Security Issues and Strategies Copyright 2003 Paradigm Publishing
Security Issues and Strategies Copyright 2003, Paradigm Publishing Inc.
Topics Cyber Crime: A Growing Issue Protecting Computer Systems and Data Network and Internet Security Risks Security Strategies Computer Viruses On the Horizon Hardware and Software Security Risks Topics Copyright 2002, Paradigm Publishing Inc. 14 - 2
Cyber Crime: A Growing Issue network and Internet security risks hardware and software security risks as we become increasingly dependent on computer systems, the properation grows correspondingly in importance computer viruses Topics Copyright 2002, Paradigm Publishing Inc. 14 - 3
Network and Internet Security Risks the Internet lacks borders - makes it valuable and vulnerable - legal systems not designed to adjust for rapid technological changes Topics Copyright 2002, Paradigm Publishing Inc. 14 - 4
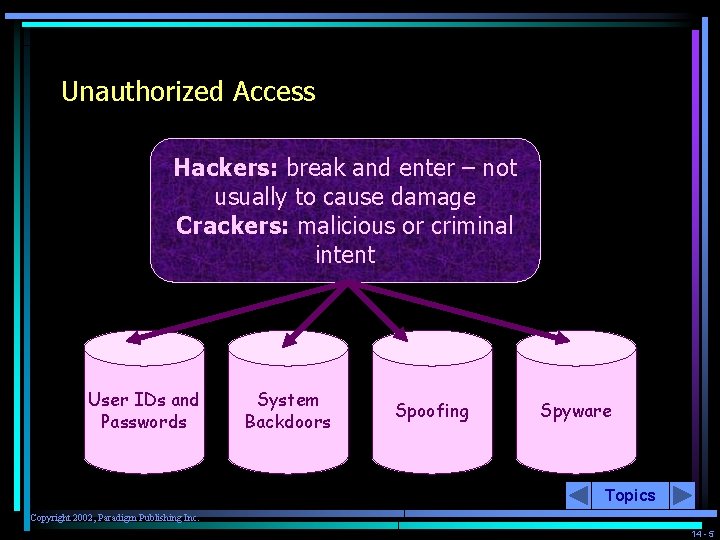
Unauthorized Access Hackers: break and enter – not usually to cause damage Crackers: malicious or criminal intent User IDs and Passwords System Backdoors Spoofing Spyware Topics Copyright 2002, Paradigm Publishing Inc. 14 - 5
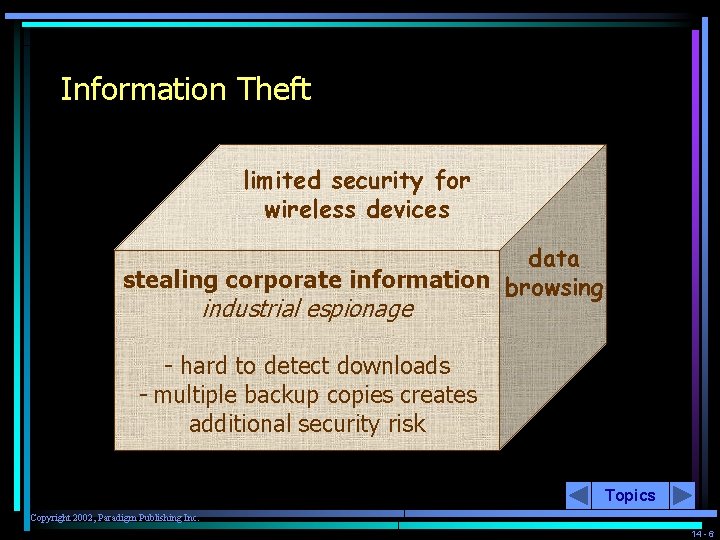
Information Theft limited security for wireless devices data stealing corporate information browsing industrial espionage - hard to detect downloads - multiple backup copies creates additional security risk Topics Copyright 2002, Paradigm Publishing Inc. 14 - 6
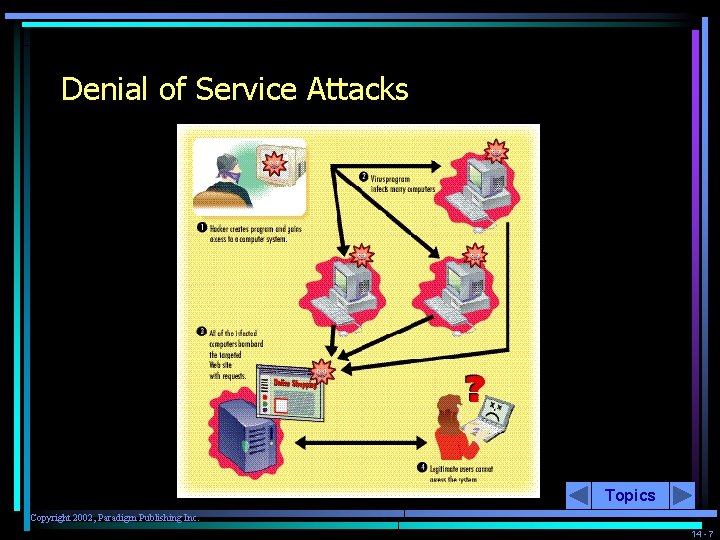
Denial of Service Attacks Topics Copyright 2002, Paradigm Publishing Inc. 14 - 7
Computer Viruses One of the most familiar forms of risk to computer security – drawing an offensive image – changing document characters to another language – reformatting hard drive – damaging the motherboard Topics Copyright 2002, Paradigm Publishing Inc. 14 - 8
Types of Viruses data-destructive nuisance hardware-destructive espionage Topics Copyright 2002, Paradigm Publishing Inc. 14 - 9
Methods of Virus Operation E-mail – transmitted as an attachment Macro – subprogram written specifically for one program Boot Sector – alters the boot sector of a floppy Trojan Horse – hides inside another program Stealth – hides itself from detection software Polymorphic – alter themselves to prevent detection Multipartite – alter their form of attack Logic (time) Bombs – dormant until specific event or condition occurs Topics Copyright 2002, Paradigm Publishing Inc. 14 - 10
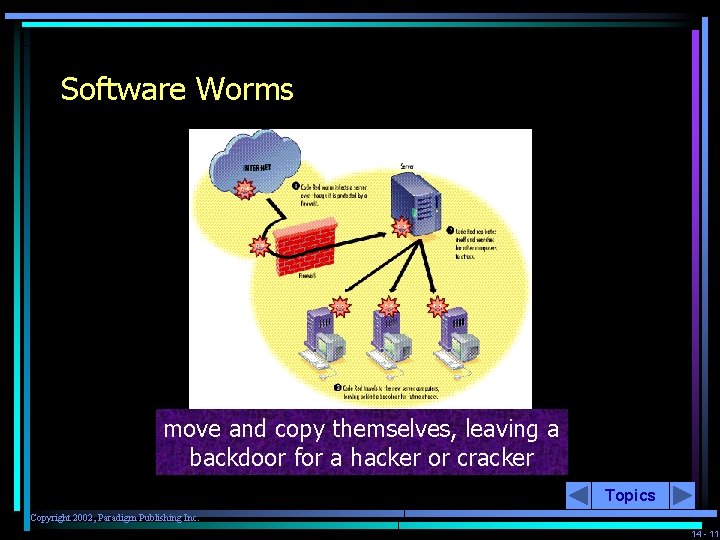
Software Worms move and copy themselves, leaving a backdoor for a hacker or cracker Topics Copyright 2002, Paradigm Publishing Inc. 14 - 11
Virus Symptoms Some files become corrupted and do not work properly Specific program does not operate properly Programs or files have suddenly vanished Unknown programs or files appear on hard drive Strange messages or images display on monitor System has less available memory or disk space than it should A disk or volume name has been changed Unexpected sounds are played at random times You receive same e-mail message repeatedly Topics Copyright 2002, Paradigm Publishing Inc. 14 - 12
Antivirus Software Norton Antivirus can only detect viruses with known signatures the Internet allows antivirus software to update itself the majority of viruses in the wild are e-mail attachments Topics Copyright 2002, Paradigm Publishing Inc. 14 - 13
Hardware and Software Security Risks Systems failure – power spike can cause poor performance or permanently damage hardware • surge protector • uninterruptible power supply Employee theft – cost involves replacing hardware, lost data, time lost, installation of new machines, training Cracking software for copying – crack a software protection scheme Topics Copyright 2002, Paradigm Publishing Inc. 14 - 14
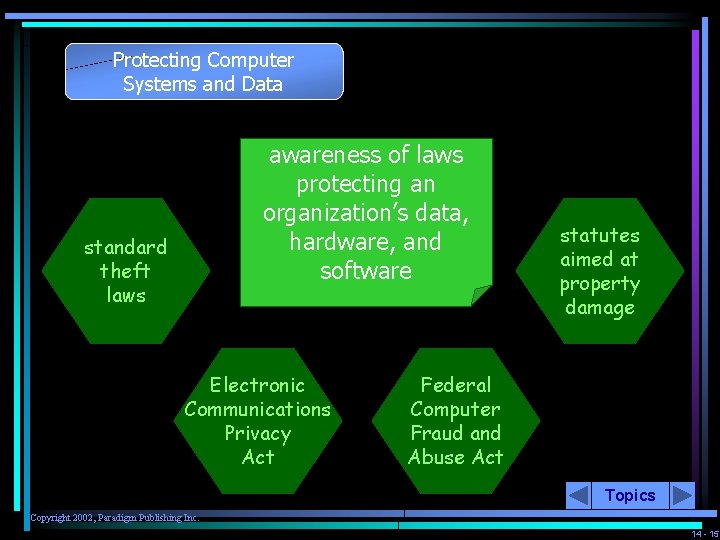
Protecting Computer Systems and Data awareness of laws protecting an organization’s data, hardware, and software standard theft laws Electronic Communications Privacy Act statutes aimed at property damage Federal Computer Fraud and Abuse Act Topics Copyright 2002, Paradigm Publishing Inc. 14 - 15
Security Strategies As the Internet and computer technology have evolved, security strategies to prevent damage and losses have been developed Topics Copyright 2002, Paradigm Publishing Inc. 14 - 16
Data Backups prepare for the worst Backups one n a h t more place e f a s a n i keep update regula rly rotatin g Topics Copyright 2002, Paradigm Publishing Inc. 14 - 17
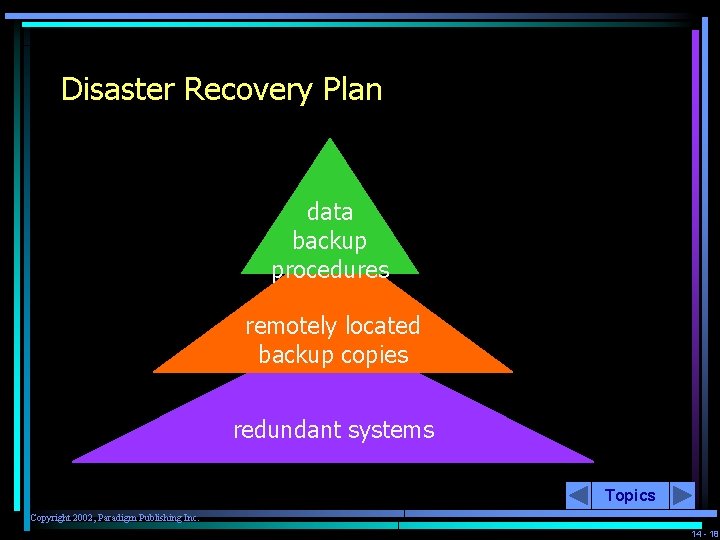
Disaster Recovery Plan data backup procedures remotely located backup copies redundant systems Topics Copyright 2002, Paradigm Publishing Inc. 14 - 18
Data Encryption to prevent people from spying on sensitive transactions schemes include encryption key that is generated automatically and shared between two communicating computers Topics Copyright 2002, Paradigm Publishing Inc. 14 - 19
Firewall on computers attached to the Internet checks incoming data against a list of known, trusted sources Topics Copyright 2002, Paradigm Publishing Inc. 14 - 20
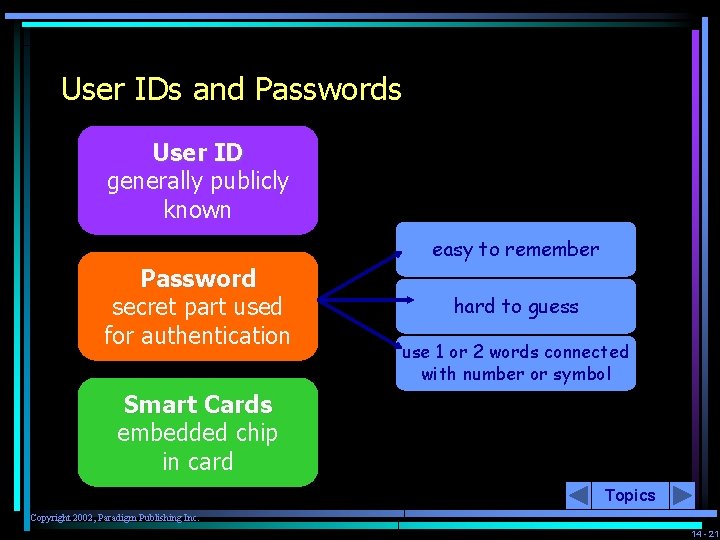
User IDs and Passwords User ID generally publicly known easy to remember Password secret part used for authentication hard to guess use 1 or 2 words connected with number or symbol Smart Cards embedded chip in card Topics Copyright 2002, Paradigm Publishing Inc. 14 - 21
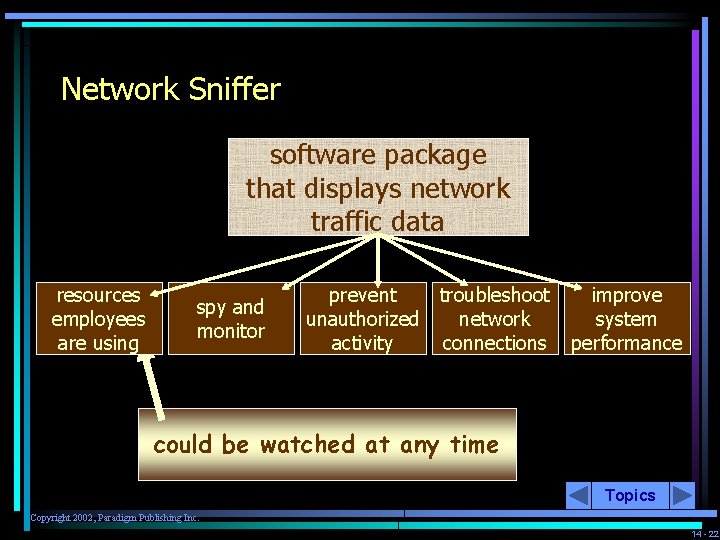
Network Sniffer software package that displays network traffic data resources employees are using spy and monitor prevent troubleshoot unauthorized network activity connections improve system performance could be watched at any time Topics Copyright 2002, Paradigm Publishing Inc. 14 - 22
Mini Web Cam originally designed to allow for audio/video conversations now used as a security tool Topics Copyright 2002, Paradigm Publishing Inc. 14 - 23
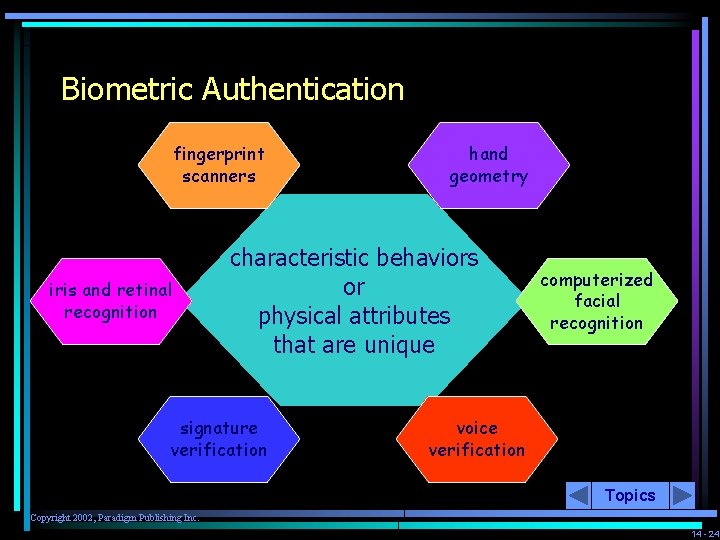
Biometric Authentication fingerprint scanners iris and retinal recognition hand geometry characteristic behaviors or physical attributes that are unique signature verification computerized facial recognition voice verification Topics Copyright 2002, Paradigm Publishing Inc. 14 - 24
On the Horizon Keystroke Identification Quantum Cryptography Topics Copyright 2002, Paradigm Publishing Inc. 14 - 25
Topics Copyright 2002, Paradigm Publishing Inc. 14 - 26
- Slides: 26