Security Working Group 2017 Oct 10 Weekly Meeting



![Managed Object • Name: UUID • Type: [connected device, microservice, edge system] • Properties Managed Object • Name: UUID • Type: [connected device, microservice, edge system] • Properties](https://slidetodoc.com/presentation_image_h/aeb578cc07dd0d414d467dff36697a19/image-25.jpg)




- Slides: 68

Security Working Group 2017 Oct 10 Weekly Meeting edgexfoundry. org | @edgexfoundry
2017 Oct 10 Security Working Group Meeting Agenda • Review of Security Updates Provided at Barcelona • Inbound Connection Manager Firewall (Priority #1) • Key Management API (Priority #2) • System Management • Inbound Connection Manager Firewall (Priority #1) • David Ferriera (Forge. Rock) update progress on definition of requirements and search for open source candidates • James White (Dell)/Steve Osselton (IOTech) Clean up and donation of Dell Fuse Security Service • Key Management API (Priority #2) • Riaz Zolfonoon (RSA) update progress definition of REST API • Internal container to container security API (Priority #3) • Starter-set of APIs to kick start Security API • James White/Steve Osselton • Next action – James and Steve to propose API post Barcelona release edgexfoundry. org | @edgexfoundry

Weekly Meeting edgexfoundry. org | @edgexfoundry
California Release – Near Term Security Goal • Protected communication (inbound and outbound) over the public internet on north bound interface • OAuth 2. 0 methods • PKI certificate methods • Mutually authenticated TLS • Key Management API • Inbound Connection Manager (Firewall) • Overall plan - Provide well defined API interfaces for security services with basic implementation right out of the box • Allow commercial partners to supply enhanced features and services using the same API interface with drop in replacements edgexfoundry. org | @edgexfoundry
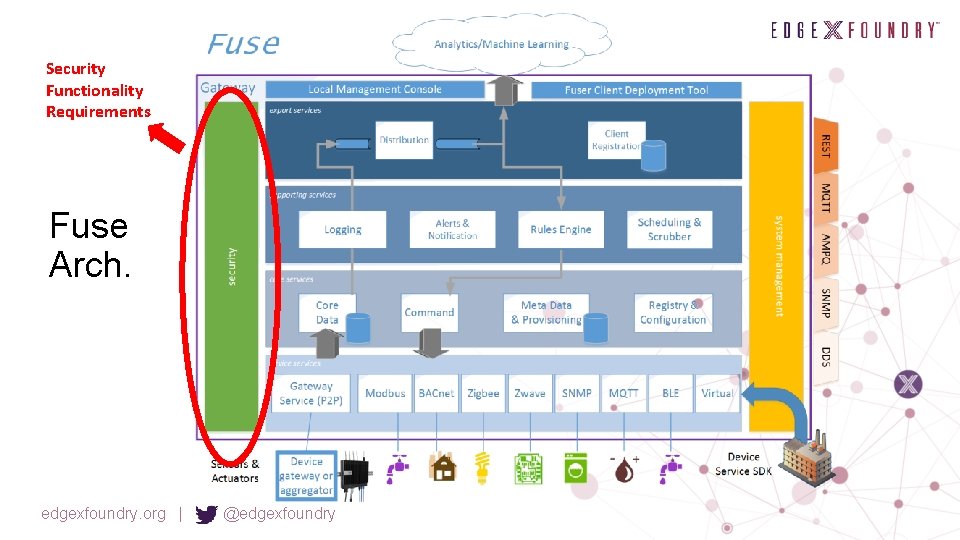
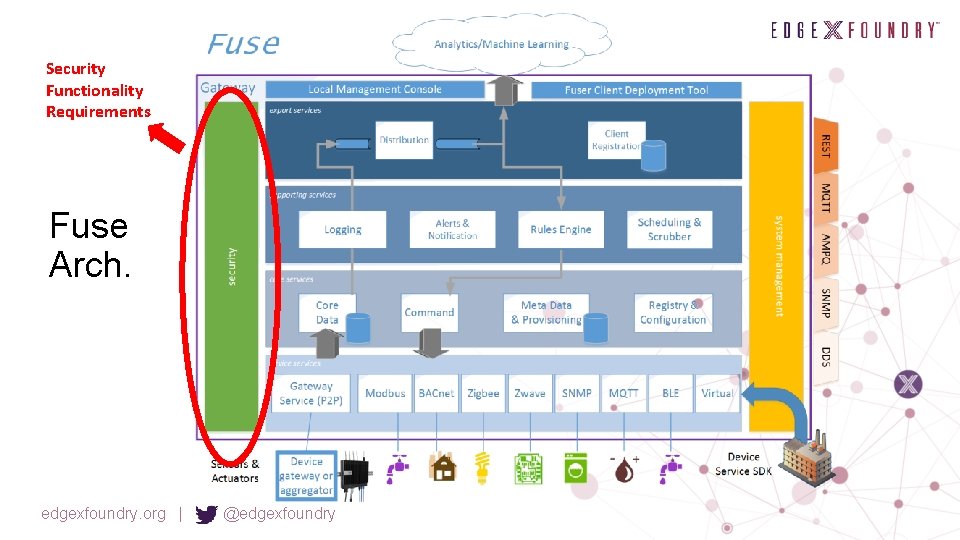
Security Functionality Requirements Fuse Arch. edgexfoundry. org | @edgexfoundry
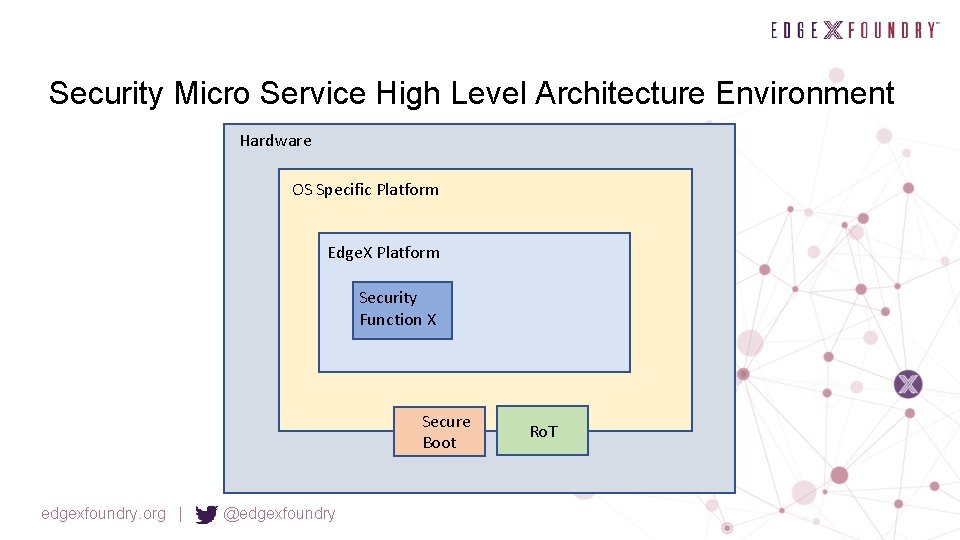
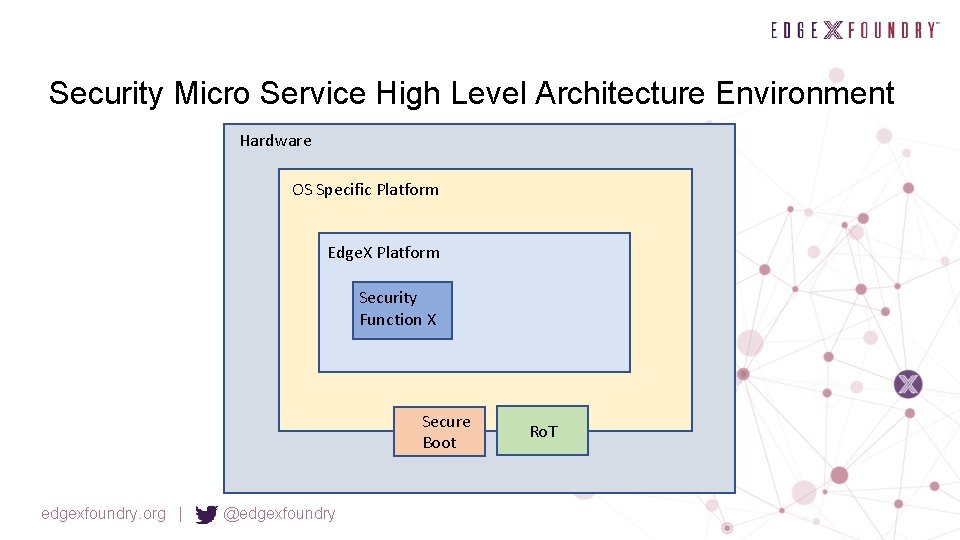
Security Micro Service High Level Architecture Environment Hardware OS Specific Platform Edge. X Platform Security Function X Secure Boot edgexfoundry. org | @edgexfoundry Ro. T
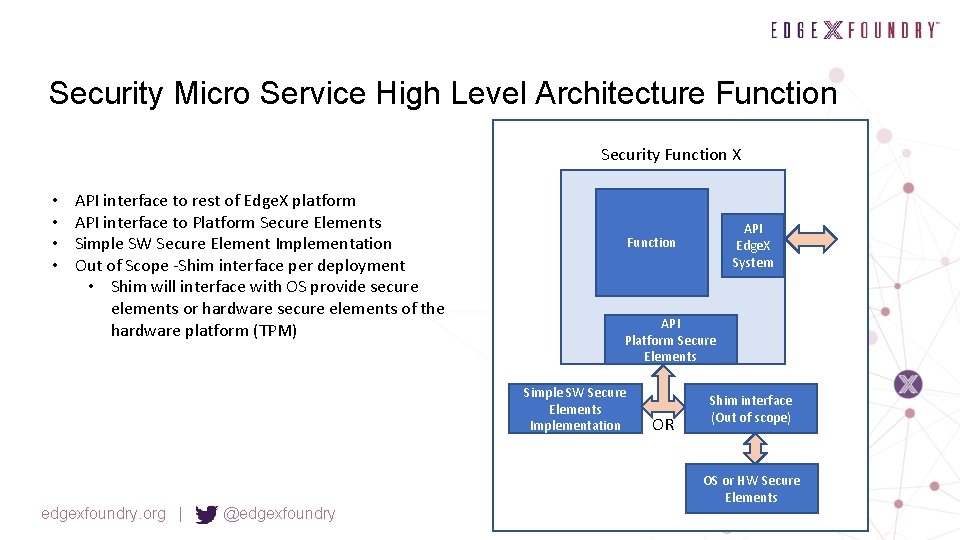
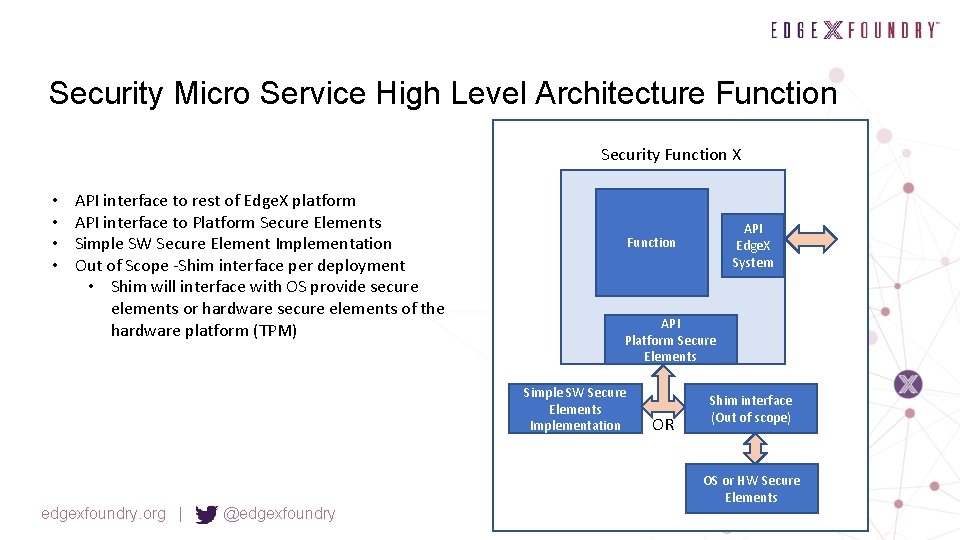
Security Micro Service High Level Architecture Function Security Function X • • API interface to rest of Edge. X platform API interface to Platform Secure Elements Simple SW Secure Element Implementation Out of Scope -Shim interface per deployment • Shim will interface with OS provide secure elements or hardware secure elements of the hardware platform (TPM) API Platform Secure Elements Simple SW Secure Elements Implementation edgexfoundry. org | @edgexfoundry API Edge. X System Function OR Shim interface (Out of scope) OS or HW Secure Elements
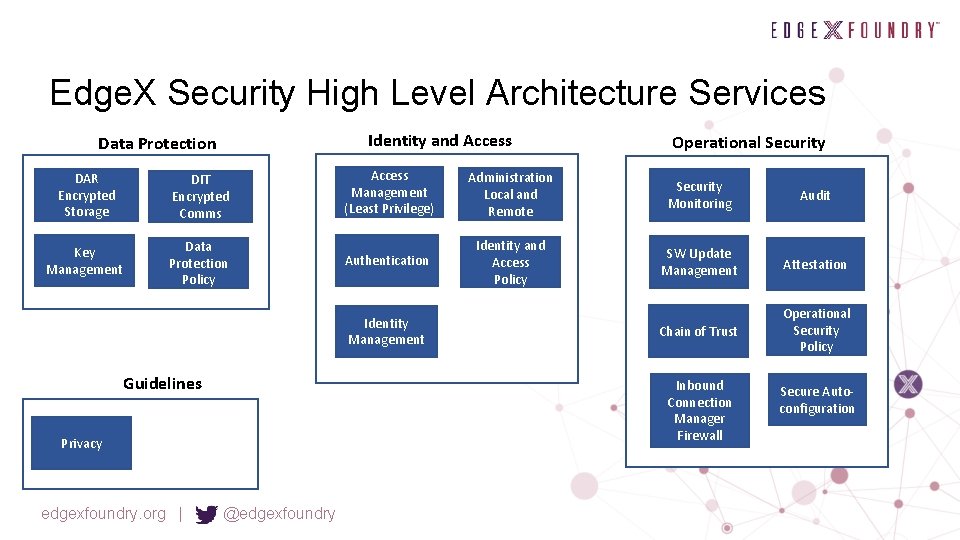
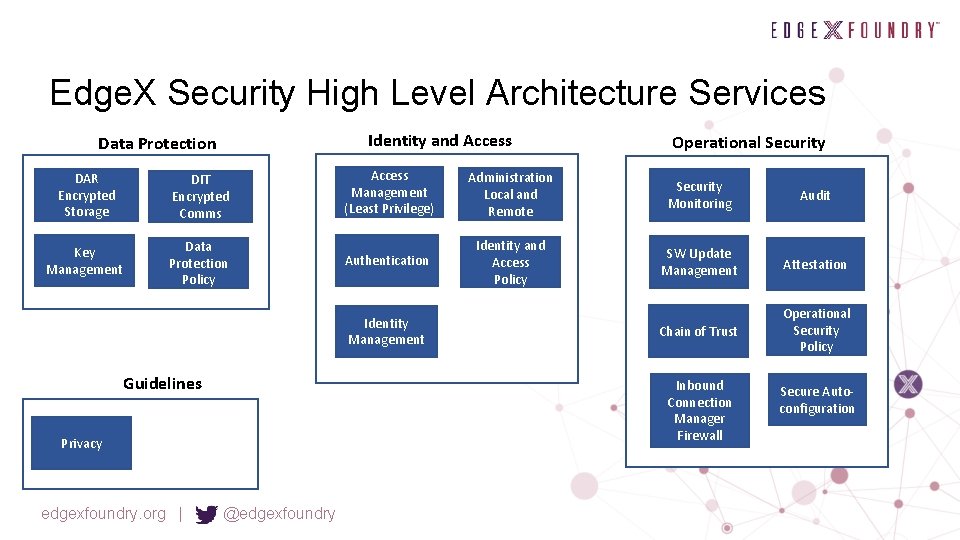
Edge. X Security High Level Architecture Services Identity and Access Data Protection DAR Encrypted Storage DIT Encrypted Comms Key Management Data Protection Policy Access Management (Least Privilege) Administration Local and Remote Security Monitoring Audit Authentication Identity and Access Policy SW Update Management Attestation Chain of Trust Operational Security Policy Identity Management Guidelines Inbound Connection Manager Firewall Privacy edgexfoundry. org | Operational Security @edgexfoundry Secure Autoconfiguration

Review Barcelona Security Discussion edgexfoundry. org | @edgexfoundry
API Proxy Security Working Group David Ferriera, Forgerock edgexfoundry. org | @edgexfoundry
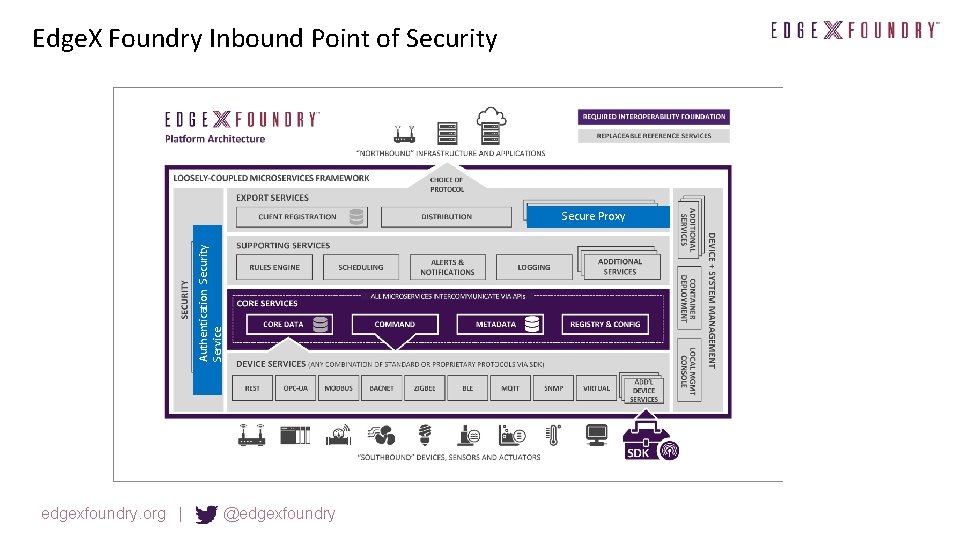
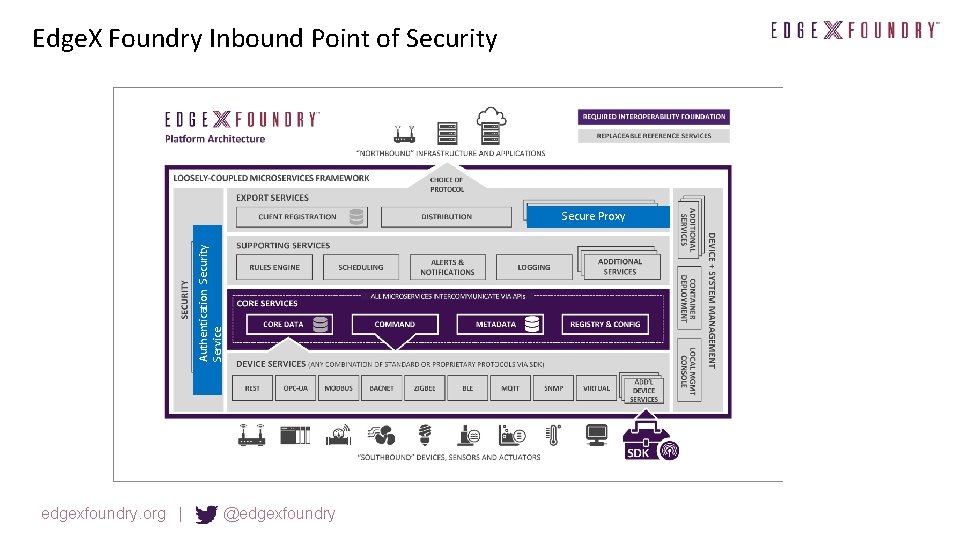
Edge. X Foundry Inbound Point of Security Authentication Security Service Secure Proxy edgexfoundry. org | @edgexfoundry
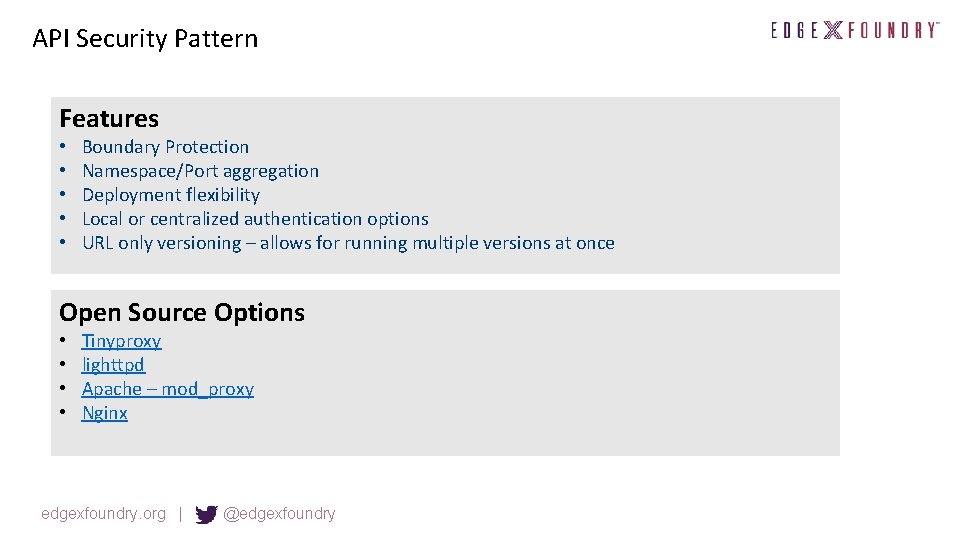
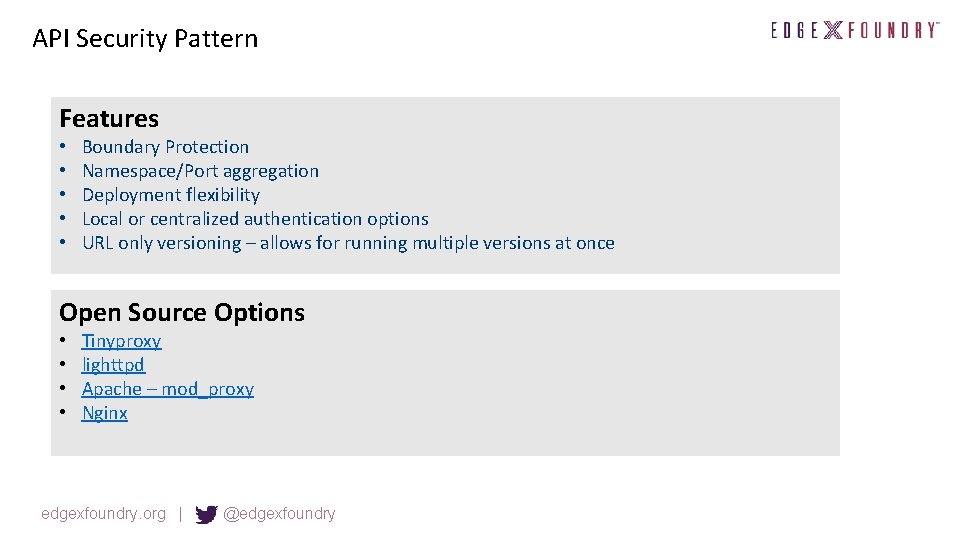
API Security Pattern Features • • • Boundary Protection Namespace/Port aggregation Deployment flexibility Local or centralized authentication options URL only versioning – allows for running multiple versions at once Open Source Options • • Tinyproxy lighttpd Apache – mod_proxy Nginx edgexfoundry. org | @edgexfoundry
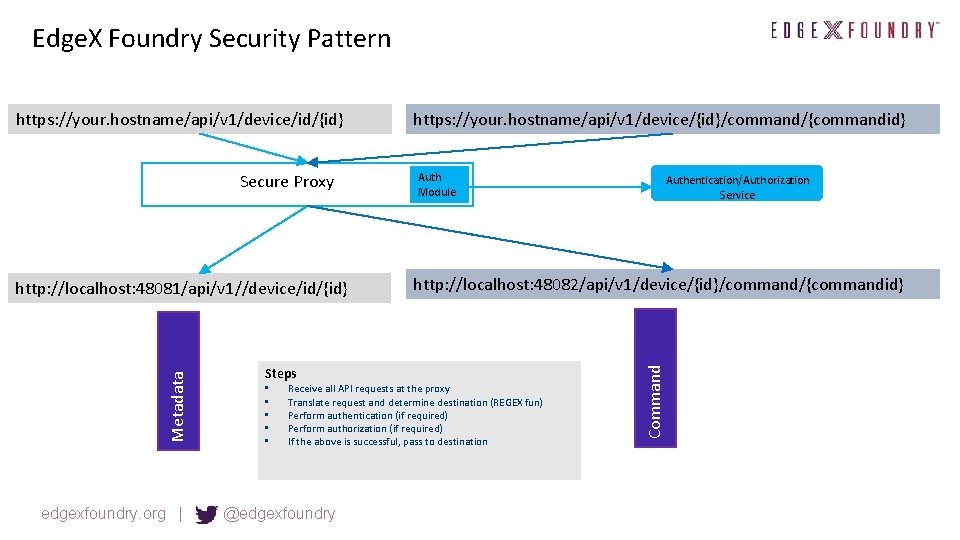
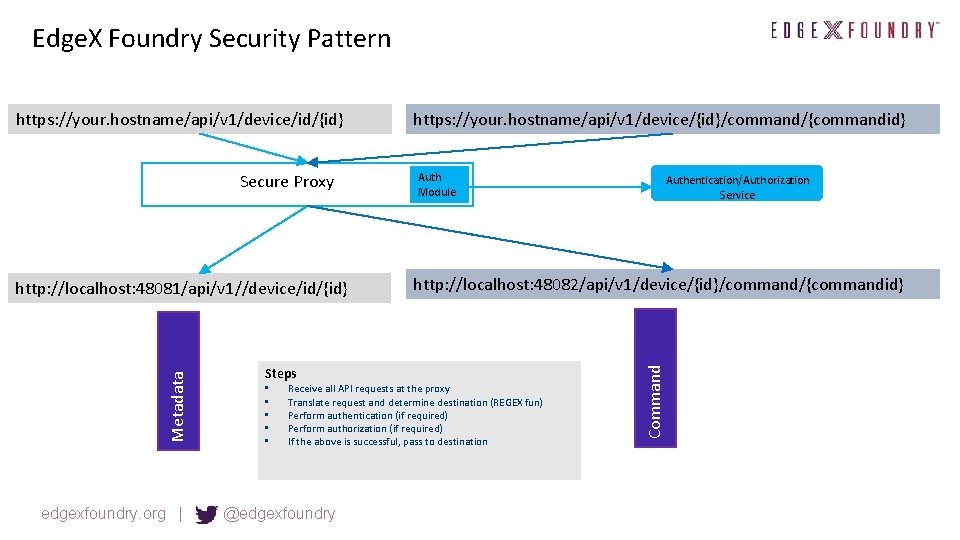
Edge. X Foundry Security Pattern Secure Proxy Metadata http: //localhost: 48081/api/v 1//device/id/{id} edgexfoundry. org | Steps • • • https: //your. hostname/api/v 1/device/{id}/command/{commandid} Auth Module http: //localhost: 48082/api/v 1/device/{id}/command/{commandid} Receive all API requests at the proxy Translate request and determine destination (REGEX fun) Perform authentication (if required) Perform authorization (if required) If the above is successful, pass to destination @edgexfoundry Authentication/Authorization Service Command https: //your. hostname/api/v 1/device/id/{id}
Key Manager API Discussion topics Riaz Zolfonoon (RSA)
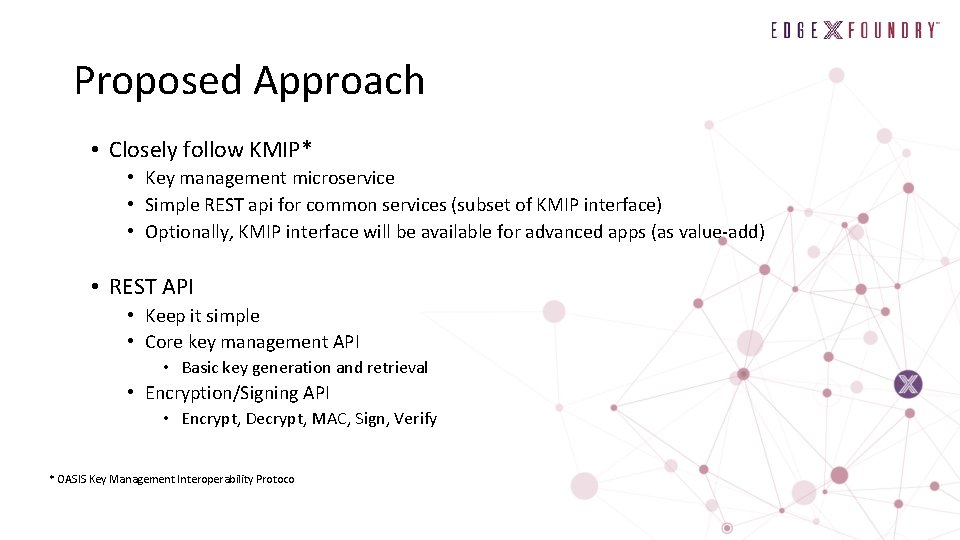
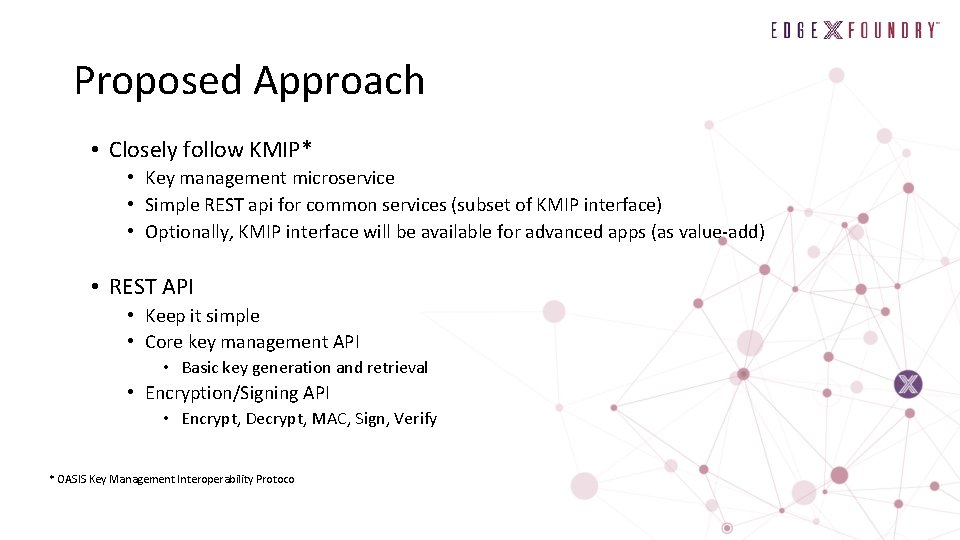
Proposed Approach • Closely follow KMIP* • Key management microservice • Simple REST api for common services (subset of KMIP interface) • Optionally, KMIP interface will be available for advanced apps (as value-add) • REST API • Keep it simple • Core key management API • Basic key generation and retrieval • Encryption/Signing API • Encrypt, Decrypt, MAC, Sign, Verify * OASIS Key Management Interoperability Protoco
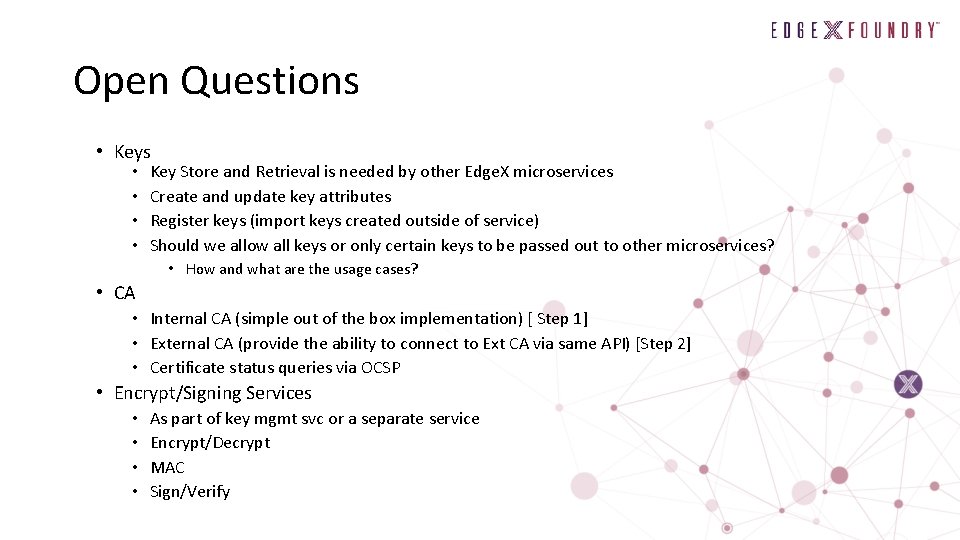
Key Management API • Core API • Keys • Create Symmetric Key • Create Asymmetric Key • Get Key • Delete/Shred Key • Secrets • Register Secret • Get Secret • Certificates • Register Certificate • Get Certificate • Secure Channel • TLS with mutual auth is required for all access to Key Mgmt Svc
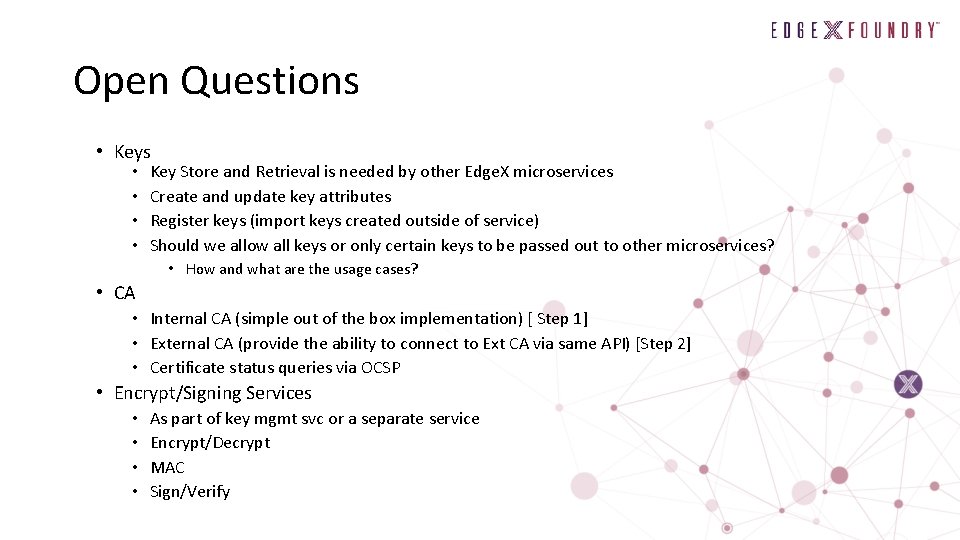
Open Questions • Keys • • Key Store and Retrieval is needed by other Edge. X microservices Create and update key attributes Register keys (import keys created outside of service) Should we allow all keys or only certain keys to be passed out to other microservices? • How and what are the usage cases? • CA • Internal CA (simple out of the box implementation) [ Step 1] • External CA (provide the ability to connect to Ext CA via same API) [Step 2] • Certificate status queries via OCSP • Encrypt/Signing Services • • As part of key mgmt svc or a separate service Encrypt/Decrypt MAC Sign/Verify
Edge. X System Management Salim Abi. Ezzi edgexfoundry. org | @edgexfoundry
Summary • Provision, monitor & manage an edge system with connected devices to insure its proper function. • Scale, security and reliability are key. • Facilitate ecosystem formation by defining common cross vendor building blocks.
Scope • Provisioning – Bootstrap – On board devices – Inventory • Infrastructure telemetry • Infrastructure notification/alerts • Configuration and software updates
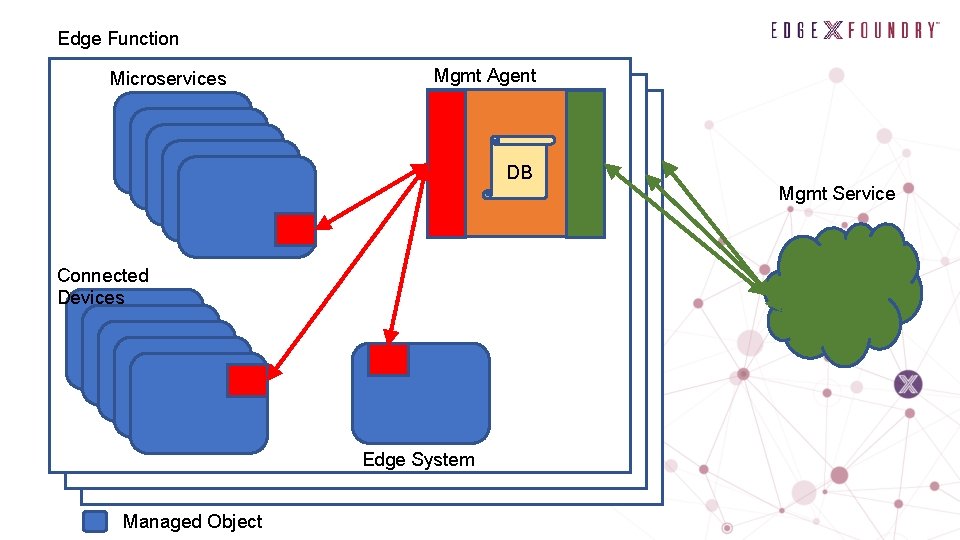
Topics • Edge system secure auto-configuration • Managed Objects • Mgmt Agent to Managed Object API • Mgmt Agent to Mgmt Service API
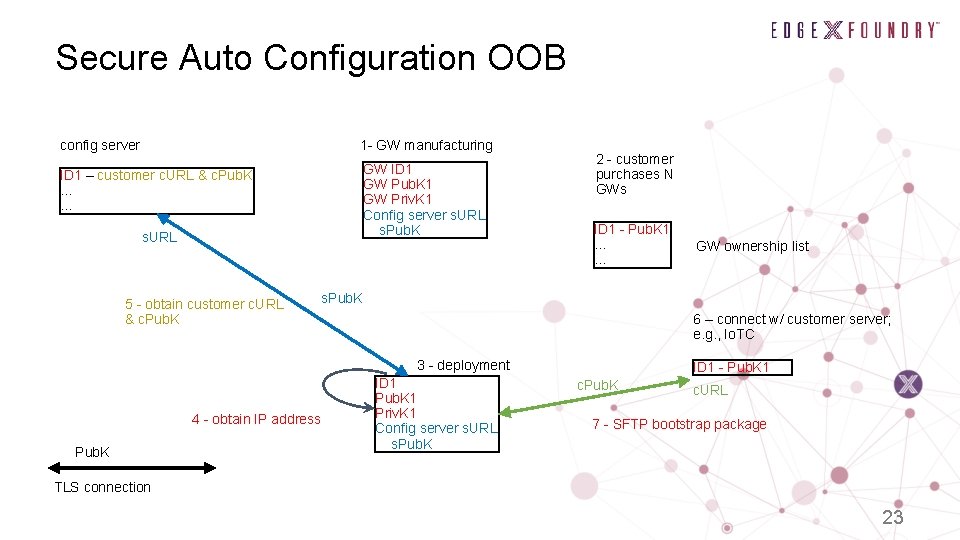
Secure Auto Configuration OOB • Edge devices have no UI console • Provisioning at large numbers while requiring manual steps is expensive • Opportunity for Edge. X to define steps for secure auto-config out of the box
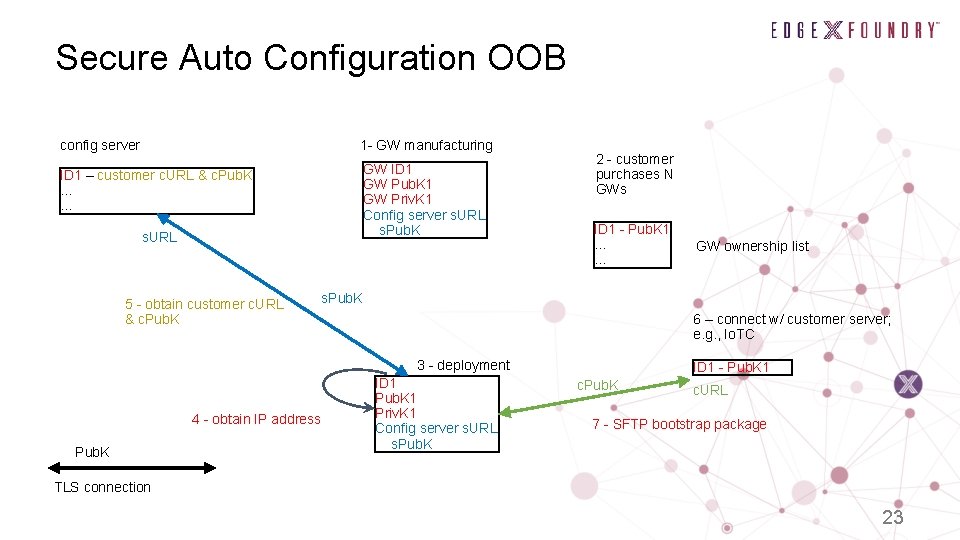
Secure Auto Configuration OOB config server 1 - GW manufacturing ID 1 – customer c. URL & c. Pub. K … … GW ID 1 GW Pub. K 1 GW Priv. K 1 Config server s. URL s. Pub. K s. URL 5 - obtain customer c. URL & c. Pub. K 2 - customer purchases N GWs ID 1 - Pub. K 1 … … s. Pub. K 6 – connect w/ customer server; e. g. , Io. TC 3 - deployment 4 - obtain IP address Pub. K GW ownership list ID 1 Pub. K 1 Priv. K 1 Config server s. URL s. Pub. K ID 1 - Pub. K 1 c. Pub. K c. URL 7 - SFTP bootstrap package TLS connection 23
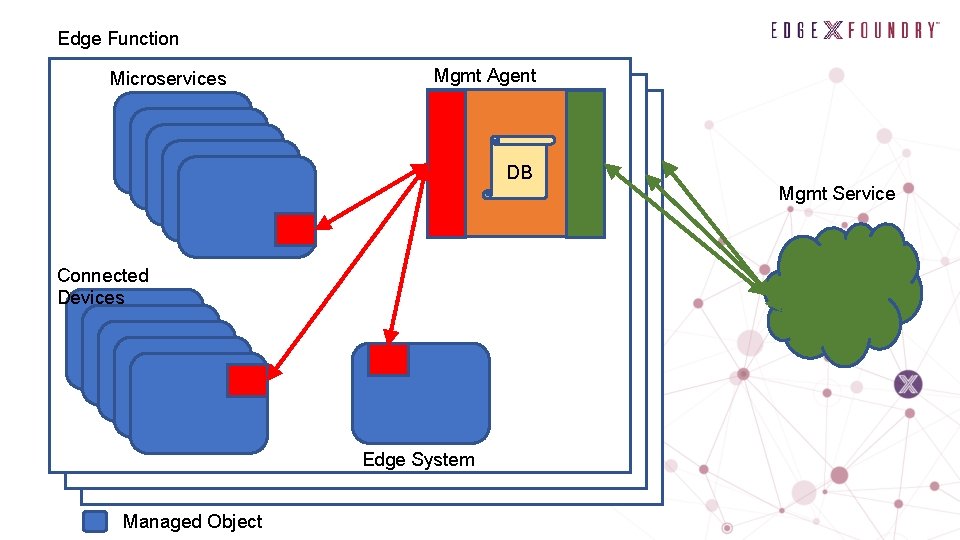
Edge Function Microservices Mgmt Agent DB Connected Devices Edge System Managed Object Mgmt Service
![Managed Object Name UUID Type connected device microservice edge system Properties Managed Object • Name: UUID • Type: [connected device, microservice, edge system] • Properties](https://slidetodoc.com/presentation_image_h/aeb578cc07dd0d414d467dff36697a19/image-25.jpg)
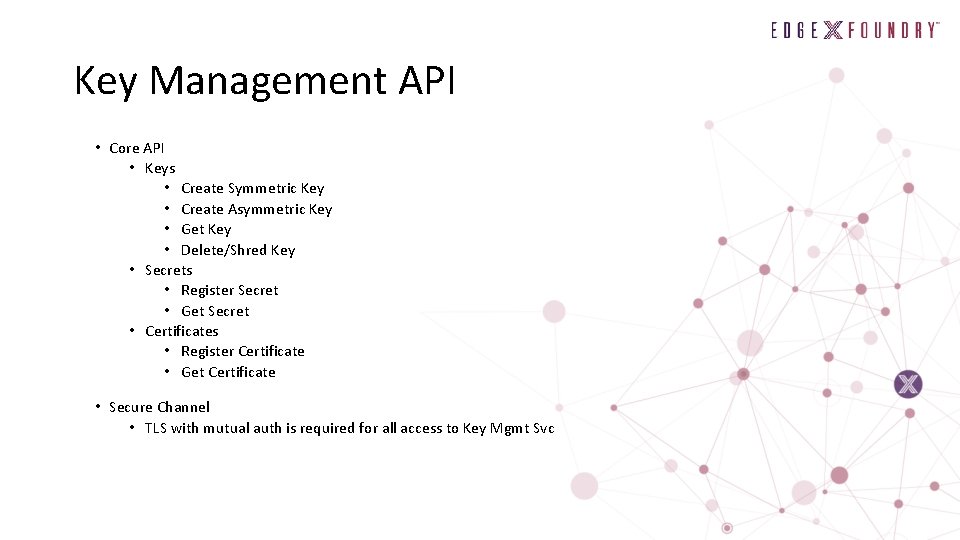
Managed Object • Name: UUID • Type: [connected device, microservice, edge system] • Properties as key-value pairs: [k 1=v 1, k 2=v 2, …] – e. g. : make, model, serial number, time in service • Metrics: [(name, units, interval, precision, accuracy, function. ID), …] • Actions: [(name, function. ID, [name: parameter type, …]), …] • Alerts: MO-UUID, metric name, value that caused alert
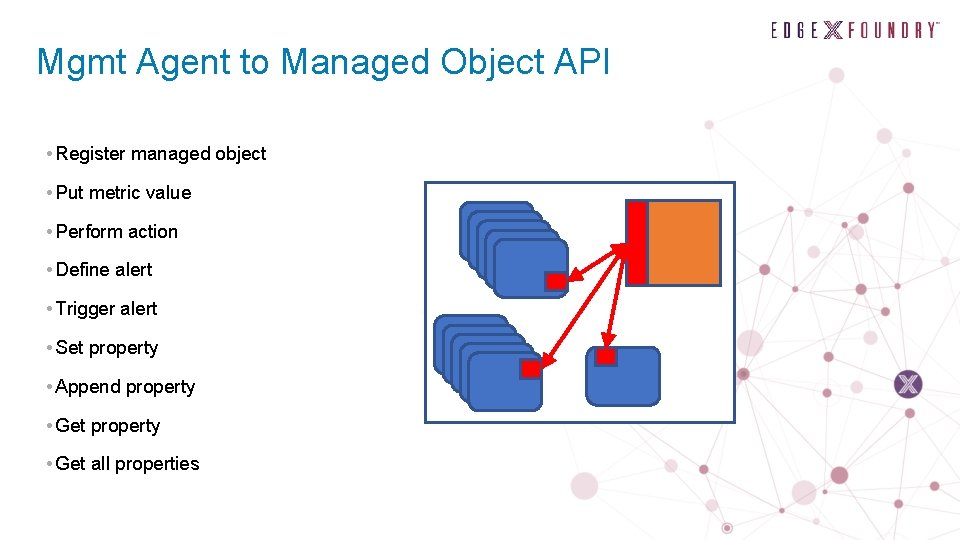
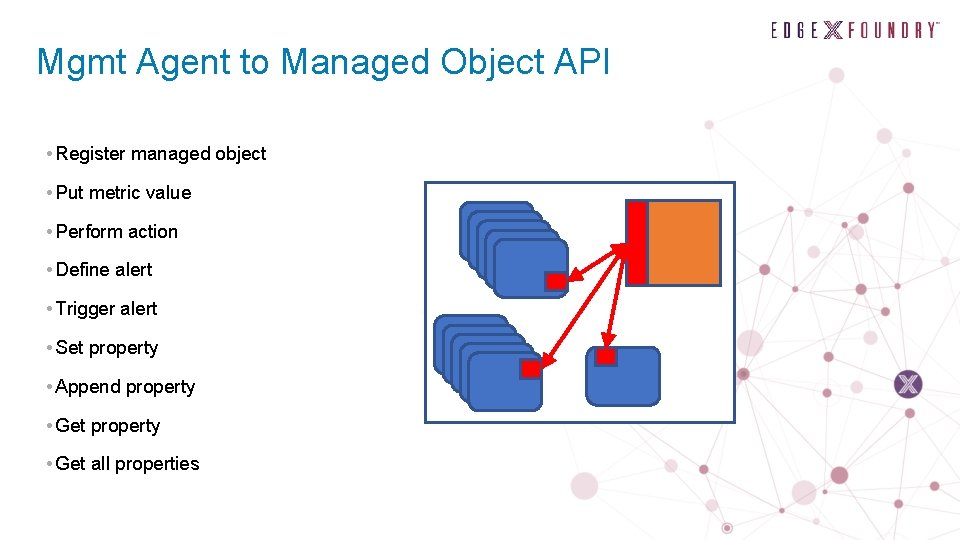
Mgmt Agent to Managed Object API • Register managed object • Put metric value • Perform action • Define alert • Trigger alert • Set property • Append property • Get all properties
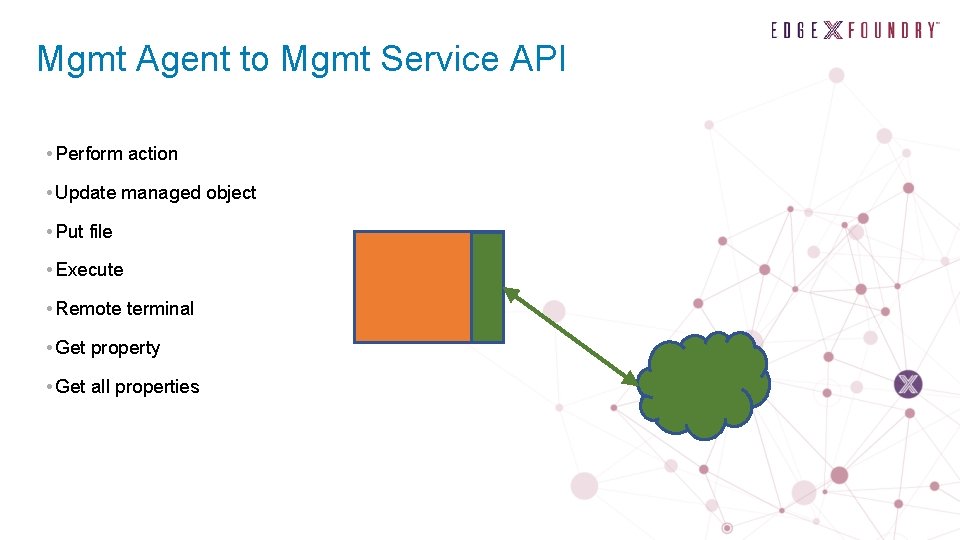
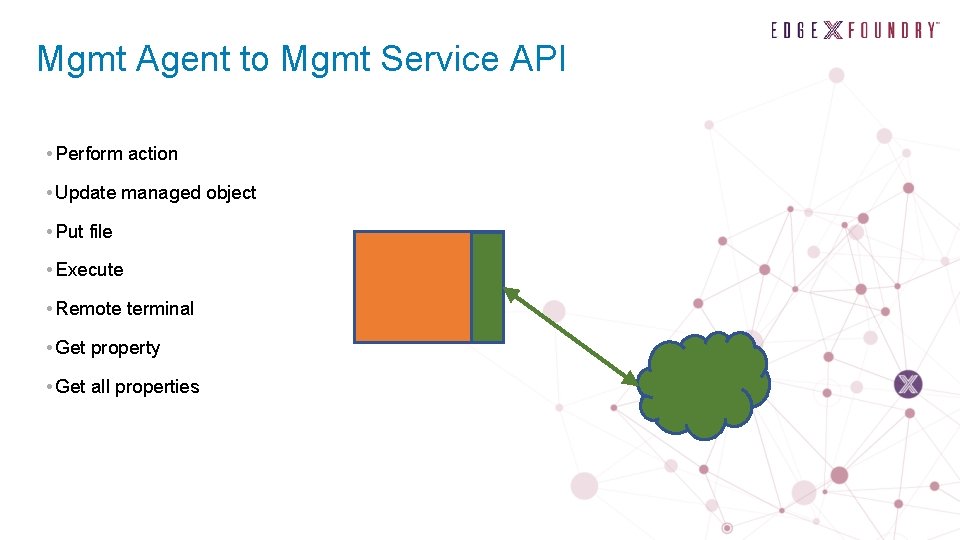
Mgmt Agent to Mgmt Service API • Perform action • Update managed object • Put file • Execute • Remote terminal • Get property • Get all properties
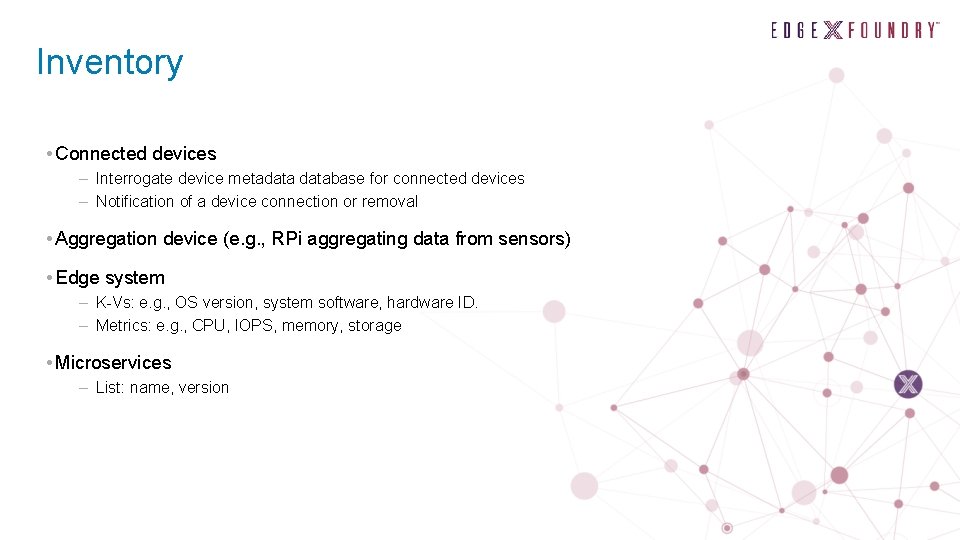
Inventory • Connected devices – Interrogate device metadatabase for connected devices – Notification of a device connection or removal • Aggregation device (e. g. , RPi aggregating data from sensors) • Edge system – K-Vs: e. g. , OS version, system software, hardware ID. – Metrics: e. g. , CPU, IOPS, memory, storage • Microservices – List: name, version
Examples • Heart beat as metric • Ping as action • Notification of battery charge, connection state • Notification of edge system compute resource concerns
Examples of Configuration through Actions • Firewall settings • NAT traversal • Change SSH port • Wifi passcode • Certificate revocation • Installing new certificate
Software Updates • Three types: 1. 2. 3. Microservices Connected devices Edge device OS • #1 is in scope • Is #2 in scope? • #3 is out of scope; however: – Could be orchestrated – Need to shut down microservices, apply update and resume – Update might require root privilege and/or a reboot
Power Management • Restart or shutdown – Might be required by system software updates • Remote restart or shutdown – E. g. , Wake on LAN • Energy saving
Edge. X for Fog Computing • Using Edge. X microservices on multi computing tiers between [edge and cloud[ • East-west communication • Failover • Load balancing • Kubernetes for orchestration
Application Lifecycle Management

Role Based Access Control

End Review of Barcelona

Inbound Connection Manager Firewall (Priority #1) Edge. X Security High Level Function David Ferriera - Technical Lead • Actions to define requirements and search for open source candidates James White (Dell)/Dell Team • Clean up and donation of Dell Fuse Security Service • Work to begin post Barcelona • Inbound Connection Manager Firewall API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Priority #1 Inbound Connection Manager Firewall Implement the Fuse Security Service • The Edge. X Security WG identified a high priority need @ the Face to Face • Inbound Connection Manager (Firewall) • Protected communications of north bound interface • Dell began a security microservice that implemented functionality similar to the Inbound Connection Manager • A firewall/proxy type service that protects the north side interface • The implementation was prototyped but not completed and placed into Fuse due to infrastructure needs to be determined (keystore, firewall, etc. ) • Proposal #1 • Post Barcelona, prioritize the work of one of our implementation teams to complete this implementation for California • Puts a strawman in place for the security working groups #1 priority • Will also require picking/using some open source infrastructure to further complete the implementation • • This will assist in other security implementation efforts (or show weaknesses that need to be corrected) Firewall, keystore, etc. • Details on the next slide edgexfoundry. org | @edgexfoundry
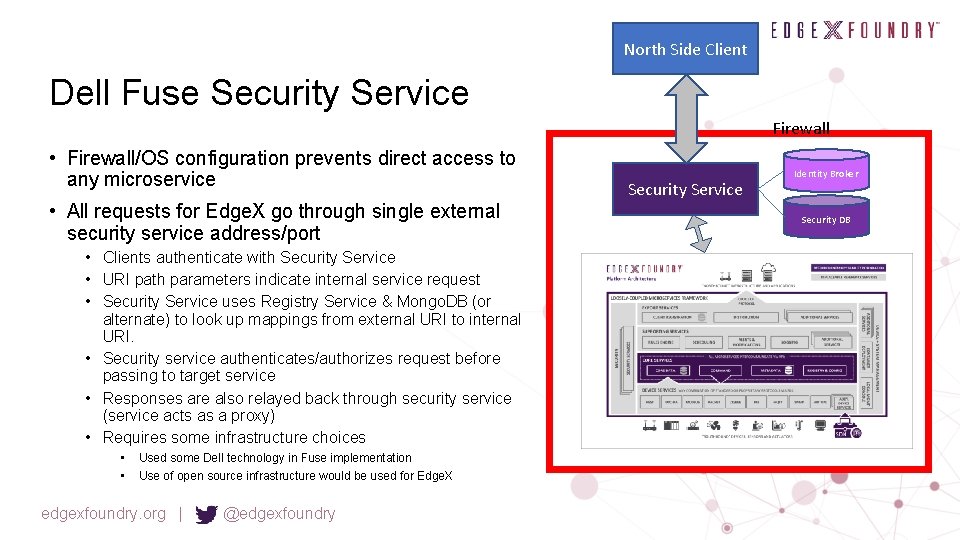
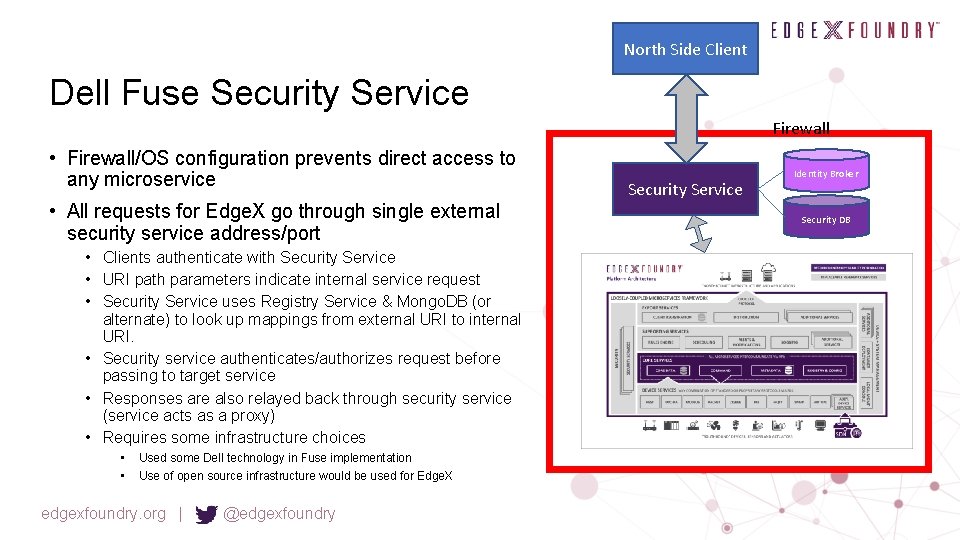
North Side Client Dell Fuse Security Service Firewall • Firewall/OS configuration prevents direct access to any microservice • All requests for Edge. X go through single external security service address/port • Clients authenticate with Security Service • URI path parameters indicate internal service request • Security Service uses Registry Service & Mongo. DB (or alternate) to look up mappings from external URI to internal URI. • Security service authenticates/authorizes request before passing to target service • Responses are also relayed back through security service (service acts as a proxy) • Requires some infrastructure choices • • Used some Dell technology in Fuse implementation Use of open source infrastructure would be used for Edge. X edgexfoundry. org | @edgexfoundry Security Service Identity Broker Security DB
Key Management (Priority #2) Edge. X Security High Level Function Riaz Zolfonnon - Technical Lead • Actions to define requirements for REST API and search for open source candidates • Key Management • Containerize Key Vault • Later someone would need to connect this to other OS services and hardware Ro. T Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • Need to design a REST Edge. X API to these services • PKCS #11 services?
Internal Microservice Security Protocol (Priority #3) Edge. X Security High Level Function James White (Dell)/Steve Osselton (IOTech) • Next action – James and Steve to propose API post Barcelona release • Internal Microservice Security Protocol • ? ? API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Priority #3 Implement an internal microservice communication security protocol • Several security APIs around service communications already exist • OMG’s DDS Security API (http: //www. omg. org/spec/DDS-SECURITY/1. 0/) • OWASP REST Security API (https: //www. owasp. org/index. php/REST_Security_Cheat_Sheet) • JWT (https: //jwt. io/introduction/) • Proposal #2 • Allow two Edge. X/industry architects to provide a survey of the options and recommendation for implementation to the security WG • Again use the security implementation team to implement the APIs throughout Edge. X services for California • While not as high a priority, allow Edge. X security to be improved via some standard API set (not requiring wheel re -invention) • Allows Security Working Group to react/consider a design/architecture versus starting from scratch and work from requirements all the way to implementation • Help to • identify additional infrastructure needs • abstract the implementation to allow other future implementations • provide more secure services as a reference implementation edgexfoundry. org | @edgexfoundry
Access Management Edge. X Security High Level Function • Access Management • OAuth 2. 0 Roles Resource Owner Client Resource Server Authorization Server Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • •
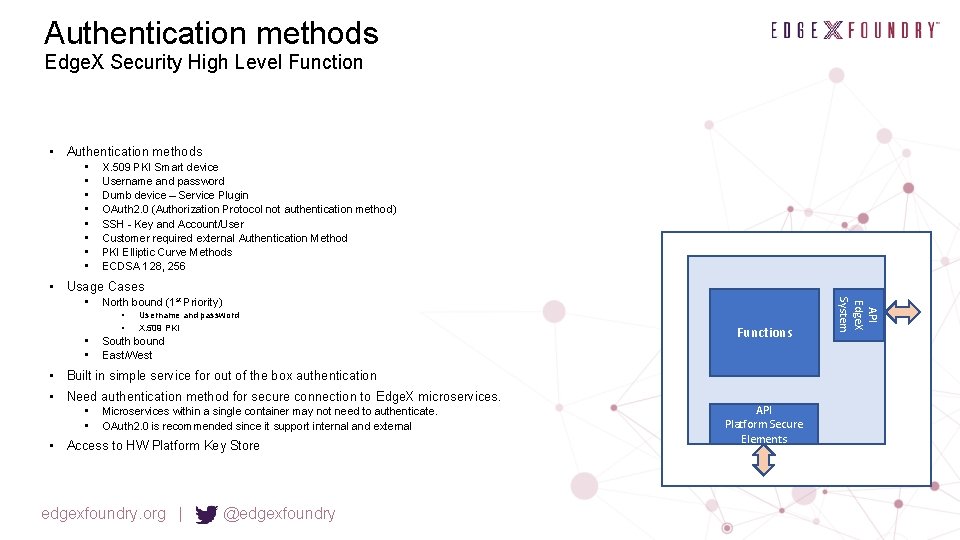
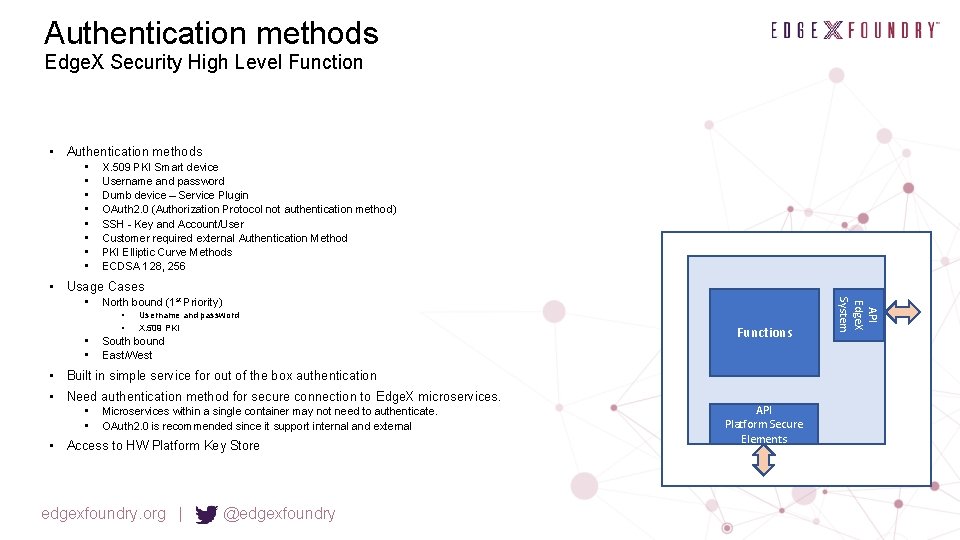
Authentication methods Edge. X Security High Level Function • Authentication methods • • X. 509 PKI Smart device Username and password Dumb device – Service Plugin OAuth 2. 0 (Authorization Protocol not authentication method) SSH - Key and Account/User Customer required external Authentication Method PKI Elliptic Curve Methods ECDSA 128, 256 • Usage Cases North bound (1 st Priority) • • Username and password X. 509 PKI South bound East/West Functions • Built in simple service for out of the box authentication • Need authentication method for secure connection to Edge. X microservices. • • Microservices within a single container may not need to authenticate. OAuth 2. 0 is recommended since it support internal and external • Access to HW Platform Key Store edgexfoundry. org | @edgexfoundry API Platform Secure Elements API Edge. X System •
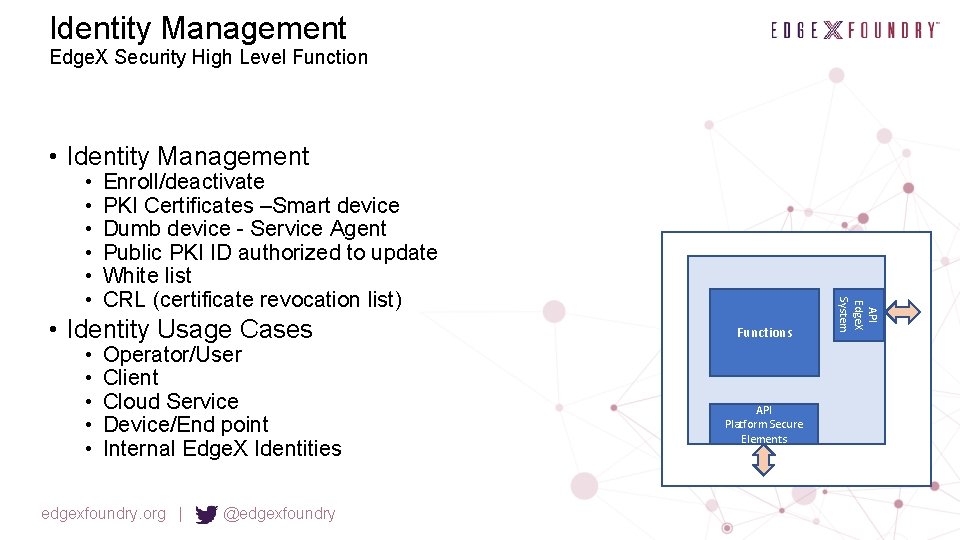
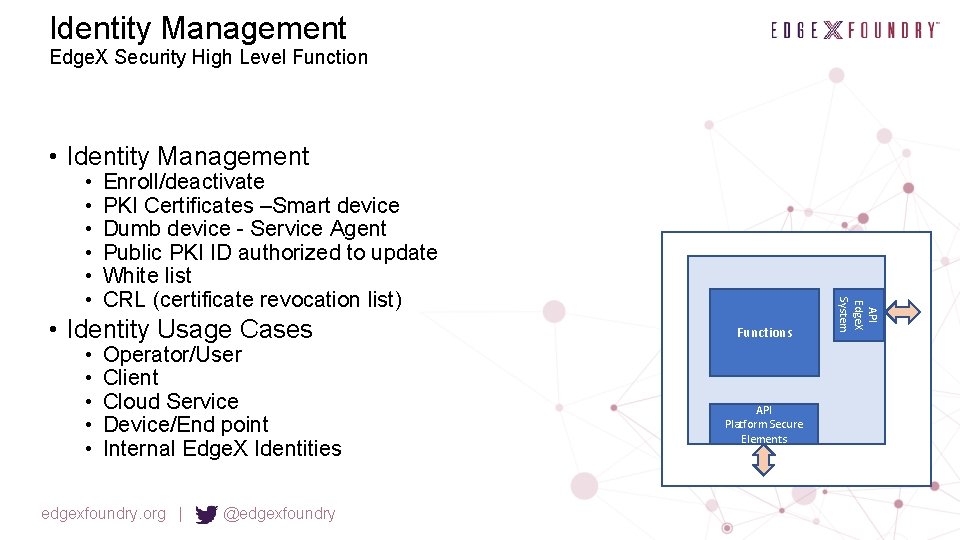
Identity Management Edge. X Security High Level Function • Identity Management Enroll/deactivate PKI Certificates –Smart device Dumb device - Service Agent Public PKI ID authorized to update White list CRL (certificate revocation list) • Identity Usage Cases • • • Operator/User Client Cloud Service Device/End point Internal Edge. X Identities edgexfoundry. org | @edgexfoundry Functions API Platform Secure Elements API Edge. X System • • •
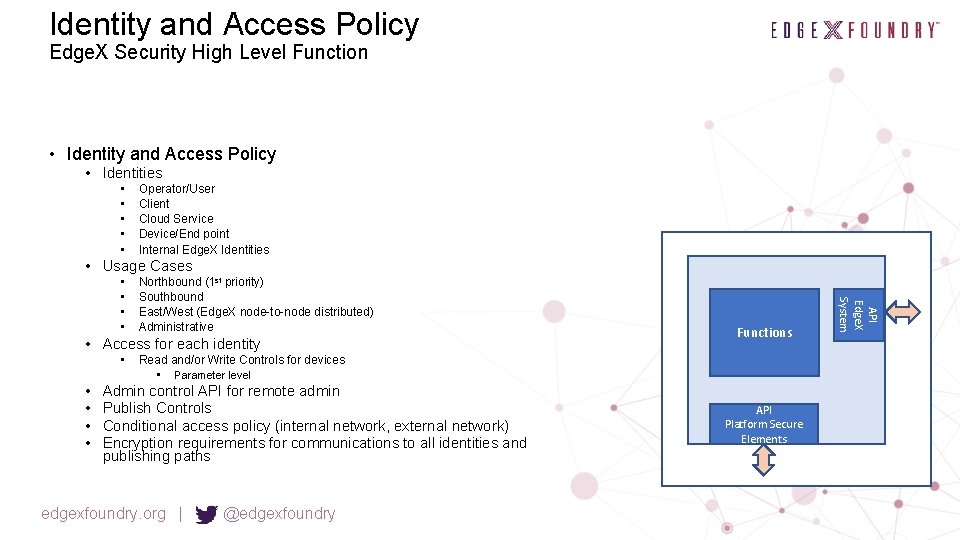
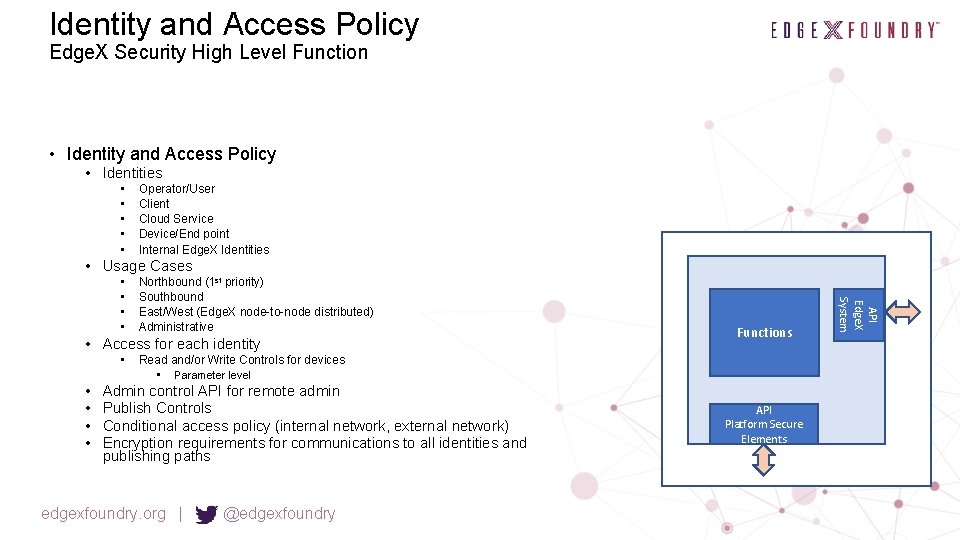
Identity and Access Policy Edge. X Security High Level Function • Identity and Access Policy • Identities • • • Operator/User Client Cloud Service Device/End point Internal Edge. X Identities • Usage Cases Northbound (1 st priority) Southbound East/West (Edge. X node-to-node distributed) Administrative • Access for each identity • • • Functions Read and/or Write Controls for devices • Parameter level Admin control API for remote admin Publish Controls Conditional access policy (internal network, external network) Encryption requirements for communications to all identities and publishing paths edgexfoundry. org | @edgexfoundry API Platform Secure Elements API Edge. X System • •
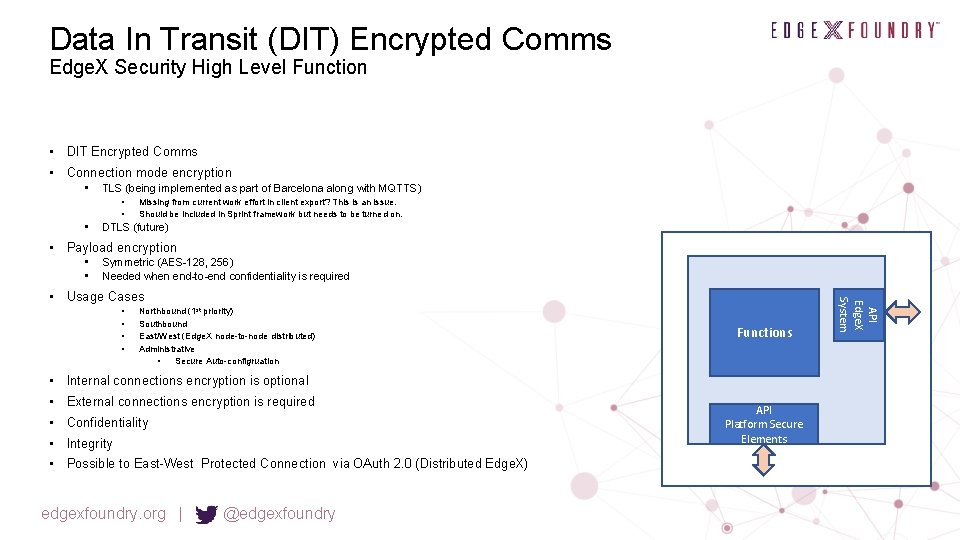
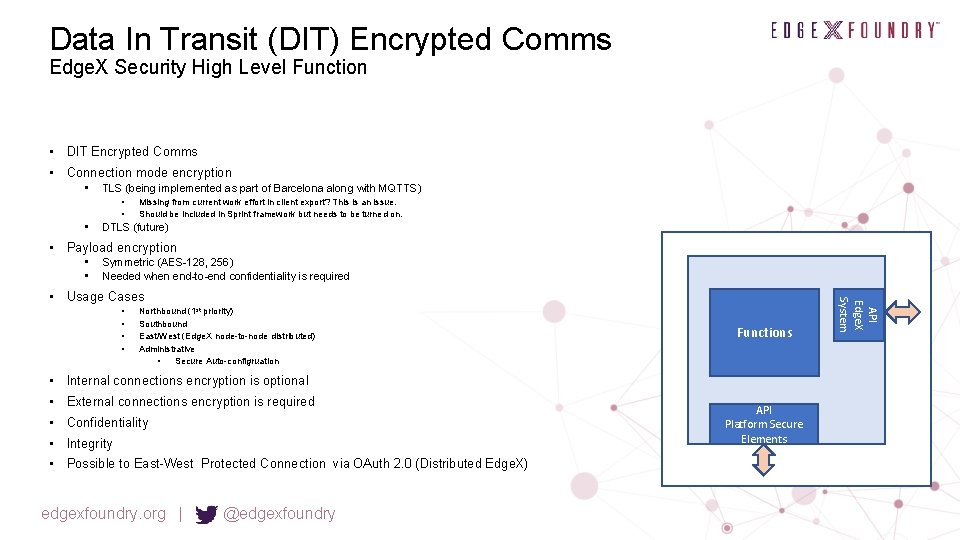
Data In Transit (DIT) Encrypted Comms Edge. X Security High Level Function • DIT Encrypted Comms • Connection mode encryption • TLS (being implemented as part of Barcelona along with MQTTS) • • • Missing from current work effort in client export? This is an issue. Should be included in Sprint framework but needs to be turned on. DTLS (future) • Payload encryption • • Symmetric (AES-128, 256) Needed when end-to-end confidentiality is required • • Northbound (1 st priority) Southbound East/West (Edge. X node-to-node distributed) Administrative • Secure Auto-configruation Functions • Internal connections encryption is optional • External connections encryption is required • Confidentiality • Integrity • Possible to East-West Protected Connection via OAuth 2. 0 (Distributed Edge. X) edgexfoundry. org | @edgexfoundry API Platform Secure Elements API Edge. X System • Usage Cases
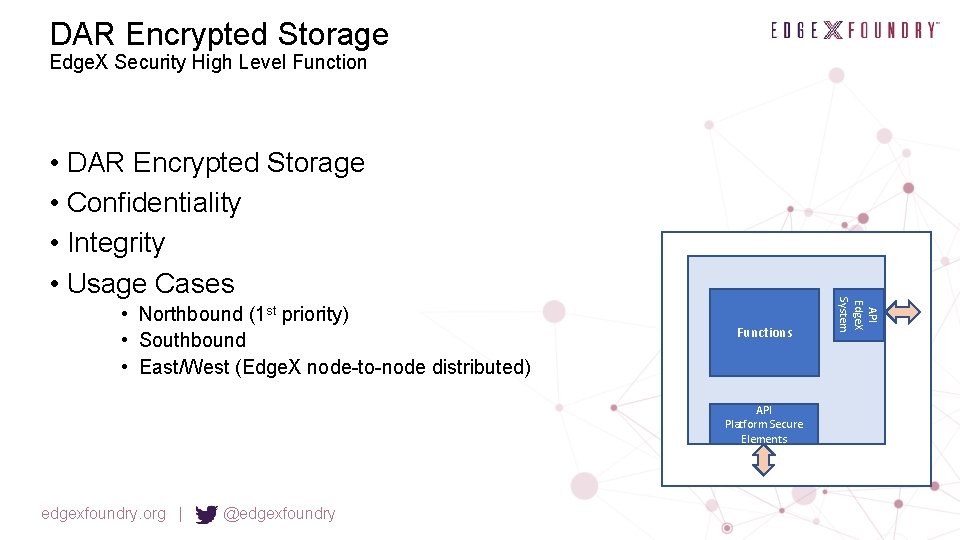
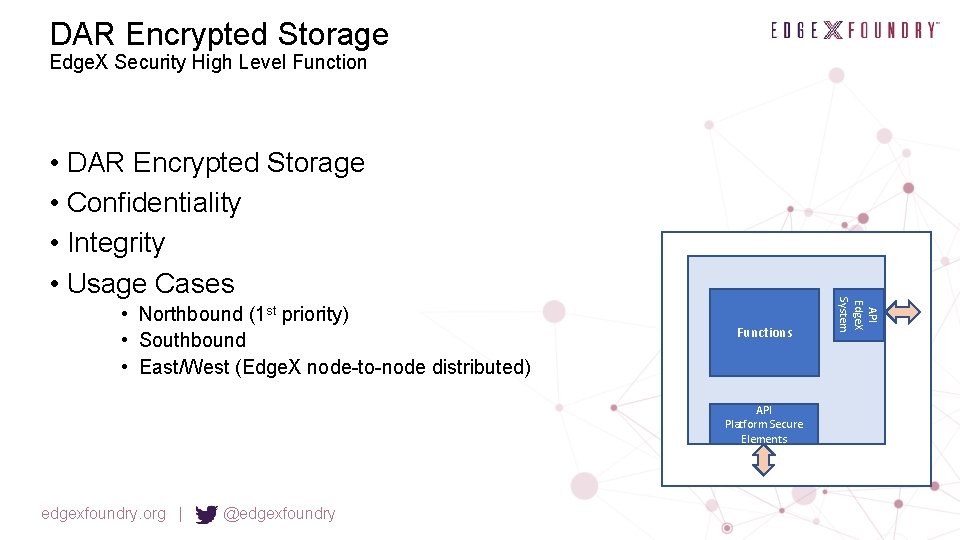
DAR Encrypted Storage Edge. X Security High Level Function • Northbound (1 st priority) • Southbound • East/West (Edge. X node-to-node distributed) Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • DAR Encrypted Storage • Confidentiality • Integrity • Usage Cases
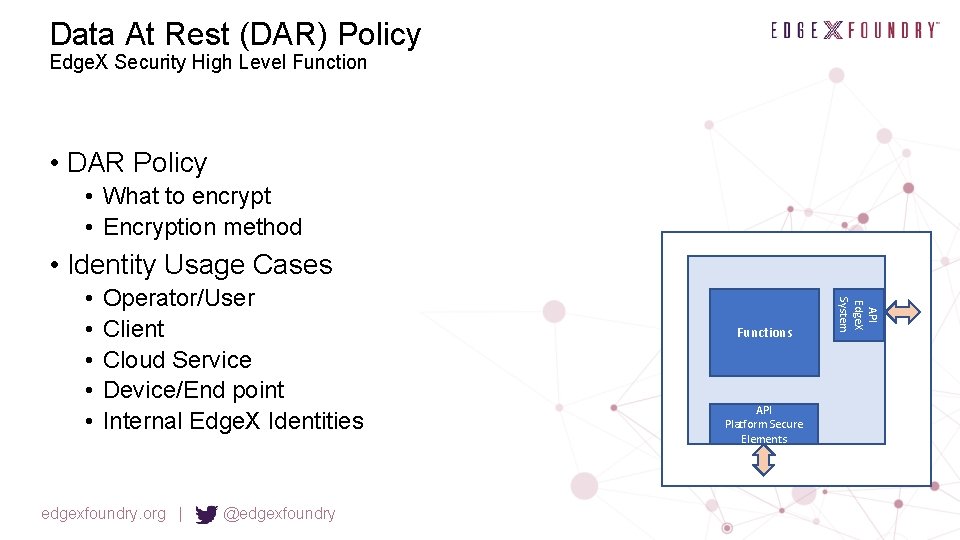
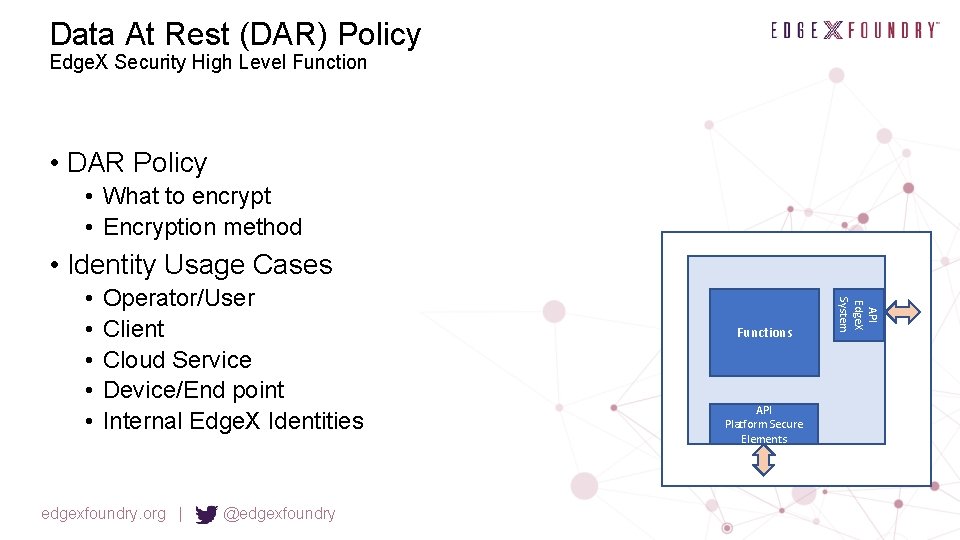
Data At Rest (DAR) Policy Edge. X Security High Level Function • DAR Policy • What to encrypt • Encryption method • Identity Usage Cases Operator/User Client Cloud Service Device/End point Internal Edge. X Identities edgexfoundry. org | @edgexfoundry Functions API Platform Secure Elements API Edge. X System • • •
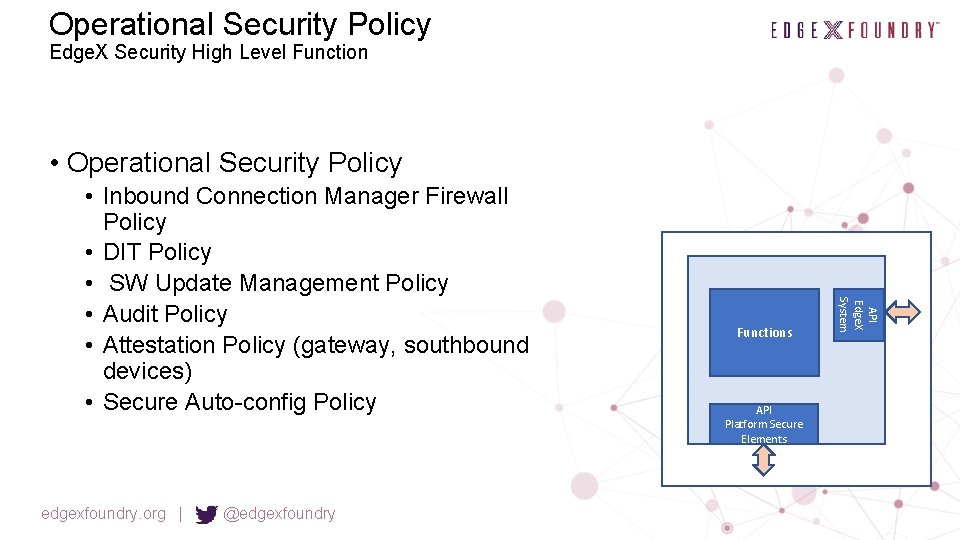
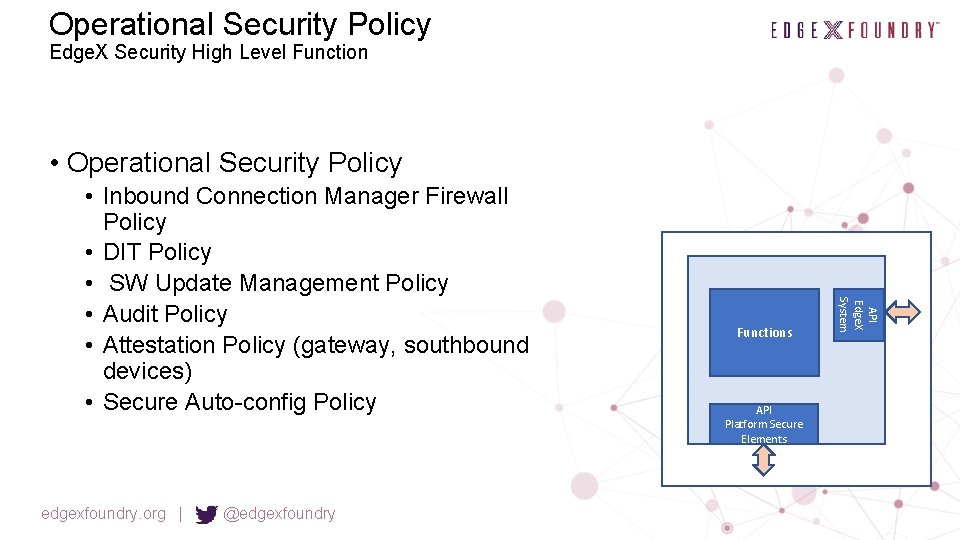
Operational Security Policy Edge. X Security High Level Function • Operational Security Policy edgexfoundry. org | @edgexfoundry Functions API Platform Secure Elements API Edge. X System • Inbound Connection Manager Firewall Policy • DIT Policy • SW Update Management Policy • Audit Policy • Attestation Policy (gateway, southbound devices) • Secure Auto-config Policy
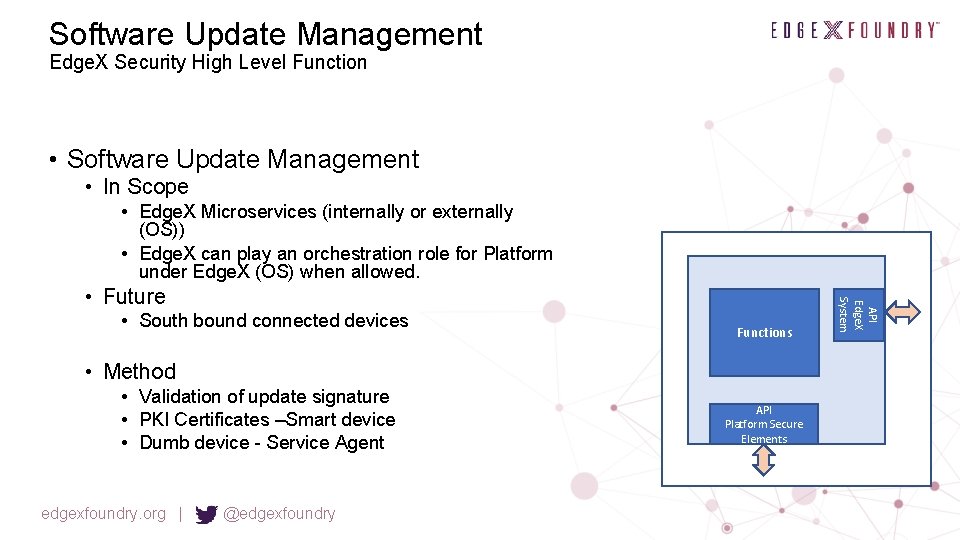
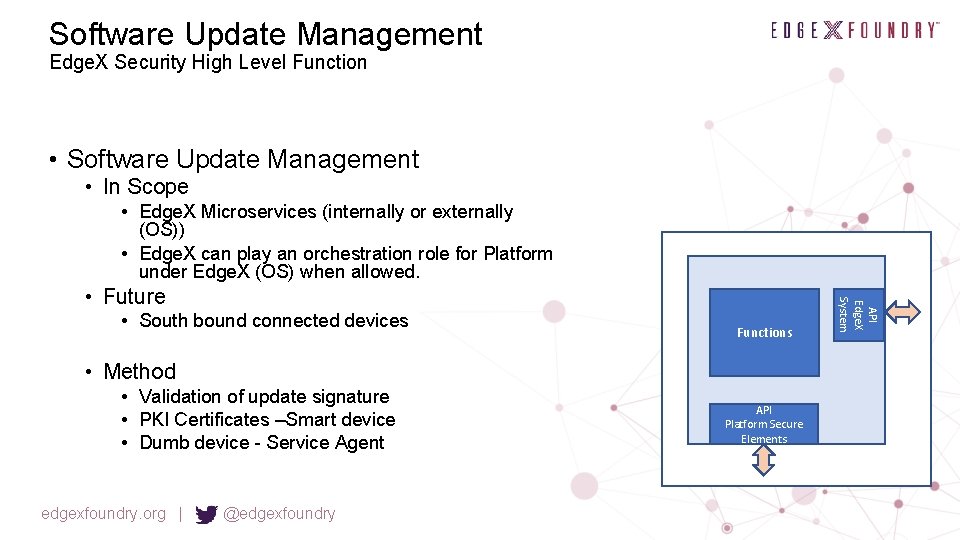
Software Update Management Edge. X Security High Level Function • Software Update Management • In Scope • Edge. X Microservices (internally or externally (OS)) • Edge. X can play an orchestration role for Platform under Edge. X (OS) when allowed. • South bound connected devices Functions • Method • Validation of update signature • PKI Certificates –Smart device • Dumb device - Service Agent edgexfoundry. org | @edgexfoundry API Platform Secure Elements API Edge. X System • Future
Security Monitoring Edge. X Security High Level Function • Security Monitoring Alerts Anomaly detection Intrusion detection Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • •
Audit Edge. X Security High Level Function • Audit • Log security events • Signing and anti-tamper protections API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Attestation Edge. X Security High Level Function • Attestation gateway • Measurement for chain of trust • Measurement of boot images • Measurement of control and configuration Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • Future Attestation southbound device
Chain of Trust Edge. X Security High Level Function • Chain of Trust • What so measure • How to measure • Attestation measurement signing API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
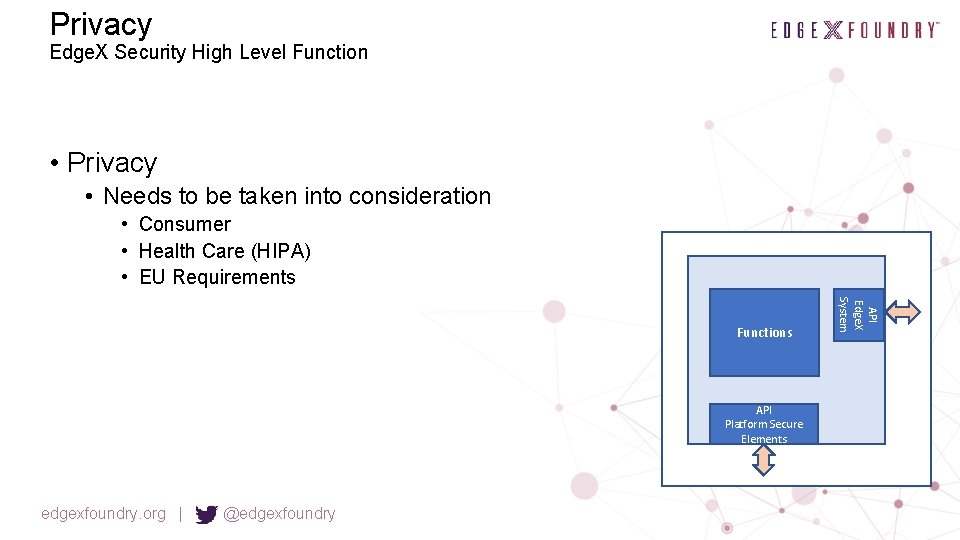
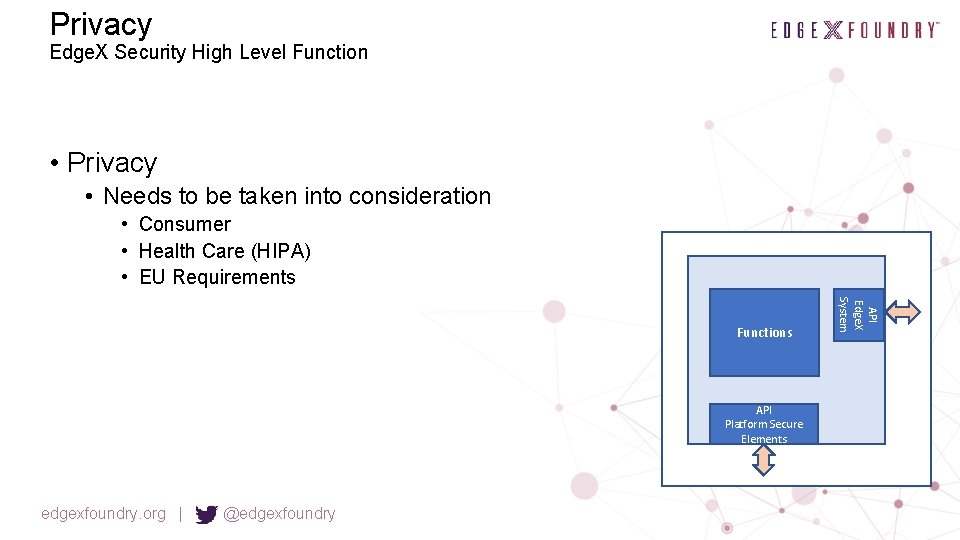
Privacy Edge. X Security High Level Function • Privacy • Needs to be taken into consideration • Consumer • Health Care (HIPA) • EU Requirements API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
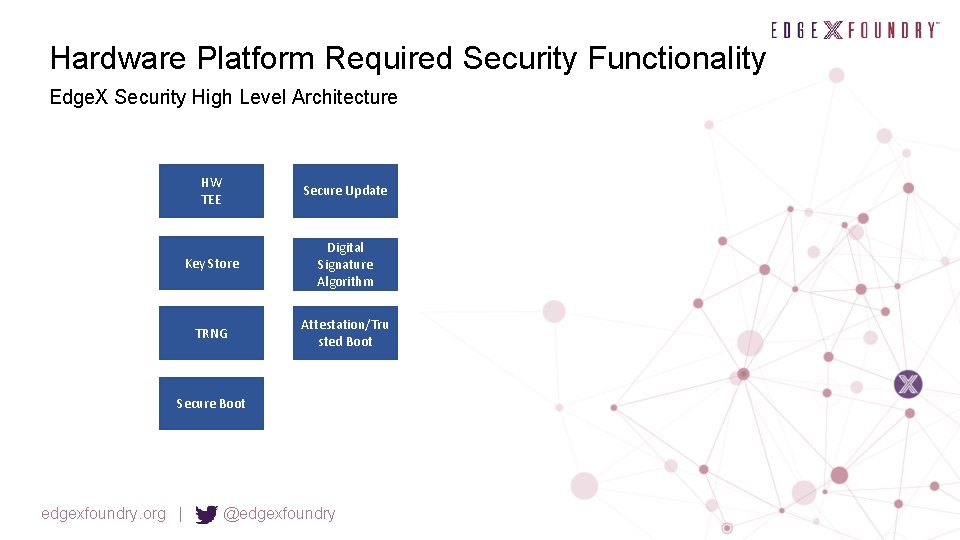
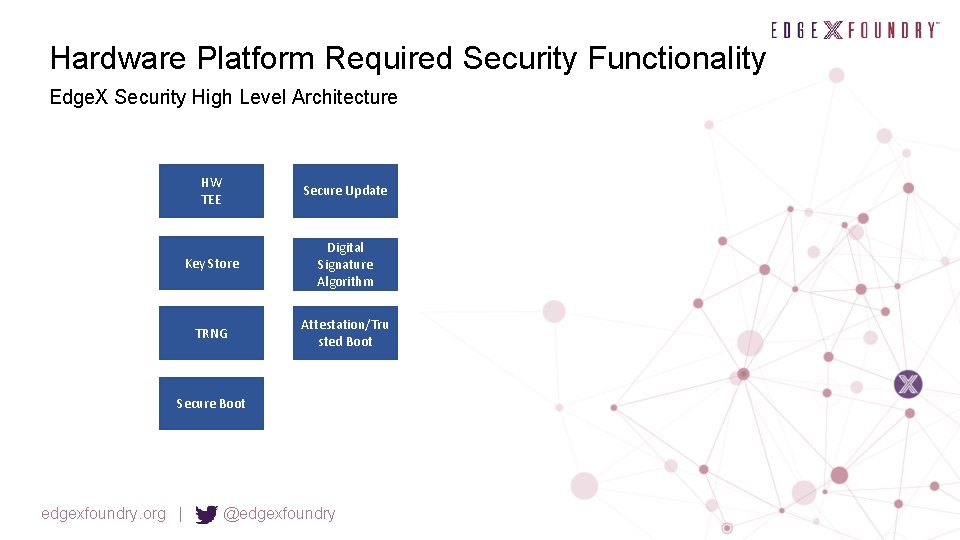
Hardware Platform Required Security Functionality Edge. X Security High Level Architecture HW TEE Secure Update Key Store Digital Signature Algorithm TRNG Attestation/Tru sted Boot Secure Boot edgexfoundry. org | @edgexfoundry
HW TEE (Trusted Execution Environment) Edge. X Security High Level Function • HW TEE (Trusted Execution Environment) • Required in platform to protect and isolate security sensitive values API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Key Store Edge. X Security High Level Function • Key Store • Required in platform to protect stored keys API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
RNG (Random Number Generator) Edge. X Security High Level Function • RNG (Random Number Generator) • TRNG (True Random Number Generator) • DRNG (Deterministic RNG) API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Secure Boot Edge. X Security High Level Function • Secure Boot Signature validation at each boot level Integrity checks at each boot level Connection into chain of trust in Edge. X System will only boot of integrity checks pass Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • •
Digital Signature Algorithm Edge. X Security High Level Function • Digital Signature Algorithm • ECDSA API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System Functions
Attestation/Trusted Boot Edge. X Security High Level Function • Attestation • Measurement of each boot level • Connection into attestation in Edge. X • Trusted Boot Functions API Platform Secure Elements edgexfoundry. org | @edgexfoundry API Edge. X System • Measurement and reporting of attestation vector. System always boots.

Edge. X Security High Level Architecture Open Questions • Out of Scope - Provide guidance on how security features can/should be tested edgexfoundry. org | @edgexfoundry
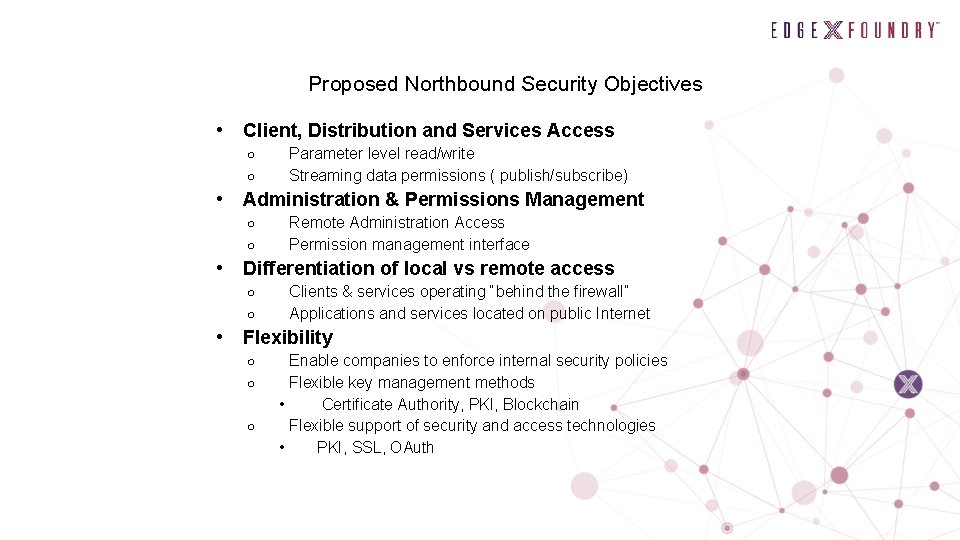
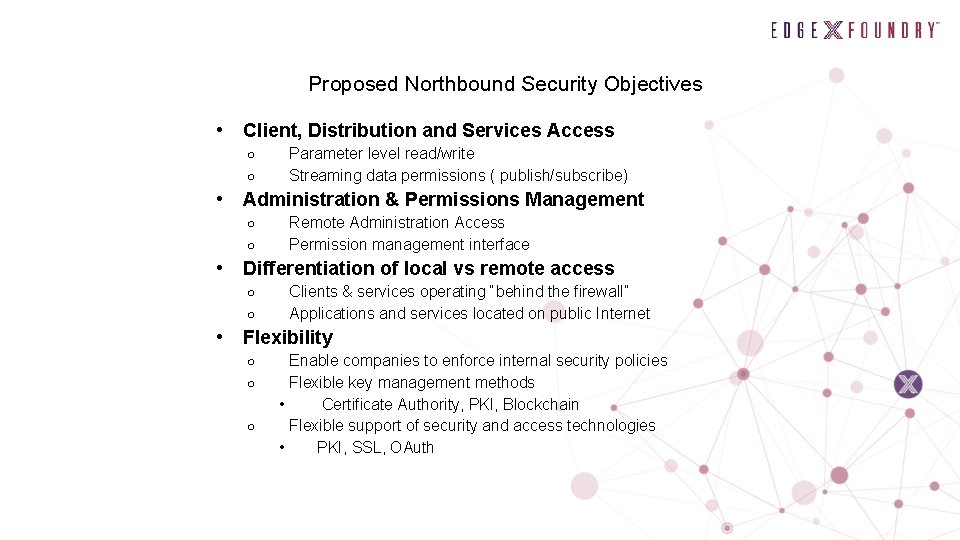
Proposed Northbound Security Objectives • Client, Distribution and Services Access ○ ○ • Administration & Permissions Management ○ ○ • Remote Administration Access Permission management interface Differentiation of local vs remote access ○ ○ • Parameter level read/write Streaming data permissions ( publish/subscribe) Clients & services operating “behind the firewall” Applications and services located on public Internet Flexibility ○ ○ ○ Enable companies to enforce internal security policies Flexible key management methods • Certificate Authority, PKI, Blockchain Flexible support of security and access technologies • PKI, SSL, OAuth
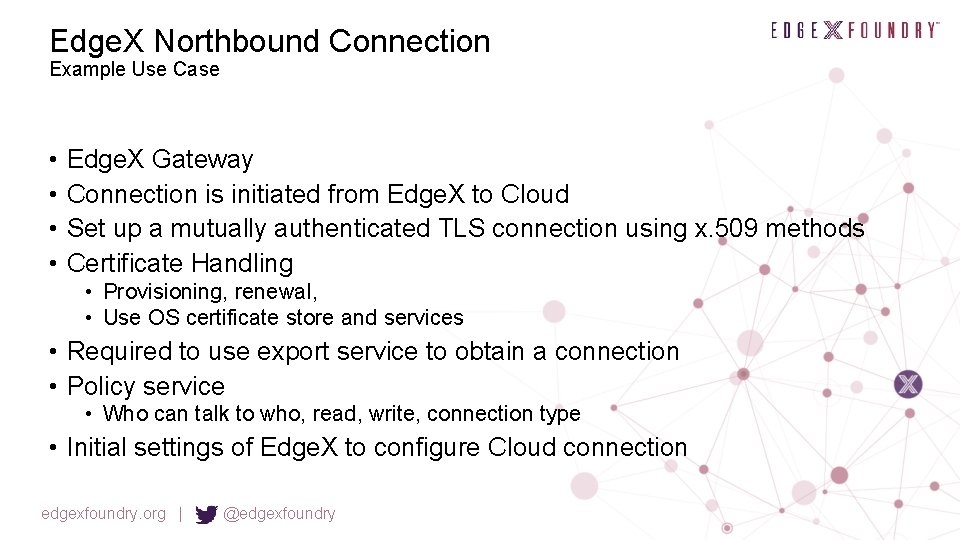
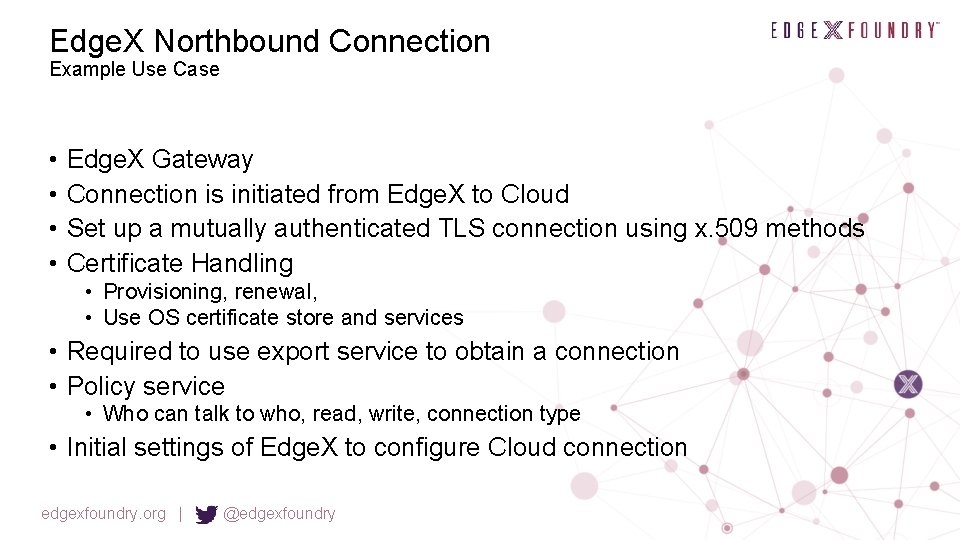
Edge. X Northbound Connection Example Use Case • • Edge. X Gateway Connection is initiated from Edge. X to Cloud Set up a mutually authenticated TLS connection using x. 509 methods Certificate Handling • Provisioning, renewal, • Use OS certificate store and services • Required to use export service to obtain a connection • Policy service • Who can talk to who, read, write, connection type • Initial settings of Edge. X to configure Cloud connection edgexfoundry. org | @edgexfoundry
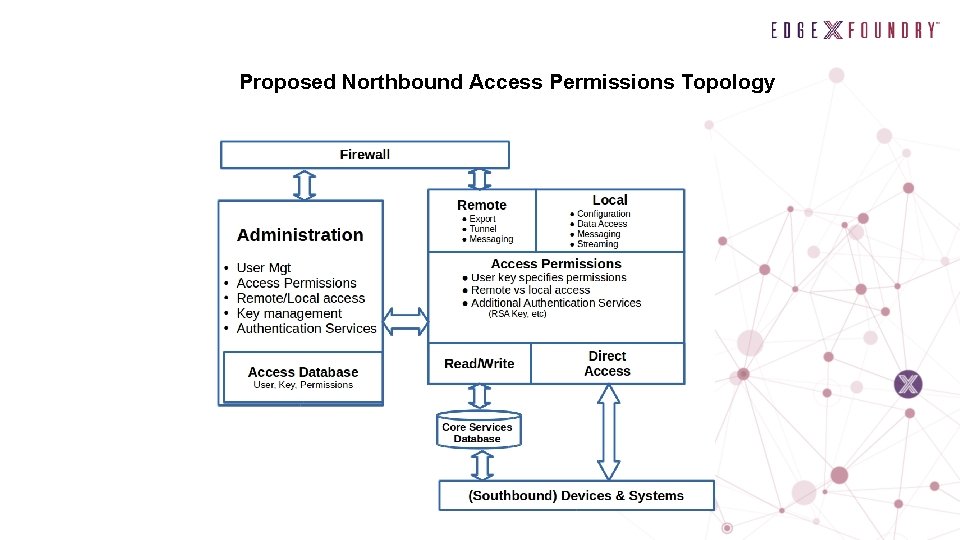
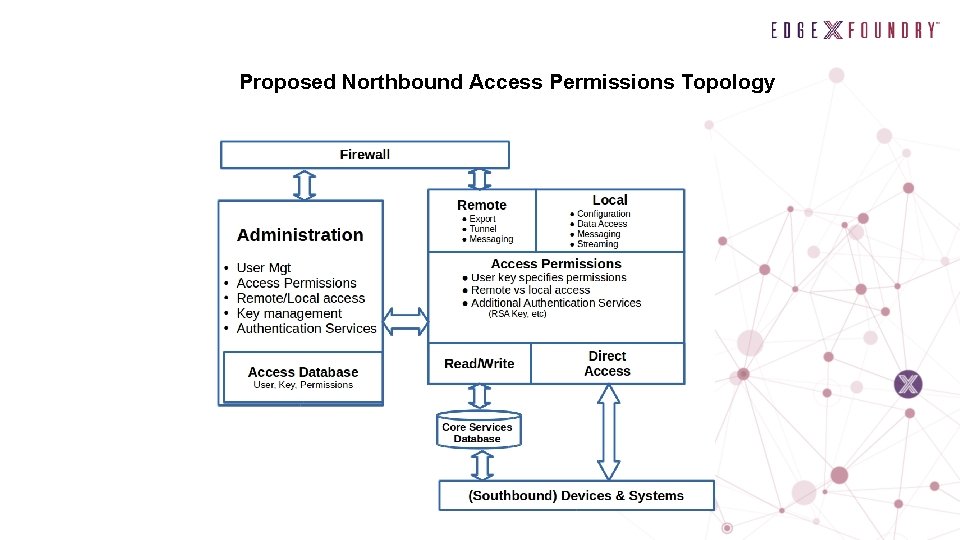
Proposed Northbound Access Permissions Topology
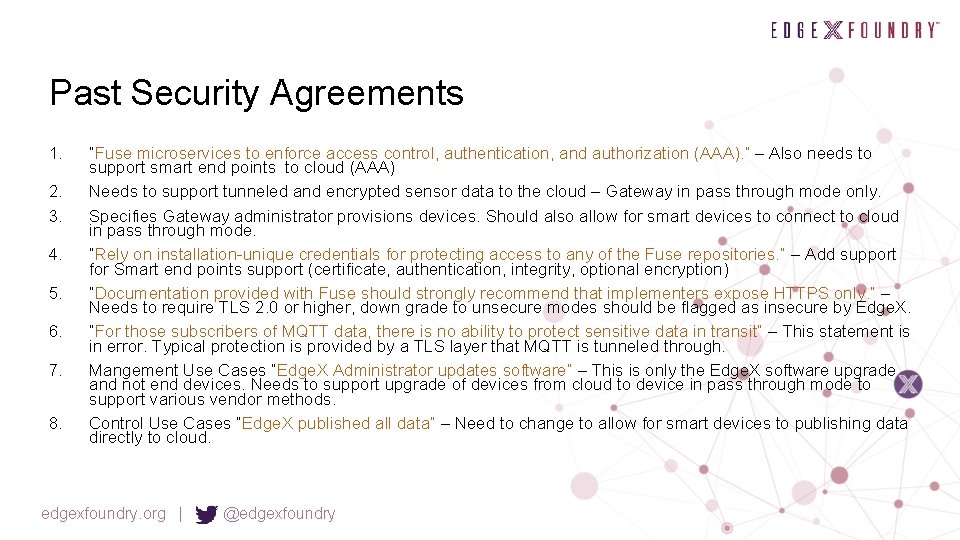
Past Security Agreements 1. 2. 3. 4. 5. 6. 7. 8. “Fuse microservices to enforce access control, authentication, and authorization (AAA). ” – Also needs to support smart end points to cloud (AAA) Needs to support tunneled and encrypted sensor data to the cloud – Gateway in pass through mode only. Specifies Gateway administrator provisions devices. Should also allow for smart devices to connect to cloud in pass through mode. “Rely on installation-unique credentials for protecting access to any of the Fuse repositories. ” – Add support for Smart end points support (certificate, authentication, integrity, optional encryption) “Documentation provided with Fuse should strongly recommend that implementers expose HTTPS only. ” – Needs to require TLS 2. 0 or higher, down grade to unsecure modes should be flagged as insecure by Edge. X. “For those subscribers of MQTT data, there is no ability to protect sensitive data in transit” – This statement is in error. Typical protection is provided by a TLS layer that MQTT is tunneled through. Mangement Use Cases “Edge. X Administrator updates software” – This is only the Edge. X software upgrade and not end devices. Needs to support upgrade of devices from cloud to device in pass through mode to support various vendor methods. Control Use Cases “Edge. X published all data” – Need to change to allow for smart devices to publishing data directly to cloud. edgexfoundry. org | @edgexfoundry