SECURITY PRECAUTIONS STARTER WHATS THE QUESTION You have


- Slides: 16

SECURITY PRECAUTIONS
STARTER – WHAT’S THE QUESTION? • You have been given two answers to questions, you should write a suitable question to get the following answers. • 1. monitors the ingoing and outgoing traffic of a network to monitor for suspicious activity • 2. should be a mixture of letters and numbers including capital letters and symbols
SECURITY PRECAUTIONS Learning Intention: We are learning to understand how encryption and biometrics are used to secure our data Success Criteria: • I can describe and explain the benefits of biometrics • I can explain the purpose of encryption • I can differentiate and explain public and private keys
BIOMETRICS • Some systems use biometric technology to ensure that only authorised users gain access to a network. • Biometric security involves storing data about: – Fingerprints – Voices – Eyes

FINGERPRINT SCAN • Your fingerprints are unique and add and extra layer of security onto your network. • You can even get your own personal USB fingerprint scanner to add as an extra layer of security to your PC
RETINA SCAN • System scans the users eye as everyone's is unique – simples! Ethan Hunt has to get a retina scan every time he is sent a mission! Voice recognition Although voices can be similar each person has a voice print which is unique to them
BIOMETRIC PASSPORTS Killing the need for Passwords
BENEFITS OF BIOMETRICS • Think: – Individually take 60 seconds to think of the benefits of biometric passwords • Pair: – Share your thoughts with your pair • Share: – Feedback to the class
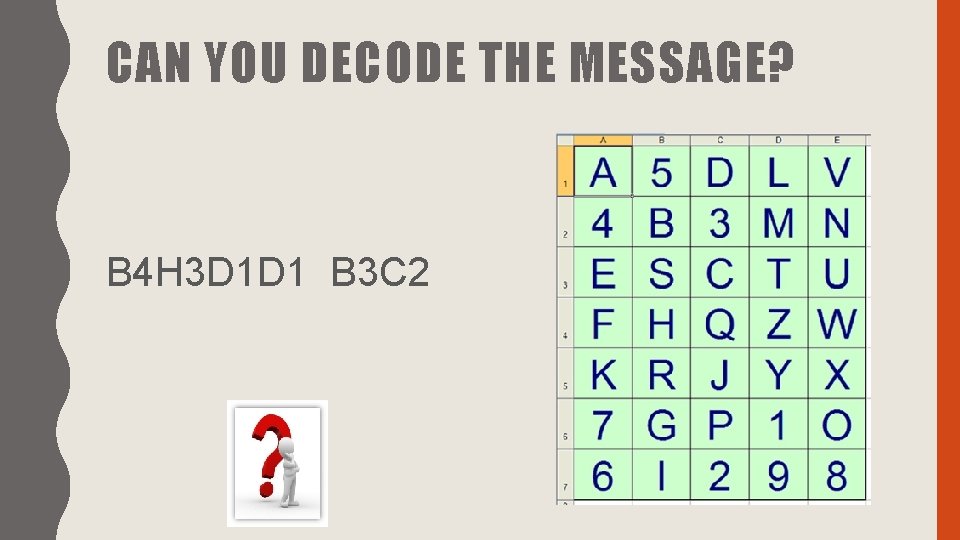
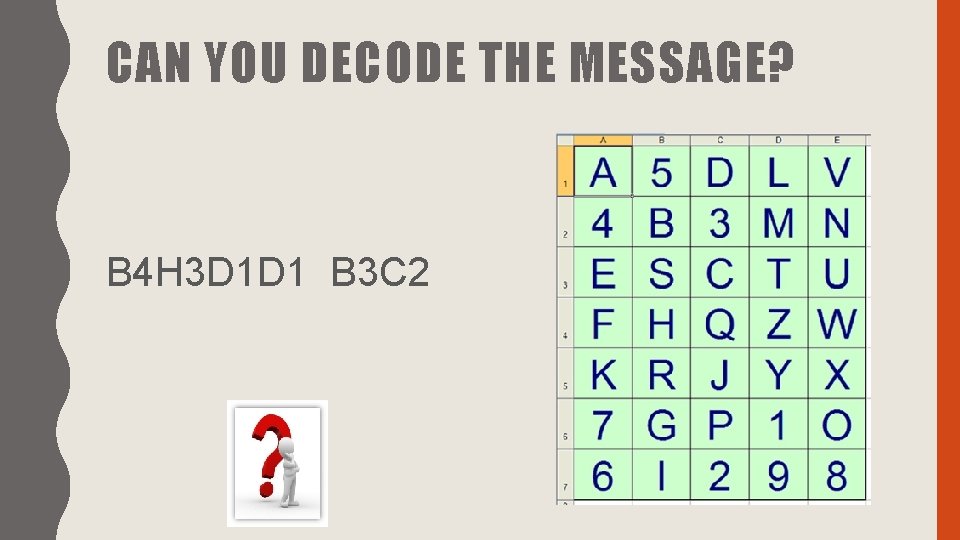
CAN YOU DECODE THE MESSAGE? B 4 H 3 D 1 D 1 B 3 C 2
ENCRYPTION Can you come up with a sentence that you think defines/describes what encryption is?
ENCRYPTION Is the process of encoding information to make it unreadable to those who gain unauthorised access to it.
ENCRYPTION What I’m looking for is for you to work as a team to learn how cryptography works and to solve some cryptograms as quickly as possible This is because throughout the world, people need to send secret messages: when communicating on the internet, when talking to spies, when having affairs….
MURDER IN THE MATHS FACULTY • In the maths faculty! • The body has not yet been identified. . . • Your task is to figure out who did it, where, and with what weapon • Teams of three or four people – one minute to organise this!
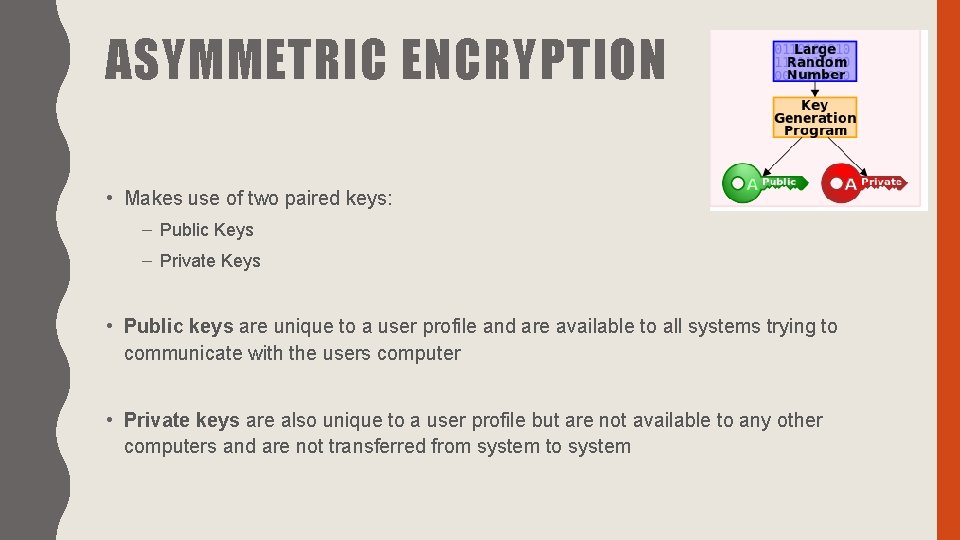
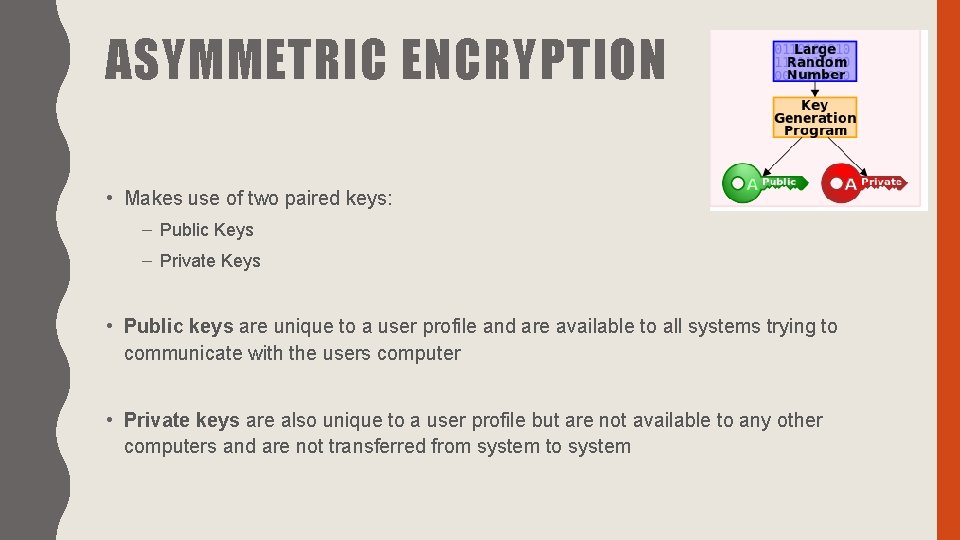
ASYMMETRIC ENCRYPTION • Makes use of two paired keys: – Public Keys – Private Keys • Public keys are unique to a user profile and are available to all systems trying to communicate with the users computer • Private keys are also unique to a user profile but are not available to any other computers and are not transferred from system to system
ASYMMETRIC ENCRYPTION When system A wishes to send a secure message to system B, it will use system B’s public key to encrypt the data. System B then uses its own private key to decrypt the data SYSTEM A SYSTEM B Draw a diagram to reflect the scenario given above
PLENARY – EXIT PASS • On an exit pass write one word that summarises today’s lesson – this should be encrypted with your Caesar Cipher Wheel with the key given underneath for it to be decoded by your teacher