Slides Prepared By Adeel Ahmed Updated By Syed
Slides Prepared By Adeel Ahmed, Updated By, Syed Ameen Quadri. 1
Rules of Access List • All deny statements have to be given First • There should be at least one Permit statement • An implicit deny blocks all traffic by default when there is no match (an invisible statement). • Can have one access-list per interface per direction. (i. e. ) Two access-list per interface, one in inbound direction and one in outbound direction. • Works in Sequential order • Editing of access-lists is not possible (i. e) Selectively adding or removing access-list statements is not possible. 2
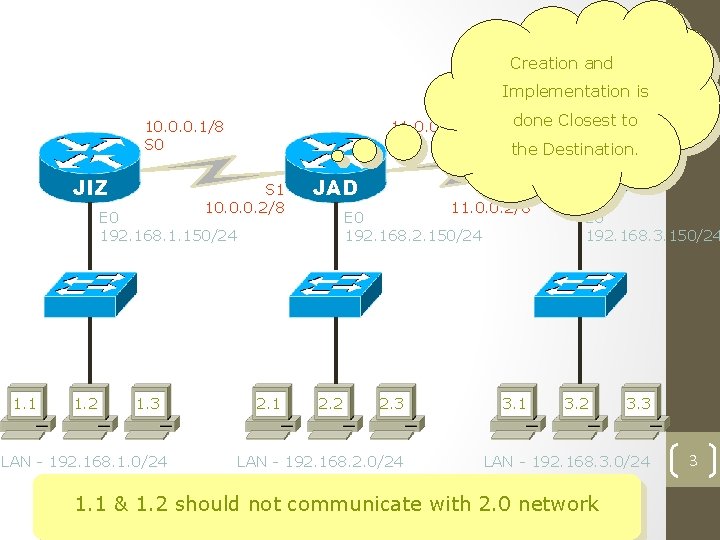
Standard ACL - Network Diagram Creation and Implementation is 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 done Closest to the Destination. S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 1. 1 & 1. 2 should not communicate with 2. 0 network 3
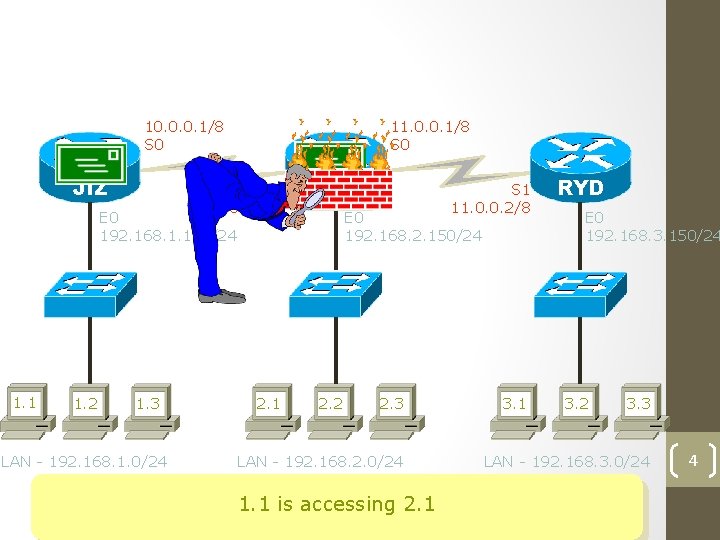
How Standard ACL Works ? 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 1. 1 is accessing 2. 1 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 4
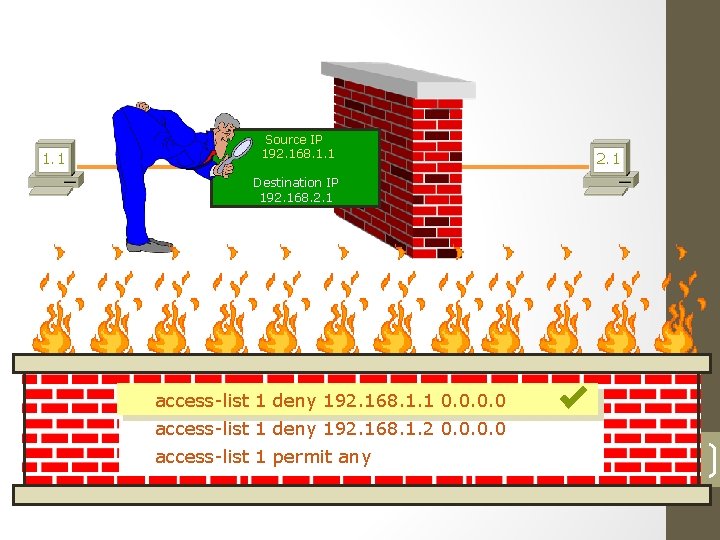
How Standard ACL Works ? 1. 1 Source IP 192. 168. 1. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 1 deny 192. 168. 1. 1 0. 0 access-list 1 deny 192. 168. 1. 2 0. 0 access-list 1 permit any 5
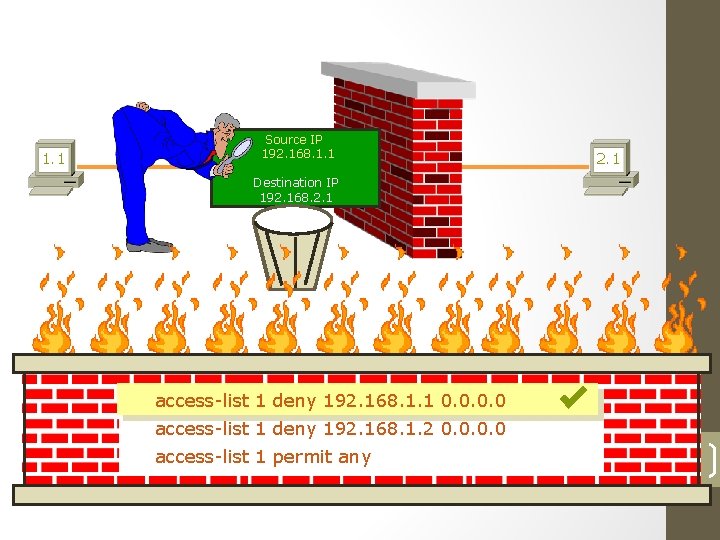
How Standard ACL Works ? 1. 1 Source IP 192. 168. 1. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 1 deny 192. 168. 1. 1 0. 0 access-list 1 deny 192. 168. 1. 2 0. 0 access-list 1 permit any 6
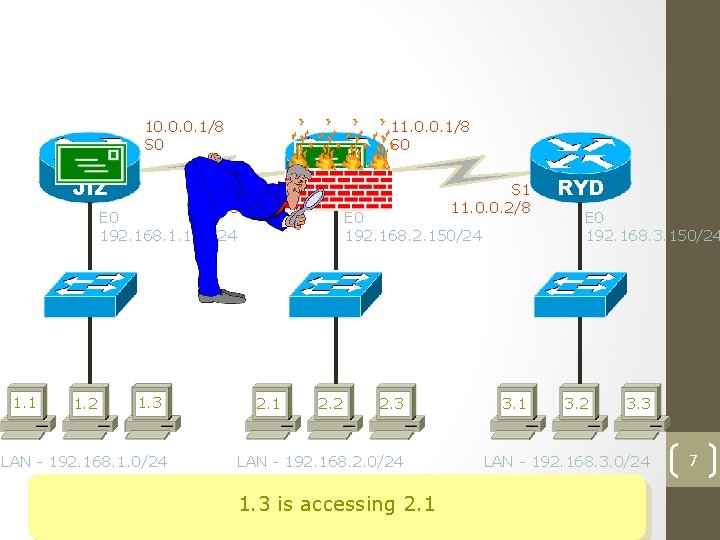
How Standard ACL Works ? 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 1. 3 is accessing 2. 1 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 7
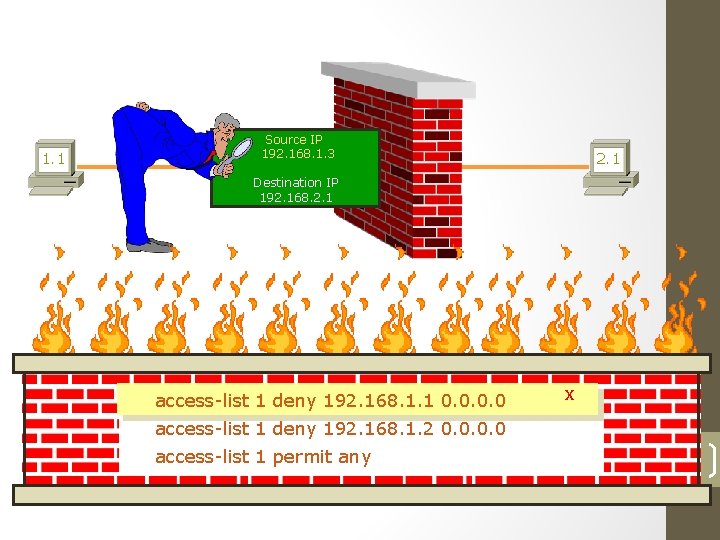
How Standard ACL Works ? 1. 1 Source IP 192. 168. 1. 3 2. 1 Destination IP 192. 168. 2. 1 access-list 1 deny 192. 168. 1. 1 0. 0 x access-list 1 deny 192. 168. 1. 2 0. 0 access-list 1 permit any 8
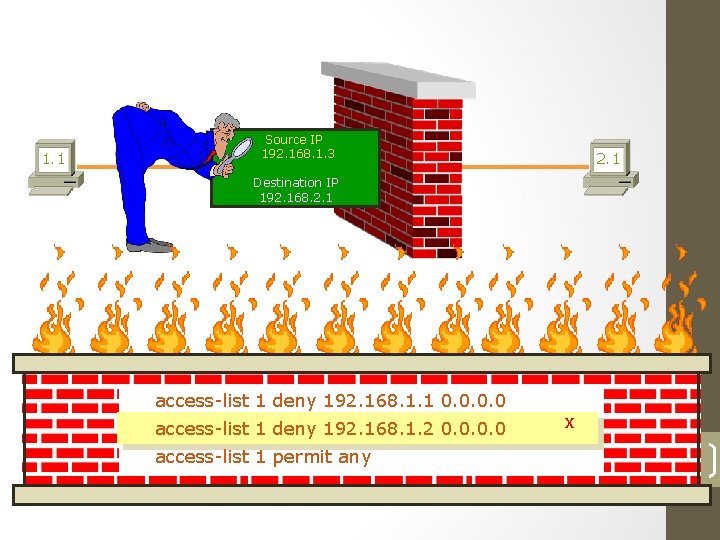
How Standard ACL Works ? 1. 1 Source IP 192. 168. 1. 3 2. 1 Destination IP 192. 168. 2. 1 access-list 1 deny 192. 168. 1. 1 0. 0 access-list 1 deny 192. 168. 1. 2 0. 0 access-list 1 permit any x 9
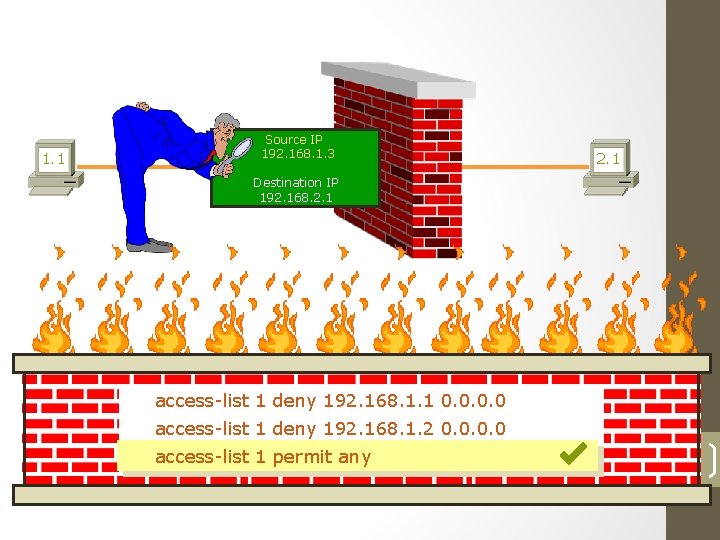
How Standard ACL Works ? 1. 1 Source IP 192. 168. 1. 3 2. 1 Destination IP 192. 168. 2. 1 access-list 1 deny 192. 168. 1. 1 0. 0 access-list 1 deny 192. 168. 1. 2 0. 0 access-list 1 permit any 10
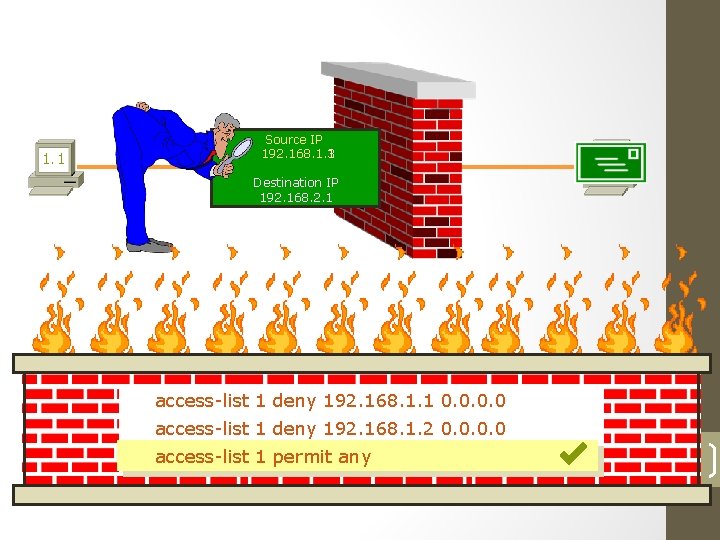
1. 1 Source IP 192. 168. 1. 3 192. 168. 1. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 1 deny 192. 168. 1. 1 0. 0 access-list 1 deny 192. 168. 1. 2 0. 0 access-list 1 permit any 11
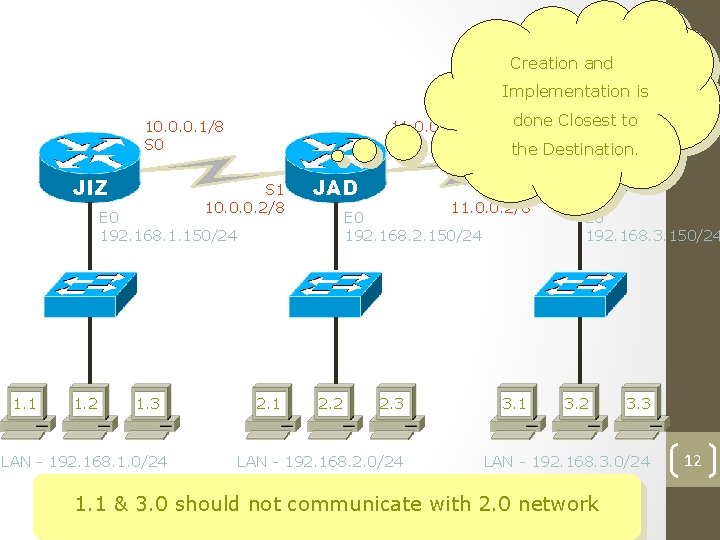
Standard ACL - Network Diagram Creation and Implementation is 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 done Closest to the Destination. S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 1. 1 & 3. 0 should not communicate with 2. 0 network 12
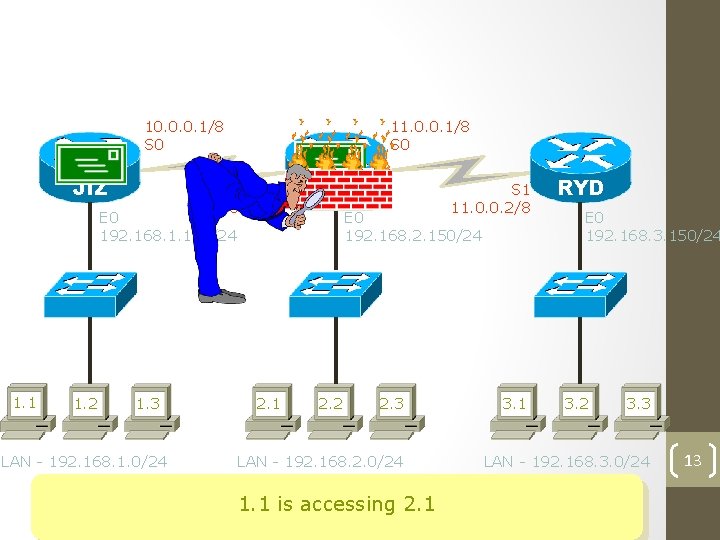
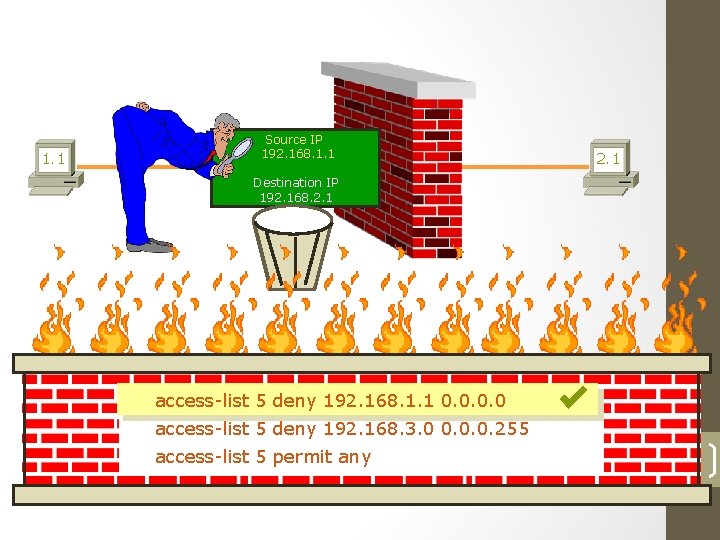
How Standard ACL Works ? 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 1. 1 is accessing 2. 1 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 13
How Standard ACL Works ? 1. 1 Source IP 192. 168. 1. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any 14
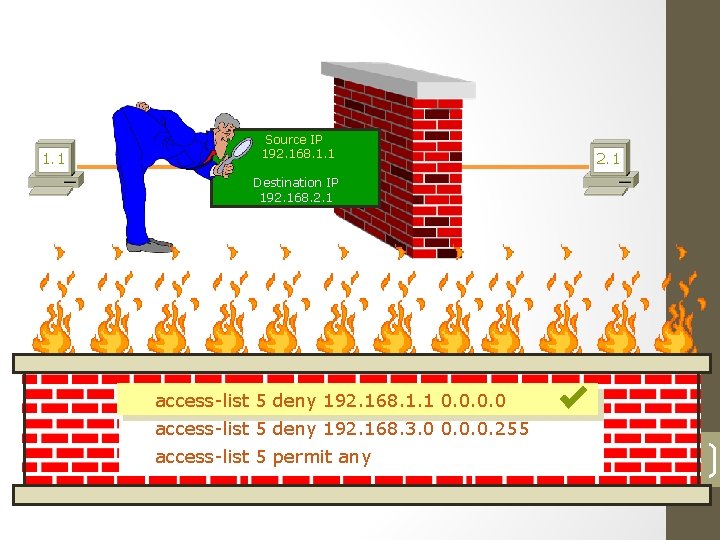
How Standard ACL Works ? 1. 1 Source IP 192. 168. 1. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any 15
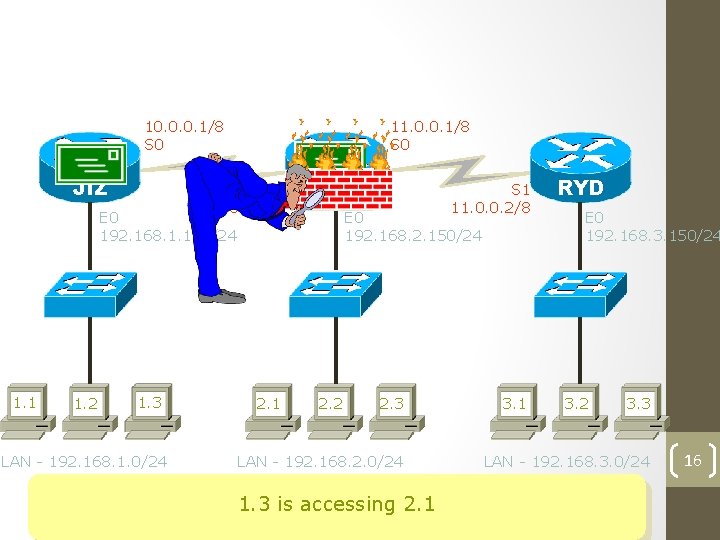
How Standard ACL Works ? 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 1. 3 is accessing 2. 1 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 16
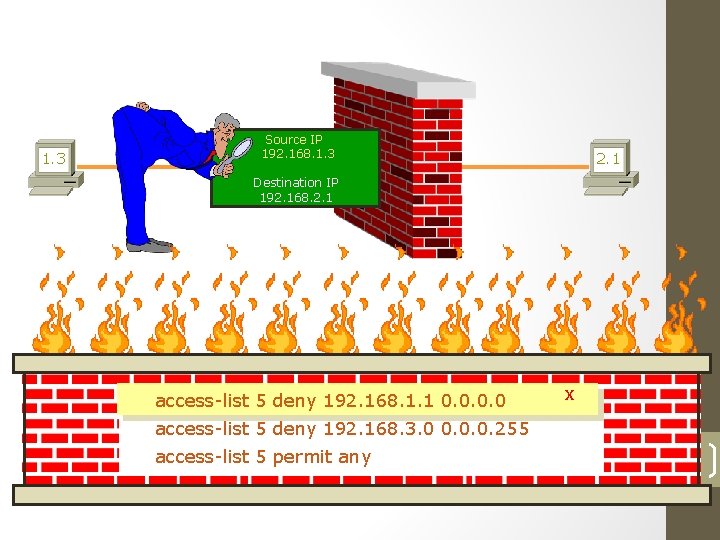
How Standard ACL Works ? 1. 3 Source IP 192. 168. 1. 3 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 x access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any 17
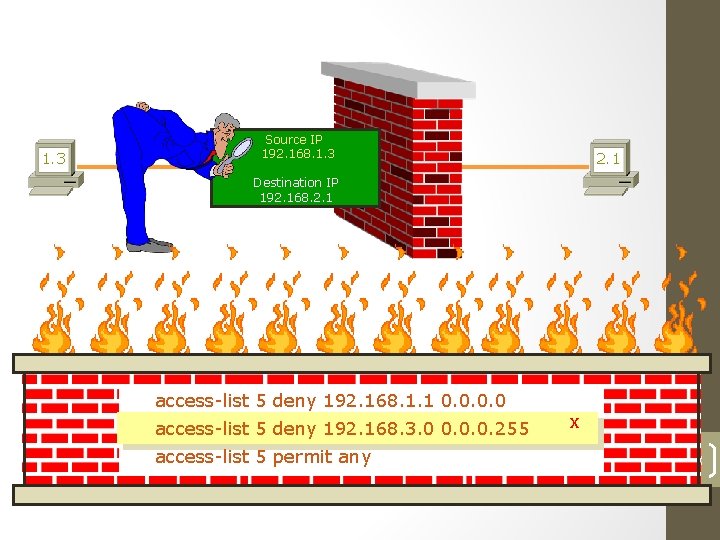
How Standard ACL Works ? 1. 3 Source IP 192. 168. 1. 3 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any x 18
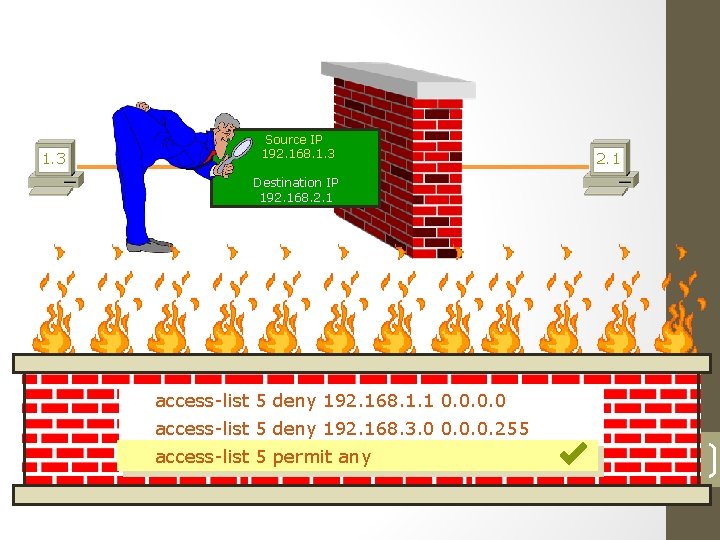
How Standard ACL Works ? 1. 3 Source IP 192. 168. 1. 3 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any 19
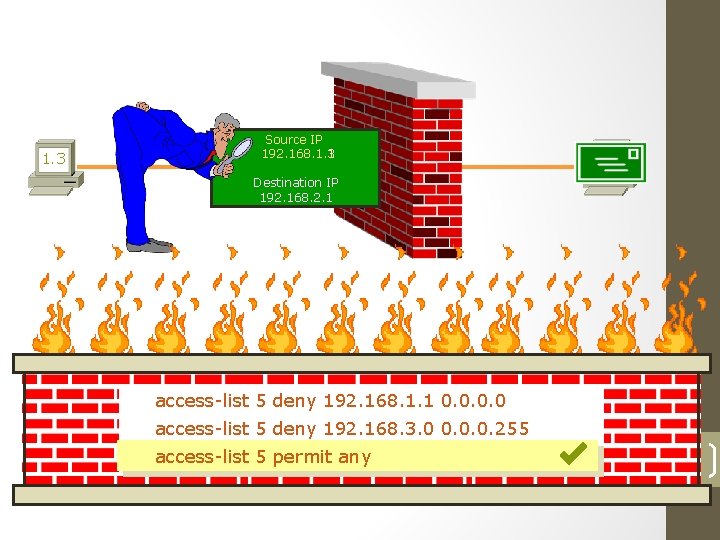
1. 3 Source IP 192. 168. 1. 3 192. 168. 1. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any 20
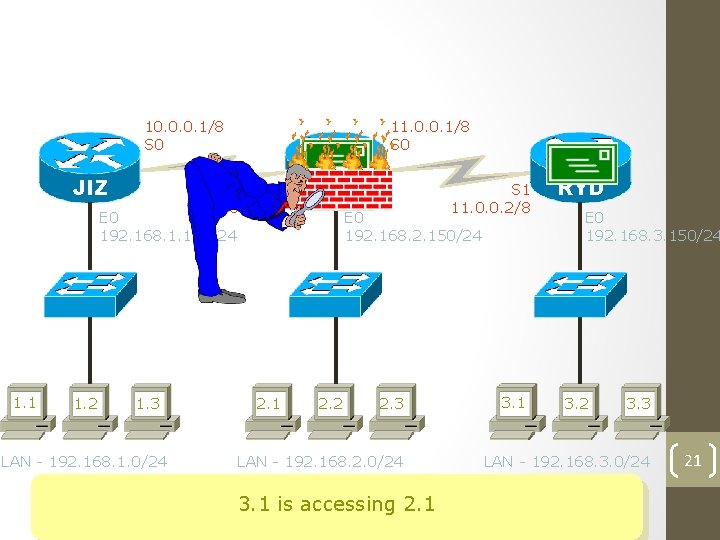
How Standard ACL Works ? 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 3. 1 is accessing 2. 1 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 21
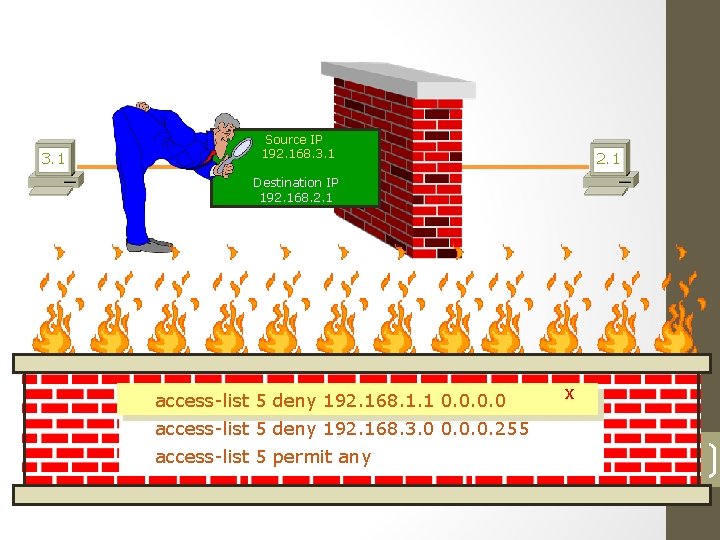
How Standard ACL Works ? 3. 1 Source IP 192. 168. 3. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 x access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any 22
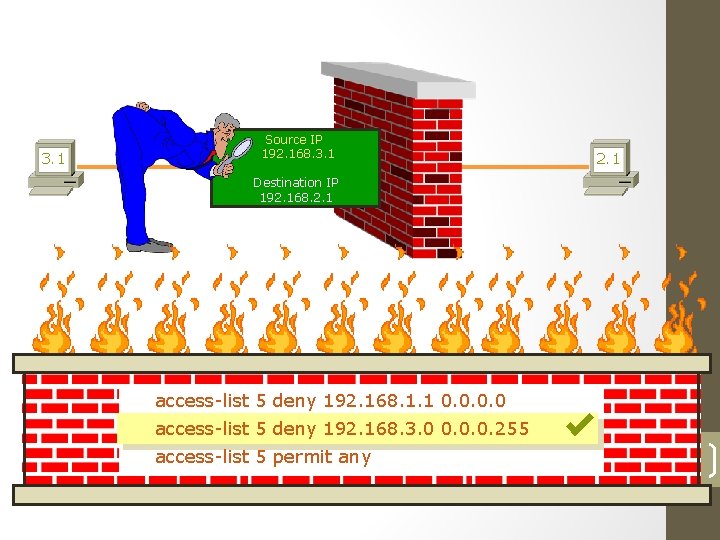
How Standard ACL Works ? 3. 1 Source IP 192. 168. 3. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any 23
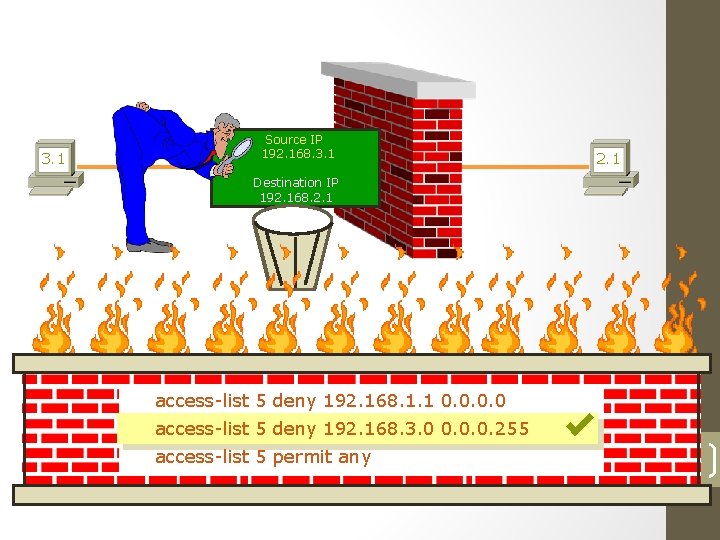
How Standard ACL Works ? 3. 1 Source IP 192. 168. 3. 1 2. 1 Destination IP 192. 168. 2. 1 access-list 5 deny 192. 168. 1. 1 0. 0 access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 access-list 5 permit any 24
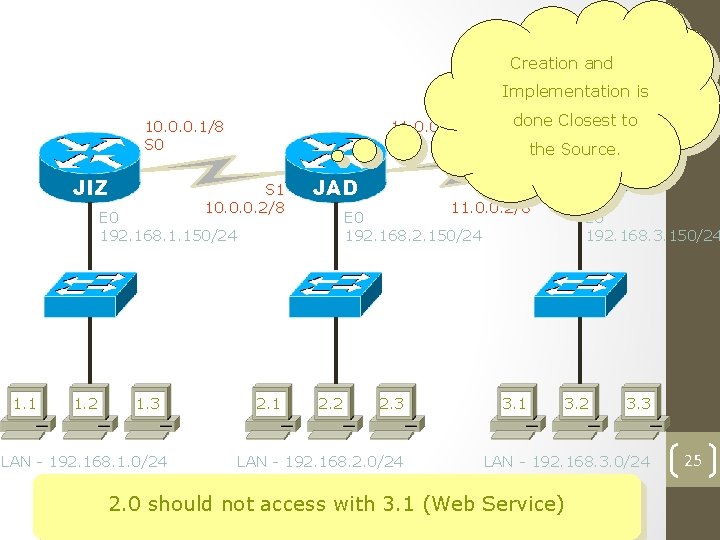
Extended ACL - Network Diagram Creation and Implementation is 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 done Closest to the Source. S 1 11. 0. 0. 2/8 RYD E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 3. 1 E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 2. 0 should not access with 3. 1 (Web Service) 25
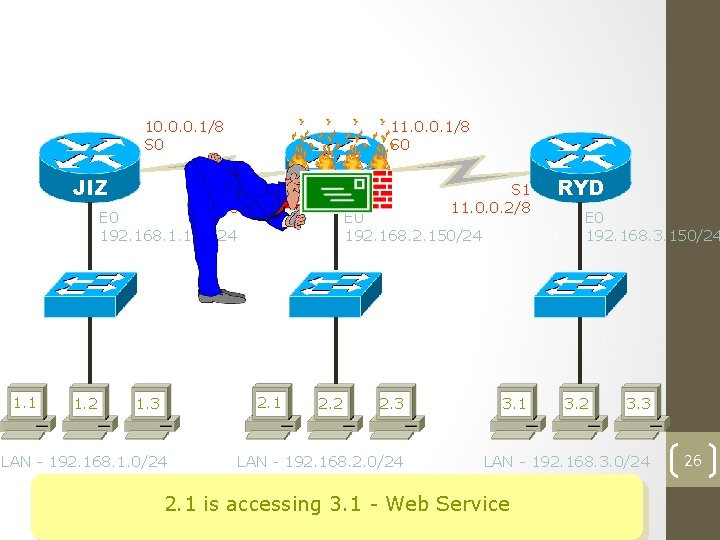
How Extended ACL Works ? 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 2. 1 1. 3 LAN - 192. 168. 1. 0/24 S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 2. 1 is accessing 3. 1 - Web Service 26
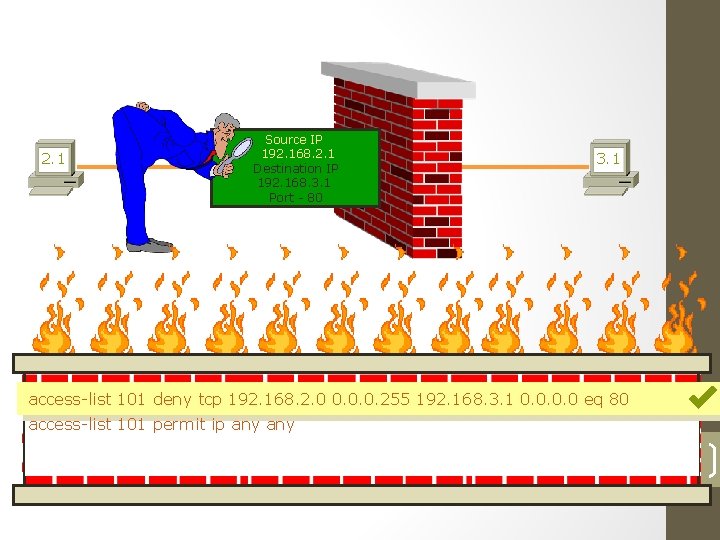
How Extended ACL Works ? 2. 1 Source IP 192. 168. 2. 1 Destination IP 192. 168. 3. 1 Port - 80 3. 1 access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 access-list 101 permit ip any 27
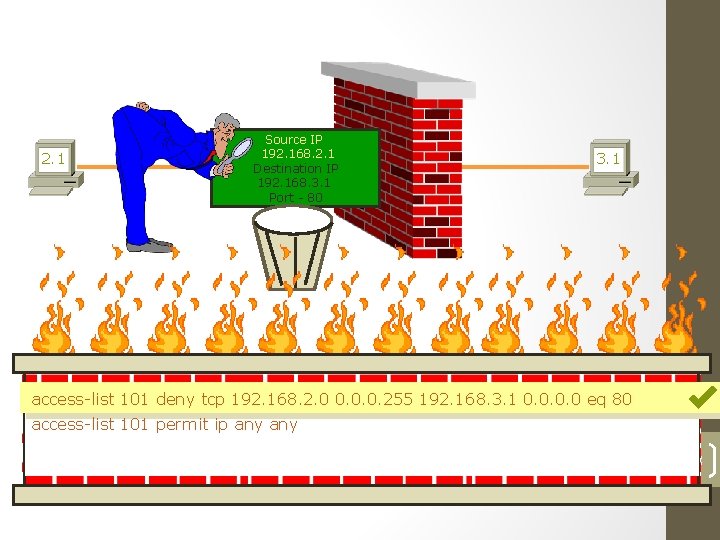
How Extended ACL Works ? 2. 1 Source IP 192. 168. 2. 1 Destination IP 192. 168. 3. 1 Port - 80 3. 1 access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 access-list 101 permit ip any 28
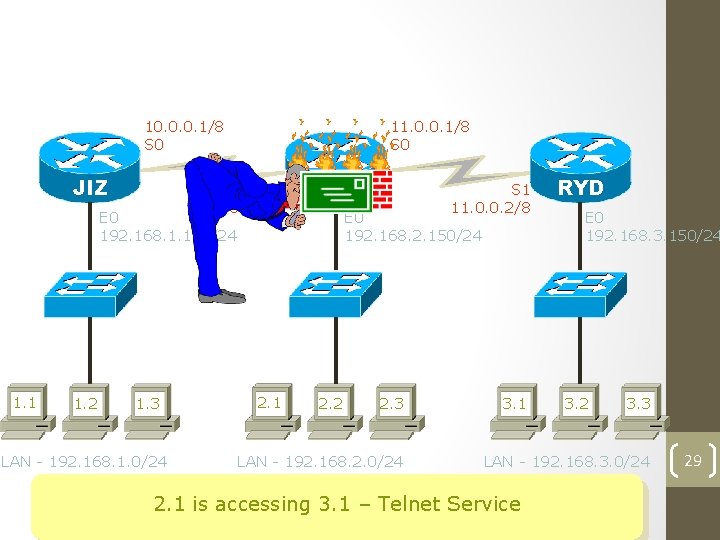
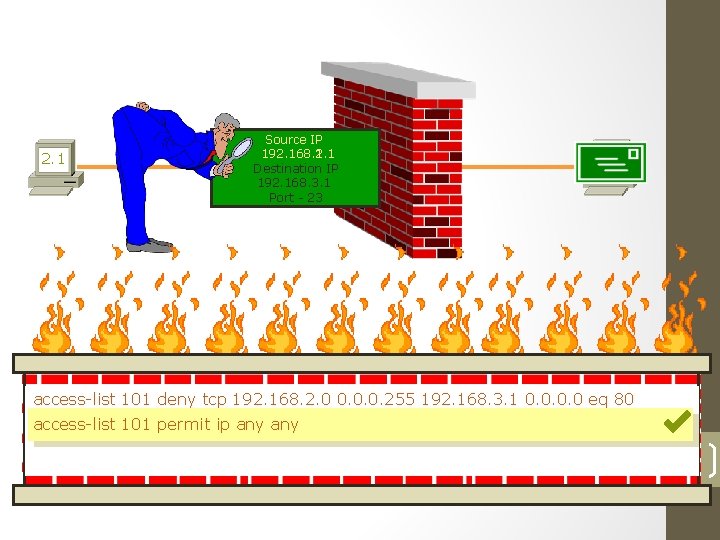
How Extended ACL Works ? 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 1. 3 LAN - 192. 168. 1. 0/24 2. 1 S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 2. 1 is accessing 3. 1 – Telnet Service 29
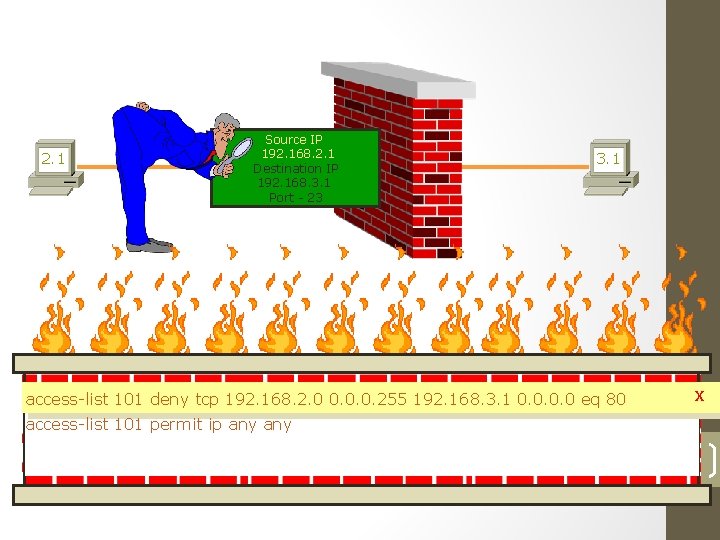
How Extended ACL Works ? 2. 1 Source IP 192. 168. 2. 1 Destination IP 192. 168. 3. 1 Port - 23 3. 1 access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 x access-list 101 permit ip any 30
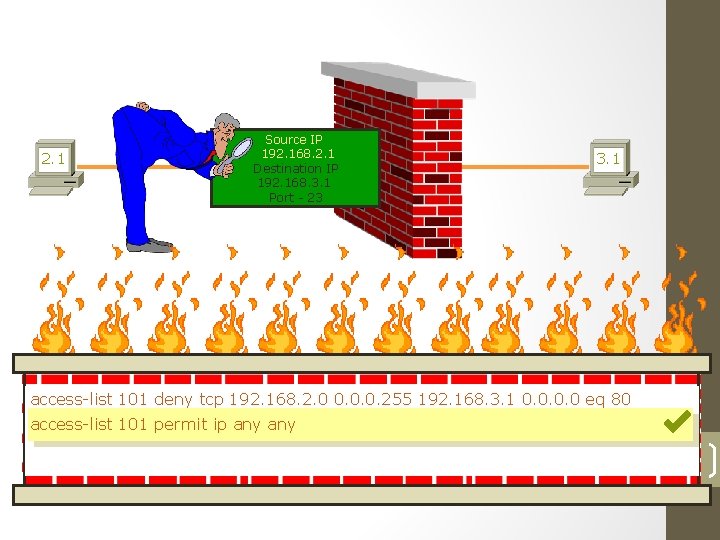
How Extended ACL Works ? 2. 1 Source IP 192. 168. 2. 1 Destination IP 192. 168. 3. 1 Port - 23 3. 1 access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 access-list 101 permit ip any 31
How Extended ACL Works ? 2. 1 Source IP 192. 168. 2. 1 192. 168. 1. 1 Destination IP 192. 168. 3. 1 Port - 23 3. 1 access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 access-list 101 permit ip any 32
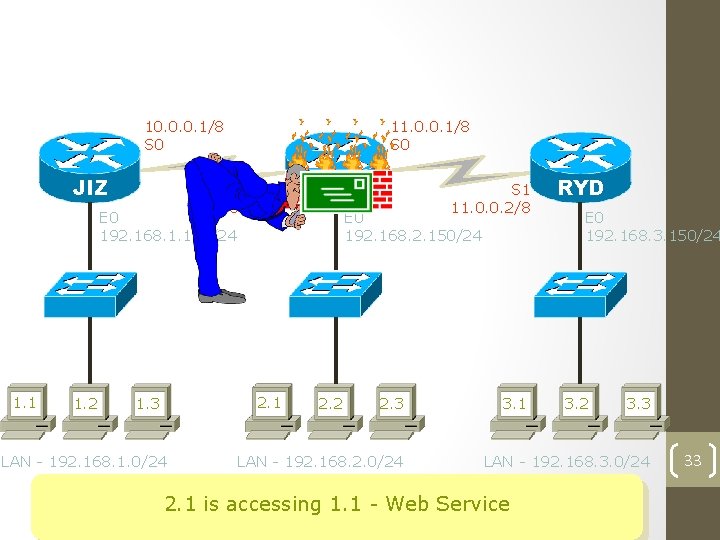
How Extended ACL Works ? 10. 0. 0. 1/8 S 0 JIZ 11. 0. 0. 1/8 S 0 S 1 10. 0. 0. 2/8 JAD E 0 192. 168. 1. 150/24 1. 1 1. 2 2. 1 1. 3 LAN - 192. 168. 1. 0/24 S 1 11. 0. 0. 2/8 E 0 192. 168. 2. 150/24 2. 2 2. 3 LAN - 192. 168. 2. 0/24 3. 1 RYD E 0 192. 168. 3. 150/24 3. 2 3. 3 LAN - 192. 168. 3. 0/24 2. 1 is accessing 1. 1 - Web Service 33
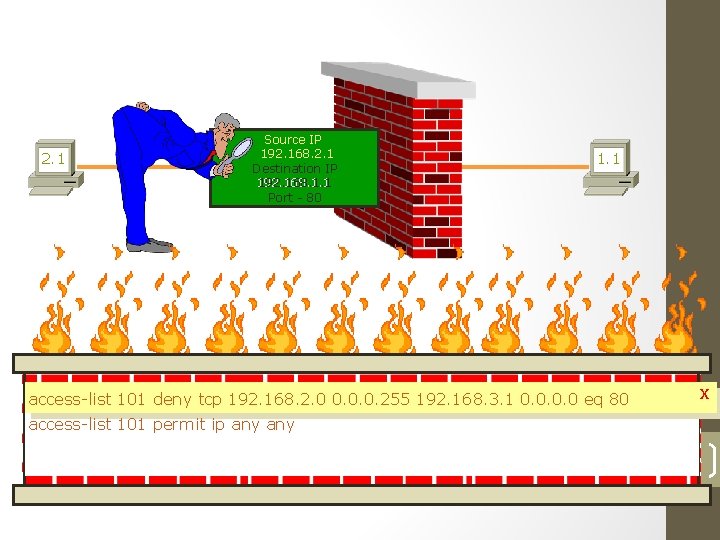
How Extended ACL Works ? 2. 1 Source IP 192. 168. 2. 1 Destination IP 192. 168. 1. 1 Port - 80 1. 1 access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 x access-list 101 permit ip any 34
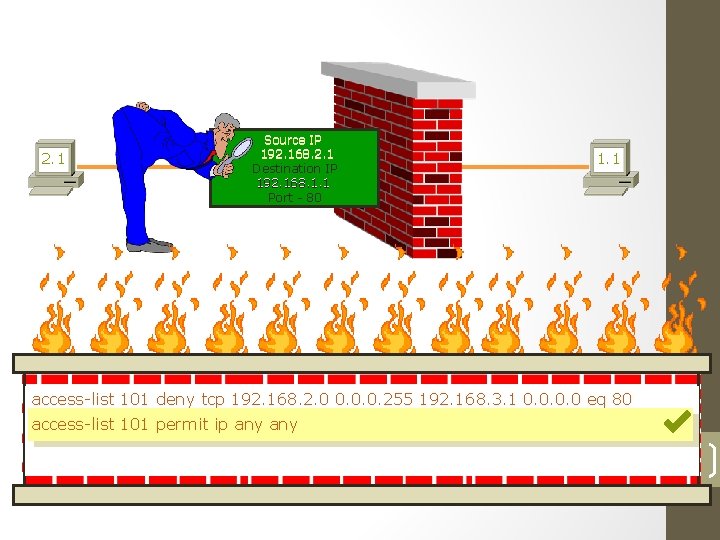
How Extended ACL Works ? 2. 1 Source IP 192. 168. 2. 1 Destination IP 192. 168. 1. 1 Port - 80 1. 1 access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 access-list 101 permit ip any 35
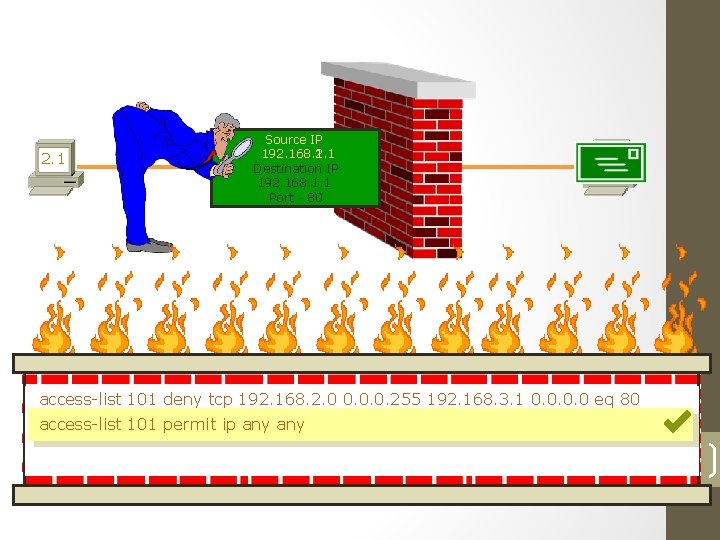
How Extended ACL Works ? 2. 1 Source IP 192. 168. 2. 1 192. 168. 1. 1 Destination IP 192. 168. 1. 1 Port - 80 1. 1 access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 access-list 101 permit ip any 36
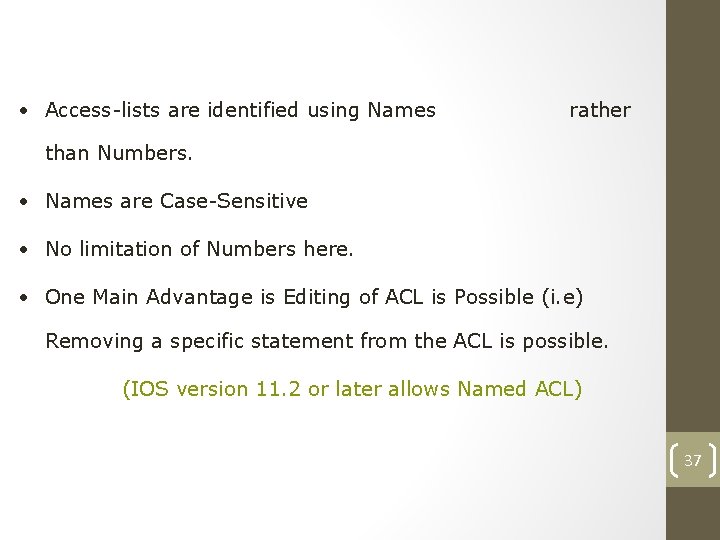
Named Access List • Access-lists are identified using Names rather than Numbers. • Names are Case-Sensitive • No limitation of Numbers here. • One Main Advantage is Editing of ACL is Possible (i. e) Removing a specific statement from the ACL is possible. (IOS version 11. 2 or later allows Named ACL) 37
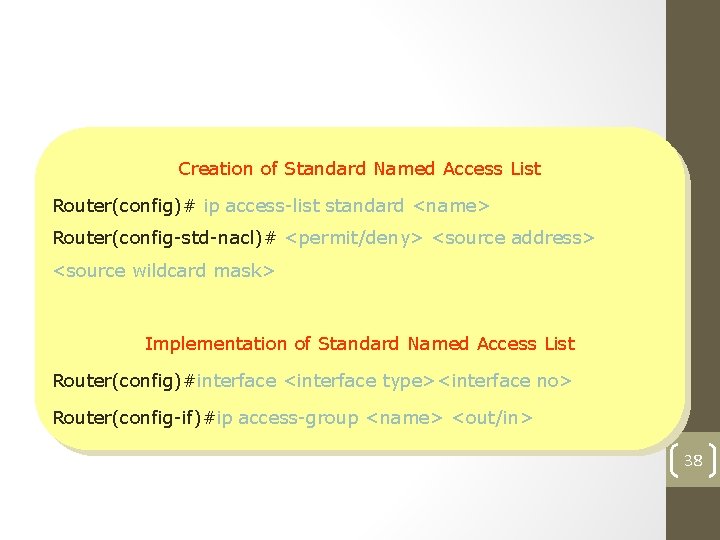
Standard Named Access List Creation of Standard Named Access List Router(config)# ip access-list standard <name> Router(config-std-nacl)# <permit/deny> <source address> <source wildcard mask> Implementation of Standard Named Access List Router(config)#interface <interface type><interface no> Router(config-if)#ip access-group <name> <out/in> 38
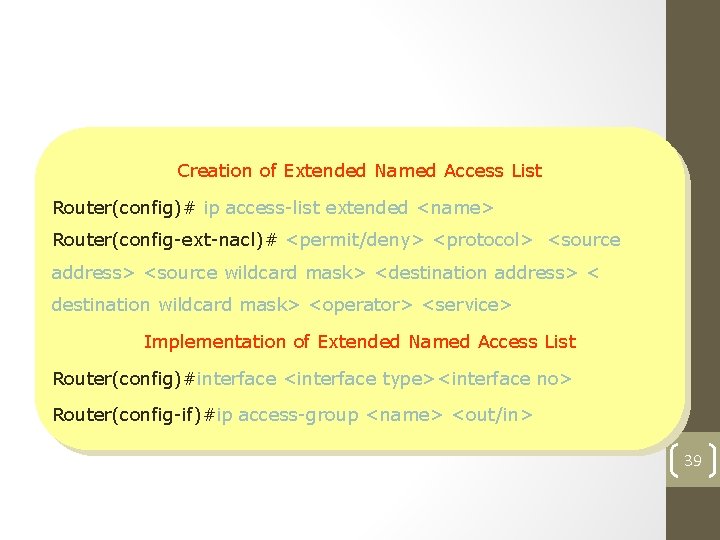
Extended Named Access List Creation of Extended Named Access List Router(config)# ip access-list extended <name> Router(config-ext-nacl)# <permit/deny> <protocol> <source address> <source wildcard mask> <destination address> < destination wildcard mask> <operator> <service> Implementation of Extended Named Access List Router(config)#interface <interface type><interface no> Router(config-if)#ip access-group <name> <out/in> 39

40
![Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C: Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C:](http://slidetodoc.com/presentation_image_h2/83b40e9c0496269d4c795c8e5951c04a/image-41.jpg)
Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C: > telnet 192. 168. 1. 150 Connecting. . . ================ Welcome to Jizan Router ================ User Access Verification password : **** Jizan> enable password : **** Jizan# show ip route Gateway of last resort is not set C 10. 0/8 is directly connected, Serial 0 R 11. 0. 0. 0/8 [120/1] via 10. 0. 0. 2, 00: 25, Serial 0 C 192. 168. 1. 0/24 is directly connected, Ethernet 0 R 192. 168. 2. 0/24 [120/1] via 10. 0. 0. 2, 00: 25, Serial 0 R 192. 168. 3. 0/24 [120/2] via 10. 0. 0. 2, 00: 25, Serial 0 Jizan# 41
![Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C: Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C:](http://slidetodoc.com/presentation_image_h2/83b40e9c0496269d4c795c8e5951c04a/image-42.jpg)
Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C: > telnet 192. 168. 2. 150 Connecting. . . ================ Welcome to Jaddah Router ================ User Access Verification password : **** Jaddah> enable password : **** Jaddah# show ip route Gateway of last resort is not set C 10. 0/8 is directly connected, Serial 1 C 11. 0. 0. 0/8 is directly connected, Serial 0 R 192. 168. 1. 0/24 [120/1] via 10. 0. 0. 1, 00: 01, Serial 1 C 192. 168. 2. 0/24 is directly connected, Ethernet 0 R 192. 168. 3. 0/24 [120/1] via 11. 0. 0. 2, 00: 12, Serial 0 Jaddah# 42
![Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C: Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C:](http://slidetodoc.com/presentation_image_h2/83b40e9c0496269d4c795c8e5951c04a/image-43.jpg)
Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C: > telnet 192. 168. 3. 150 Connecting. . . ================ Welcome to Riyadh Router ================ User Access Verification password : **** Riyadh> enable password : **** Riyadh# show ip route Gateway of last resort is not set R 10. 0/8 [120/1] via 11. 0. 0. 1, 00: 04, Serial 1 C 11. 0. 0. 0/8 is directly connected, Serial 1 R 192. 168. 1. 0/24 [120/2] via 11. 0. 0. 1, 00: 04, Serial 1 R 192. 168. 2. 0/24 [120/1] via 11. 0. 0. 1, 00: 04, Serial 1 C 192. 168. 3. 0/24 is directly connected, Ethernet 0 Riyadh# 43
![Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C: Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C:](http://slidetodoc.com/presentation_image_h2/83b40e9c0496269d4c795c8e5951c04a/image-44.jpg)
Microsoft Windows 2000 [Version 5. 00. 2195] (C) Copyright 1985 -2000 Microsoft Corp. C: > telnet 192. 168. 2. 150 Connecting. . . ================ Welcome to Jaddah Router ================ User Access Verification password : **** Jaddah> enable password : **** Jaddah# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Jaddah(config)# interface serial 1 Jaddah(config-if)# ip address 10. 0. 0. 2 255. 0. 0. 0 Jaddah(config-if)# no shut Jaddah(config-if)# encapsulation hdlc Jaddah(config-if)# interface serial 0 Jaddah(config-if)# ip address 11. 0. 0. 1 255. 0. 0. 0 44 Jaddah(config-if)# no shut Jaddah(config-if)# encapsulation hdlc
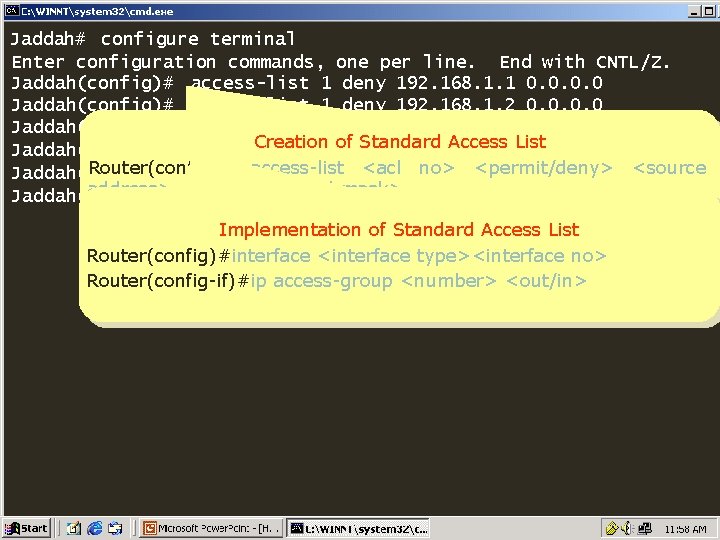
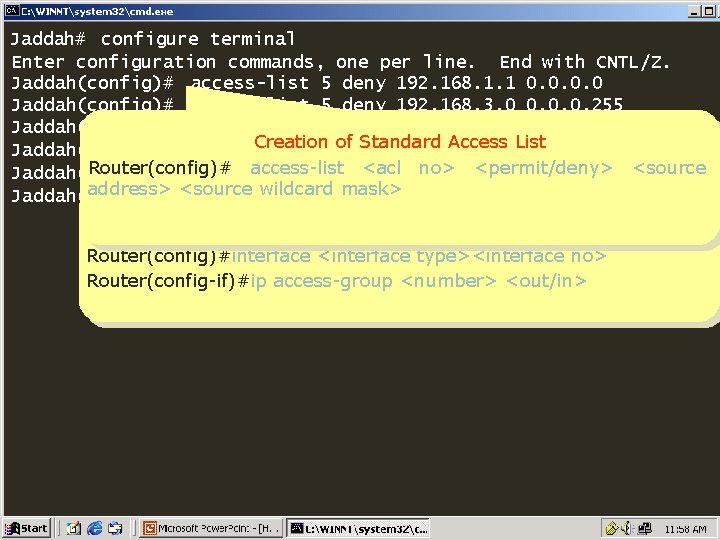
Jaddah# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Jaddah(config)# access-list 1 deny 192. 168. 1. 1 0. 0 Jaddah(config)# access-list 1 deny 192. 168. 1. 2 0. 0 Jaddah(config)# access-list 1 permit any Creation of Standard Access List Jaddah(config)# interface ethernet 0 Router(config)# <acl 1 out no> <permit/deny> <source Jaddah(config-if)# ip access-list access-group address> <source wildcard mask> Jaddah(config-if)# Implementation of Standard Access List Router(config)#interface <interface type><interface no> Router(config-if)#ip access-group <number> <out/in> 45
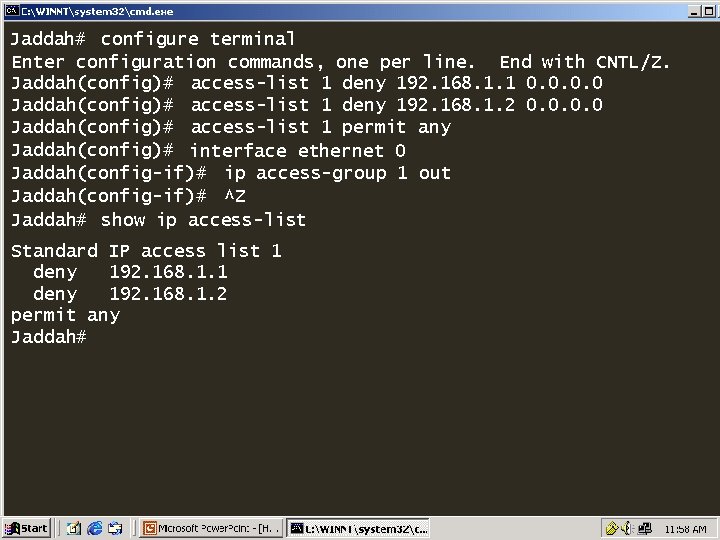
Jaddah# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Jaddah(config)# access-list 1 deny 192. 168. 1. 1 0. 0 Jaddah(config)# access-list 1 deny 192. 168. 1. 2 0. 0 Jaddah(config)# access-list 1 permit any Jaddah(config)# interface ethernet 0 Jaddah(config-if)# ip access-group 1 out Jaddah(config-if)# ^Z Jaddah# show ip access-list Standard IP access list 1 deny 192. 168. 1. 2 permit any Jaddah# 46
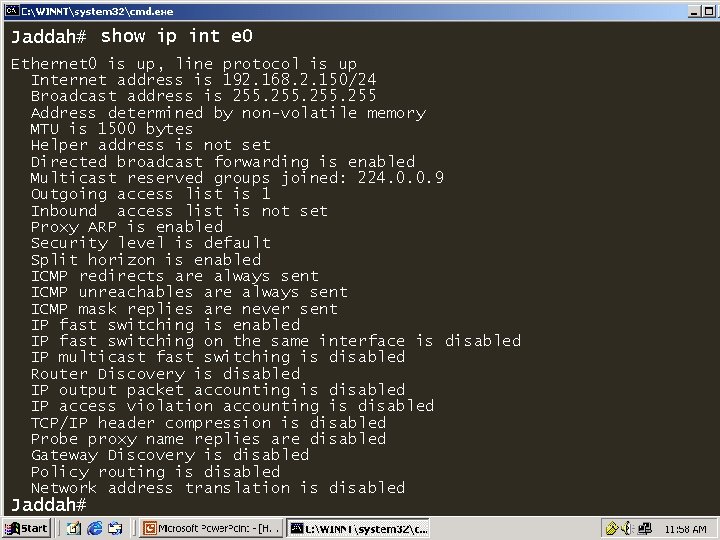
Jaddah# show ip int e 0 Ethernet 0 is up, line protocol is up Internet address is 192. 168. 2. 150/24 Broadcast address is 255 Address determined by non-volatile memory MTU is 1500 bytes Helper address is not set Directed broadcast forwarding is enabled Multicast reserved groups joined: 224. 0. 0. 9 Outgoing access list is 1 Inbound access list is not set Proxy ARP is enabled Security level is default Split horizon is enabled ICMP redirects are always sent ICMP unreachables are always sent ICMP mask replies are never sent IP fast switching is enabled IP fast switching on the same interface is disabled IP multicast fast switching is disabled Router Discovery is disabled IP output packet accounting is disabled IP access violation accounting is disabled TCP/IP header compression is disabled Probe proxy name replies are disabled Gateway Discovery is disabled Policy routing is disabled Network address translation is disabled Jaddah# 47
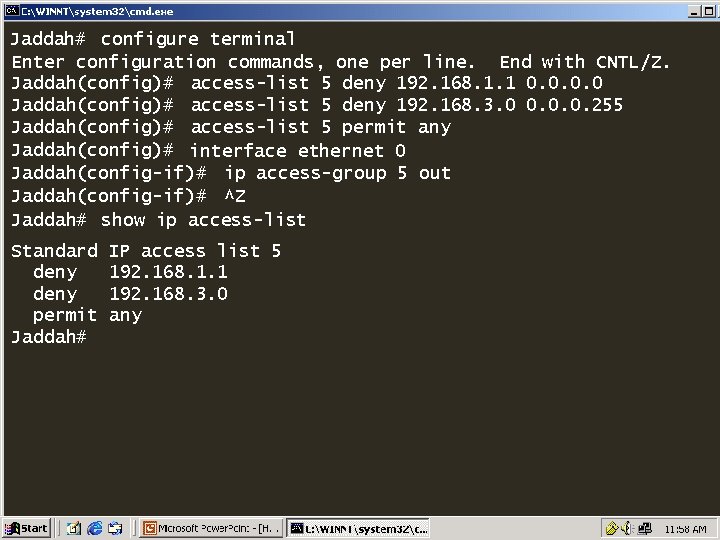
Jaddah# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Jaddah(config)# access-list 5 deny 192. 168. 1. 1 0. 0 Jaddah(config)# access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 Jaddah(config)# access-list 5 permit any Jaddah(config)# interface ethernet 0 Jaddah(config-if)# ip access-group 5 out Jaddah(config-if)# ^Z Jaddah# show ip access-list Standard deny permit Jaddah# IP access list 5 192. 168. 1. 1 192. 168. 3. 0 any 48
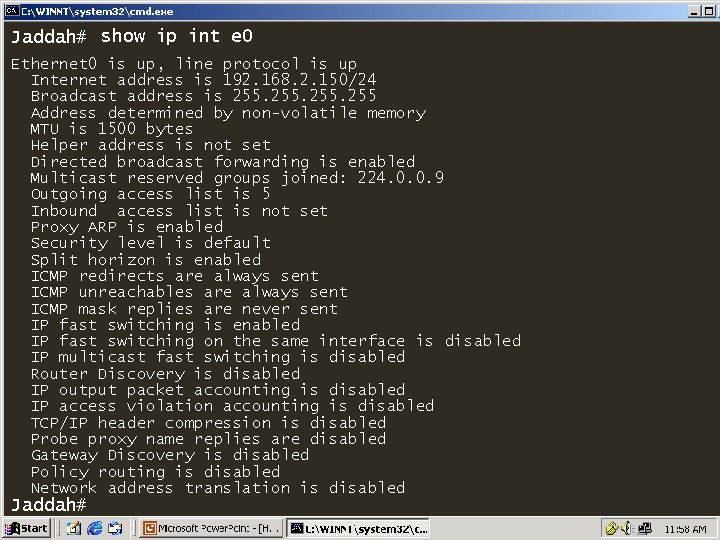
Jaddah# show ip int e 0 Ethernet 0 is up, line protocol is up Internet address is 192. 168. 2. 150/24 Broadcast address is 255 Address determined by non-volatile memory MTU is 1500 bytes Helper address is not set Directed broadcast forwarding is enabled Multicast reserved groups joined: 224. 0. 0. 9 Outgoing access list is 5 Inbound access list is not set Proxy ARP is enabled Security level is default Split horizon is enabled ICMP redirects are always sent ICMP unreachables are always sent ICMP mask replies are never sent IP fast switching is enabled IP fast switching on the same interface is disabled IP multicast fast switching is disabled Router Discovery is disabled IP output packet accounting is disabled IP access violation accounting is disabled TCP/IP header compression is disabled Probe proxy name replies are disabled Gateway Discovery is disabled Policy routing is disabled Network address translation is disabled Jaddah# 49
Jaddah# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Jaddah(config)# access-list 5 deny 192. 168. 1. 1 0. 0 Jaddah(config)# access-list 5 deny 192. 168. 3. 0 0. 0. 0. 255 Jaddah(config)# access-list 5 permit any Creation of Standard Access List Jaddah(config)# interface ethernet 0 Router(config)# <acl 5 out no> <permit/deny> <source Jaddah(config-if)# ip access-list access-group address> <source wildcard mask> Jaddah(config-if)# Implementation of Standard Access List Router(config)#interface <interface type><interface no> Router(config-if)#ip access-group <number> <out/in> 50
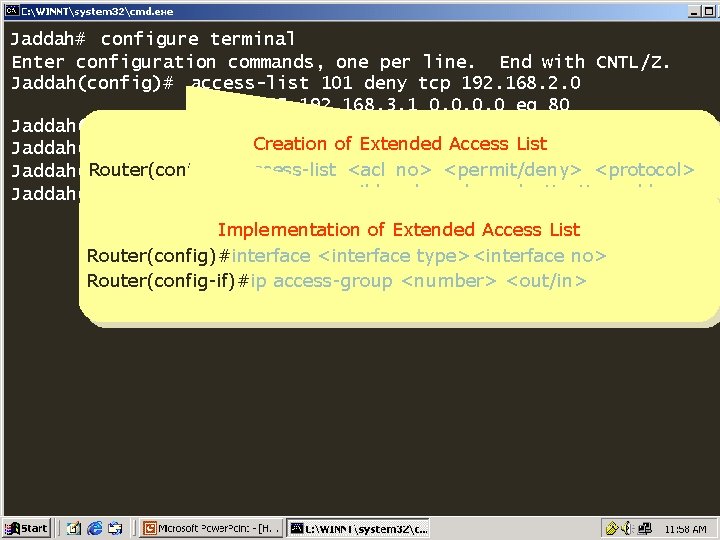
Jaddah# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Jaddah(config)# access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 Jaddah(config)# access-list 101 permit ip any Creation of Extended Access List Jaddah(config)# interface ethernet 0 Router(config)# <acl no> <permit/deny> <protocol> Jaddah(config-if)# ipaccess-list access-group 101 in <source address> <source wildcard mask> <destination address> Jaddah(config-if)# < destination wildcard mask> <operator> <service> Implementation of Extended Access List Router(config)#interface <interface type><interface no> Router(config-if)#ip access-group <number> <out/in> 51
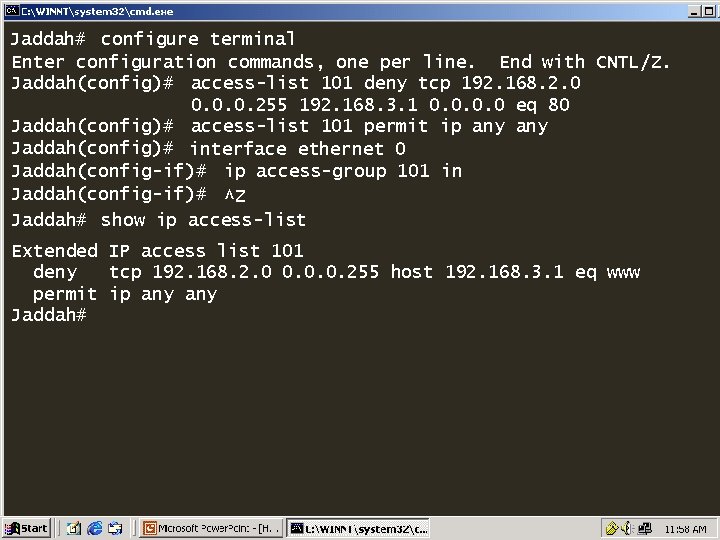
Jaddah# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Jaddah(config)# access-list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 192. 168. 3. 1 0. 0 eq 80 Jaddah(config)# access-list 101 permit ip any Jaddah(config)# interface ethernet 0 Jaddah(config-if)# ip access-group 101 in Jaddah(config-if)# ^Z Jaddah# show ip access-list Extended IP access list 101 deny tcp 192. 168. 2. 0 0. 0. 0. 255 host 192. 168. 3. 1 eq www permit ip any Jaddah# 52
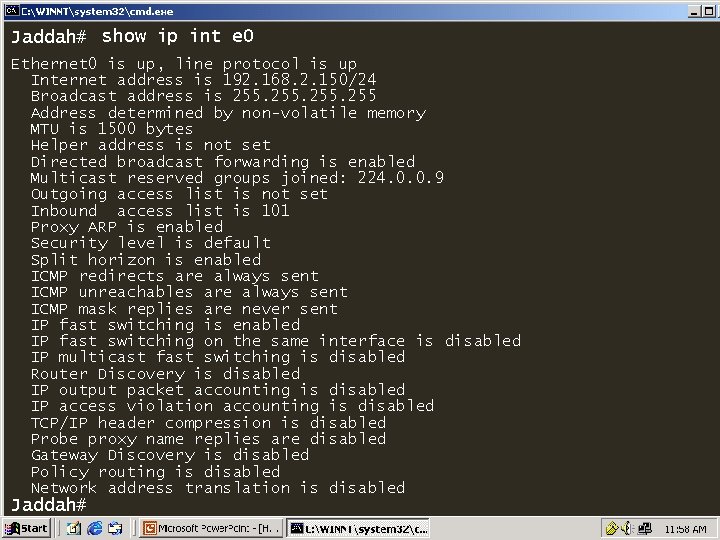
Jaddah# show ip int e 0 Ethernet 0 is up, line protocol is up Internet address is 192. 168. 2. 150/24 Broadcast address is 255 Address determined by non-volatile memory MTU is 1500 bytes Helper address is not set Directed broadcast forwarding is enabled Multicast reserved groups joined: 224. 0. 0. 9 Outgoing access list is not set Inbound access list is 101 Proxy ARP is enabled Security level is default Split horizon is enabled ICMP redirects are always sent ICMP unreachables are always sent ICMP mask replies are never sent IP fast switching is enabled IP fast switching on the same interface is disabled IP multicast fast switching is disabled Router Discovery is disabled IP output packet accounting is disabled IP access violation accounting is disabled TCP/IP header compression is disabled Probe proxy name replies are disabled Gateway Discovery is disabled Policy routing is disabled Network address translation is disabled Jaddah# 53
- Slides: 53