SECURITY PRIVACY RELIABILITY Secures against attacks Protects from


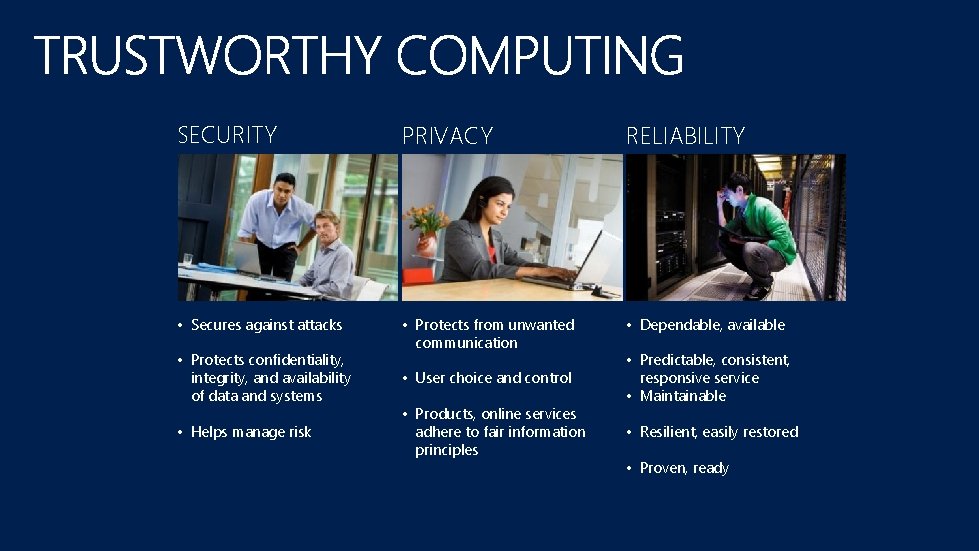
SECURITY PRIVACY RELIABILITY • Secures against attacks • Protects from unwanted communication • Dependable, available • Protects confidentiality, integrity, and availability of data and systems • Helps manage risk • User choice and control • Products, online services adhere to fair information principles • Predictable, consistent, responsive service • Maintainable • Resilient, easily restored • Proven, ready

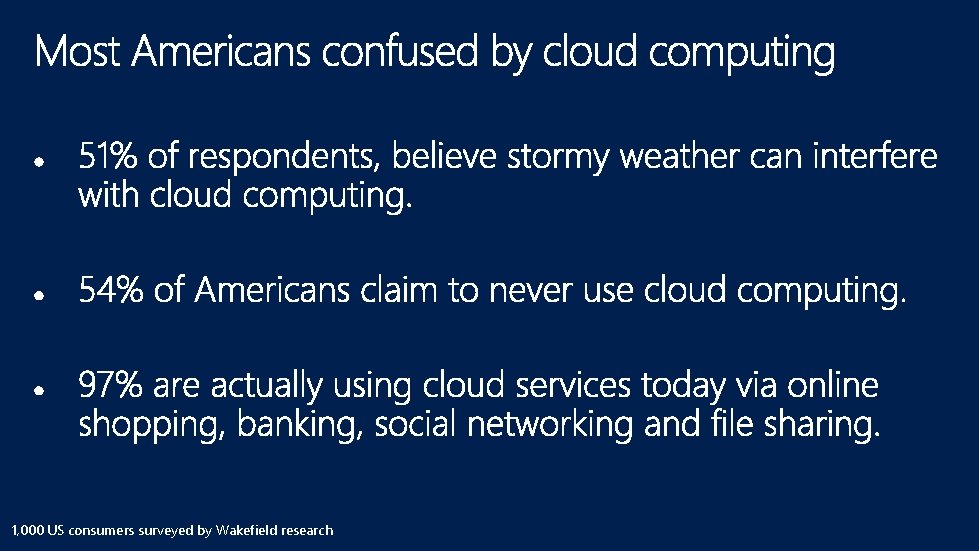
1, 000 US consumers surveyed by Wakefield research
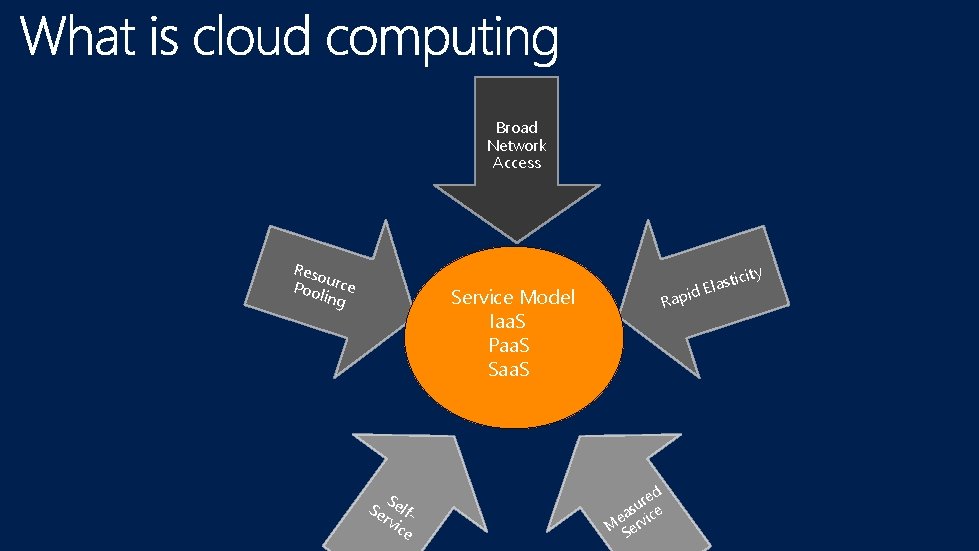
Broad Network Access Reso Poo urce ling Service Model Iaa. S Paa. S S Se elfrvi ce city sti a l E id Rap d re u s ea rvice M e S

CONCERNS BENEFITS scalability increased agility flexibility Reduced costs privacy security reliability
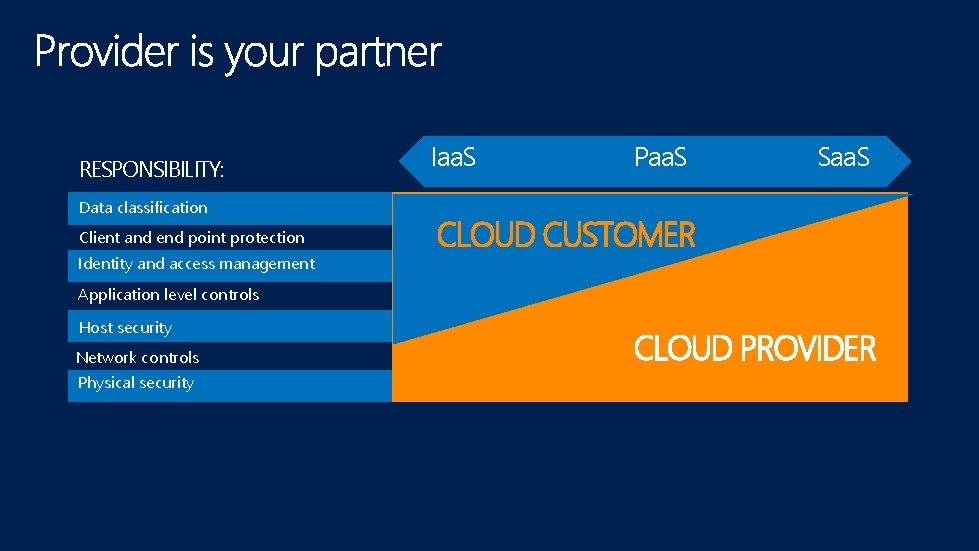
RESPONSIBILITY: Data classification Client and end point protection Identity and access management Iaa. S Paa. S Saa. S CLOUD CUSTOMER Application level controls Host security Network controls Physical security CLOUD PROVIDER
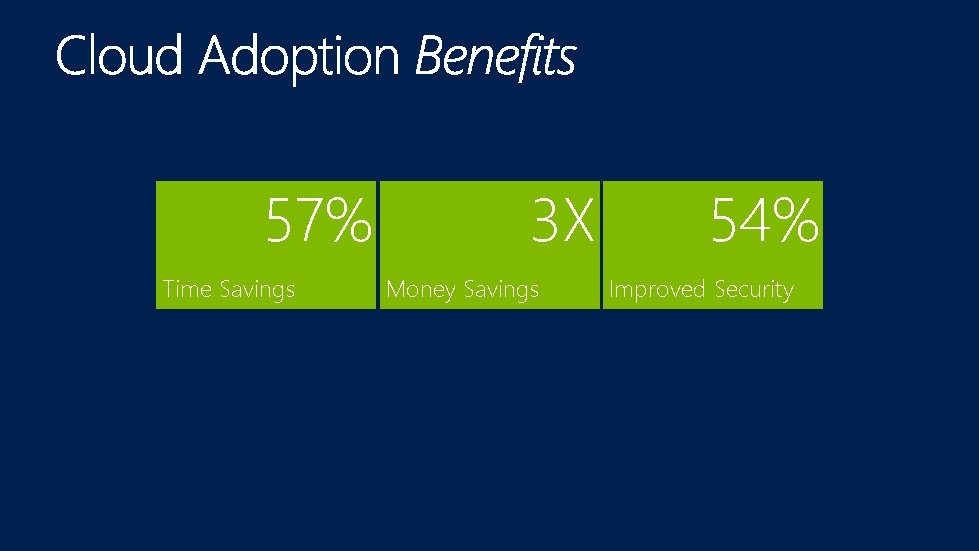
57% Time Savings 3 X Money Savings 54% Improved Security
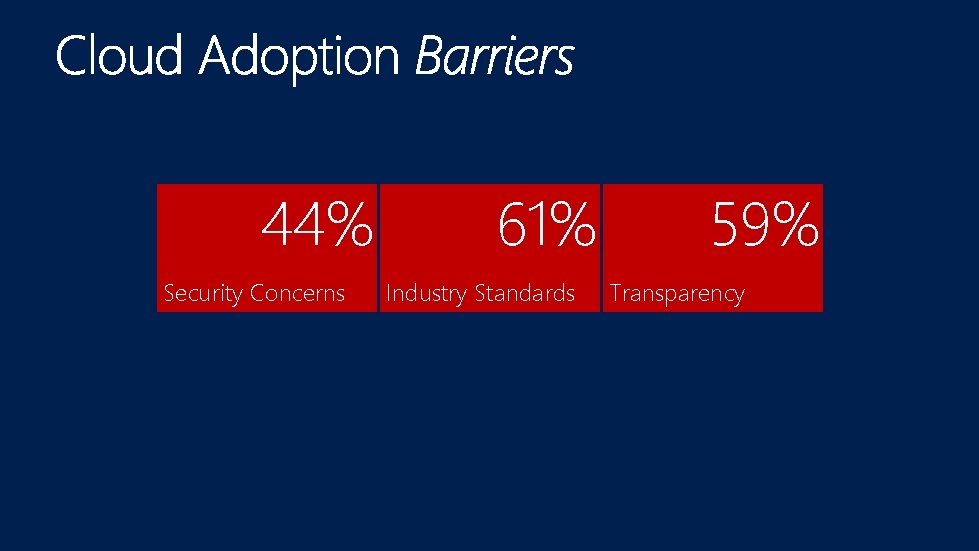
44% Security Concerns 61% Industry Standards 59% Transparency
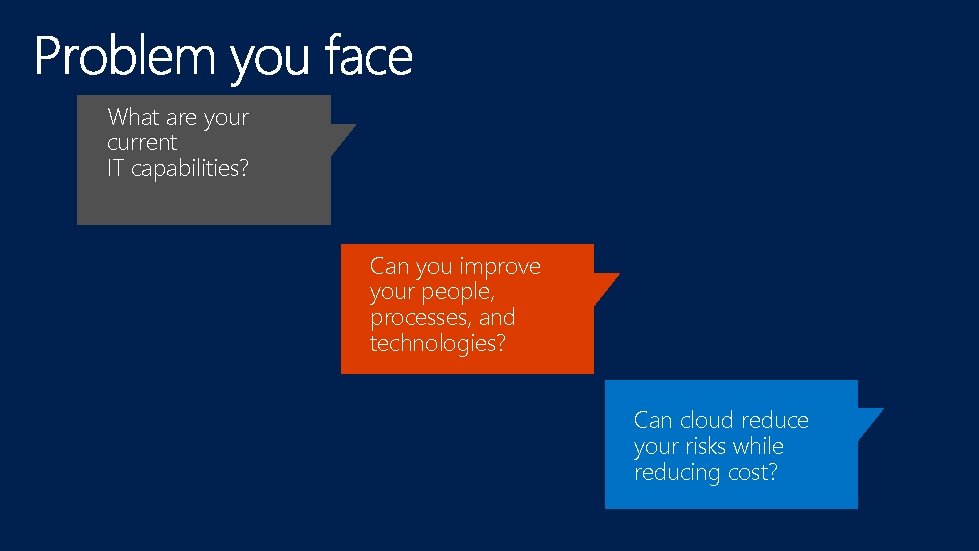
What are your current IT capabilities? Can you improve your people, processes, and technologies? Can cloud reduce your risks while reducing cost?


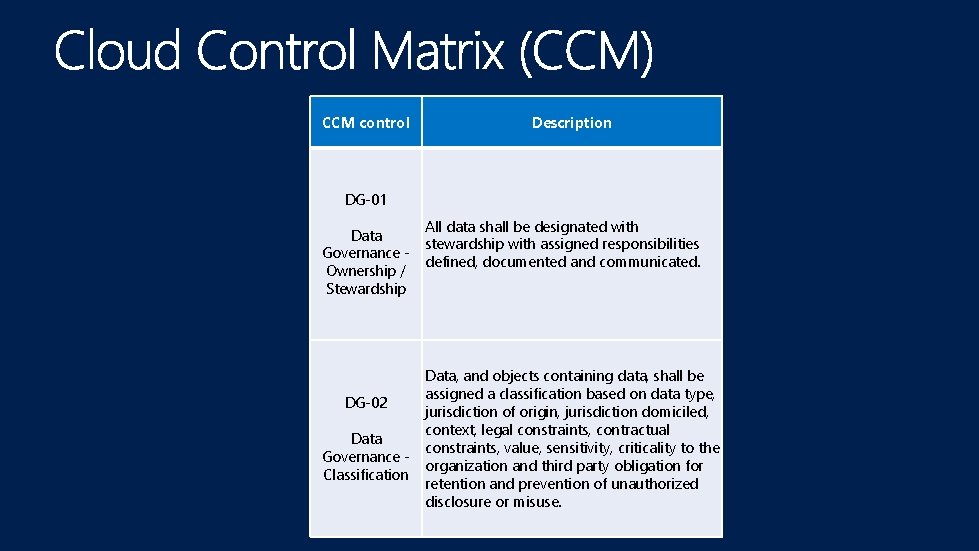
CCM control Description DG-01 Data Governance Ownership / Stewardship DG-02 Data Governance Classification All data shall be designated with stewardship with assigned responsibilities defined, documented and communicated. Data, and objects containing data, shall be assigned a classification based on data type, jurisdiction of origin, jurisdiction domiciled, context, legal constraints, contractual constraints, value, sensitivity, criticality to the organization and third party obligation for retention and prevention of unauthorized disclosure or misuse.
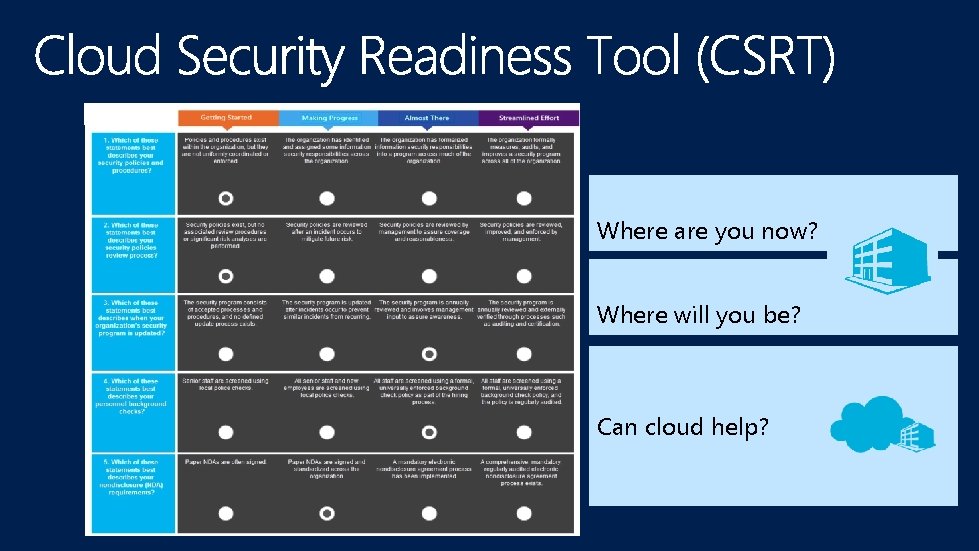
Where are you now? Where will you be? Can cloud help?





• Cloud Security Readiness Tool (CSRT) data between October 2012 and March 2013. • Approximately 5700 anonymized answers to CSRT questions • Margin of error • +/- 1% USA/EUROPE • +/- 10% ASIA
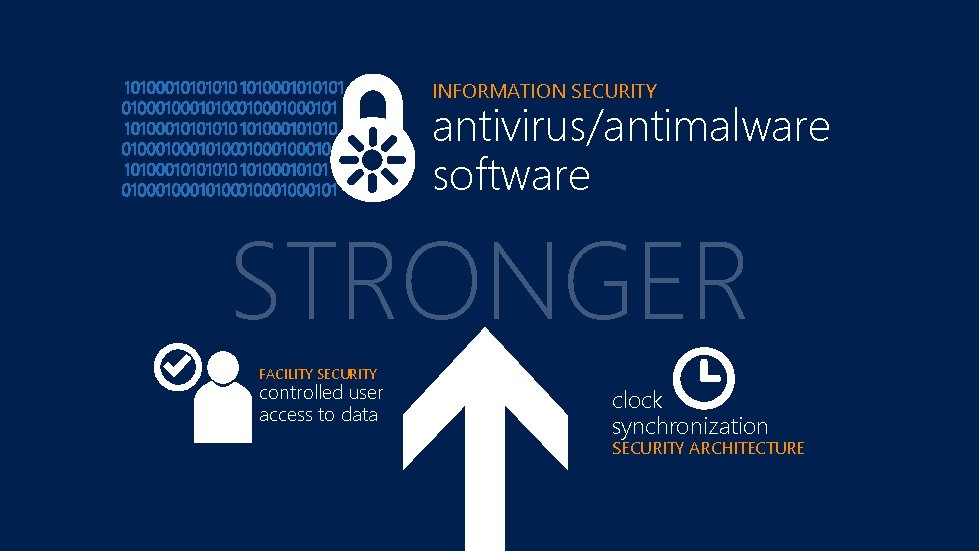
INFORMATION SECURITY antivirus/antimalware software STRONGER FACILITY SECURITY controlled user access to data clock synchronization SECURITY ARCHITECTURE

HUMAN RESOURCES SECURITY prudent hiring practices OPERATIONS MANAGEMENT effective capacity planning WEAKER OPERATIONS MANAGEMENT effective equipment maintenance INFORMATION SECURITY consistent incident reporting LEGAL PROTECTION nondisclosure agreements
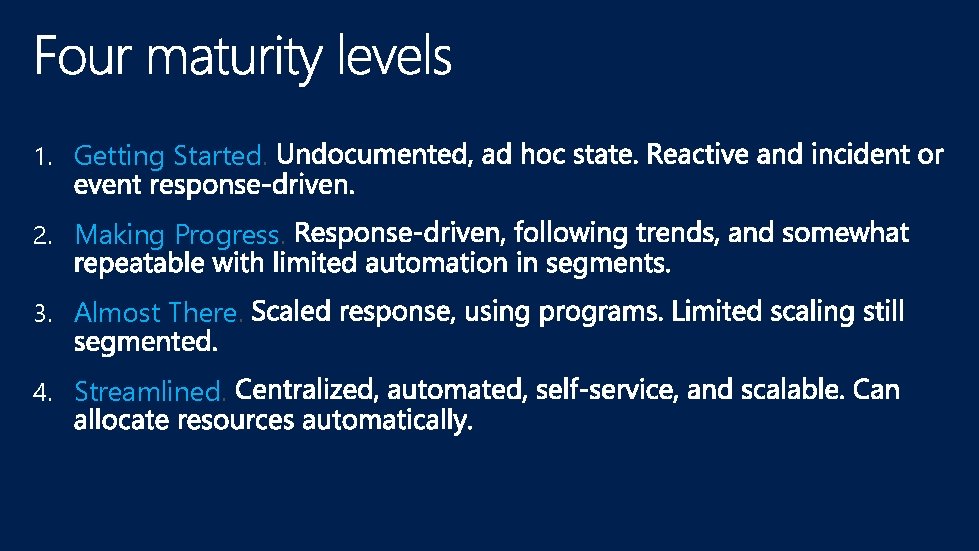
1. Getting Started. 2. Making Progress. 3. Almost There. 4. Streamlined.
If the answer was Almost There or Streamlined, a +1 value was assigned for maturity. If the answer was Getting Started or Making Progress, a -1 value was assigned for maturity.






Resource planning Equipment maintenance






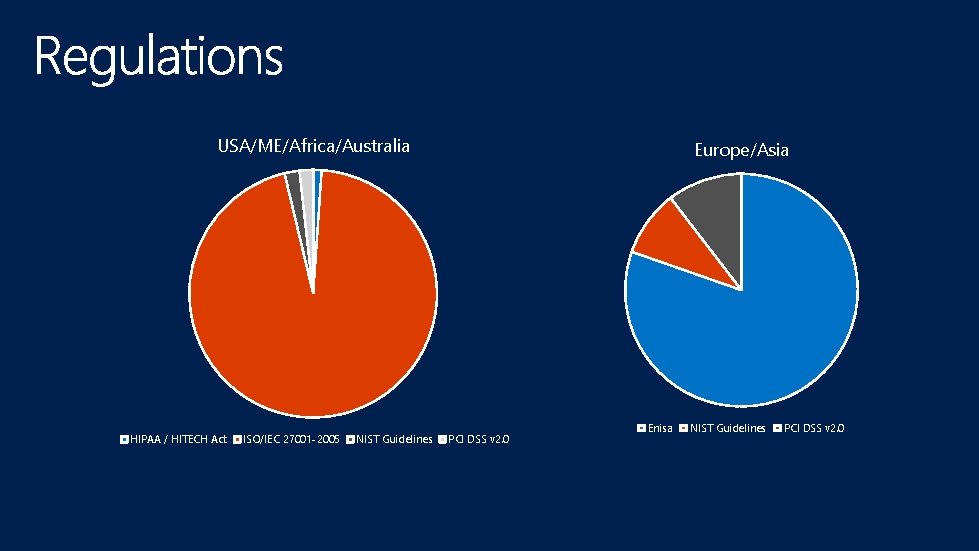
USA/ME/Africa/Australia HIPAA / HITECH Act ISO/IEC 27001 -2005 NIST Guidelines Europe/Asia PCI DSS v 2. 0 Enisa NIST Guidelines PCI DSS v 2. 0


The better you understand your people, processes, and technologies, the more you will be able to make informed comparisons and evaluate the benefits of the cloud. Visit the Trustworthy Computing – Cloud Tech. Center and its many resources: The Cloud Security Readiness Tool A free assessment to help you • evaluate the benefits of the cloud • create a plan for adoption • better understand your organization’s capabilities • Additional resources on cloud security, privacy, and reliability microsoft. com/trustedcloud
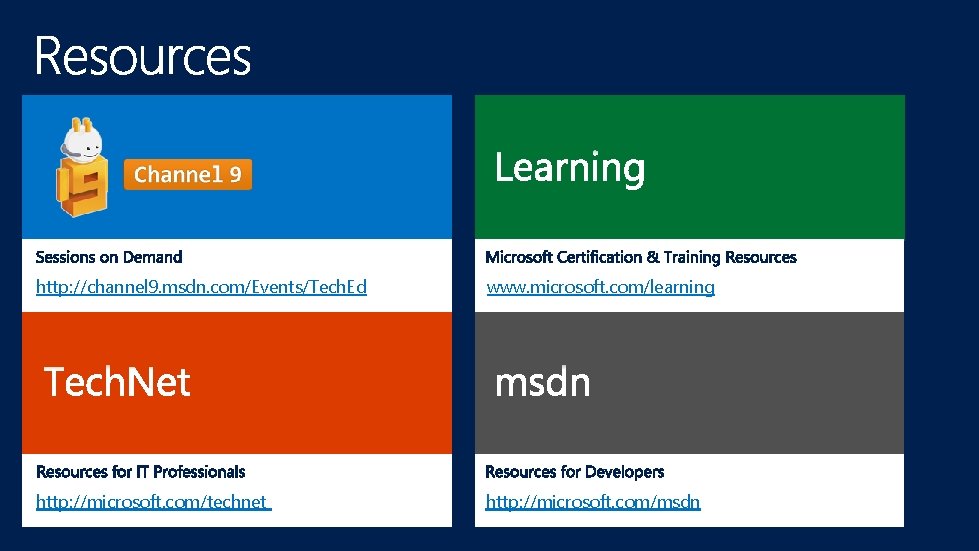
http: //channel 9. msdn. com/Events/Tech. Ed www. microsoft. com/learning http: //microsoft. com/technet http: //microsoft. com/msdn


- Slides: 45