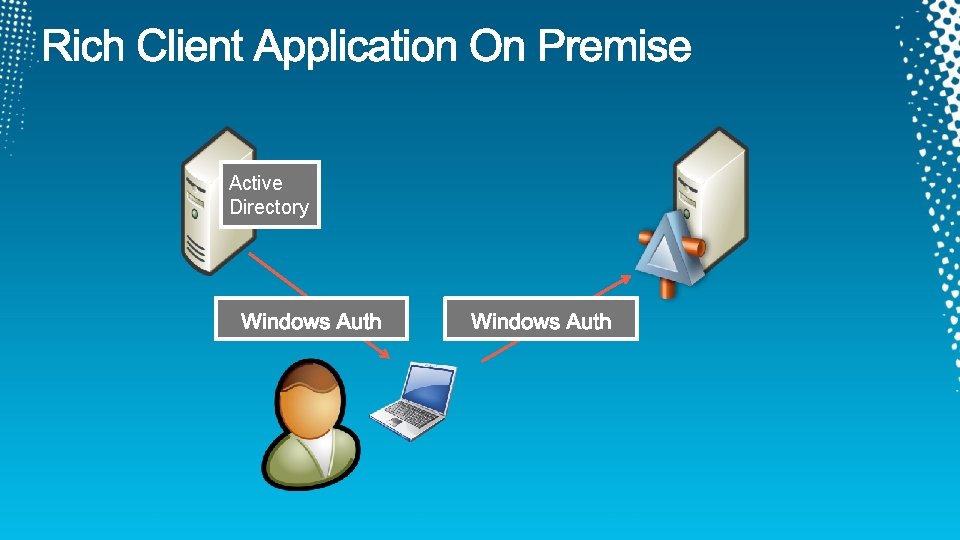
SIM 323 Active Directory Active Directory Active Directory






![https: //[server]/adfs/services/trust/13/usernamemixed https: //[server]/adfs/services/trust/13/windowstransport https: //[server]/adfs/services/trust/13/usernamemixed https: //[server]/adfs/services/trust/13/windowstransport](https://slidetodoc.com/presentation_image_h2/431c8b9bfece818677ee4dfefa8b0cb1/image-19.jpg)











- Slides: 57
SIM 323
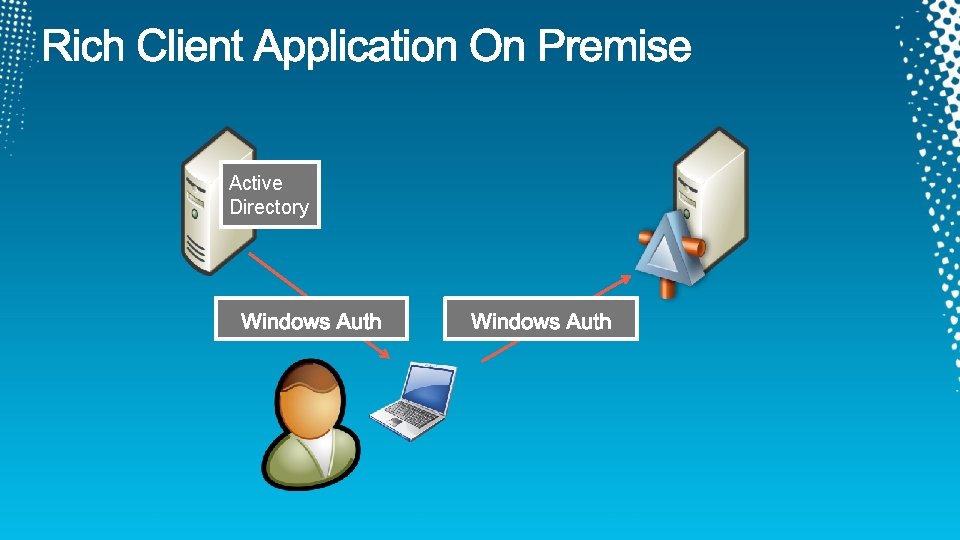
Active Directory

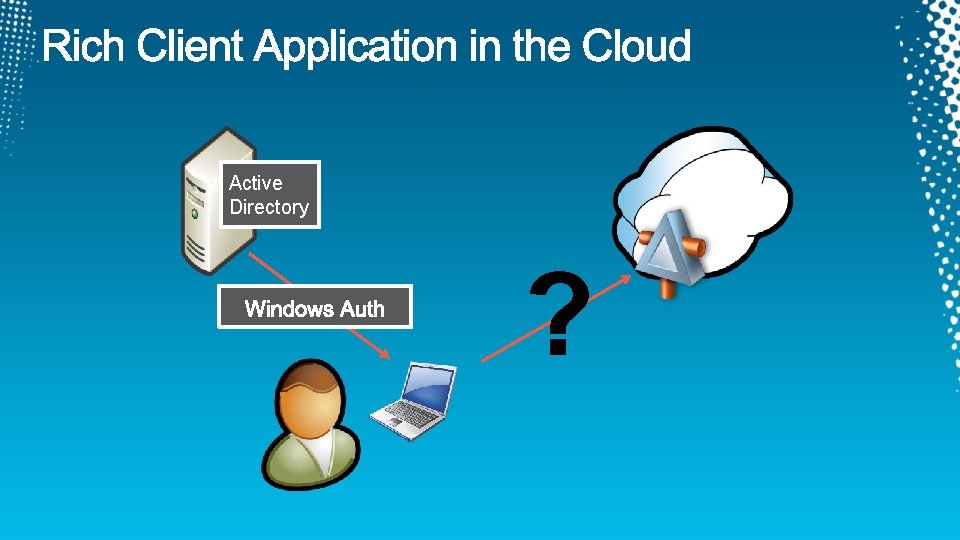
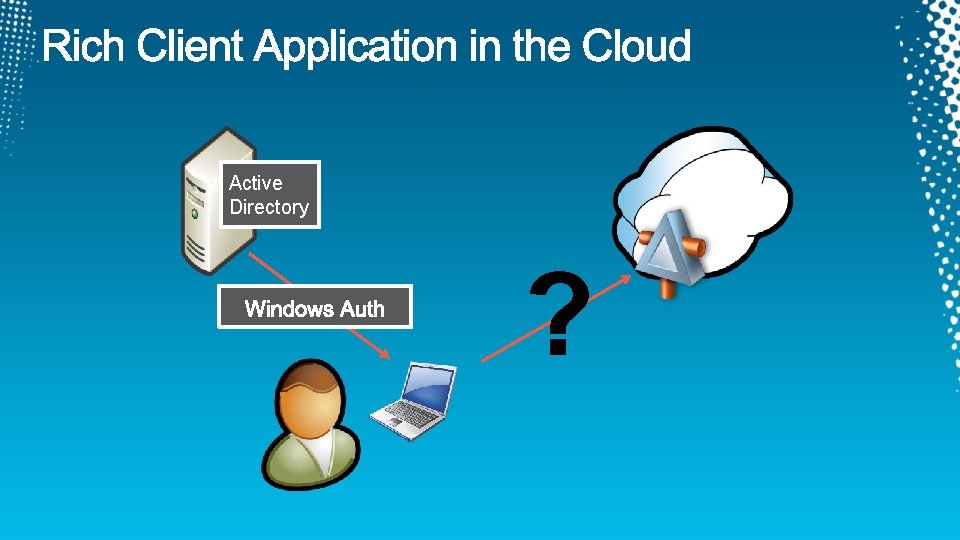
Active Directory ?


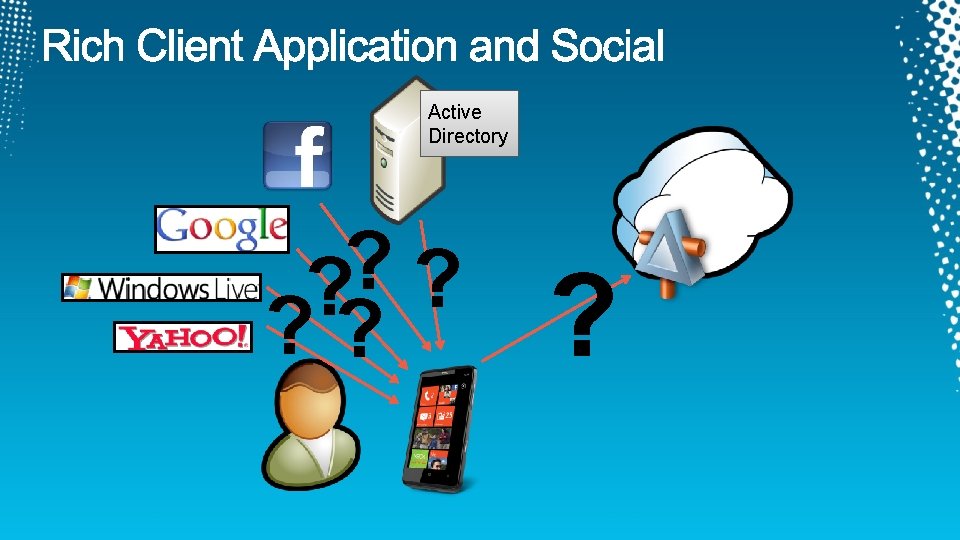
Active Directory ? ?

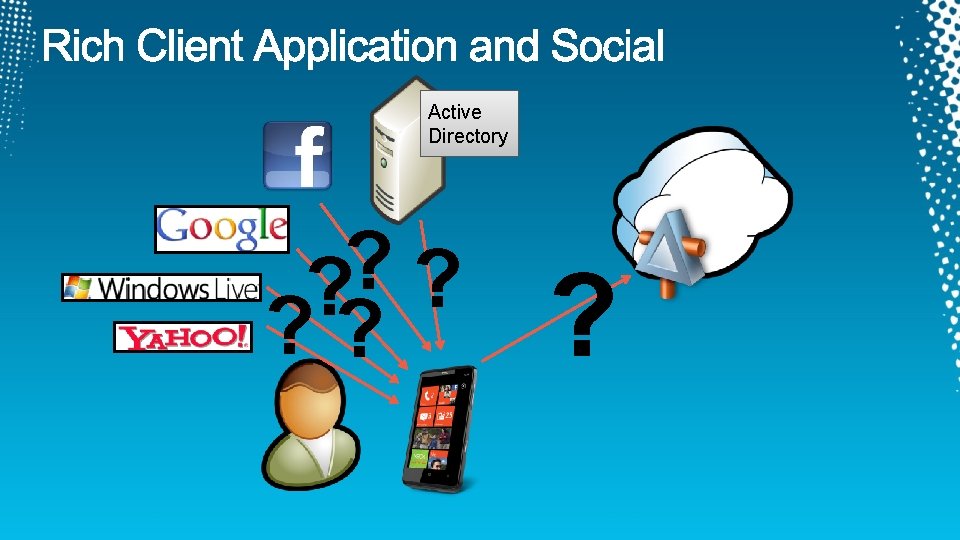
Active Directory ? ? ? ?

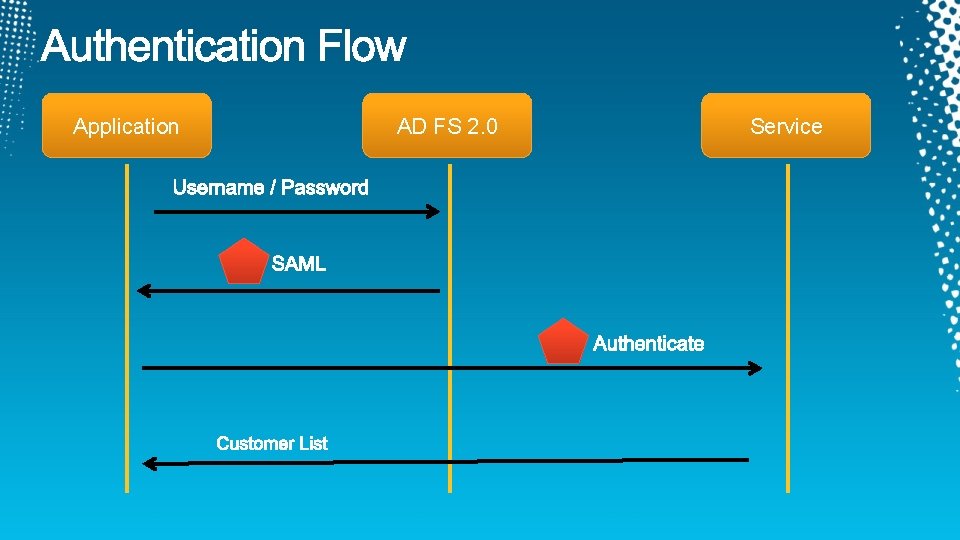
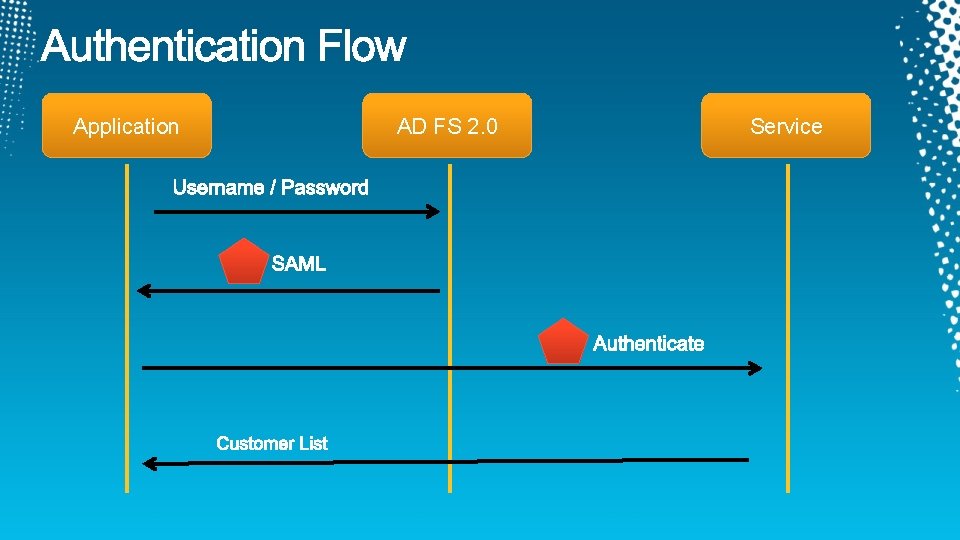
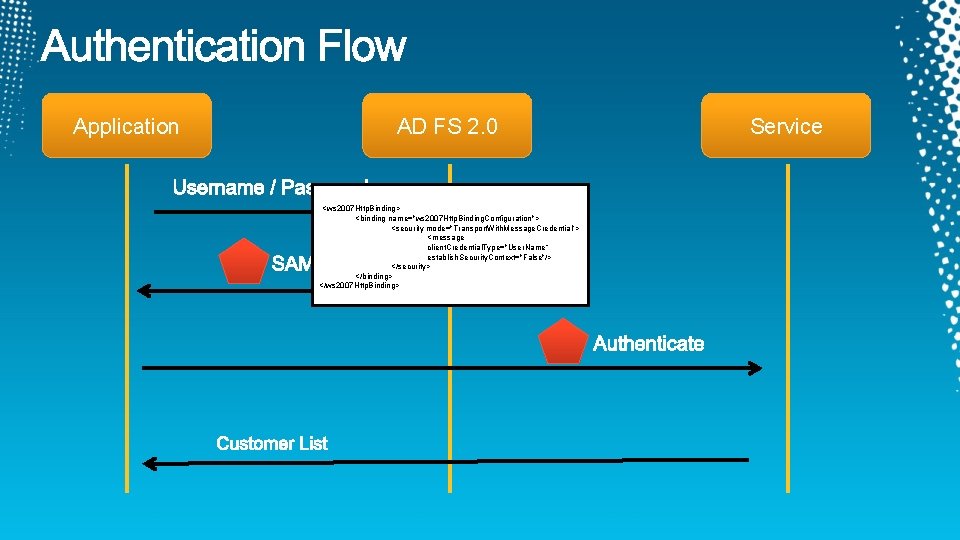
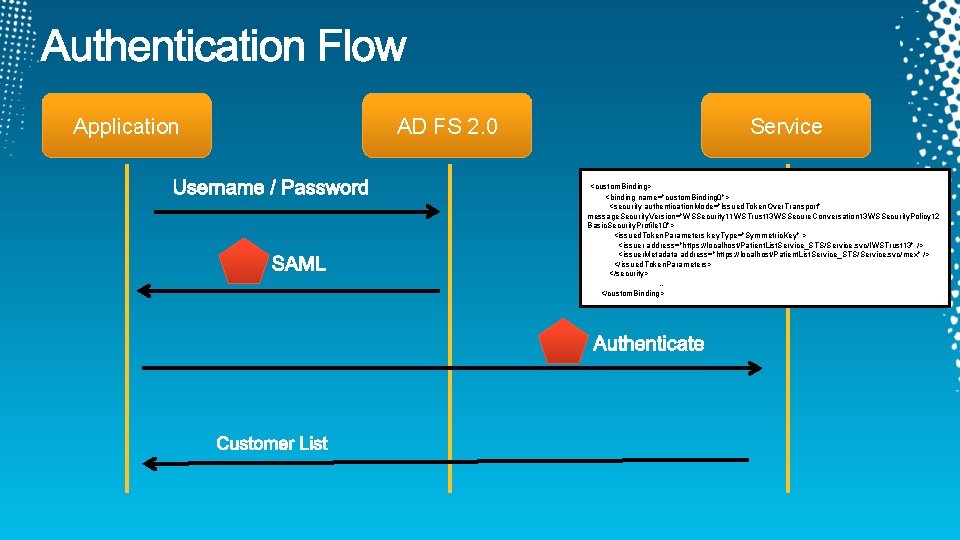
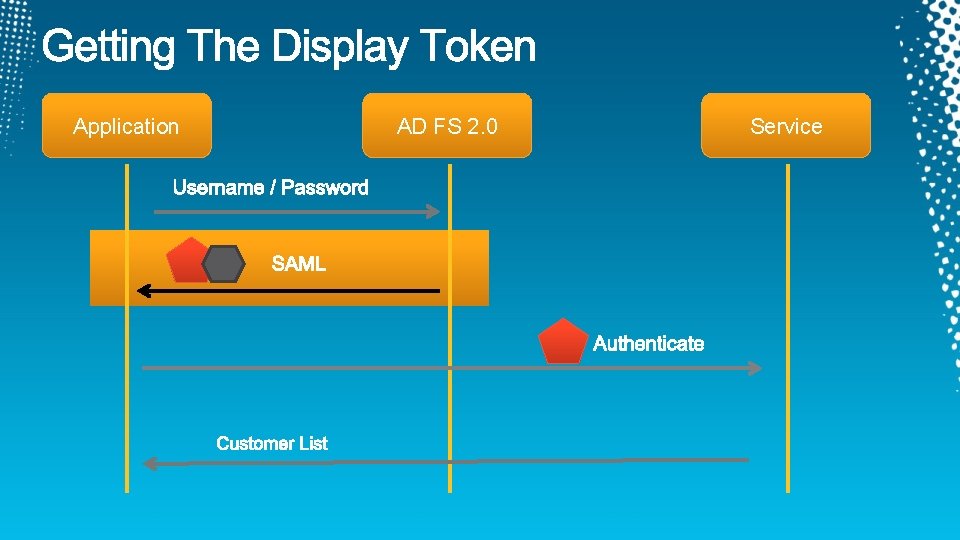
Application AD FS 2. 0 Service

demo
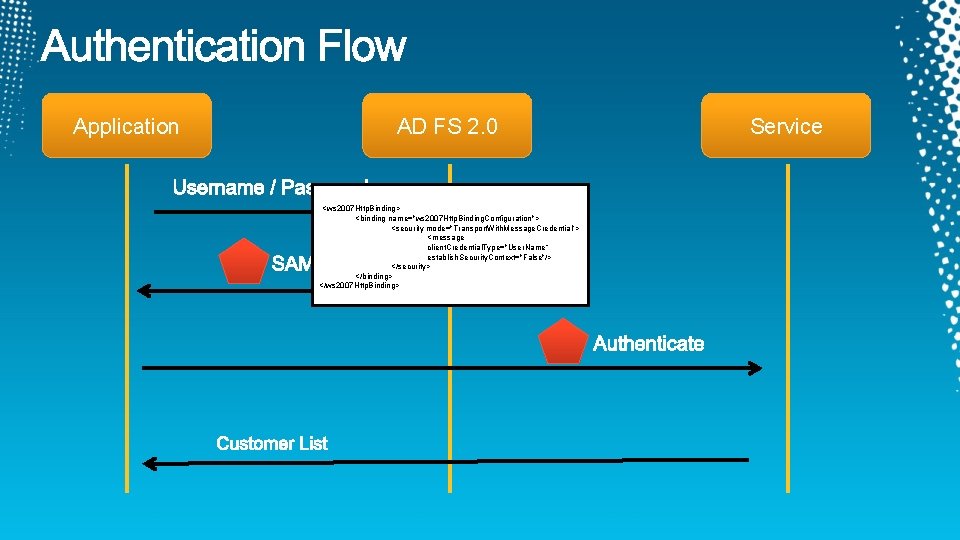
Application AD FS 2. 0 <ws 2007 Http. Binding> <binding name="ws 2007 Http. Binding. Configuration"> <security mode="Transport. With. Message. Credential"> <message client. Credential. Type="User. Name“ establish. Security. Context="False"/> </security> </binding> </ws 2007 Http. Binding> Service
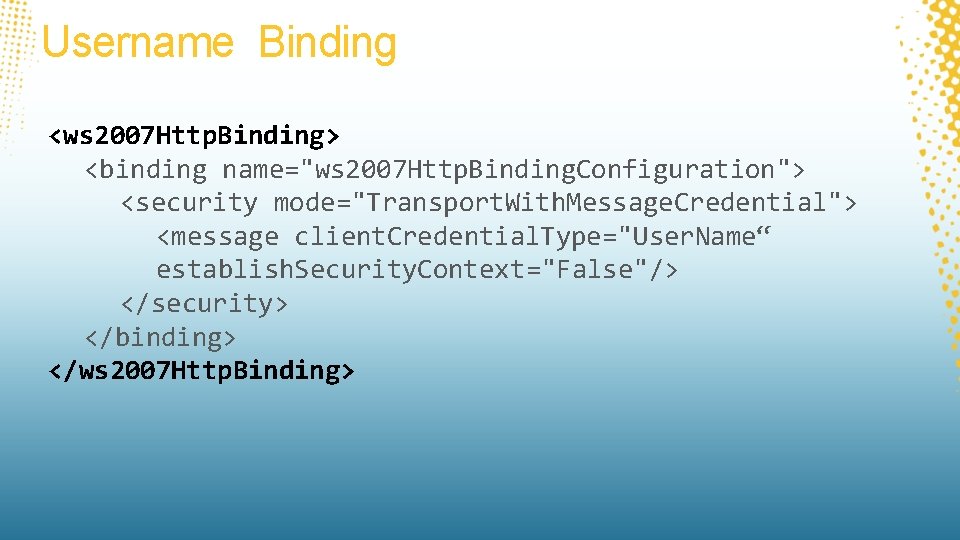
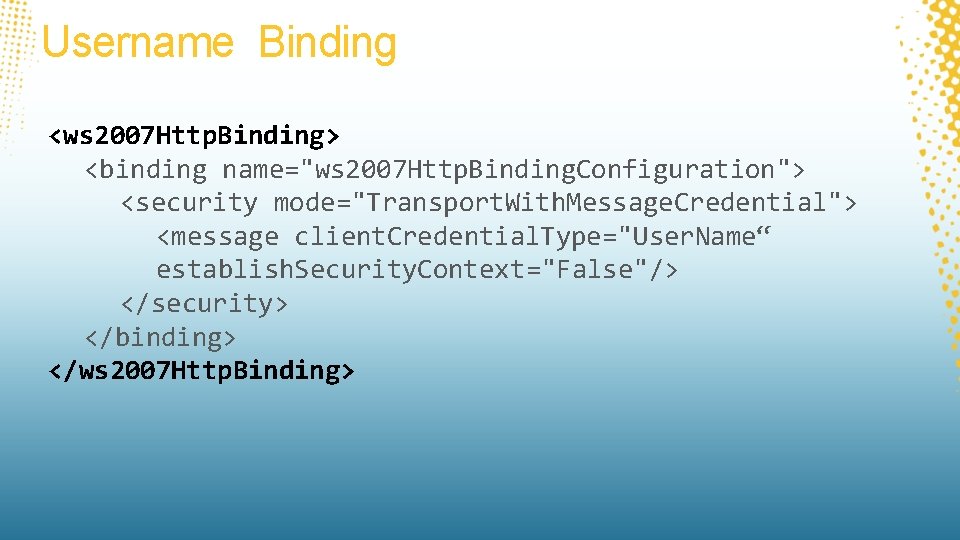
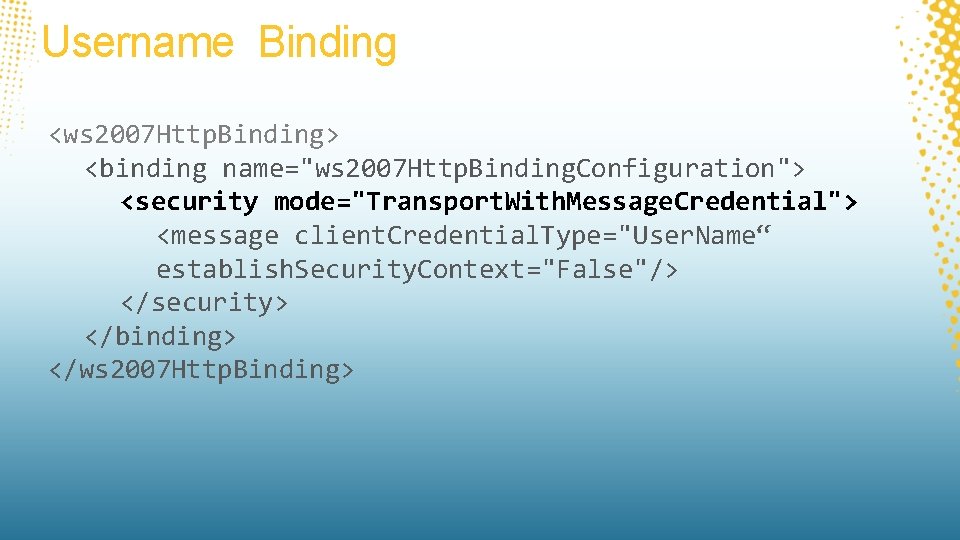
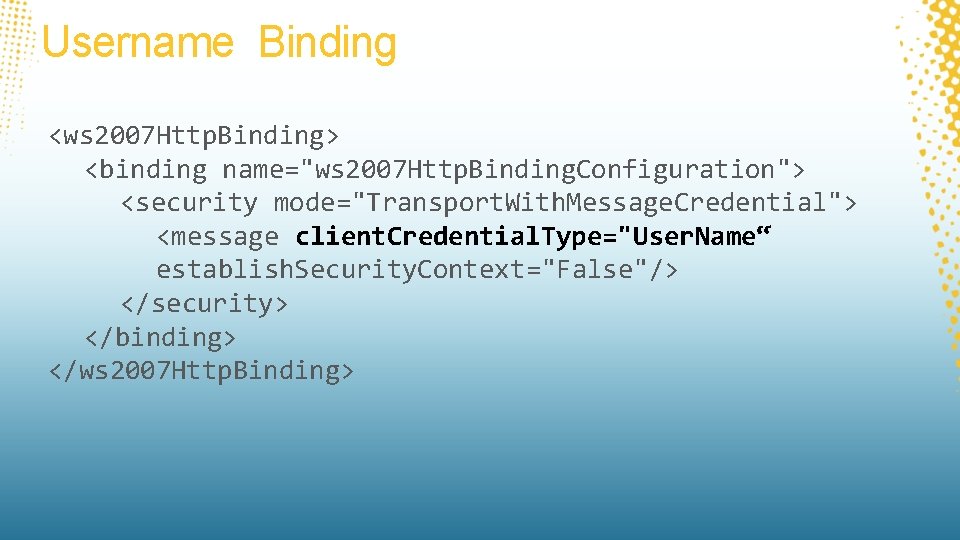
Username Binding <ws 2007 Http. Binding> <binding name="ws 2007 Http. Binding. Configuration"> <security mode="Transport. With. Message. Credential"> <message client. Credential. Type="User. Name“ establish. Security. Context="False"/> </security> </binding> </ws 2007 Http. Binding>
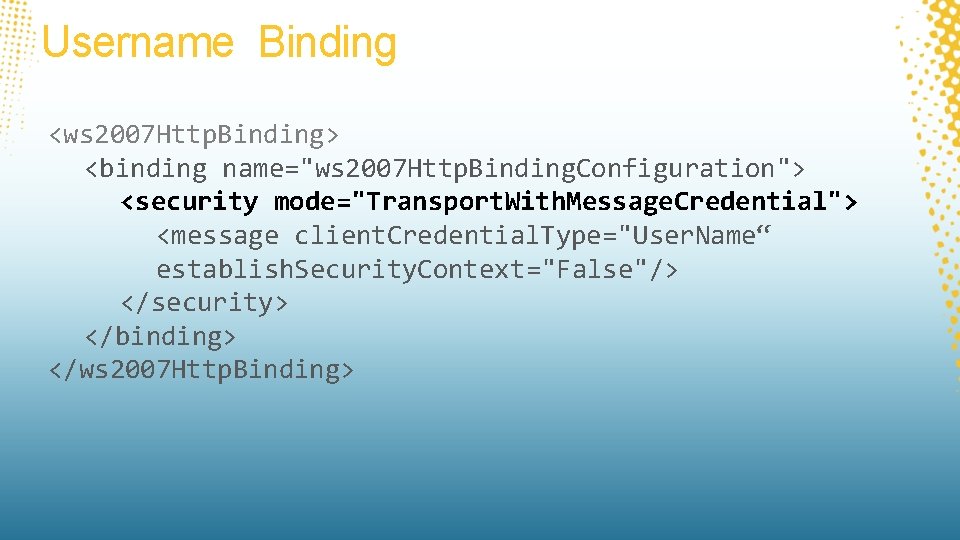
Username Binding <ws 2007 Http. Binding> <binding name="ws 2007 Http. Binding. Configuration"> <security mode="Transport. With. Message. Credential"> <message client. Credential. Type="User. Name“ establish. Security. Context="False"/> </security> </binding> </ws 2007 Http. Binding>
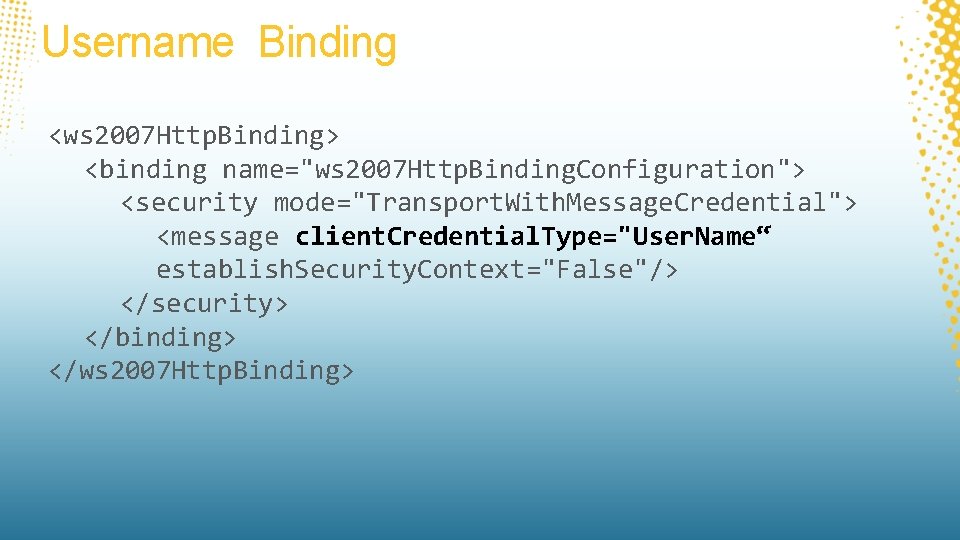
Username Binding <ws 2007 Http. Binding> <binding name="ws 2007 Http. Binding. Configuration"> <security mode="Transport. With. Message. Credential"> <message client. Credential. Type="User. Name“ establish. Security. Context="False"/> </security> </binding> </ws 2007 Http. Binding>
![https serveradfsservicestrust13usernamemixed https serveradfsservicestrust13windowstransport https: //[server]/adfs/services/trust/13/usernamemixed https: //[server]/adfs/services/trust/13/windowstransport](https://slidetodoc.com/presentation_image_h2/431c8b9bfece818677ee4dfefa8b0cb1/image-19.jpg)
https: //[server]/adfs/services/trust/13/usernamemixed https: //[server]/adfs/services/trust/13/windowstransport
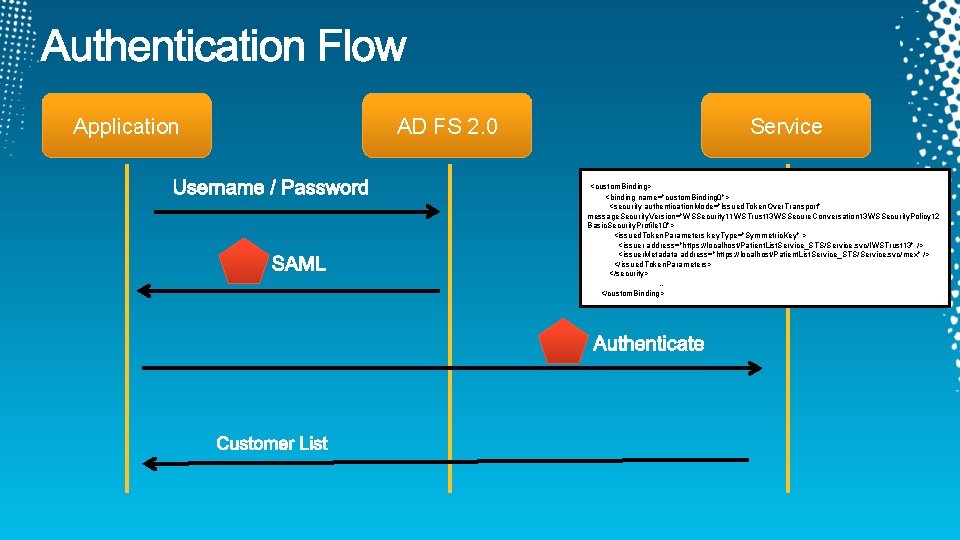
Application AD FS 2. 0 Service <custom. Binding> <binding name="custom. Binding 0"> <security authentication. Mode="Issued. Token. Over. Transport" message. Security. Version="WSSecurity 11 WSTrust 13 WSSecure. Conversation 13 WSSecurity. Policy 12 Basic. Security. Profile 10"> <issued. Token. Parameters key. Type="Symmetric. Key" > <issuer address="https: //localhost/Patient. List. Service_STS/Service. svc/IWSTrust 13" /> <issuer. Metadata address="https: //localhost/Patient. List. Service_STS/Service. svc/mex" /> </issued. Token. Parameters> </security> … </custom. Binding>
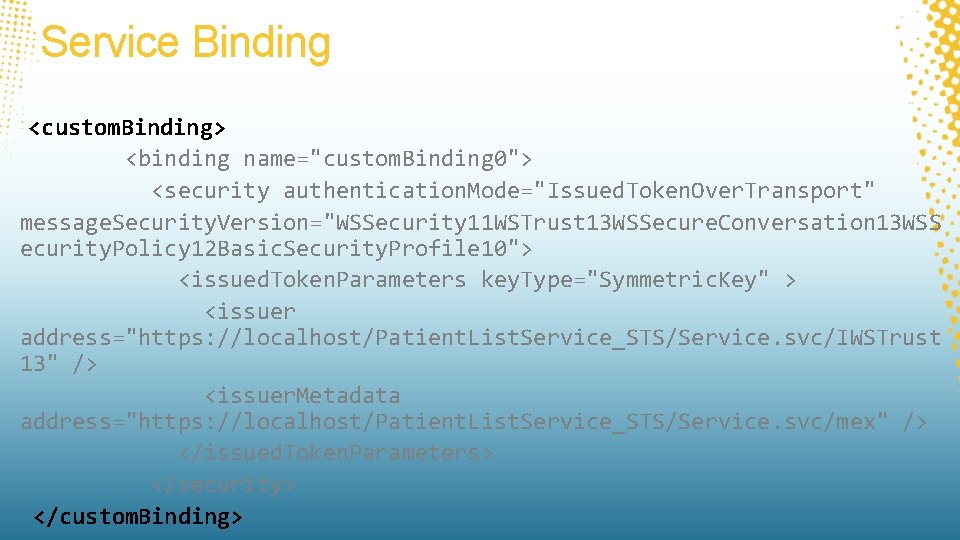
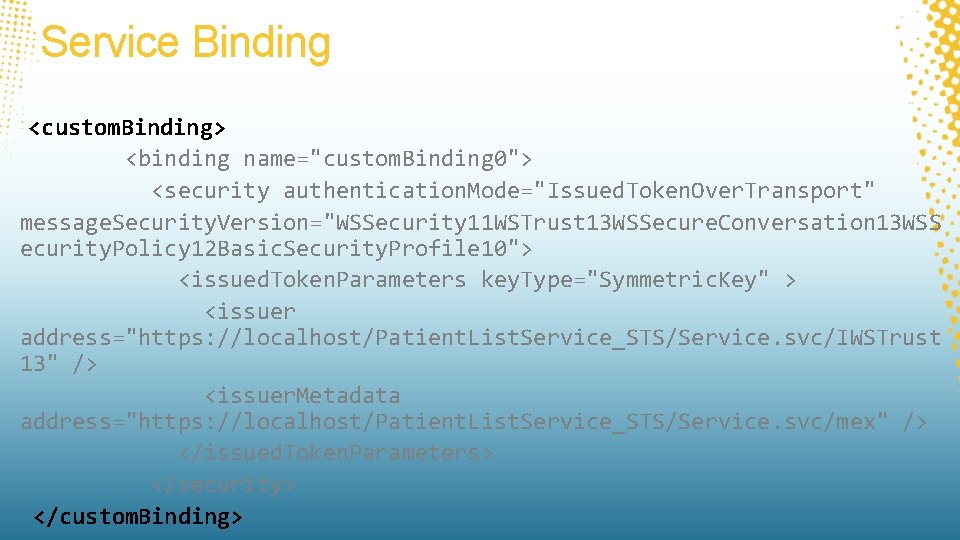
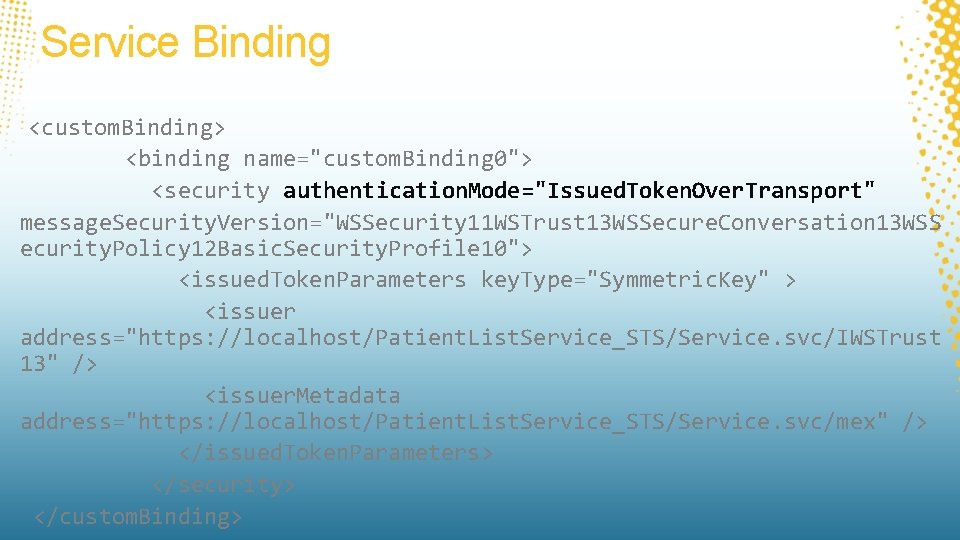
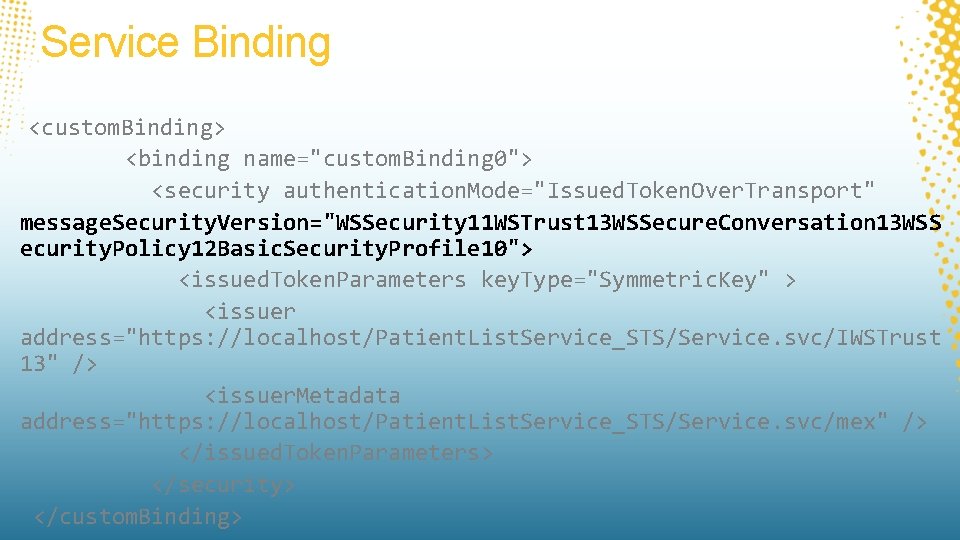
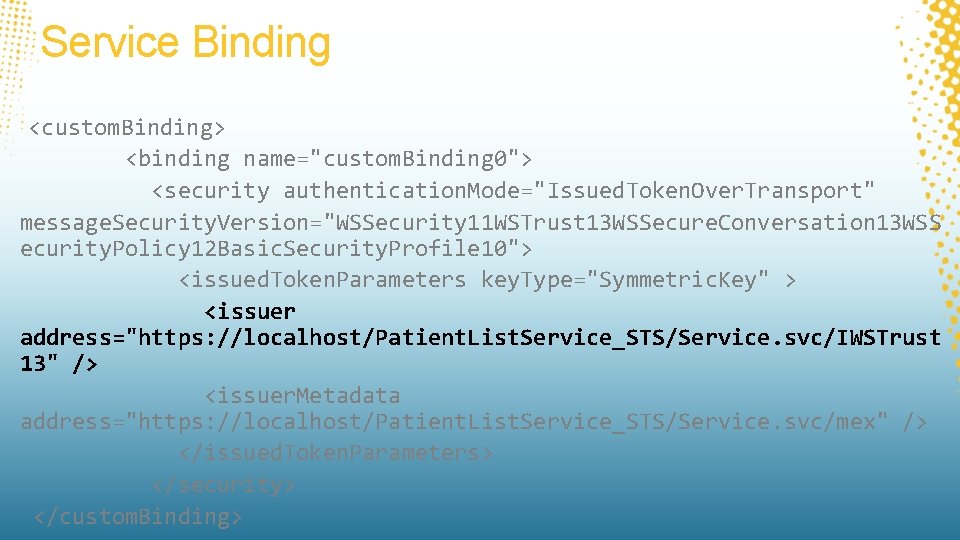
Service Binding <custom. Binding> <binding name="custom. Binding 0"> <security authentication. Mode="Issued. Token. Over. Transport" message. Security. Version="WSSecurity 11 WSTrust 13 WSSecure. Conversation 13 WSS ecurity. Policy 12 Basic. Security. Profile 10"> <issued. Token. Parameters key. Type="Symmetric. Key" > <issuer address="https: //localhost/Patient. List. Service_STS/Service. svc/IWSTrust 13" /> <issuer. Metadata address="https: //localhost/Patient. List. Service_STS/Service. svc/mex" /> </issued. Token. Parameters> </security> </custom. Binding>
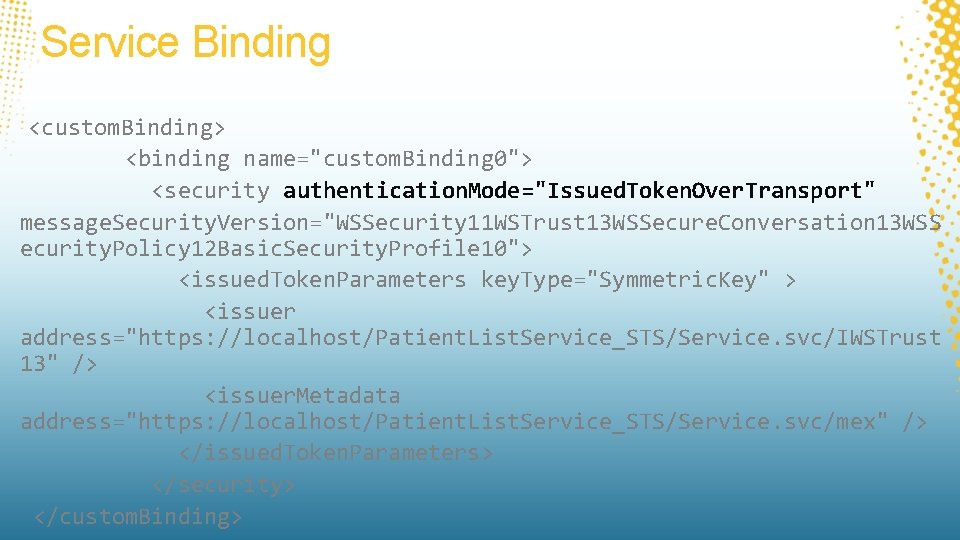
Service Binding <custom. Binding> <binding name="custom. Binding 0"> <security authentication. Mode="Issued. Token. Over. Transport" message. Security. Version="WSSecurity 11 WSTrust 13 WSSecure. Conversation 13 WSS ecurity. Policy 12 Basic. Security. Profile 10"> <issued. Token. Parameters key. Type="Symmetric. Key" > <issuer address="https: //localhost/Patient. List. Service_STS/Service. svc/IWSTrust 13" /> <issuer. Metadata address="https: //localhost/Patient. List. Service_STS/Service. svc/mex" /> </issued. Token. Parameters> </security> </custom. Binding>
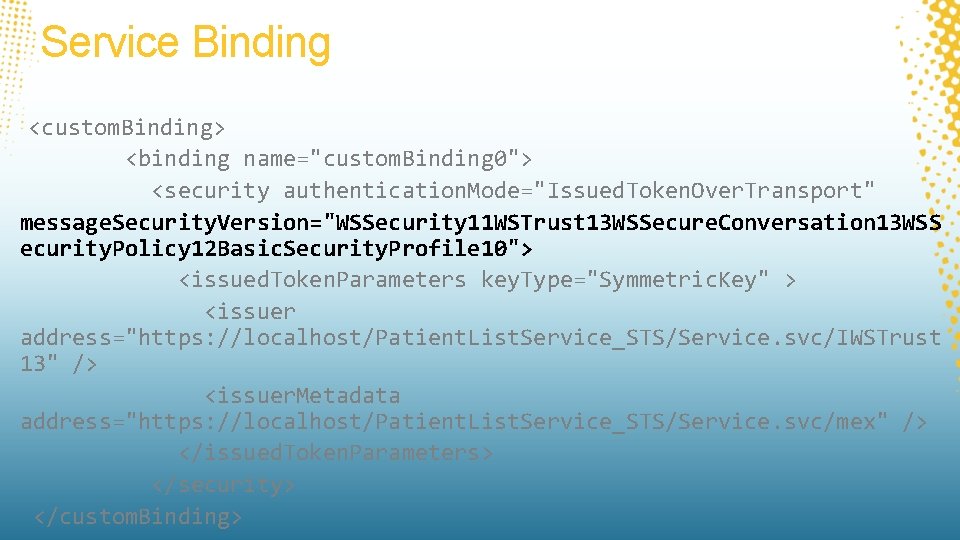
Service Binding <custom. Binding> <binding name="custom. Binding 0"> <security authentication. Mode="Issued. Token. Over. Transport" message. Security. Version="WSSecurity 11 WSTrust 13 WSSecure. Conversation 13 WSS ecurity. Policy 12 Basic. Security. Profile 10"> <issued. Token. Parameters key. Type="Symmetric. Key" > <issuer address="https: //localhost/Patient. List. Service_STS/Service. svc/IWSTrust 13" /> <issuer. Metadata address="https: //localhost/Patient. List. Service_STS/Service. svc/mex" /> </issued. Token. Parameters> </security> </custom. Binding>
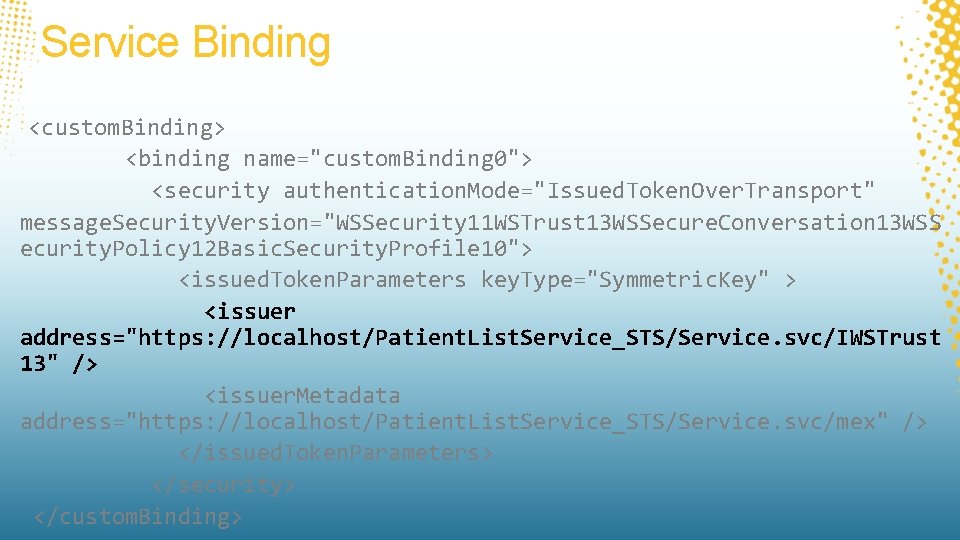
Service Binding <custom. Binding> <binding name="custom. Binding 0"> <security authentication. Mode="Issued. Token. Over. Transport" message. Security. Version="WSSecurity 11 WSTrust 13 WSSecure. Conversation 13 WSS ecurity. Policy 12 Basic. Security. Profile 10"> <issued. Token. Parameters key. Type="Symmetric. Key" > <issuer address="https: //localhost/Patient. List. Service_STS/Service. svc/IWSTrust 13" /> <issuer. Metadata address="https: //localhost/Patient. List. Service_STS/Service. svc/mex" /> </issued. Token. Parameters> </security> </custom. Binding>
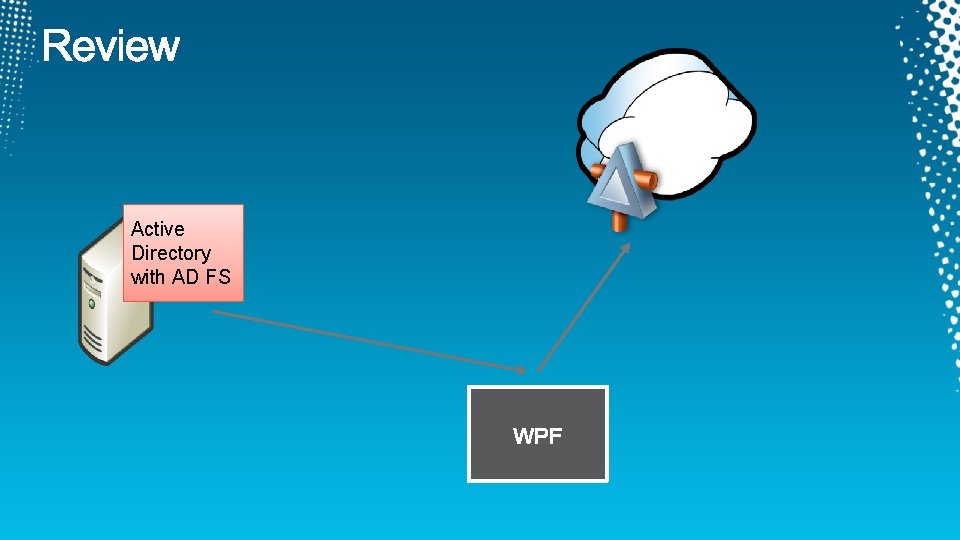
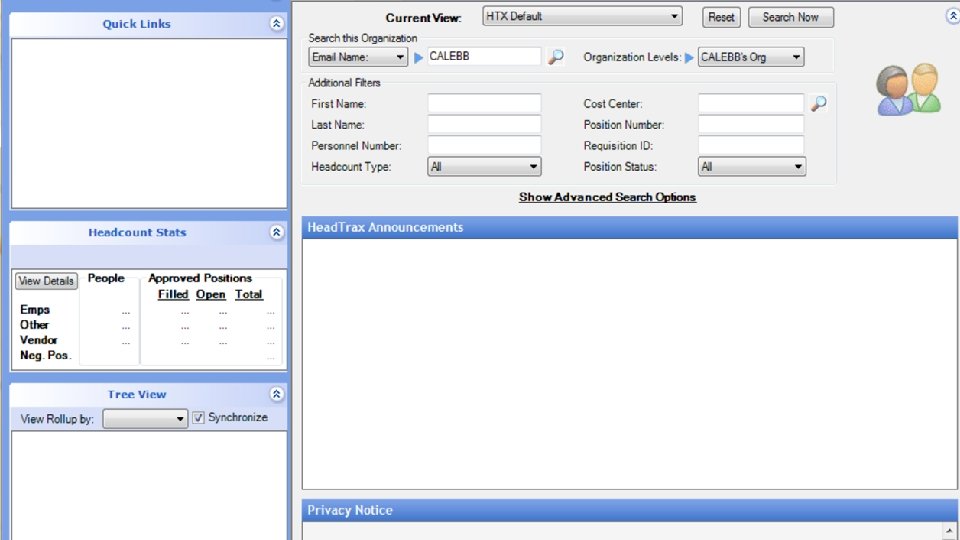
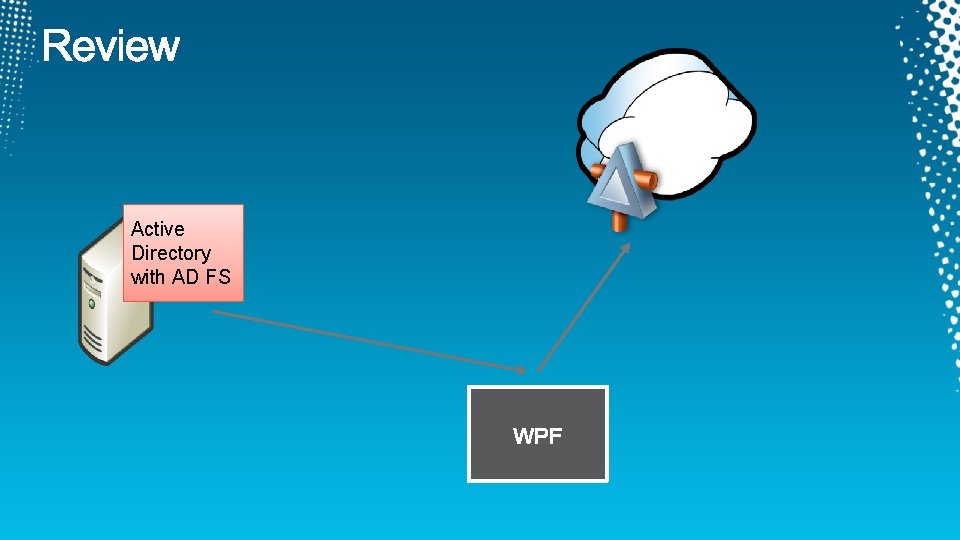
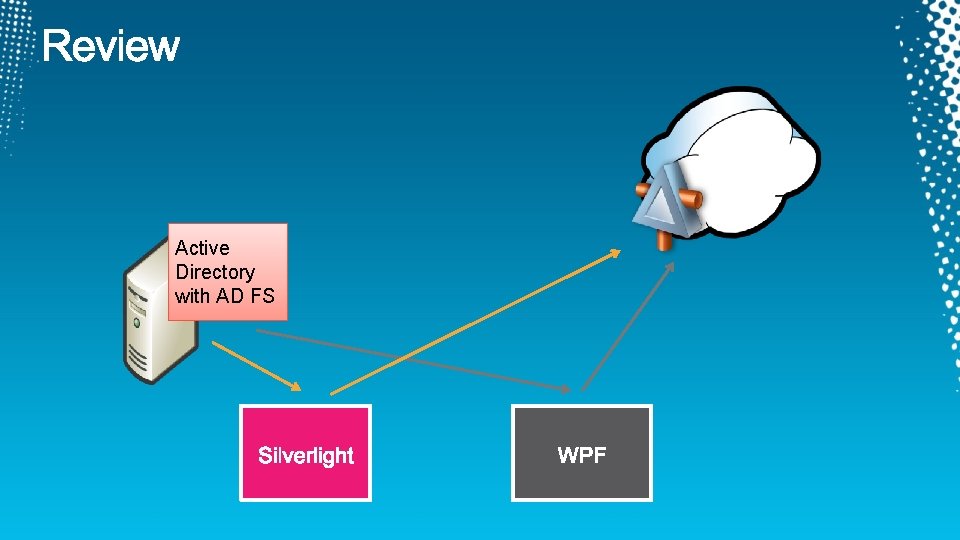
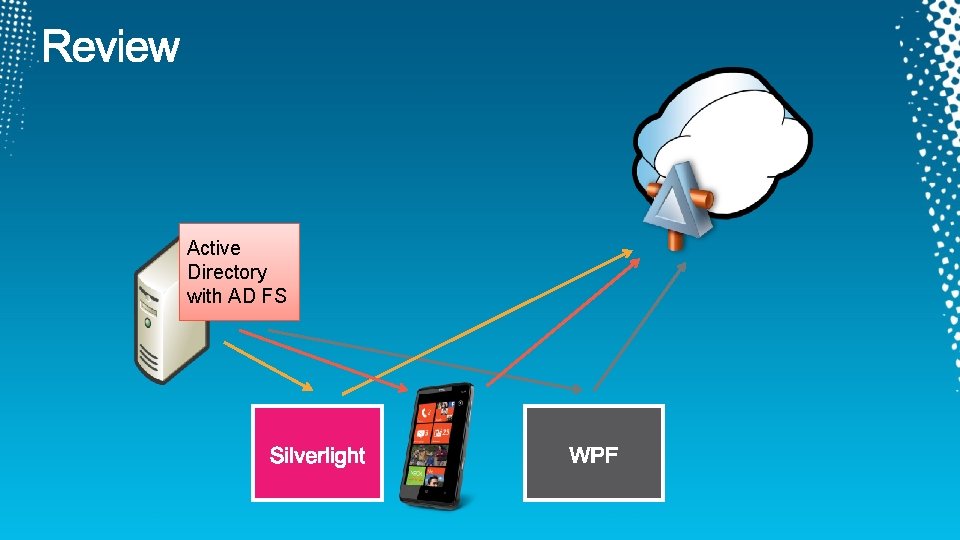
Active Directory with AD FS

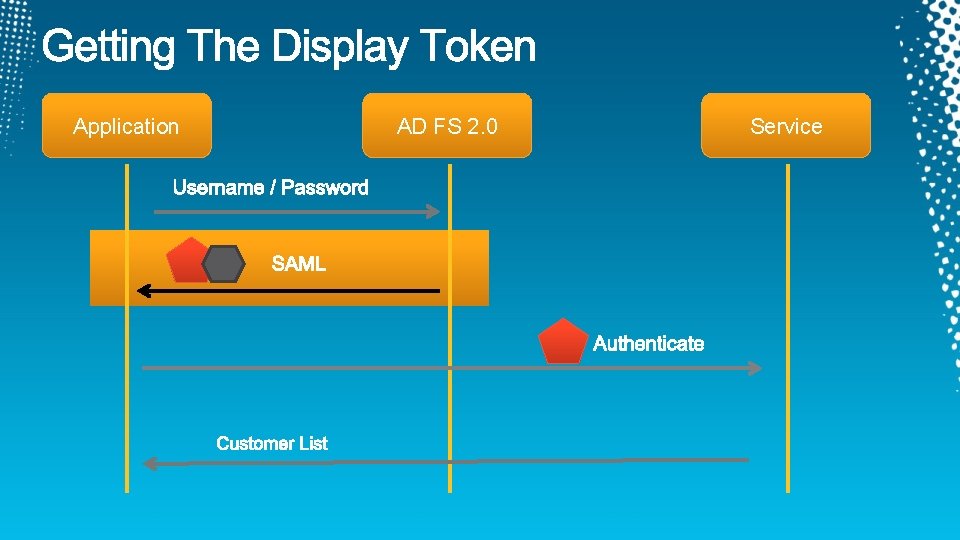
Application AD FS 2. 0 Service

demo

Active Directory with AD FS


demo
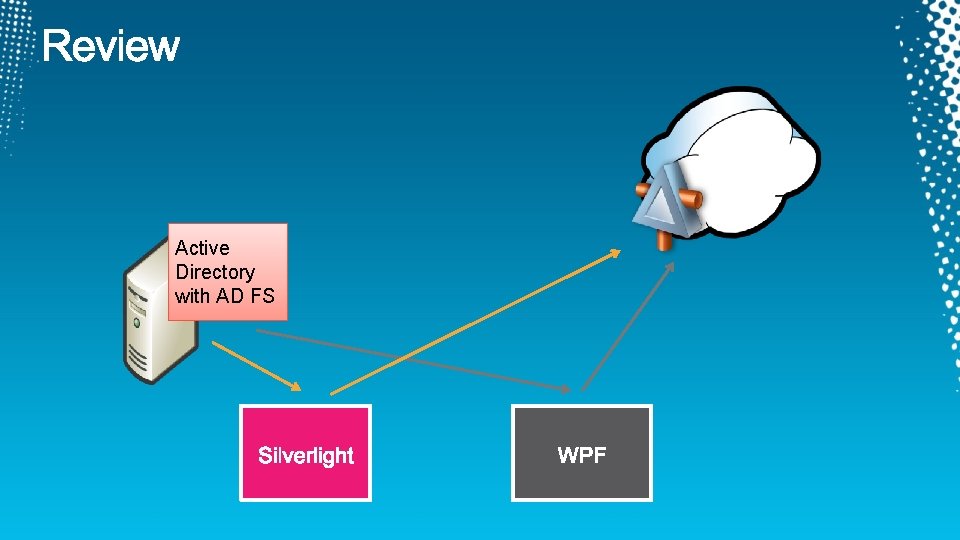
Active Directory with AD FS
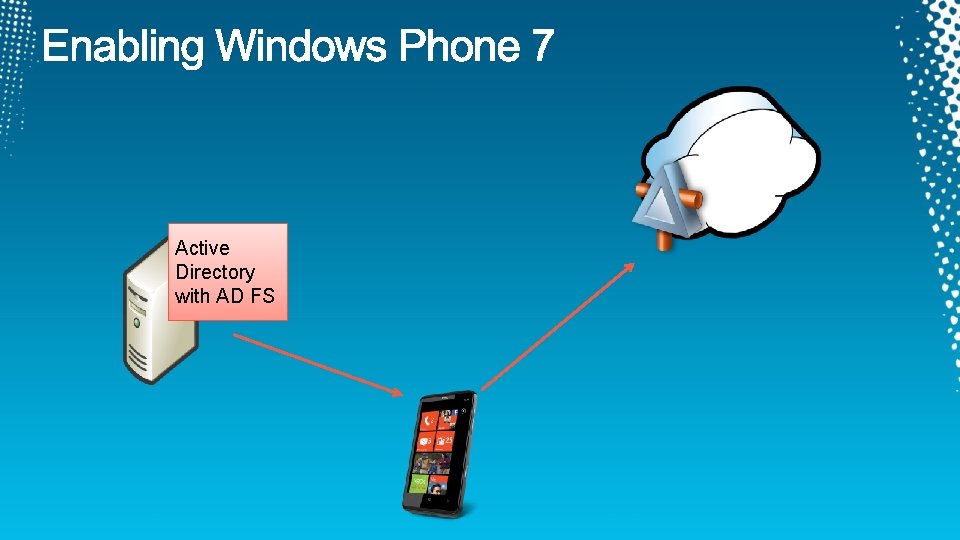
Active Directory with AD FS

demo
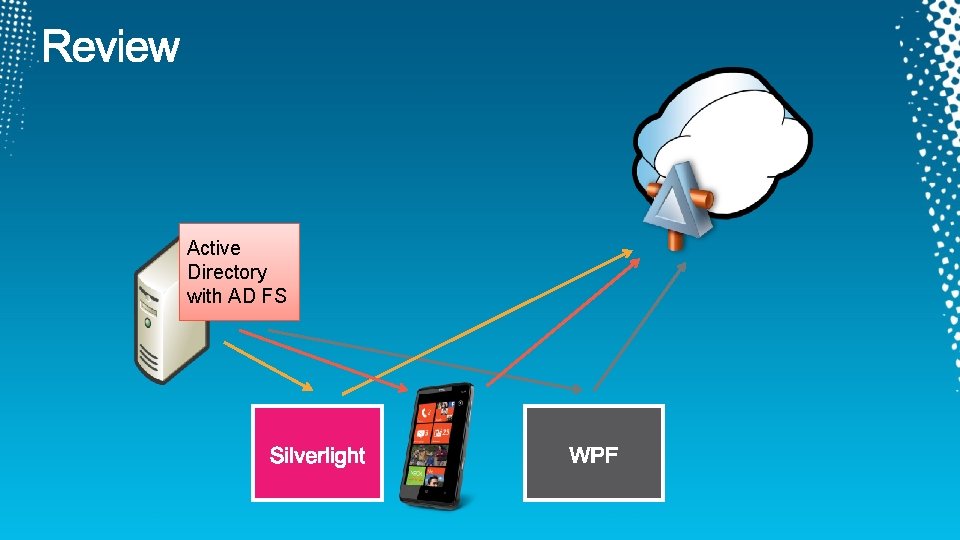
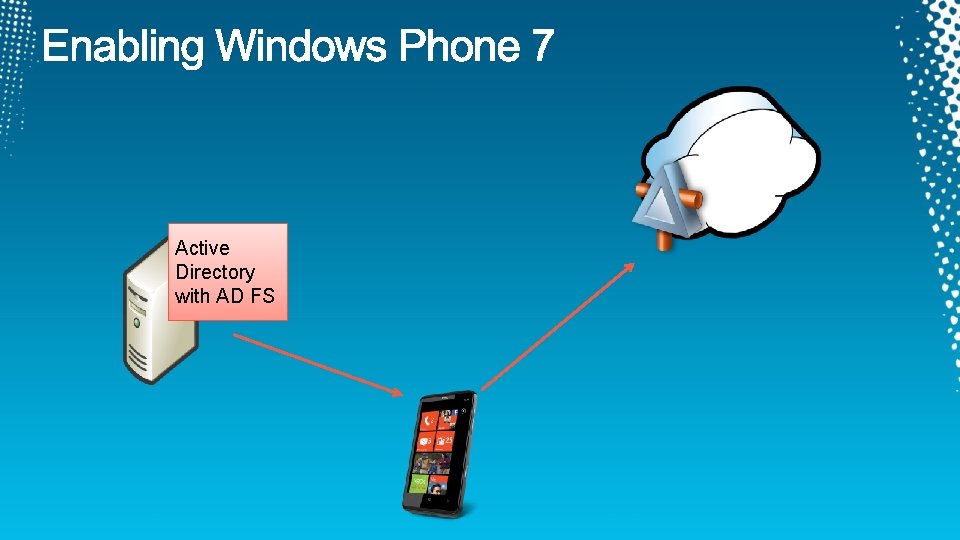
Active Directory with AD FS
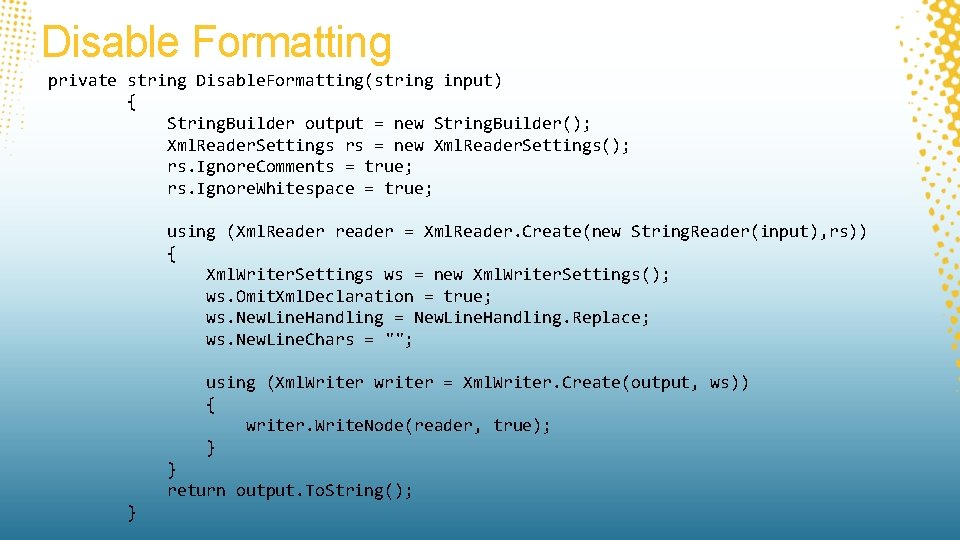
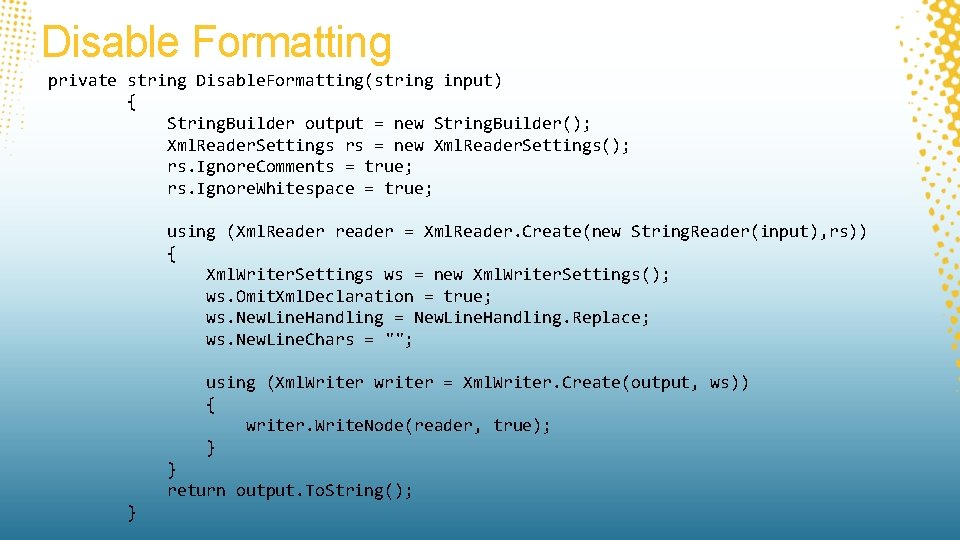
Disable Formatting private string Disable. Formatting(string input) { String. Builder output = new String. Builder(); Xml. Reader. Settings rs = new Xml. Reader. Settings(); rs. Ignore. Comments = true; rs. Ignore. Whitespace = true; using (Xml. Reader reader = Xml. Reader. Create(new String. Reader(input), rs)) { Xml. Writer. Settings ws = new Xml. Writer. Settings(); ws. Omit. Xml. Declaration = true; ws. New. Line. Handling = New. Line. Handling. Replace; ws. New. Line. Chars = ""; using (Xml. Writer writer = Xml. Writer. Create(output, ws)) { writer. Write. Node(reader, true); } } return output. To. String(); }
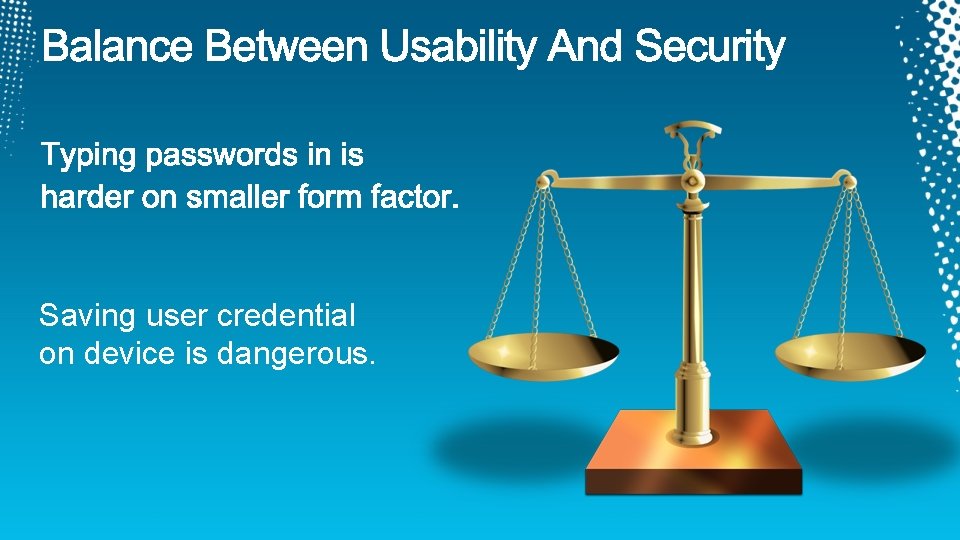
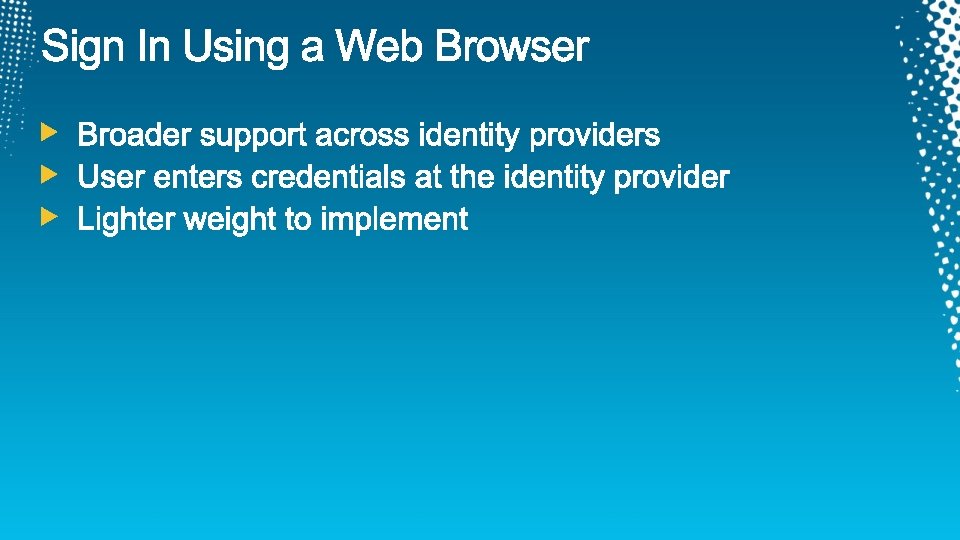
Saving user credential on device is dangerous.

Set AD FS token lifetime Set-ADFSRelying. Party. Trust -Target. Name "RP name" Token. Life. Time 600
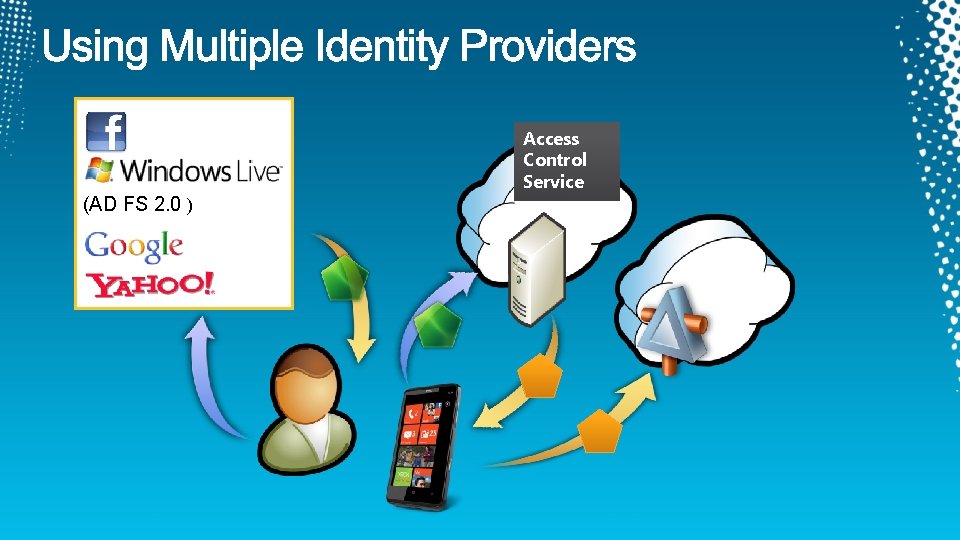
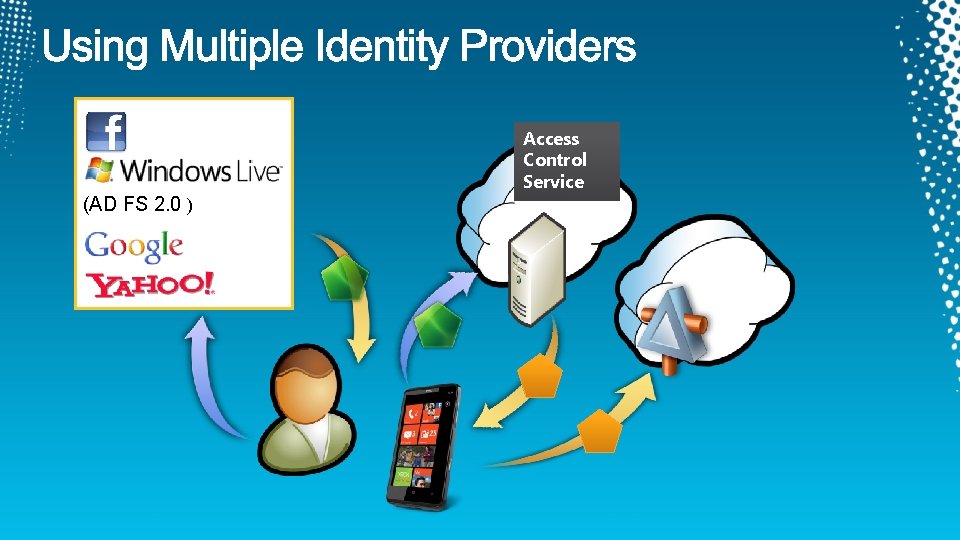
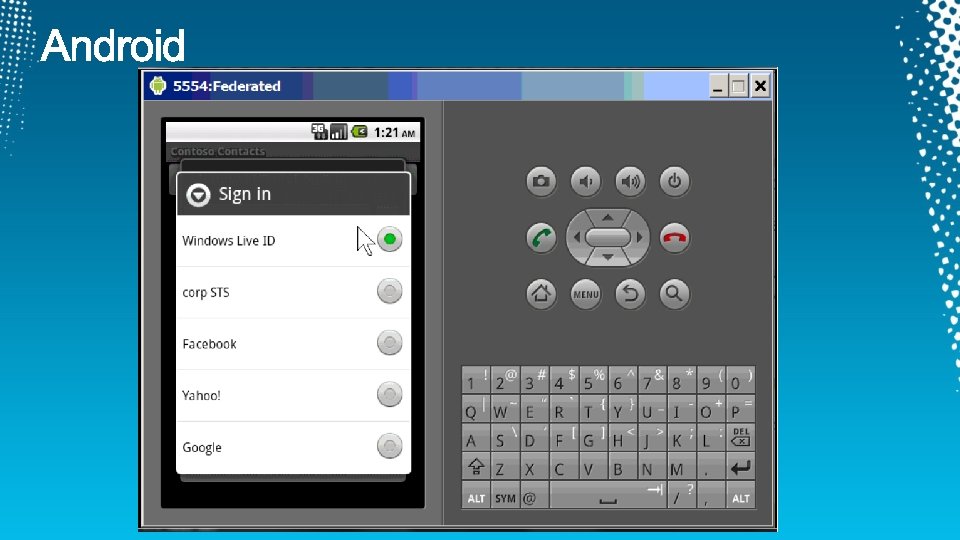
Access Control Service (AD FS 2. 0 )
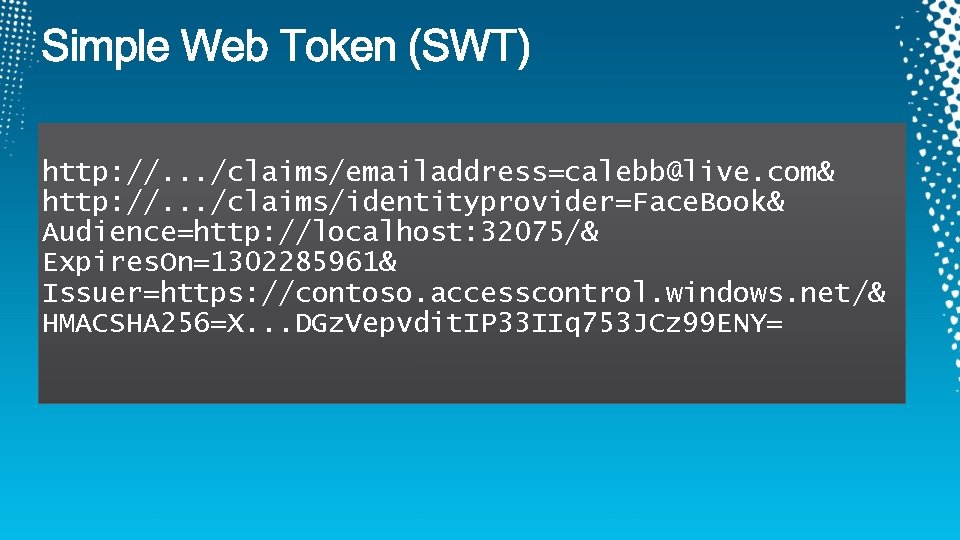
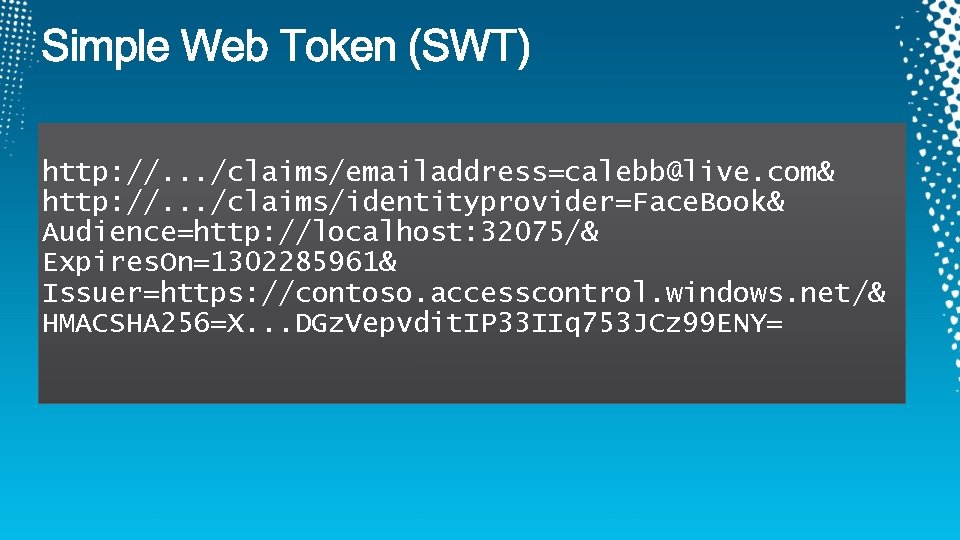
http: //. . . /claims/emailaddress=calebb@live. com& http: //. . . /claims/identityprovider=Face. Book& Audience=http: //localhost: 32075/& Expires. On=1302285961& Issuer=https: //contoso. accesscontrol. windows. net/& HMACSHA 256=X. . . DGz. Vepvdit. IP 33 IIq 753 JCz 99 ENY=
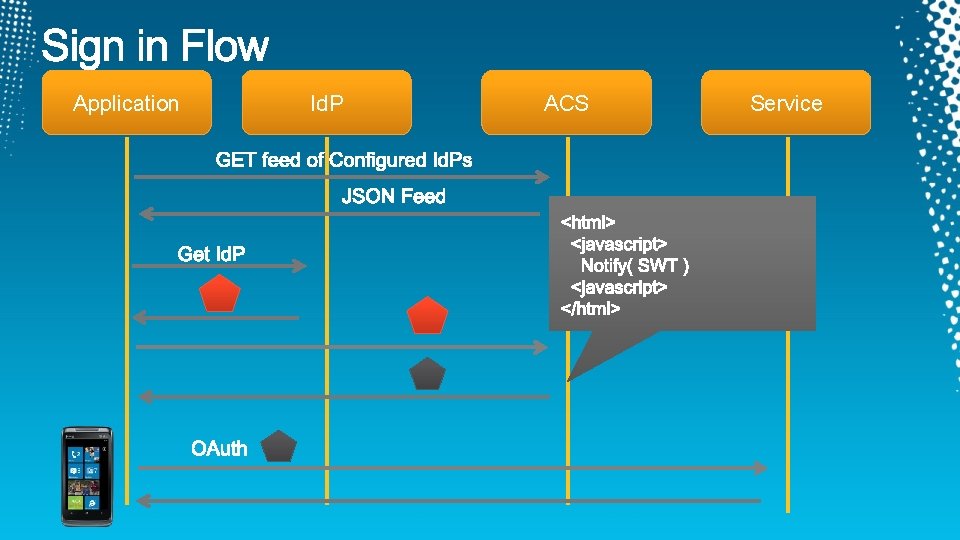
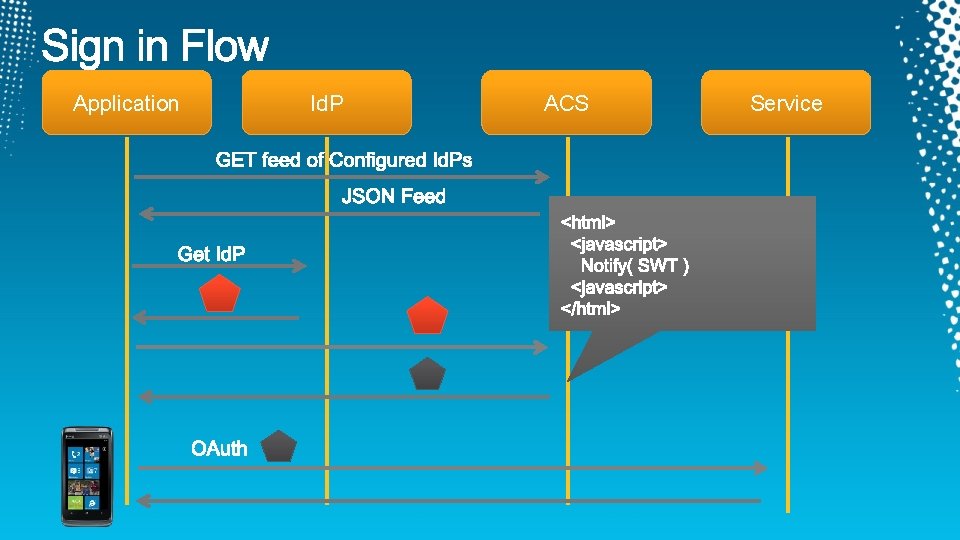
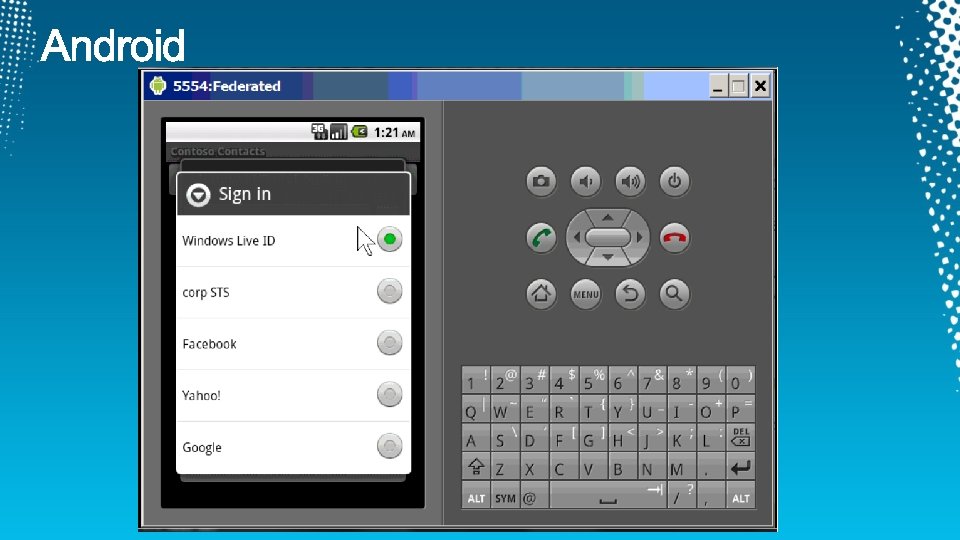
Application Id. P ACS Service
demo
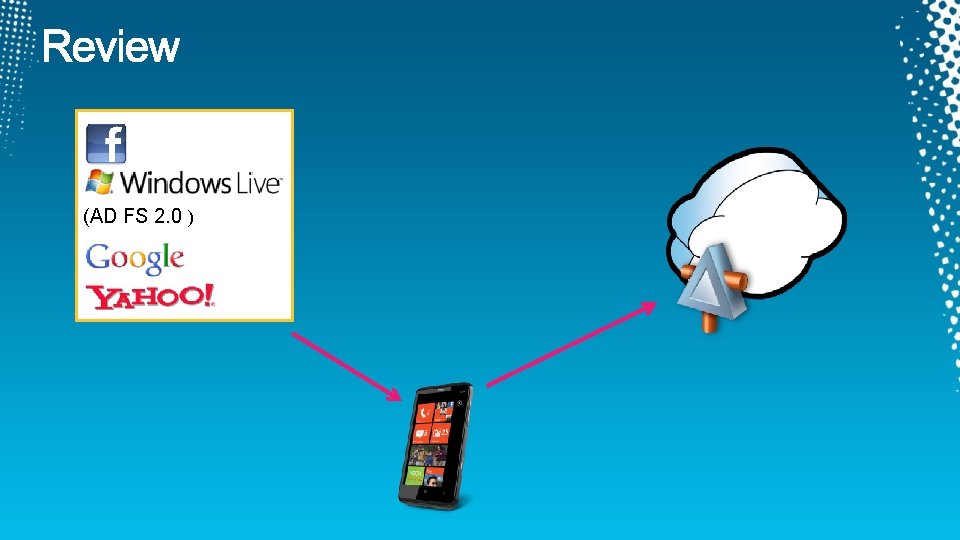
(AD FS 2. 0 )
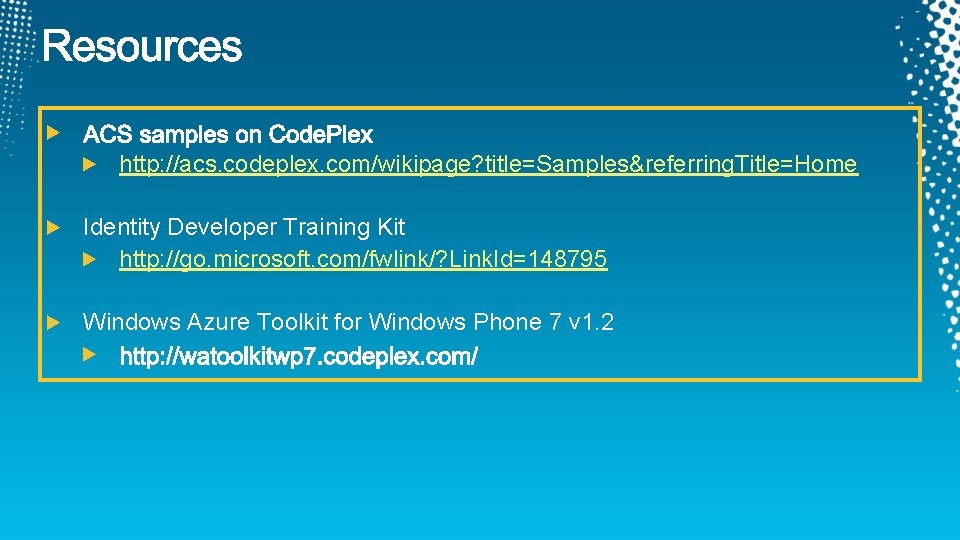
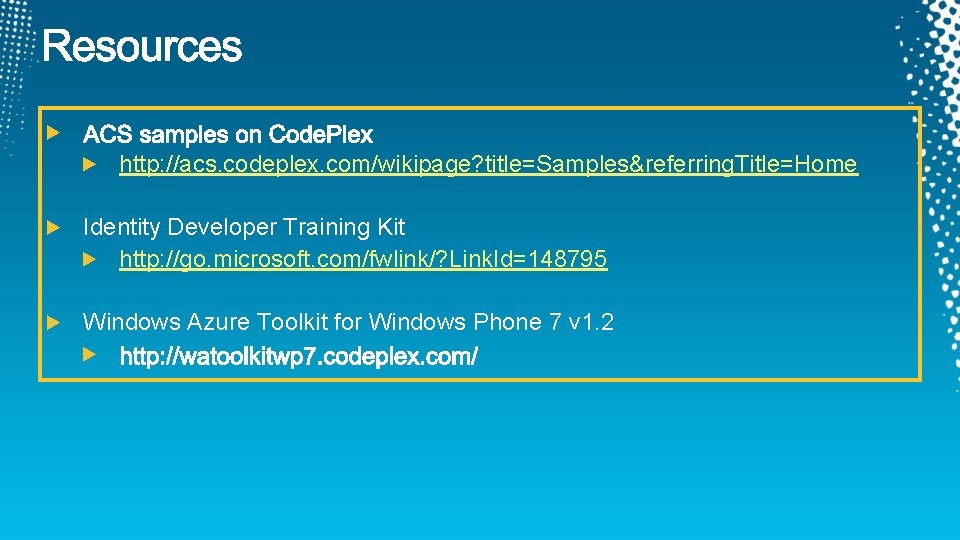
http: //acs. codeplex. com/wikipage? title=Samples&referring. Title=Home Identity Developer Training Kit http: //go. microsoft. com/fwlink/? Link. Id=148795 Windows Azure Toolkit for Windows Phone 7 v 1. 2
Blue Section http: //www. microsoft. com/cloud/ http: //www. microsoft. com/privatecloud/ http: //www. microsoft. com/windowsserver/ http: //www. microsoft. com/windowsazure/ http: //www. microsoft. com/systemcenter/ http: //www. microsoft. com/forefront/
Connect. Share. Discuss. http: //northamerica. msteched. com Sessions On-Demand & Community Microsoft Certification & Training Resources www. microsoft. com/teched www. microsoft. com/learning Resources for IT Professionals Resources for Developers http: //microsoft. com/technet http: //microsoft. com/msdn


Scan the Tag to evaluate this session now on my. Tech • Ed Mobile

