Security Proofs for IdentityBased Identification and Signature Schemes
Security Proofs for Identity-Based Identification and Signature Schemes Mihir Bellare University of California at San Diego, USA Chanathip Nampre Thammasat University, Thailand Gregory Neven Katholieke Universiteit Leuven, Belgium
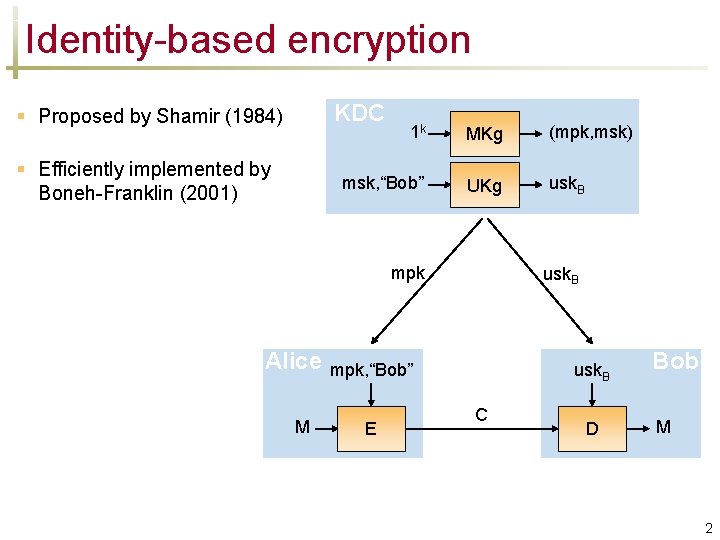
Identity-based encryption KDC § Proposed by Shamir (1984) § Efficiently implemented by Boneh-Franklin (2001) 1 k MKg (mpk, msk) msk, “Bob” UKg usk. B mpk Alice M usk. B mpk, “Bob” E usk. B C D Bob M 2
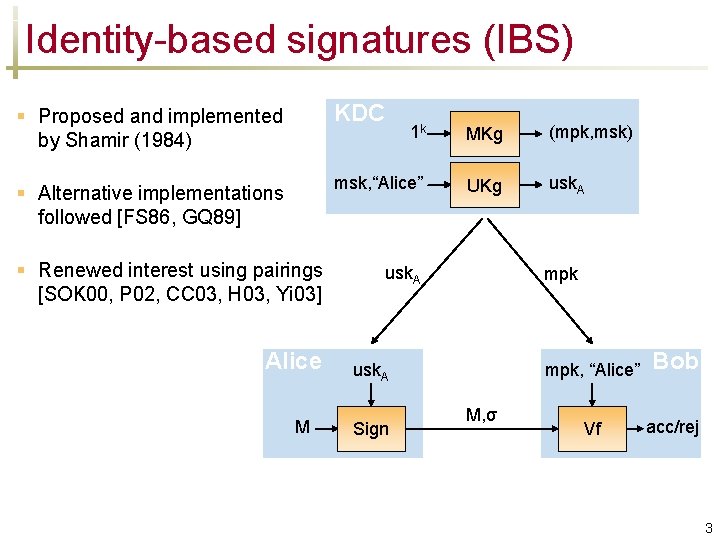
Identity-based signatures (IBS) § Proposed and implemented by Shamir (1984) KDC 1 k MKg (mpk, msk) § Alternative implementations followed [FS 86, GQ 89] msk, “Alice” UKg usk. A § Renewed interest using pairings [SOK 00, P 02, CC 03, H 03, Yi 03] Alice M usk. A mpk usk. A Sign M, σ mpk, “Alice” Bob Vf acc/rej 3
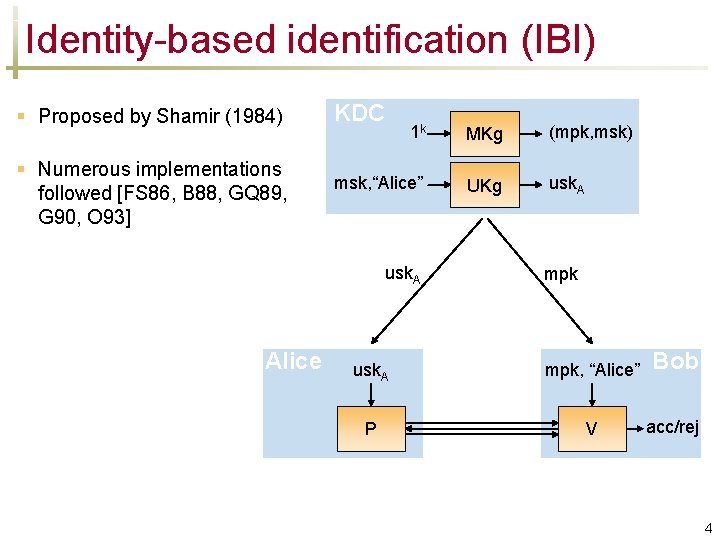
Identity-based identification (IBI) § Proposed by Shamir (1984) § Numerous implementations followed [FS 86, B 88, GQ 89, G 90, O 93] KDC 1 k MKg (mpk, msk) msk, “Alice” UKg usk. A Alice mpk usk. A mpk, “Alice” Bob P V acc/rej 4
Provable security of IBI/IBS schemes § IBI schemes § no appropriate security definitions § proofs in weak model (fixed identity) or entirely lacking § IBS schemes § good security definition [CC 03] § security proofs for some schemes directly [CC 03] or through “trapdoor SS” to IBS transform [DKXY 03] § some gaps remain 5
![Existing security proofs for § identification schemes underlying IBI schemes e. g. [FFS 88] Existing security proofs for § identification schemes underlying IBI schemes e. g. [FFS 88]](http://slidetodoc.com/presentation_image_h/0617538fa8508787e22fa7b0d06c8672/image-6.jpg)
Existing security proofs for § identification schemes underlying IBI schemes e. g. [FFS 88] prove [FS 86] [BP 02] prove [GQ 89] § signature schemes underlying IBS schemes e. g. analyses of Fiat-Shamir transform [PS 96, OO 98, AABN 02] refer to standard identification (SI) and signature (SS) schemes. Build on these proofs, rather than from scratch. 6
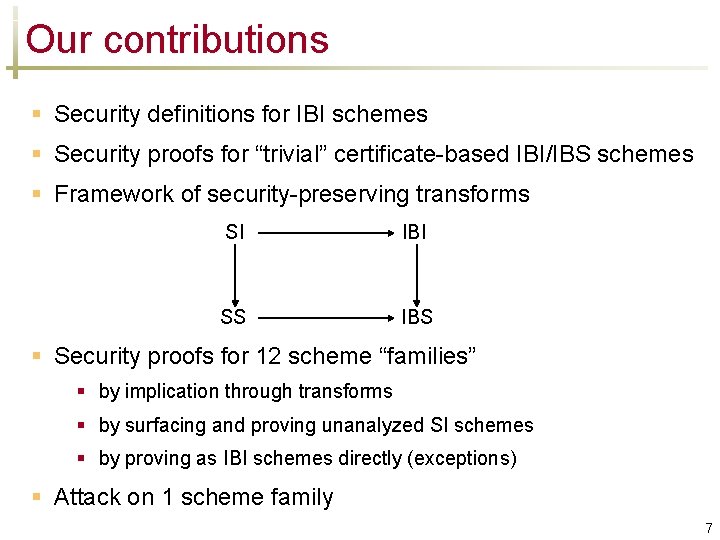
Our contributions § Security definitions for IBI schemes § Security proofs for “trivial” certificate-based IBI/IBS schemes § Framework of security-preserving transforms SI IBI SS IBS § Security proofs for 12 scheme “families” § by implication through transforms § by surfacing and proving unanalyzed SI schemes § by proving as IBI schemes directly (exceptions) § Attack on 1 scheme family 7
Independent work Kurosawa, Heng (PKC 2004): § security definitions for IBI schemes § transform from SS to IBI schemes 8
![Security of IBS and IBI schemes § IBS schemes: uf-cma security [CC 03] mpk Security of IBS and IBI schemes § IBS schemes: uf-cma security [CC 03] mpk](http://slidetodoc.com/presentation_image_h/0617538fa8508787e22fa7b0d06c8672/image-9.jpg)
Security of IBS and IBI schemes § IBS schemes: uf-cma security [CC 03] mpk Sign(usk. ID, ·) M, ID σ ID F Initialize ID usk. ID Corrupt ID, M, σ § IBI schemes: imp-pa, imp-aa, imp-ca security 1. Learning phase: Initialize and corrupt oracles, see conversation transcripts (pa), interact with provers sequentially (aa) or in parallel (ca) 2. Attack phase: Impersonate uncorrupted identity IDbreak of adversary’s choice Oracles blocked of for ID = IDbreak 9
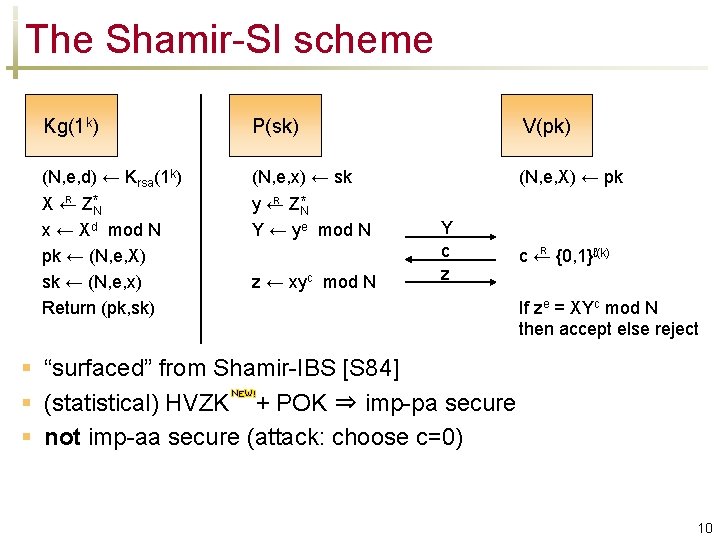
The Shamir-SI scheme Kg(1 k) P(sk) V(pk) (N, e, d) ← Krsa(1 k) R X← Z*N (N, e, x) ← sk R y← Z*N (N, e, X) ← pk x ← Xd mod N pk ← (N, e, X) sk ← (N, e, x) Return (pk, sk) Y ← ye mod N z ← xyc mod N Y c z R c← {0, 1}ℓ(k) If ze = XYc mod N then accept else reject § “surfaced” from Shamir-IBS [S 84] § (statistical) HVZK + POK ⇒ imp-pa secure § not imp-aa secure (attack: choose c=0) 10

The Shamir-SS scheme Kg(1 k) Sign(sk, M) (N, e, d) ← Krsa(1 k) R X← Z*N (N, e, x) ← sk R y← Z*N x ← Xd mod N pk ← (N, e, X) sk ← (N, e, x) Return (pk, sk) Y ← ye mod N c ← H(Y, M) z ← xyc mod N σ ← (Y, z) Vf(pk, M, σ) (N, e, X) ← pk (Y, z) ← σ c ← H(Y, M) If ze = XYc mod N then accept else reject 11
![The framework: SI to SS [FS 86] “canonical” SI scheme: sk SI IBI pk The framework: SI to SS [FS 86] “canonical” SI scheme: sk SI IBI pk](http://slidetodoc.com/presentation_image_h/0617538fa8508787e22fa7b0d06c8672/image-12.jpg)
The framework: SI to SS [FS 86] “canonical” SI scheme: sk SI IBI pk Cmt Ch Rsp P V Dec(pk, Cmt, Ch, Rsp) fs-I-2 -S SS IBS Theorem: SI is imp-pa secure ⇓ SS = fs-I-2 -S(SI) is uf-cma secure in the RO model [AABN 02] § Sign(sk, M): Ch ← H(Cmt, M) σ ← (Cmt, Rsp) § Vf(pk, M, σ): Dec(pk, Cmt, H(Cmt, M), Rsp) 12
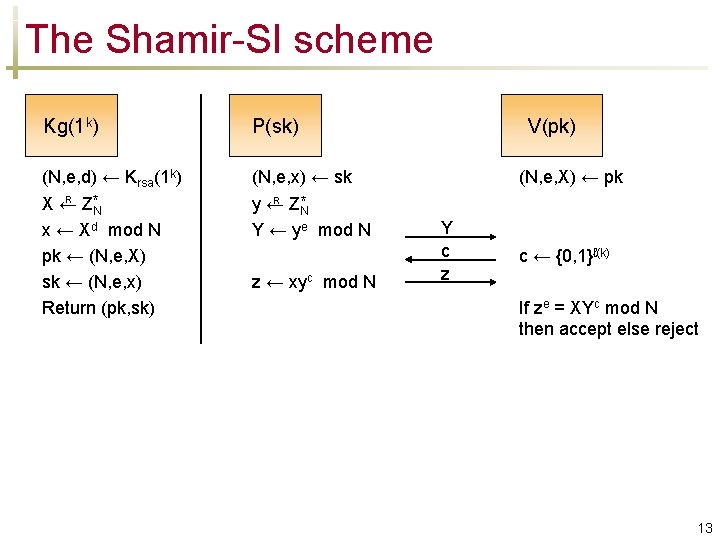
The Shamir-SI scheme Kg(1 k) P(sk) (N, e, d) ← Krsa(1 k) R X← Z*N (N, e, x) ← sk R y← Z*N x ← Xd mod N pk ← (N, e, X) sk ← (N, e, x) Return (pk, sk) Y ← ye mod N z ← xyc mod N V(pk) (N, e, X) ← pk Y c z c ← {0, 1}ℓ(k) If ze = XYc mod N then accept else reject 13
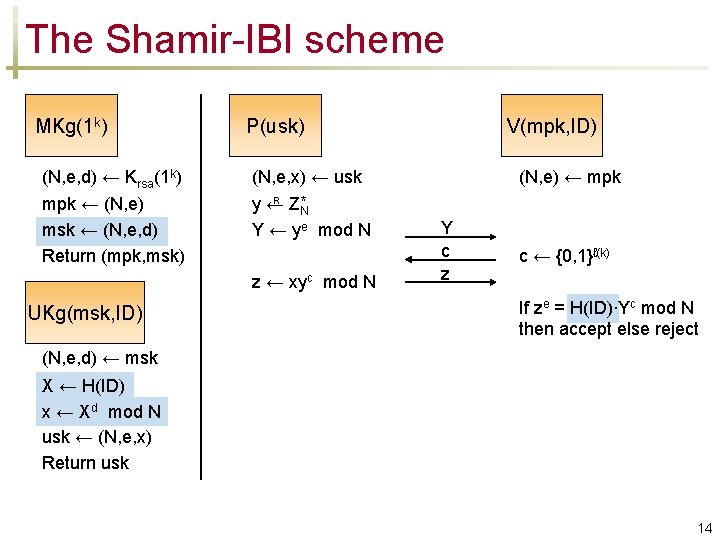
The Shamir-IBI scheme MKg(1 k) (N, e, d) ← Krsa(1 k) mpk ← (N, e) msk ← (N, e, d) Return (mpk, msk) P(usk) (N, e, x) ← usk R y← Z*N Y ← ye mod N z ← xyc mod N UKg(msk, ID) V(mpk, ID) (N, e) ← mpk Y c z c ← {0, 1}ℓ(k) If ze = H(ID)∙Yc mod N then accept else reject (N, e, d) ← msk X ← H(ID) x ← Xd mod N usk ← (N, e, x) Return usk 14
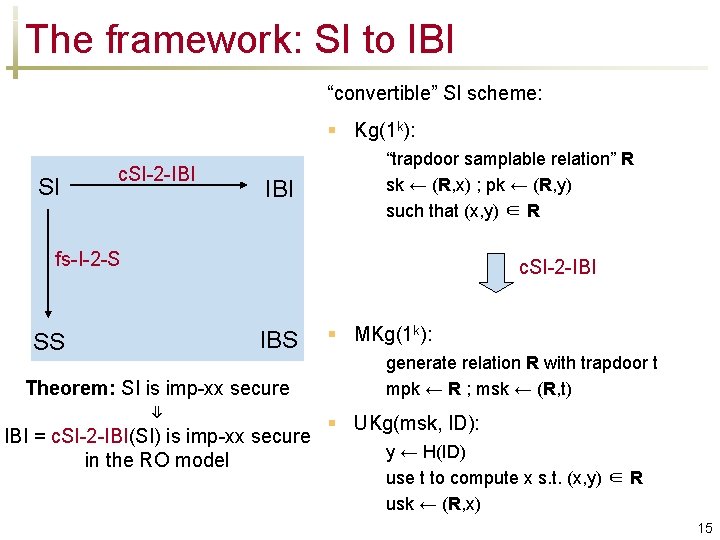
The framework: SI to IBI “convertible” SI scheme: § Kg(1 k): SI c. SI-2 -IBI “trapdoor samplable relation” R sk ← (R, x) ; pk ← (R, y) such that (x, y) ∈ R fs-I-2 -S SS c. SI-2 -IBI IBS § MKg(1 k): generate relation R with trapdoor t mpk ← R ; msk ← (R, t) Theorem: SI is imp-xx secure ⇓ § UKg(msk, ID): IBI = c. SI-2 -IBI(SI) is imp-xx secure y ← H(ID) in the RO model use t to compute x s. t. (x, y) ∈ R usk ← (R, x) 15
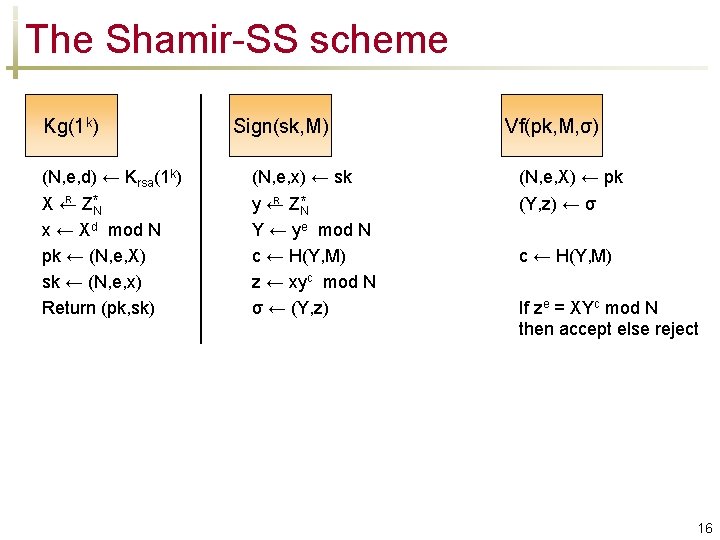
The Shamir-SS scheme Kg(1 k) Sign(sk, M) (N, e, d) ← Krsa(1 k) R X← Z*N (N, e, x) ← sk R y← Z*N x ← Xd mod N pk ← (N, e, X) sk ← (N, e, x) Return (pk, sk) Y ← ye mod N c ← H(Y, M) z ← xyc mod N σ ← (Y, z) Vf(pk, M, σ) (N, e, X) ← pk (Y, z) ← σ c ← H(Y, M) If ze = XYc mod N then accept else reject 16
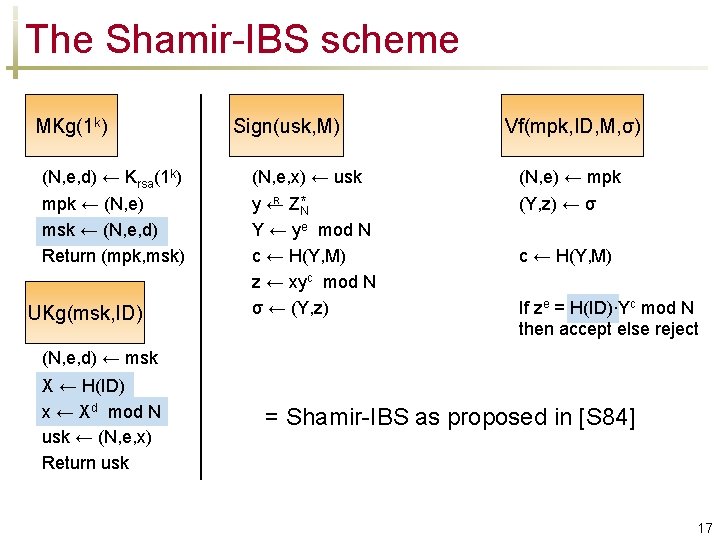
The Shamir-IBS scheme MKg(1 k) (N, e, d) ← Krsa(1 k) mpk ← (N, e) msk ← (N, e, d) Return (mpk, msk) UKg(msk, ID) Sign(usk, M) (N, e, x) ← usk R y← Z*N Y ← ye mod N c ← H(Y, M) z ← xyc mod N σ ← (Y, z) Vf(mpk, ID, M, σ) (N, e) ← mpk (Y, z) ← σ c ← H(Y, M) If ze = H(ID)∙Yc mod N then accept else reject (N, e, d) ← msk X ← H(ID) x ← Xd mod N usk ← (N, e, x) Return usk = Shamir-IBS as proposed in [S 84] 17
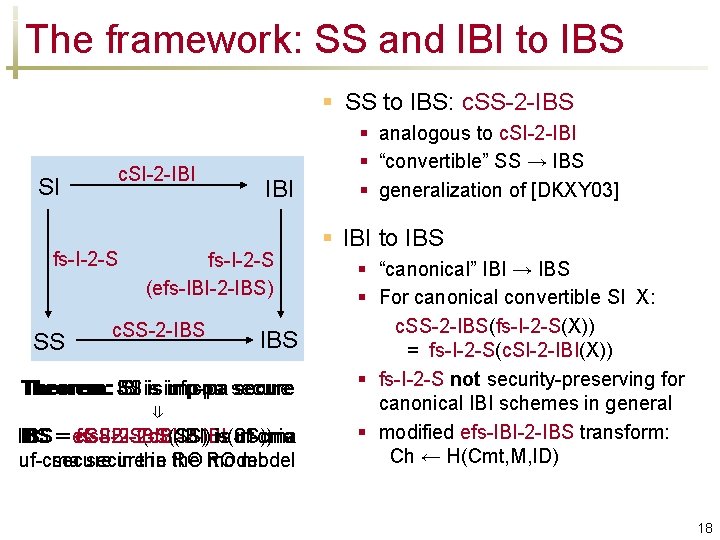
The framework: SS and IBI to IBS § SS to IBS: c. SS-2 -IBS SI c. SI-2 -IBI fs-I-2 -S SS IBI fs-I-2 -S (efs-IBI-2 -IBS) c. SS-2 -IBS Theorem: SS SI is IBI is imp-pa secure Theorem: uf-cma secure ⇓ fs-I-2 -S(c. SI-2 -IBI(SS)) is IBS is uf-cma IBS == efs-IBI-2 -IB(IBI) c. SS-2 -IBS(SS) is uf-cma secure in RO the RO model secure in the model § analogous to c. SI-2 -IBI § “convertible” SS → IBS § generalization of [DKXY 03] § IBI to IBS § “canonical” IBI → IBS § For canonical convertible SI X: c. SS-2 -IBS(fs-I-2 -S(X)) = fs-I-2 -S(c. SI-2 -IBI(X)) § fs-I-2 -S not security-preserving for canonical IBI schemes in general § modified efs-IBI-2 -IBS transform: Ch ← H(Cmt, M, ID) 18
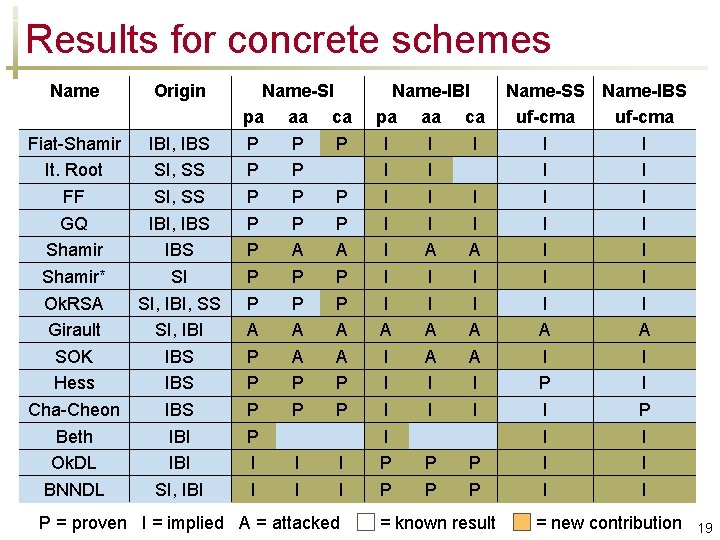
Results for concrete schemes Name Origin Fiat-Shamir IBI, IBS It. Root SI, SS FF SI, SS GQ IBI, IBS Shamir* SI Ok. RSA SI, IBI, SS Girault SI, IBI SOK IBS Hess IBS Cha-Cheon IBS Beth IBI Ok. DL IBI BNNDL SI, IBI Name-SI pa aa ca P P P A A P P P A A A P P P P I I I P = proven I = implied A = attacked Name-IBI pa aa ca I I I A A I I I A A A I I I I P P P = known result Name-SS Name-IBS uf-cma I I I I A A I I P I I I = new contribution 19
- Slides: 19