Skype Bruce Maggs Gratuitous Quote of the Day
Skype Bruce Maggs
Gratuitous Quote of the Day "There have been members of the Maggs family in south east Suffolk since the great subsidy of 1327 but they were of no great distinction either then or afterwards. “ -- from Allan Farquar Bottomley, "Introduction, " in the Southwold Diary of James Maggs, 1818 -1876, edited by Allan Farquar Bottomley, Volume I - 1818 -1848, (Suffolk: Published for the Suffolk Records Society by the Boydell Press, 1983), p. 1. 2
References • S. A. Baset and H. G. Schulzrinne, ”An • Analysis of the Skype Peer-to-Peer Internet Telephony Protocol, ” Proceedings of the 25 th IEEE International Conference on Computer Communications (INFOCOMM), April 2006, pp. 1 -11. Wikipedia article 3
Skype • Developed by Danes Niklas Zennstrom • • and Janus Friis, creators of Kazaa, Skype, and Joost, and a team of software developers in Estonia. First peer-to-peer VOIP application. 12, 049, 795 people on-line today, 276 M accounts in Q 4 2007, $115 M Q 4 revenue Now owned by e. Bay. Protocol not publically disclosed 4
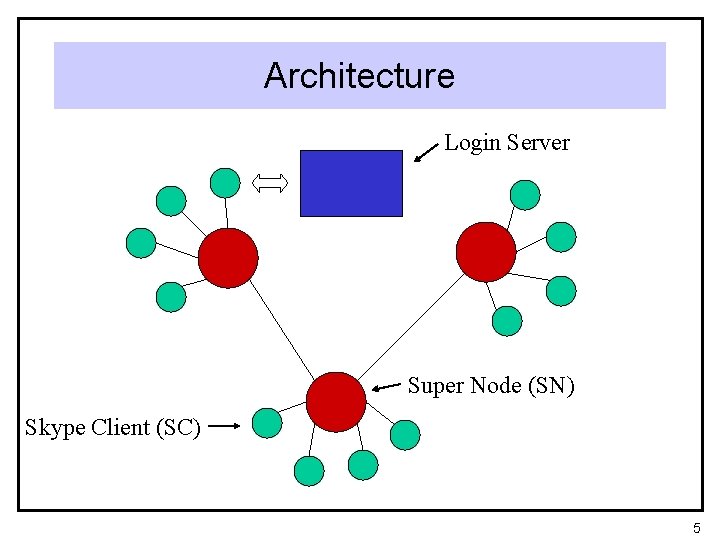
Architecture Login Server Super Node (SN) Skype Client (SC) 5
Supernodes • Any client with a public IP address and • sufficient performance can be a supernode Skype claims at most 40 kbits/sec upload/download (? ) 6
Login Protocol • SC connects to SN listed in host cache • • • (stored locally in Windows registry), up to 200 entries On first use, SC uses to bootstrap SNs SC then authenticates with login server via user name and password If access to login server is blocked, login is routed through SN SC also checks with skype. com via HTTP for latest software version Mysterious ICMP messages to various continents 7
NAT and Firewall Traversal • UDP preferred for voice packets • SC chooses sending/listening port at • • • random Uses ports 80, 443 if random port is blocked Tries UDP first, then TCP Uses SN as a relay station, if necessary 8
Encryption • All communications are encrypted! • 256 -bit AES (Advanced Encryption • • Standard, a. k. a. Rijndael) symmetric cryptosystem 1024 -bit RSA to exchange private keys User public keys certified with 1536 or 2048 -bit certificates 9
Finding a User • Buddy list stored locally in earlier • • • versions, now centrally Skype claims to find users logged on within past 72 hours User can simultaneously login in at multiple locations Messages, calls, sent to all instantiations of user 10
“Global Index” Technology • • • SC queries its SN about user location SN responds with 8 IP addresses If SC asks again, SN provides 16 more Search faster the second time, evidence that search results are cached at intermediate nodes Rest of the protocol is a bit mysterious 11
Telephony • i. LBC, i. SAC, and i. PCM codecs developed by • • • Global. IPSound, other codecs 67 -byte packets at 40 kbits/sec, needs 16 kbits/sec minimum Frequency band approximately 50 -8000 Hz PSTN uses uncompressed 56 kbits/sec, 8000 samples per sec (max 4000 Hz), nonuniform intervals Skype keeps transmitting during silence! Calls on hold send less frequent keepalive messages 12
Bridging to PSTN • Skype. In and Skype. OUT servers for • making PSTN-to-PC and PC-to-PSTN calls To use Skype. In, local phone number assigned to PC 13
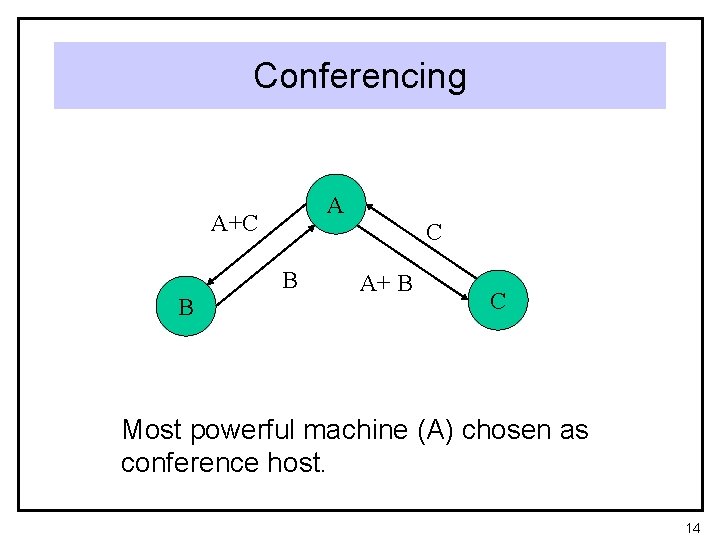
Conferencing A A+C C B B A+ B C Most powerful machine (A) chosen as conference host. 14
- Slides: 14