Seminar On Ethical Hacking NameSubhashree Sahoo U Roll
Seminar On Ethical Hacking Name-Subhashree Sahoo U. Roll no-1702010420490208 Dept. of Computer Science Raghunathjew Degree Colleege, Deula Sahi 1
Contents § Introduction to Ethical Hacking § Hackers § Hacking Process § Why we need ethical hacking § What do hackers do after hacking § Advantages § Disadvantages § Conclusion 2
1. Introduction to Ethical hacking Ø Ethical Hacking refers to the act of locating weaknesses and vulnerabilities of computer and duplicating the intent in information systems. Ø This is also known as penetration testing or intrusion testing. Ø It neither damage the target system nor steal information. Ø It evaluate target systems security and report back to owners about the vulnerabilities found. Ø It uses the same tools, tricks and techniques that hackers ese, but with one major difference that ethical hacking is legal. 3
2. Hackers o Hacker is someone who explores methods for breaching defences and exploiting weaknesses in a computer system. o Hackers may be motivated by a multitude of reasons, such as profit, challenges, information gathering and to evaluate system weaknesses. o We can also define the term ‘Hackers’ as someone with an advanced understanding of computers. Hacker Black Hat White Hat Grey Hat 4
Fig. (A) Fig. (B) Fig. (C) 5
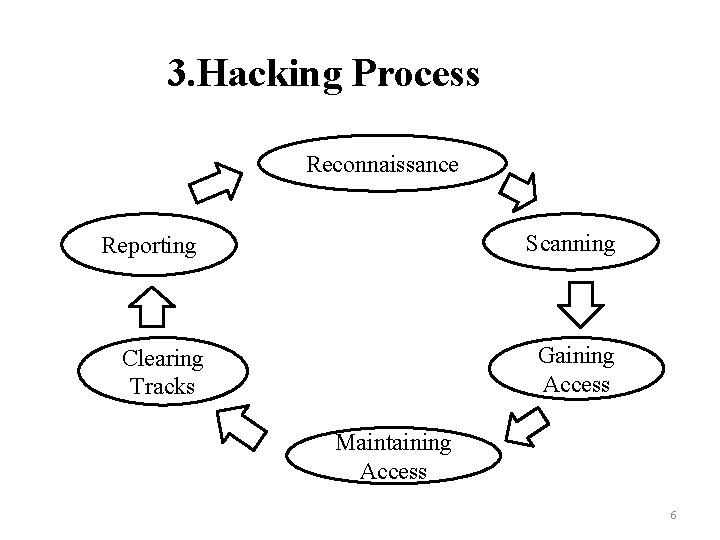
3. Hacking Process Reconnaissance Scanning Reporting Gaining Access Clearing Tracks Maintaining Access 6
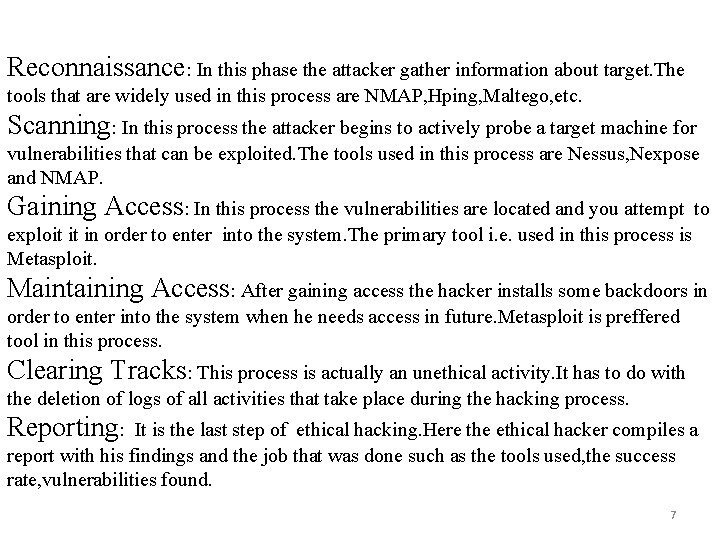
Reconnaissance: In this phase the attacker gather information about target. The tools that are widely used in this process are NMAP, Hping, Maltego, etc. Scanning: In this process the attacker begins to actively probe a target machine for vulnerabilities that can be exploited. The tools used in this process are Nessus, Nexpose and NMAP. Gaining Access: In this process the vulnerabilities are located and you attempt to exploit it in order to enter into the system. The primary tool i. e. used in this process is Metasploit. Maintaining Access: After gaining access the hacker installs some backdoors in order to enter into the system when he needs access in future. Metasploit is preffered tool in this process. Clearing Tracks: This process is actually an unethical activity. It has to do with the deletion of logs of all activities that take place during the hacking process. Reporting: It is the last step of ethical hacking. Here the ethical hacker compiles a report with his findings and the job that was done such as the tools used, the success rate, vulnerabilities found. 7
4. Why we need Ethical Hacking • To build a computer system that prevents hackers’ access and safeguard system and information from malicious attack. • To test networks at regular intervals. • To create security awareness at all levels in a business. • To manage adequate preventive measures in order to avoid security breaches. 8
5. What do hackers do after hacking Ø Patch security hole Ø Install exploit program Ø Install roolkit(backdoor) Ø Use of all installed program silently Ø Install scanner program Ø Install denial of service program 9
6. Advantages § Testing security measures § Understanding hacker techniques § Fighting against terrorism and national security breaches § Having a computer system that prevents malicious hackers from gaining access. 10
7. Disadvantages o Massive security breach o The possibilty that the ethical hacker will send and/or place malicious code, viruses, malware and other destructive and harmful things on a computer system. o Allowing the company’s financial and banking details to be seen. o All depends upon the trustworthiness of the ethical hacker. 11
8. Conclusion • In this section , now we can see what can we do against hacking or to protect ourselves from hacking. • The first thing we should do is to keep ourselves updated about those softwares we are using for official and reliable sources. • Educate the employees and users against black hat hacking. 12
9. References ü Sommerville, Software Engineering, 9/e, Addison Wesley. ü www. wikipedia. org ü www. quora. com ü www. google. com 13
Thank You 14
Any Query 15
- Slides: 15