Security Risk Management Steve Lamb Technical Security Advisor
Security Risk Management Steve Lamb Technical Security Advisor http: //blogs. msdn. com/steve_lamb stephlam@microsoft. com
Session Prerequisites Basic understanding of network security fundamentals Basic understanding of security risk management concepts Level 300
Target Audience This session is primarily intended for: ü Systems architects and planners ü Members of the information security team ü Security and IT auditors ü Senior executives, business analysts, and business decision makers ü Consultants and partners
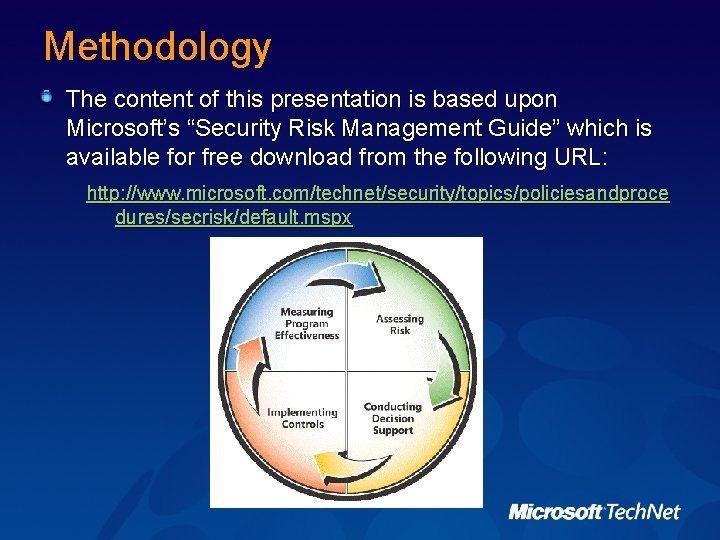
Methodology The content of this presentation is based upon Microsoft’s “Security Risk Management Guide” which is available for free download from the following URL: http: //www. microsoft. com/technet/security/topics/policiesandproce dures/secrisk/default. mspx
Session Overview Security Risk Management Concepts Identifying Security Risk Management Prerequisites Assessing Risk Conducting Decision Support Implementing Controls and Measuring Program Effectiveness
Security Risk Management Concepts Identifying Security Risk Management Prerequisites Assessing Risk Conducting Decision Support Implementing Controls and Measuring Program Effectiveness
Goals of Microsoft's Security Risk Management Guide Moving customers to a proactive security posture and freeing them from a reactive frustrating process Making security measurable by showing the value of security projects Helping customers to efficiently mitigate the largest risks in their environments rather than applying scarce resources to all possible risks
Why Develop a Security Risk Management Process? Security risk management: A process for identifying, prioritizing, and managing risk to an acceptable level within the organization Developing a formal security risk management process can address the Threat response time following: Regulatory compliance Infrastructure management costs Risk prioritization and management
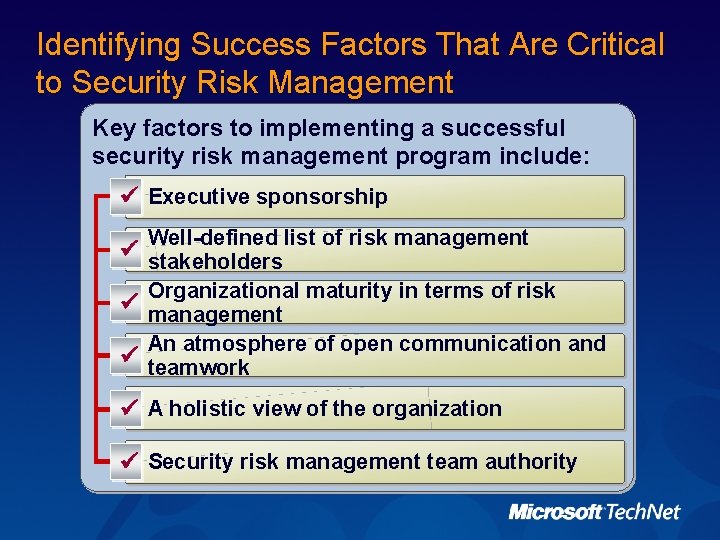
Identifying Success Factors That Are Critical to Security Risk Management Key factors to implementing a successful security risk management program include: ü Executive sponsorship Well-defined list of risk management ü stakeholders Organizational maturity in terms of risk ü management An atmosphere of open communication and ü teamwork ü A holistic view of the organization ü Security risk management team authority
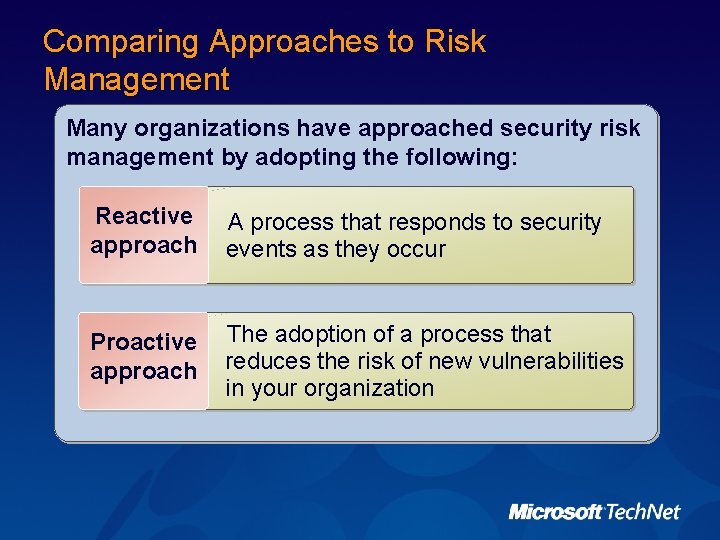
Comparing Approaches to Risk Management Many organizations have approached security risk management by adopting the following: Reactive approach A process that responds to security events as they occur Proactive approach The adoption of a process that reduces the risk of new vulnerabilities in your organization
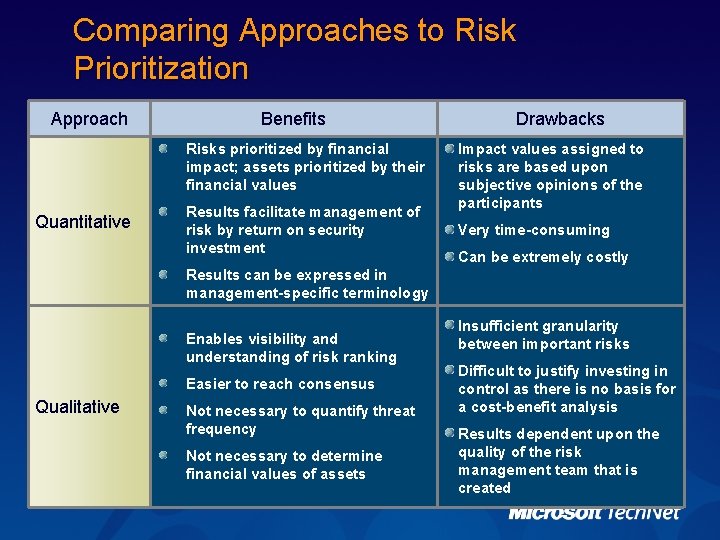
Comparing Approaches to Risk Prioritization Approach Benefits Risks prioritized by financial impact; assets prioritized by their financial values Quantitative Results facilitate management of risk by return on security investment Drawbacks Impact values assigned to risks are based upon subjective opinions of the participants Very time-consuming Can be extremely costly Results can be expressed in management-specific terminology Enables visibility and understanding of risk ranking Easier to reach consensus Qualitative Not necessary to quantify threat frequency Not necessary to determine financial values of assets Insufficient granularity between important risks Difficult to justify investing in control as there is no basis for a cost-benefit analysis Results dependent upon the quality of the risk management team that is created

Introducing the Microsoft Security Risk Management Process 4 Measuring Program Effectiveness 1 Assessing Risk 3 Implementing Controls 2 Conducting Decision Support
Identifying Security Risk Management Prerequisites Security Risk Management Concepts Identifying Security Risk Management Prerequisites Assessing Risk Conducting Decision Support Implementing Controls and Measuring Program Effectiveness
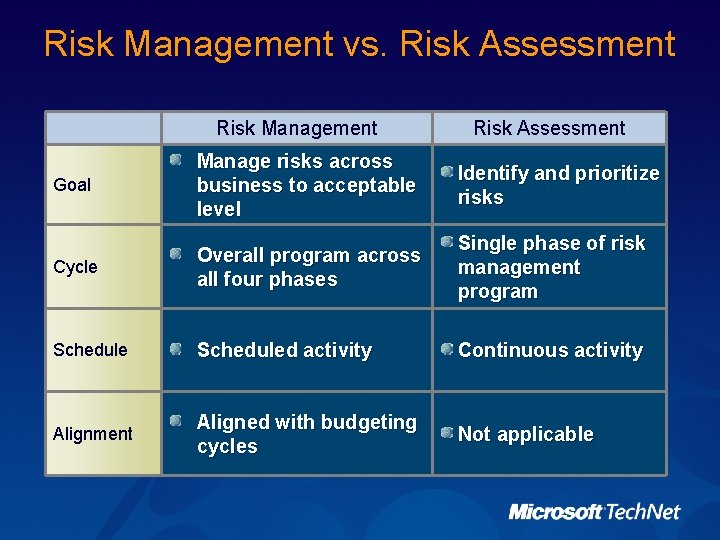
Risk Management vs. Risk Assessment Risk Management Risk Assessment Goal Manage risks across business to acceptable level Identify and prioritize risks Cycle Overall program across all four phases Single phase of risk management program Scheduled activity Continuous activity Alignment Aligned with budgeting cycles Not applicable
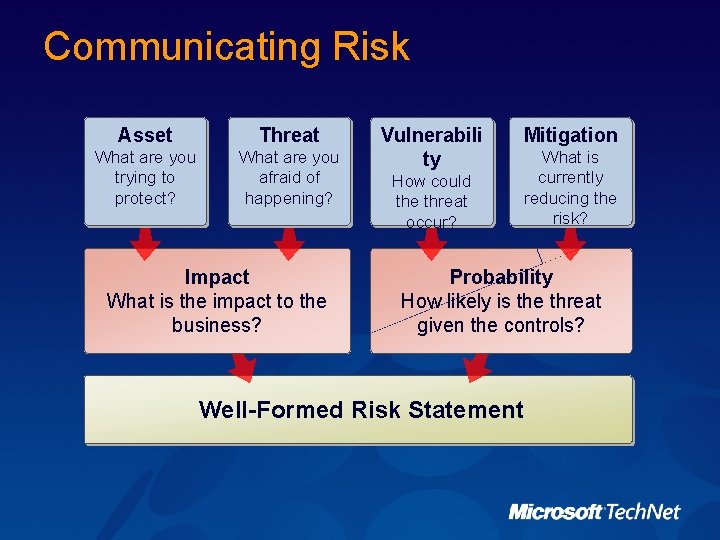
Communicating Risk Asset Threat What are you trying to protect? What are you afraid of happening? Impact What is the impact to the business? Vulnerabili ty Mitigation How could the threat occur? What is currently reducing the risk? Probability How likely is the threat given the controls? Well-Formed Risk Statement
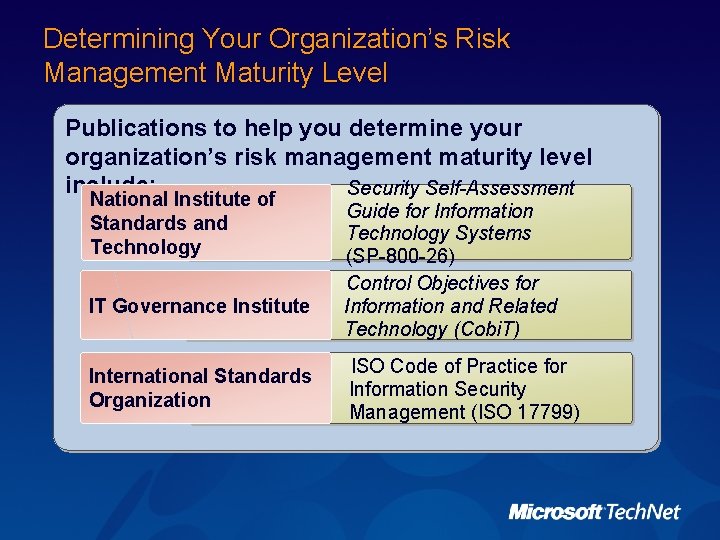
Determining Your Organization’s Risk Management Maturity Level Publications to help you determine your organization’s risk management maturity level include: Security Self-Assessment National Institute of Standards and Technology IT Governance Institute International Standards Organization Guide for Information Technology Systems (SP-800 -26) Control Objectives for Information and Related Technology (Cobi. T) ISO Code of Practice for Information Security Management (ISO 17799)
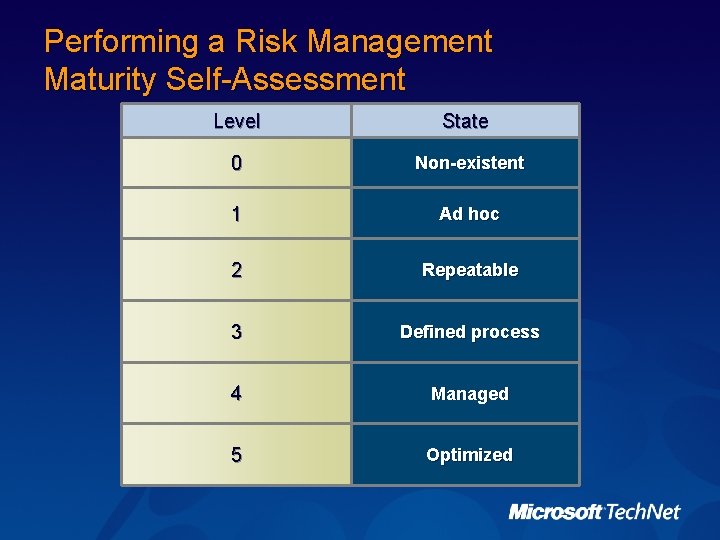
Performing a Risk Management Maturity Self-Assessment Level State 0 Non-existent 1 Ad hoc 2 Repeatable 3 Defined process 4 Managed 5 Optimized
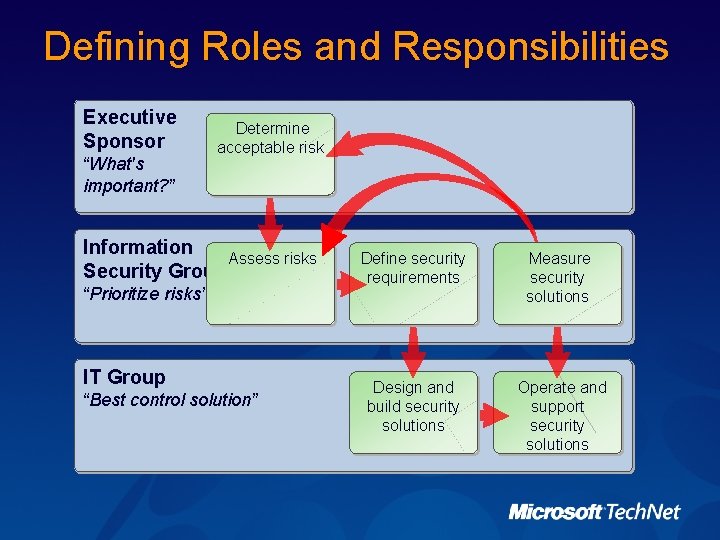
Defining Roles and Responsibilities Executive Sponsor “What's important? ” Determine acceptable risk Information Assess risks Security Group “Prioritize risks” IT Group “Best control solution” Define security requirements Measure security solutions Design and build security solutions Operate and support security solutions
Assessing Risk Security Risk Management Concepts Identifying Security Risk Management Prerequisites Assessing Risk Conducting Decision Support Implementing Controls and Measuring Program Effectiveness
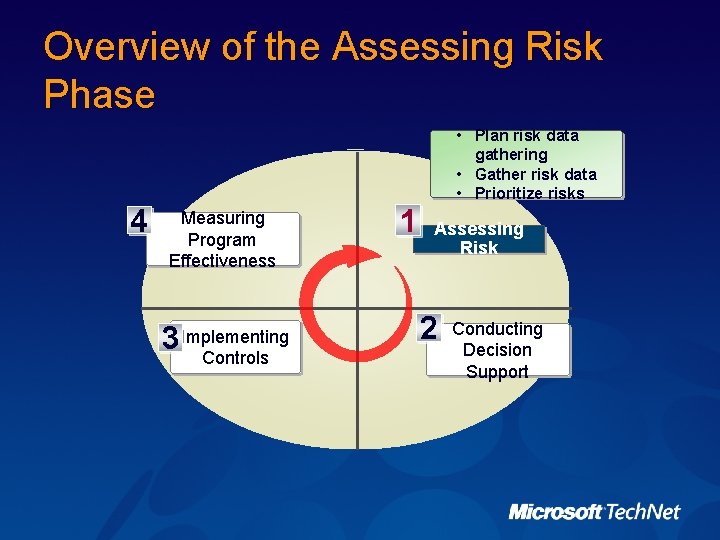
Overview of the Assessing Risk Phase • Plan risk data gathering • Gather risk data • Prioritize risks 4 Measuring Program Effectiveness 3 Implementing Controls 1 Assessing Risk 2 Conducting Decision Support
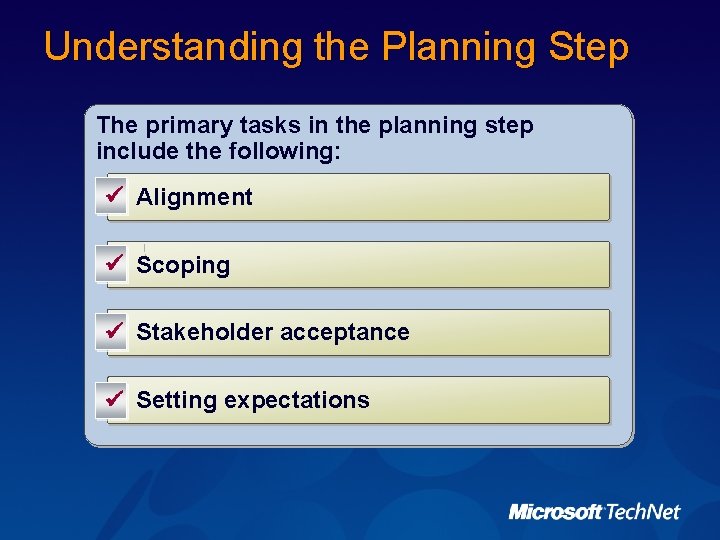
Understanding the Planning Step The primary tasks in the planning step include the following: ü Alignment ü Scoping ü Stakeholder acceptance ü Setting expectations
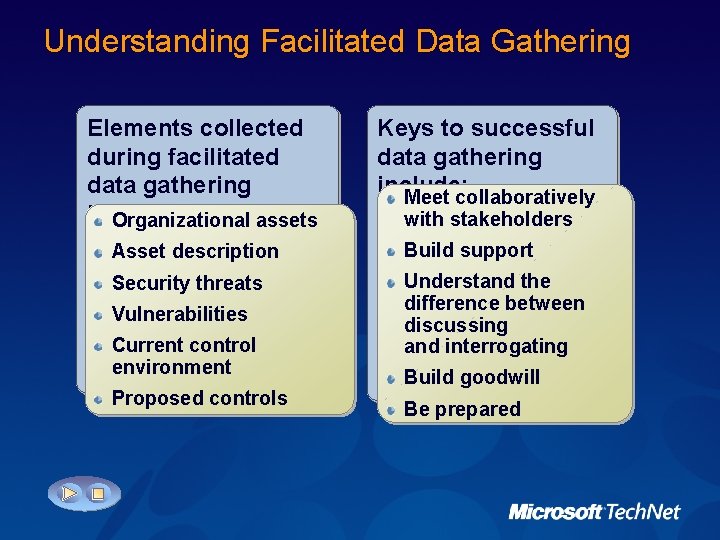
Understanding Facilitated Data Gathering Elements collected during facilitated data gathering include: Organizational assets Keys to successful data gathering include: Meet collaboratively with stakeholders Asset description Build support Security threats Understand the difference between discussing and interrogating Vulnerabilities Current control environment Proposed controls Build goodwill Be prepared
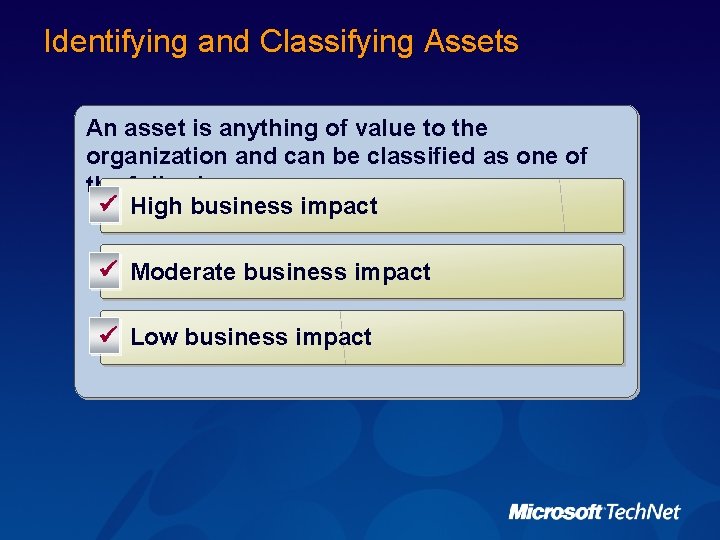
Identifying and Classifying Assets An asset is anything of value to the organization and can be classified as one of the following: ü High business impact ü Moderate business impact ü Low business impact
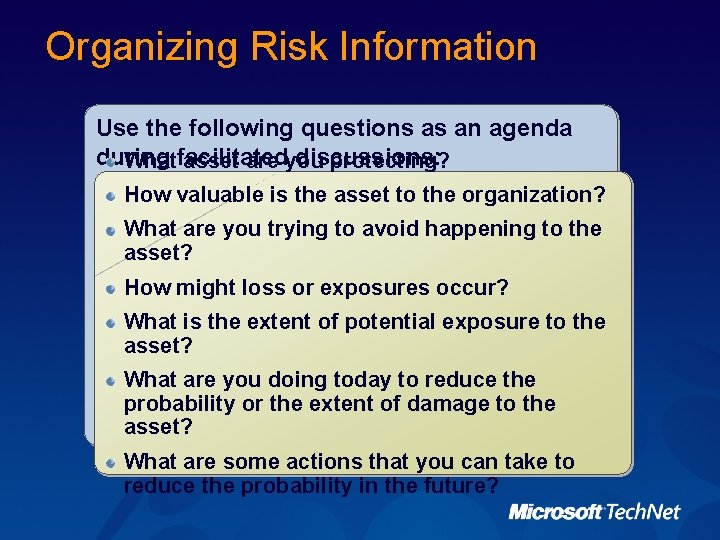
Organizing Risk Information Use the following questions as an agenda during discussions: Whatfacilitated asset are you protecting? How valuable is the asset to the organization? What are you trying to avoid happening to the asset? How might loss or exposures occur? What is the extent of potential exposure to the asset? What are you doing today to reduce the probability or the extent of damage to the asset? What are some actions that you can take to reduce the probability in the future?
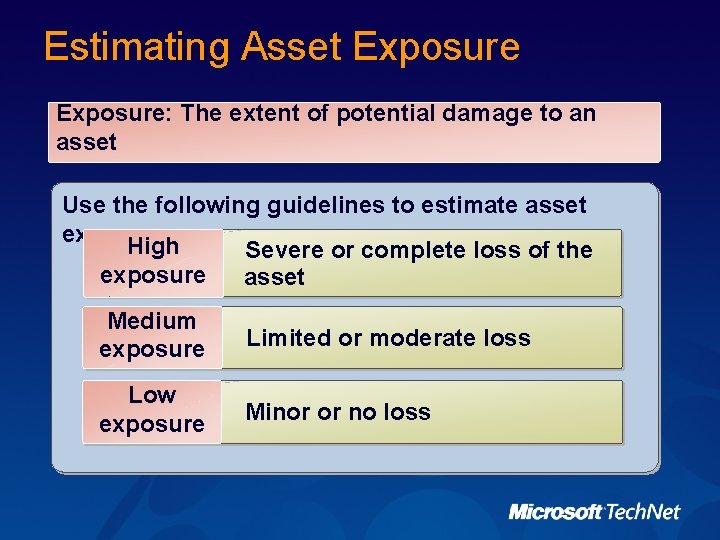
Estimating Asset Exposure: The extent of potential damage to an asset Use the following guidelines to estimate asset exposure: High Severe or complete loss of the exposure asset Medium exposure Limited or moderate loss Low exposure Minor or no loss
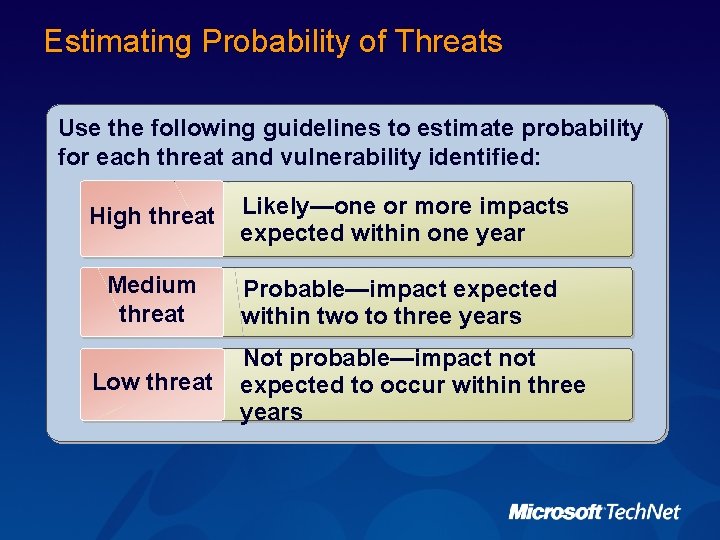
Estimating Probability of Threats Use the following guidelines to estimate probability for each threat and vulnerability identified: High threat Likely—one or more impacts expected within one year Medium threat Probable—impact expected within two to three years Low threat Not probable—impact not expected to occur within three years
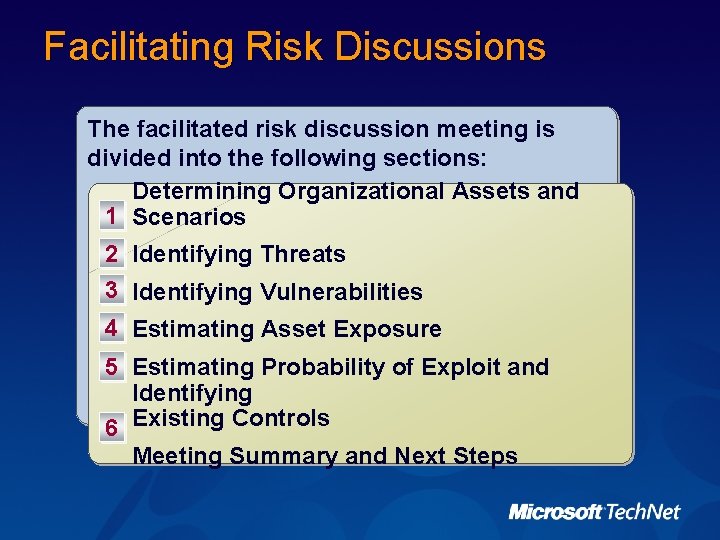
Facilitating Risk Discussions The facilitated risk discussion meeting is divided into the following sections: Determining Organizational Assets and 1 Scenarios 2 Identifying Threats 3 Identifying Vulnerabilities 4 Estimating Asset Exposure 5 Estimating Probability of Exploit and Identifying 6 Existing Controls Meeting Summary and Next Steps
Walk-through Scenario 1: Facilitating Risk Discussions Facilitating a risk discussion meeting for Woodgrove Bank
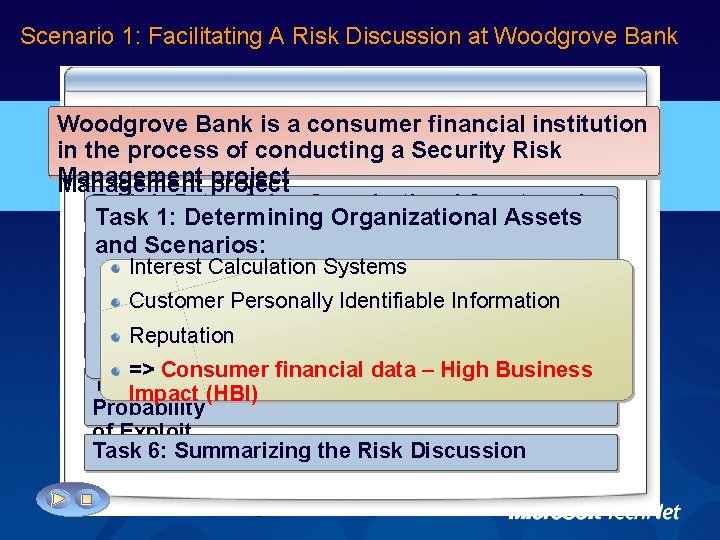
Scenario 1: Facilitating A Risk Discussion at Woodgrove Bank is is a a consumer financial institution Woodgrove in the process of of conducting a a Security Risk in Management project Management Task 1: Determining Organizational Assets and 2: Identifying Task 6: the Risk Discussion: 5: Existing Controls and Task 1: Determining Organizational Assets 3: Vulnerabilities: 4: Summarizing Estimating Asset Exposure: Breach of integrity. Threats: through trusted employee Scenarios Threat of a loss Threats ofbut integrity to consumer Probability and Scenarios: abuse: Damaging not severe. Each financial Task 2: Identifying Theft of financial advisor credentials by the Risk Assessment Facilitator summarizes financial data Interest Calculation Systems advisor only access customer dataorthat he or Agreement that highlights their remote mobile trustedcan employee abuse using non-technical of discussion Exploit: and thehosts, assets, threats, Task 3: manages. Identifying Vulnerabilities she hosts, dofor not receive the same level of or attacks, example, social engineering and vulnerabilities discussed. Customer Personally Identifiable Information management as those on credential theft on eavesdropping Breach of integrity through Reputation Task 4: LAN Estimating Asset Exposure the. LAN hosts: May result in a severe, or high, level Theft of financial advisor credentials off local => Consumer financial data – High the Business of damage. area network (LAN) hosts through use of Task 5: Identifying Existing Controls and Impact (HBI) outdated Probability Breach of security integrityconfigurations through credential theft on of Exploit mobile Could have acredentials severe, or high, Theft ofhosts: financial advisor off level Task 6: Summarizing the Risk Discussion of damage. discussion group notesof that the remote, or The mobile, hosts as a result security configurations on remote hosts often lag outdated security configurations behind LAN systems.
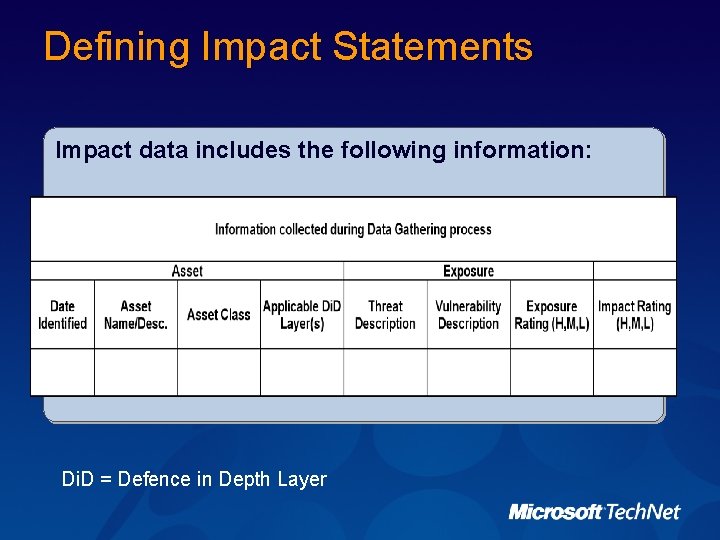
Defining Impact Statements Impact data includes the following information: Di. D = Defence in Depth Layer
Walk-through Scenario 2: Defining Impact Statements Defining an impact statement for Woodgrove Bank
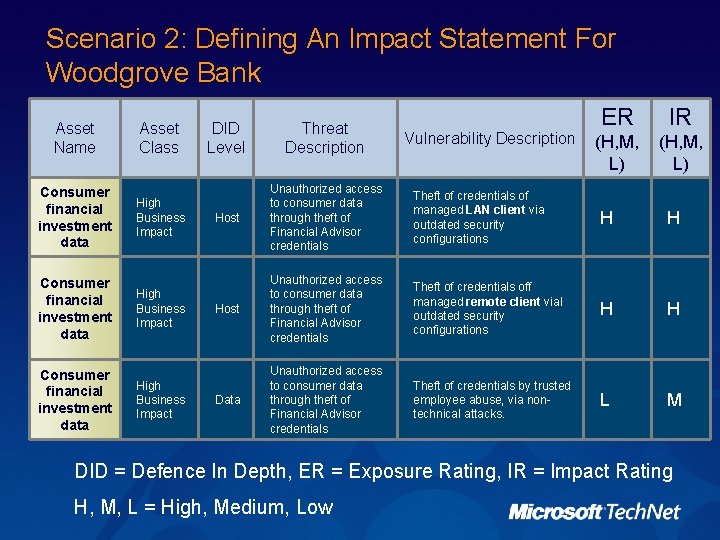
Scenario 2: Defining An Impact Statement For Woodgrove Bank Asset Name Asset Class Consumer financial investment data High Business Impact ER IR (H, M, L) DID Level Threat Description Host Unauthorized access to consumer data through theft of Financial Advisor credentials Theft of credentials of managed LAN client via outdated security configurations H H Host Unauthorized access to consumer data through theft of Financial Advisor credentials Theft of credentials off managed remote client vial outdated security configurations H H Data Unauthorized access to consumer data through theft of Financial Advisor credentials Theft of credentials by trusted employee abuse, via nontechnical attacks. L M Vulnerability Description DID = Defence In Depth, ER = Exposure Rating, IR = Impact Rating H, M, L = High, Medium, Low
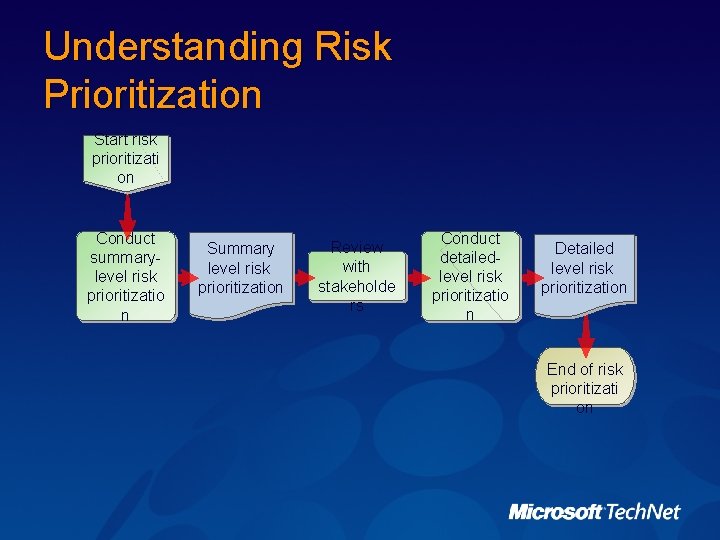
Understanding Risk Prioritization Start risk prioritizati on Conduct summarylevel risk prioritizatio n Summary level risk prioritization Review with stakeholde rs Conduct detailedlevel risk prioritizatio n Detailed level risk prioritization End of risk prioritizati on
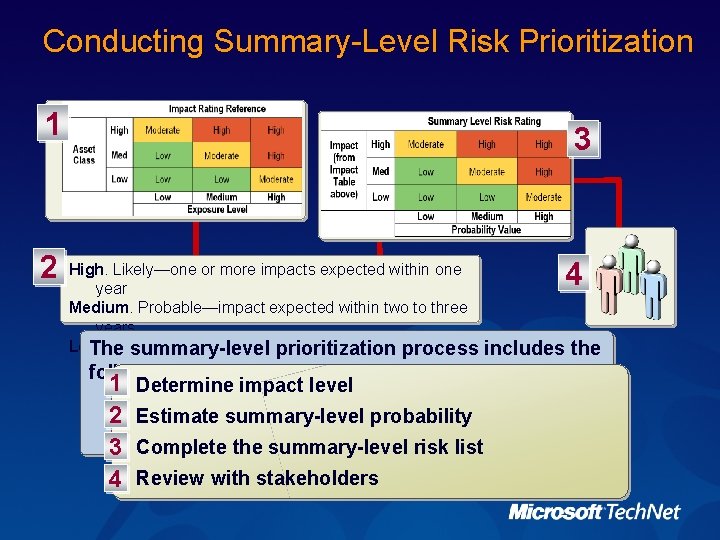
Conducting Summary-Level Risk Prioritization 1 2 3 High. Likely—one or more impacts expected within one year Medium. Probable—impact expected within two to three years Low. Notsummary-level probable—impact not expected to occur within The prioritization process three years following: 1 Determine impact level 2 Estimate summary-level probability 3 Complete the summary-level risk list 4 Review with stakeholders 4 includes the
Walk-through Scenario 3: Conducting Summary-Level Risk Prioritization Conducting a summary-level risk prioritization for Woodgrove Bank
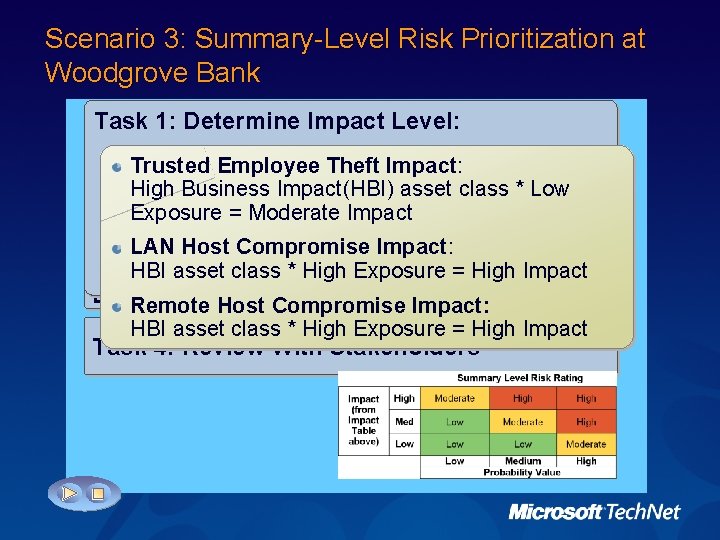
Scenario 3: Summary-Level Risk Prioritization at Woodgrove Bank Task 2: Summary Level Probability: 4: Review With Stakeholders 1: Determine Impact Level: 3: Estimate Complete the Summary-Level Risk Trusted Employee abuse risk is rated as Low in Trusted Employee Theft Probability: Risk: Task Determine Level List: Trusted Employee Theft the 1: summary level. Impact risk list and does not. Low need to Trusted Employee Theft Impact: = Low Moderate Impact * Low Probability graduate to. Compromise the. Impact(HBI) detailed level risk prioritization High Host Business asset class. Medium * Low LAN Probability: LAN Host Risk: step Exposure =Compromise Moderate Impact Task 2: Estimate Summary Level Probability Remote Host* Compromise Probability: High Impact Medium Probability = High LAN host compromise risks are LAN and Hostremote Compromise Impact: Remote Host Compromise both rated as high and. Summary-Level so are. Risk: then= prioritized Task 3: asset Complete Riskat HBI class * the High Exposure High Impactlevel * High Probability = High detailed Listthe Remote Host Compromise Impact: Enter Results in *the Impact Statement HBI asset class High Exposure = High Impact spreadsheet Task 4: Review With Stakeholders
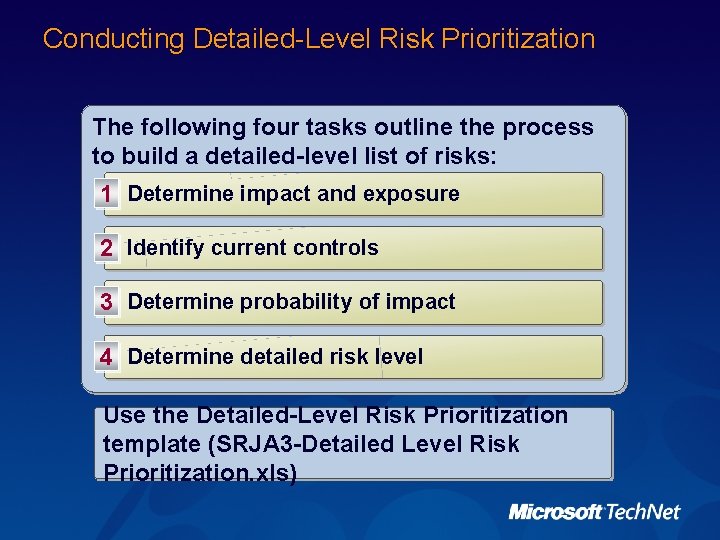
Conducting Detailed-Level Risk Prioritization The following four tasks outline the process to build a detailed-level list of risks: 1 Determine impact and exposure 2 Identify current controls 3 Determine probability of impact 4 Determine detailed risk level Use the Detailed-Level Risk Prioritization template (SRJA 3 -Detailed Level Risk Prioritization. xls)
Walk-through Scenario 4: Conducting Detailed-Level Risk Prioritization Conducting a detailed-level risk prioritization for Woodgrove Bank
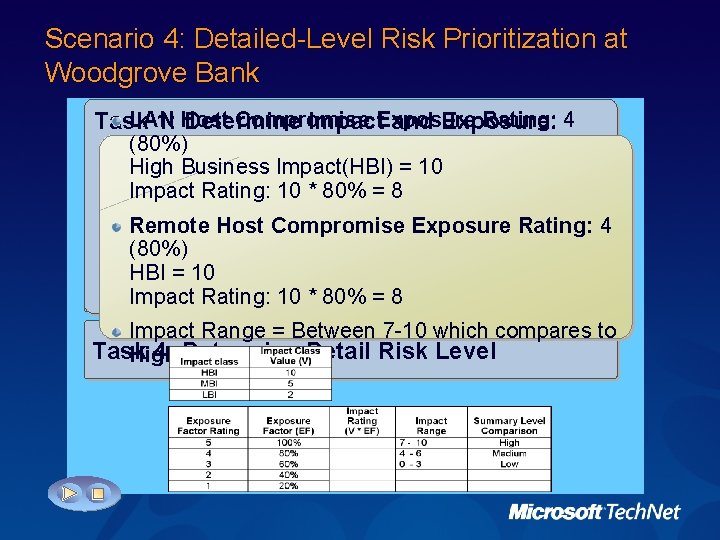
Scenario 4: Detailed-Level Risk Prioritization at Woodgrove Bank LAN Compromise Exposure Rating: 4 Task 4: Determine Detail Risk 1: Impact and Level: Exposure: 2: Identify Current Controls: 3: Host Probability of Impact: LAN and remote hosts: Likely that all vulnerability (80%) Financial Advisors can only access accounts they Task 1: Determine Impact and Exposure Impact Rating * Probability Rating attributes theexposure High category will be 100 seen inside High Business Impact(HBI) = 10 own; thus, inthe is less than percent. and outside • LAN: 8 *Rating: 6 = Woodgrove's 4810 * 80% =LAN Impact 8 environment in the E-mail notices to patch or update hosts are near future. Task 2: Identify Current Controls • Remote hosts: 8 to * 10 = 80 Remote Host Compromise Exposure proactively sent all users. Vulnerability value = 5 for both risks Rating: 4 (80%)rate an overall risk of High • Both Antivirus and patch updates are measured and Control Effectiveness: HBI = 10 enforced on the LAN every few of hours. This control Task 3: Determine Probability Impact LAN: Result of 10 Control Questions=1 Impact Rating: * 80%Effectiveness =8 reduces timeofwindow LAN hosts are Remote: the Result Controlwhen Effectiveness Impact Range = Between 7 -10 which compares to vulnerable to attack. Questions=5 Task 4: Determine Detail Risk Level High Total Probability Rating: (Sum of Vulnerability and Control Effectiveness) LAN: 6 Remote: 10
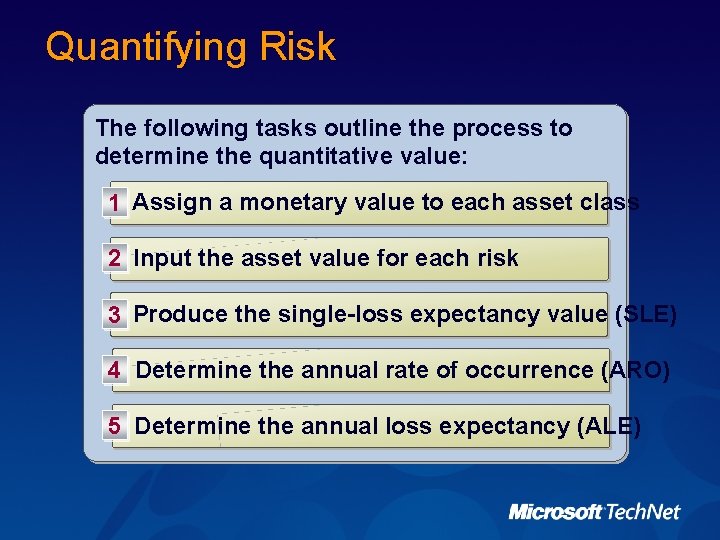
Quantifying Risk The following tasks outline the process to determine the quantitative value: 1 Assign a monetary value to each asset class 2 Input the asset value for each risk 3 Produce the single-loss expectancy value (SLE) 4 Determine the annual rate of occurrence (ARO) 5 Determine the annual loss expectancy (ALE)
Walk-through Scenario 5: Quantifying Risk Quantifying risk for Woodgrove Bank
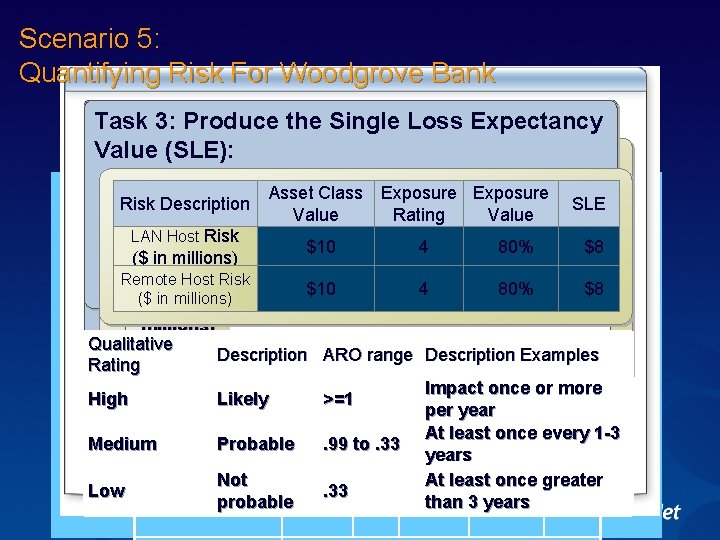
Scenario 5: Quantifying Risk For Woodgrove Bank Task 2: the Asset Value: 1: Assign Values to Asset 4: Determine the Annual Rate of 3: Produce. Monetary the Single Loss Expectancy 5: Identify Loss Using 5% Materiality Guideline for valuing assets Task 1: (SLE): Assign Monetary Values to Asset Classes: Occurrence (ARO): Value Expectancy (ALE) Consumer financial data = HBI Asset Class LAN Host ARO: Leveraging the qualitative assessment Net Income: $200 Million annually (SLE * =ARO) of Medium the Security Risk. Exposure Management HBI $10 probability, Million Asset Class Exposure Asset Risk Exposure Risk SLE HBIDescription Asset Class: $10 to. Million (200 * 5%) Team estimates the risk occur at least once Class SLE AROin two ALE Value Rating Value Task 2: Identify the Asset Value Description Value Asset Value =estimated $10 Rating Million years; thus, the ARO is. 5 Value LAN Host Risk MBI Asset Class: $10 $5 Million (based on 80% past $8 4 ($ in millions) LAN Host Remote Host ARO: Leveraging the qualitative spending) Task 3: Risk Produce the Single Loss Expectancy Remote Host Risk assessment of High probability, the Security Risk $8 $10 4 80% $8 0. 5 $4 LBI Asset Class: $1 Million (based on past ($ in Value (SLE) ($millions) in Management Team estimates the risk to occur at least spending) millions) once per year; thus, the estimated ARO is 1. Qualitative Task. High 4: Determine the Annual Exposu Rate of. Exposure Occurrence Remote Description Examples Business Impact ARO range Description Rating re (ARO) Host Value. Risk = $M Factor % $10 4 80% $8 once 1 or more $8 Rating Impact ($ in High Likely >=1 Task 5: Determine the Annual Loss Expectancy per year 5 100 millions) (ALE) At least once Asset Class 4 80 every 1 -3 Medium Probable. 99 to. 33 (SLEHBI * ARO) years Value $M 3 60 MBI Value. Not $M/2 2 40 greater At least once Low. 33 than 1 3 years 20 LBI Valueprobable$ M / 4
Assessing Risk: Best Practices ü Analyze risks during the data gathering process ü Conduct research to build credibility for estimating probability ü Communicate risk in business terms ü Reconcile new risks with previous risks
Conducting Decision Support Security Risk Management Concepts Identifying Security Risk Management Prerequisites Assessing Risk Conducting Decision Support Implementing Controls and Measuring Program Effectiveness
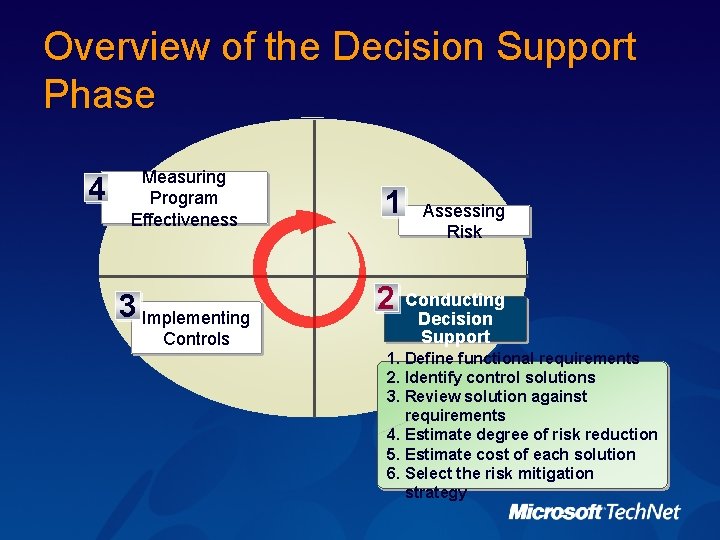
Overview of the Decision Support Phase 4 Measuring Program Effectiveness 3 Implementing Controls 1 2 Assessing Risk Conducting Decision Support 1. Define functional requirements 2. Identify control solutions 3. Review solution against requirements 4. Estimate degree of risk reduction 5. Estimate cost of each solution 6. Select the risk mitigation strategy
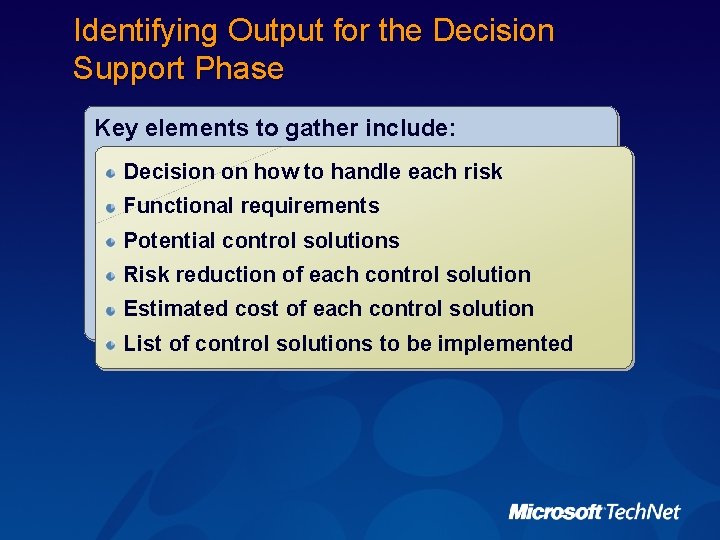
Identifying Output for the Decision Support Phase Key elements to gather include: Decision on how to handle each risk Functional requirements Potential control solutions Risk reduction of each control solution Estimated cost of each control solution List of control solutions to be implemented
Considering the Decision Support Options for handling risk: ü Accepting the current risk ü Implementing controls to reduce risk
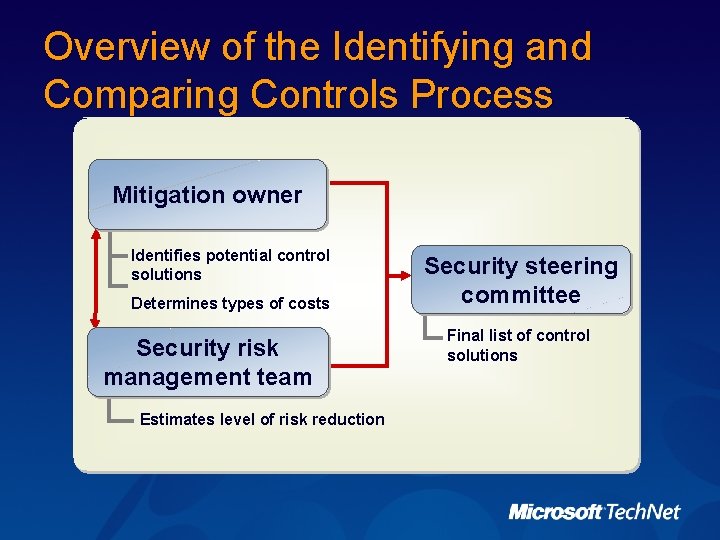
Overview of the Identifying and Comparing Controls Process Mitigation owner Identifies potential control solutions Determines types of costs Security risk management team Estimates level of risk reduction Security steering committee Final list of control solutions
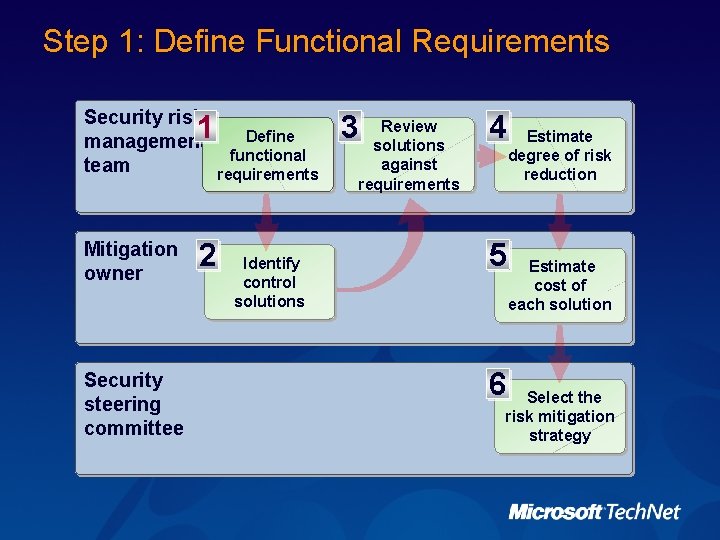
Step 1: Define Functional Requirements Security risk management team 1 Mitigation owner Security steering committee 2 Define functional requirements Identify control solutions 3 Review solutions against requirements 4 5 6 Estimate degree of risk reduction Estimate cost of each solution Select the risk mitigation strategy
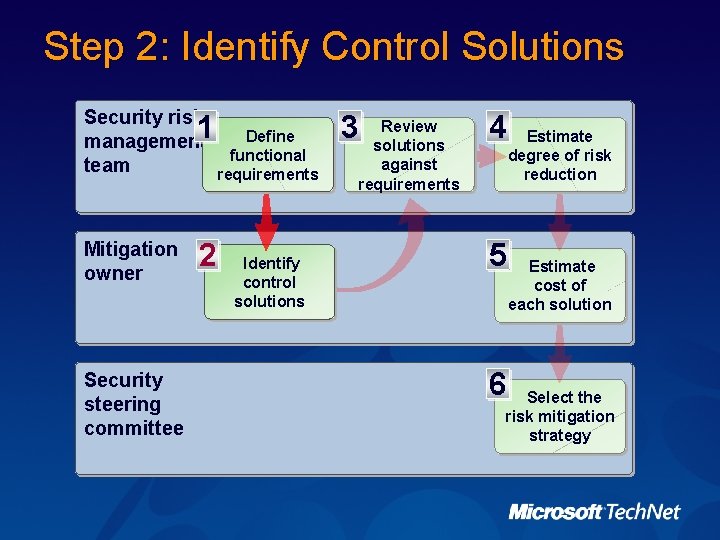
Step 2: Identify Control Solutions Security risk management team 1 Mitigation owner Security steering committee 2 Define functional requirements Identify control solutions 3 Review solutions against requirements 4 5 6 Estimate degree of risk reduction Estimate cost of each solution Select the risk mitigation strategy
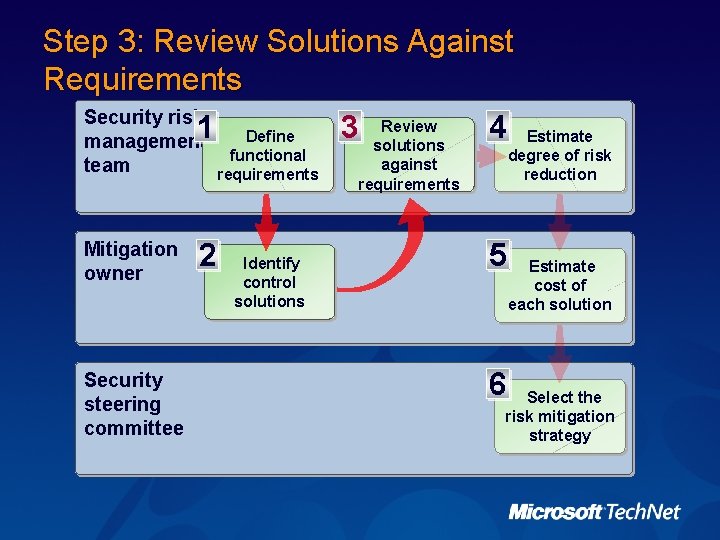
Step 3: Review Solutions Against Requirements Security risk Review 1 3 4 Define management solutions functional requirements team Mitigation owner Security steering committee 2 Identify control solutions Estimate degree of risk reduction against requirements 5 6 Estimate cost of each solution Select the risk mitigation strategy
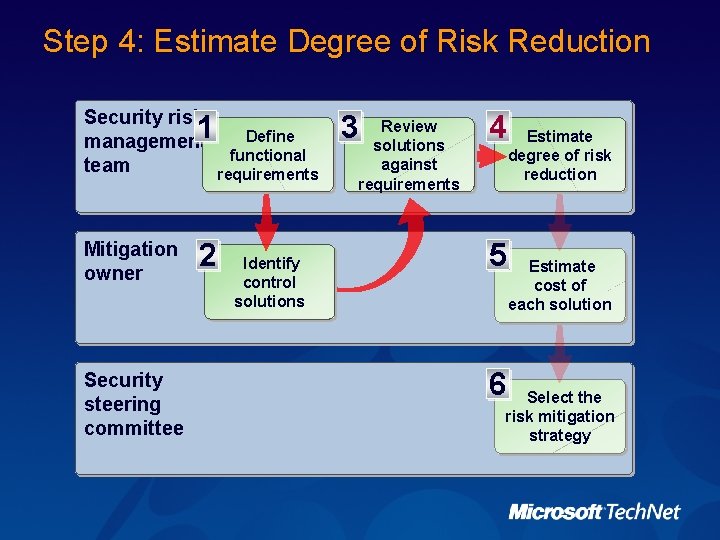
Step 4: Estimate Degree of Risk Reduction Security risk management team 1 Mitigation owner Security steering committee 2 Define functional requirements Identify control solutions 3 Review solutions against requirements 4 5 6 Estimate degree of risk reduction Estimate cost of each solution Select the risk mitigation strategy
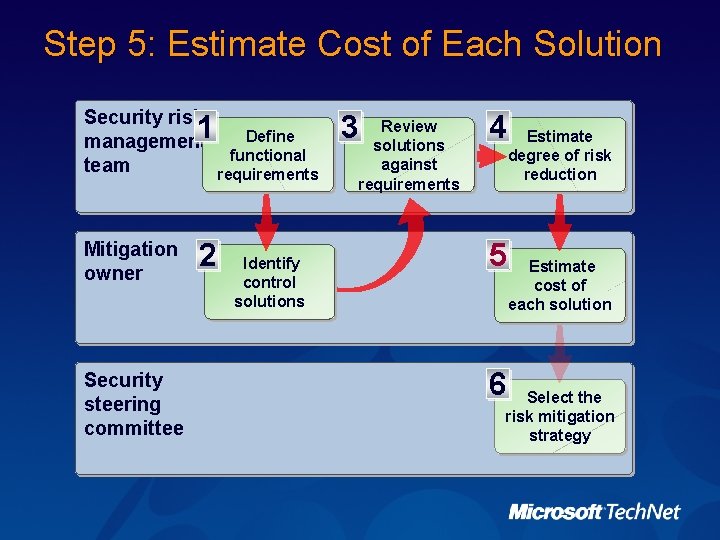
Step 5: Estimate Cost of Each Solution Security risk management team 1 Mitigation owner Security steering committee 2 Define functional requirements Identify control solutions 3 Review solutions against requirements 4 5 6 Estimate degree of risk reduction Estimate cost of each solution Select the risk mitigation strategy
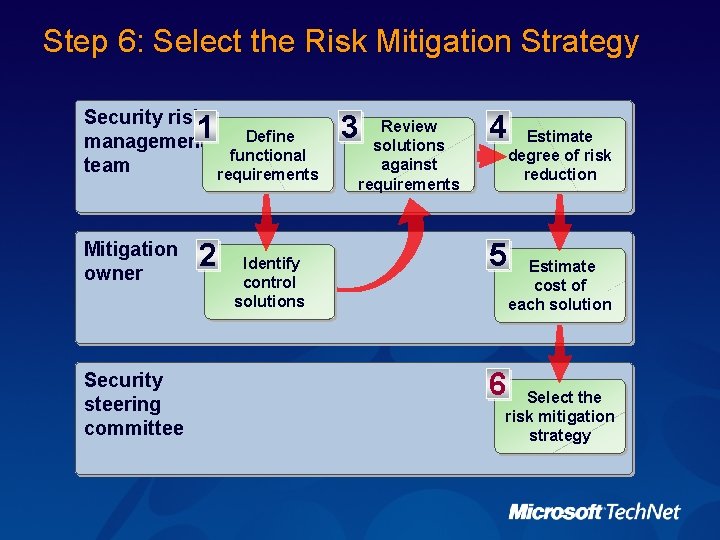
Step 6: Select the Risk Mitigation Strategy Security risk management team 1 Mitigation owner Security steering committee 2 Define functional requirements Identify control solutions 3 Review solutions against requirements 4 5 6 Estimate degree of risk reduction Estimate cost of each solution Select the risk mitigation strategy
Conducting Decision Support: Best Practices ü Consider assigning a security technologist to each identified risk ü Set reasonable expectations ü Build team consensus ü Focus on the amount of risk after the mitigation solution
Implementing Controls and Measuring Program Effectiveness Security Risk Management Concepts Identifying Security Risk Management Prerequisites Assessing Risk Conducting Decision Support Implementing Controls and Measuring Program Effectiveness
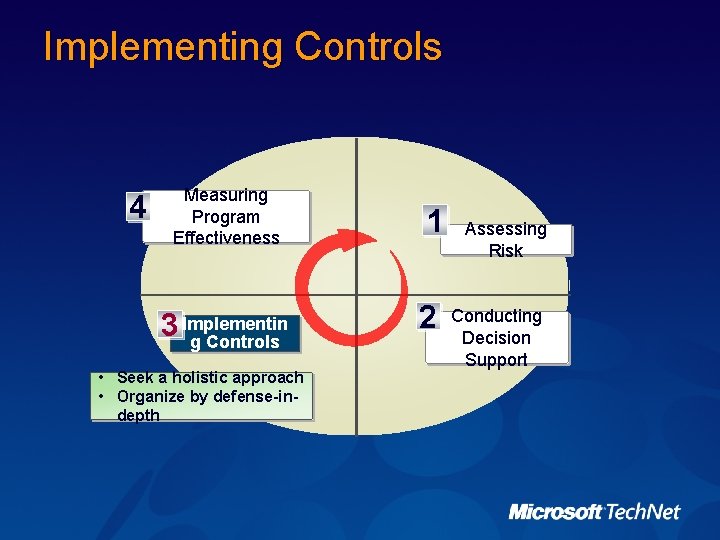
Implementing Controls 4 Measuring Program Effectiveness 3 Implementin g Controls • Seek a holistic approach • Organize by defense-indepth 1 2 Assessing Risk Conducting Decision Support
Organizing the Control Solutions Critical success determinants to organizing control solutions include: ü Communication ü Team scheduling ü Resource requirements
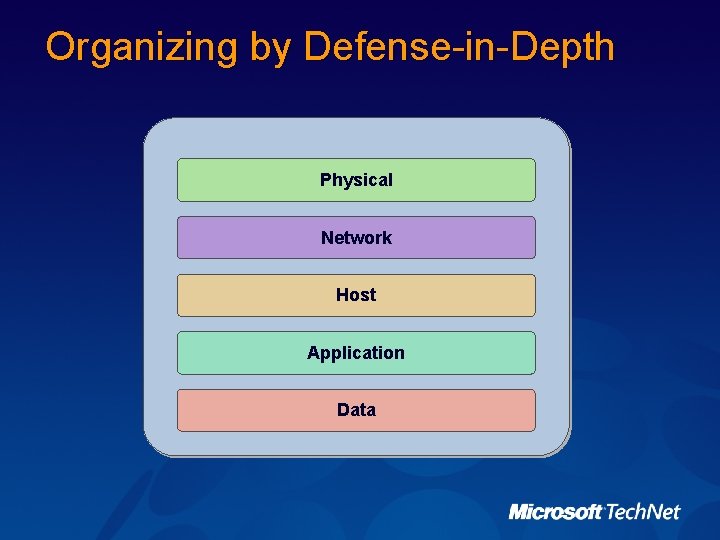
Organizing by Defense-in-Depth Physical Network Host Application Data
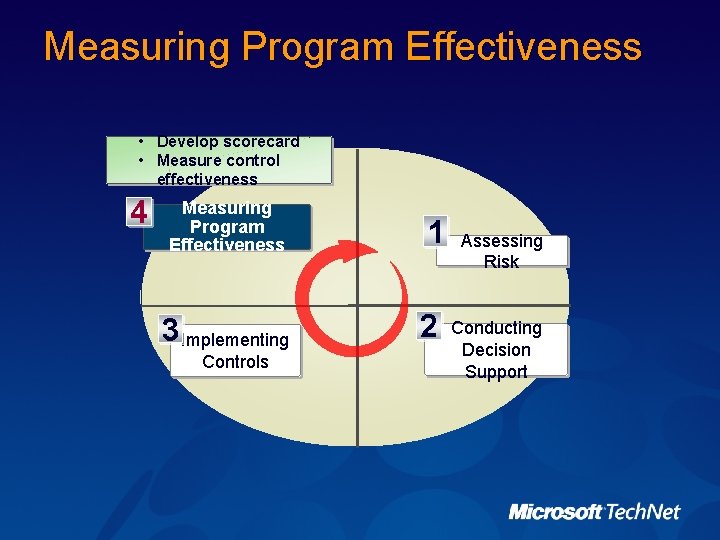
Measuring Program Effectiveness • Develop scorecard • Measure control effectiveness 4 Measuring Program Effectiveness 3 Implementing Controls 1 2 Assessing Risk Conducting Decision Support
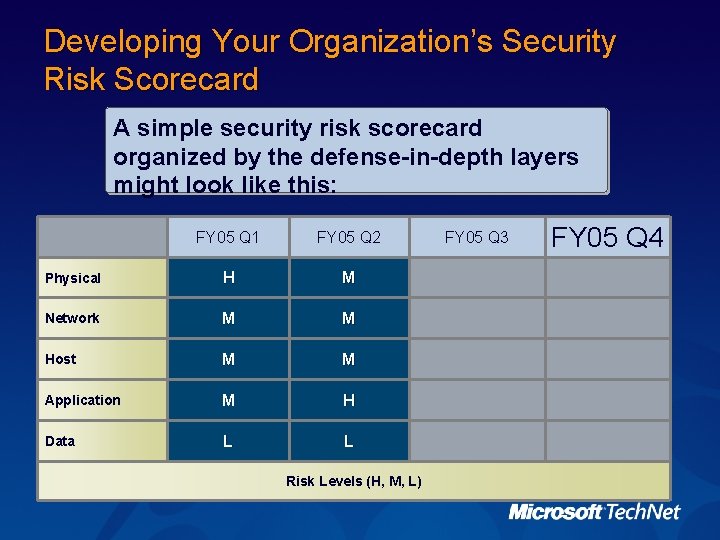
Developing Your Organization’s Security Risk Scorecard A simple security risk scorecard organized by the defense-in-depth layers might look like this: FY 05 Q 1 FY 05 Q 2 Physical H M Network M M Host M M Application M H Data L L Risk Levels (H, M, L) FY 05 Q 3 FY 05 Q 4
Measuring Control Effectiveness Methods to measure the effectiveness of implemented controls include: ü Direct testing ü Submitting periodic compliance reports ü Evaluating widespread security incidents
Session Summary ü One common thread between most risk management methodologies is that each is typically based on quantitative risk management, qualitative risk management, or a combination of the two ü Determining your organization’s maturity level will help focus on the appropriate implementation and timeframe for your risk management strategy ü Risk assessment consists of conducting a summary-level risk prioritization, and then conducting a detailed-level risk prioritization on high-impact risks ü ü The Microsoft Security Risk Management Guide provides a number of tools and templates to assist with the entire risk management process The Microsoft defense-in-depth approach organizes controls into several broad layers that make up the defense-in-depth model

Next Steps Find additional security training events: http: //www. microsoft. com/seminar/events/security. mspx Sign up for security communications: http: //www. microsoft. com/technet/security/signup/ default. mspx Order the Security Guidance Kit: http: //www. microsoft. com/security/guidance/order/ default. mspx Get additional security tools and content: http: //www. microsoft. com/security/guidance
Event Information What’s Next? Technical Roadshow Post Event Website www. microsoft. com/uk/techroadshow/postevents Available from Monday 18 th April Please complete your Evaluation Form!

http: //www. microsoft. com/Tw. C © 2004 Microsoft Corporation. All rights reserved. This presentation is for informational purposes only. Microsoft makes no warranties, express or implied, in this summary.
- Slides: 66