September 2004 15 04 0560 00 004 b
September, 2004 15 -04 -0560 -00 -004 b Project: IEEE P 802. 15 Working Group for Wireless Personal Area Networks (WPANs) Submission Title: [Computational Complexity of CCM* Mode of Operation] Date Submitted: [September 23, 2004] Source: [René Struik] Company [Certicom Corp. ] Address [5520 Explorer Drive, 4 th Floor, Mississauga, ON Canada L 4 W 5 L 1] Voice: [+1 (905) 501 -6083], FAX: [+1 (905) 507 -4230], E-Mail: [rstruik@certicom. com] Re: [IEEE submission 15 -04 -0537 -00 -004 b (CCM* Specification). ] Abstract: [This document explains the computational cost of CCM*, in settings relevant for 802. 15. 4 b. ] Purpose: [Education of IEEE 802. 15. 4 b audience, promoting sound technical analysis. ] Notice: This document has been prepared to assist the IEEE P 802. 15. It is offered as a basis for discussion and is not binding on the contributing individual(s) or organization(s). The material in this document is subject to change in form and content after further study. The contributor(s) reserve(s) the right to add, amend or withdraw material contained herein. Release: The contributor acknowledges and accepts that this contribution becomes the property of IEEE and may be made publicly available by P 802. 15. Submission 1 Rene Struik, Certicom Corp.
September, 2004 15 -04 -0560 -00 -004 b Computational Complexity of CCM* Mode of Operation René Struik, Certicom Research Submission 2 Rene Struik, Certicom Corp.
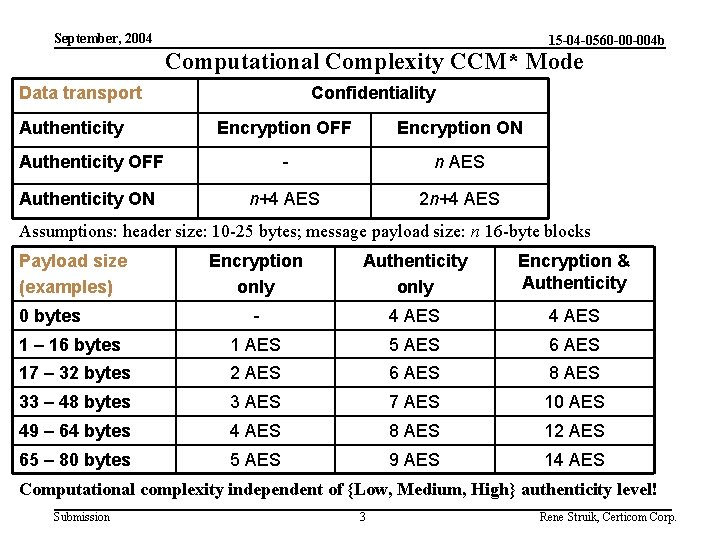
September, 2004 15 -04 -0560 -00 -004 b Computational Complexity CCM* Mode Data transport Authenticity Confidentiality Encryption OFF Encryption ON Authenticity OFF - n AES Authenticity ON n+4 AES 2 n+4 AES Assumptions: header size: 10 -25 bytes; message payload size: n 16 -byte blocks Payload size (examples) Encryption only Authenticity only Encryption & Authenticity - 4 AES 1 – 16 bytes 1 AES 5 AES 6 AES 17 – 32 bytes 2 AES 6 AES 8 AES 33 – 48 bytes 3 AES 7 AES 10 AES 49 – 64 bytes 4 AES 8 AES 12 AES 65 – 80 bytes 5 AES 9 AES 14 AES 0 bytes Computational complexity independent of {Low, Medium, High} authenticity level! Submission 3 Rene Struik, Certicom Corp.
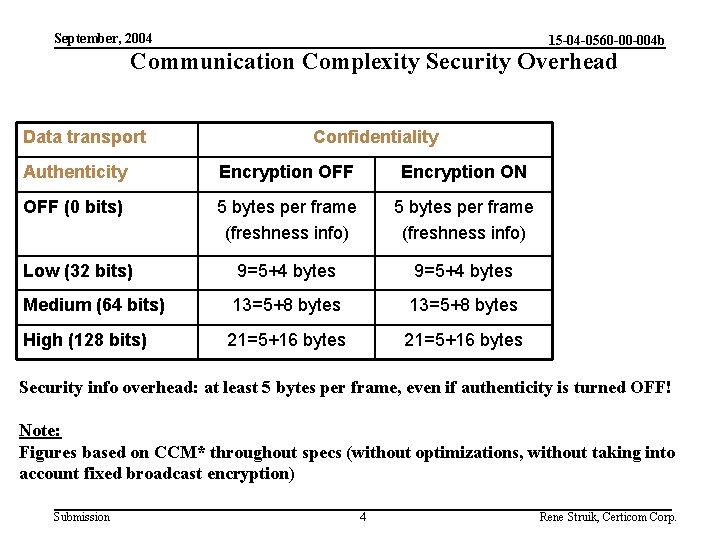
September, 2004 15 -04 -0560 -00 -004 b Communication Complexity Security Overhead Data transport Confidentiality Authenticity Encryption OFF Encryption ON OFF (0 bits) 5 bytes per frame (freshness info) Low (32 bits) 9=5+4 bytes Medium (64 bits) 13=5+8 bytes High (128 bits) 21=5+16 bytes Security info overhead: at least 5 bytes per frame, even if authenticity is turned OFF! Note: Figures based on CCM* throughout specs (without optimizations, without taking into account fixed broadcast encryption) Submission 4 Rene Struik, Certicom Corp.
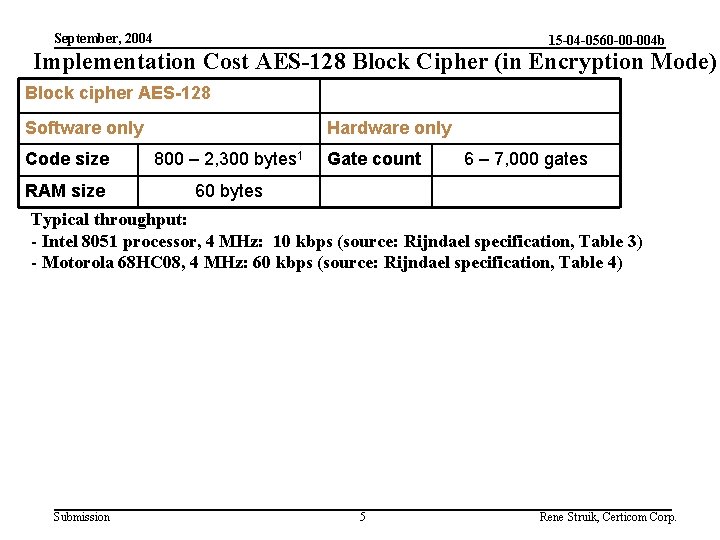
September, 2004 15 -04 -0560 -00 -004 b Implementation Cost AES-128 Block Cipher (in Encryption Mode) Block cipher AES-128 Software only Hardware only Code size 800 – 2, 300 bytes 1 RAM size 60 bytes Gate count 6 – 7, 000 gates Typical throughput: - Intel 8051 processor, 4 MHz: 10 kbps (source: Rijndael specification, Table 3) - Motorola 68 HC 08, 4 MHz: 60 kbps (source: Rijndael specification, Table 4) Submission 5 Rene Struik, Certicom Corp.
- Slides: 5