SIA Secure Information Aggregation in Sensor Networks B
SIA: Secure Information Aggregation in Sensor Networks B. Przydatek, D. Song, and A. Perrig. In Proc. of ACM Sen. Sys 2003 Natalia Stakhanova cs 610
Sensor networks ¡ wireless network consisting of large number of small sensor devices Main objective: data collection ¡ Sensors are severely constrained: l Low memory Low power l Limited bandwidth l ¡ Transfer of raw information is expensive l (often individual readings are not needed) Solution: aggregate data and transfer the result only!
Data aggregation ¡ Selected nodes are aggregators l ¡ responsible for ¡ data collection ¡ computation of aggregated result ¡ result transfer to the user (home server) Security concern: l l compromised aggregator compromised sensors
Proposed approach ¡ Previous works assumed honest sensors ¡ This work’s focus: l stealthy attacks If user accepts the aggregation result, then there isa high probability that the reported result is “close” to the true result value
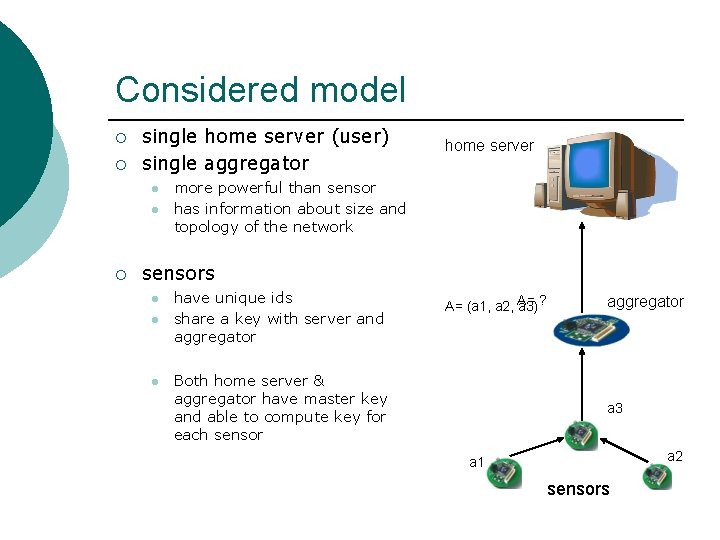
Considered model ¡ ¡ single home server (user) single aggregator l l ¡ home server more powerful than sensor has information about size and topology of the network sensors l l l have unique ids share a key with server and aggregator A= (a 1, a 2, A= a 3) ? Both home server & aggregator have master key and able to compute key for each sensor aggregator a 3 a 2 a 1 sensors
Aggregate-Commit-Prove approach ¡ aggregate l l ¡ aggregator collect the data from sensors compute aggregated result commit l aggregator commits to the data ¡ ¡ guarantee that result is computed using sensors’ data prove l l aggregator send the aggregate result and commitment to home server ¡ ¡ checks if commitment is good representation of the sensor data aggregation result is close to the committed data values
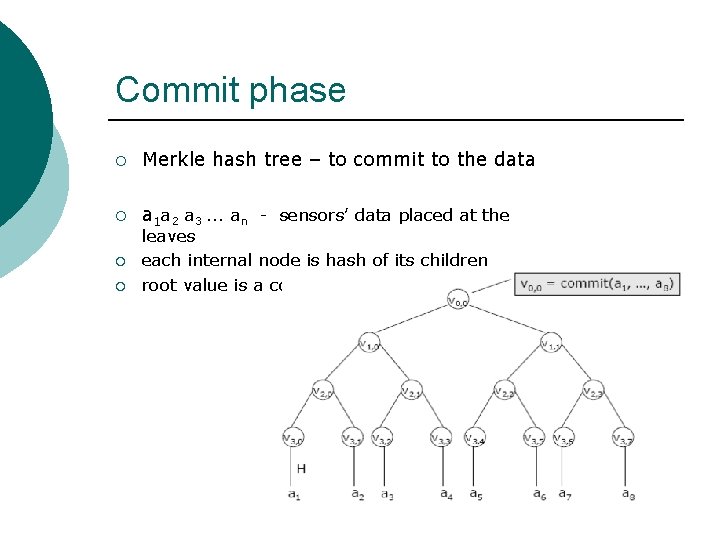
Commit phase ¡ Merkle hash tree – to commit to the data ¡ a 1 a 2 a 3. . . an - sensors’ data placed at the ¡ ¡ leaves each internal node is hash of its children root value is a commitment
Considered … ¡ Most commonly used aggregation operations: l l l Compute median Compute min, max Counting distinct elements
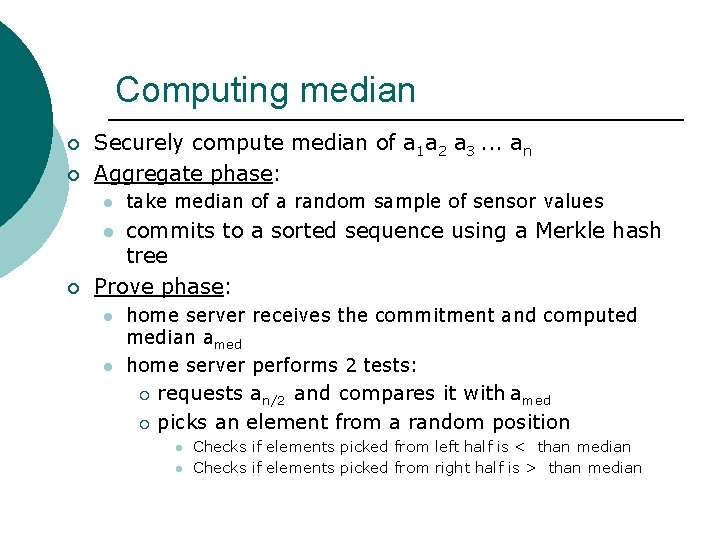
Computing median ¡ ¡ Securely compute median of a 1 a 2 a 3. . . an Aggregate phase: l take median of a random sample of sensor values commits to a sorted sequence using a Merkle hash tree Prove phase: l ¡ l l home server receives the commitment and computed median amed home server performs 2 tests: requests an/2 and compares it with amed ¡ picks an element from a random position ¡ l l Checks if elements picked from left half is < than median Checks if elements picked from right half is > than median
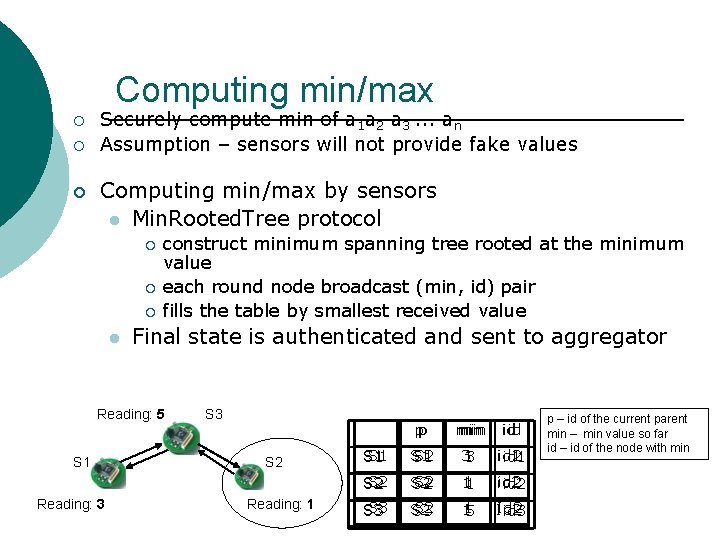
Computing min/max ¡ ¡ ¡ Securely compute min of a 1 a 2 a 3. . . an Assumption – sensors will not provide fake values Computing min/max by sensors l Min. Rooted. Tree protocol ¡ ¡ ¡ l construct minimum spanning tree rooted at the minimum value each round node broadcast (min, id) pair fills the table by smallest received value Final state is authenticated and sent to aggregator Reading: 5 S 1 Reading: 3 S 2 Reading: 1 pp min min id id S 1 S 2 S 1 31 3 id 2 id 1 S 2 S 2 11 1 id 2 S 3 S 2 S 3 11 5 Id 2 id 3 p – id of the current parent min – min value so far id – id of the node with min
Computing min/max ¡ Aggregate phase: ¡ aggregator commits to the list of the states ¡ reports the root of the tree to the server ¡ Prove phase: ¡ home server randomly picks a node in the list ¡ traverses the path from the node to the root ¡ If unsuccessful - rejects
Counting distinct elements ¡ Securely determine number of distinct values given a 1 a 2 a 3. . . an ¡ Basic protocol: l l ¡ Pick random hash function h Apply to all elements ai Keep v=mini=1 n h(ai) Number of distinct elements can be estimated by 1/v Protocol can be used for: l l computing the size of the network computing average value

Conclusion ¡ Hierarchical aggregation for very large networks l ¡ Consider forward secure authentication for past results querying l l ¡ the proposed protocols need to be slightly modified sensor’s key is recomputed each time interval using one-way function past readings are secure in case sensor is compromised This is the first work that allows existence of malicious sensors
- Slides: 13