Security Strategies in Linux Platforms and Applications Chapter
- Slides: 16
Security Strategies in Linux Platforms and Applications Chapter 1 Security Threats to Linux © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved.
Learning Objective § Identify threats to the Linux operating system and other open source applications. Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 2
Key Concepts § Open source software security considerations § Impact of laws and regulations on a security policy § Threats to the seven domains of an information technology (IT) infrastructure § Standard methodologies for testing vulnerabilities on Linux and open source applications § Linux in the emerging virtual machine (VM) market Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 3
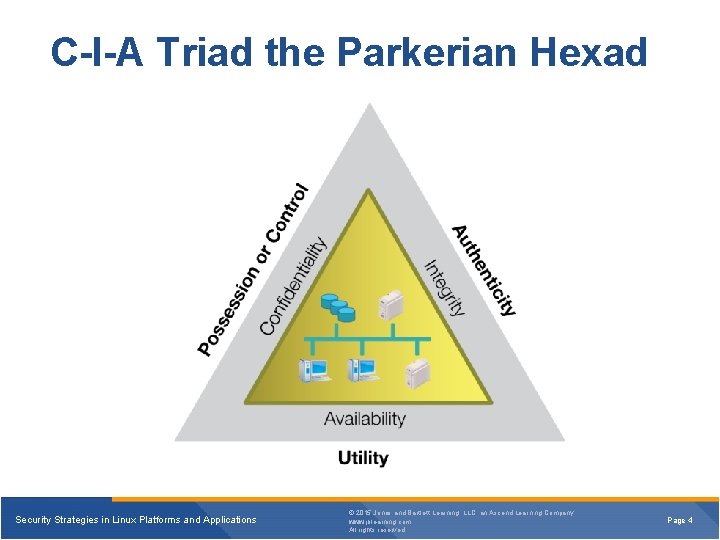
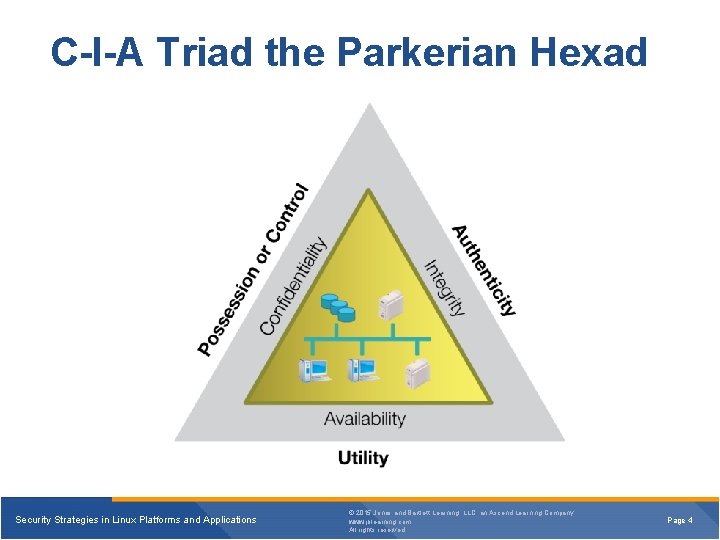
C-I-A Triad the Parkerian Hexad Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 4
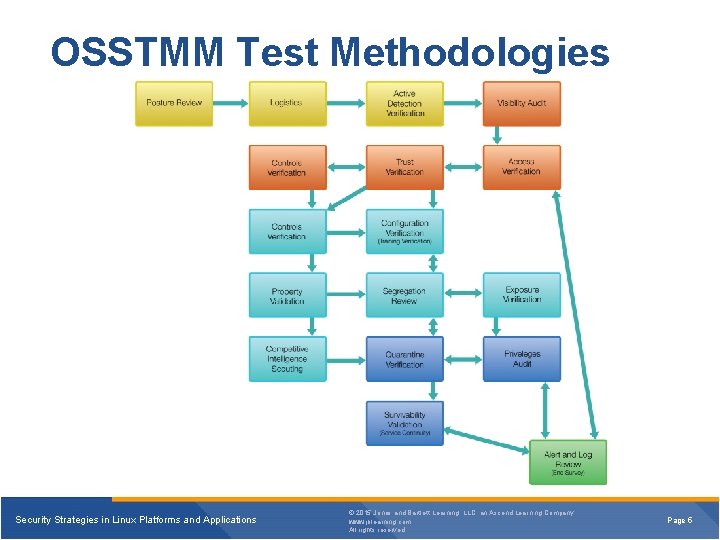
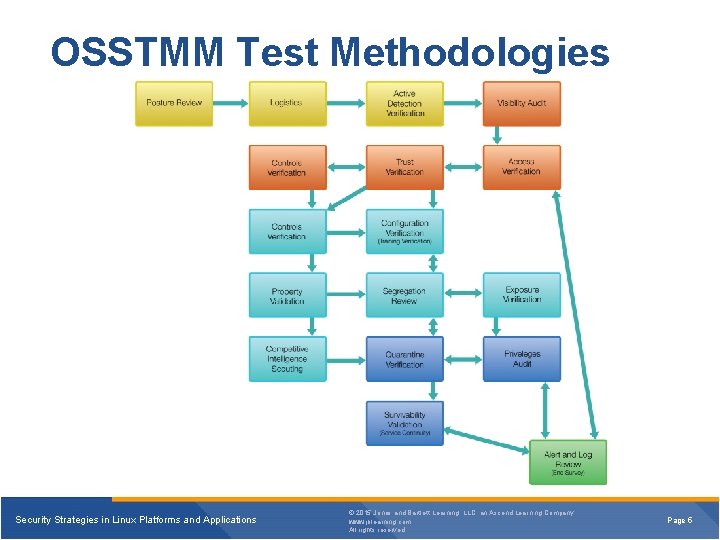
OSSTMM Test Methodologies Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 5
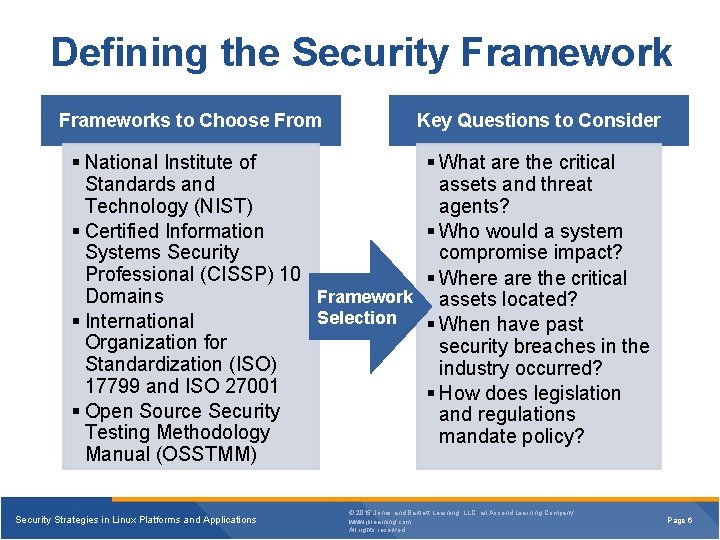
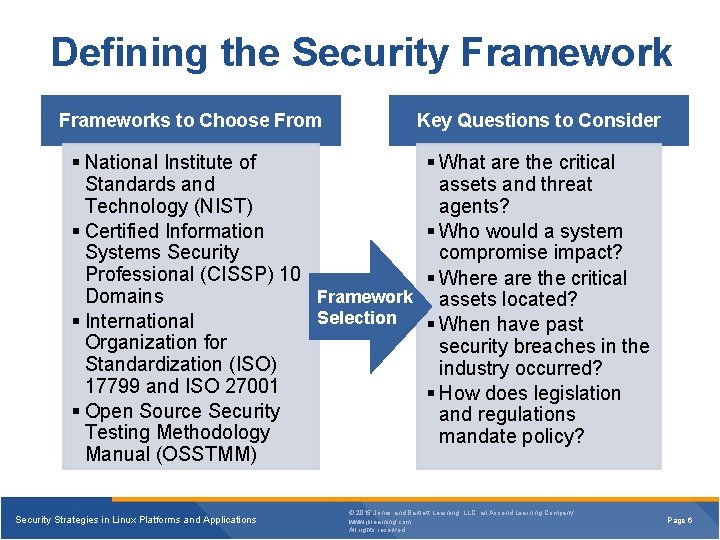
Defining the Security Frameworks to Choose From Key Questions to Consider § National Institute of § What are the critical Standards and assets and threat Technology (NIST) agents? § Certified Information § Who would a system Systems Security compromise impact? Professional (CISSP) 10 § Where are the critical Framework assets located? Domains Selection § International § When have past Organization for security breaches in the Standardization (ISO) industry occurred? 17799 and ISO 27001 § How does legislation § Open Source Security and regulations Testing Methodology mandate policy? Manual (OSSTMM) Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 6
Responsibilities of a Linux System Administrator § System availability and performance § User access and denial § Maintenance of the integrity of operating system, application, storage files, resources, and data transmission Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 7
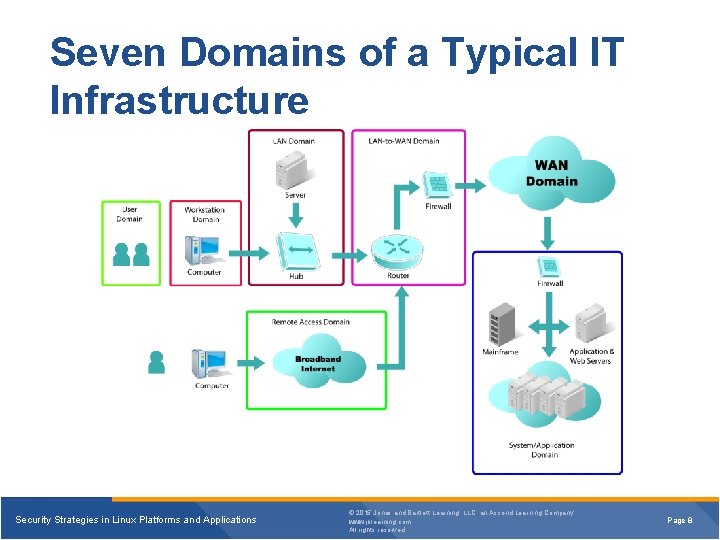
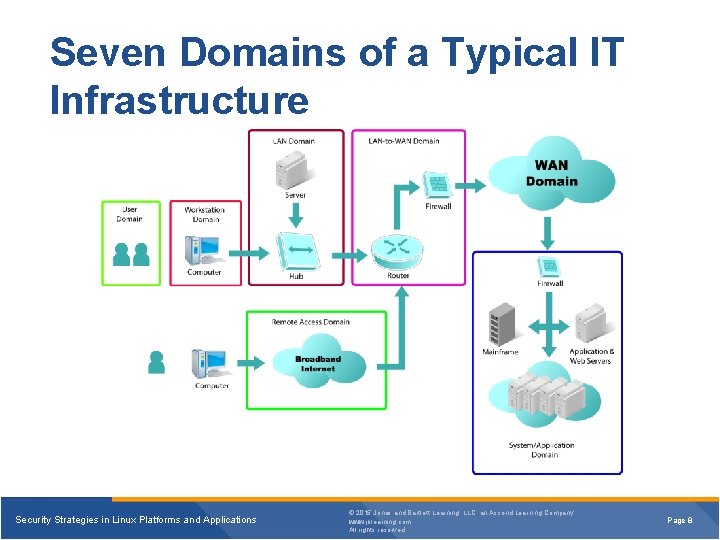
Seven Domains of a Typical IT Infrastructure Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 8
Linux in the Seven Domains § User Domain § Workstation Domain § LAN Domain § WAN Domain Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 9
Linux in the Seven Domains (Continued) § LAN-to-WAN Domain § Remote Access Domain § System Domain Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 10
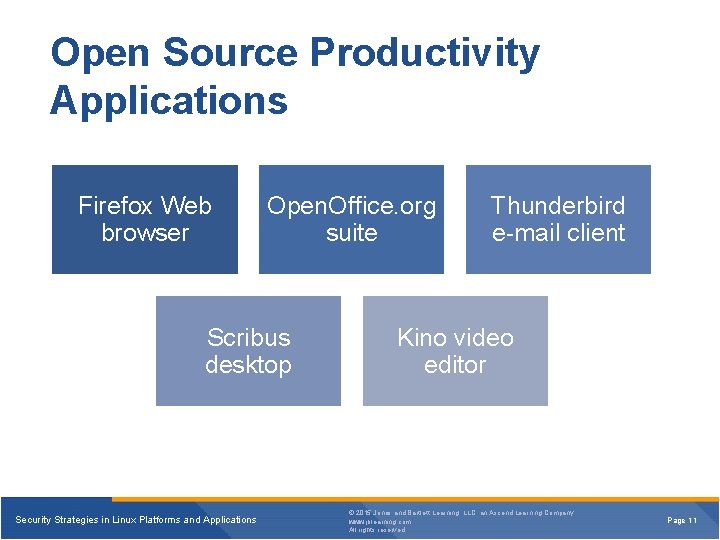
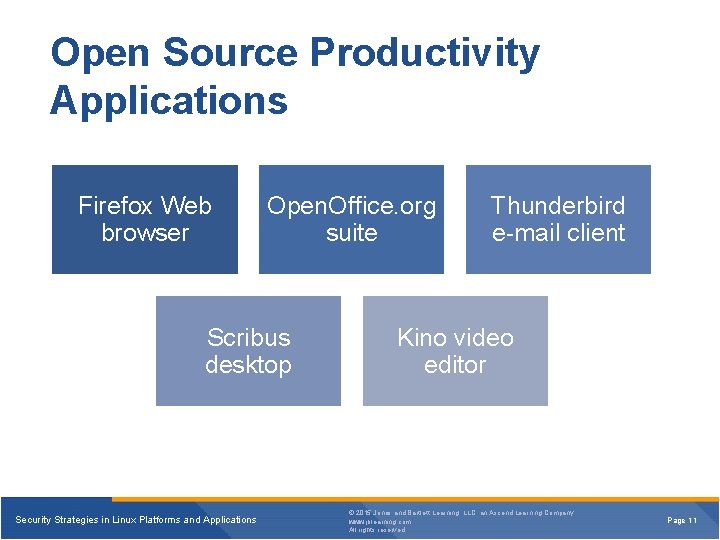
Open Source Productivity Applications Firefox Web browser Open. Office. org suite Scribus desktop Security Strategies in Linux Platforms and Applications Thunderbird e-mail client Kino video editor © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 11
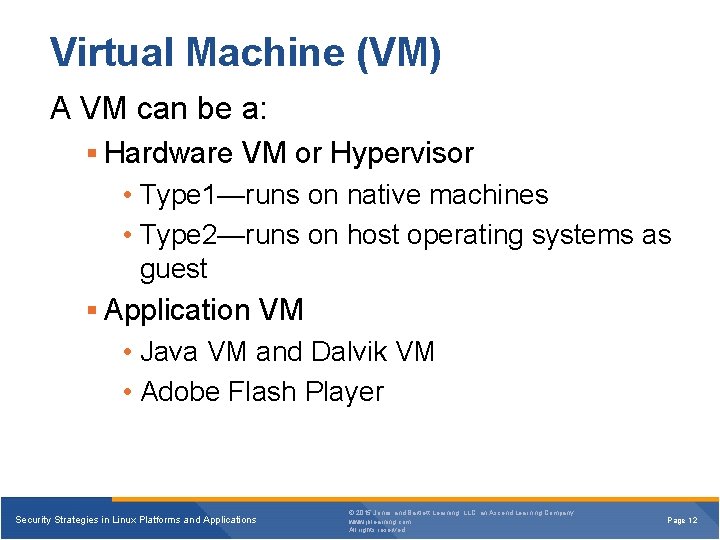
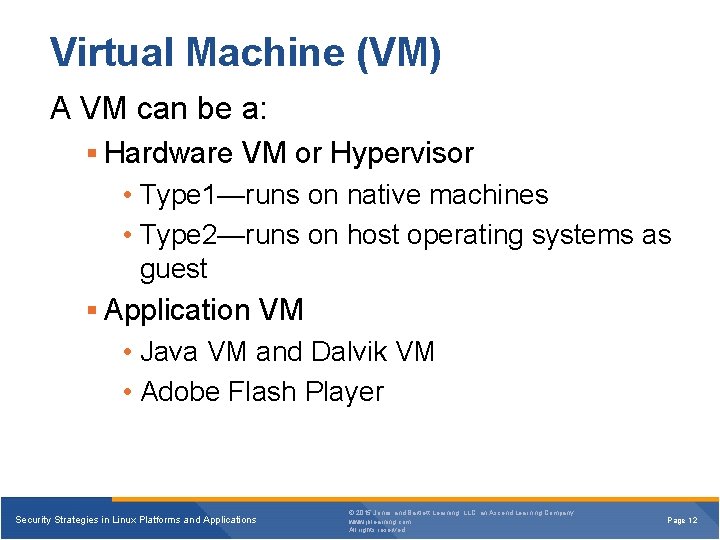
Virtual Machine (VM) A VM can be a: § Hardware VM or Hypervisor • Type 1—runs on native machines • Type 2—runs on host operating systems as guest § Application VM • Java VM and Dalvik VM • Adobe Flash Player Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 12
Advantages of a Hypervisor § Saves money on hardware and power § Well-positioned for bastion hosts § Makes better use of hardware resources § Easier to manage Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 13
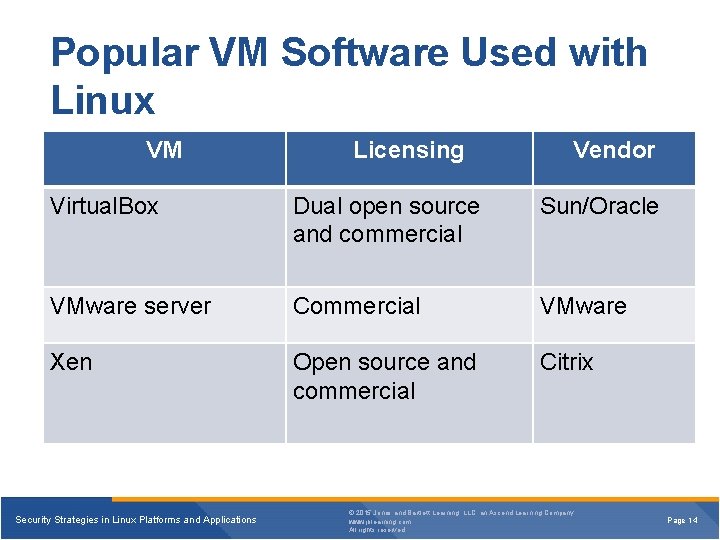
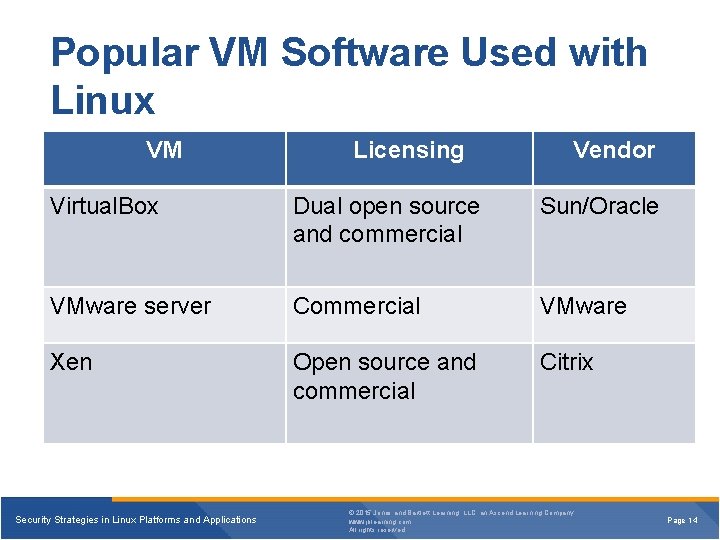
Popular VM Software Used with Linux VM Licensing Vendor Virtual. Box Dual open source and commercial Sun/Oracle VMware server Commercial VMware Xen Open source and commercial Citrix Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 14
Summary § Linux in the seven domains and various open source productivity applications § Facts about the use of Linux in the market § Responsibilities and tasks of a Linux system administrator § Process to define a security framework § Linux in the VM market and various VM software used with Linux Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 15
Virtual Lab § Installing a Core Linux Operating System on a Server Security Strategies in Linux Platforms and Applications © 2015 Jones and Bartlett Learning, LLC, an Ascend Learning Company www. jblearning. com All rights reserved. Page 16