Security Program and Policies Principles and Practices by
Security Program and Policies Principles and Practices by Sari Stern Greene Chapter 3: Information Security Framework
Objectives q q q Recognize the importance of the CIA security model and describe the security objectives of confidentiality, integrity, and availability Discuss why organizations choose to adopt a security framework Recognize the values of NIST resources Understand the intent of ISO/IEC 27000 -series of information security standards Outline the domains of an information security program Copyright 2014 Pearson Education, Inc. 2
Need for a framework n n Like how foundation of a building clearly defines the rooms, boundaries in a building, framework defines the different domains which we need to concentrate in order to write a ISP NIST and ISO have done intense research and come up with frameworks, which we just need to follow! Copyright 2014 Pearson Education, Inc. 3
CIA n The CIA Triad or CIA security model q q q Stands for Confidentiality, Integrity, and Availability An attack against either or several of the elements of the CIA triad is an attack against the Information Security of the organization Protecting the CIA triad means protecting the assets of the company Copyright 2014 Pearson Education, Inc. 4
Relationship between IS and CIA The Federal Information Security Management Act (FISMA) defines the relationship between information security and the CIA triad as follows: n (1) The term “information security” means protecting information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction in order to provide— n (A) integrity, which means guarding against improper information modification or destruction, and includes ensuring information nonrepudiation, accuracy, and authenticity; n (B) confidentiality, which means preserving authorized restrictions on access and disclosure, including means for protecting personal privacy and proprietary information; and n (C) availability, which means ensuring timely and reliable access to and use of information. n Copyright 2014 Pearson Education, Inc. 5
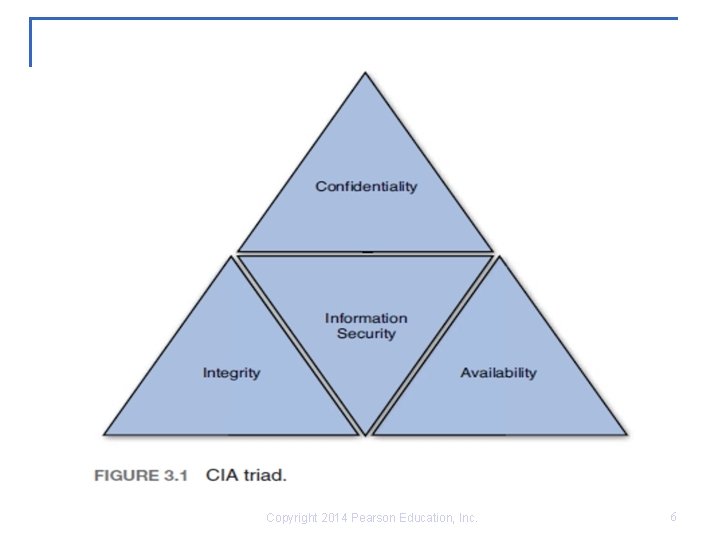
Copyright 2014 Pearson Education, Inc. 6
What Is Confidentiality? q q Not all data owned by the company should be made available to the public Failing to protect data confidentiality can be disastrous for an organization: n n Dissemination of Protected Health Information (PHI) between doctor and patient (Law- doctor-patient privilege) Between client and lawyer – protected by attorney-client privilege law Dissemination of Protected Financial Information (PFI) between bank and customer Dissemination of business-critical information to rival company 7 Copyright 2014 Pearson Education, Inc.
What Is Confidentiality? Cont. q q Only authorized users should gain access to information Information must be protected when it is used, shared, transmitted, and stored Information must be protected from unauthorized users both internally and externally Information must be protected whether it is in digital or paper format Copyright 2014 Pearson Education, Inc. 8
What Is Confidentiality? Cont. n The threats to confidentiality must be identified. They include: q q q Hackers and hacktivists Shoulder surfing Lack of shredding of paper documents Malicious Code (Virus, worms, Trojans) Unauthorized employee activity Improper access control Copyright 2014 Pearson Education, Inc. 9
What Is Integrity? Cont. q Protecting data, processes, or systems from intentional or accidental unauthorized modification n n q q Data integrity System integrity A business that cannot trust the integrity of its data is a business that cannot operate An attack against data integrity can mean the end of an organization’s capability to conduct business Copyright 2014 Pearson Education, Inc. 10
What Is Integrity? Cont. n Threats to data integrity include: q q q Human error Hackers Unauthorized user activity Improper access control Malicious code Interception and alteration of data during transmission Copyright 2014 Pearson Education, Inc. 11
What Is Integrity? Cont. n Controls that can be deployed to protect data integrity include: q Access controls: n n q Process controls n q Code testing Monitoring controls n n q Encryption Digital signatures File integrity monitoring Log analysis Behavioral controls: n n n Separation of duties Rotation of duties End user security training Copyright 2014 Pearson Education, Inc. 12
What Is Availability? q q q Availability: The assurance that the data and systems are accessible when needed by authorized users What is the cost of the loss of data availability to the organization? A risk assessment should be conducted to more efficiently protect data availability Copyright 2014 Pearson Education, Inc. 13
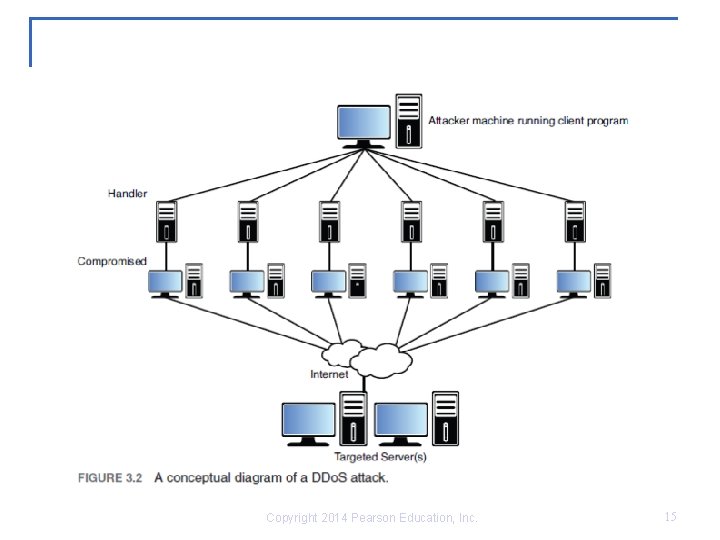
What Is Availability? Cont. n Threats to data availability include: q q q q Natural disaster Hardware failures Programming errors Human errors Distributed Denial of Service attacks Loss of power Malicious code Temporary or permanent loss of key personnel Copyright 2014 Pearson Education, Inc. 14
Copyright 2014 Pearson Education, Inc. 15
The Five A’s of Information Security q q q Accountability Assurance Authentication Authorization Accounting Copyright 2014 Pearson Education, Inc. 16
The. Five A’s of Information Security Cont. n Accountability q q q All actions should be traceable to the person who committed them Logs should be kept, archived, and secured to provide non-repudiation Intrusion detection systems should be deployed Computer forensic techniques can be used retroactively Accountability should be focused on both internal and external actions Copyright 2014 Pearson Education, Inc. 17

The Five A’s of Information Security Cont. n Assurance q q q Security measures need to be designed and tested to ascertain that they are efficient and appropriate The knowledge that these measures are indeed efficient is known as assurance The activities related to assurance include: n n n Auditing and monitoring Testing Reporting Copyright 2014 Pearson Education, Inc. 18
The Five A’s of Information Security Cont. n Authentication q q q Authentication is the cornerstone of most network security models It is the positive identification of the person or system seeking access to secured information and/or system Examples of authentication models: n n n User ID and password combination Tokens Biometric devices Copyright 2014 Pearson Education, Inc. 19
The Five A’s of Information Security Cont. n Authorization q q q Act of granting users or systems actual access to information resources Note that the level of access may change based on the user’s defined access level Examples of access level include the following: n n n Read only Read and write Full Copyright 2014 Pearson Education, Inc. 20
The Five A’s of Information Security Cont. n Accounting q q q Defined as the logging of access and usage of resources Keeps track of who accesses what resource, when, and for how long An example of use: n Internet café, where users are charged by the minute of use of the service Copyright 2014 Pearson Education, Inc. 21
Who Is Responsible for CIA? n Information owner q q n An official with statutory or operational authority for specified information Has the responsibility for ensuring information is protected from creation through destruction Information custodian q Maintain the systems that store, process, and transmit the information normally the IT dept. Network managers, admins, webmasters etc. Copyright 2014 Pearson Education, Inc. 22
Information Security Framework n n Security framework is a collective term given to guidance on topics related to information systems security, predominantly regarding the planning, implementing, managing, and auditing of overall information security practices. Two of the most widely used frameworks are: q q Information Technology and Security Framework by NIST Information Security Management System by ISO Copyright 2014 Pearson Education, Inc. 23
NIST Functions n Founded in 1901 Nonregulatory federal agency n US Govt. Agency n n They rise awareness towards IS, research, develop guidelines, standards, publish bulletins, papers. Its mission is to develop and promote measurement, standards, and technology to enhance productivity, facilitate trade, and improve quality of life Published more than 300 information security-related documents including q q q Federal Information Processing Standards (FIPS) Special Publication 800 series ITL bulletins (IT laboratory) Copyright 2014 Pearson Education, Inc. 24
ISO Functions n n n A network of national standards institutes of 146 countries Nongovernmental organization that has developed more than 13, 000 international standards – Head office in Geneva The ISO/IEC 27000 series represents information security standards published by ISO and Electro-technical Commission (IEC) Copyright 2014 Pearson Education, Inc. 25
n n n n The first six documents in the ISO/IEC 27000 series provide recommendations for “establishing, implementing, operating, monitoring, reviewing, maintaining, and improving an Information Security Management System. ” In all, there are 22 documents in the series, and several more are still under development. ■■ ISO 27001 is the specification for an Information Security Management System (ISMS). ■■ ISO 27002 describes the Code of Practice for information security management. ■■ ISO 27003 provides details implementation guidance. ■■ ISO 27004 outlines how an organization can monitor and measure security using metrics. ■■ ISO 27005 defines the high-level risk management approach recommended by ISO. ■■ ISO 27006 outlines the requirements for organizations that will measure ISO 27000 compliance for certification. Copyright 2014 Pearson Education, Inc. 26
ISO 27002: 2013 Code of Practice n n Comprehensive set of information security recommendations on best practices in information security In ISO 27002: 2013 -the recommendations are organized in the following domains: q q q q Information security policies (Section 5) Organization of information security (Section 6) Human Resources security (Section 7) Asset management (Section 8) Access control (Section 9) Cryptography (Section 10) Physical and environmental security (Section 11) Copyright 2014 Pearson Education, Inc. 27
ISO 27002: 2013 Code of Practice cont. q q q q Operations security (Section 12) Communications security (Section 13) Information systems acquisition, development, and maintenance (Section 14) Supplier relationships (Section 15) Information security incident management (Section 16) Business continuity (Section 17) Compliance management (Section 18) Copyright 2014 Pearson Education, Inc. 28
Summary q q q The CIA triad is the blueprint of what assets needs to be protected to protect the organization. Protecting the organization’s information security can seem vague and too conceptual. Protecting the confidentiality, integrit, and availability of the data is a concrete way of saying the same thing. Standards such as the ISO 27002 exist to help organizations better define appropriate ways to protect their information assets. Copyright 2014 Pearson Education, Inc. 29
- Slides: 29