Security Level 2021227 Security Hardening Service www huawei






- Slides: 29
Security Level: 2021/2/27 Security Hardening Service www. huawei. com HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential

1 The Industry of Security Overview 2 The Challenge of Security Facing 3 Security Hardening Services Package 4 Security Service Advantages & Values 5 Successful Stories HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 2
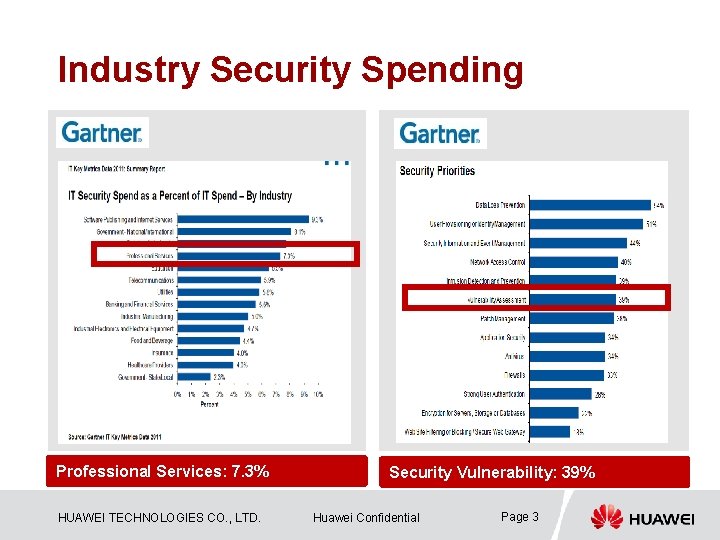
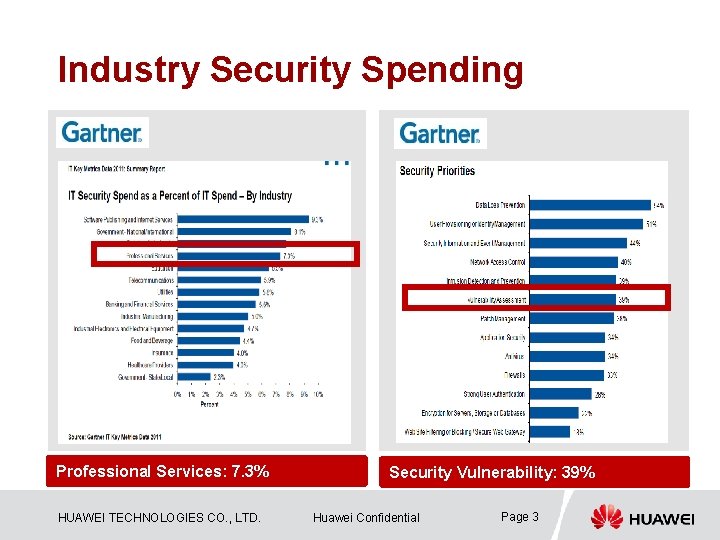
Industry Security Spending Professional Services: 7. 3% HUAWEI TECHNOLOGIES CO. , LTD. Security Vulnerability: 39% Huawei Confidential Page 3
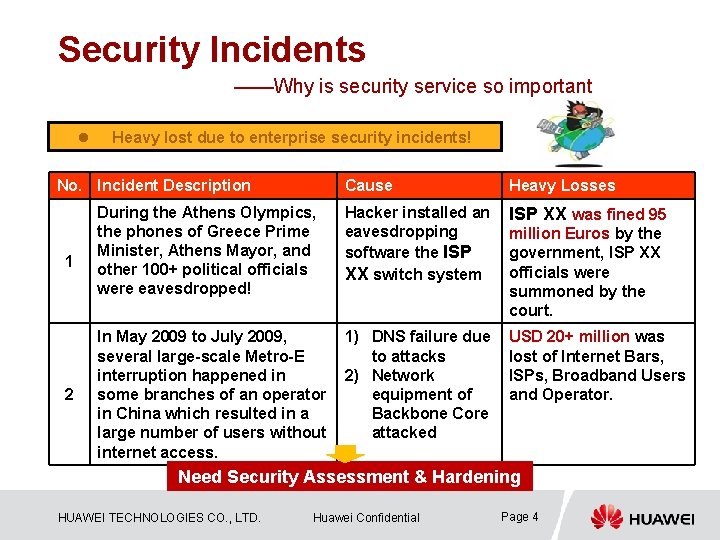
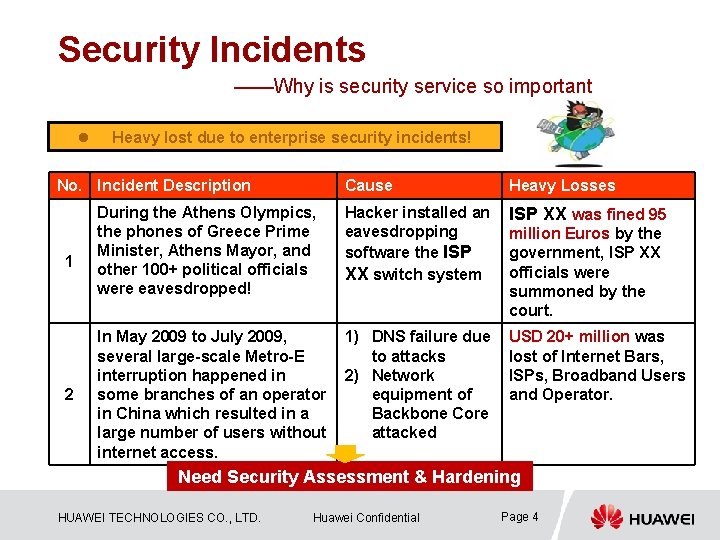
Security Incidents ——Why is security service so important l Heavy lost due to enterprise security incidents! No. Incident Description 1 2 Cause Heavy Losses During the Athens Olympics, the phones of Greece Prime Minister, Athens Mayor, and other 100+ political officials were eavesdropped! Hacker installed an eavesdropping software the ISP XX switch system ISP XX was fined 95 In May 2009 to July 2009, several large-scale Metro-E interruption happened in some branches of an operator in China which resulted in a large number of users without internet access. 1) DNS failure due to attacks 2) Network equipment of Backbone Core attacked USD 20+ million was lost of Internet Bars, ISPs, Broadband Users and Operator. million Euros by the government, ISP XX officials were summoned by the court. Need Security Assessment & Hardening HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 4

1 The Industry of Security Overview 2 The Challenge of Security Facing 3 Security Hardening Services Package 4 Security Service Advantages & Values 5 Successful Stories HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 5
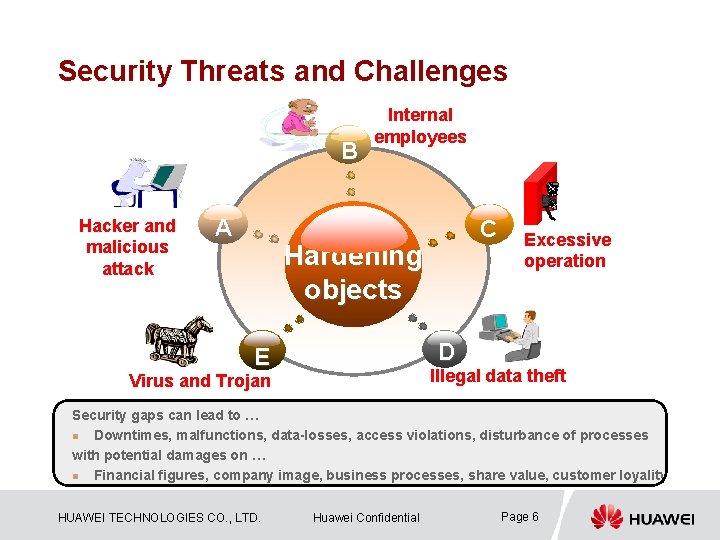
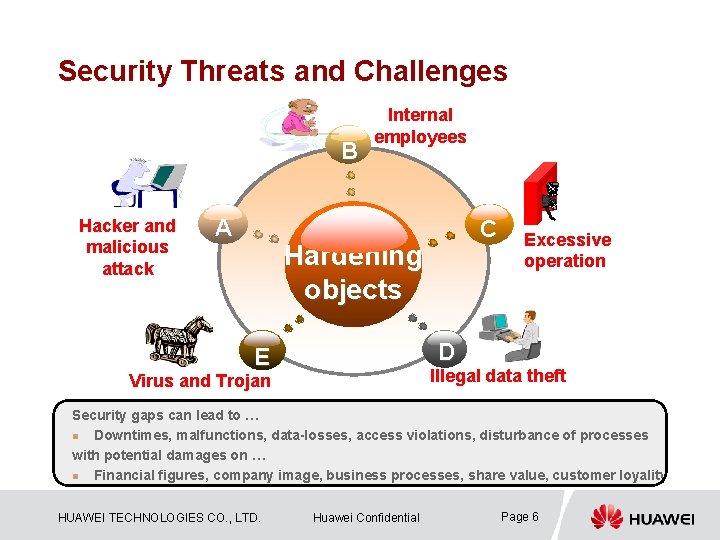
Security Threats and Challenges B Hacker and malicious attack A Internal employees C Hardening objects Excessive operation D E Illegal data theft Virus and Trojan Security gaps can lead to … n Downtimes, malfunctions, data-losses, access violations, disturbance of processes with potential damages on … n Financial figures, company image, business processes, share value, customer loyality HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 6
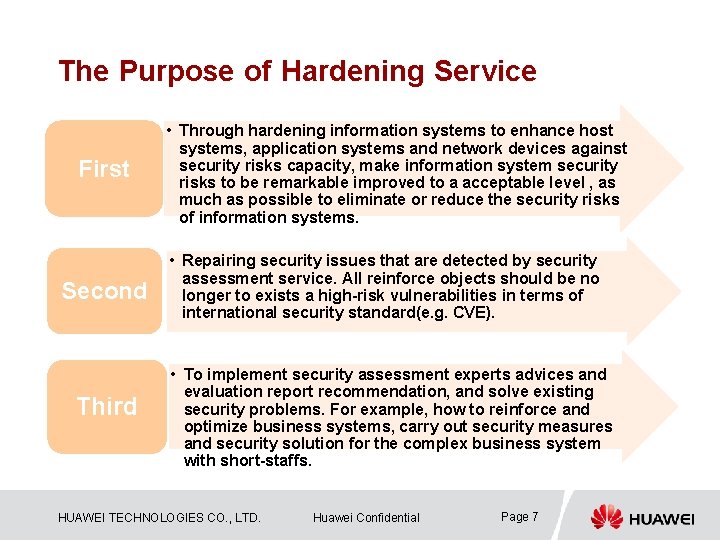
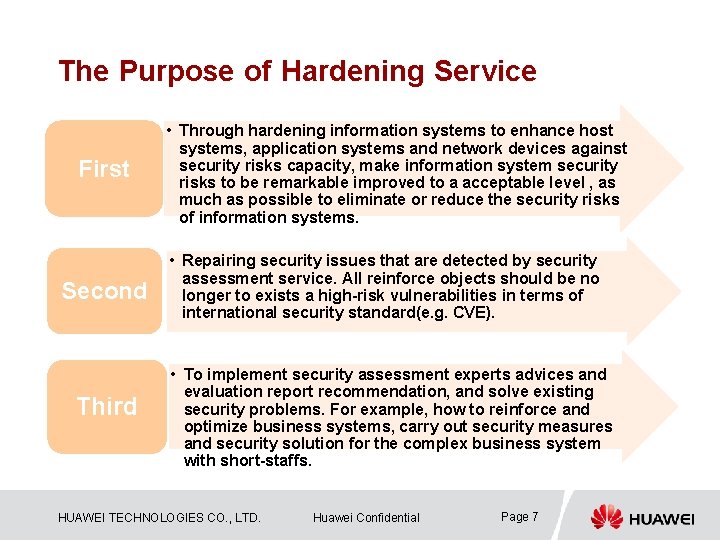
The Purpose of Hardening Service First Second Third • Through hardening information systems to enhance host systems, application systems and network devices against security risks capacity, make information system security risks to be remarkable improved to a acceptable level , as much as possible to eliminate or reduce the security risks of information systems. • Repairing security issues that are detected by security assessment service. All reinforce objects should be no longer to exists a high-risk vulnerabilities in terms of international security standard(e. g. CVE). • To implement security assessment experts advices and evaluation report recommendation, and solve existing security problems. For example, how to reinforce and optimize business systems, carry out security measures and security solution for the complex business system with short-staffs. HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 7

1 The Industry of Security Overview 2 The Challenge of Security Facing 3 Security Hardening Services Package 4 Security Service Advantages & Values 5 Successful Stories HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 8
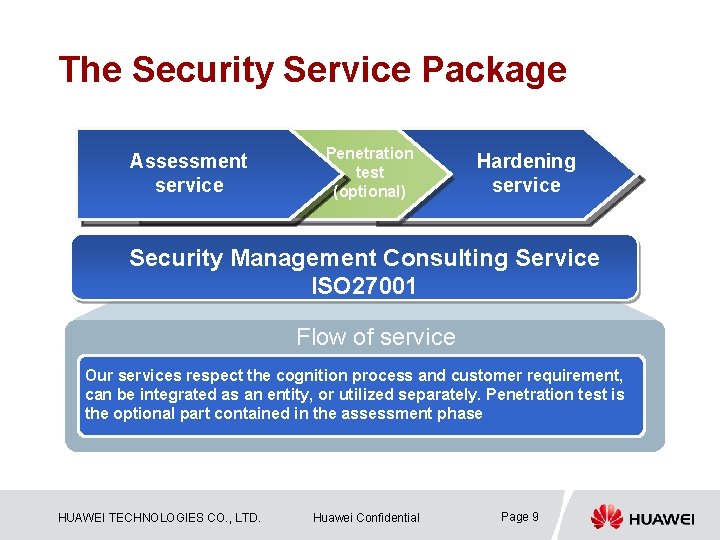
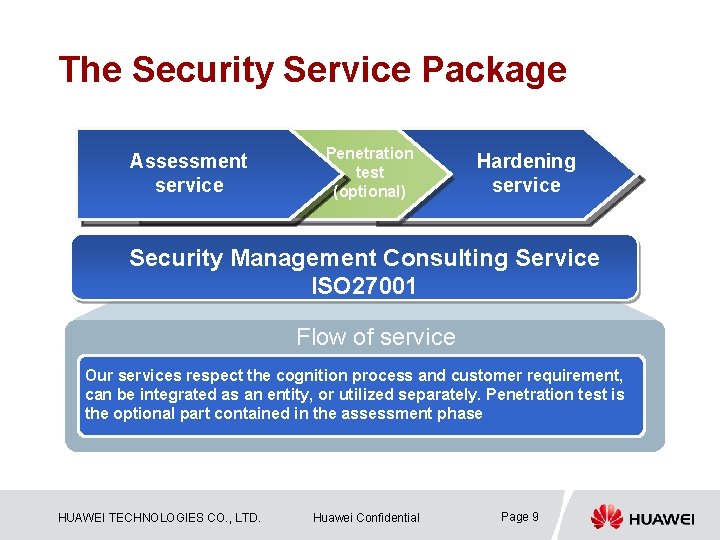
The Security Service Package Assessment service Penetration test (optional) Hardening service Security Management Consulting Service ISO 27001 Flow of service Our services respect the cognition process and customer requirement, can be integrated as an entity, or utilized separately. Penetration test is the optional part contained in the assessment phase HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 9
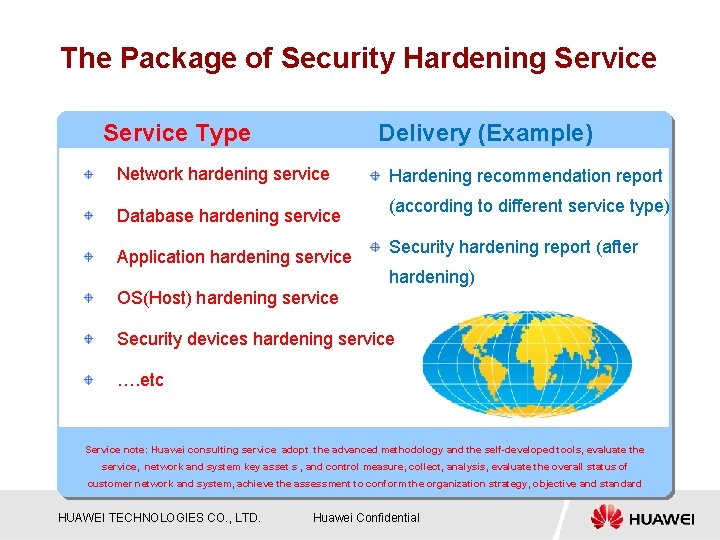
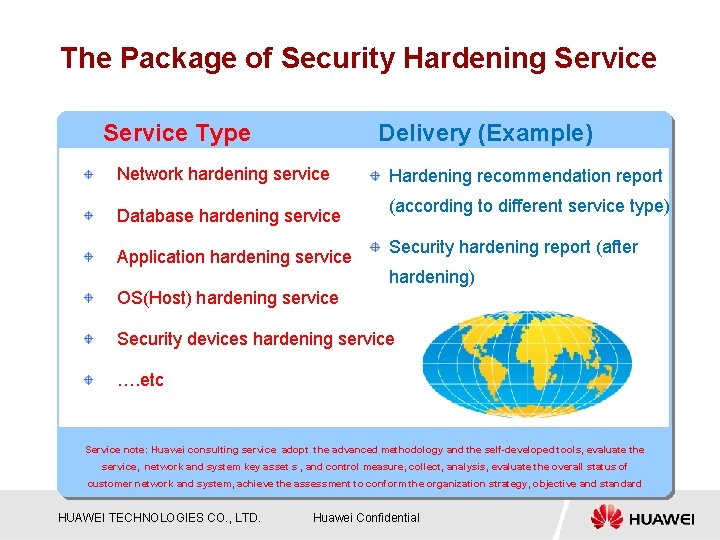
The Package of Security Hardening Service Type Delivery (Example) Network hardening service Database hardening service Application hardening service Hardening recommendation report (according to different service type) Security hardening report (after hardening) OS(Host) hardening service Security devices hardening service …. etc Service note: Huawei consulting service adopt the advanced methodology and the self-developed tools, evaluate the service, network and system key asset s , and control measure, collect, analysis, evaluate the overall status of customer network and system, achieve the assessment to conform the organization strategy, objective and standard HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential
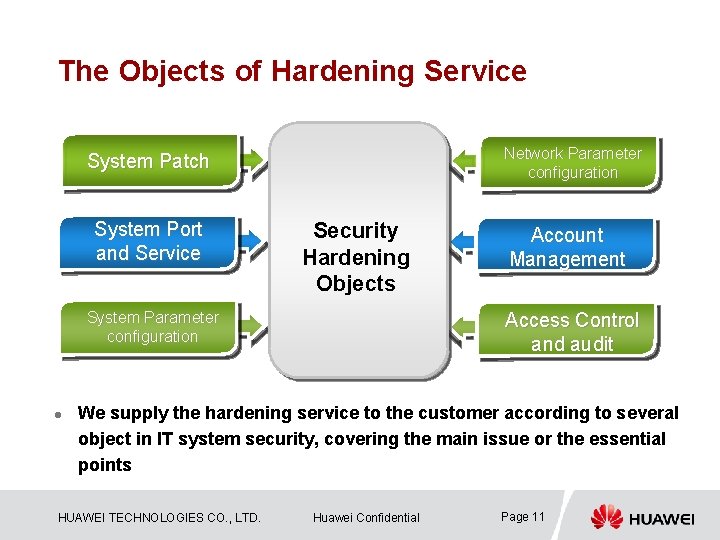
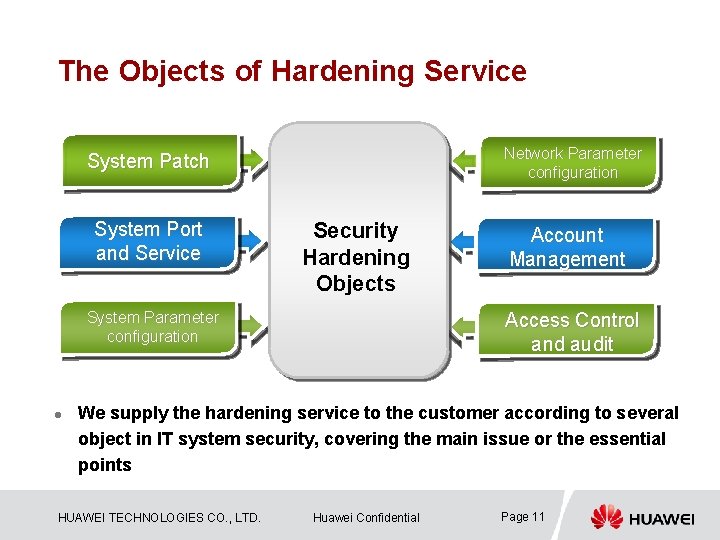
The Objects of Hardening Service Network Parameter configuration System Patch System Port and Service Security Hardening Objects System Parameter configuration l Account Management Access Control and audit We supply the hardening service to the customer according to several object in IT system security, covering the main issue or the essential points HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 11
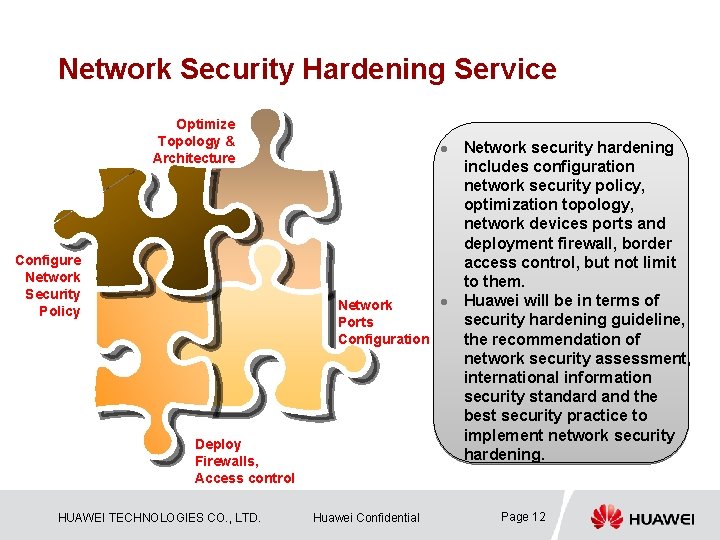
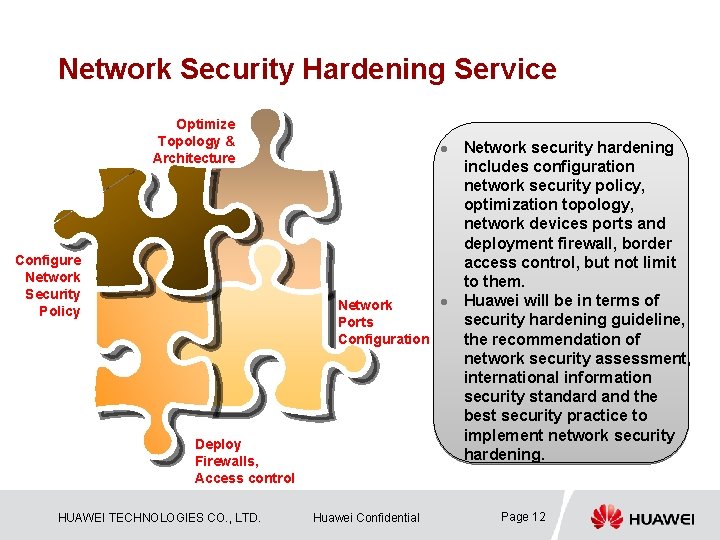
Network Security Hardening Service Optimize Topology & Architecture Configure Network Security Policy l Network Ports Configuration Deploy Firewalls, Access control HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential l Network security hardening includes configuration network security policy, optimization topology, network devices ports and deployment firewall, border access control, but not limit to them. Huawei will be in terms of security hardening guideline, the recommendation of network security assessment, international information security standard and the best security practice to implement network security hardening. Page 12
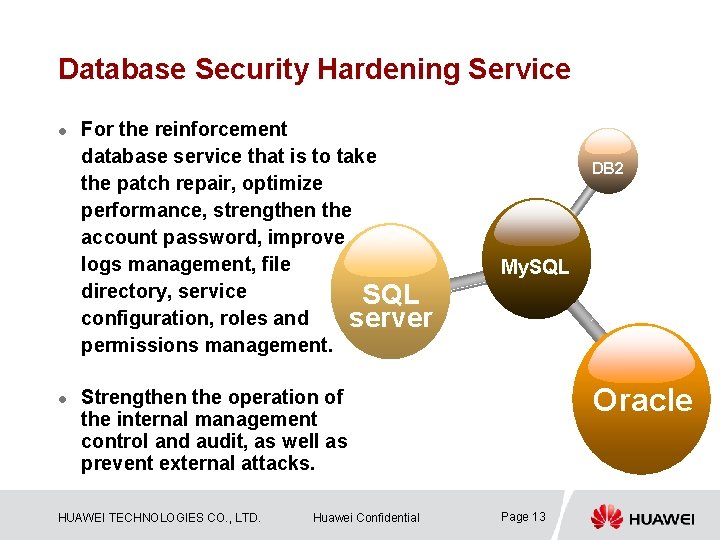
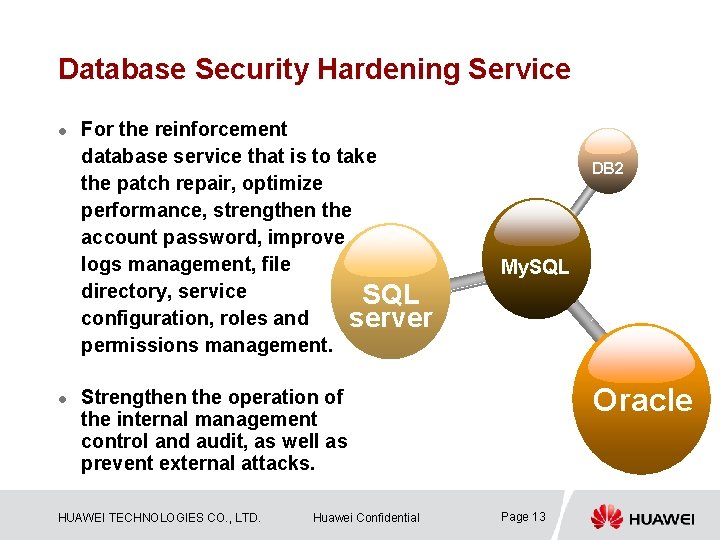
Database Security Hardening Service l l For the reinforcement database service that is to take the patch repair, optimize performance, strengthen the account password, improve logs management, file directory, service SQL configuration, roles and server permissions management. DB 2 My. SQL Oracle Strengthen the operation of the internal management control and audit, as well as prevent external attacks. HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 13
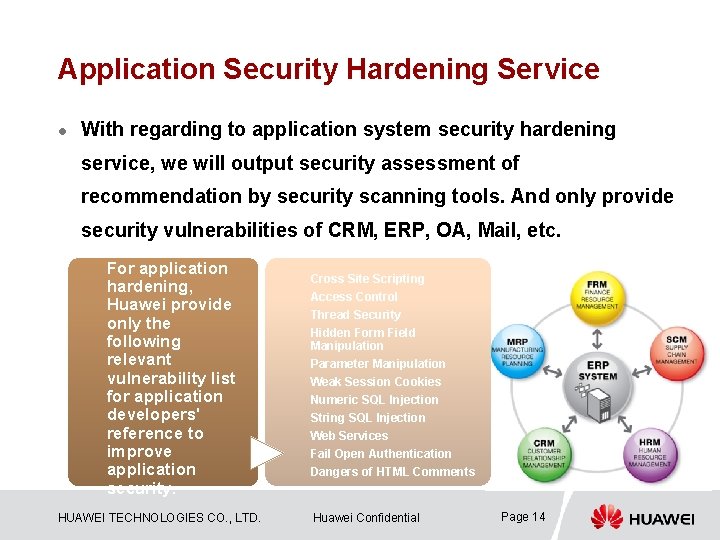
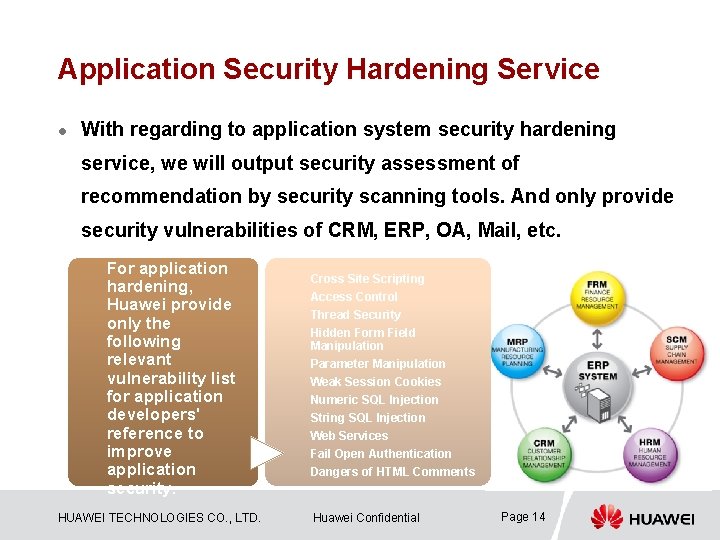
Application Security Hardening Service l With regarding to application system security hardening service, we will output security assessment of recommendation by security scanning tools. And only provide security vulnerabilities of CRM, ERP, OA, Mail, etc. For application hardening, Huawei provide only the following relevant vulnerability list for application developers' reference to improve application security. HUAWEI TECHNOLOGIES CO. , LTD. Cross Site Scripting Access Control Thread Security Hidden Form Field Manipulation Parameter Manipulation Weak Session Cookies Numeric SQL Injection String SQL Injection Web Services Fail Open Authentication Dangers of HTML Comments Huawei Confidential Page 14
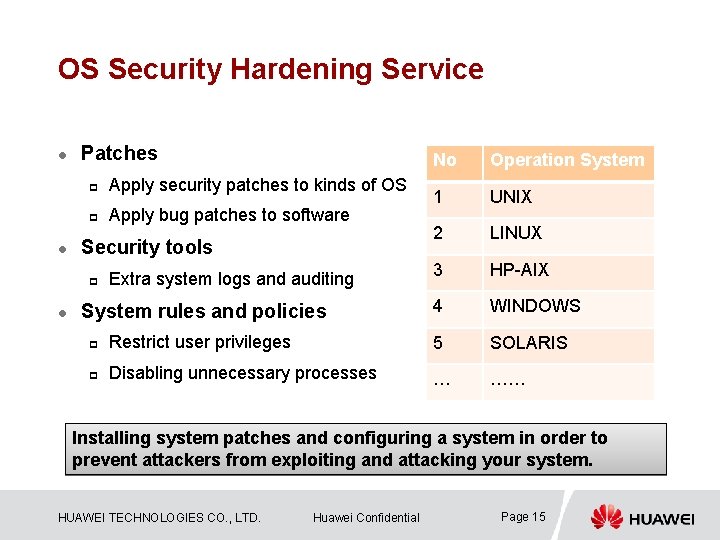
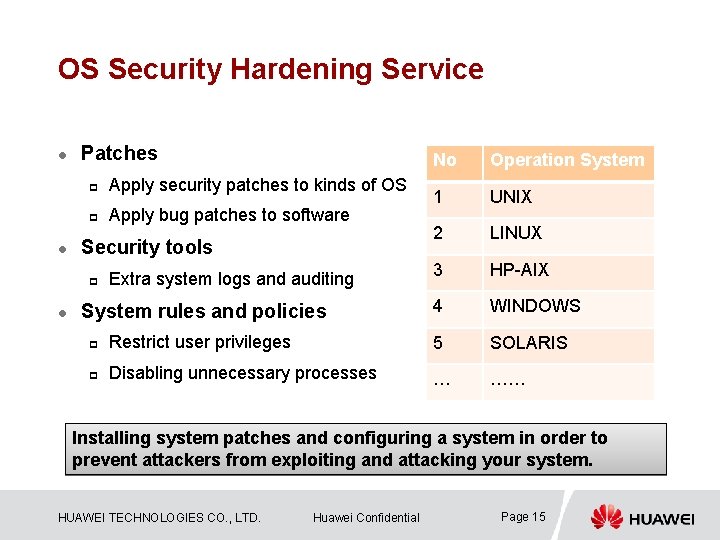
OS Security Hardening Service l l Patches No Operation System 1 UNIX 2 LINUX 3 HP-AIX System rules and policies 4 WINDOWS p Restrict user privileges 5 SOLARIS p Disabling unnecessary processes … …… p Apply security patches to kinds of OS p Apply bug patches to software Security tools p l Extra system logs and auditing Installing system patches and configuring a system in order to prevent attackers from exploiting and attacking your system. HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 15
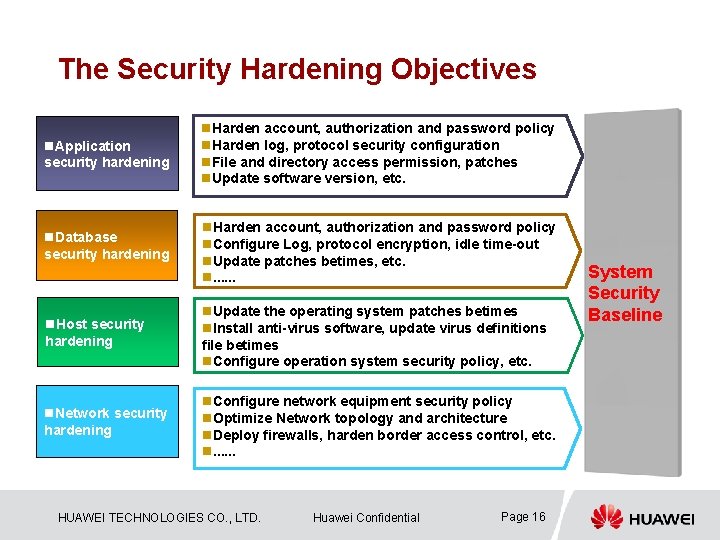
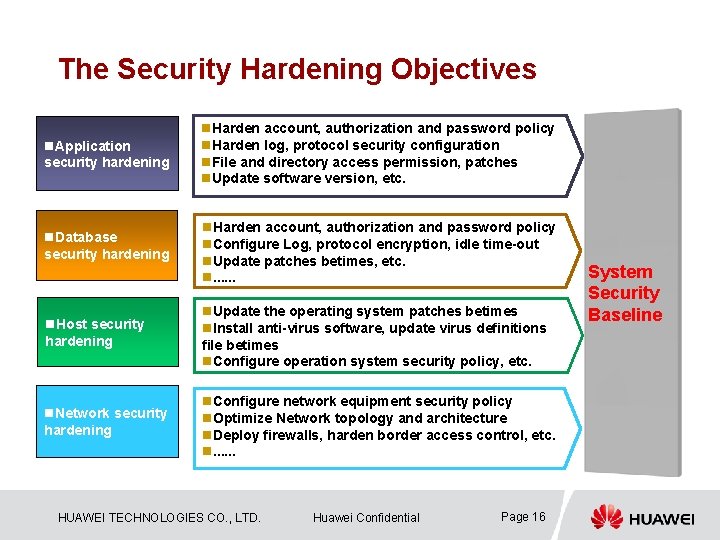
The Security Hardening Objectives n. Application security hardening n. Harden account, authorization and password policy n. Harden log, protocol security configuration n. File and directory access permission, patches n. Update software version, etc. n. Database security hardening n. Harden account, authorization and password policy n. Configure Log, protocol encryption, idle time-out n. Update patches betimes, etc. n. . . n. Host security hardening n. Update the operating system patches betimes n. Install anti-virus software, update virus definitions file betimes n. Configure operation system security policy, etc. n. Network security hardening n. Configure network equipment security policy n. Optimize Network topology and architecture n. Deploy firewalls, harden border access control, etc. n. . . HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 16 System Security Baseline
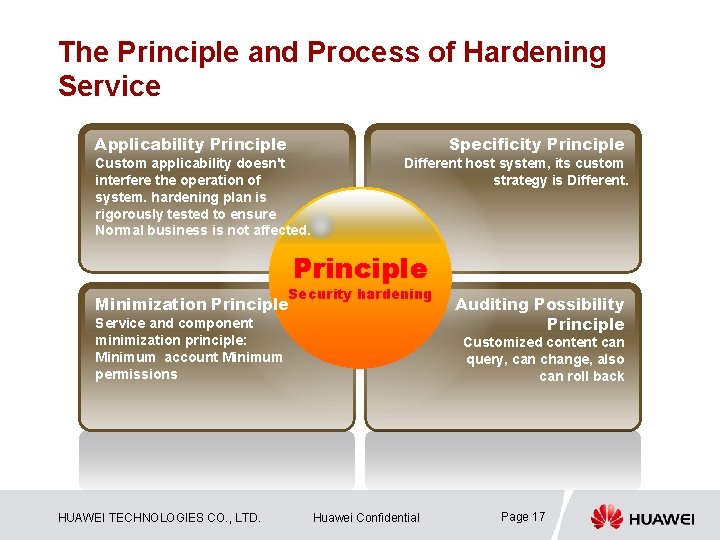
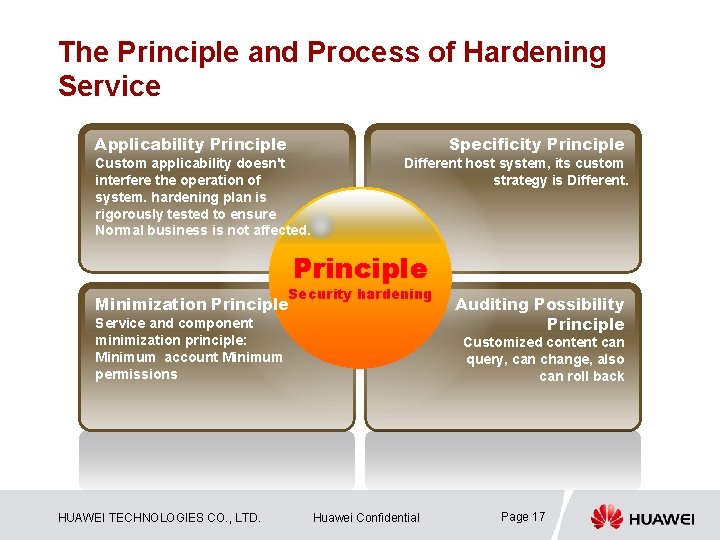
The Principle and Process of Hardening Service Applicability Principle Specificity Principle Custom applicability doesn't interfere the operation of system. hardening plan is rigorously tested to ensure Normal business is not affected. Different host system, its custom strategy is Different. Principle Security hardening Minimization Principle Service and component minimization principle: Minimum account Minimum permissions HUAWEI TECHNOLOGIES CO. , LTD. Auditing Possibility Principle Customized content can query, can change, also can roll back Huawei Confidential Page 17
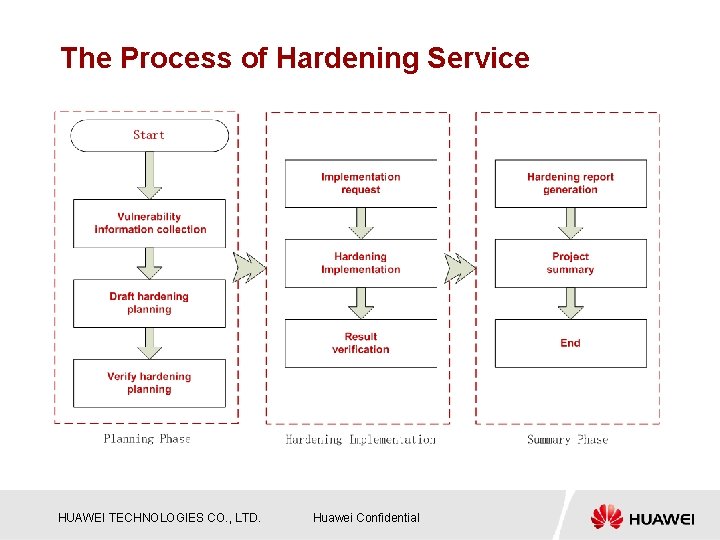
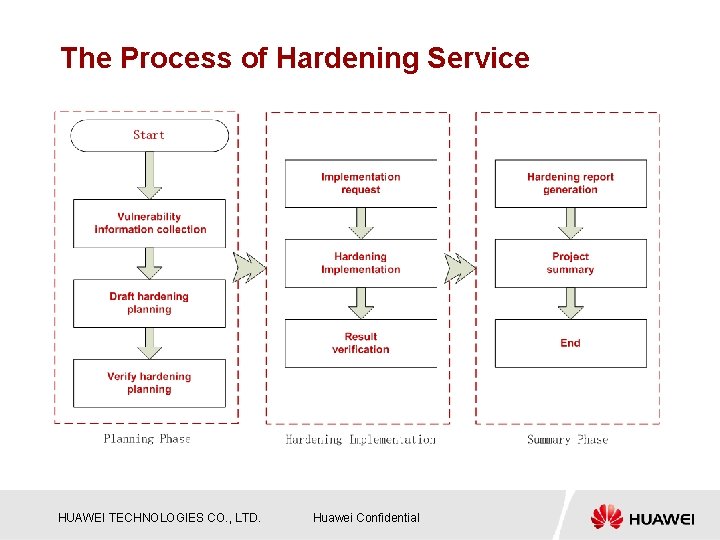
The Process of Hardening Service HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential

1 The Industry of Security Overview 2 The Challenge of Security Facing 3 Security Hardening Services Package 4 Security Service Advantages & Values 5 Successful Stories HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 19
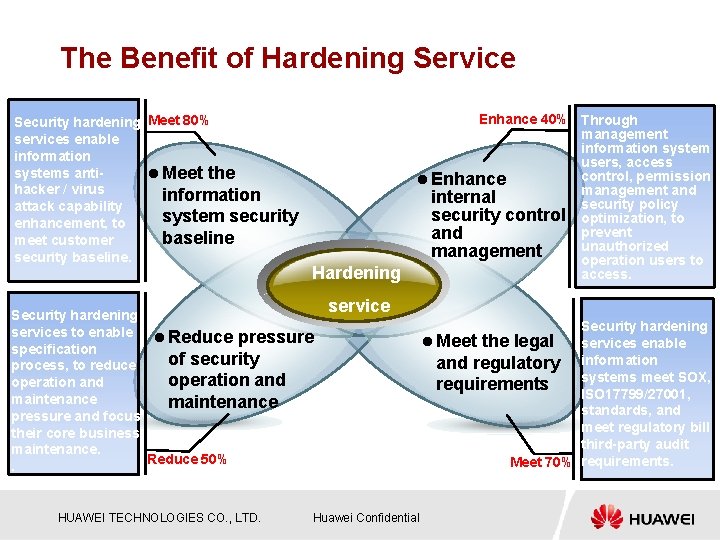
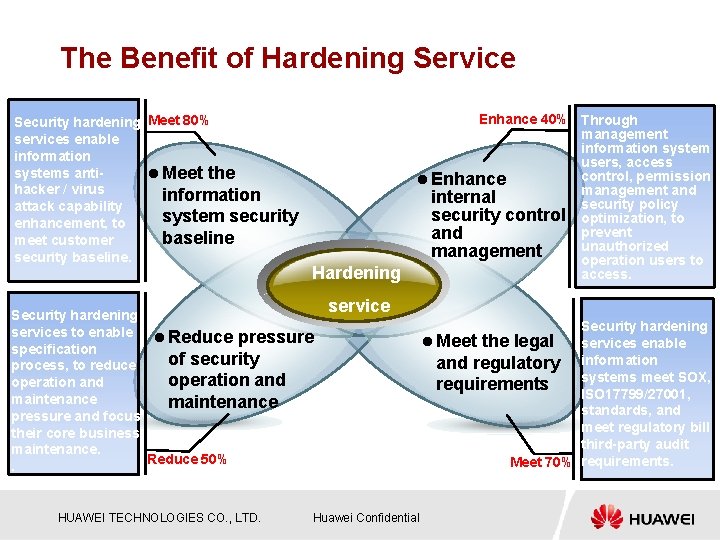
The Benefit of Hardening Service Security hardening Meet 80% services enable information systems antil Meet the hacker / virus information attack capability system security enhancement, to baseline meet customer security baseline. Hardening Security hardening services to enable l Reduce pressure specification of security process, to reduce operation and maintenance pressure and focus their core business maintenance. Reduce 50%. HUAWEI TECHNOLOGIES CO. , LTD. Enhance 40% Through management information system users, access control, permission l Enhance management and internal security policy security control optimization, to prevent and unauthorized management operation users to access. service Huawei Confidential Security hardening l Meet the legal services enable and regulatory information systems meet SOX, requirements ISO 17799/27001, standards, and meet regulatory bill third-party audit Meet 70% requirements.
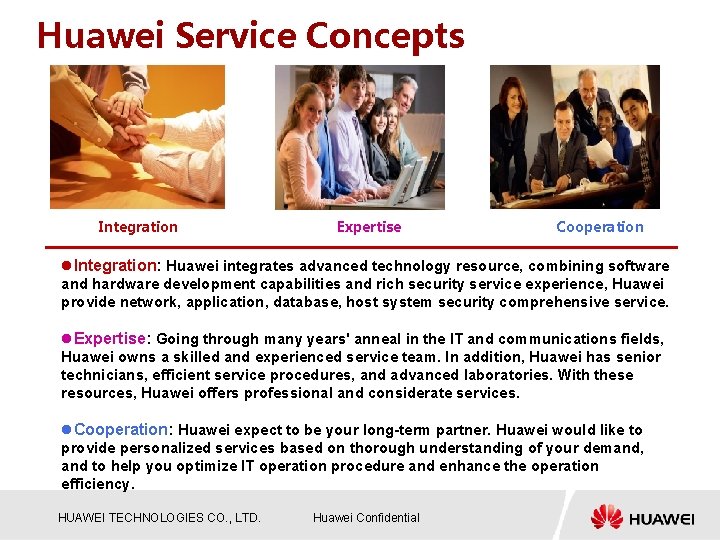
Huawei Service Concepts Integration Expertise Cooperation l. Integration: Huawei integrates advanced technology resource, combining software and hardware development capabilities and rich security service experience, Huawei provide network, application, database, host system security comprehensive service. l. Expertise: Going through many years' anneal in the IT and communications fields, Huawei owns a skilled and experienced service team. In addition, Huawei has senior technicians, efficient service procedures, and advanced laboratories. With these resources, Huawei offers professional and considerate services. l. Cooperation: Huawei expect to be your long-term partner. Huawei would like to provide personalized services based on thorough understanding of your demand, and to help you optimize IT operation procedure and enhance the operation efficiency. HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential
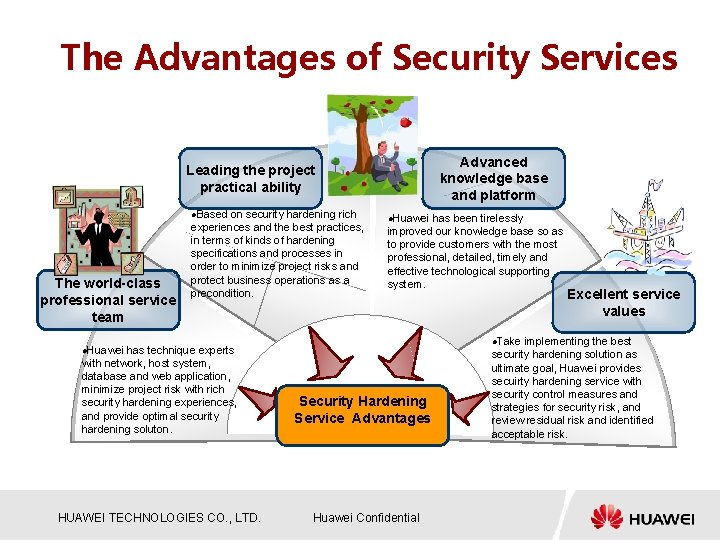
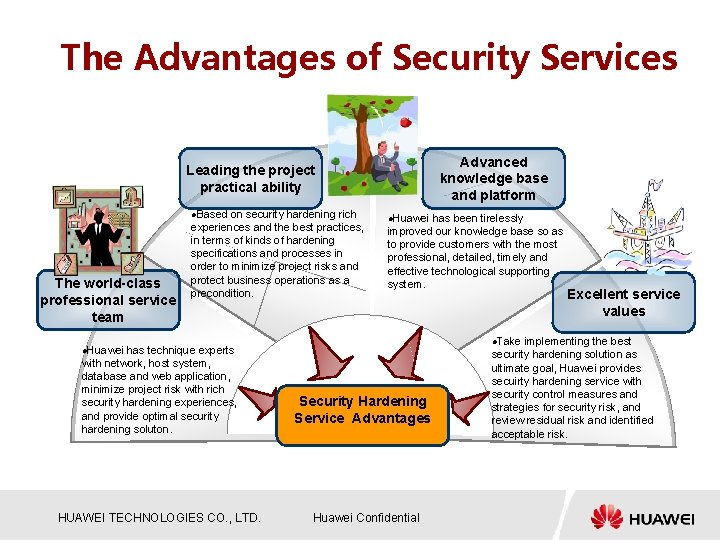
The Advantages of Security Services Advanced knowledge base and platform Leading the project practical ability l. Based The world-class professional service team on security hardening rich experiences and the best practices, in terms of kinds of hardening specifications and processes in order to minimize project risks and protect business operations as a precondition. has technique experts with network, host system, database and web application, minimize project risk with rich security hardening experiences, and provide optimal security hardening soluton. l. Huawei has been tirelessly improved our knowledge base so as to provide customers with the most professional, detailed, timely and effective technological supporting system. l. Take l. Huawei HUAWEI TECHNOLOGIES CO. , LTD. Security Hardening Service Advantages Huawei Confidential Excellent service values implementing the best security hardening solution as ultimate goal, Huawei provides secuirty hardening service with security control measures and strategies for security risk, and review residual risk and identified acceptable risk.
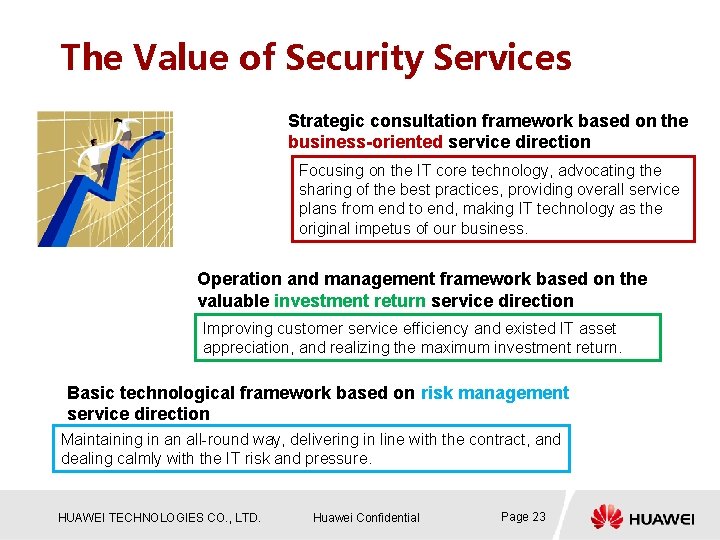
The Value of Security Services Strategic consultation framework based on the business-oriented service direction Focusing on the IT core technology, advocating the sharing of the best practices, providing overall service plans from end to end, making IT technology as the original impetus of our business. Operation and management framework based on the valuable investment return service direction Improving customer service efficiency and existed IT asset appreciation, and realizing the maximum investment return. Basic technological framework based on risk management service direction Maintaining in an all-round way, delivering in line with the contract, and dealing calmly with the IT risk and pressure. HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 23
Security Perspective Advance brand value Improve investment efficiency Enhance security ability Solve security problem HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 24

1 The Industry of Security Overview 2 The Challenge of Security Facing 3 Security Hardening Services Package 4 Security Service Advantages & Values 5 Successful Stories HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 25
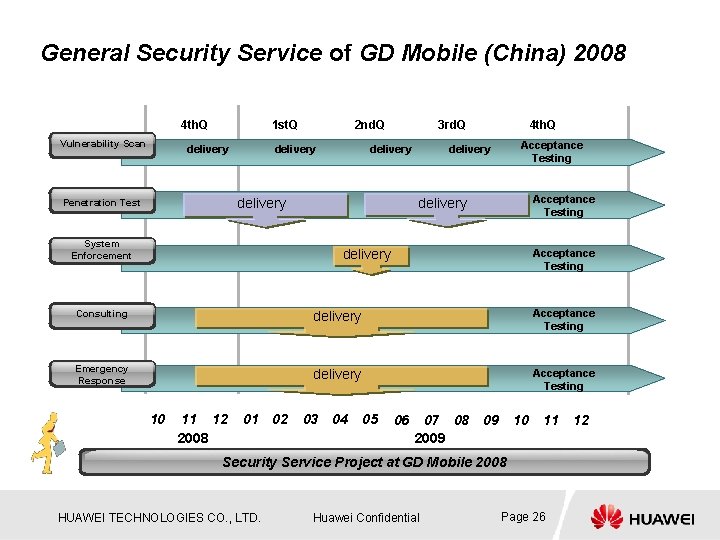
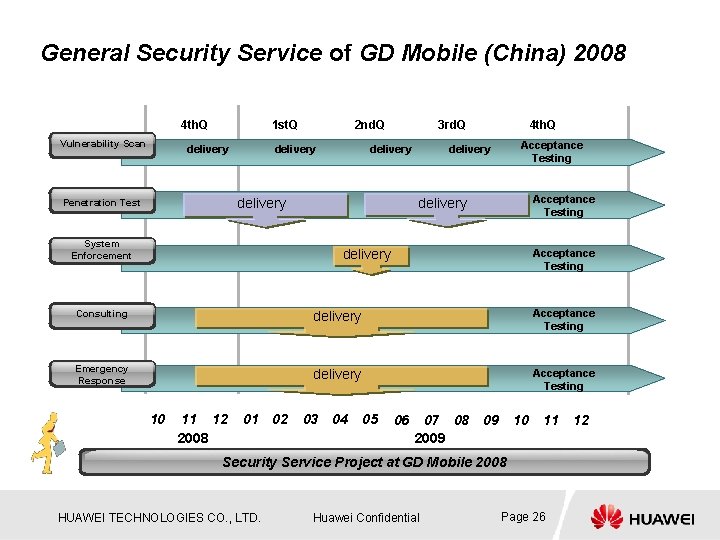
General Security Service of GD Mobile (China) 2008 4 th. Q Vulnerability Scan 1 st. Q delivery 2 nd. Q delivery 3 rd. Q delivery Acceptance Testing delivery Penetration Test 4 th. Q System Enforcement delivery Acceptance Testing Consulting delivery Acceptance Testing Emergency Response delivery Acceptance Testing 10 11 12 2008 01 02 03 04 05 06 07 08 2009 09 10 11 Security Service Project at GD Mobile 2008 HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 26 12
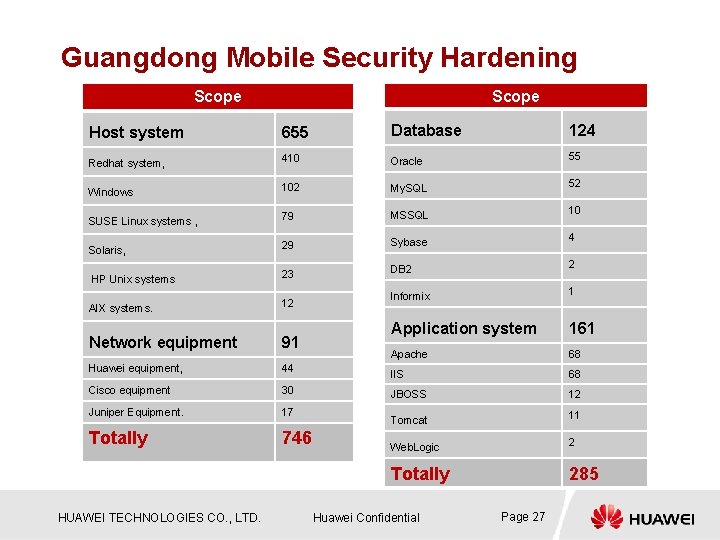
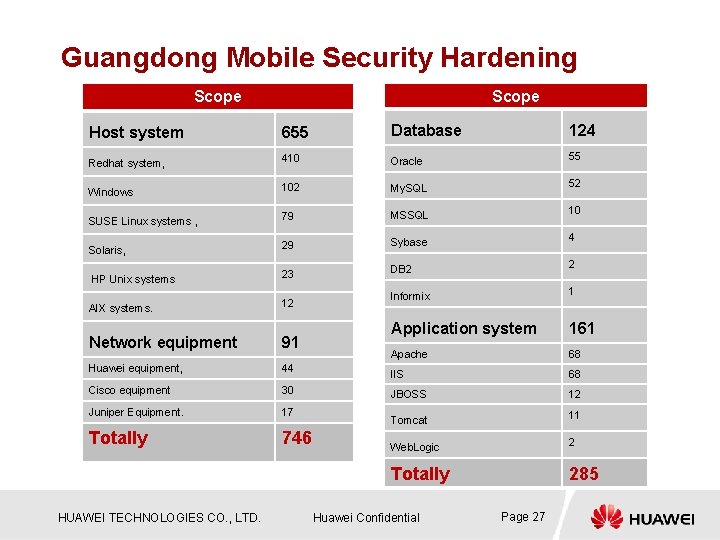
Guangdong Mobile Security Hardening Scope Host system 655 Database 124 Redhat system, 410 Oracle 55 Windows 102 My. SQL 52 SUSE Linux systems , 79 MSSQL 10 29 Sybase 4 Solaris, DB 2 2 HP Unix systems 23 Informix 1 AIX systems. 12 Application system 161 Apache 68 IIS 68 JBOSS 12 Tomcat 11 Web. Logic 2 Totally 285 Network equipment 91 Huawei equipment, 44 Cisco equipment 30 Juniper Equipment. 17 Totally 746 HUAWEI TECHNOLOGIES CO. , LTD. Huawei Confidential Page 27
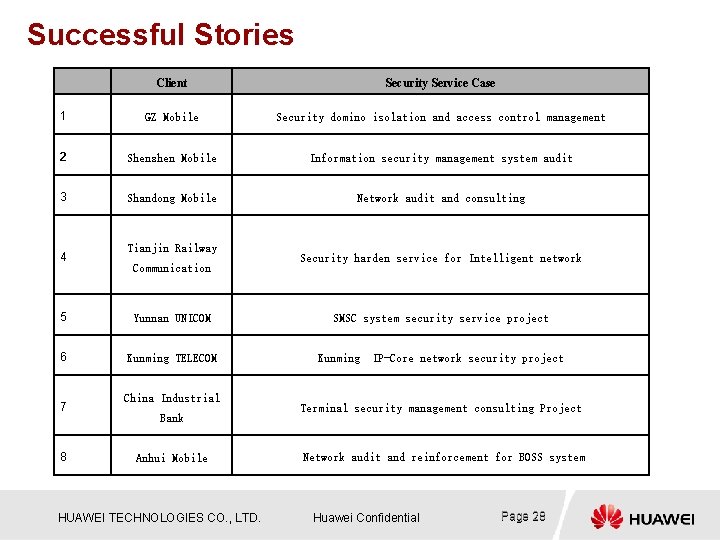
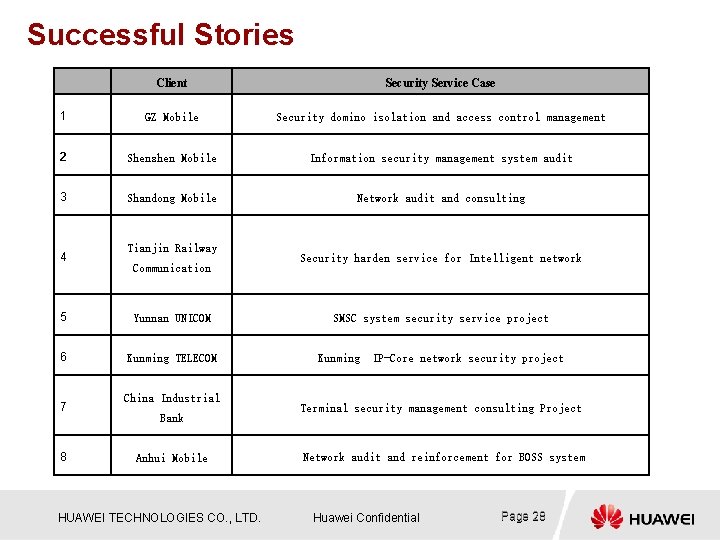
Successful Stories Client Security Service Case 1 GZ Mobile Security domino isolation and access control management 2 Shenzhen Mobile Information security management system audit 3 Shandong Mobile Network audit and consulting 4 Tianjin Railway Communication 5 Yunnan UNICOM 6 Kunming TELECOM 7 8 China Industrial Bank Anhui Mobile HUAWEI TECHNOLOGIES CO. , LTD. Security harden service for Intelligent network SMSC system security service project Kunming IP-Core network security project Terminal security management consulting Project Network audit and reinforcement for BOSS system Huawei Confidential Page 28

Thank you www. huawei. com Copyright© 2007 Huawei Technologies Co. , Ltd. All Rights Reserved. The information contained in this document is for reference purpose only, and is subject to change or withdrawal according to specific customer requirements and conditions.