Security in Wireless Communications Wireless Communication Security Service
- Slides: 14
Security in Wireless Communications
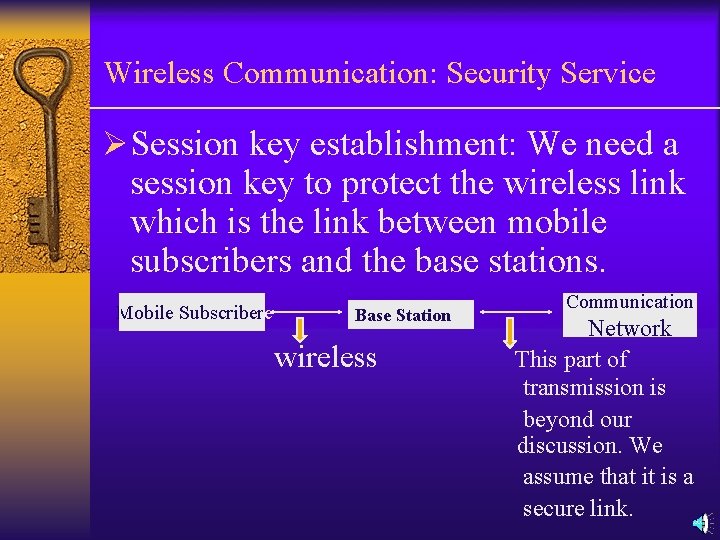
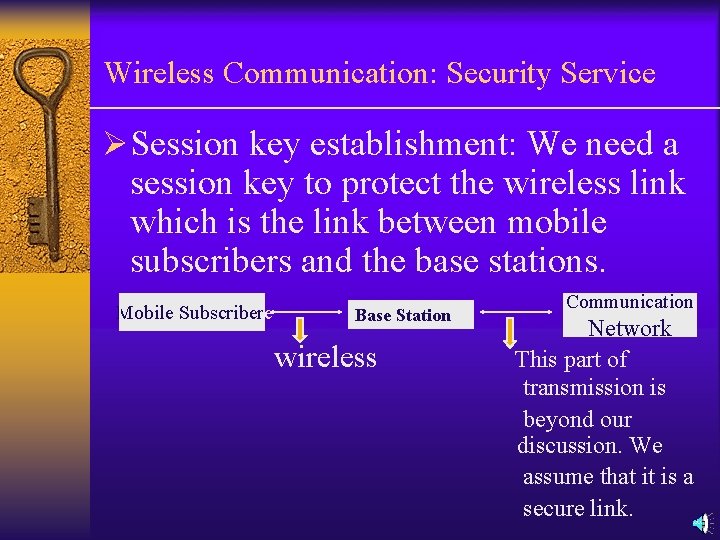
Wireless Communication: Security Service ØSession key establishment: We need a session key to protect the wireless link which is the link between mobile subscribers and the base stations. Mobile Subscribere Base Stationio wireless Communication Network This part of transmission is beyond our discussion. We assume that it is a secure link.
Wireless Communication: Security Services ØCaller ID Confidentiality ØUser authentication: In user registration, the server and user will share an authentication key with HLR. Mobile Subscriber share an authentication key HLR: Home Area Registration VLR: Visiting Area Registration HLR Note: True Caller ID Confidentiality can only be achieved in using public-key cryptosystem.
Wireless Communication: Security Services Ø Mutual authentication: Most servers provide one-way authentication. The server can authenticate the users; but the users cannot authenticate the server. Ø Non-repudiation service
Wireless Communication: Security Services Ø When the mobile subscriber is out of the home service area, the mobile subscriber will need VLR to connect the phone calls. However, HLR does not want to share the authentication key with VLR. Therefore, we should come up with some solutions that can help mobile subscriber to connect phone calls through VLR without revealing the authentication key to the VLR.
GSM (Global System for Mobile Communications) Ø Terms: International Mobile Subscriber Identity (IMSI): When mobile subscribers register in the HLR, each mobile subscriber will get an IMSI from HLR, and an authentication key is shared between HLR and mobile subscriber. A 3, A 8: One-way functions (similar to MD 5) A 5 : Encryption function
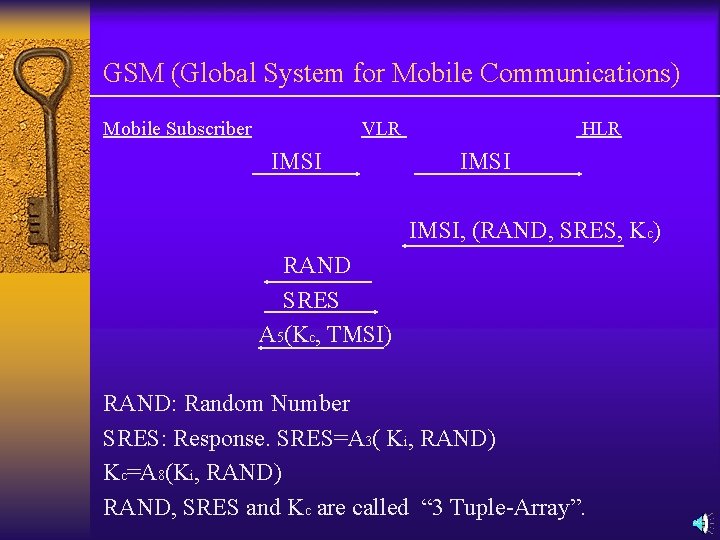
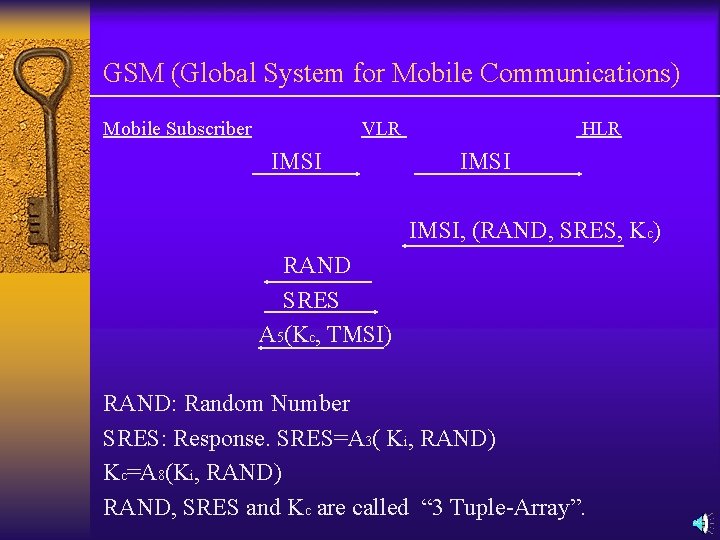
GSM (Global System for Mobile Communications) Mobile Subscriber VLR IMSI HLR IMSI, (RAND, SRES, Kc) RAND SRES A 5(Kc, TMSI) RAND: Random Number SRES: Response. SRES=A 3( Ki, RAND) Kc=A 8(Ki, RAND) RAND, SRES and Kc are called “ 3 Tuple-Array”.
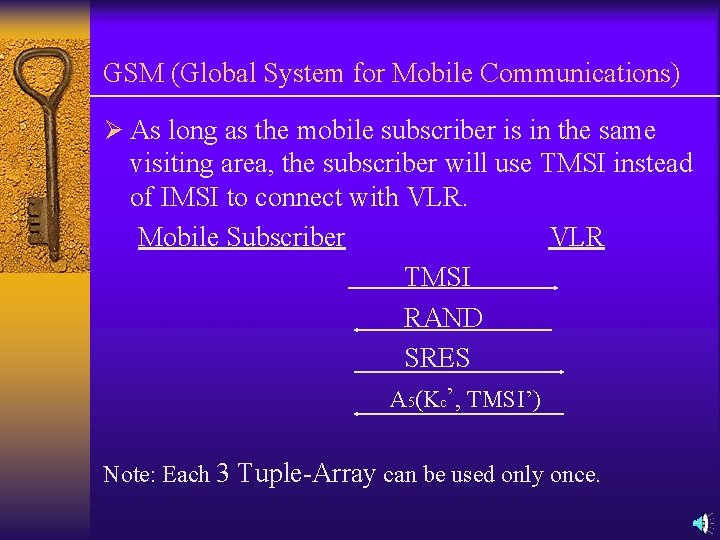
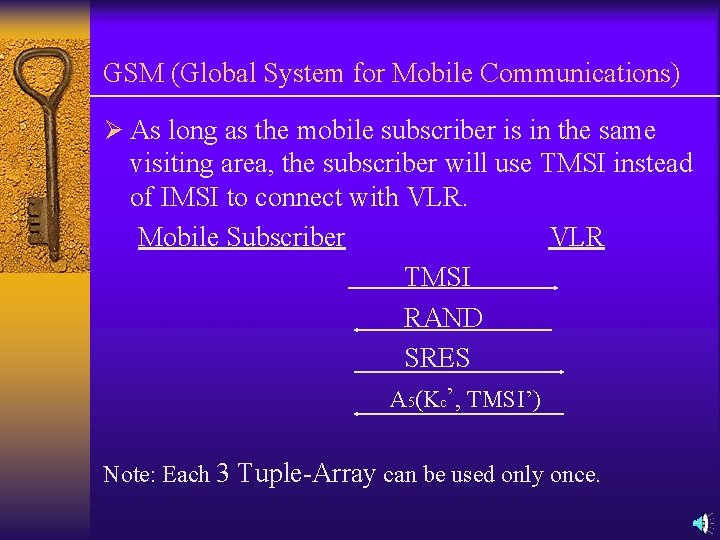
GSM (Global System for Mobile Communications) Ø As long as the mobile subscriber is in the same visiting area, the subscriber will use TMSI instead of IMSI to connect with VLR. Mobile Subscriber VLR TMSI RAND SRES A 5(Kc’, TMSI’) Note: Each 3 Tuple-Array can be used only once.
GSM (Global System for Mobile Communications) Ø When the attackers crack one authentication key, attackers can impersonate the VLR by playing back the corresponding RAND. Ø The VLR can get several “ 3 Tuple-Array ” from HLR at once. This can save time on the communication that is between HLR and VLR.
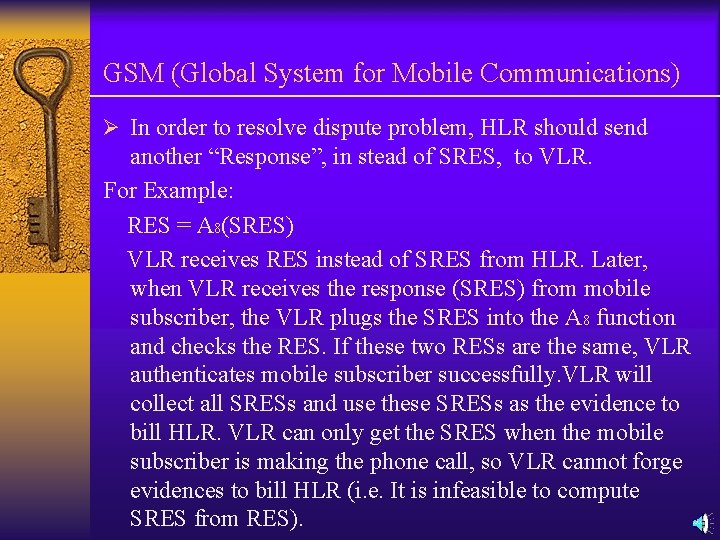
GSM (Global System for Mobile Communications) Ø In order to resolve dispute problem, HLR should send another “Response”, in stead of SRES, to VLR. For Example: RES = A 8(SRES) VLR receives RES instead of SRES from HLR. Later, when VLR receives the response (SRES) from mobile subscriber, the VLR plugs the SRES into the A 8 function and checks the RES. If these two RESs are the same, VLR authenticates mobile subscriber successfully. VLR will collect all SRESs and use these SRESs as the evidence to bill HLR. VLR can only get the SRES when the mobile subscriber is making the phone call, so VLR cannot forge evidences to bill HLR (i. e. It is infeasible to compute SRES from RES).
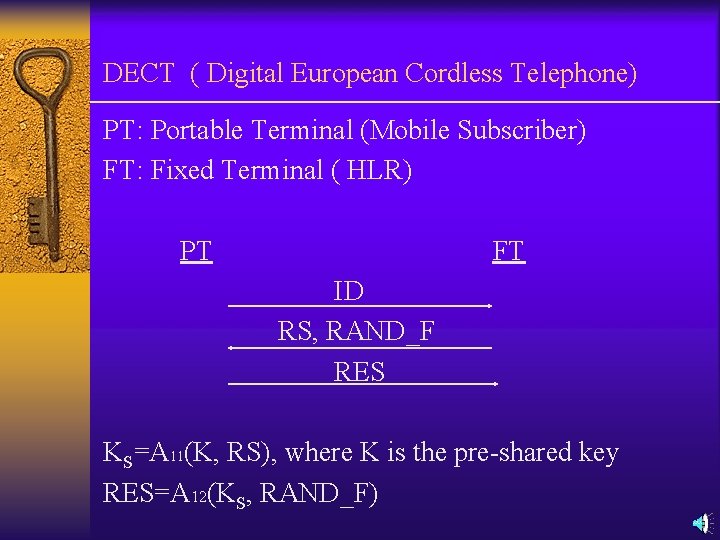
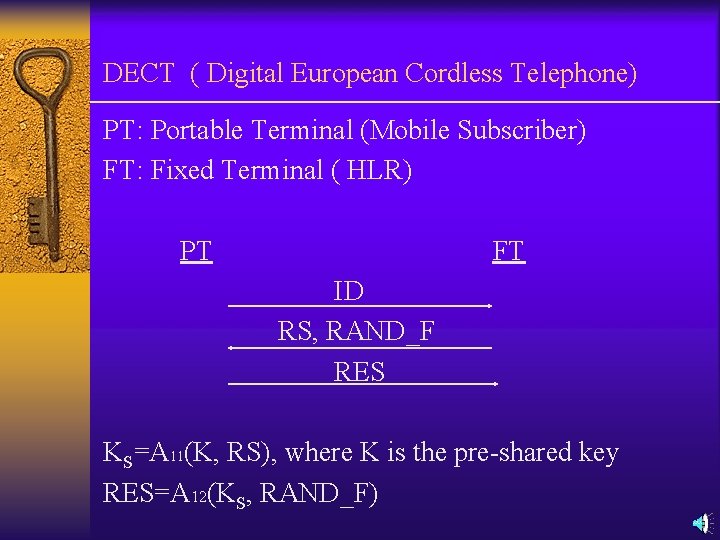
DECT ( Digital European Cordless Telephone) PT: Portable Terminal (Mobile Subscriber) FT: Fixed Terminal ( HLR) PT FT ID RS, RAND_F RES KS=A 11(K, RS), where K is the pre-shared key RES=A 12(KS, RAND_F)
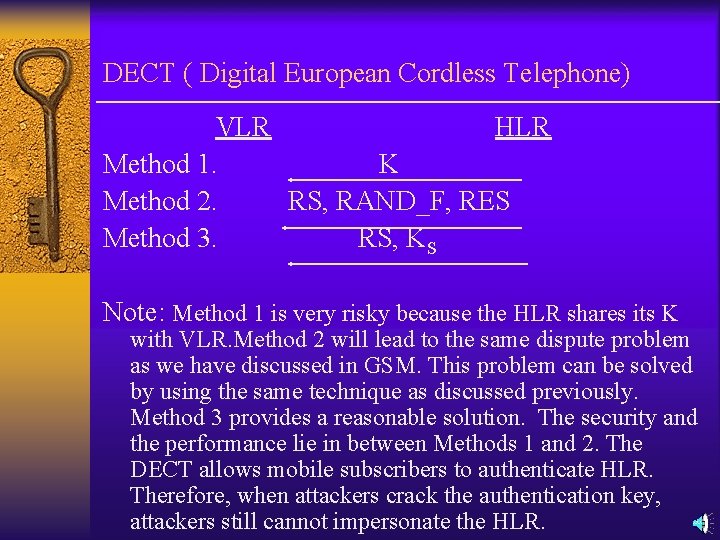
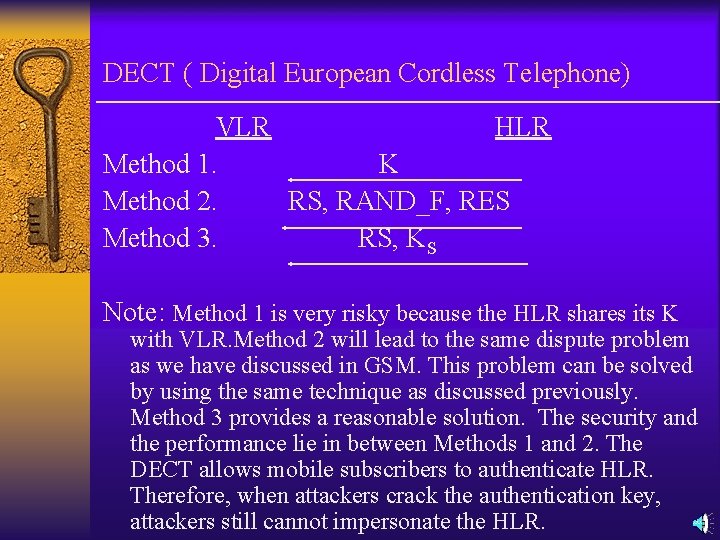
DECT ( Digital European Cordless Telephone) VLR HLR Method 1. K Method 2. RS, RAND_F, RES Method 3. RS, KS Note: Method 1 is very risky because the HLR shares its K with VLR. Method 2 will lead to the same dispute problem as we have discussed in GSM. This problem can be solved by using the same technique as discussed previously. Method 3 provides a reasonable solution. The security and the performance lie in between Methods 1 and 2. The DECT allows mobile subscribers to authenticate HLR. Therefore, when attackers crack the authentication key, attackers still cannot impersonate the HLR.
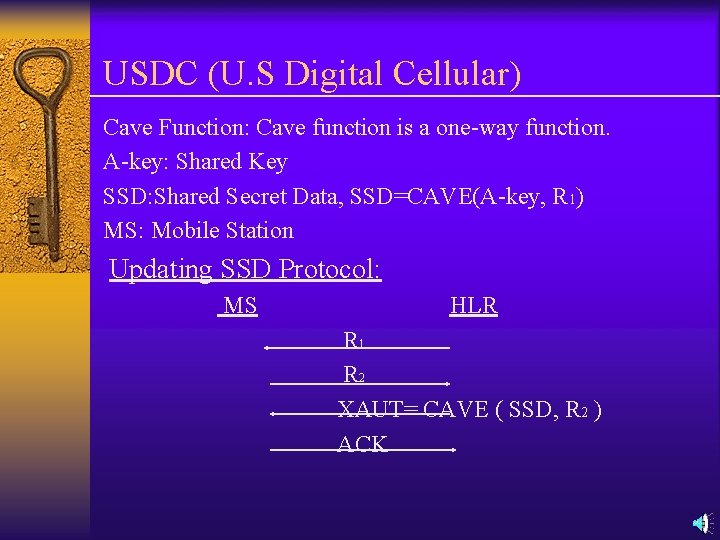
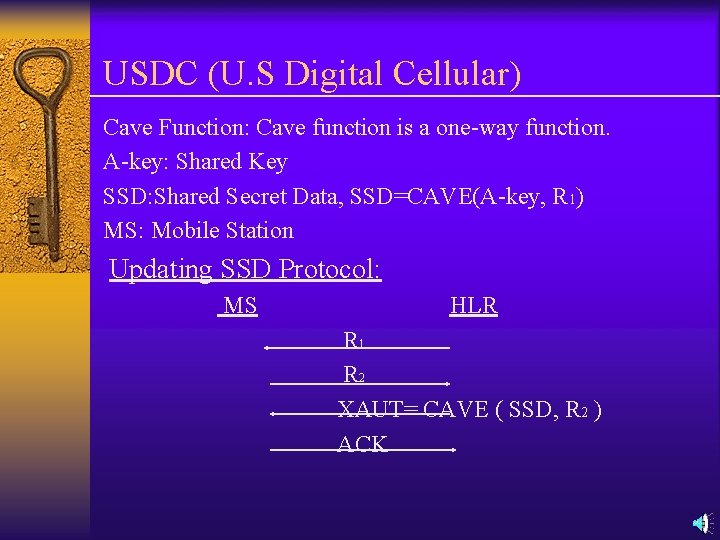
USDC (U. S Digital Cellular) Cave Function: Cave function is a one-way function. A-key: Shared Key SSD: Shared Secret Data, SSD=CAVE(A-key, R 1) MS: Mobile Station Updating SSD Protocol: MS HLR R 1 R 2 XAUT= CAVE ( SSD, R 2 ) ACK
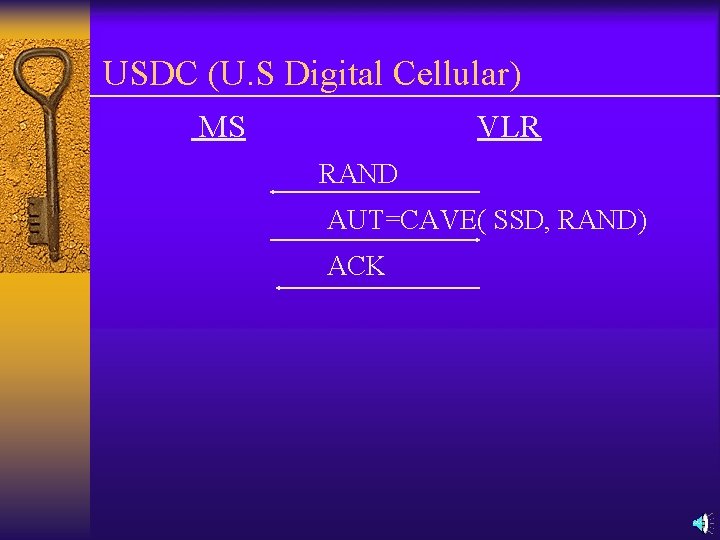
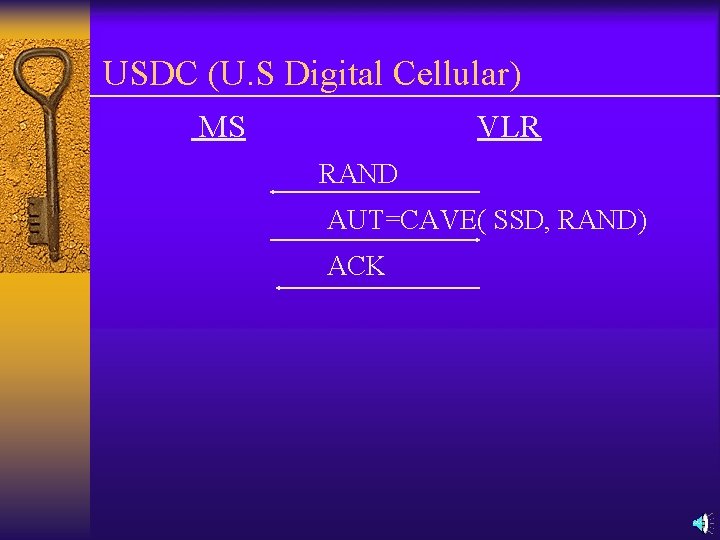
USDC (U. S Digital Cellular) MS VLR RAND AUT=CAVE( SSD, RAND) ACK