Slide Template for Module 4 Data Storage Backup
Slide Template for Module 4 Data Storage, Backup, and Security
Learner Objectives 1. Understand why data storage, backup, and security of research data are important 2. Understand data storage, backup, and security methods for research data 3. Understand best practices for research data storage, access control, migration to newer storage media, and security of research data 4. Identify an approach to creating a data storage, backup, and security plan for a project
Storage, Backup, and Security • They are fundamental and interrelated components of a data management strategy. • Together they ensure the ongoing integrity of research data. • Project planning and data management must account for all three.
Storage • The media to which you save your data files and software – Optical, magnetic • All storage media are vulnerable to risk. • Evaluate and refresh regularly.
Storage • • • Internal, local hard drives Networked storage External storage devices Remote storage services (The Cloud) Physical storage (Label, label! See Module x on Metadata. )
Storage • Remote storage services – Data sharing is not data storage. – Read terms of service. – Consult your PI or institutional policies on filesharing services.
Backup • Allows you to restore your data if it is lost. – Hardware or software malfunction – Environmental disaster (fire, flood) – Theft – Unauthorized access Does your operating system and/or network administrator already have existing backup protocols and tools in place?
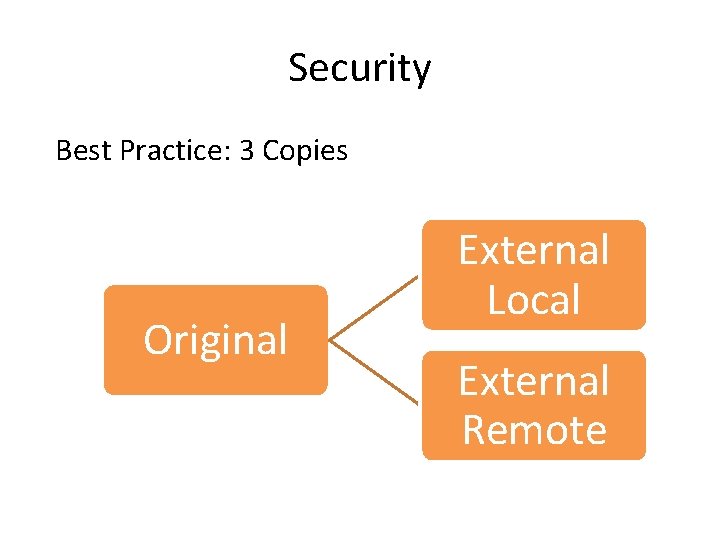
Security Best Practice: 3 Copies Original External Local External Remote
Backup • Backup Procedure – Full – Differential incremental – Cumulative incremental • Backup Frequency – Daily – Weekly – Monthly • Test your strategy!
Other Considerations • File formats • Data migration • Responsibility assignments
Levels of Security • Safeguard your data from malicious or accidental access to your system. – Access – Systems – Data Integrity Does your network administrator have security services that meet your needs?
Security • Limit the availability of your data. – User ID/passwords – Role-based access rights – Limitations of wireless devices
Security • Protect the hardware and software systems you use. – Anti-virus software – Up-to-date versions of software and storage media – Firewalls – Intrusion detection software – Limit physical access
Security • Protect the integrity of your data at the file level – Encryption – Electronic signatures – Watermarking
- Slides: 14