Security Working Group 2018 Jan 03 Weekly Meeting




- Slides: 60

Security Working Group 2018 Jan 03 Weekly Meeting edgexfoundry. org | @edgexfoundry
2018 Jan 03 Security Working Group Meeting Agenda • Inbound Connection Manager Firewall (Priority #1) • David Ferriera (Forge. Rock) update progress on definition of requirements and search for open source candidates • Key Management API (Priority #2) • Riaz Zolfonoon (RSA) update progress definition of REST API • Internal container to container security API (Priority #3) • Starter-set of APIs to kick start Security API • James White/Steve Osselton • Next action – James and Steve to propose API post Barcelona release edgexfoundry. org | @edgexfoundry
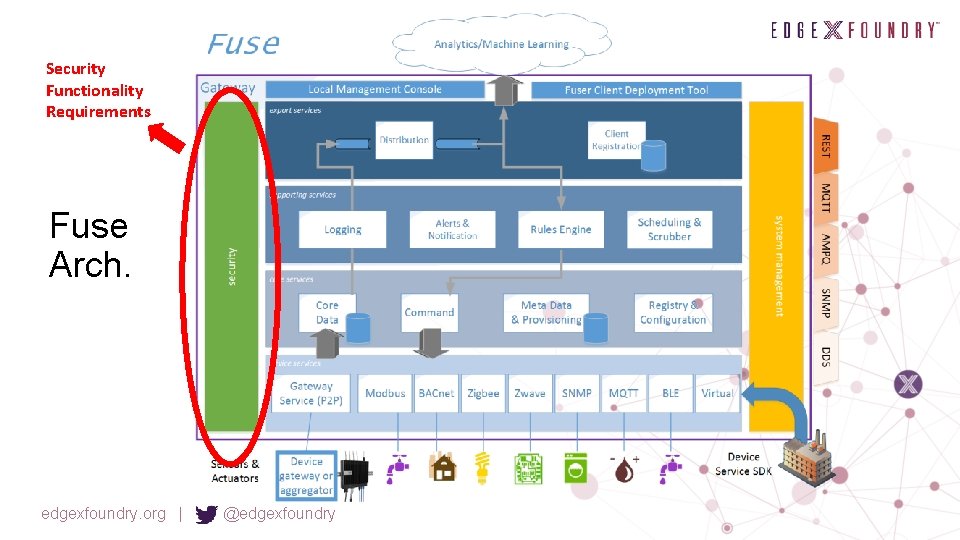
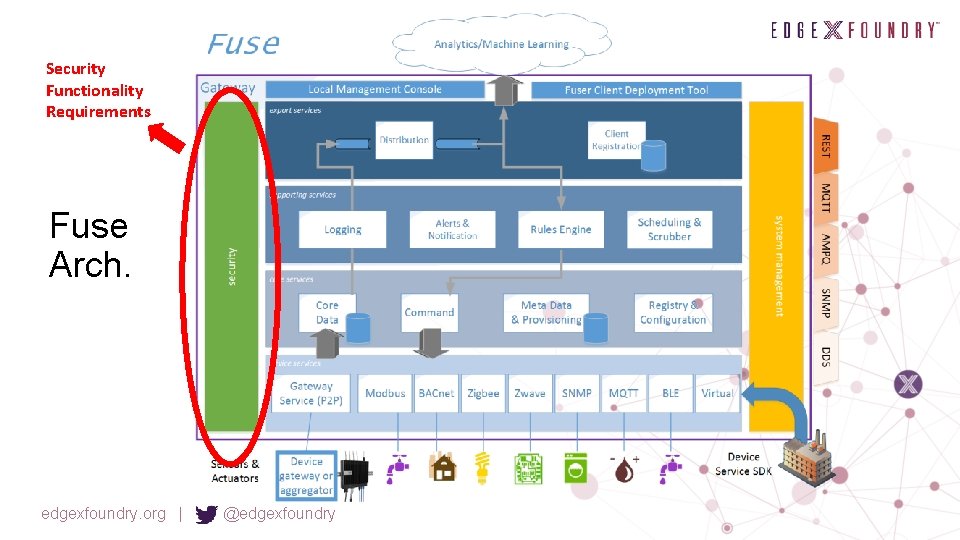
Security Functionality Requirements Fuse Arch. edgexfoundry. org | @edgexfoundry
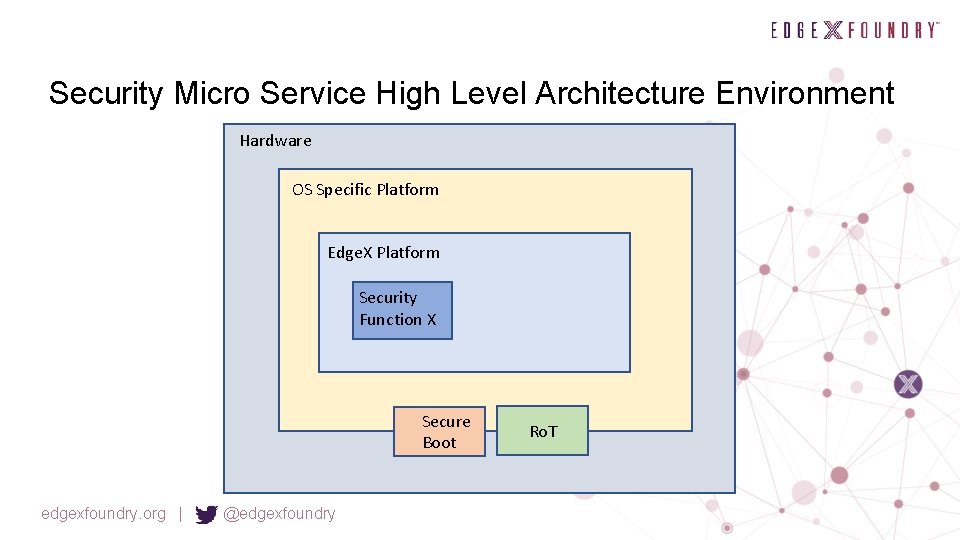
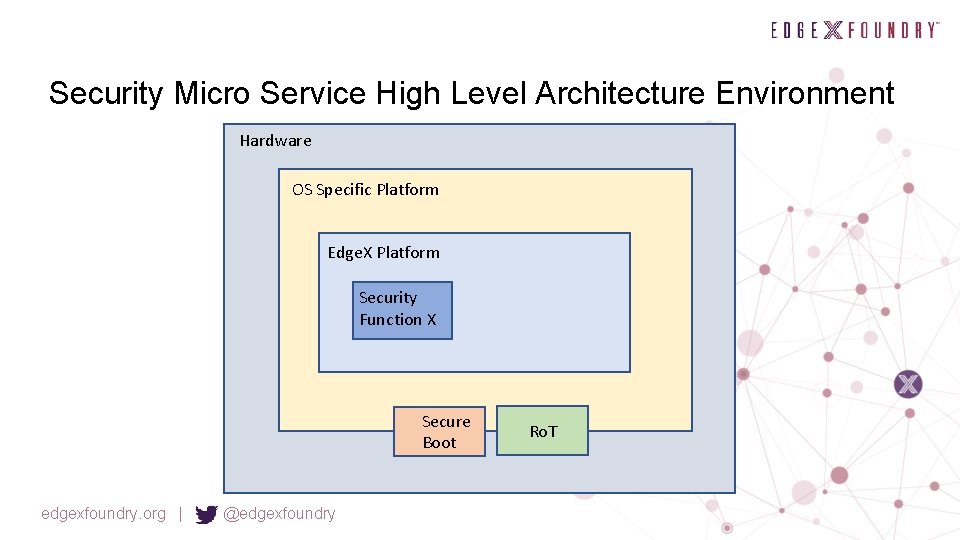
Security Micro Service High Level Architecture Environment Hardware OS Specific Platform Edge. X Platform Security Function X Secure Boot edgexfoundry. org | @edgexfoundry Ro. T
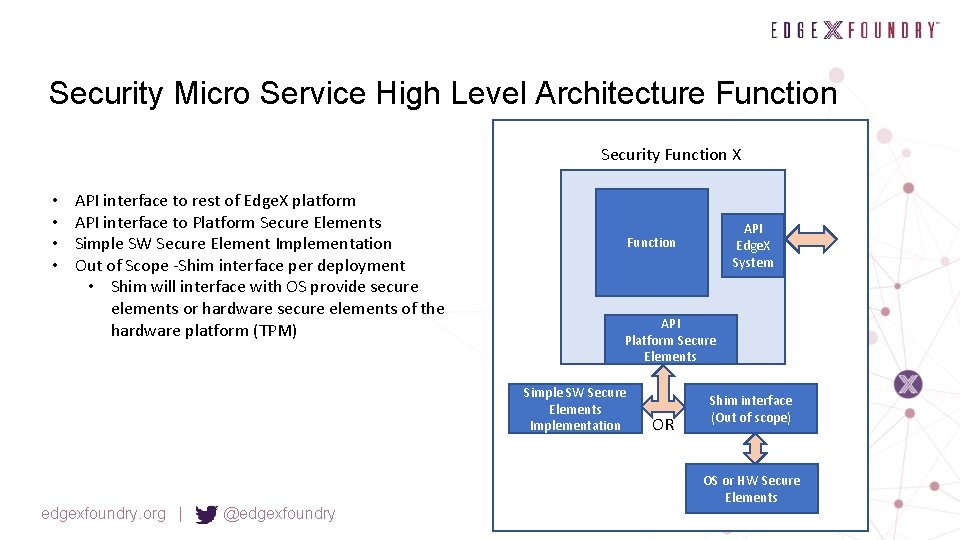
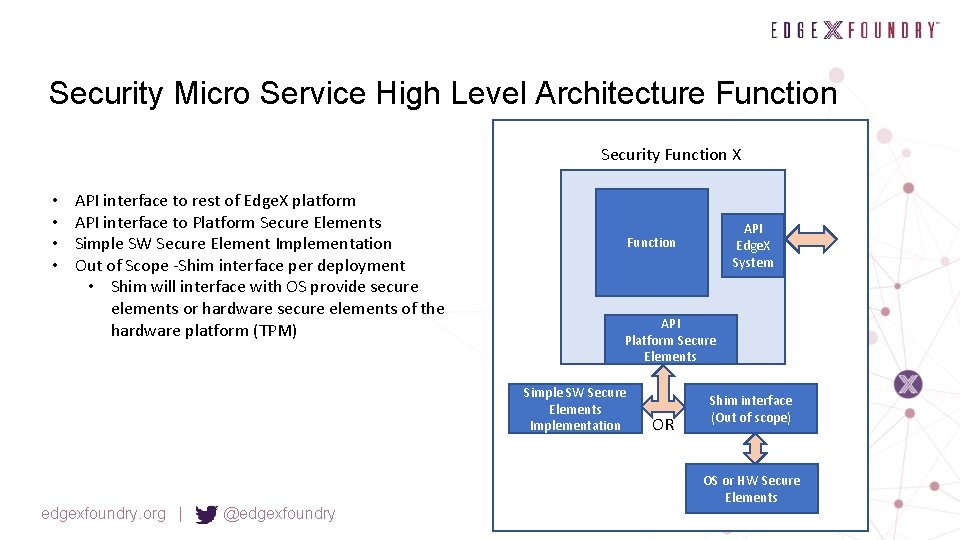
Security Micro Service High Level Architecture Function Security Function X • • API interface to rest of Edge. X platform API interface to Platform Secure Elements Simple SW Secure Element Implementation Out of Scope -Shim interface per deployment • Shim will interface with OS provide secure elements or hardware secure elements of the hardware platform (TPM) API Platform Secure Elements Simple SW Secure Elements Implementation edgexfoundry. org | @edgexfoundry API Edge. X System Function OR Shim interface (Out of scope) OS or HW Secure Elements
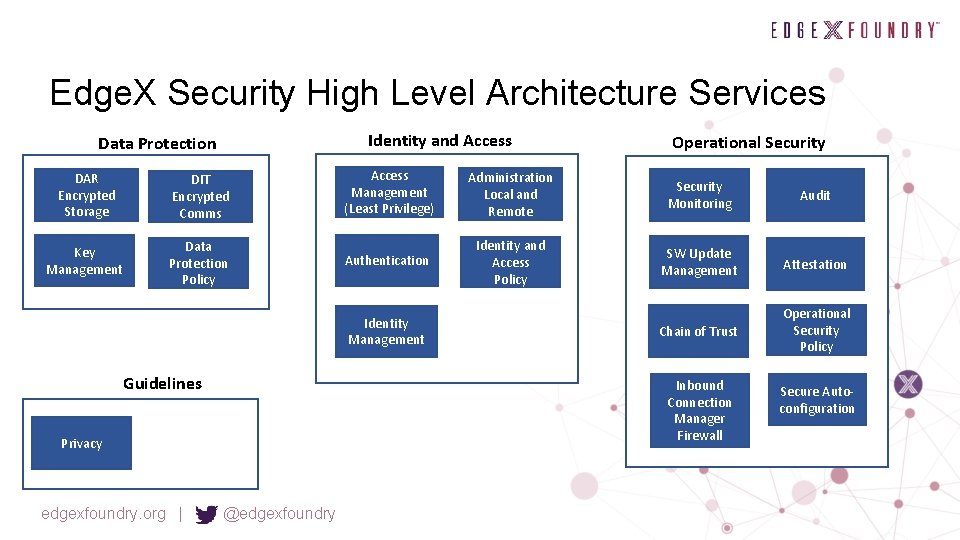
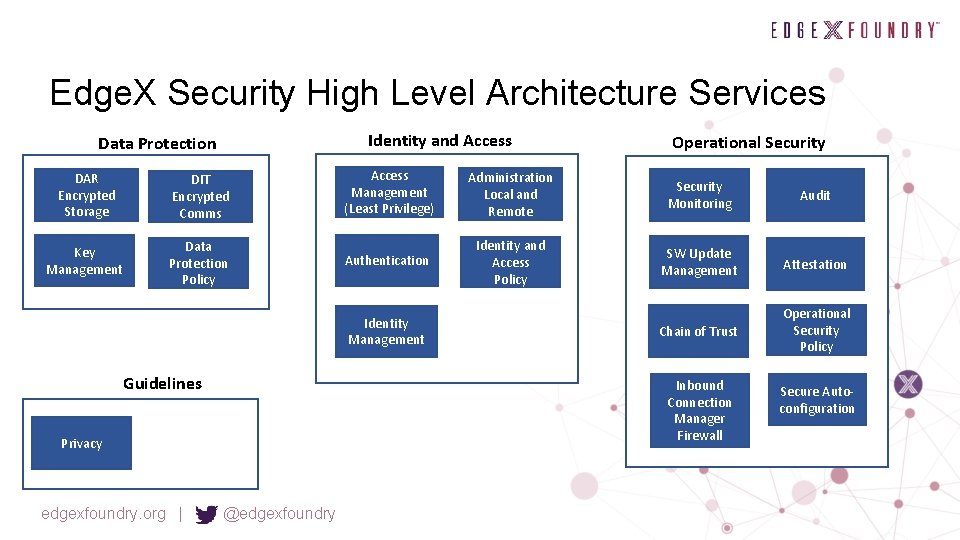
Edge. X Security High Level Architecture Services Identity and Access Data Protection DAR Encrypted Storage DIT Encrypted Comms Key Management Data Protection Policy Access Management (Least Privilege) Administration Local and Remote Security Monitoring Audit Authentication Identity and Access Policy SW Update Management Attestation Chain of Trust Operational Security Policy Identity Management Guidelines Inbound Connection Manager Firewall Privacy edgexfoundry. org | Operational Security @edgexfoundry Secure Autoconfiguration
Security Working Group Priorities • Priority #1 - Inbound Connection Manager Firewall • Priority #2 - Key Management • Priority #3 - Internal Micro service Security Protocol edgexfoundry. org | @edgexfoundry
Pick Next 3 High Priorities • Access Management • Authentication • Identity Management edgexfoundry. org | @edgexfoundry
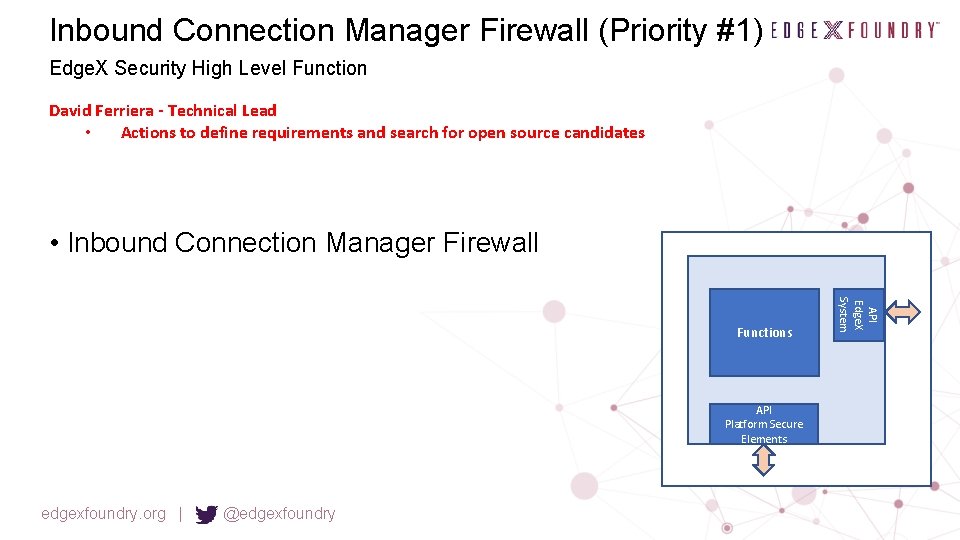
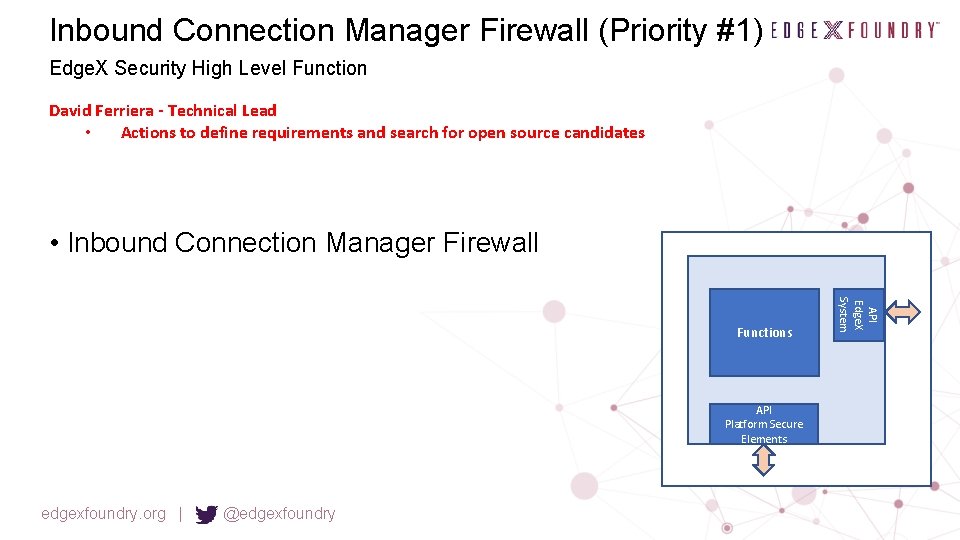
Inbound Connection Manager Firewall (Priority #1) Edge. X Security High Level Function David Ferriera - Technical Lead • Actions to define requirements and search for open source candidates • Inbound Connection Manager Firewall API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Priority #1 Inbound Connection Manager Firewall Implement the Fuse Security Service Ou td ate d– • The Edge. X Security WG identified a high priority need @ the Face to Face • Inbound Connection Manager (Firewall) • Protected communications of north bound interface • Dell began a security microservice that implemented functionality similar to the Inbound Connection Manager Ne eds • A firewall/proxy type service that protects the north side interface • The implementation was prototyped but not completed and placed into Fuse due to infrastructure needs to be determined (keystore, firewall, etc. ) • Proposal #1 Up • Post Barcelona, prioritize the work of one of our implementation teams to complete this implementation for California • Puts a strawman in place for the security working groups #1 priority • Will also require picking/using some open source infrastructure to further complete the implementation • • dat e This will assist in other security implementation efforts (or show weaknesses that need to be corrected) Firewall, keystore, etc. • Details on the next slide edgexfoundry. org | @edgexfoundry

Ou td a Inboundte Connection d –N Manager eed s Security Working Group Technical Lead: David Ferriera, Forgerock edgexfoundry. org | @edgexfoundry Up dat e
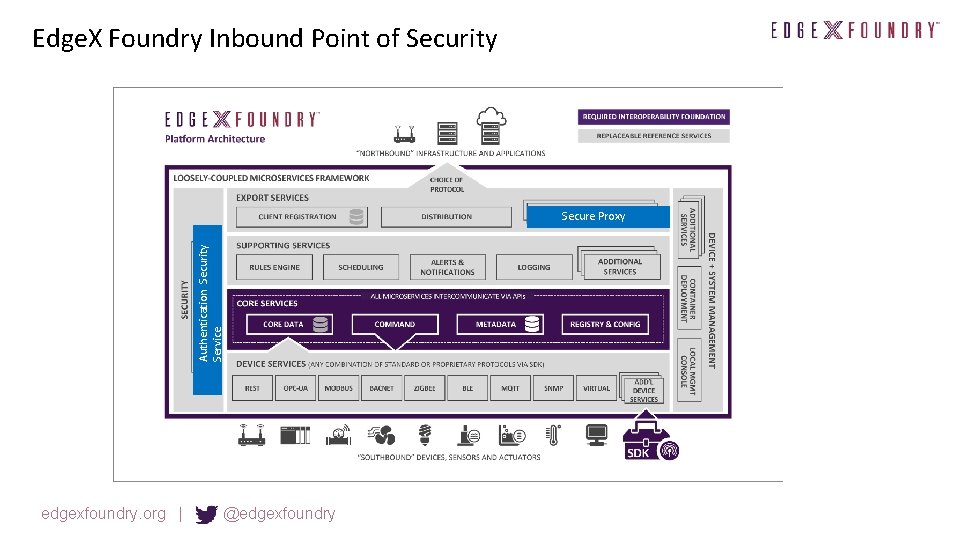
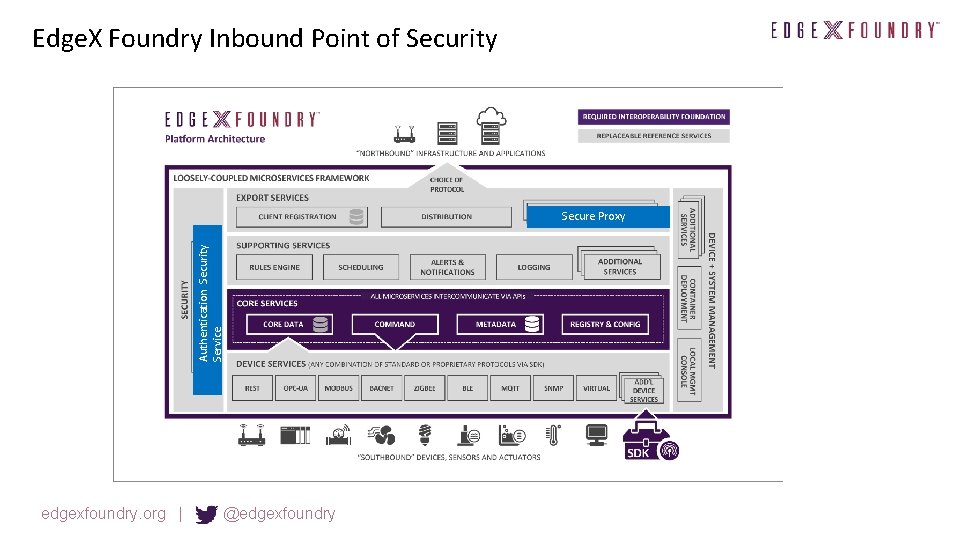
Edge. X Foundry Inbound Point of Security Authentication Security Service Secure Proxy edgexfoundry. org | @edgexfoundry
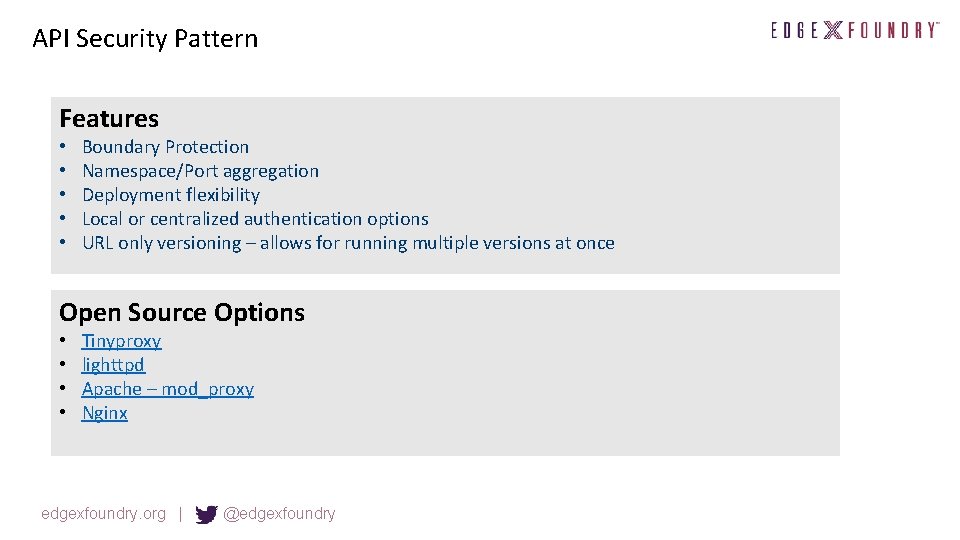
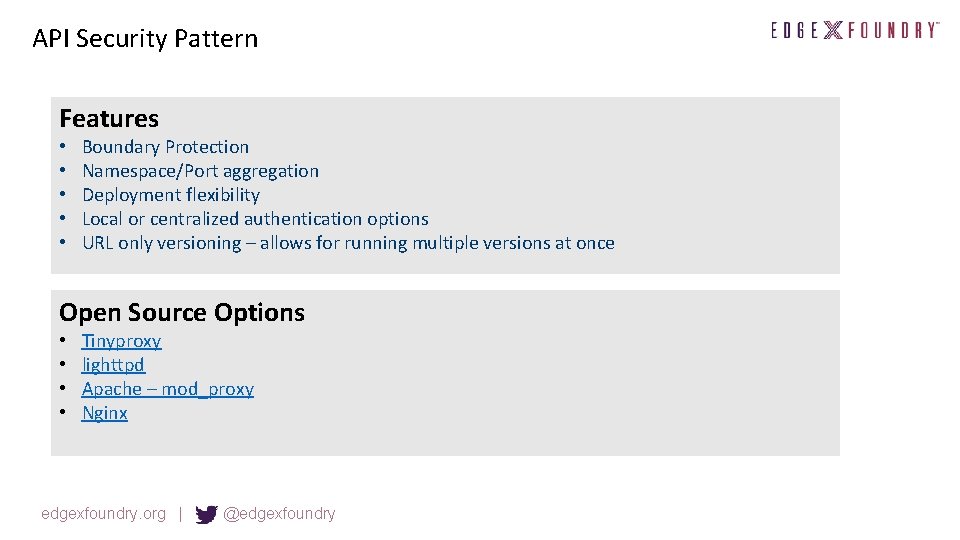
API Security Pattern Features • • • Boundary Protection Namespace/Port aggregation Deployment flexibility Local or centralized authentication options URL only versioning – allows for running multiple versions at once Open Source Options • • Tinyproxy lighttpd Apache – mod_proxy Nginx edgexfoundry. org | @edgexfoundry
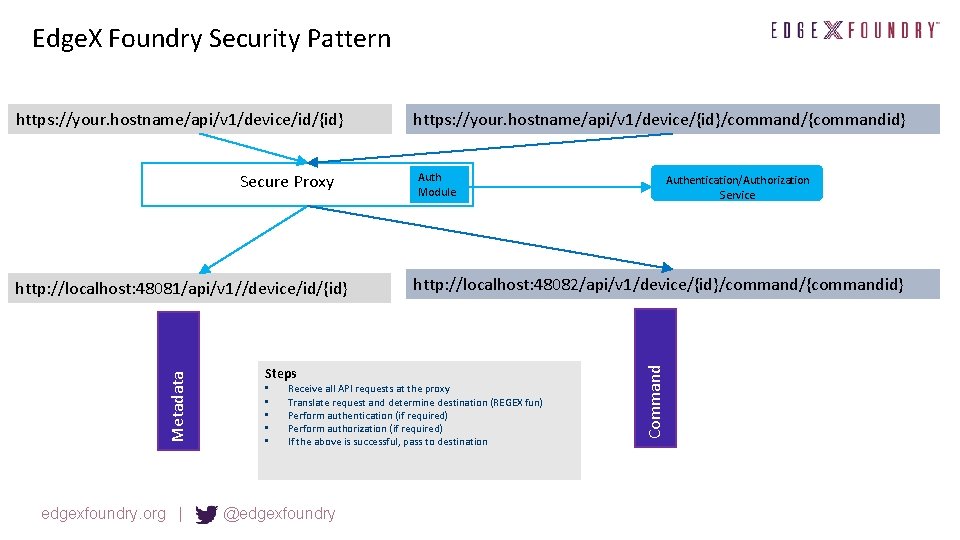
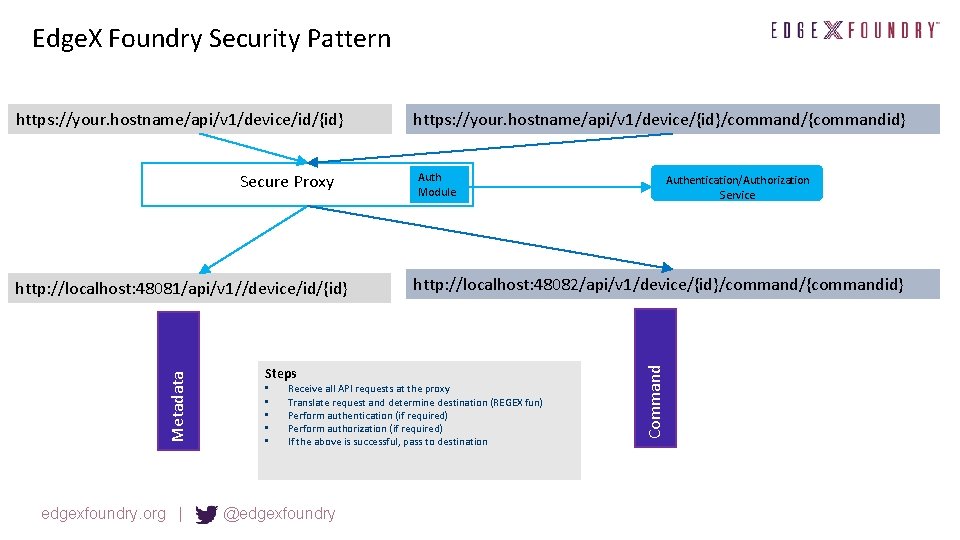
Edge. X Foundry Security Pattern Secure Proxy Metadata http: //localhost: 48081/api/v 1//device/id/{id} edgexfoundry. org | Steps • • • https: //your. hostname/api/v 1/device/{id}/command/{commandid} Auth Module http: //localhost: 48082/api/v 1/device/{id}/command/{commandid} Receive all API requests at the proxy Translate request and determine destination (REGEX fun) Perform authentication (if required) Perform authorization (if required) If the above is successful, pass to destination @edgexfoundry Authentication/Authorization Service Command https: //your. hostname/api/v 1/device/id/{id}
Inbound Connection Manager Firewall Next Steps • David is building a matrix of features and functionality for the proposed 4 proxies. • Target matrix date is last week of Nov. edgexfoundry. org | @edgexfoundry
Key Management (Priority #2) Edge. X Security High Level Function Riaz Zolfonnon - Technical Lead • Actions to define requirements for REST API and search for open source candidates • Key Management • Containerize Key Vault • Later someone would need to connect this to other OS services and hardware Ro. T Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • Need to design a REST Edge. X API to these services • PKCS #11 services?
Key Manager API Discussion topics Technical Lead: Riaz Zolfonoon (RSA)
Objectives • Simple REST API for basic Data Protection (DP) services • • • Key Management Certificate Services Encryption • Provide an implementation of the DP API • Ideally, adopt an existing open source options • Pluggable Modules • Third parties should be able to replace or extend all or portions of the API implementation as value-add with no negative impact on the clients (e. g. add hardwarebased key store). edgexfoundry. org | @edgexfoundry
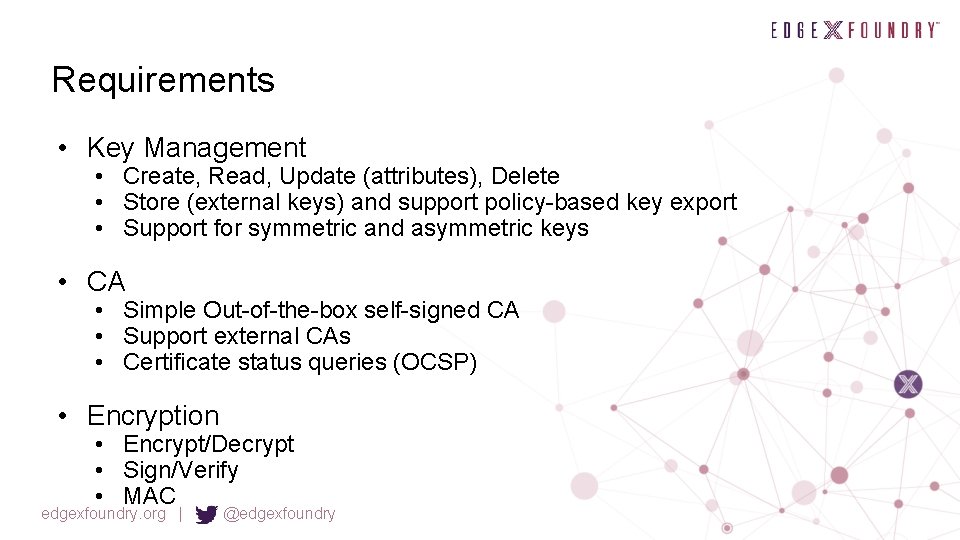
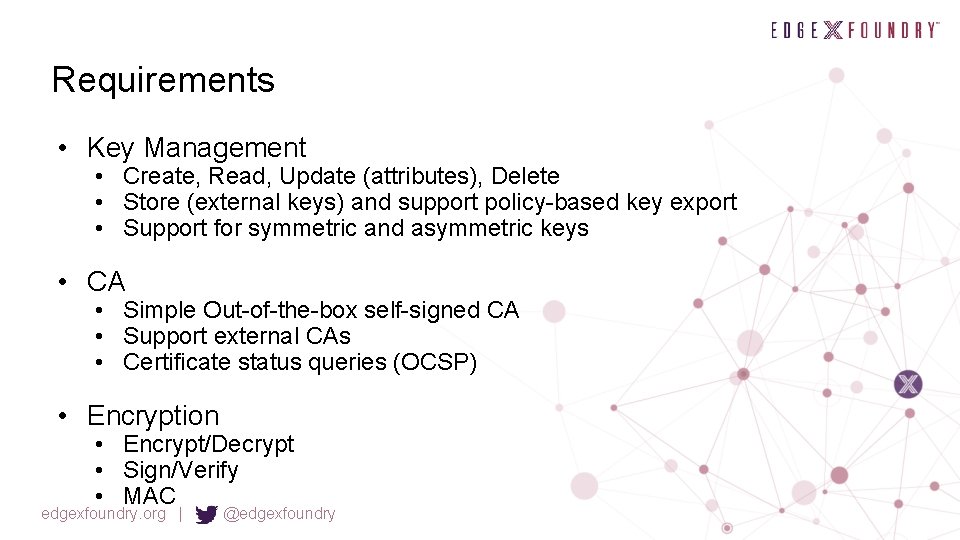
Requirements • Key Management • Create, Read, Update (attributes), Delete • Store (external keys) and support policy-based key export • Support for symmetric and asymmetric keys • CA • Simple Out-of-the-box self-signed CA • Support external CAs • Certificate status queries (OCSP) • Encryption • Encrypt/Decrypt • Sign/Verify • MAC edgexfoundry. org | @edgexfoundry
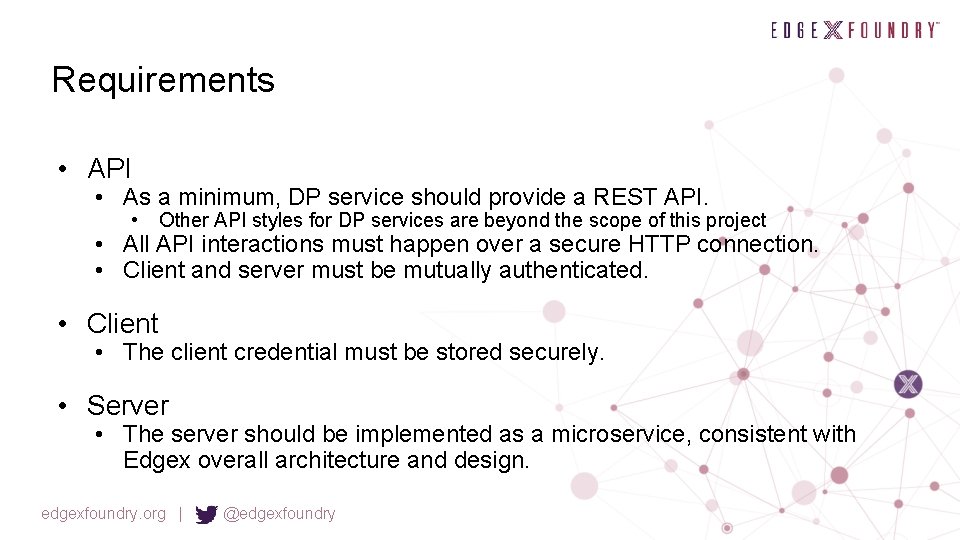
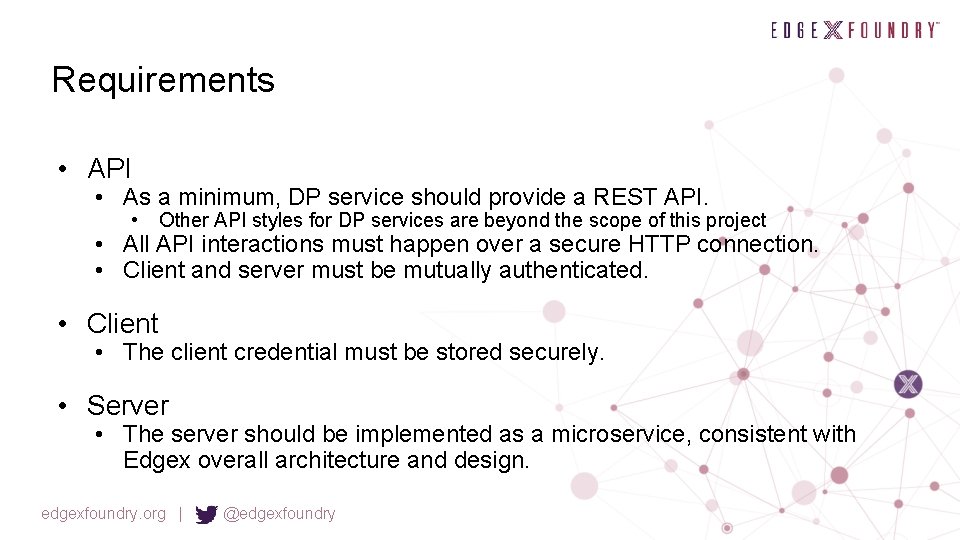
Requirements • API • As a minimum, DP service should provide a REST API. • Other API styles for DP services are beyond the scope of this project • All API interactions must happen over a secure HTTP connection. • Client and server must be mutually authenticated. • Client • The client credential must be stored securely. • Server • The server should be implemented as a microservice, consistent with Edgex overall architecture and design. edgexfoundry. org | @edgexfoundry
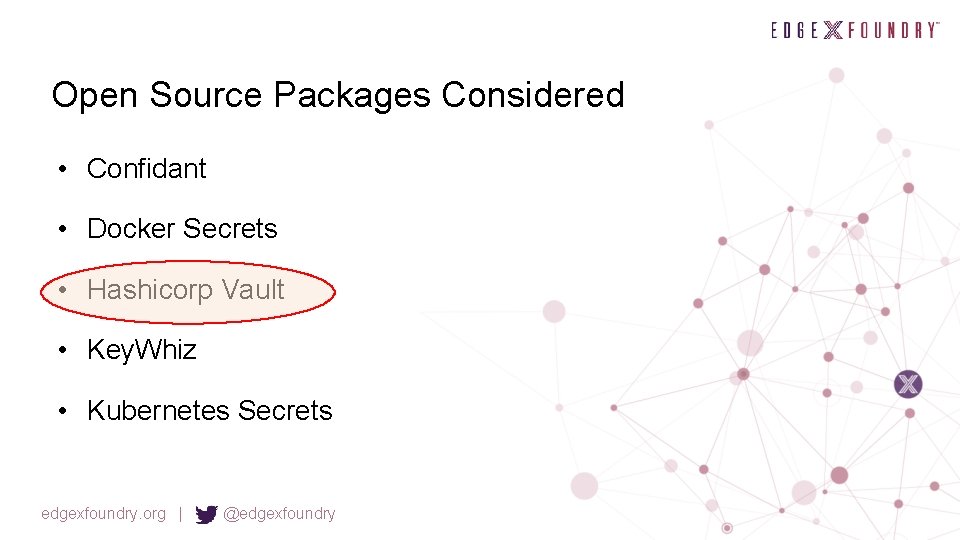
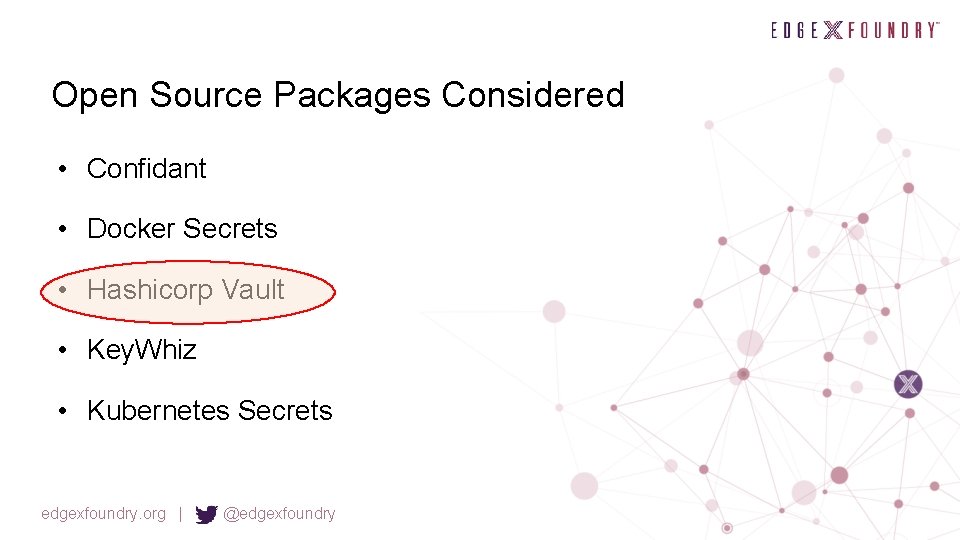
Open Source Packages Considered • Confidant • Docker Secrets • Hashicorp Vault • Key. Whiz • Kubernetes Secrets edgexfoundry. org | @edgexfoundry
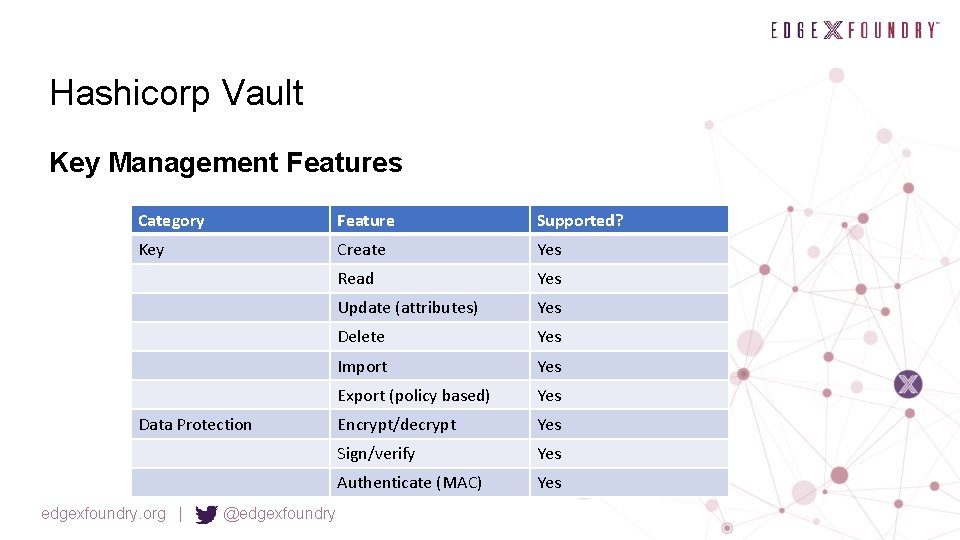
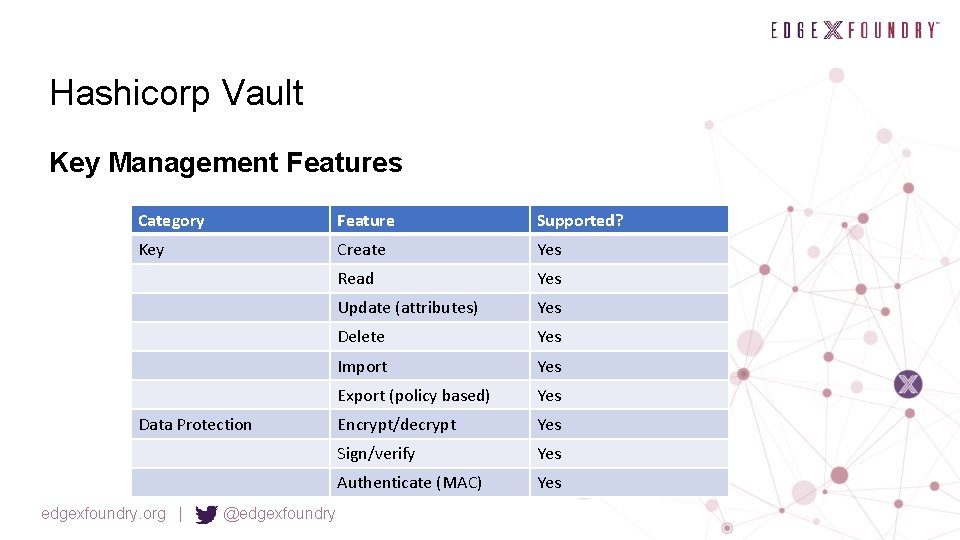
Hashicorp Vault Key Management Features Category Feature Supported? Key Create Yes Read Yes Update (attributes) Yes Delete Yes Import Yes Export (policy based) Yes Encrypt/decrypt Yes Sign/verify Yes Authenticate (MAC) Yes Data Protection edgexfoundry. org | @edgexfoundry
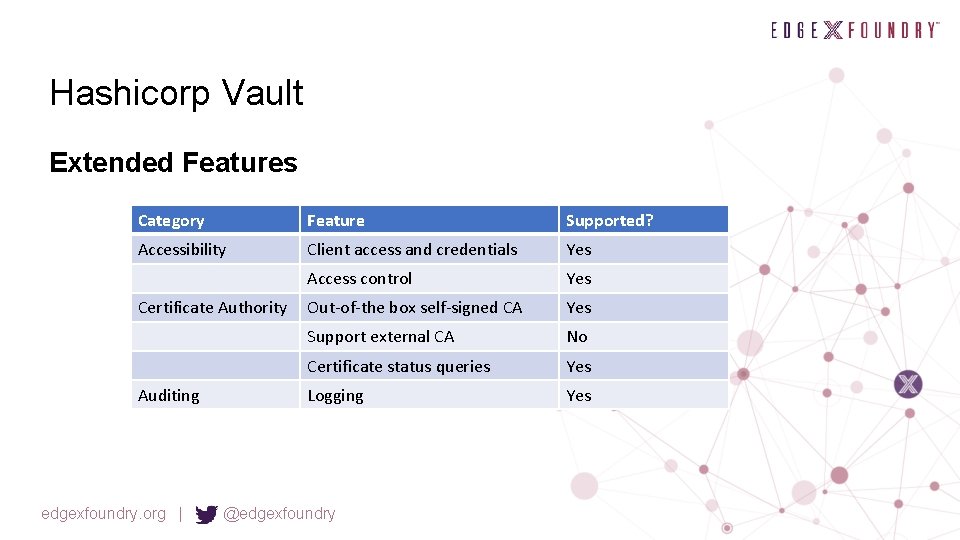
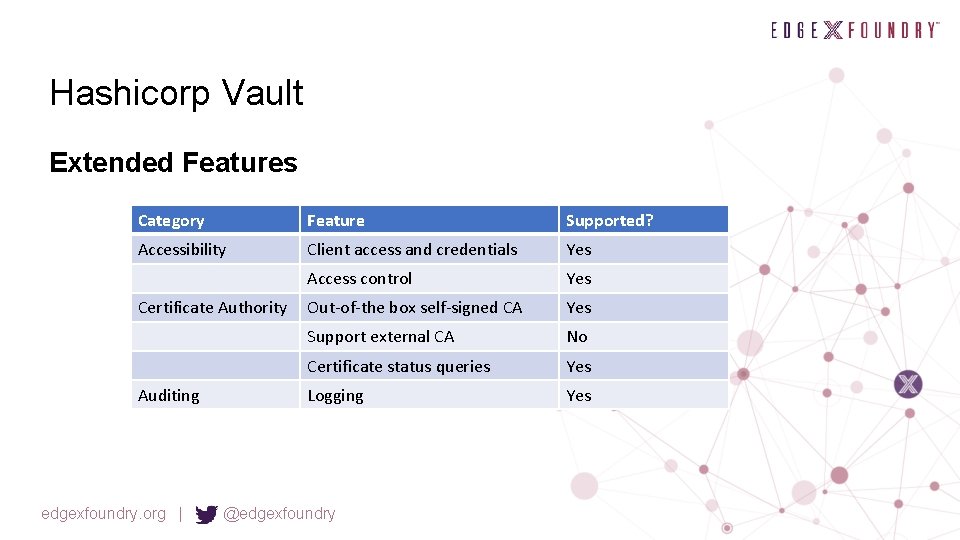
Hashicorp Vault Extended Features Category Feature Supported? Accessibility Client access and credentials Yes Access control Yes Out-of-the box self-signed CA Yes Support external CA No Certificate status queries Yes Logging Yes Certificate Authority Auditing edgexfoundry. org | @edgexfoundry
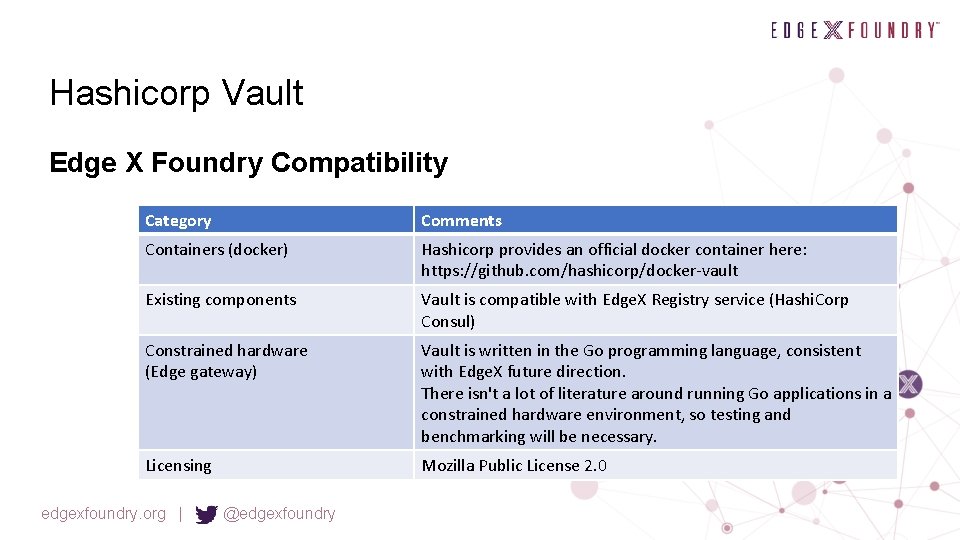
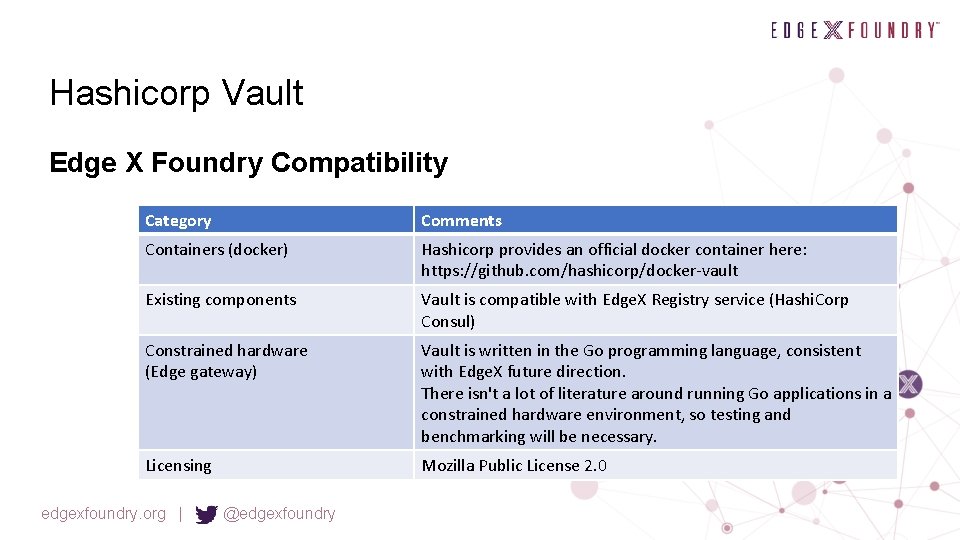
Hashicorp Vault Edge X Foundry Compatibility Category Comments Containers (docker) Hashicorp provides an official docker container here: https: //github. com/hashicorp/docker-vault Existing components Vault is compatible with Edge. X Registry service (Hashi. Corp Consul) Constrained hardware (Edge gateway) Vault is written in the Go programming language, consistent with Edge. X future direction. There isn't a lot of literature around running Go applications in a constrained hardware environment, so testing and benchmarking will be necessary. Licensing Mozilla Public License 2. 0 edgexfoundry. org | @edgexfoundry
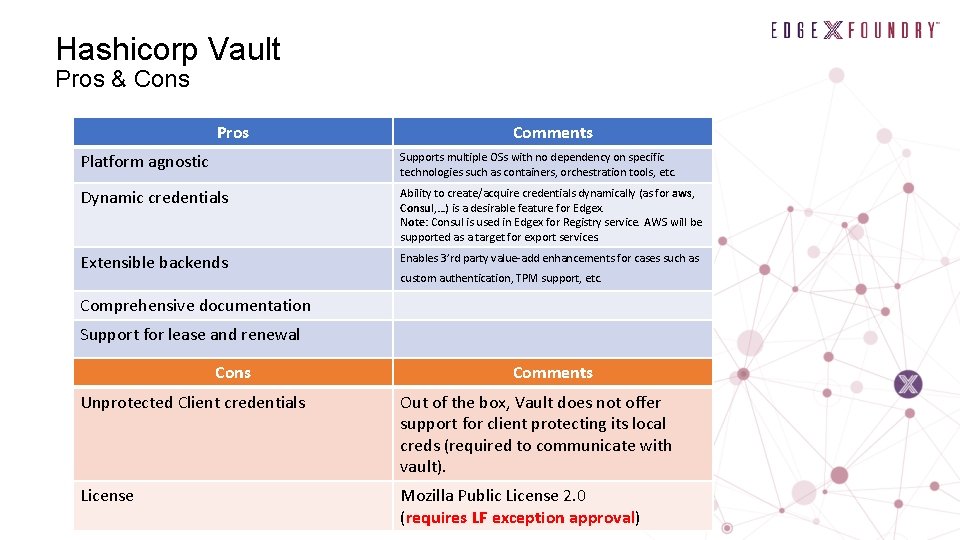
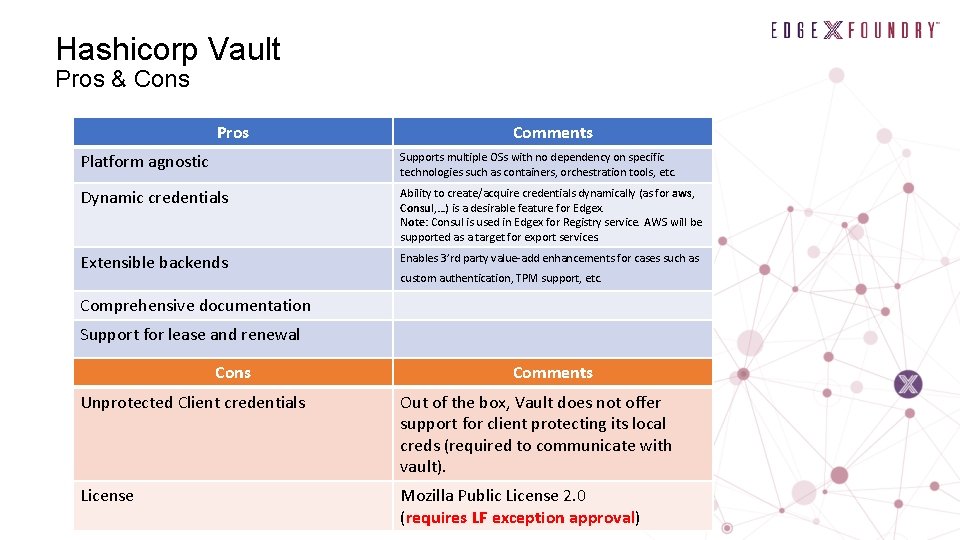
Hashicorp Vault Pros & Cons Pros Comments Platform agnostic Supports multiple OSs with no dependency on specific technologies such as containers, orchestration tools, etc. Dynamic credentials Ability to create/acquire credentials dynamically (as for aws, Consul, …) is a desirable feature for Edgex. Note: Consul is used in Edgex for Registry service. AWS will be supported as a target for export services. Extensible backends Enables 3’rd party value-add enhancements for cases such as custom authentication, TPM support, etc. Comprehensive documentation Support for lease and renewal Cons Comments Unprotected Client credentials Out of the box, Vault does not offer support for client protecting its local creds (required to communicate with vault). License Mozilla Public License 2. 0 (requires LF exception approval)

Potential Improvements Required • External CA support • Local crypto library • Bootstrap provisioning • Local secure store for bootstrap credentials • Unattended startup
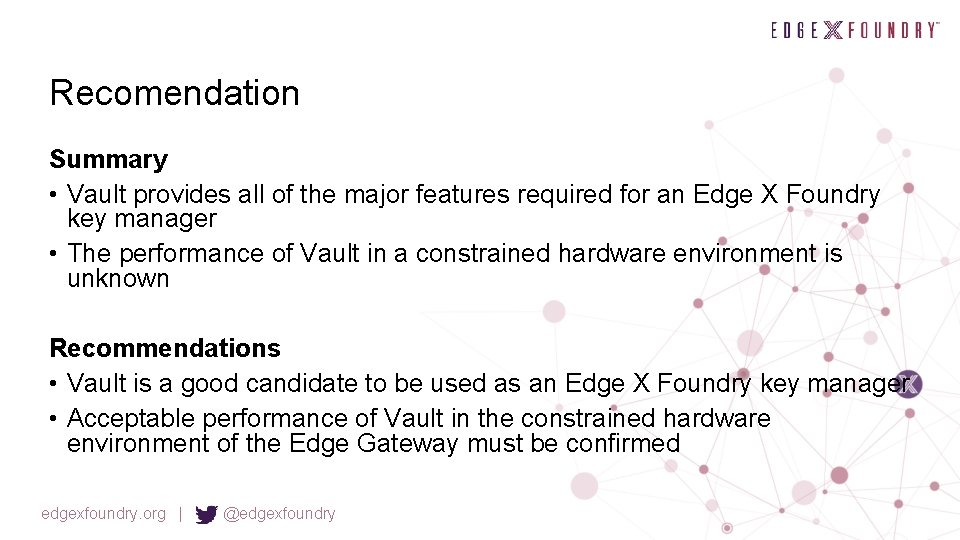
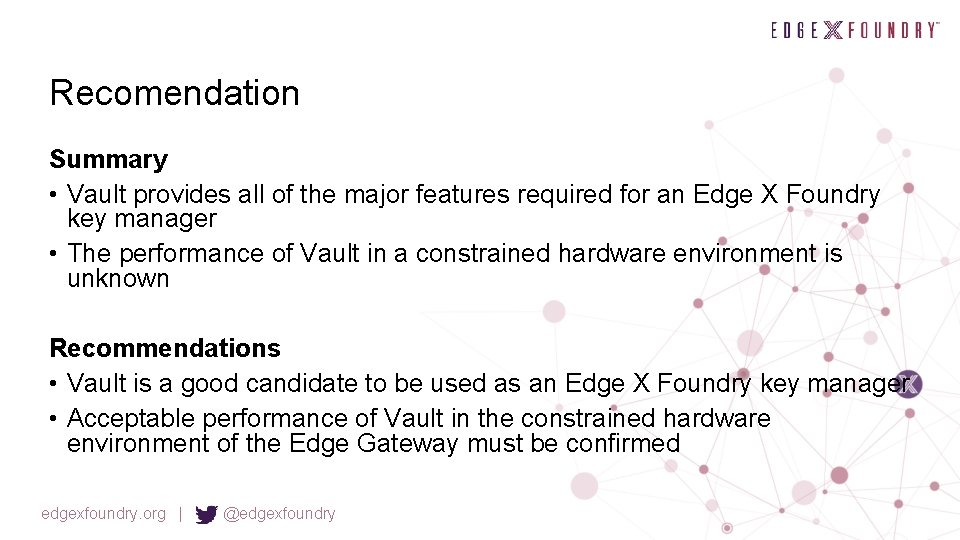
Recomendation Summary • Vault provides all of the major features required for an Edge X Foundry key manager • The performance of Vault in a constrained hardware environment is unknown Recommendations • Vault is a good candidate to be used as an Edge X Foundry key manager • Acceptable performance of Vault in the constrained hardware environment of the Edge Gateway must be confirmed edgexfoundry. org | @edgexfoundry
Questions • Do we need to provide local library for the client for local encryption services when server-slide encryption is not acceptable? • Alternatively, we only return the key to client, when allowed by policy, and client uses a library (ideally one recommended by Edgex) to perform encryption functions. edgexfoundry. org | @edgexfoundry
Open Questions • Keys • • Key Store and Retrieval is needed by other Edge. X microservices Create and update key attributes Register keys (import keys created outside of service) Should we allow all keys or only certain keys to be passed out to other microservices? • How and what are the usage cases? • CA • Internal CA (simple out of the box implementation) [ Step 1] • External CA (provide the ability to connect to Ext CA via same API) [Step 2] • Certificate status queries via OCSP • Encrypt/Signing Services • • As part of key mgmt svc or a separate service Encrypt/Decrypt MAC Sign/Verify
Key Management API Next Steps • Riaz is building a matrix of features and functionality for Key Management options. • Target matrix date is last week of Nov. edgexfoundry. org | @edgexfoundry
Internal Microservice Security Protocol (Priority #3) Edge. X Security High Level Function James White (Dell)/Steve Osselton (IOTech) • Next action – James and Steve to propose API post Barcelona release • Target to have this complete prior to January Face-to-Face • Internal Micro service Security Protocol • ? ? API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Priority #3 Implement an internal microservice communication security protocol Ou td ate d– • Several security APIs around service communications already exist • OMG’s DDS Security API (http: //www. omg. org/spec/DDS-SECURITY/1. 0/) • OWASP REST Security API (https: //www. owasp. org/index. php/REST_Security_Cheat_Sheet) • JWT (https: //jwt. io/introduction/) • Proposal #2 Ne eds • Allow two Edge. X/industry architects to provide a survey of the options and recommendation for implementation to the security WG • Again use the security implementation team to implement the APIs throughout Edge. X services for California • While not as high a priority, allow Edge. X security to be improved via some standard API set (not requiring wheel re -invention) • Allows Security Working Group to react/consider a design/architecture versus starting from scratch and work from requirements all the way to implementation • Help to Up • identify additional infrastructure needs • abstract the implementation to allow other future implementations • provide more secure services as a reference implementation edgexfoundry. org | @edgexfoundry dat e
Internal Microservice Security Protocol Next Steps • Jim White and Steve Osselton are building a matrix of tools, features and functionality. • Target matrix date is last week of Nov. edgexfoundry. org | @edgexfoundry
Other Priority Items Volunteer Please!! edgexfoundry. org | @edgexfoundry
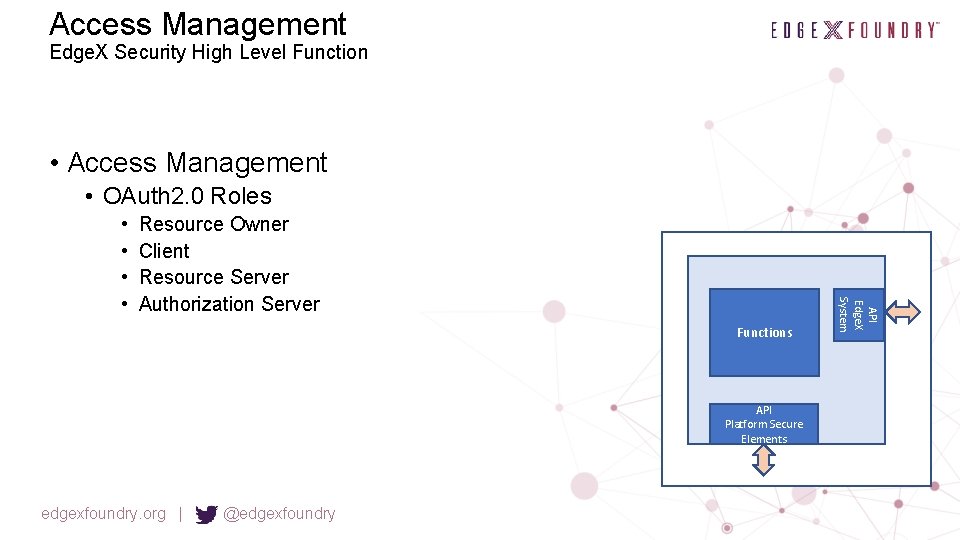
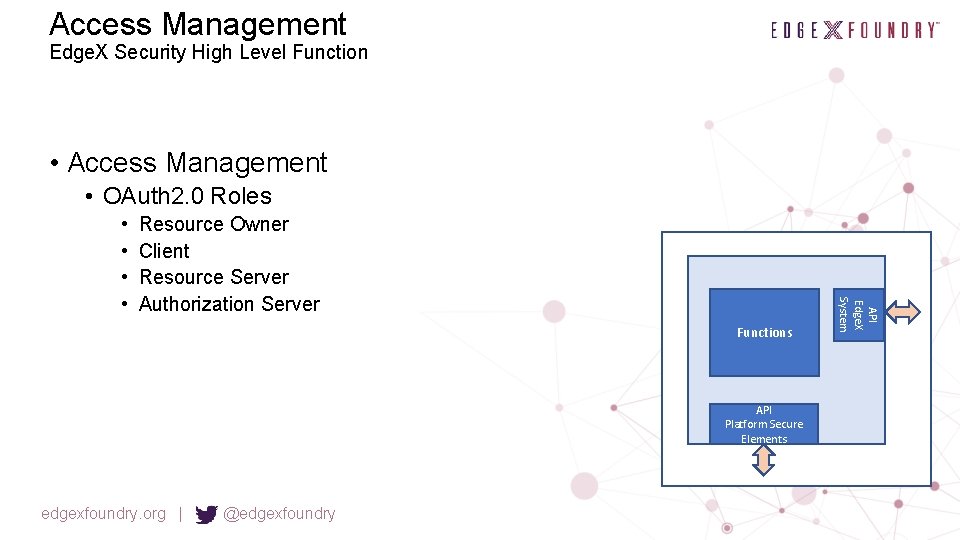
Access Management Edge. X Security High Level Function • Access Management • OAuth 2. 0 Roles Resource Owner Client Resource Server Authorization Server Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • •
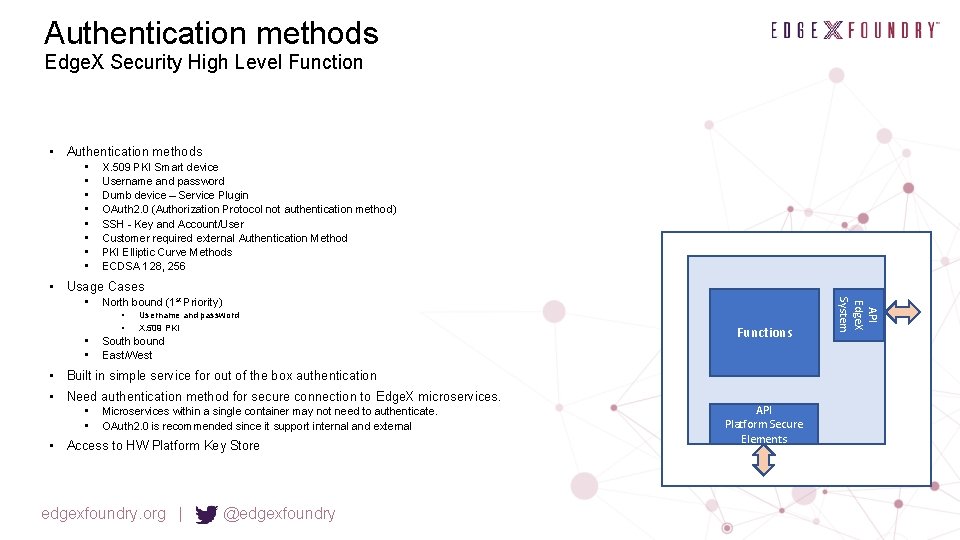
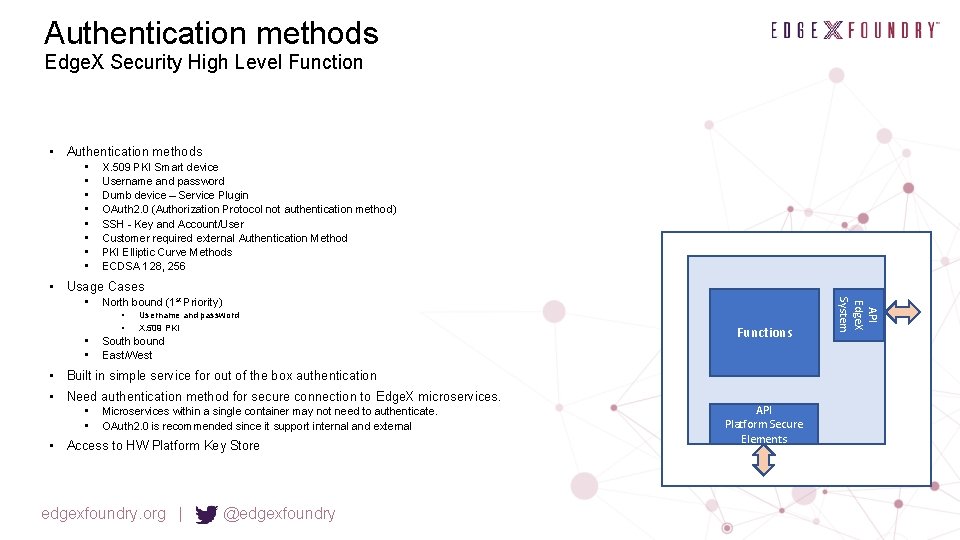
Authentication methods Edge. X Security High Level Function • Authentication methods • • X. 509 PKI Smart device Username and password Dumb device – Service Plugin OAuth 2. 0 (Authorization Protocol not authentication method) SSH - Key and Account/User Customer required external Authentication Method PKI Elliptic Curve Methods ECDSA 128, 256 • Usage Cases North bound (1 st Priority) • • Username and password X. 509 PKI South bound East/West Functions • Built in simple service for out of the box authentication • Need authentication method for secure connection to Edge. X microservices. • • Microservices within a single container may not need to authenticate. OAuth 2. 0 is recommended since it support internal and external • Access to HW Platform Key Store edgexfoundry. org | @edgexfoundry API Platform Secure Elements API Edge. X System •
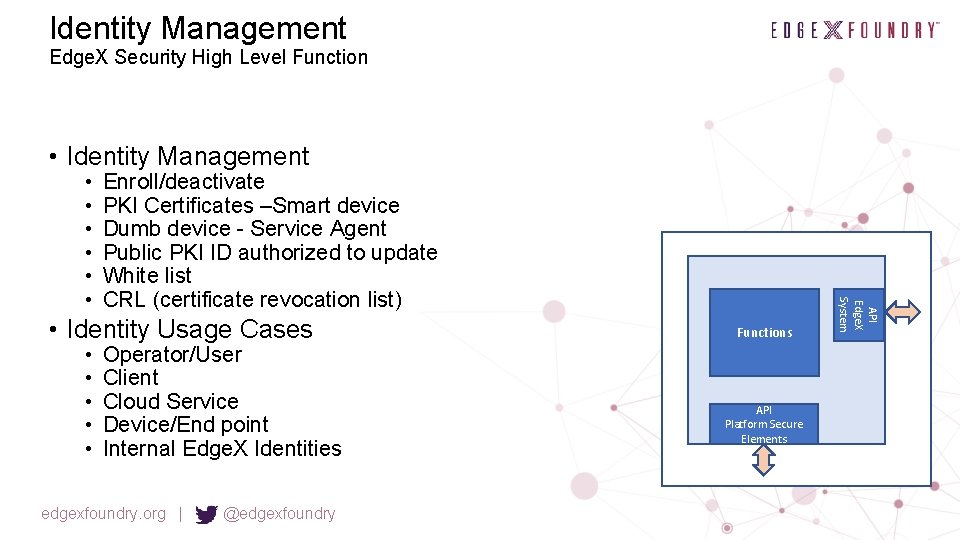
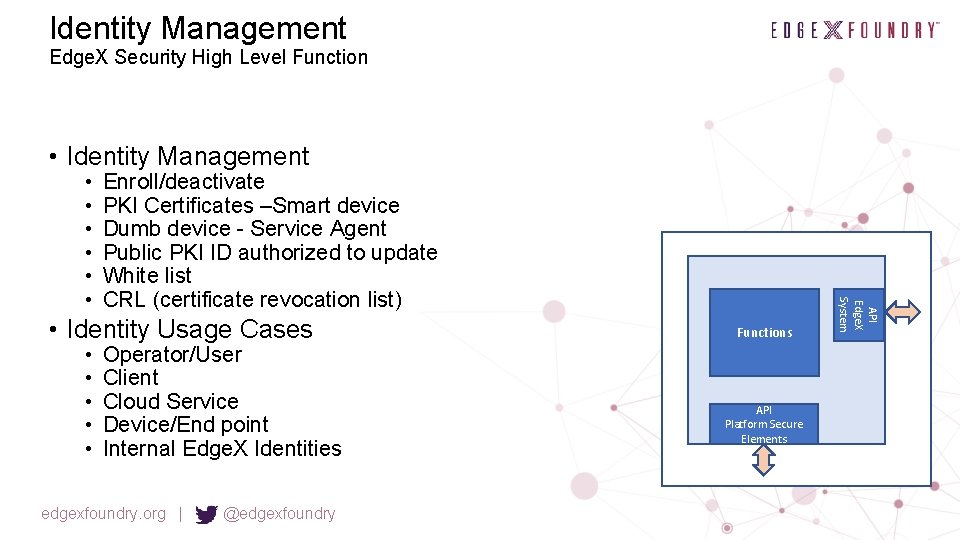
Identity Management Edge. X Security High Level Function • Identity Management Enroll/deactivate PKI Certificates –Smart device Dumb device - Service Agent Public PKI ID authorized to update White list CRL (certificate revocation list) • Identity Usage Cases • • • Operator/User Client Cloud Service Device/End point Internal Edge. X Identities edgexfoundry. org | @edgexfoundry Functions API Platform Secure Elements API Edge. X System • • •
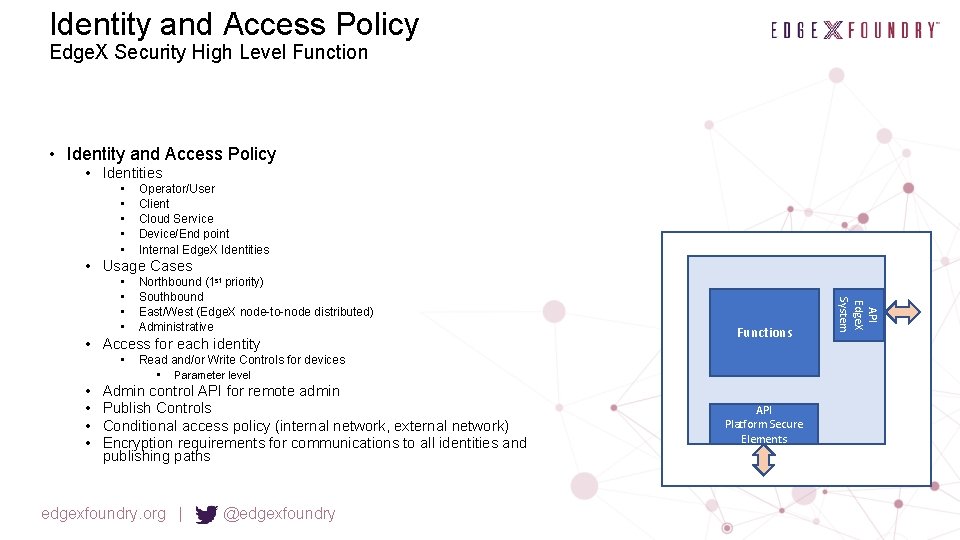
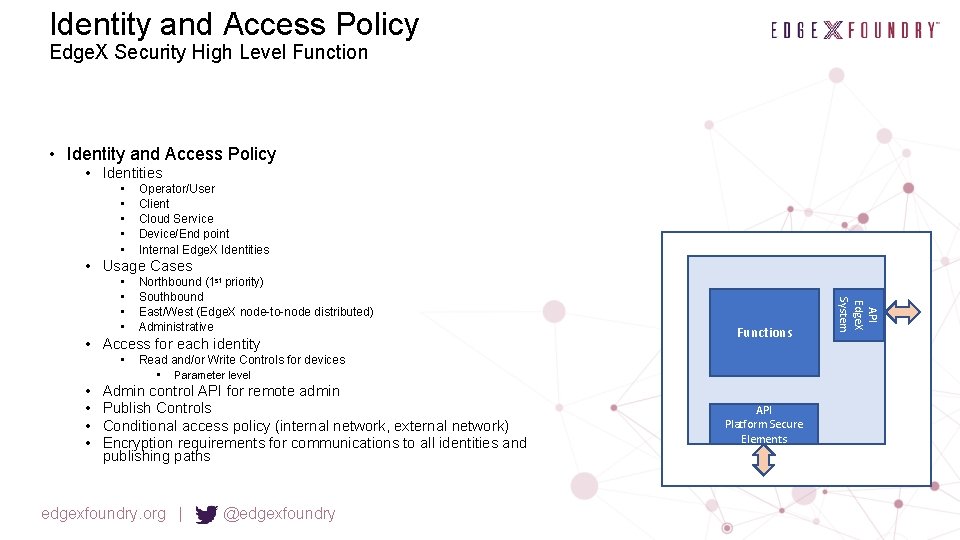
Identity and Access Policy Edge. X Security High Level Function • Identity and Access Policy • Identities • • • Operator/User Client Cloud Service Device/End point Internal Edge. X Identities • Usage Cases Northbound (1 st priority) Southbound East/West (Edge. X node-to-node distributed) Administrative • Access for each identity • • • Functions Read and/or Write Controls for devices • Parameter level Admin control API for remote admin Publish Controls Conditional access policy (internal network, external network) Encryption requirements for communications to all identities and publishing paths edgexfoundry. org | @edgexfoundry API Platform Secure Elements API Edge. X System • •
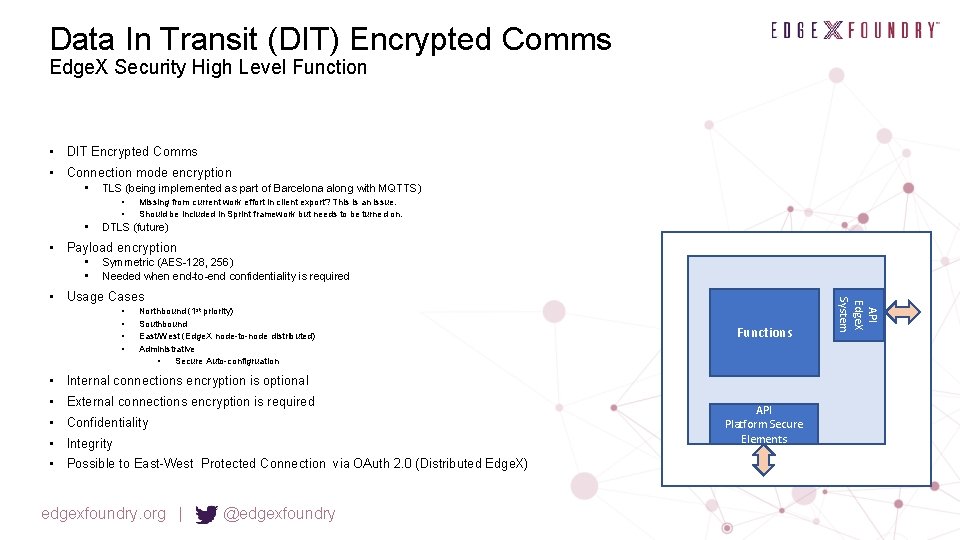
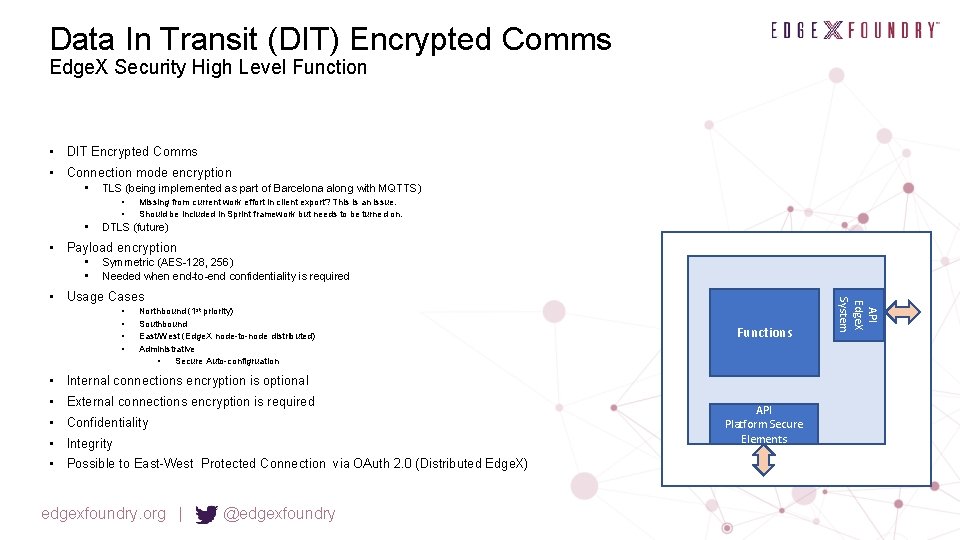
Data In Transit (DIT) Encrypted Comms Edge. X Security High Level Function • DIT Encrypted Comms • Connection mode encryption • TLS (being implemented as part of Barcelona along with MQTTS) • • • Missing from current work effort in client export? This is an issue. Should be included in Sprint framework but needs to be turned on. DTLS (future) • Payload encryption • • Symmetric (AES-128, 256) Needed when end-to-end confidentiality is required • • Northbound (1 st priority) Southbound East/West (Edge. X node-to-node distributed) Administrative • Secure Auto-configruation Functions • Internal connections encryption is optional • External connections encryption is required • Confidentiality • Integrity • Possible to East-West Protected Connection via OAuth 2. 0 (Distributed Edge. X) edgexfoundry. org | @edgexfoundry API Platform Secure Elements API Edge. X System • Usage Cases
DAR Encrypted Storage Edge. X Security High Level Function • Northbound (1 st priority) • Southbound • East/West (Edge. X node-to-node distributed) Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • DAR Encrypted Storage • Confidentiality • Integrity • Usage Cases
Data At Rest (DAR) Policy Edge. X Security High Level Function • DAR Policy • What to encrypt • Encryption method • Identity Usage Cases Operator/User Client Cloud Service Device/End point Internal Edge. X Identities edgexfoundry. org | @edgexfoundry Functions API Platform Secure Elements API Edge. X System • • •
Operational Security Policy Edge. X Security High Level Function • Operational Security Policy edgexfoundry. org | @edgexfoundry Functions API Platform Secure Elements API Edge. X System • Inbound Connection Manager Firewall Policy • DIT Policy • SW Update Management Policy • Audit Policy • Attestation Policy (gateway, southbound devices) • Secure Auto-config Policy
Software Update Management Edge. X Security High Level Function • Software Update Management • In Scope • Edge. X Microservices (internally or externally (OS)) • Edge. X can play an orchestration role for Platform under Edge. X (OS) when allowed. • South bound connected devices Functions • Method • Validation of update signature • PKI Certificates –Smart device • Dumb device - Service Agent edgexfoundry. org | @edgexfoundry API Platform Secure Elements API Edge. X System • Future
Security Monitoring Edge. X Security High Level Function • Security Monitoring Alerts Anomaly detection Intrusion detection Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • •
Audit Edge. X Security High Level Function • Audit • Log security events • Signing and anti-tamper protections API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Attestation Edge. X Security High Level Function • Attestation gateway • Measurement for chain of trust • Measurement of boot images • Measurement of control and configuration Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • Future Attestation southbound device
Chain of Trust Edge. X Security High Level Function • Chain of Trust • What so measure • How to measure • Attestation measurement signing API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Privacy Edge. X Security High Level Function • Privacy • Needs to be taken into consideration • Consumer • Health Care (HIPA) • EU Requirements API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
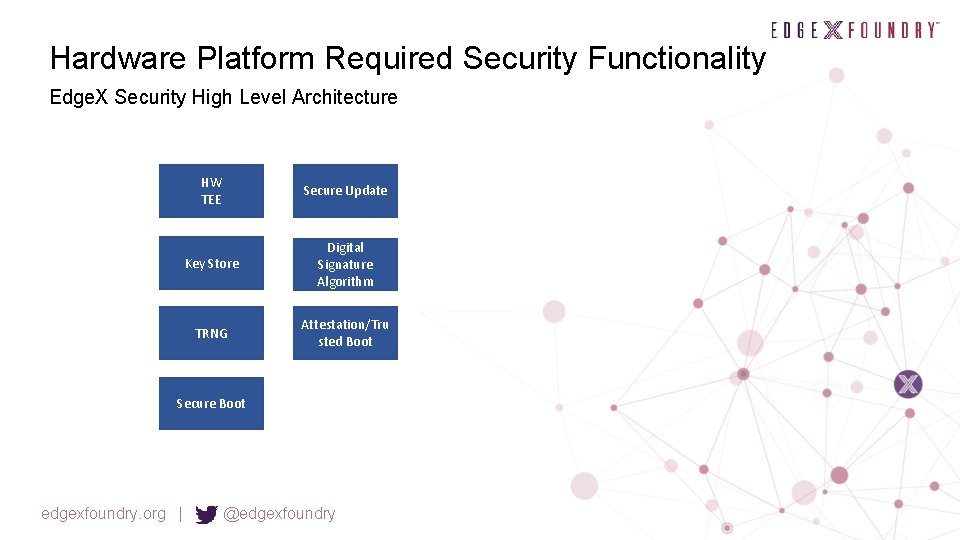
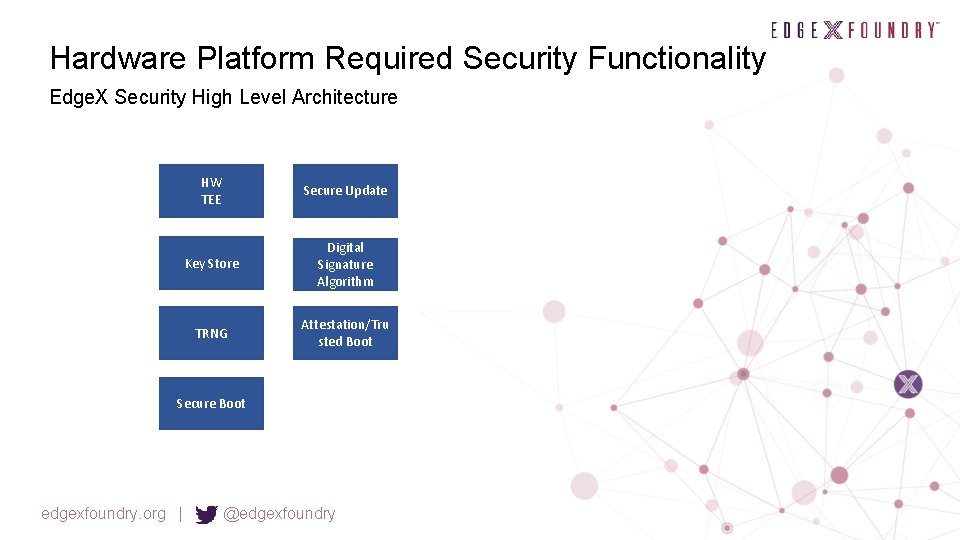
Hardware Platform Required Security Functionality Edge. X Security High Level Architecture HW TEE Secure Update Key Store Digital Signature Algorithm TRNG Attestation/Tru sted Boot Secure Boot edgexfoundry. org | @edgexfoundry
HW TEE (Trusted Execution Environment) Edge. X Security High Level Function • HW TEE (Trusted Execution Environment) • Required in platform to protect and isolate security sensitive values API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Key Store Edge. X Security High Level Function • Key Store • Required in platform to protect stored keys API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
RNG (Random Number Generator) Edge. X Security High Level Function • RNG (Random Number Generator) • TRNG (True Random Number Generator) • DRNG (Deterministic RNG) API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Secure Boot Edge. X Security High Level Function • Secure Boot Signature validation at each boot level Integrity checks at each boot level Connection into chain of trust in Edge. X System will only boot of integrity checks pass Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • •
Digital Signature Algorithm Edge. X Security High Level Function • Digital Signature Algorithm • ECDSA API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Attestation/Trusted Boot Edge. X Security High Level Function • Attestation • Measurement of each boot level • Connection into attestation in Edge. X • Trusted Boot Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • Measurement and reporting of attestation vector. System always boots.
Edge. X Security High Level Architecture Open Questions • Out of Scope - Provide guidance on how security features can/should be tested edgexfoundry. org | @edgexfoundry

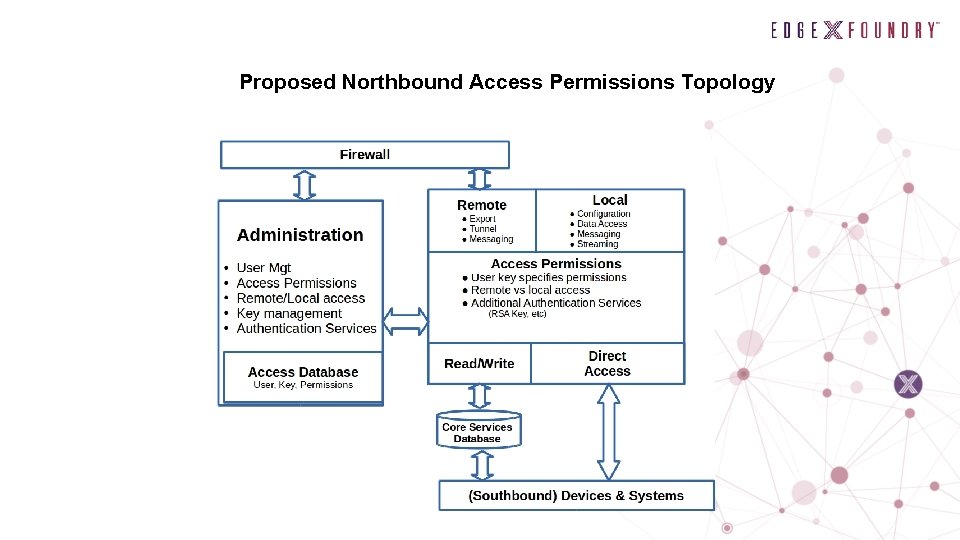
Proposed Northbound Security Objectives • Client, Distribution and Services Access ○ ○ • Administration & Permissions Management ○ ○ • Remote Administration Access Permission management interface Differentiation of local vs remote access ○ ○ • Parameter level read/write Streaming data permissions ( publish/subscribe) Clients & services operating “behind the firewall” Applications and services located on public Internet Flexibility ○ ○ ○ Enable companies to enforce internal security policies Flexible key management methods • Certificate Authority, PKI, Blockchain Flexible support of security and access technologies • PKI, SSL, OAuth
Edge. X Northbound Connection Example Use Case • • Edge. X Gateway Connection is initiated from Edge. X to Cloud Set up a mutually authenticated TLS connection using x. 509 methods Certificate Handling • Provisioning, renewal, • Use OS certificate store and services • Required to use export service to obtain a connection • Policy service • Who can talk to who, read, write, connection type • Initial settings of Edge. X to configure Cloud connection edgexfoundry. org | @edgexfoundry
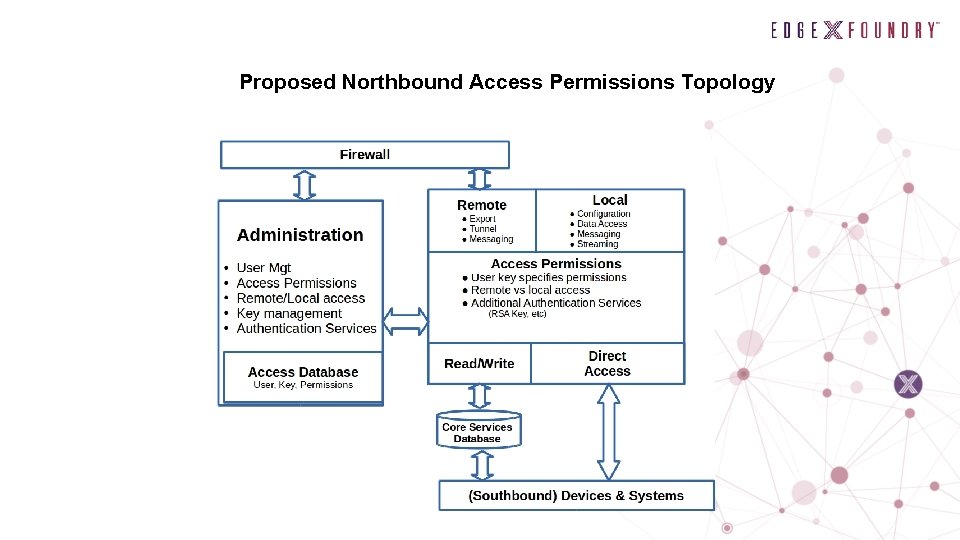
Proposed Northbound Access Permissions Topology
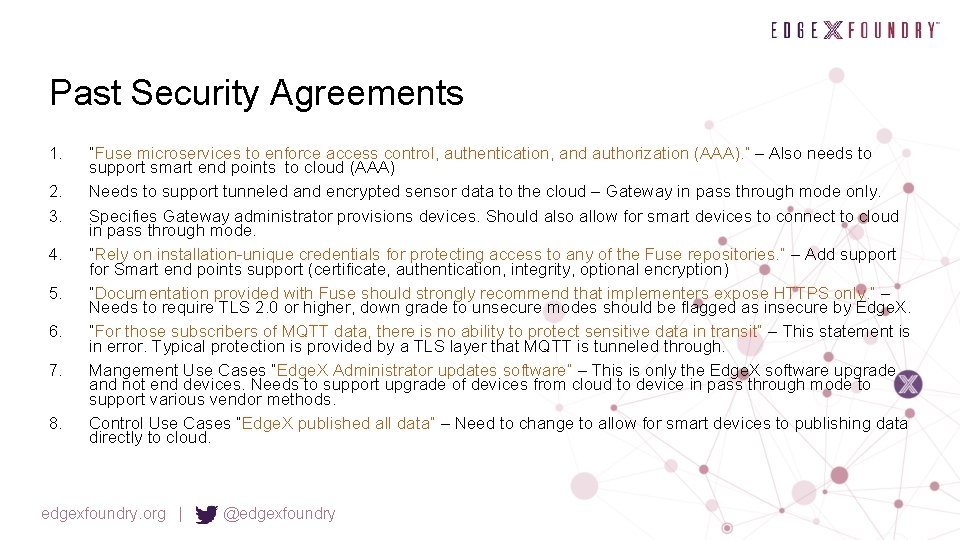
Past Security Agreements 1. 2. 3. 4. 5. 6. 7. 8. “Fuse microservices to enforce access control, authentication, and authorization (AAA). ” – Also needs to support smart end points to cloud (AAA) Needs to support tunneled and encrypted sensor data to the cloud – Gateway in pass through mode only. Specifies Gateway administrator provisions devices. Should also allow for smart devices to connect to cloud in pass through mode. “Rely on installation-unique credentials for protecting access to any of the Fuse repositories. ” – Add support for Smart end points support (certificate, authentication, integrity, optional encryption) “Documentation provided with Fuse should strongly recommend that implementers expose HTTPS only. ” – Needs to require TLS 2. 0 or higher, down grade to unsecure modes should be flagged as insecure by Edge. X. “For those subscribers of MQTT data, there is no ability to protect sensitive data in transit” – This statement is in error. Typical protection is provided by a TLS layer that MQTT is tunneled through. Mangement Use Cases “Edge. X Administrator updates software” – This is only the Edge. X software upgrade and not end devices. Needs to support upgrade of devices from cloud to device in pass through mode to support various vendor methods. Control Use Cases “Edge. X published all data” – Need to change to allow for smart devices to publishing data directly to cloud. edgexfoundry. org | @edgexfoundry