September 2004 doc IEEE 802 11 041117 00
September 2004 doc. : IEEE 802. 11 -04/1117 -00 Just-in-time Transition Setup Nancy Cam-Winget and Rajneesh Kumar, Cisco Systems Inc Kapil Sood and Jesse Walker, Intel Corporation Stefano Faccin, Nokia Michael Montemurro, Chantry Networks Chris Durand, Spectralink Submission 1 N. Cam-Winget, et al
September 2004 doc. : IEEE 802. 11 -04/1117 -00 Just-in-Time Security Associations • Allow interoperability with 802. 11 i and 802. 11 e • Reuse existing 802. 11 i and 802. 11 e mechanisms and implementations • Pre-compute PTK on the STA prior to Re-Association – Relieve computational constraints on low power clients • Establish security associations liveness and GTK at reassociation time • Integrate Qo. S and Security • Reuse 802. 11 k to optimize scanning time and AP selection based on resource availability – “Ask Forgiveness” protocols are generally more efficient than “Ask Permission” protocols Submission 2 N. Cam-Winget, et al
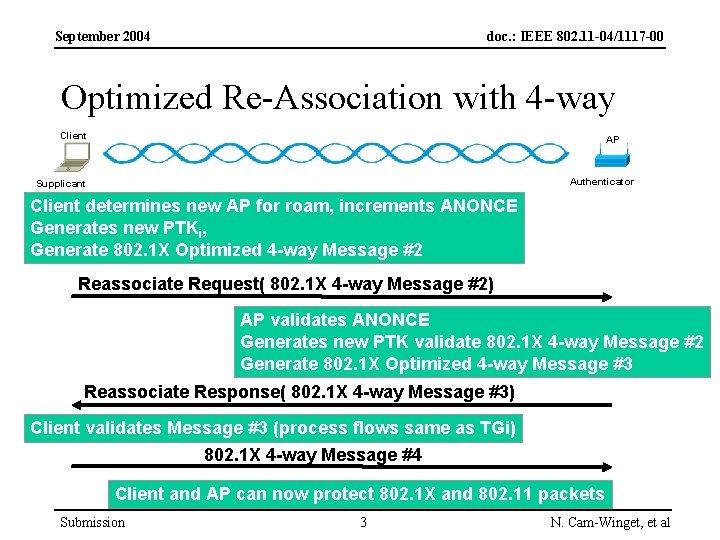
September 2004 doc. : IEEE 802. 11 -04/1117 -00 Optimized Re-Association with 4 -way Client AP Authenticator Supplicant Client determines new AP for roam, increments ANONCE Generates new PTKi, Generate 802. 1 X Optimized 4 -way Message #2 Reassociate Request( 802. 1 X 4 -way Message #2) AP validates ANONCE Generates new PTK validate 802. 1 X 4 -way Message #2 Generate 802. 1 X Optimized 4 -way Message #3 Reassociate Response( 802. 1 X 4 -way Message #3) Client validates Message #3 (process flows same as TGi) 802. 1 X 4 -way Message #4 Client and AP can now protect 802. 1 X and 802. 11 packets Submission 3 N. Cam-Winget, et al
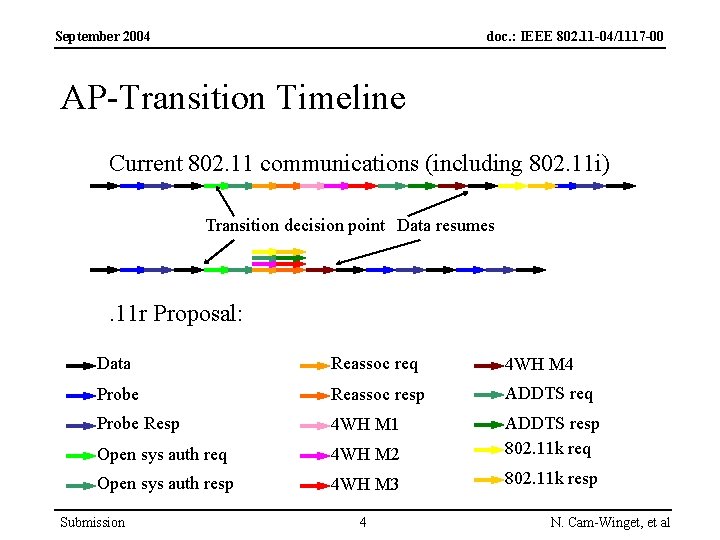
September 2004 doc. : IEEE 802. 11 -04/1117 -00 AP-Transition Timeline Current 802. 11 communications (including 802. 11 i) Transition decision point Data resumes . 11 r Proposal: Data Reassoc req 4 WH M 4 Probe Reassoc resp ADDTS req Probe Resp 4 WH M 1 Open sys auth req 4 WH M 2 ADDTS resp 802. 11 k req Open sys auth resp 4 WH M 3 802. 11 k resp Submission 4 N. Cam-Winget, et al
- Slides: 4