Signed Binary Representations Revisited Katsuyuki Okeya Hitachi Katja
Signed Binary Representations Revisited Katsuyuki Okeya, Hitachi Katja Schmidt-Samoa, Christian Spahn, Tsuyoshi Takagi, TU Darmstadt http: //www. informatik. tu-darmstadt. de/KP/ Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
Content • • • Motivation Non-Adjacent Form Proposed Scheme – MOF Application to ECC Conclusion Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
Efficiency is Important Smart Cards - tamper-resistant - mobility We need efficient cryptographic algorithms Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
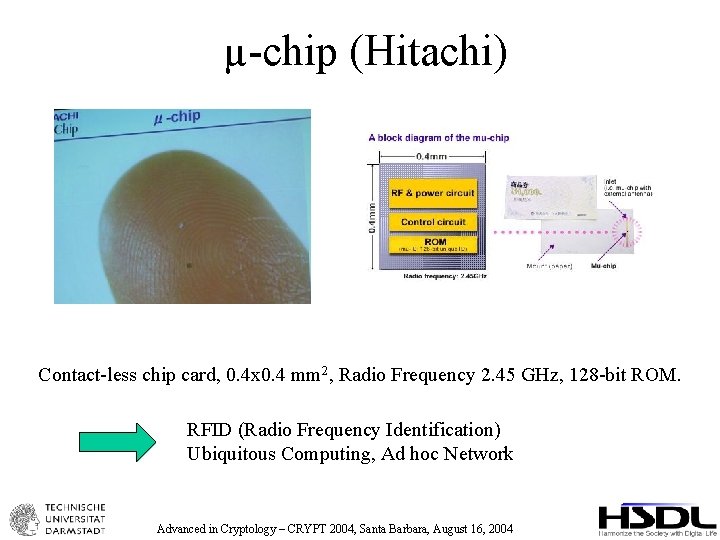
µ-chip (Hitachi) Contact-less chip card, 0. 4 x 0. 4 mm 2, Radio Frequency 2. 45 GHz, 128 -bit ROM. RFID (Radio Frequency Identification) Ubiquitous Computing, Ad hoc Network Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
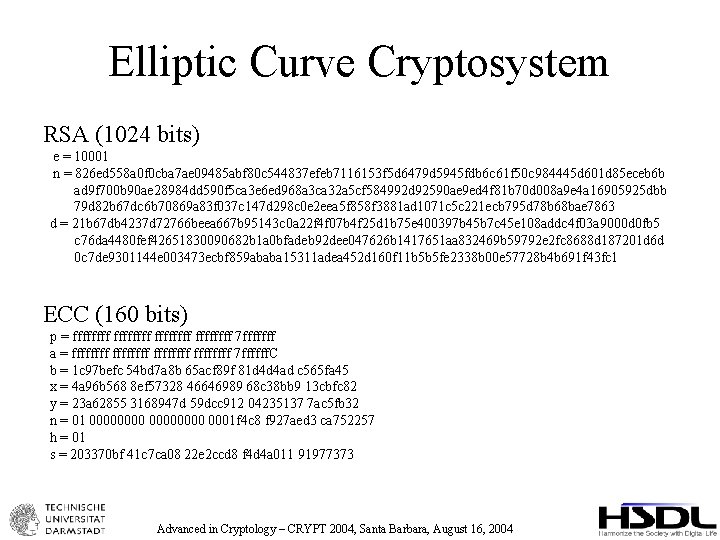
Elliptic Curve Cryptosystem RSA (1024 bits) e = 10001 n = 826 ed 558 a 0 f 0 cba 7 ae 09485 abf 80 c 544837 efeb 7116153 f 5 d 6479 d 5945 fdb 6 c 61 f 50 c 984445 d 601 d 85 eceb 6 b ad 9 f 700 b 90 ae 28984 dd 590 f 5 ca 3 e 6 ed 968 a 3 ca 32 a 5 cf 584992 d 92590 ae 9 ed 4 f 81 b 70 d 008 a 9 e 4 a 16905925 dbb 79 d 82 b 67 dc 6 b 70869 a 83 f 037 c 147 d 298 c 0 e 2 eea 5 f 858 f 3881 ad 1071 c 5 c 221 ecb 795 d 78 b 68 bae 7863 d = 21 b 67 db 4237 d 72766 beea 667 b 95143 c 0 a 22 f 4 f 07 b 4 f 25 d 1 b 75 e 400397 b 45 b 7 c 45 e 108 addc 4 f 03 a 9000 d 0 fb 5 c 76 da 4480 fef 42651830090682 b 1 a 0 bfadeb 92 dee 047626 b 1417651 aa 832469 b 59792 e 2 fc 8688 d 187201 d 6 d 0 c 7 de 9301144 e 003473 ecbf 859 ababa 15311 adea 452 d 160 f 11 b 5 b 5 fe 2338 b 00 e 57728 b 4 b 691 f 43 fc 1 ECC (160 bits) p = ffffffff 7 fffffff a = ffffffff 7 ffffff. C b = 1 c 97 befc 54 bd 7 a 8 b 65 acf 89 f 81 d 4 d 4 ad c 565 fa 45 x = 4 a 96 b 568 8 ef 57328 46646989 68 c 38 bb 9 13 cbfc 82 y = 23 a 62855 3168947 d 59 dcc 912 04235137 7 ac 5 fb 32 n = 01 00000000 0001 f 4 c 8 f 927 aed 3 ca 752257 h = 01 s = 203370 bf 41 c 7 ca 08 22 e 2 ccd 8 f 4 d 4 a 011 91977373 Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
![Standard Addition Formula (Weierstraß-form of an elliptic curve) [Standard Formula] ECADD ECDBL Advanced in Standard Addition Formula (Weierstraß-form of an elliptic curve) [Standard Formula] ECADD ECDBL Advanced in](http://slidetodoc.com/presentation_image/78a37d3b966dd62dbda1f966d67ef82b/image-6.jpg)
Standard Addition Formula (Weierstraß-form of an elliptic curve) [Standard Formula] ECADD ECDBL Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
![Scalar Multiplication d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20. times Square & Multiply Method Q=P for Scalar Multiplication d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20. times Square & Multiply Method Q=P for](http://slidetodoc.com/presentation_image/78a37d3b966dd62dbda1f966d67ef82b/image-7.jpg)
Scalar Multiplication d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20. times Square & Multiply Method Q=P for i=n-2 down to 0 Q = ECDBL(Q) if d[i] = 1, then Q = ECADD(Q, P) return(Q) Example d = 345 = 1 0 P D 2 P D 1 4 P A 5 P 0 10 P D D 1 20 P A 21 P 1 42 P D A 0 86 P D 43 P Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004 D 0 172 P D 1 344 P A 345 P
![Non-Adjacent Form (NAF) NAF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where d[i] in {-1, Non-Adjacent Form (NAF) NAF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where d[i] in {-1,](http://slidetodoc.com/presentation_image/78a37d3b966dd62dbda1f966d67ef82b/image-8.jpg)
Non-Adjacent Form (NAF) NAF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where d[i] in {-1, 0, 1} and d[i]*d[i-1]=0 for i=1, 2, . . , n-1. 345 = 1 0 -1 1 0 0 -1 Scalar Multiplication using NAF Q=P for i=n-2 down to 0 Q = ECDBL(Q) if d[i] = 1, then Q = ECADD(Q, P) if d[i] = -1, then Q = ECADD(Q, -P) return(Q[0]) 1 0 1 -1 0 0 1 (Binary representation) 1 (NAF representation) -P = (x, -y) for P = (x, y), virtually for free The average density of non-zero bits of NAF is asymptotically 1/3. NAF can achieve faster scalar multiplication. Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
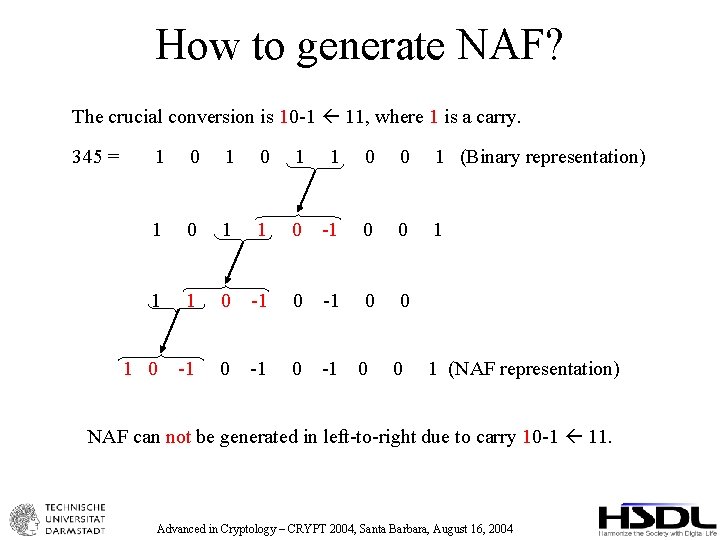
How to generate NAF? The crucial conversion is 10 -1 11, where 1 is a carry. 345 = 1 0 1 1 0 0 1 (Binary representation) 1 0 1 1 0 -1 0 0 1 0 -1 0 0 1 (NAF representation) NAF can not be generated in left-to-right due to carry 10 -1 11. Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
![Left-to-right is more efficient Left-to-right method Right-to-left method Q[0] = P Q[0] = O, Left-to-right is more efficient Left-to-right method Right-to-left method Q[0] = P Q[0] = O,](http://slidetodoc.com/presentation_image/78a37d3b966dd62dbda1f966d67ef82b/image-10.jpg)
Left-to-right is more efficient Left-to-right method Right-to-left method Q[0] = P Q[0] = O, Q[1] = P for i=n-2 down to 0 Q[0] = ECDBL(Q[0]) Q[0] = ECADD(Q[0], d[i]P) return(Q[0]) for i=0 down to n-1 Q[0] = ECADD(Q[0], d[i]Q[1]) Q[1] = ECDBL(Q[1]) return(Q[0]) P is represented by P = (X: Y: 1), which is fixed during the scalar multiplication. ECADD with Z=1 requires only 11 multiplications Q[1] is NOT represented by Q[1] = (X: Y: 1). ECADD with Z≠ 1 requires 16 multiplications Is there any efficient left-to-right exponent recording? Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
Related Works • Joye, Yen: IEEE Trans. , 2000. • Joye, Tymen: PKC 2001. Very recently, • Muir, Stinson: TR of CACR, 2004. • Avanzi: SAC 2004. • Heuberger, Katti, Prodinger, Ruan: Preprint. Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
![Mutual Opposite Form (MOF) MOF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where (1) d[i] Mutual Opposite Form (MOF) MOF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where (1) d[i]](http://slidetodoc.com/presentation_image/78a37d3b966dd62dbda1f966d67ef82b/image-12.jpg)
Mutual Opposite Form (MOF) MOF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where (1) d[i] in {-1, 0, 1} (2) The signs of adjacent non-zero bits (ignoring 0 bits) are opposite (3) The most and least non-zero bits are 1 and -1, respectively. 345 = 1 1 -1 0 1 -1 0 0 0 1 (Binary representation) 1 -1 (MOF representation) We can prove the following facts: - Every n-bit integer is uniquely represented by (n+1)-bit MOF. - The average density of non-zero bits is asymptotically 1/2. Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
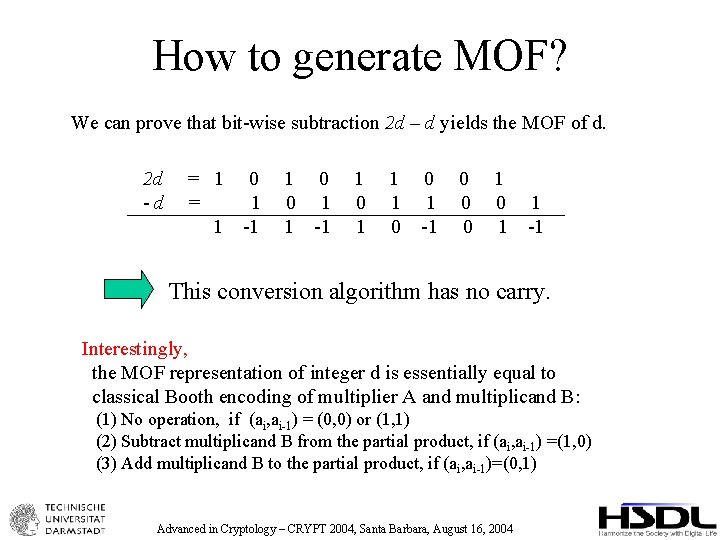
How to generate MOF? We can prove that bit-wise subtraction 2 d – d yields the MOF of d. 2 d -d = 1 0 = 1 1 -1 1 0 0 1 1 -1 1 0 1 1 1 0 0 1 -1 0 0 0 1 1 -1 This conversion algorithm has no carry. Interestingly, the MOF representation of integer d is essentially equal to classical Booth encoding of multiplier A and multiplicand B: (1) No operation, if (ai, ai-1) = (0, 0) or (1, 1) (2) Subtract multiplicand B from the partial product, if (ai, ai-1) =(1, 0) (3) Add multiplicand B to the partial product, if (ai, ai-1)=(0, 1) Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
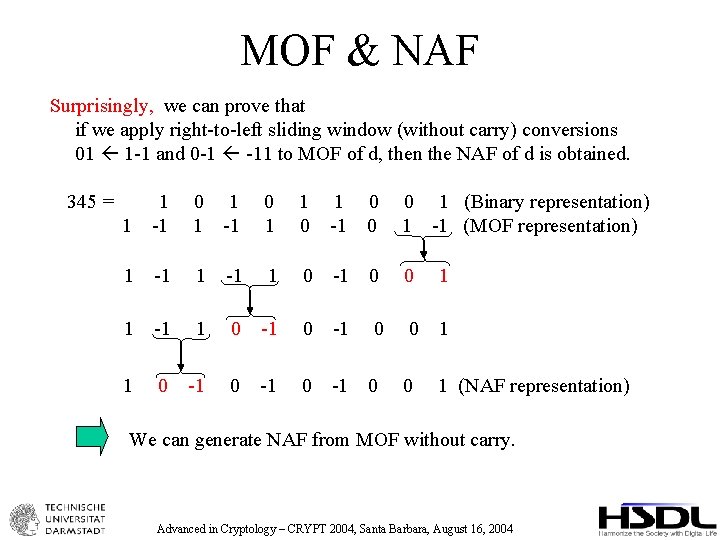
MOF & NAF Surprisingly, we can prove that if we apply right-to-left sliding window (without carry) conversions 01 1 -1 and 0 -1 -11 to MOF of d, then the NAF of d is obtained. 345 = 1 1 -1 0 1 -1 0 0 0 1 (Binary representation) 1 -1 (MOF representation) 1 -1 1 0 -1 0 0 1 1 0 -1 0 0 1 (NAF representation) We can generate NAF from MOF without carry. Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
Left-to-right conversion to MOF How about applying the sliding window conversions 1 -1 01, -11 0 -1? 345 = 1 1 -1 0 1 -1 0 0 0 1 (Binary representation) 1 -1 (MOF representation) 0 1 1 -1 1 0 -1 0 1 0 1 1 0 -1 0 0 -1 1 (New Chain: 2 MOF) Happily, we can prove that the average non-zero density of this new chain is asymptotically 1/3. Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
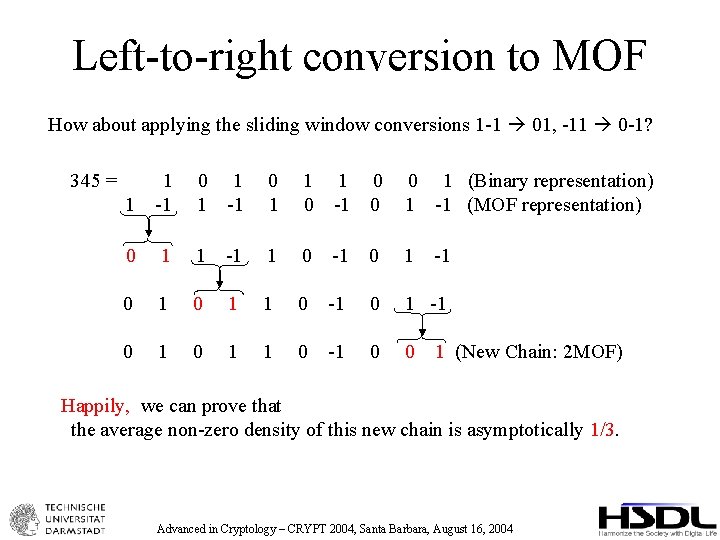
Application to ECC Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
![w. NAF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where (1) d[i] in {0, ± w. NAF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where (1) d[i] in {0, ±](http://slidetodoc.com/presentation_image/78a37d3b966dd62dbda1f966d67ef82b/image-17.jpg)
w. NAF is d = d[n-1]2 n-1+d[n-2]2 n-2+…+d[1]21+d[0]20, where (1) d[i] in {0, ± 1, ± 3, …, ±(2 w-1 -1)} (2) Among any w consecutive digits, at most one is non-zero. (3) The most significant non-zero bit is positive. 345 = 1 1 0 0 1 0 -3 0 0 1 (Binary representation) 1 (3 NAF representation) We can prove the following facts: - Every integer is uniquely represented by w. NAF. - The average non-zero density is asymptotically 1/(w+1). Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
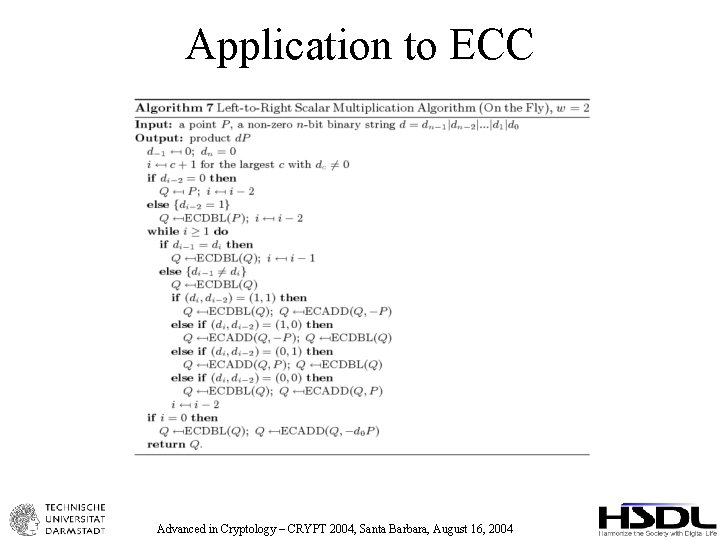
How to generate w. NAF We can extend NAF to its width-w version, called w. NAF. For example, crucial conversion for w=3 is 100 -1 111, 100 -3 101, and 003 011 345 = 1 0 1 1 0 0 1 (Binary representation) 1 0 1 1 0 0 3 0 0 1 0 0 -3 0 0 1 (3 NAF representation) w. NAF can not be generated in left-to-right due to carry. Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
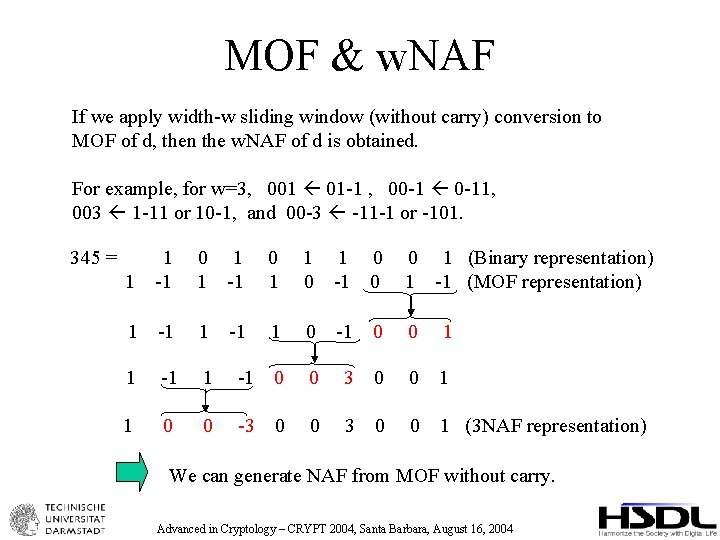
MOF & w. NAF If we apply width-w sliding window (without carry) conversion to MOF of d, then the w. NAF of d is obtained. For example, for w=3, 001 01 -1 , 00 -1 0 -11, 003 1 -11 or 10 -1, and 00 -3 -11 -1 or -101. 345 = 1 1 -1 0 1 -1 0 0 0 1 (Binary representation) 1 -1 (MOF representation) 1 -1 1 1 0 -1 0 0 1 1 -1 0 0 3 0 0 1 1 0 0 -3 0 0 1 (3 NAF representation) -1 We can generate NAF from MOF without carry. Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
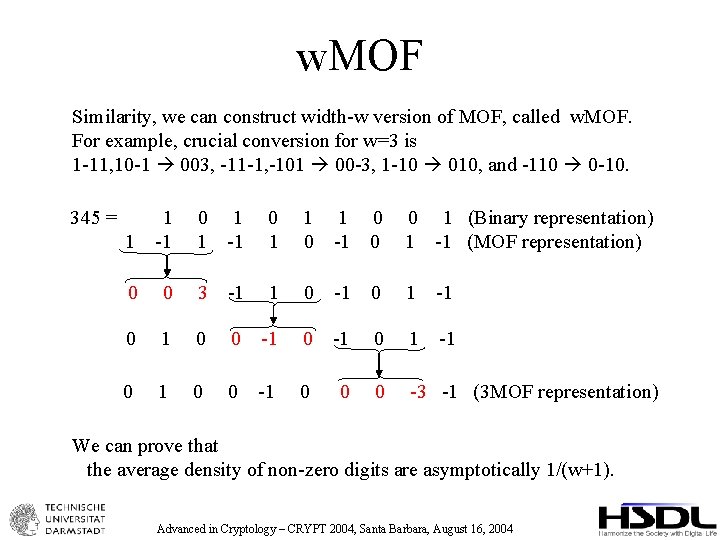
w. MOF Similarity, we can construct width-w version of MOF, called w. MOF. For example, crucial conversion for w=3 is 1 -11, 10 -1 003, -11 -1, -101 00 -3, 1 -10 010, and -110 0 -10. 345 = 1 1 -1 0 1 -1 0 0 0 1 (Binary representation) 1 -1 (MOF representation) 0 0 3 -1 1 0 -1 0 1 0 0 -1 0 0 0 -3 -1 (3 MOF representation) We can prove that the average density of non-zero digits are asymptotically 1/(w+1). Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
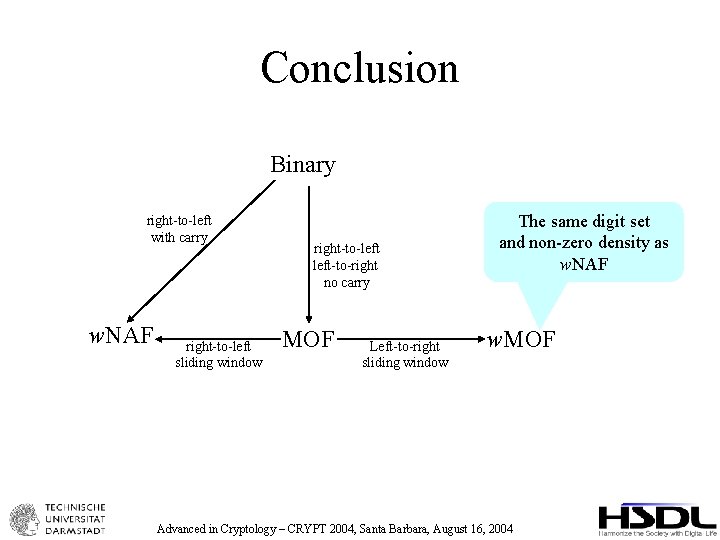
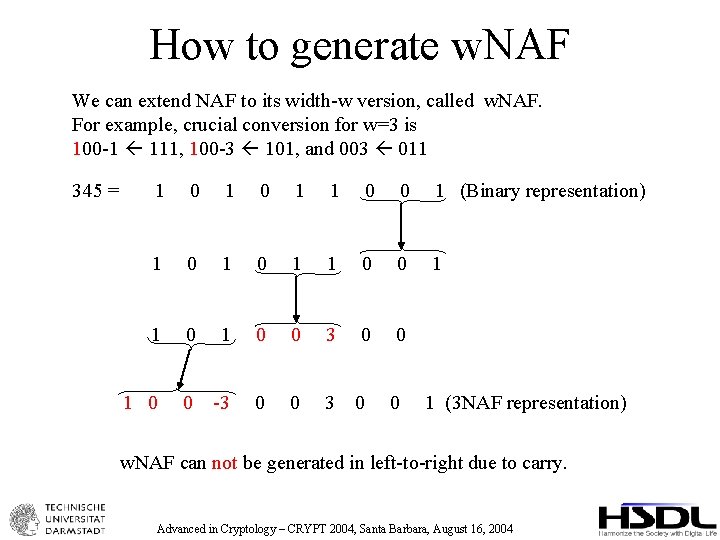
Conclusion Binary right-to-left with carry w. NAF right-to-left sliding window right-to-left-to-right no carry MOF Left-to-right sliding window The same digit set and non-zero density as w. NAF w. MOF Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
Thank you! The full version is available from IACR e. Print. http: //eprint. iacr. org/2004/195/ The home of MOF is the following URL. http: //www. informatik. tu-darmstadt. de/KP/MOF/ Advanced in Cryptology – CRYPT 2004, Santa Barbara, August 16, 2004
- Slides: 22