SIMPLY CONNECTED THE NEW NETWORK MEANS BUSINESS MAJOR
SIMPLY CONNECTED THE NEW NETWORK MEANS BUSINESS
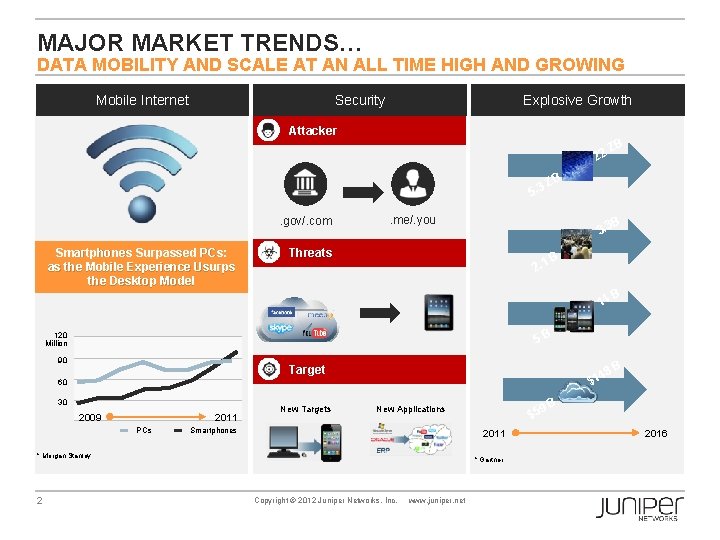
MAJOR MARKET TRENDS… DATA MOBILITY AND SCALE AT AN ALL TIME HIGH AND GROWING Mobile Internet Security Explosive Growth Attacker 22 5. 3. gov/. com Smartphones Surpassed PCs: as the Mobile Experience Usurps the Desktop Model ZB ZB . me/. you B 3. 3 Threats 2. 1 B 14 5 B 120 Million 90 8 B Target 4 $1 60 30 2009 2011 PCs New Targets 9 B $5 New Applications Smartphones 2011 * Morgan Stanley 2 B * Gartner Copyright © 2012 Juniper Networks, Inc. www. juniper. net 2016
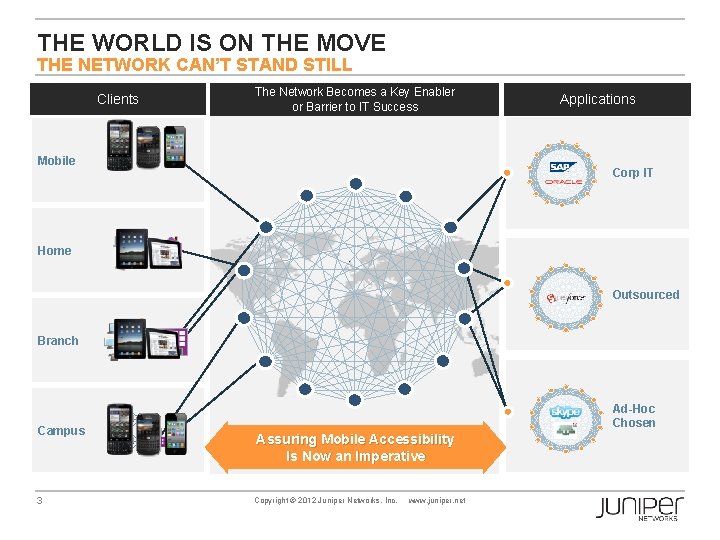
THE WORLD IS ON THE MOVE THE NETWORK CAN’T STAND STILL Clients The Network Becomes a Key Enabler or Barrier to IT Success Mobile Applications Corp IT Home Outsourced Branch Campus 3 Ad-Hoc Chosen Assuring Mobile Accessibility Is Now an Imperative Copyright © 2012 Juniper Networks, Inc. www. juniper. net

MOBILITY REDEFINES BUSINESS PRACTICES AN OPPORTUNITY, NOT A PROBLEM Business Applications Personal Applications Pulse 42% 39% 37% Increased Productivity Reduced Paperwork Increased Revenue Source : Forrester, Frost &Sullivan, Business week, Gigaom pro, ABI research 4 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
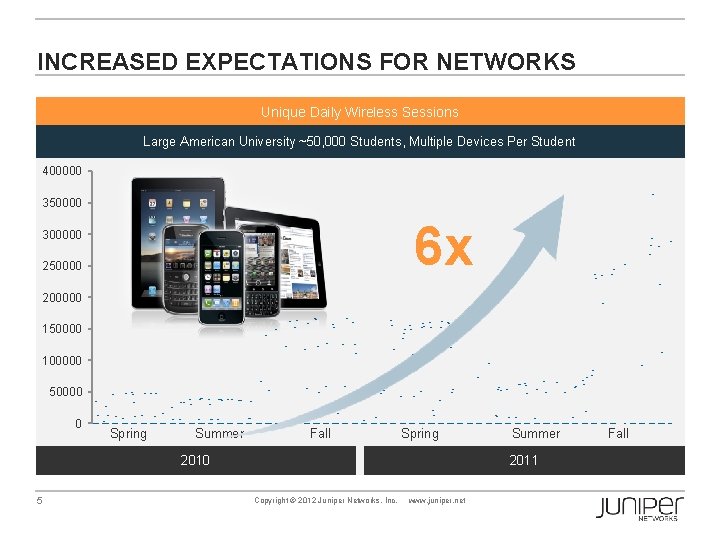
INCREASED EXPECTATIONS FOR NETWORKS Unique Daily Wireless Sessions Large American University ~50, 000 Students, Multiple Devices Per Student 400000 350000 6 x 300000 250000 200000 150000 100000 50000 0 Spring Summer Fall Spring 2010 5 Summer 2011 Copyright © 2012 Juniper Networks, Inc. www. juniper. net Fall
THE SOLUTION IS TO BE SIMPLY CONNECTED An integrated portfolio of resilient wired, wireless and security products that simply enable mobility at scale. Consistent Security 6 Performance at Scale Copyright © 2012 Juniper Networks, Inc. www. juniper. net Highly Resilient
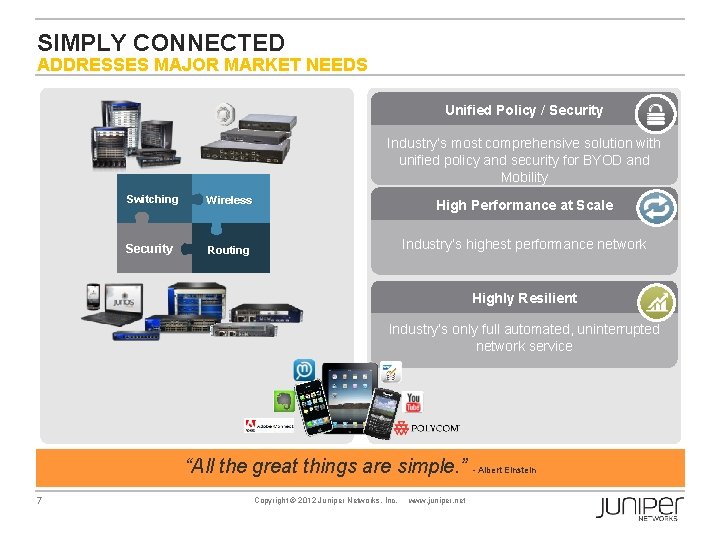
SIMPLY CONNECTED ADDRESSES MAJOR MARKET NEEDS Unified Policy / Security Industry’s most comprehensive solution with unified policy and security for BYOD and Mobility Switching Wireless Security Routing High Performance at Scale Industry’s highest performance network Highly Resilient Industry’s only full automated, uninterrupted network service “All the great things are simple. ” - Albert Einstein 7 Copyright © 2012 Juniper Networks, Inc. www. juniper. net

SIMPLY CONNECTED JUNIPER WIRELESS SOLUTION March 20, 2012
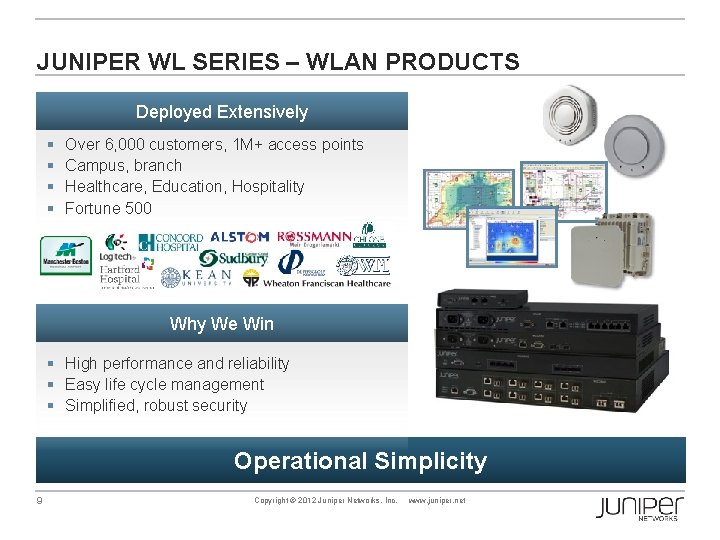
JUNIPER WL SERIES – WLAN PRODUCTS Deployed Extensively § § Over 6, 000 customers, 1 M+ access points Campus, branch Healthcare, Education, Hospitality Fortune 500 Why We Win § High performance and reliability § Easy life cycle management § Simplified, robust security Operational Simplicity 9 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
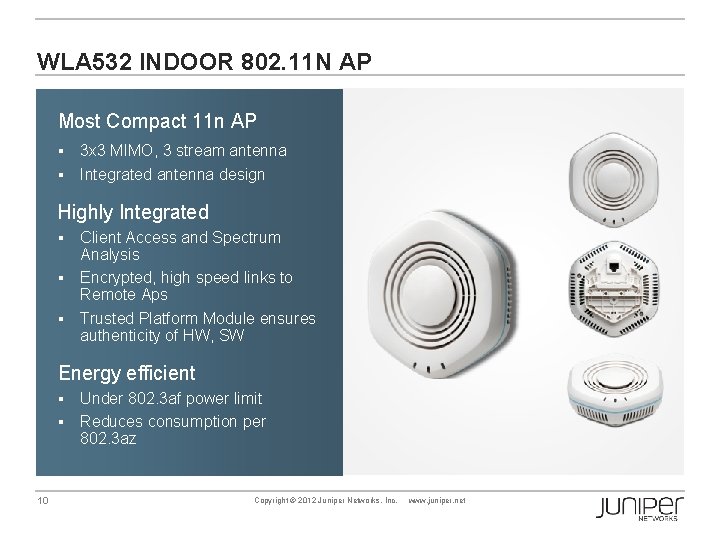
WLA 532 INDOOR 802. 11 N AP Most Compact 11 n AP 3 x 3 MIMO, 3 stream antenna § Integrated antenna design § Highly Integrated Client Access and Spectrum Analysis § Encrypted, high speed links to Remote Aps § Trusted Platform Module ensures authenticity of HW, SW § Energy efficient Under 802. 3 af power limit § Reduces consumption per 802. 3 az § 10 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
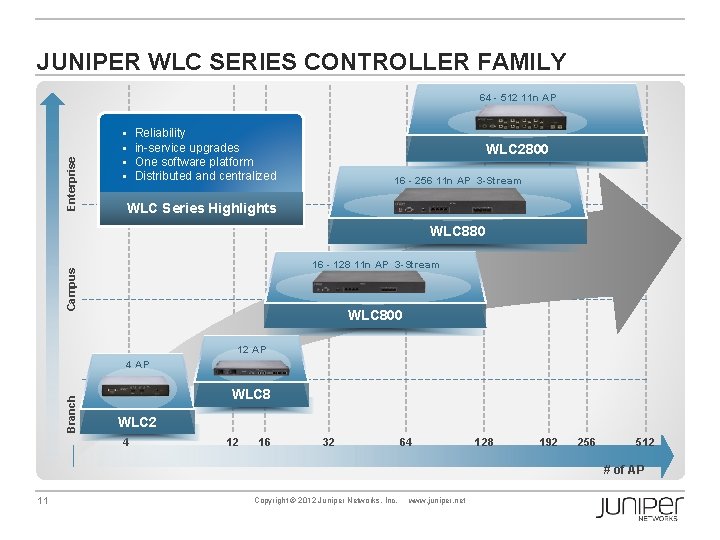
JUNIPER WLC SERIES CONTROLLER FAMILY Enterprise 64 - 512 11 n AP § § Reliability in-service upgrades One software platform Distributed and centralized WLC 2800 16 - 256 11 n AP 3 -Stream WLC Series Highlights WLC 880 Campus 16 - 128 11 n AP 3 -Stream WLC 800 12 AP Branch 4 AP WLC 8 WLC 2 4 12 16 32 64 128 192 256 512 # of AP 11 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
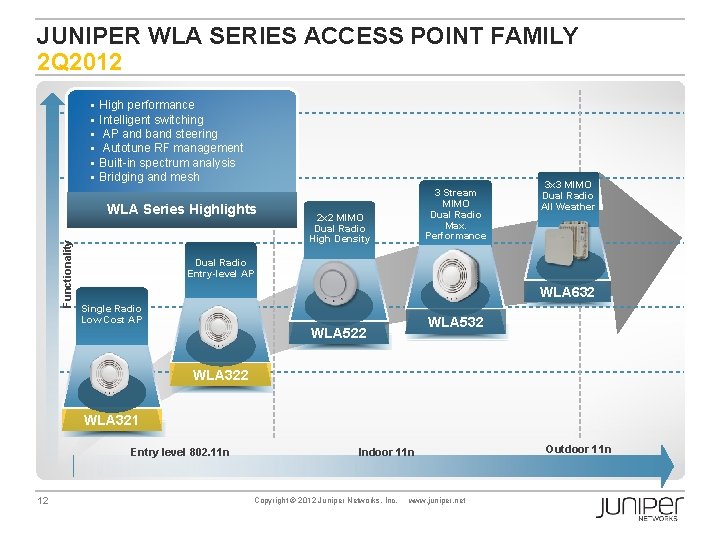
JUNIPER WLA SERIES ACCESS POINT FAMILY 2 Q 2012 § § § High performance Intelligent switching AP and band steering Autotune RF management Built-in spectrum analysis Bridging and mesh Functionality WLA Series Highlights 3 Stream MIMO Dual Radio Max. Performance 2 x 2 MIMO Dual Radio High Density 3 x 3 MIMO Dual Radio All Weather Dual Radio Entry-level AP WLA 632 Single Radio Low Cost AP WLA 532 WLA 522 WLA 321 Entry level 802. 11 n 12 Indoor 11 n Copyright © 2012 Juniper Networks, Inc. www. juniper. net Outdoor 11 n

JUNIPER WLM SERIES LIFE CYCLE MANAGEMENT Ring. Master Planning and deployment § 3 D predictive planning tool § Indoor and outdoor network plan Configuration and Verification § Complete offline configuration § System and service wizards § Pushes configuration to WLCs Monitoring and reporting § By user, radio, AP, WLC, SSID § 30 day history aids compliance § WIDS/WIPS integration Location aware § Search by location § Roaming history § Geo fencing 13 Copyright © 2012 Juniper Networks, Inc. Plan Report Trouble shoot www. juniper. net Config Monitor
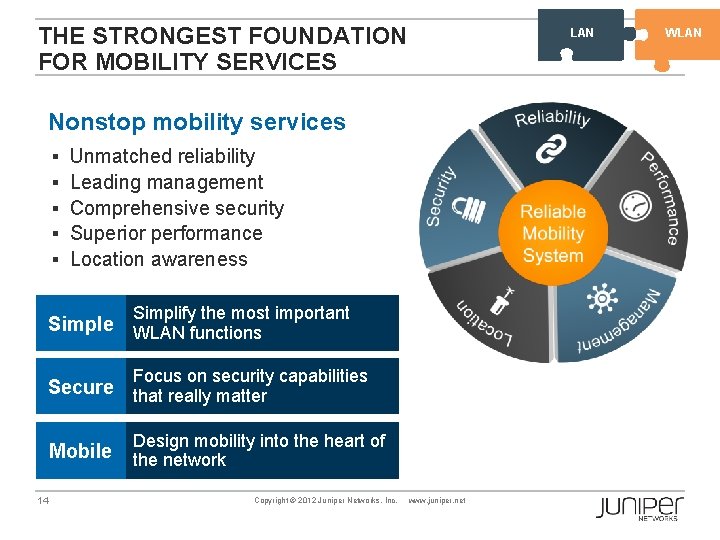
THE STRONGEST FOUNDATION FOR MOBILITY SERVICES LAN Nonstop mobility services § § § Unmatched reliability Leading management Comprehensive security Superior performance Location awareness Simplify the most important Simple WLAN functions Focus on security capabilities Secure that really matter Mobile 14 Design mobility into the heart of the network Copyright © 2012 Juniper Networks, Inc. www. juniper. net WLAN

LAN SINGLE POINT OF MANAGEMENT FOR ALL CONTROLLERS Primary Seed Secondary Seed Member 15 Member Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member WLAN
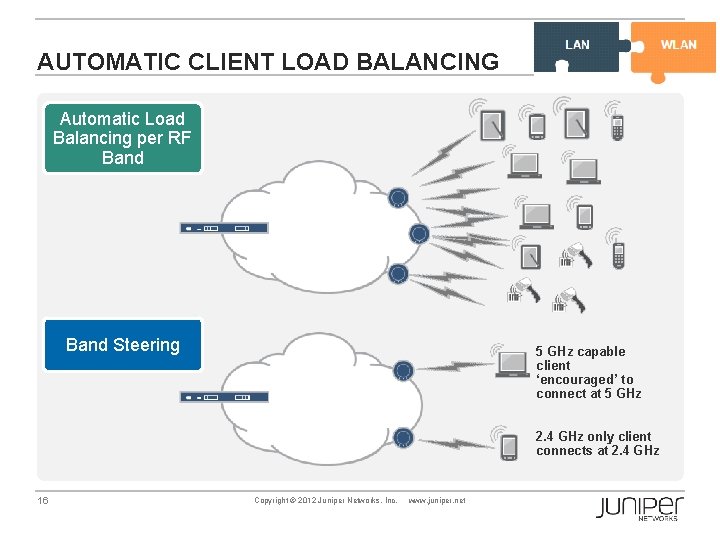
EX Series WL Series AUTOMATIC CLIENT LOAD BALANCING Automatic Load Balancing per RF Band Steering 5 GHz capable client ‘encouraged’ to connect at 5 GHz 2. 4 GHz only client connects at 2. 4 GHz 16 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
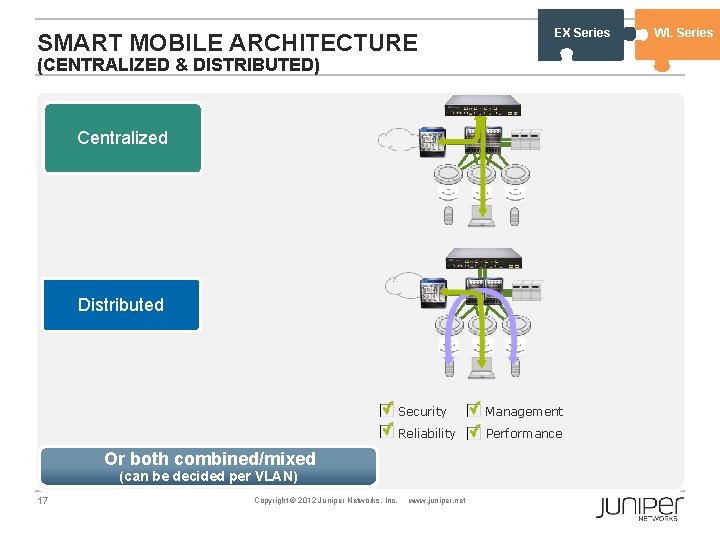
SMART MOBILE ARCHITECTURE EX Series (CENTRALIZED & DISTRIBUTED) Centralized Distributed Security Management Reliability Performance Or both combined/mixed (can be decided per VLAN) 17 Copyright © 2012 Juniper Networks, Inc. www. juniper. net WL Series
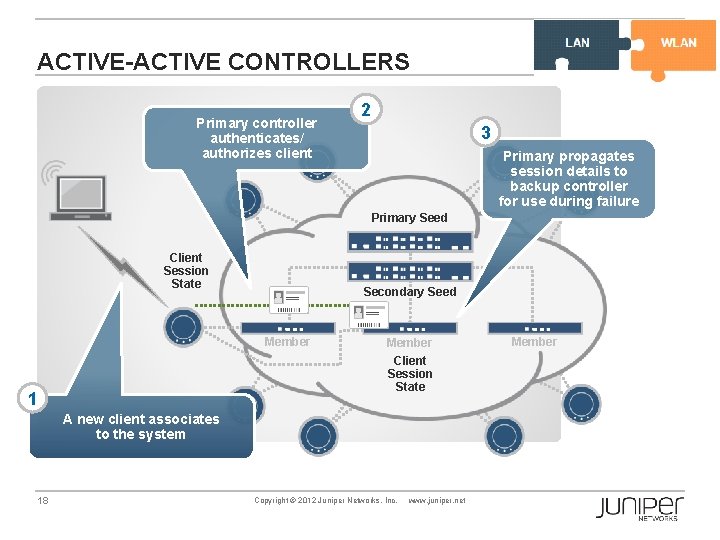
EX Series ACTIVE-ACTIVE CONTROLLERS Primary controller authenticates/ authorizes client 2 3 Primary propagates session details to backup controller for use during failure Primary Seed Client Session State Secondary Seed Member 1 Member Client Session State A new client associates to the system 18 Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member WL Series
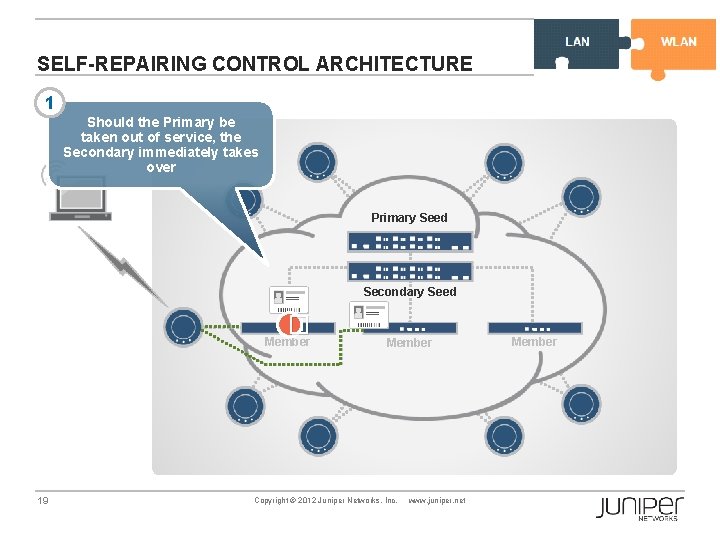
EX Series SELF-REPAIRING CONTROL ARCHITECTURE 1 Should the Primary be taken out of service, the Secondary immediately takes over Primary Seed Secondary Seed � Member 19 Member Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member WL Series
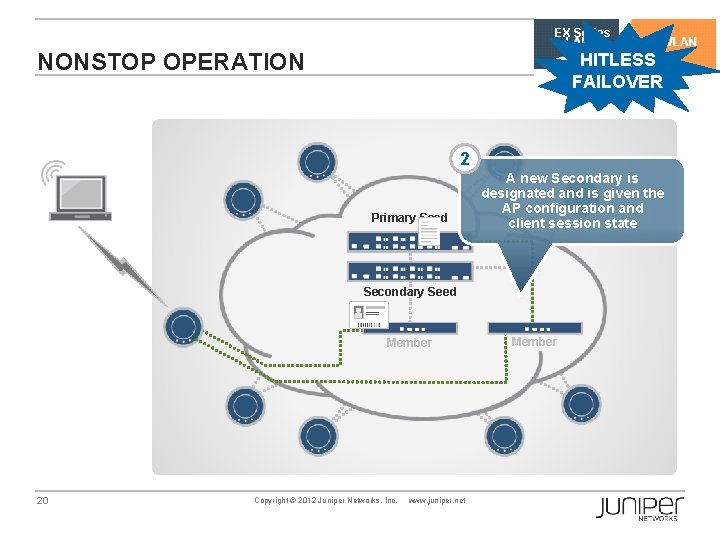
EX Series NONSTOP OPERATION HITLESS FAILOVER 2 Primary Seed A new Secondary is designated and is given the AP configuration and client session state Secondary Seed Member 20 Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member
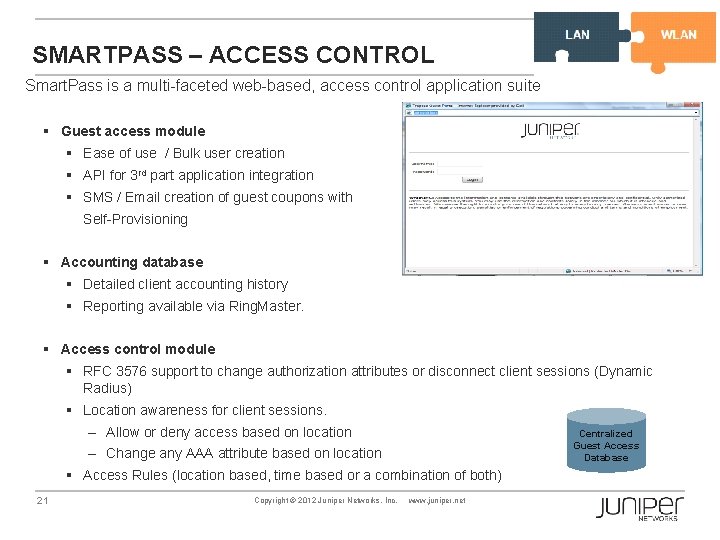
WL Series SMARTPASS – ACCESS CONTROL Smart. Pass is a multi-faceted web-based, access control application suite § Guest access module § Ease of use / Bulk user creation § API for 3 rd part application integration § SMS / Email creation of guest coupons with Self-Provisioning § Accounting database § Detailed client accounting history § Reporting available via Ring. Master. § Access control module § RFC 3576 support to change authorization attributes or disconnect client sessions (Dynamic Radius) § Location awareness for client sessions. – Allow or deny access based on location Centralized Guest Access Database – Change any AAA attribute based on location § Access Rules (location based, time based or a combination of both) 21 Copyright © 2012 Juniper Networks, Inc. www. juniper. net

SIMPLY CONNECTED ELEMENTS OF A SIMPLY CONNECTED CAMPUS March 20, 2012

SIMPLY CONNECTED ADDRESSES MAJOR MARKET NEEDS Unified Policy / Security Industry’s most comprehensive solution with unified policy and security for BYOD and Mobility Switching Wireless Security Routing High Performance at Scale Industry’s highest performance network Highly Resilient Industry’s only full automated, uninterrupted network service “All the great things are simple. ” - Albert Einstein 23 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
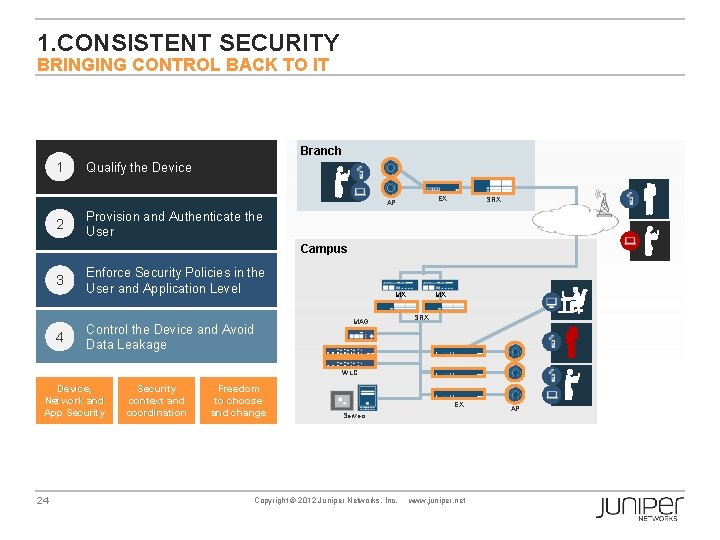
1. CONSISTENT SECURITY BRINGING CONTROL BACK TO IT Branch 1 Qualify the Device EX AP 2 SRX Provision and Authenticate the User Campus 3 4 Enforce Security Policies in the User and Application Level Control the Device and Avoid Data Leakage MX MAG MX SRX WLC Device, Network and App Security 24 Security context and coordination Freedom to choose and change EX Servers Copyright © 2012 Juniper Networks, Inc. www. juniper. net AP
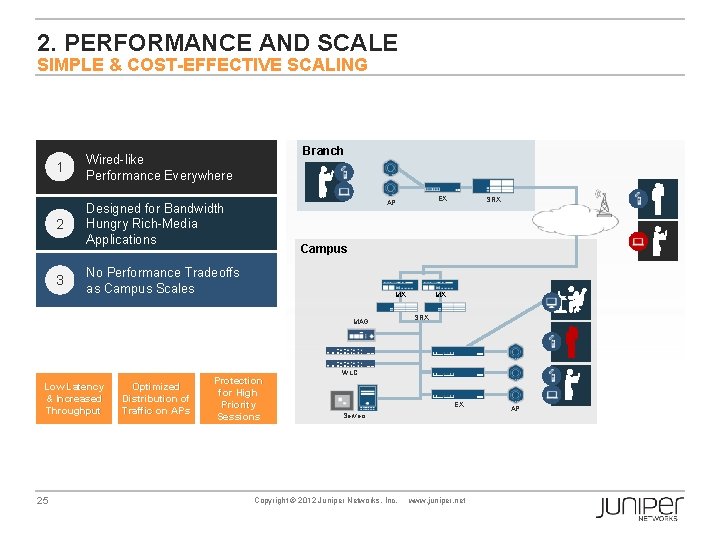
2. PERFORMANCE AND SCALE SIMPLE & COST-EFFECTIVE SCALING 1 Wired-like Performance Everywhere 2 Designed for Bandwidth Hungry Rich-Media Applications 3 Branch MX MAG 25 Optimized Distribution of Traffic on APs SRX Campus No Performance Tradeoffs as Campus Scales Low Latency & Increased Throughput EX AP Protection for High Priority Sessions MX SRX WLC EX Servers Copyright © 2012 Juniper Networks, Inc. www. juniper. net AP
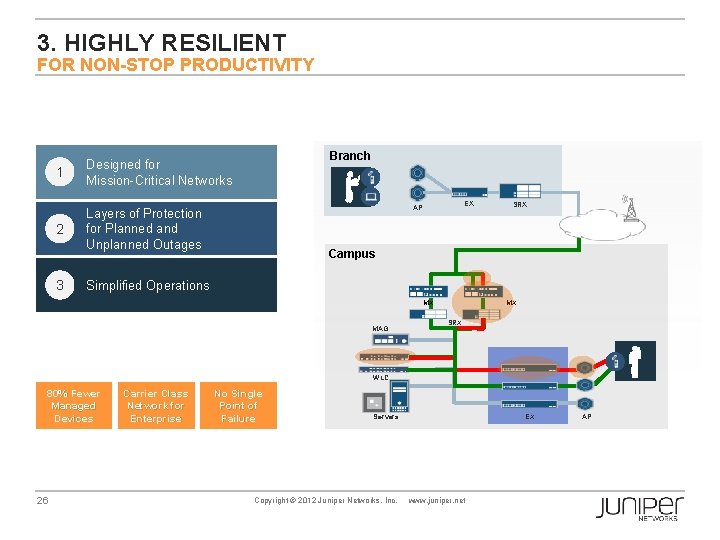
3. HIGHLY RESILIENT FOR NON-STOP PRODUCTIVITY 1 Designed for Mission-Critical Networks 2 Layers of Protection for Planned and Unplanned Outages 3 Branch EX AP SRX Campus Simplified Operations MX MAG MX SRX WLC 80% Fewer Managed Devices 26 Carrier Class Network for Enterprise No Single Point of Failure EX Servers Copyright © 2012 Juniper Networks, Inc. www. juniper. net AP
SIMPLY CONNECTED A DAY IN THE LIFE OF A SIMPLY CONNECTED USER March 20, 2012

THE GOAL IS TO BE SIMPLY CONNECTED Simplified switching architecture, now a complete, feature-rich portfolio Wired-like experience on wireless – resiliency and performance Simple for users Simple for IT EX Series WL Series Superb Qo. E Highly economic Integrated security Always on resiliency High performance Simplified architecture Automation 28 SRX Series Security follows user, and application intelligence Copyright © 2012 Juniper Networks, Inc. www. juniper. net Device-agnostic secure connectivity

THE SIMPLY CONNECTED STORY A DAY IN THE LIFE of a simply connected user § We will show you how a Juniper network manages voice and video calls from non-company owned devices and how our WL and EX series provide a uniquely resilient environment for the mobile user § We will detail some of the key differentiating technologies that we have to offer for wireless and ethernet switching Our technical experts are standing by to take your detailed technical questions on any of the material presented at the end of this seminar 29 Copyright©© 2012 2010 Juniper. Networks, Inc. www. juniper. net
Network SIMPLY CONNECTED • Coordinated Threat Control • Wireless – scalability, simplicity, automation • Next – managing congestion 30 1 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
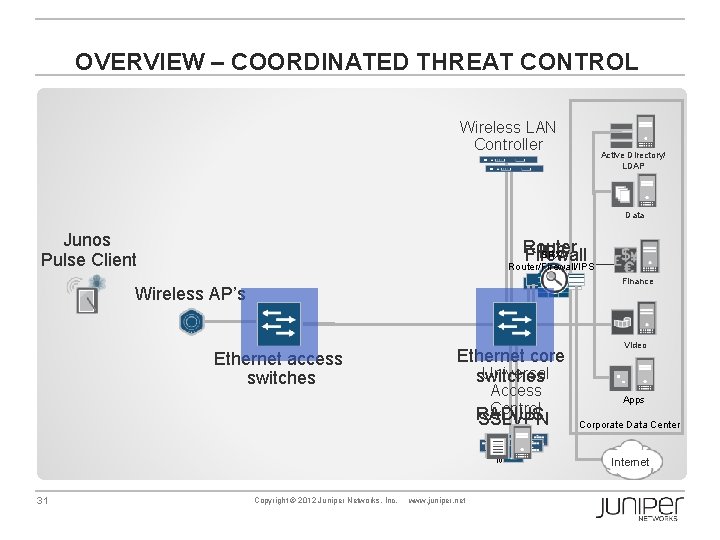
OVERVIEW – COORDINATED THREAT CONTROL Wireless LAN Controller Active Directory/ LDAP Data Junos Pulse Client Router IPS SRX Firewall Router/Firewall/IPS Finance Wireless AP’s Ethernet access switches Ethernet core Universal switches Access Control RADIUS SSLVPN MAG 31 Copyright © 2012 Juniper Networks, Inc. www. juniper. net Video Apps Corporate Data Center Internet
Network SIMPLY CONNECTED • Coordinated Threat Control • Wireless – scalability, simplicity, automation • Next – managing congestion 32 1 Copyright © 2012 Juniper Networks, Inc. www. juniper. net

COMPONENTS OF A WIRELESS LAN (WLAN) Access Point WLAN Controller WLAN Management Wireless LAN CONTROLLER (WLC) Campus Core Encrypted WLAN Management Firewall MAG Access (Location) WLM 1200 802. 1 x Authentication Trusted Client 33 Copyright © 2012 Juniper Networks, Inc. www. juniper. net

SINGLE POINT OF MANAGEMENT FOR ALL CONTROLLERS Primary Seed Secondary Seed Member 34 Member Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member
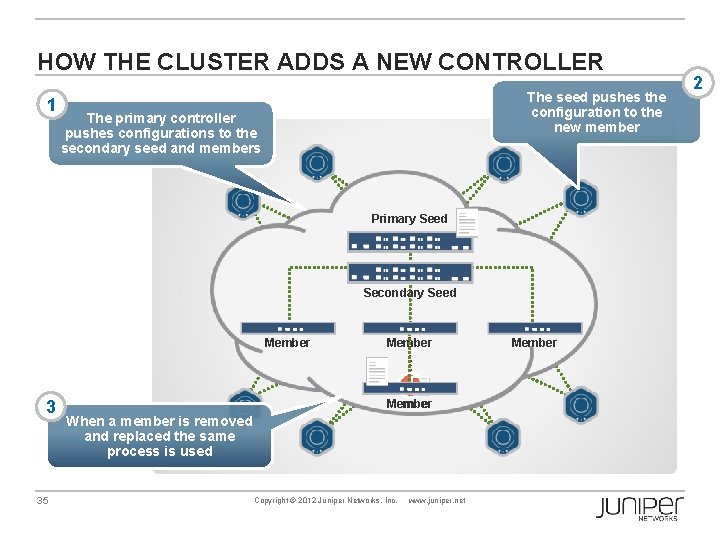
HOW THE CLUSTER ADDS A NEW CONTROLLER 1 The seed pushes the configuration to the new member The primary controller pushes configurations to the secondary seed and members Primary Seed Secondary Seed Member 3 35 Member � Member When a member is removed and replaced the same process is used Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member 2
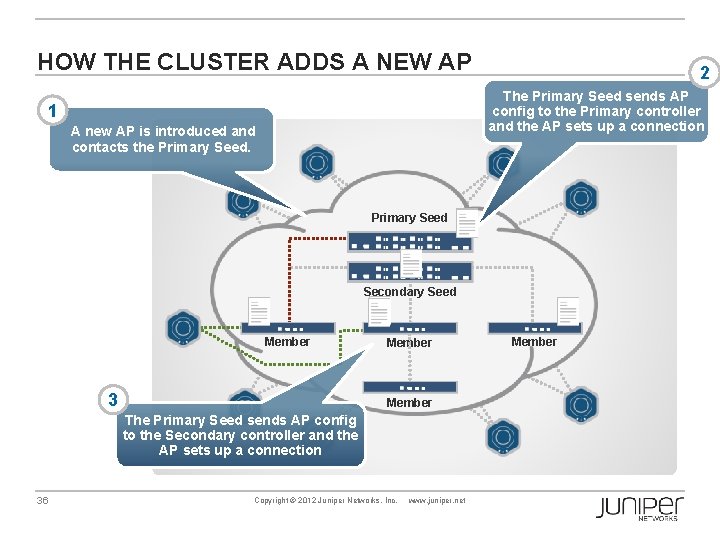
HOW THE CLUSTER ADDS A NEW AP 2 The Primary Seed sends AP config to the Primary controller and the AP sets up a connection 1 A new AP is introduced and contacts the Primary Seed Secondary Seed Member 3 Member The Primary Seed sends AP config to the Secondary controller and the AP sets up a connection 36 Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member

HOW CLIENTS ARE ASSIGNED PRIMARY AND SECONDARY CONTROLLERS Primary controller authenticates/ authorizes client 2 3 Primary Seed Client Session State Secondary Seed Member 1 Member Client Session State A new client associates to the system 37 Primary propagates session details to backup controller for use during failure Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member

Network SIMPLY CONNECTED • Coordinated Threat Control • Wireless – scalability, simplicity, automation • Next – managing congestion 1 2 38 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
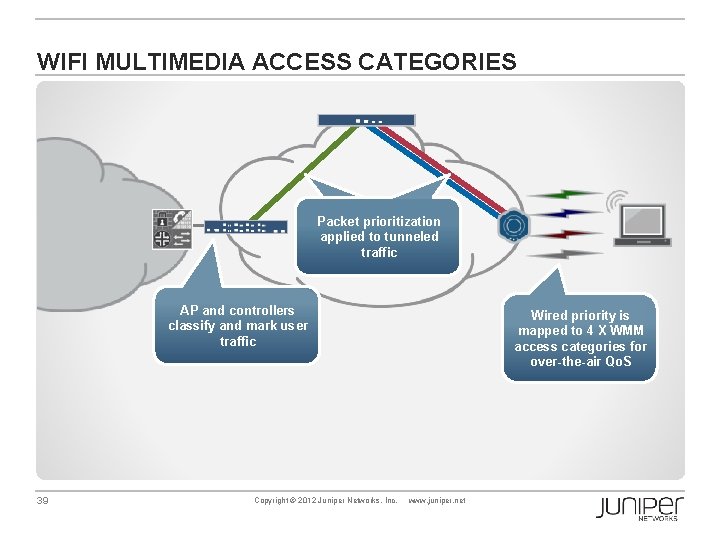
WIFI MULTIMEDIA ACCESS CATEGORIES Packet prioritization applied to tunneled traffic AP and controllers classify and mark user traffic 39 Copyright © 2012 Juniper Networks, Inc. Wired priority is mapped to 4 X WMM access categories for over-the-air Qo. S www. juniper. net
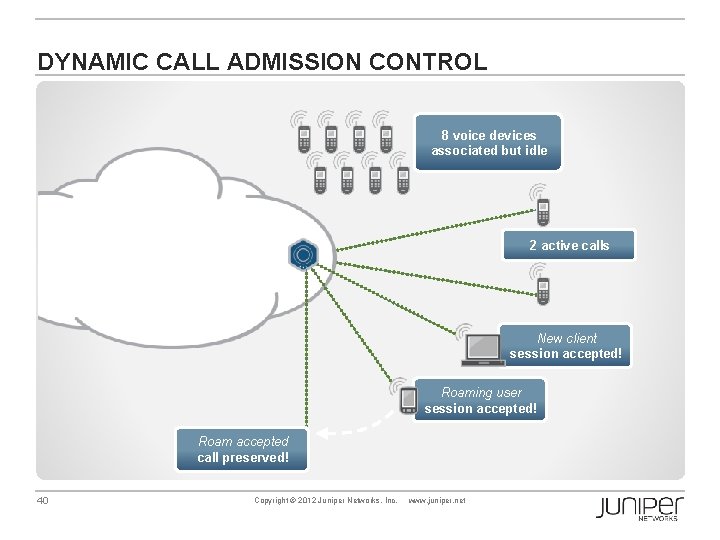
DYNAMIC CALL ADMISSION CONTROL 8 voice devices associated but idle 2 active calls New client session accepted! Roaming user session accepted! Roam accepted call preserved! 40 Copyright © 2012 Juniper Networks, Inc. www. juniper. net

AUTOMATIC CLIENT LOAD BALANCING Automatic Load Balancing per RF Band Steering 5 GHz capable client ‘encouraged’ to connect at 5 GHz 2. 4 GHz only client connects at 2. 4 GHz 41 Copyright © 2012 Juniper Networks, Inc. www. juniper. net

Network SIMPLY CONNECTED • • Coordinated Threat Control Wireless – scalability, simplicity, automation Managing congestion Next – Simplifying the wired network 1 3 2 42 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
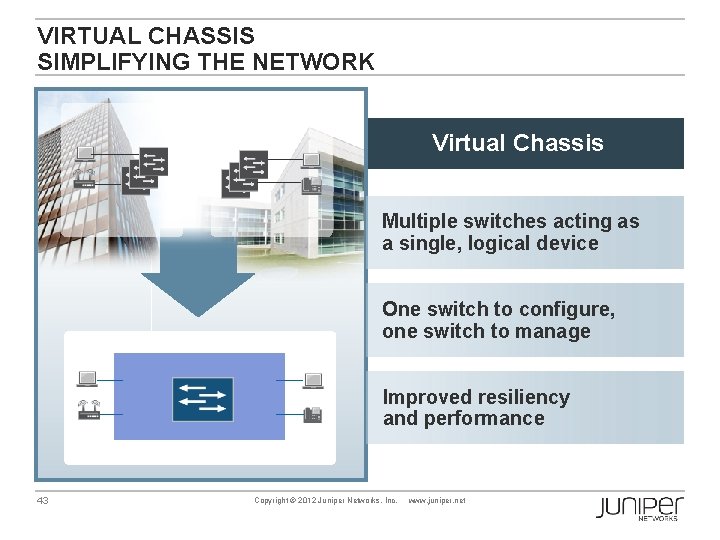
VIRTUAL CHASSIS SIMPLIFYING THE NETWORK Virtual Chassis Multiple switches acting as a single, logical device One switch to configure, one switch to manage Improved resiliency and performance 43 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
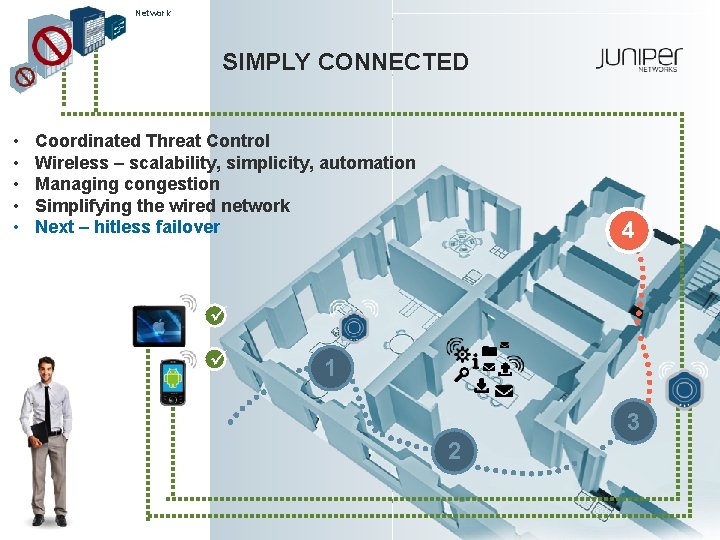
Network SIMPLY CONNECTED • • • Coordinated Threat Control Wireless – scalability, simplicity, automation Managing congestion Simplifying the wired network Next – hitless failover 4 1 3 2 44 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
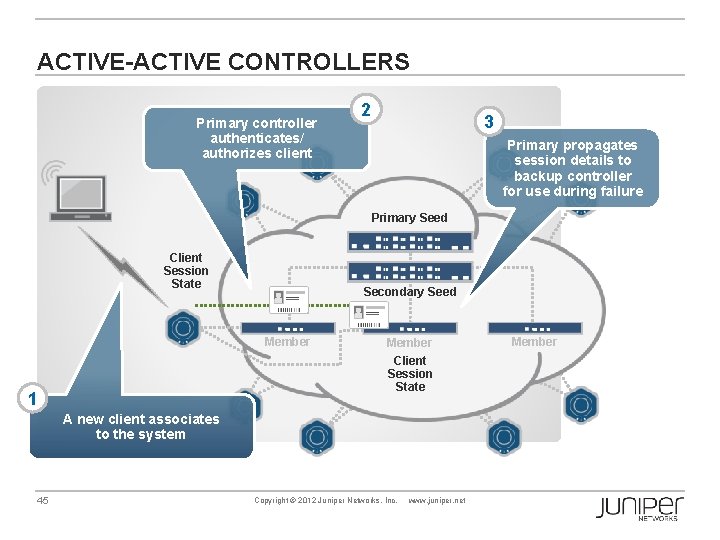
ACTIVE-ACTIVE CONTROLLERS Primary controller authenticates/ authorizes client 2 3 Primary propagates session details to backup controller for use during failure Primary Seed Client Session State Secondary Seed Member 1 Member Client Session State A new client associates to the system 45 Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member
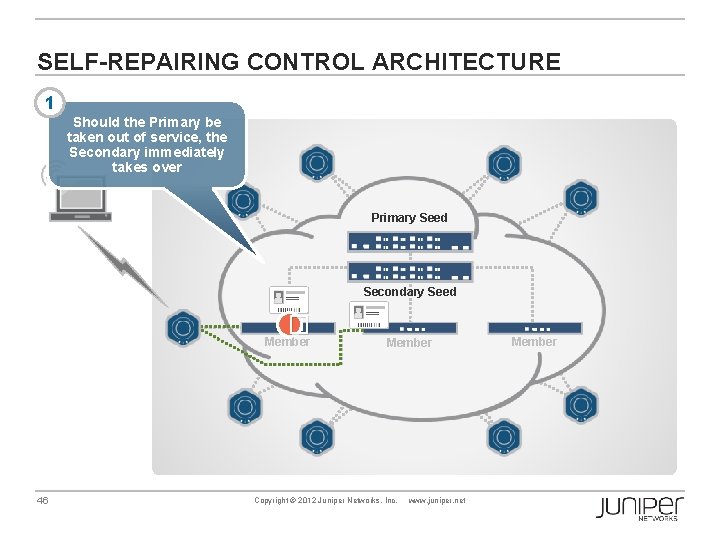
SELF-REPAIRING CONTROL ARCHITECTURE 1 Should the Primary be taken out of service, the Secondary immediately takes over Primary Seed Secondary Seed � Member 46 Member Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member

NONSTOP OPERATION HITLESS FAILOVER 2 Primary Seed A new Secondary is designated and is given the AP configuration and client session state Secondary Seed Member 47 Copyright © 2012 Juniper Networks, Inc. www. juniper. net Member
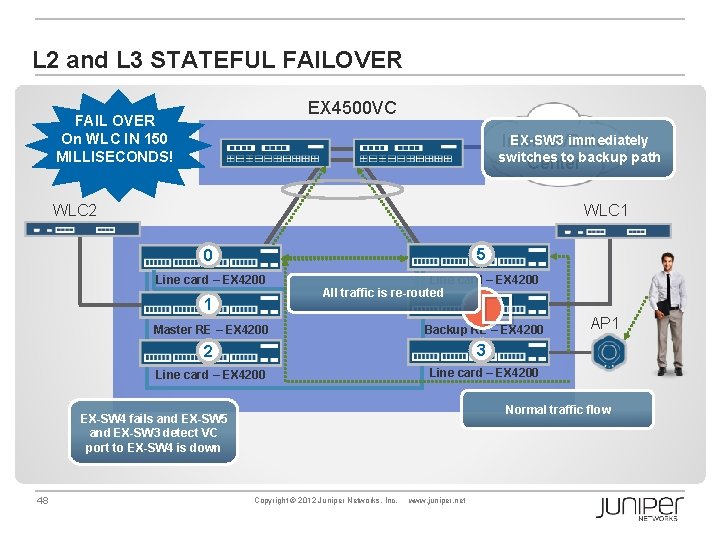
L 2 and L 3 STATEFUL FAILOVER EX 4500 VC FAIL OVER On WLC IN 150 MILLISECONDS! EX-SW 3 immediately Internet/Data switches to backup path Center WLC 2 WLC 1 5 0 Line card – EX 4200 All traffic is re-routed � 4 1 Master RE – EX 4200 Backup RE – EX 4200 2 3 Line card – EX 4200 Normal traffic flow EX-SW 4 fails and EX-SW 5 and EX-SW 3 detect VC port to EX-SW 4 is down 48 AP 1 Copyright © 2012 Juniper Networks, Inc. www. juniper. net

Network SIMPLY CONNECTED • • • Coordinated Threat Control Wireless – scalability, simplicity, automation Managing congestion Simplifying the wired network Hitless failover Next – Consistent security X 5 4 1 3 2 49 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
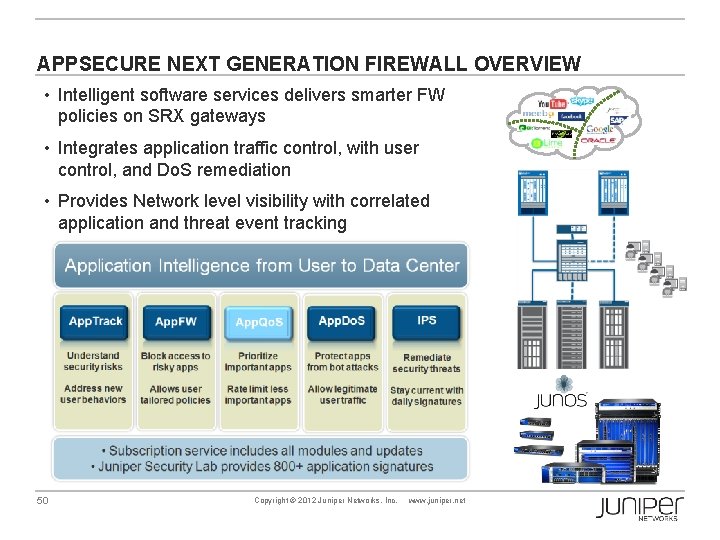
APPSECURE NEXT GENERATION FIREWALL OVERVIEW • Intelligent software services delivers smarter FW policies on SRX gateways • Integrates application traffic control, with user control, and Do. S remediation • Provides Network level visibility with correlated application and threat event tracking 50 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
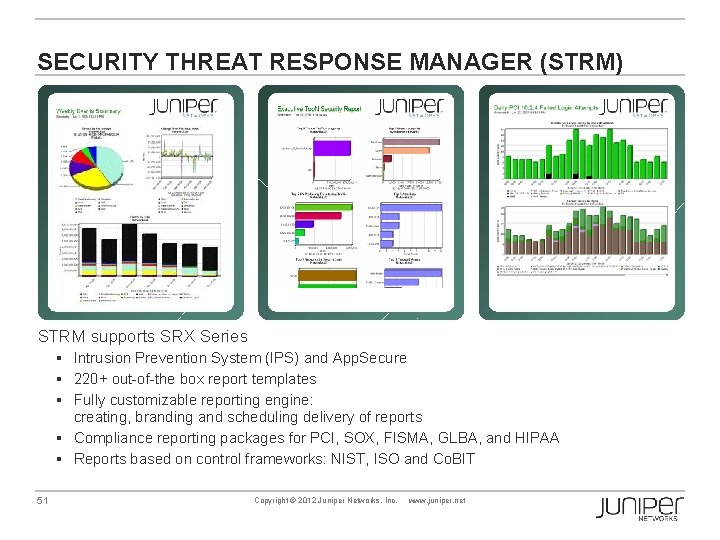
SECURITY THREAT RESPONSE MANAGER (STRM) STRM supports SRX Series § Intrusion Prevention System (IPS) and App. Secure § 220+ out-of-the box report templates § Fully customizable reporting engine: creating, branding and scheduling delivery of reports § Compliance reporting packages for PCI, SOX, FISMA, GLBA, and HIPAA § Reports based on control frameworks: NIST, ISO and Co. BIT 51 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
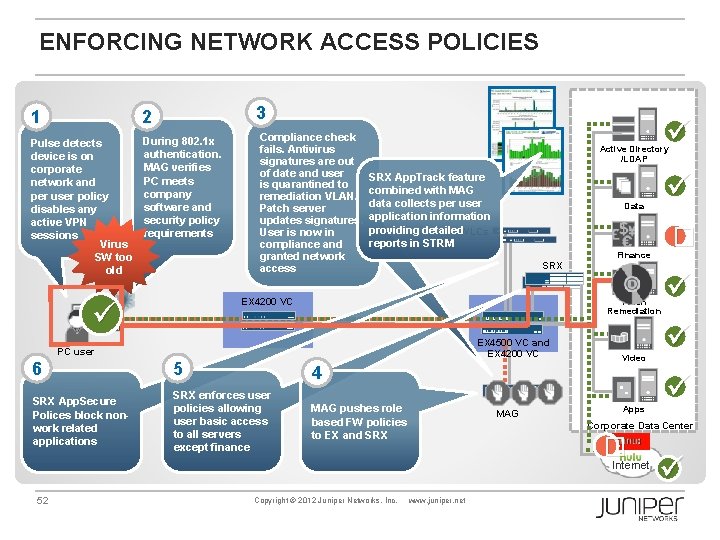
ENFORCING NETWORK ACCESS POLICIES 3 1 2 Pulse detects device is on corporate network and per user policy disables any active VPN sessions Virus SW too old During 802. 1 x authentication. MAG verifies PC meets company software and security policy requirements Compliance check fails. Antivirus signatures are out of date and user is quarantined to remediation VLAN. Patch server updates signatures. User is now in compliance and granted network access Active Directory /LDAP SRX App. Track feature combined with MAG data collects per user application information providing detailed. WLCs reports in STRM � Finance SRX EX 4200 VC Patch Remediation EX 4500 VC and EX 4200 VC PC user 6 5 4 SRX App. Secure Polices block nonwork related applications SRX enforces user policies allowing user basic access to all servers except finance MAG pushes role based FW policies to EX and SRX MAG Video Apps Copyright © 2012 Juniper Networks, Inc. Corporate Data Center � Internet 52 Data www. juniper. net
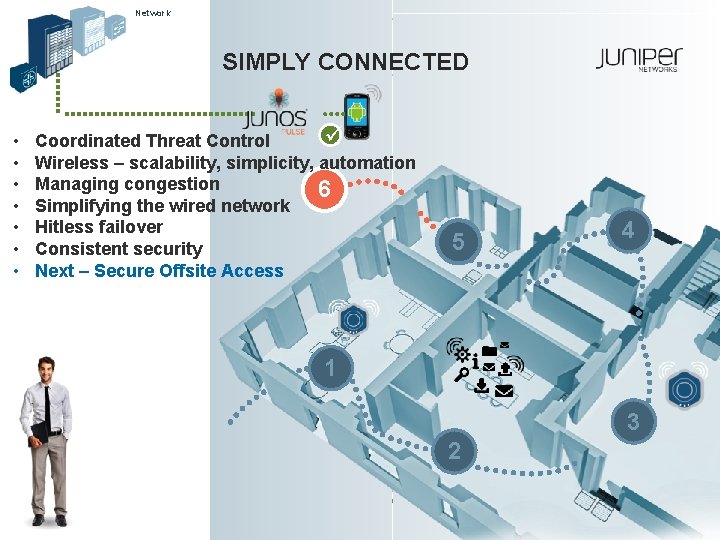
Network SIMPLY CONNECTED • • Coordinated Threat Control Wireless – scalability, simplicity, automation Managing congestion 6 Simplifying the wired network Hitless failover Consistent security Next – Secure Offsite Access 5 4 1 3 2 53 Copyright © 2012 Juniper Networks, Inc. www. juniper. net
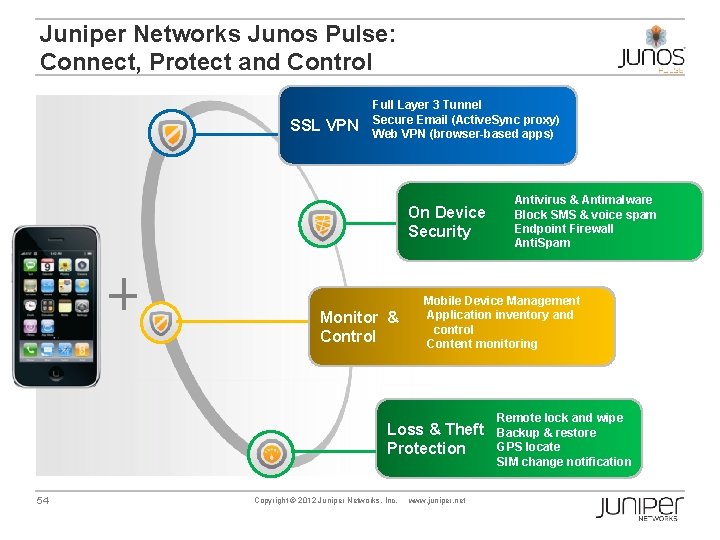
Juniper Networks Junos Pulse: Connect, Protect and Control SSL VPN Full Layer 3 Tunnel Secure Email (Active. Sync proxy) Web VPN (browser-based apps) On Device Security Monitor & Control Mobile Device Management Application inventory and control Content monitoring Loss & Theft Protection 54 Copyright © 2012 Juniper Networks, Inc. Antivirus & Antimalware Block SMS & voice spam Endpoint Firewall Anti. Spam www. juniper. net Remote lock and wipe Backup & restore GPS locate SIM change notification
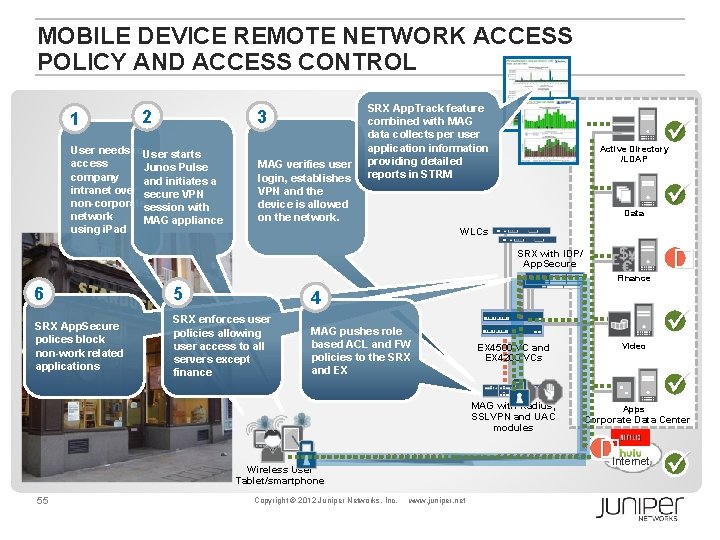
MOBILE DEVICE REMOTE NETWORK ACCESS POLICY AND ACCESS CONTROL 1 2 3 User needs to. User starts access Junos Pulse company and initiates a intranet over secure VPN non-corporatesession with network MAG appliance using i. Pad MAG verifies user login, establishes VPN and the device is allowed on the network. SRX App. Track feature combined with MAG data collects per user application information providing detailed reports in STRM Active Directory /LDAP Data WLCs � SRX with IDP/ App. Secure Finance 6 5 4 SRX App. Secure polices block non-work related applications SRX enforces user policies allowing user access to all servers except finance MAG pushes role based ACL and FW policies to the SRX and EX Copyright © 2012 Juniper Networks, Inc. Video MAG with Radius, SSLVPN and UAC modules Apps www. juniper. net Corporate Data Center �Internet Wireless User Tablet/smartphone 55 EX 4500 VC and EX 4200 VCs
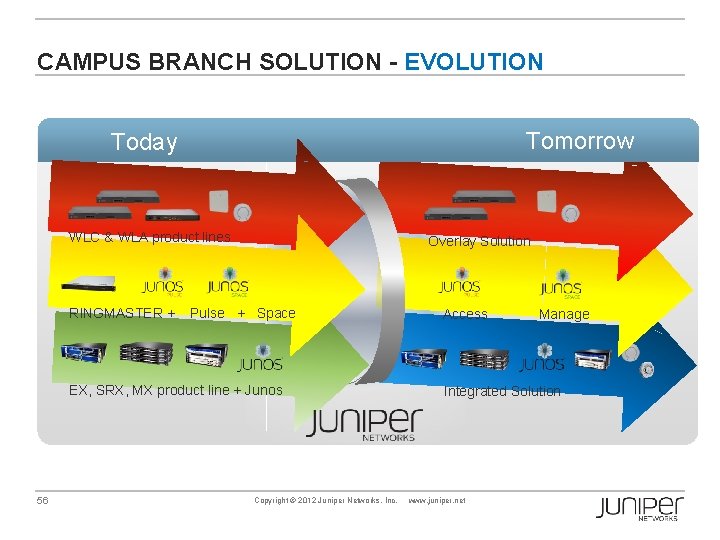
CAMPUS BRANCH SOLUTION - EVOLUTION Tomorrow Today WLC & WLA product lines RINGMASTER + Overlay Solution Pulse + Space EX, SRX, MX product line + Junos 56 Copyright © 2012 Juniper Networks, Inc. Access Manage Integrated Solution www. juniper. net
- Slides: 56