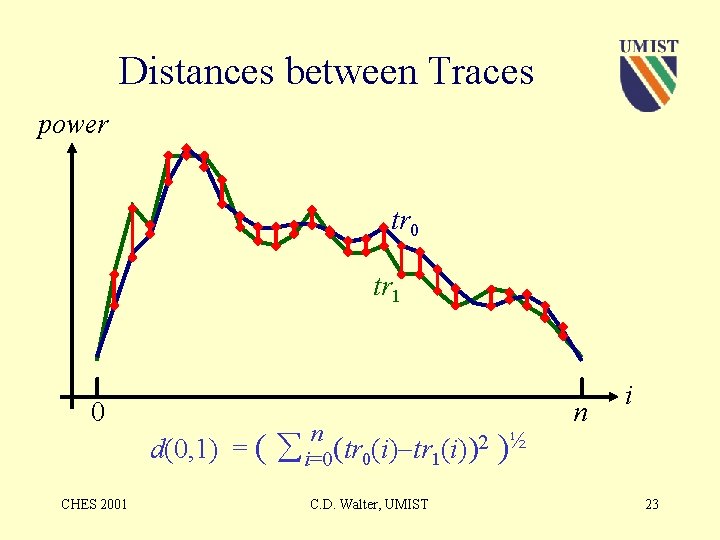
Distances between Traces power tr 0 tr 1 0 CHES 2001 d(0, 1) = ( n i=0(tr 0(i) tr 1(i))2 )½ C. D. Walter, UMIST n i 23
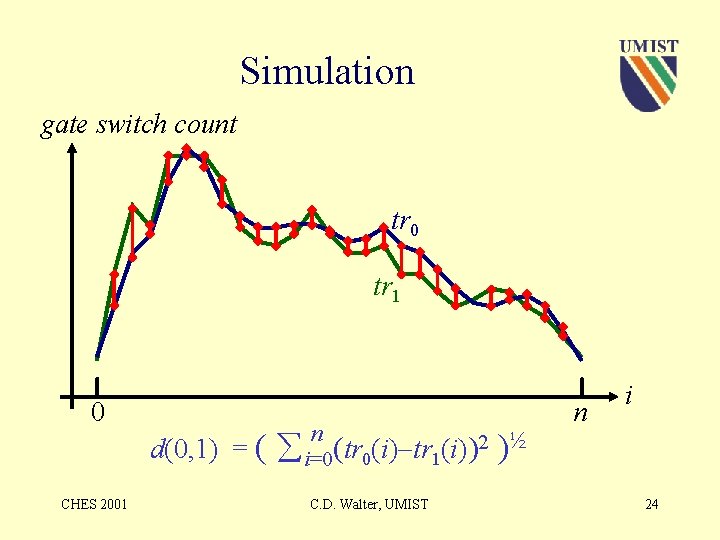
Simulation gate switch count tr 0 tr 1 0 CHES 2001 d(0, 1) = ( n i=0(tr 0(i) tr 1(i))2 )½ C. D. Walter, UMIST n i 24
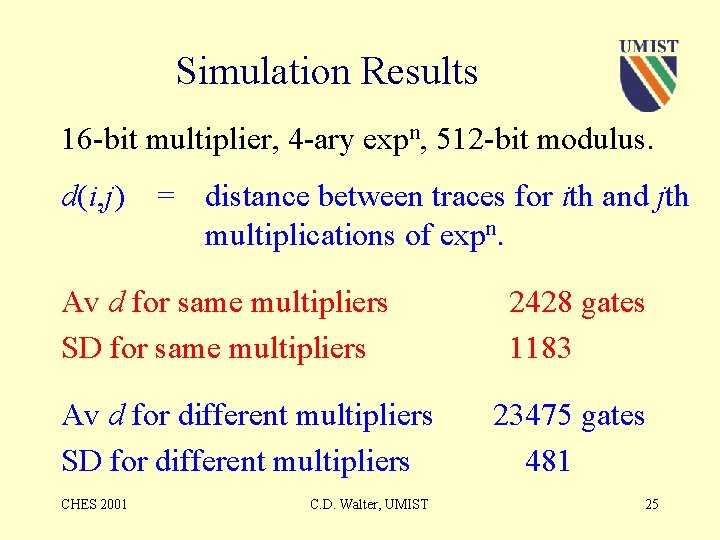
Simulation Results 16 -bit multiplier, 4 -ary expn, 512 -bit modulus. d(i, j) = distance between traces for ith and jth multiplications of expn. Av d for same multipliers SD for same multipliers Av d for different multipliers SD for different multipliers CHES 2001 C. D. Walter, UMIST 2428 gates 1183 23475 gates 481 25
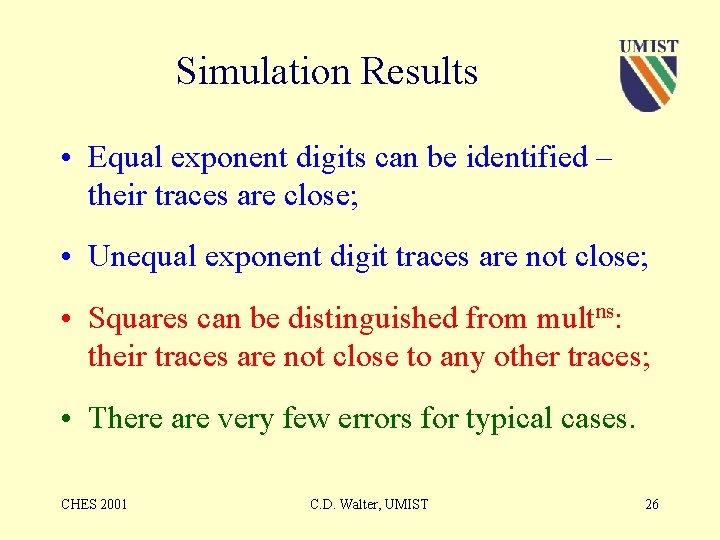
Simulation Results • Equal exponent digits can be identified – their traces are close; • Unequal exponent digit traces are not close; • Squares can be distinguished from multns: their traces are not close to any other traces; • There are very few errors for typical cases. CHES 2001 C. D. Walter, UMIST 26
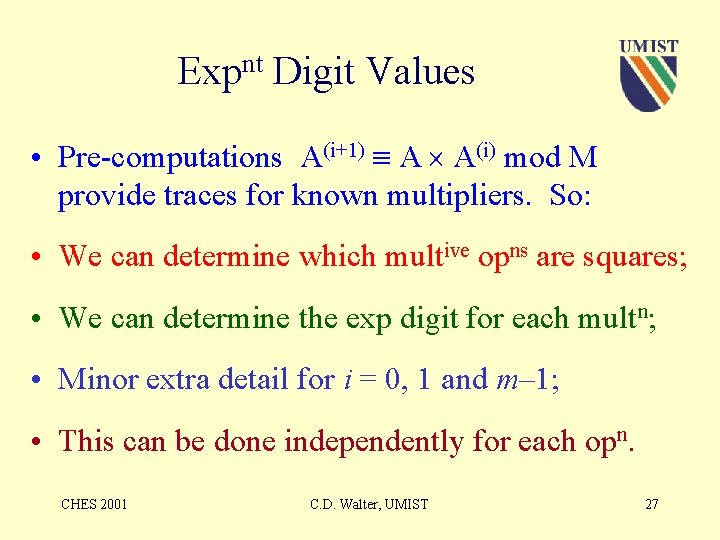
Expnt Digit Values • Pre-computations A(i+1) A A(i) mod M provide traces for known multipliers. So: • We can determine which multive opns are squares; • We can determine the exp digit for each multn; • Minor extra detail for i = 0, 1 and m– 1; • This can be done independently for each opn. CHES 2001 C. D. Walter, UMIST 27
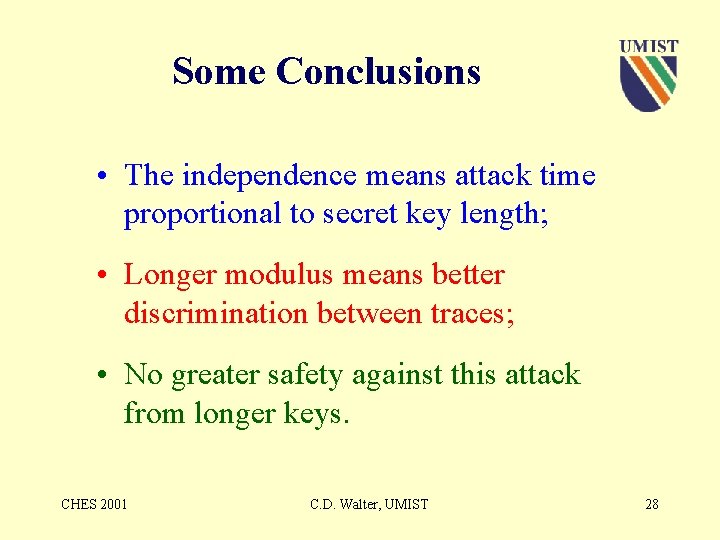
Some Conclusions • The independence means attack time proportional to secret key length; • Longer modulus means better discrimination between traces; • No greater safety against this attack from longer keys. CHES 2001 C. D. Walter, UMIST 28
Warning • With the usual DPA averaging already done, it may be possible to use a single exponentiation to obtain the secret key; • So using expnt d+rφ(M) with random r may be no defence. CHES 2001 C. D. Walter, UMIST 29
Final Conclusions • Sliding Windows expn method may be broken in this way; • Like a Big Mac, you can nibble away at each secret exponent digit in turn and enjoy finding out its value. CHES 2001 C. D. Walter, UMIST 30
- Slides: 30