Seeing the Future Information Stacks and Interfaces Management

- Slides: 3

Seeing the Future Information Stacks and Interfaces Management Layer Energy Control Layer Energy Management Layer Sensor & Feedback Layer Mission Systems Layer Posture Assessment (Supply, Demand, Allocation) Energy Playbook (Source & Load Mgmt Options) Energy Profile (Status & Thresholds) Mission Criticality (Static & Dynamic) Multiple Layers of Information are Converged Multiple OSI Layer 1 Transport Mediums (IP, Wi. Fi 6, Lo. Ra. WAN, RF, and/or 5 G)
Busting the Myth: Isolated = Secure The Persistent Insider Threat: The persistent insider threat reinforces the notion that some of the most serious threats are trusted individuals that have the motivation, the ability, and the access required to identify highvalue material, find it, and create under-the-radar access pathways. The Persistent Outsider Threat: The persistent outsider threat reinforces the notion that adversaries are willing to spend months or years on a specific cyber attack mission. In the Ukraine power grid denial of service attack in December of 2016 the attack sequence progressed through multiple stages constituting a penetration testing phase, a land expand phase, an operational observation phase, an attack phase which included situational awareness denial.
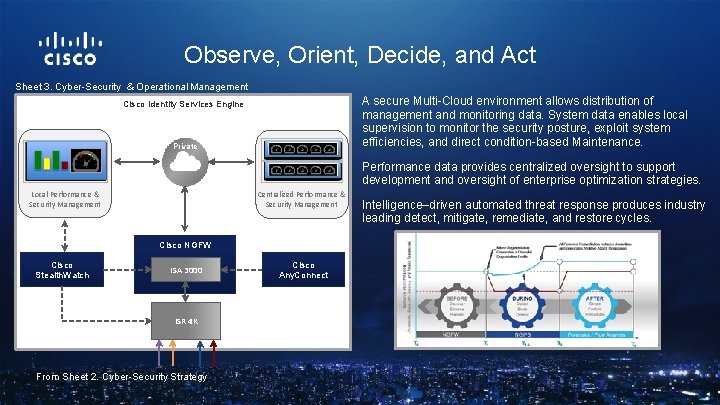
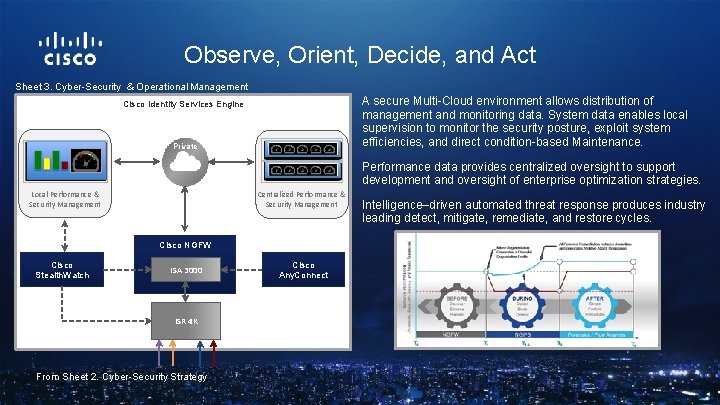
Observe, Orient, Decide, and Act Sheet 3. Cyber-Security & Operational Management A secure Multi-Cloud environment allows distribution of management and monitoring data. System data enables local supervision to monitor the security posture, exploit system efficiencies, and direct condition-based Maintenance. Cisco Identity Services Engine Private Performance data provides centralized oversight to support development and oversight of enterprise optimization strategies. Cloud Local Performance & Security Management Centralized Performance & Security Management Cisco NGFW Cisco IE Stealth. Watch 4000 ISA 3000 IE 4000 Cisco Any. Connect From Sheet 1. Enclave-driven, Protocol-based Clustering Strategy ISR 4 K From Sheet 2. Cyber-Security Strategy Intelligence–driven automated threat response produces industry leading detect, mitigate, remediate, and restore cycles.