Signatures Homomorphic Daniel Wichs Northeastern University based on
Signatures Homomorphic Daniel Wichs Northeastern University based on work with: Sergey Gorbunov and Vinod Vaikuntanathan
![Fully Homomorphic Encryption (FHE) [Rivest-Adleman-Dertouzos ’ 78, Gentry ’ 09, …] Alice Fully Homomorphic Encryption (FHE) [Rivest-Adleman-Dertouzos ’ 78, Gentry ’ 09, …] Alice](http://slidetodoc.com/presentation_image_h/14a7735ad1d60cb25d4e3c003ba3cf4b/image-2.jpg)
Fully Homomorphic Encryption (FHE) [Rivest-Adleman-Dertouzos ’ 78, Gentry ’ 09, …] Alice
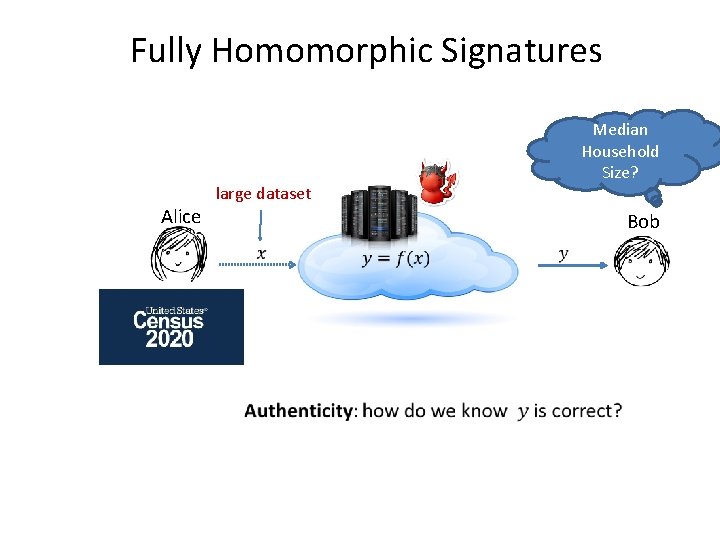
Fully Homomorphic Signatures Alice Median Household Size? large dataset Bob
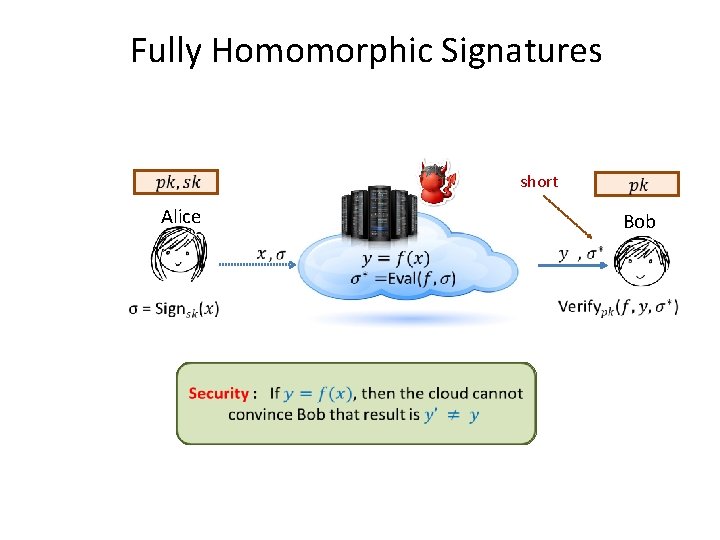
Fully Homomorphic Signatures short Alice Bob
![Theorem [Gorbunov, Vaikuntanathan, Wichs’ 15]: A leveled fully homomorphic signature (HS) scheme for all Theorem [Gorbunov, Vaikuntanathan, Wichs’ 15]: A leveled fully homomorphic signature (HS) scheme for all](http://slidetodoc.com/presentation_image_h/14a7735ad1d60cb25d4e3c003ba3cf4b/image-5.jpg)
Theorem [Gorbunov, Vaikuntanathan, Wichs’ 15]: A leveled fully homomorphic signature (HS) scheme for all circuits of some a-priori bounded depth d. Shortness: Size of certificate σf, y is poly(λ, d) where λ is the security parameter and d is the circuit depth for f. Security: assuming hardness of LWE/SIS. Caveat: Need large public random string (public params) or random oracle model.
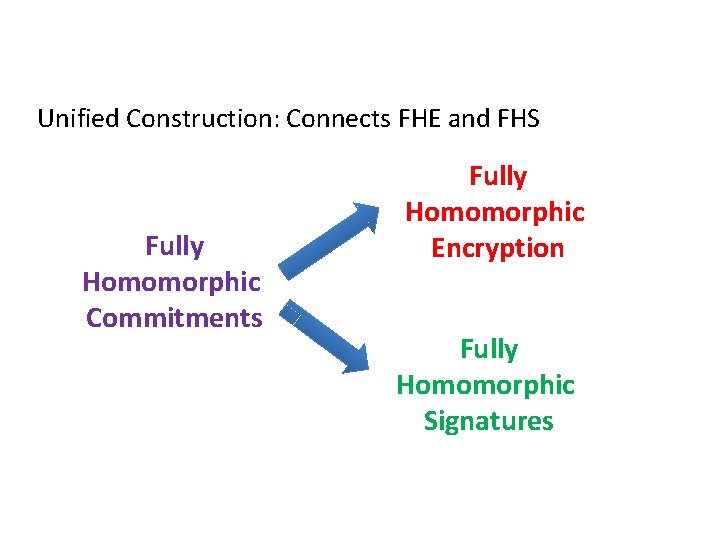
Unified Construction: Connects FHE and FHS Fully Homomorphic Commitments Fully Homomorphic Encryption Fully Homomorphic Signatures
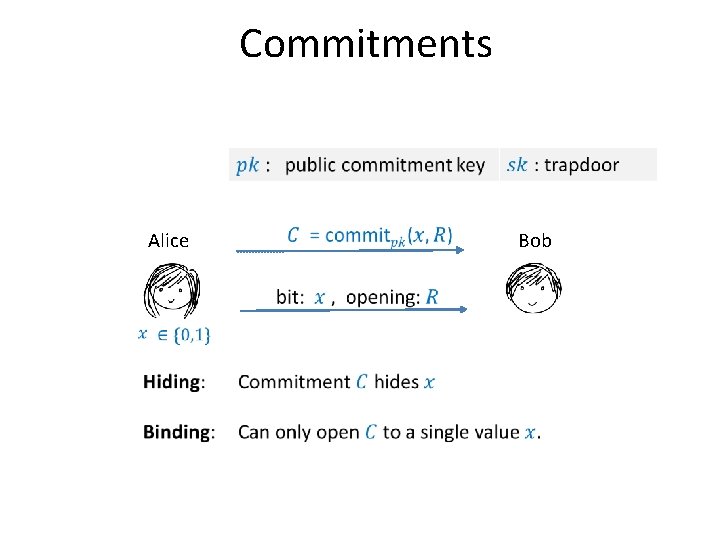
Commitments Alice Bob
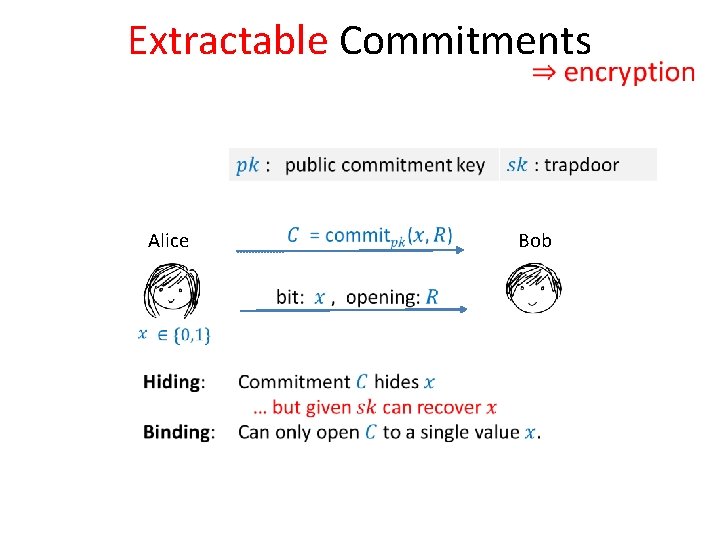
Extractable Commitments Alice Bob
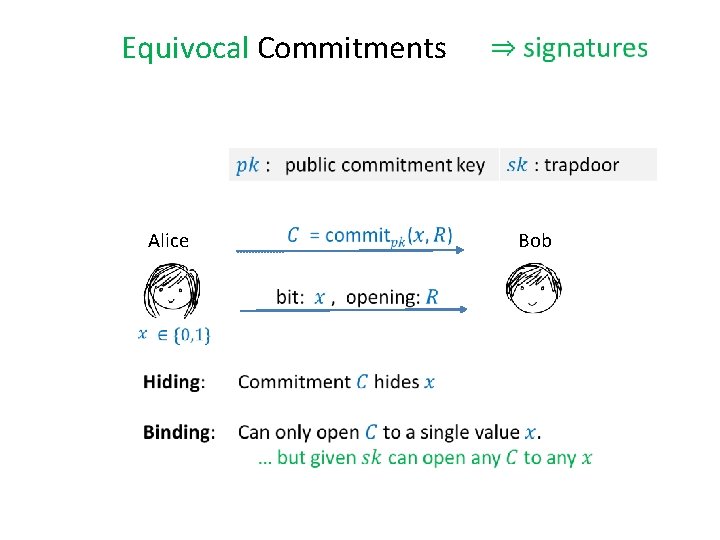
Equivocal Commitments Alice Bob
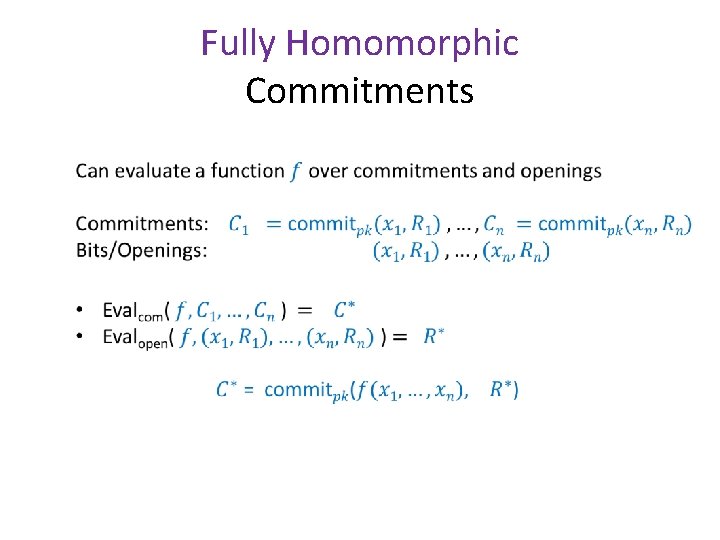
Fully Homomorphic Commitments •
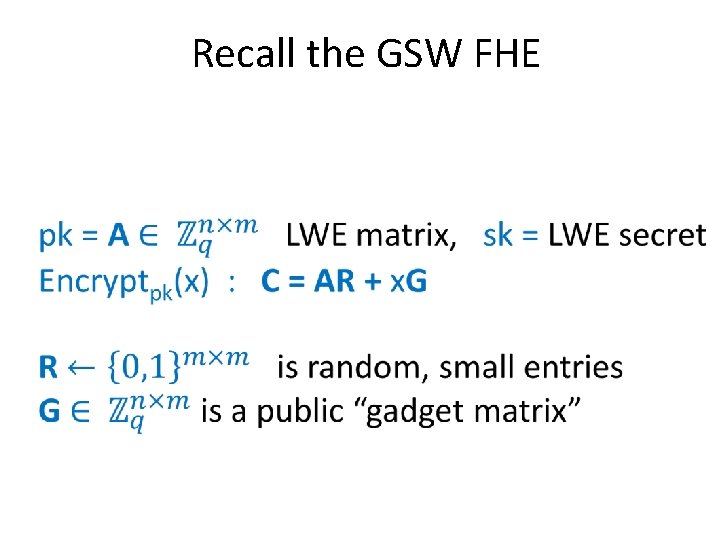
Recall the GSW FHE
GSW as a Commitment
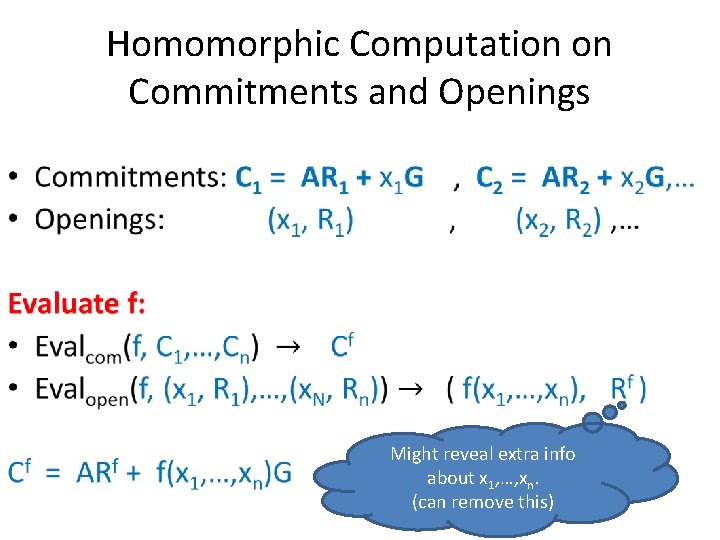
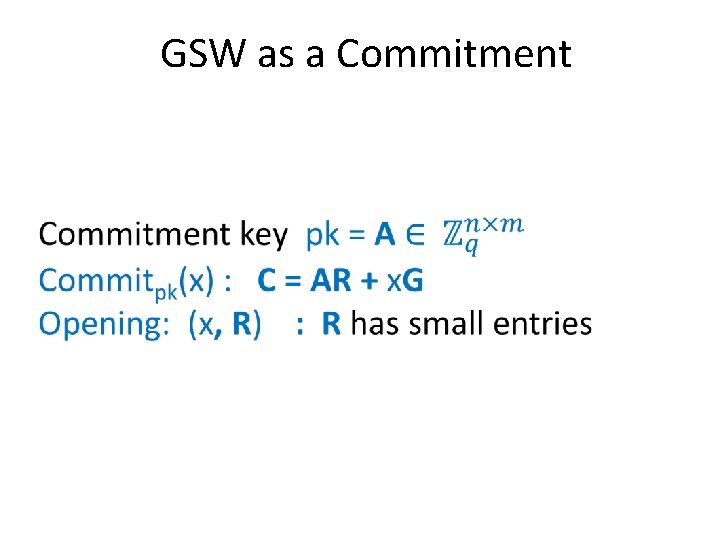
Homomorphic Computation on Commitments and Openings • Might reveal extra info about x 1, …, xn. (can remove this)
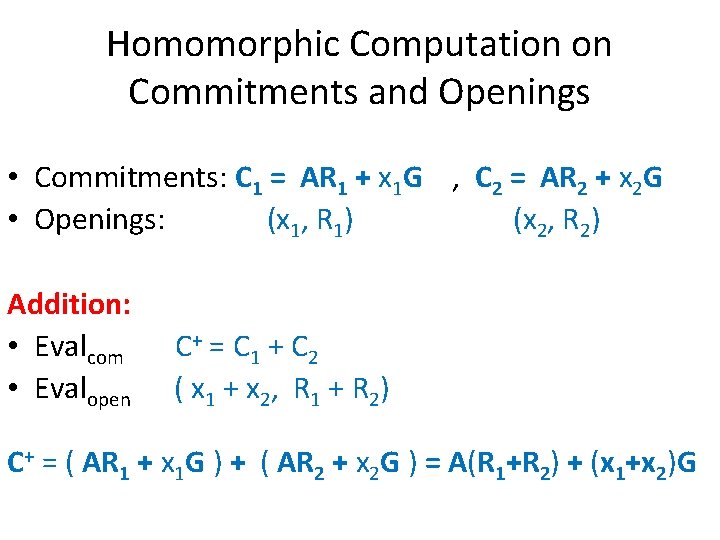
Homomorphic Computation on Commitments and Openings • Commitments: C 1 = AR 1 + x 1 G , C 2 = AR 2 + x 2 G • Openings: (x 1, R 1) (x 2, R 2) Addition: • Evalcom C+ = C 1 + C 2 • Evalopen ( x 1 + x 2, R 1 + R 2) C+ = ( AR 1 + x 1 G ) + ( AR 2 + x 2 G ) = A(R 1+R 2) + (x 1+x 2)G
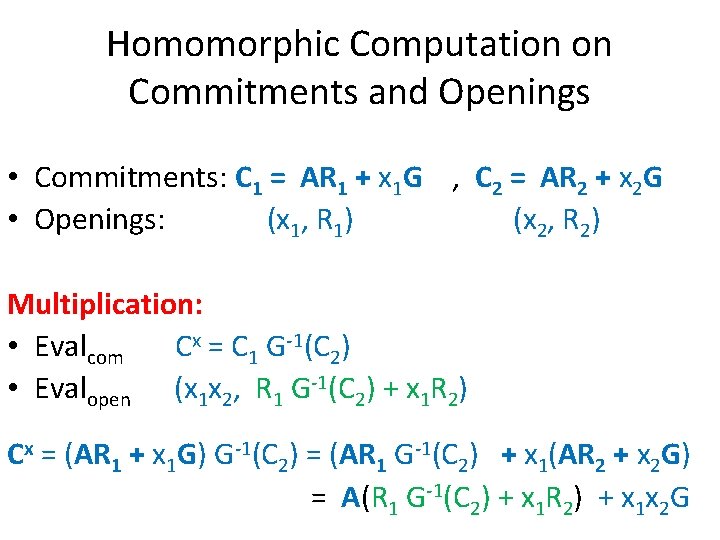
Homomorphic Computation on Commitments and Openings • Commitments: C 1 = AR 1 + x 1 G , C 2 = AR 2 + x 2 G • Openings: (x 1, R 1) (x 2, R 2) Multiplication: • Evalcom Cx = C 1 G-1(C 2) • Evalopen (x 1 x 2, R 1 G-1(C 2) + x 1 R 2) Cx = (AR 1 + x 1 G) G-1(C 2) = (AR 1 G-1(C 2) + x 1(AR 2 + x 2 G) = A(R 1 G-1(C 2) + x 1 R 2) + x 1 x 2 G
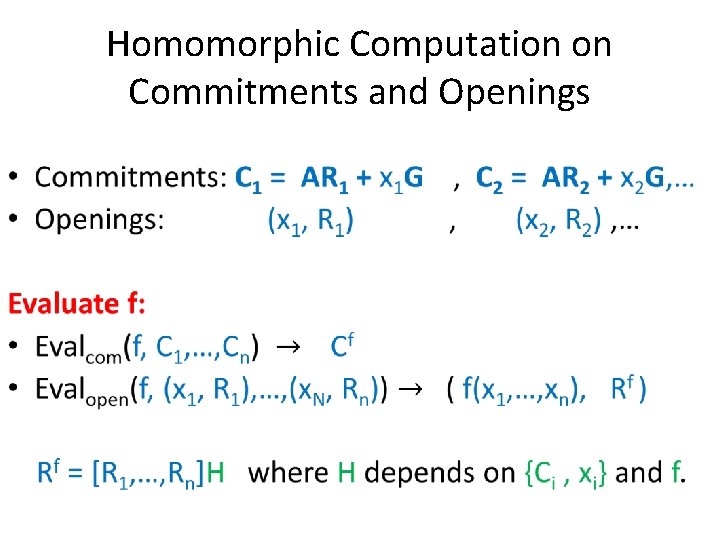
Homomorphic Computation on Commitments and Openings •
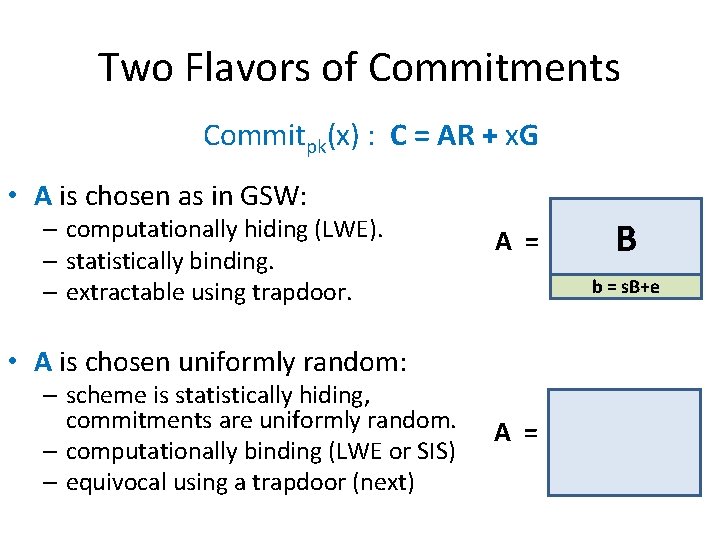
Two Flavors of Commitments Commitpk(x) : C = AR + x. G • A is chosen as in GSW: – computationally hiding (LWE). – statistically binding. – extractable using trapdoor. A = b = s. B+e • A is chosen uniformly random: – scheme is statistically hiding, commitments are uniformly random. – computationally binding (LWE or SIS) – equivocal using a trapdoor (next) B A =
![SIS Trapdoor [Ajtai 99, …, MP 12] • Goal: choose a random A with SIS Trapdoor [Ajtai 99, …, MP 12] • Goal: choose a random A with](http://slidetodoc.com/presentation_image_h/14a7735ad1d60cb25d4e3c003ba3cf4b/image-18.jpg)
SIS Trapdoor [Ajtai 99, …, MP 12] • Goal: choose a random A with a trapdoor such that for any V can find short R : AR = V. To open commitment C to a bit x, set V R = TG-1(V) = C – x. G. m/2 A = B m/2 BR* + G n Trapdoor: T = AT = G -R* I
![SIS Trapdoor with Correct Distribution [GPV 08, MP 12, LW 15] • SIS Trapdoor with Correct Distribution [GPV 08, MP 12, LW 15] •](http://slidetodoc.com/presentation_image_h/14a7735ad1d60cb25d4e3c003ba3cf4b/image-19.jpg)
SIS Trapdoor with Correct Distribution [GPV 08, MP 12, LW 15] •
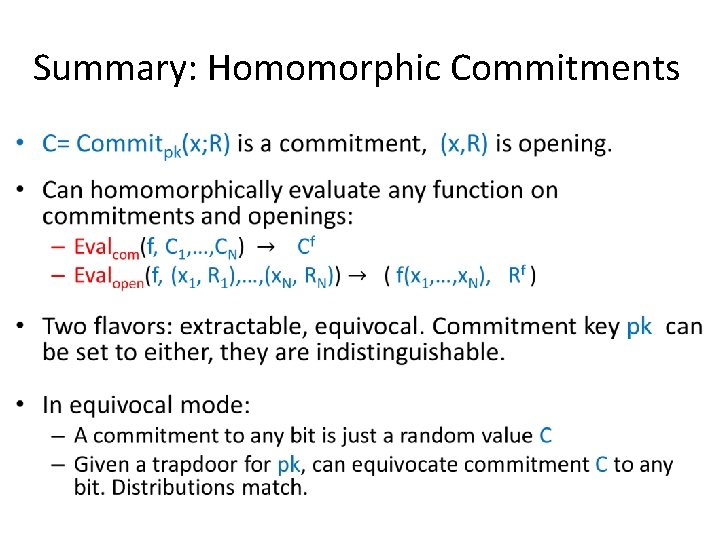
Summary: Homomorphic Commitments •
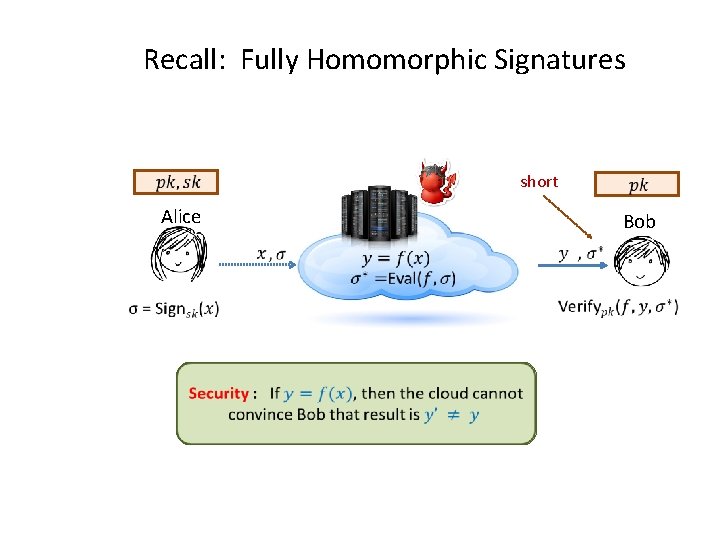
Recall: Fully Homomorphic Signatures short Alice Bob
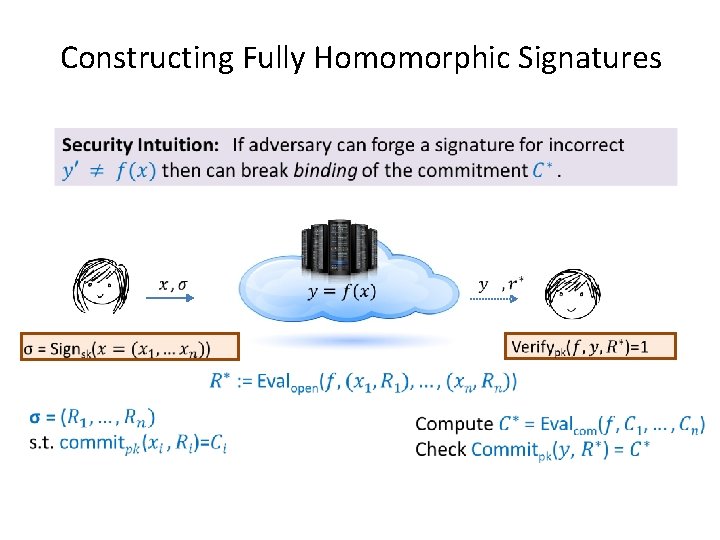
Constructing Fully Homomorphic Signatures Public randomness: random commitments $$$$$$$$$$$$$$$$$$$$$
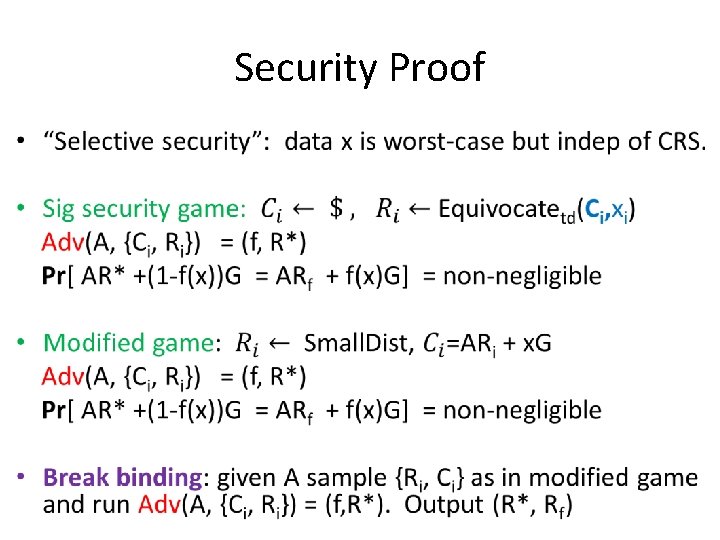
Security Proof •
![Extensions • Full security (beyond selective): – Homomorphic chameleon hash [KR 00] = Homomorphic Extensions • Full security (beyond selective): – Homomorphic chameleon hash [KR 00] = Homomorphic](http://slidetodoc.com/presentation_image_h/14a7735ad1d60cb25d4e3c003ba3cf4b/image-24.jpg)
Extensions • Full security (beyond selective): – Homomorphic chameleon hash [KR 00] = Homomorphic equivocal commitments. • Multiple data sets: – Use standard signature to sign a fresh verification key of homomorphic signature scheme for each data set. • Context Hiding (certificate only reveals output of comp. ) – Can be done generically with NIZKs. – Nice way to do this for our scheme using equivocation trapdoors.
Open Problems • Remove large public parameters? • Remove dependence on depth. Bootstrapping?

- Slides: 26