Security Issues Onno W Purbo Computer Network Research
Security Issues Onno W. Purbo Computer Network Research Group Institute of Technology Bandung yc 1 dav@itb. ac. id Computer Network Research Group ITB
Perspective. . . less then 200 security incident in 1989. l about 400 in 1989. l about 1400 in 1993. l estimated more than 2241 in 1994. l Nobody knows the correct statistics on how many attacks are actually detected by the sites broken into. l Computer Network Research Group ITB
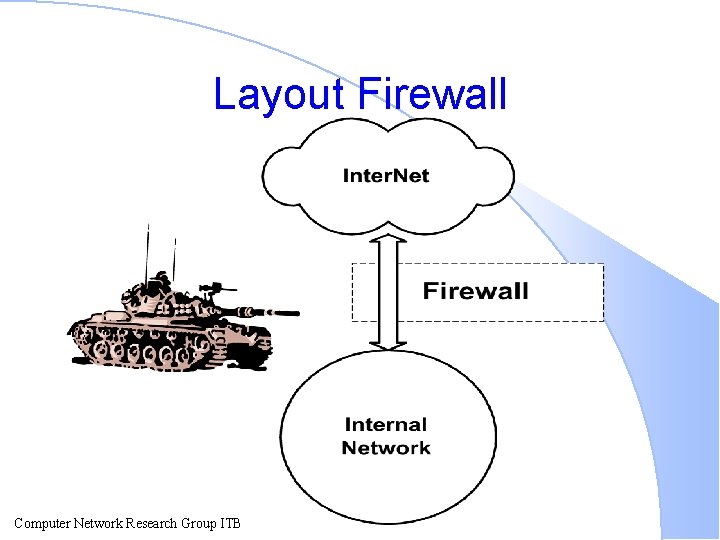
Layout Firewall Computer Network Research Group ITB
What are you trying to protect? Your Data. l Your Resources. l Your Reputation. l Computer Network Research Group ITB
What Are You Trying To Protect Against? l Type of attacks Intrusion. l Denial of Service. l Information Theft. l Computer Network Research Group ITB
Type of Attackers Joyriders. l Vandals. l Score Keepers. l Spies (Industrial & Otherwise). l Stupidity & Accidents. l Computer Network Research Group ITB
How Can You Protect Your Site No Security. l Security Through Obscurity. l Host Security. l Network Security. l No Security Model Can Do It All. l Computer Network Research Group ITB
What Can A Firewall Do? A firewall is a focus for security decisions. l A firewall can enforce security policy. l A firewall can log Internet activity efficiently. l A firewall limits your exposure. l Computer Network Research Group ITB
What Can’t A Firewall Do? A firewall can’t protect you against malicious insiders. l A firewall can’t protect you against connections that don’t go through it. l A firewall can’t protect against completely new threats. l A firewall can’t protect against viruses. l Computer Network Research Group ITB
List of A Must Secure Internet Services Electronic mail (SMTP). l File Transfer (FTP). l Usenet News (NNTP). l Remote Terminal Access (Telnet). l World Wide Web Access (HTTP). l Hostname / Address lookup (DNS). l Computer Network Research Group ITB
Security Strategies. Least Privilege. l Defense in Depth (multiple security mechanism). l Choke Point forces attackers to use a narrow channel. l Weakest Link. l Fail-Safe Stance. l Diversity of Defense. l Simplicity. l Computer Network Research Group ITB
Building Firewalls Computer Network Research Group ITB
Some Firewall Definitions l Firewall – A component or set of components that restricts access between a protected network and the Internet, or between other sets of networks. l Host – A computer system attached to a network. Computer Network Research Group ITB
Firewall Def’s Cont’. . l Bastion Host – A computer system that must be highly secured because it is vulnerable to attack, usually because it is exposed to the Internet and is a main point of contact for users of internal networks. l Dual-homed host – A general-purpose computer system that has at least two network interfaces (or homes). Computer Network Research Group ITB
Firewall Def’s Cont. . . l Packet. – The fundamental unit of communication on the Internet. l Packet filtering. – The action a device takes to selectively control the flow of data to and from a network. l Perimeter network. – a network added between a protected network and external network, to provide additional layer of security. Computer Network Research Group ITB
Firewall Def’s Cont. . . l Proxy Server – A program that deals with external servers on behalf of internal clients. Proxy client talk to proxy servers, which relay approved client requests on to real servers, and relay answer back to clients. Computer Network Research Group ITB
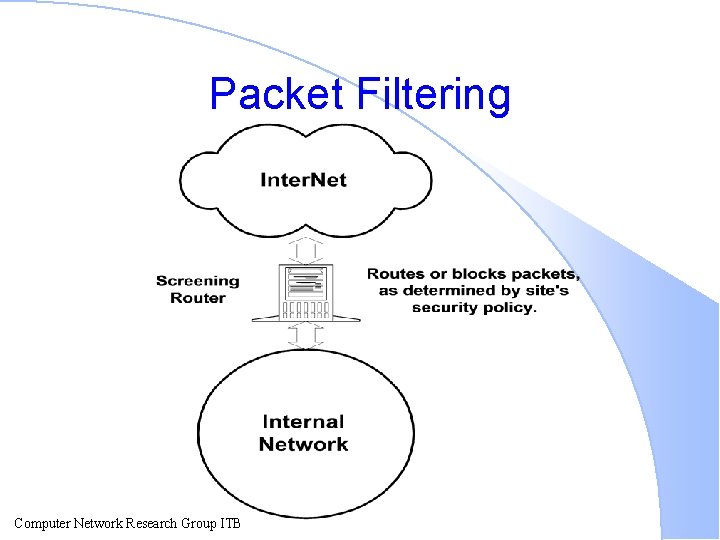
Packet Filtering Computer Network Research Group ITB
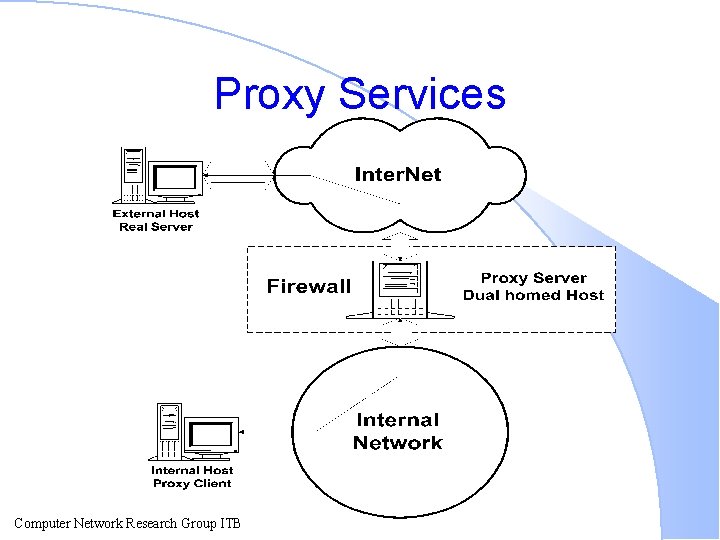
Proxy Services Computer Network Research Group ITB
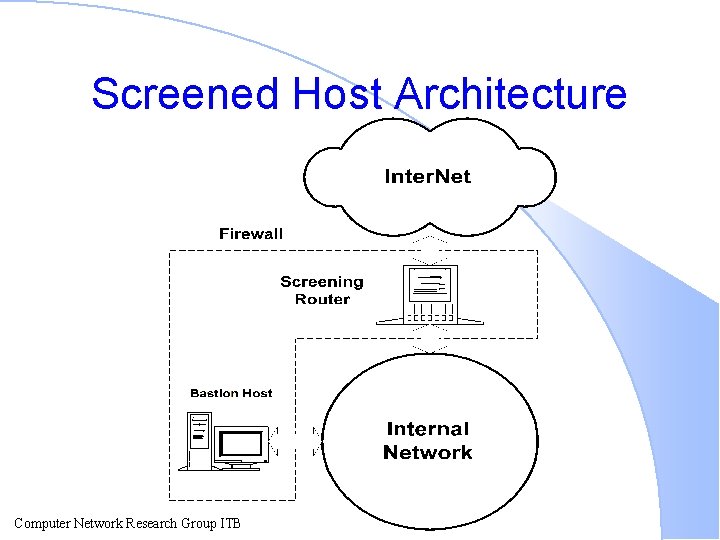
Screened Host Architecture Computer Network Research Group ITB
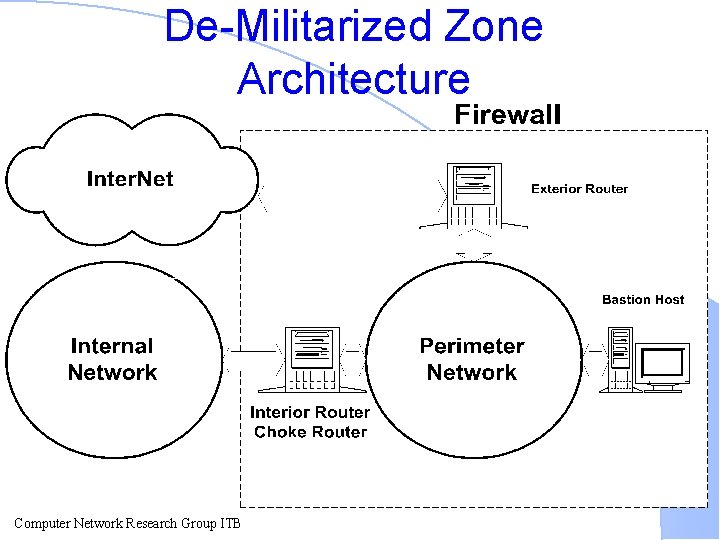
De-Militarized Zone Architecture Computer Network Research Group ITB
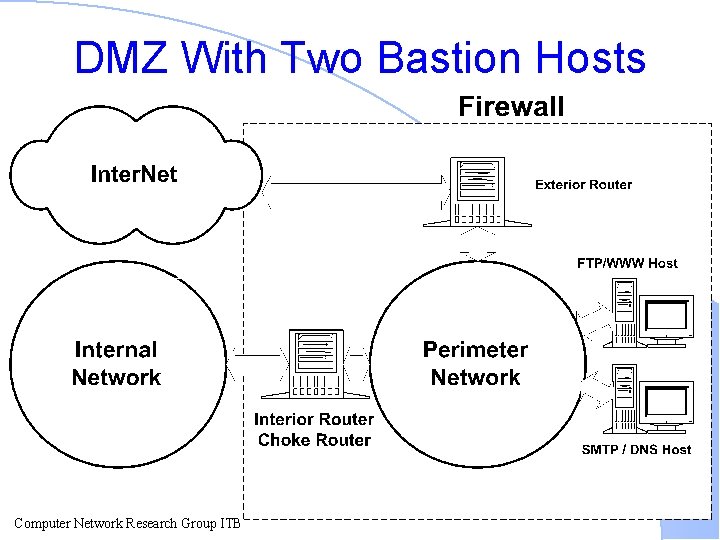
DMZ With Two Bastion Hosts Computer Network Research Group ITB
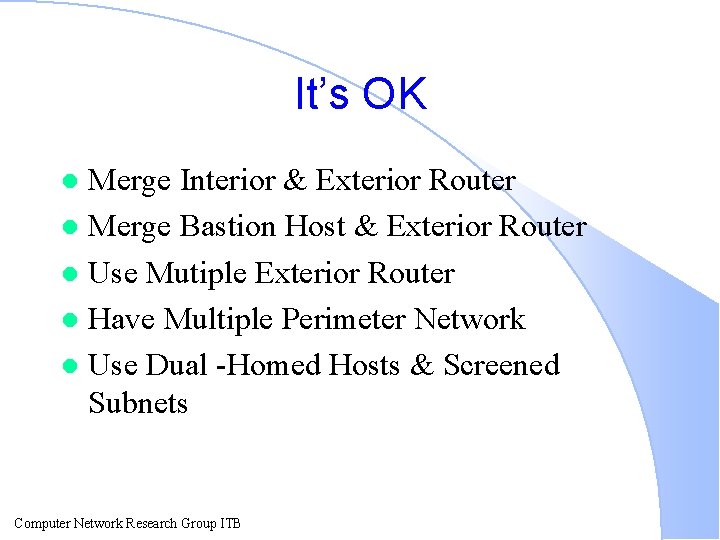
It’s OK Merge Interior & Exterior Router l Merge Bastion Host & Exterior Router l Use Mutiple Exterior Router l Have Multiple Perimeter Network l Use Dual -Homed Hosts & Screened Subnets l Computer Network Research Group ITB
It’s Dangerous Use Multiple Interior Router l Merge Bastion Host and Interior Router l Computer Network Research Group ITB
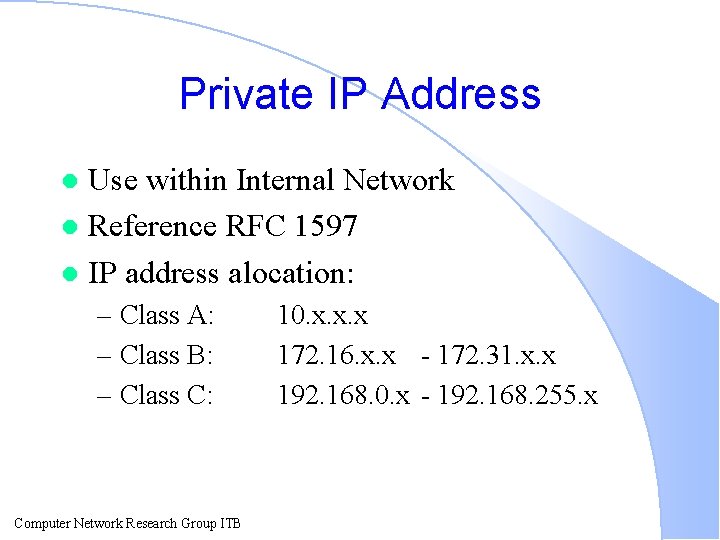
Private IP Address Use within Internal Network l Reference RFC 1597 l IP address alocation: l – Class A: – Class B: – Class C: Computer Network Research Group ITB 10. x. x. x 172. 16. x. x - 172. 31. x. x 192. 168. 0. x - 192. 168. 255. x
Bastion Host l It is our presence in Internet. Keep it simple. l Be prepared for the bastion host to be compromised. l Computer Network Research Group ITB
Special Kinds of Bastion Hosts Nonrouting Dual-Homed Hosts. l Victim Machine. l Internal Bastion Hosts. l Computer Network Research Group ITB
Choosing A Bastion Host l What Operating System? – Unix l How Fast a Machine? – 386 -based UNIX. – Micro. VAX II – Sun-3 Computer Network Research Group ITB
Proxy Systems l Why Proxying? – Proxy systems deal with the insecurity problems by avoiding user logins on the dualhomed host and by forcing connections through controlled software. – It’s also impossible for anybody to install uncontrolled software to reach Internet; the proxy acts as a control point. Computer Network Research Group ITB
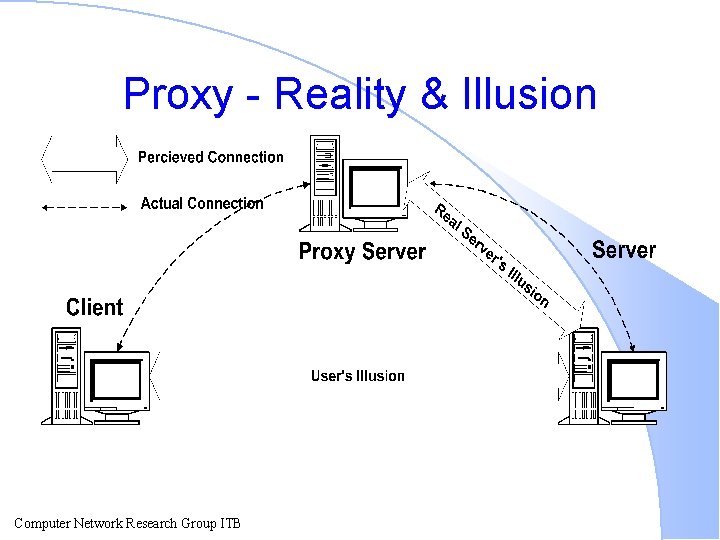
Proxy - Reality & Illusion Computer Network Research Group ITB
Advantages of Proxying Proxy services allow users to access Internet services “directly” l Proxy services are good at logging. l Computer Network Research Group ITB
Disadvantages of Proxying Proxy services lag behind non-proxied services. l Proxy services may require different servers for each service. l Proxy services usually require modifications to clients, procedures, or both. l Proxy services aren’t workable for some services. l Proxy services don’t protect you from all protocol weaknesses. l Computer Network Research Group ITB
Proxying without a Proxy Server Store-and-Forward services naturally support proxying. l Examples: l – E-mail (SMTP). – News (NNTP). – Time (NTP). Computer Network Research Group ITB
Internet Resources on Security Issues Computer Network Research Group ITB
WWW Pages http: //www. telstra. com. au/info/security. html l http: //www. cs. purdue. edu/coast. html l Computer Network Research Group ITB
Mailing Lists l firewalls@greatcircle. com – ftp: //ftp. greatcircle. com/pub/firewalls/ – http: //www. greatcircle. com/firewalls/ fwall-users@tis. com l academic-firewalls@net. tamu. edu l – ftp: //net. tamu. edu/pub/security/lists/academicfirewalls l bugtraq@fc. net Computer Network Research Group ITB

Newsgroups comp. security. announce. l comp. security. unix. l comp. security. misc. l comp. security. firewalls. l alt. security. l comp. admin. policy. l comp. protocols. tcp-ip. l comp. unix. admin. l comp. unix. wizards l Computer Network Research Group ITB
Summary In these dangerous times, firewalls are the best way to keep your site secure. l Although you’ve got to include other tipes of security in the mix, if you’re serious about connecting to the Internet, firewall should be at the very center of your security plans. l Computer Network Research Group ITB
- Slides: 37