SEMINAR ON COMPUTER VIRUS PREPARED BY Harsh dhruv
SEMINAR ON COMPUTER VIRUS PREPARED BY Harsh dhruv sreejit
Introduction of Virus Ø Len Adleman – Give the name “Virus” Ø Definition Ø Two types of Virus : ü Computer Virus ü Mobile Virus 2
Virus • A virus is a small piece of software that piggybacks on real programs 3
E-mail viruses • An e-mail virus moves around in e-mail messages, and usually replicates itself by automatically mailing itself to dozens of people in the victim's e-mail address book. Ø EXAMPLE • I Love You Virus in 4 -May, 2000 4
Worms • A worm is a small piece of software that uses computer networks and security holes to replicate itself. • Example Ø Code Red in 19 july , 2000 • It Slows Down the internet traffic while replicate itself 5
Trojan horses • A Trojan horse is simply a computer program. The program claims to do one thing (it may claim to be a game) but instead does damage when you run it (it may erase your hard disk). Trojan horses have no way to replicate automatically. • Examples: Net Bus and Back Orifice, Sub seven 6
Boot Sector Viruses • The boot sector is a small program that is the first part of the operating system that the computer loads. • The boot sector contains a tiny program that tells the computer how to load the rest of the operating system. 7
Program viruses • These infect executable program files, such as those with extensions like. BIN, . COM, . EXE, . OVL, . DRV (driver) and. SYS Multipartite viruses • A hybrid of Boot and Program viruses • Examples: Invader, Flip, and Tequila 8
Stealth viruses • These viruses use certain techniques to avoid detection • Examples: Frodo, Joshi, Whale Polymorphic viruses • These viruses are more difficult to detect. Examples: Involuntary, Stimulate, Cascade, Phoenix, Evil, Proud, Virus 101 9
Macro Viruses • A macro virus is a new type of computer virus that infects the macros within a document or template. When you open a word processing or spreadsheet document, the macro virus is activated and it infects the Normal template (Normal. dot)-a general purpose file that stores default document formatting settings. 10
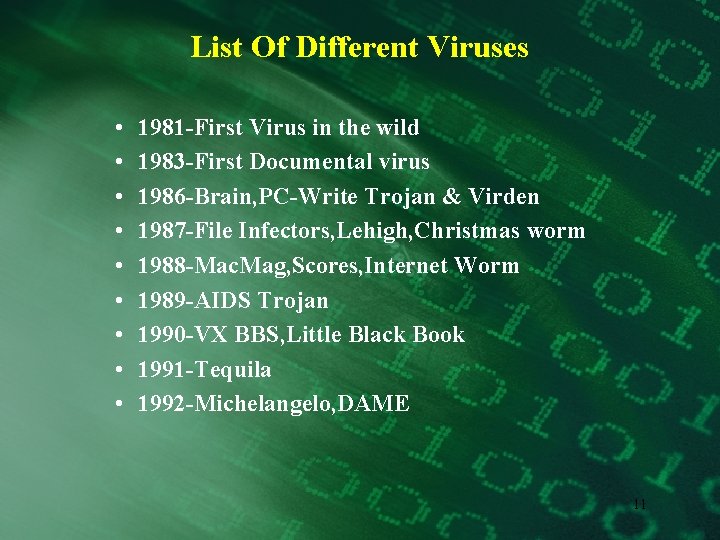
List Of Different Viruses • • • 1981 -First Virus in the wild 1983 -First Documental virus 1986 -Brain, PC-Write Trojan & Virden 1987 -File Infectors, Lehigh, Christmas worm 1988 -Mac. Mag, Scores, Internet Worm 1989 -AIDS Trojan 1990 -VX BBS, Little Black Book 1991 -Tequila 1992 -Michelangelo, DAME 11
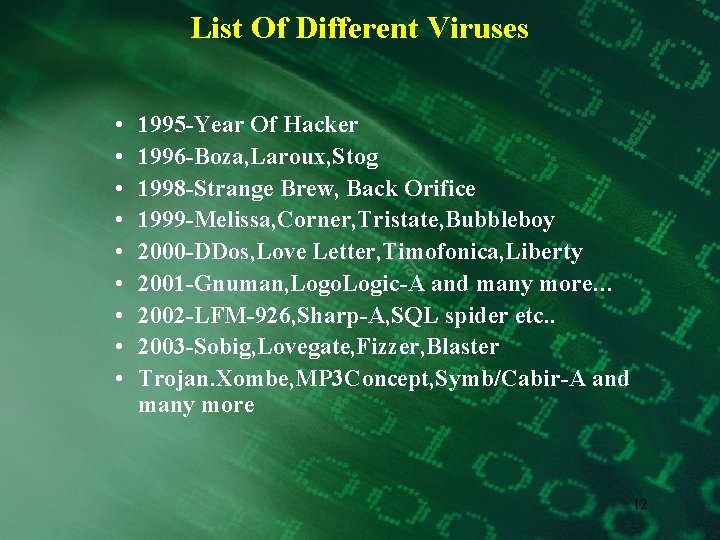
List Of Different Viruses • • • 1995 -Year Of Hacker 1996 -Boza, Laroux, Stog 1998 -Strange Brew, Back Orifice 1999 -Melissa, Corner, Tristate, Bubbleboy 2000 -DDos, Love Letter, Timofonica, Liberty 2001 -Gnuman, Logo. Logic-A and many more… 2002 -LFM-926, Sharp-A, SQL spider etc. . 2003 -Sobig, Lovegate, Fizzer, Blaster Trojan. Xombe, MP 3 Concept, Symb/Cabir-A and many more 12
2003, Slammer, sobig, Lovgate, Fizzer, Blast er/ Welchia/mimail • A Worm that carried its own SMTP mail program and used windows network shares to spread started year. • South Korea was eliminating from the network 13
2004 Trojan. Xombe, Randex, Bizex, Mp 3 Concept, Sasser, Mac Os X, W 64. Rugrat. 3344, Symb/Cabir. A, WCE/Duts, W 32/Amus-A, Jpeg Weakness • Trojan. Xombe was sent out to a wide audience. It posed as a message from Microsoft Windows Update asking you to run the attached revision to XP Service Pack 1. • MP 3 Concept turned out to be nothing more than a bad proof-of-concept that never made it into the wild. 14
2004 • The proof-of-concept Worm W 64. Rugrat. 3344 showed up the end of May. This is claimed to be the first malware that specifically attacks 64 -bit Windows files only • Symb/Cabir-A appeared to infect Nokia Series 60 mobile phones • Microsoft common. DLL file that processes the image file type and has a buffer overrun error that could allow someone to add malicious code to a JPEG image which can then open holes in an attacked system 15
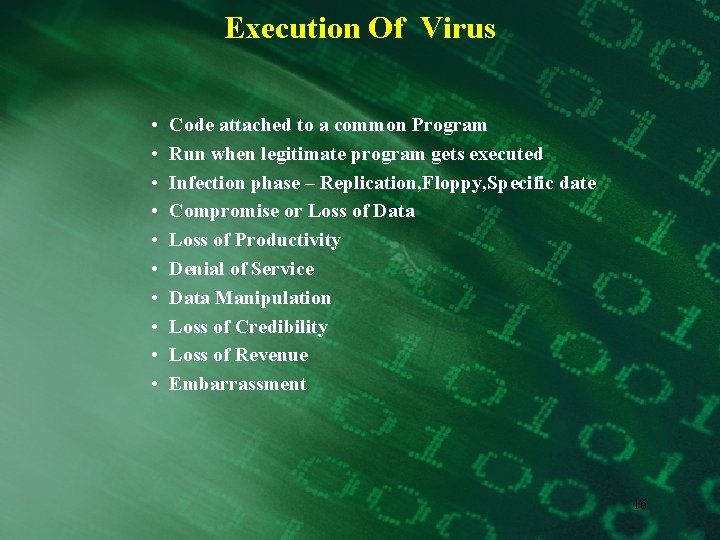
Execution Of Virus • • • Code attached to a common Program Run when legitimate program gets executed Infection phase – Replication, Floppy, Specific date Compromise or Loss of Data Loss of Productivity Denial of Service Data Manipulation Loss of Credibility Loss of Revenue Embarrassment 16

Impact and Effects • • • • Nuisance Spoofing Denial of Service Overwriting and Data diddling Destruction Psychological “Netspionage” Siphoning data Exposing vulnerabilities Compromise or Loss of Data Loss of Productivity Denial of Service Data Manipulation Loss of Credibility Loss of Revenue Embarrassment 17
Protection Against Virus • • Operating System – UNIX Virus Protection Software Macro Virus Protection Précising use of Internet, Email-attachment 18
WAP Threats • The use of WAP-enabled mobile phones is booming. Cellular phones with support for WAP (Wireless Application Protocol) allow users to access a wide variety of services. • WAP enables users to do on-line banking, monitor stock markets, use email, access the Internet – all from their mobile phones 19
CABIR • First Mobile phone Virus • Discovered by French Arm of Jaspers Labs • Developed by Global group “No Technology is reliable and safe from their attack” • Nokia, Siemens, Sony Erickson 20
CABIR • How it works? § Symbian OS § Caribe. sys § Bluetooth § No harmful Effect 21
Motives • Curiosity • Challenge • To gain wide attention 22
Virus Action • Three Logical Components of WAP Network a. The WAP Client(Mobile Terminal) b. The WAP Gateway c. The Origin Server • More Functionality means more risk • Making phone calls • Accessing & Modifying Phone Book Data • Sending SMS • Restart phones 23
Protection Against Virus • Antivirus Software : F-Secure Web Site • Nokia 6670 – First mobile with Virus Protection • Estimated Retail Price $613 • Two Tri-Band • Optimized for GAM Networks in the EMEA • Pricing plan for F-Secure Antivirus Protection • Protection License - $3. 62 per month • Nokia offer additional Security • VPN & SSL 24

Ø Protection Against Virus • Shutting the Stable Door • Gateway Level Solution • WML Script Scanner • Detect and Remove malicious code • Requiring no client software 25
Some Information Resources • Anti-virus vendors • NIPC and other CERTS http: //www. nipc. gov http: //www. cert. org http: //www. fedcirc. gov http: //www. sans. org • Virus Bulletin http: //www. virusbtn. com • The Wildlist Organization http: //www. wildlist. org • Virus Hoax Web Site http: //www. vmyths. com • European Institute for Computer Anti-Virus Research (EICAR) http: //www. eicar. org • Anti-Virus Information Exchange Network (AVIEN) http: //www. avien. net 26
Additional Resources • “The Generic Virus Writer” and other papers by Sarah Gordon http: //www. badguys. org/ • Short Course on Computer Viruses, 2 nd Edition by Fred Cohen • “Free Macro Protection Techniques” by Chengi Jimmy Kuo, Network Associates http: //download. nai. com/products/media/vil/ pdf/free_AV_tips_techniques. pdf • Computer Viruses Demystified http: //www. sophos. com/sophos/docs/eng/ref guide/viru_ben. pdf • Viruses Revealed by Robert Slade, David Harley, et al. 27
End of Presentation THANK YOU 28
- Slides: 28