Security in Near Field Communication Strengths and Weaknesses

- Slides: 23
Security in Near Field Communication Strengths and Weaknesses Ernst Haselsteiner, Klemens Breitfuss RFIDSec 06 July 13 th, 2006
Contents NFC Intro Eavesdropping Data Modification Man-in-the. Middle Secure Channel • What is NFC? • Threats & Countermeasures – Eavesdropping – Data Modification – Man-in-the-Middle • Secure Channel – Key Agreement Conclusion July 13 th, 2006 2
Contents What is NFC? NFC Intro Eavesdropping Data Modification Man-in-the. Middle Secure Channel • Designed for short distance communication (up to 10 cm) • It’s a contactless card and a contactless reader in one chip • It operates at 13. 56 MHz • It’s designed for low bandwidth (max speed is 424 k. Baud) • Applications aimed for are – Ticketing – Payment – Device Pairing Short Range 13, 56 MHz RF Link Conclusion July 13 th, 2006 3
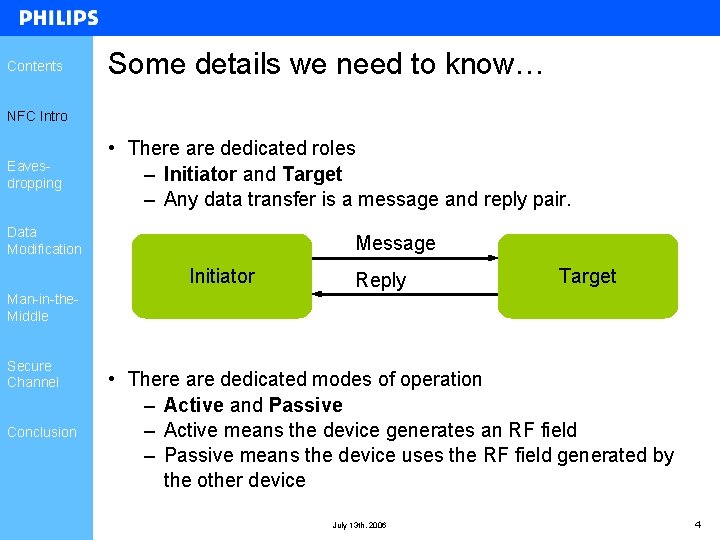
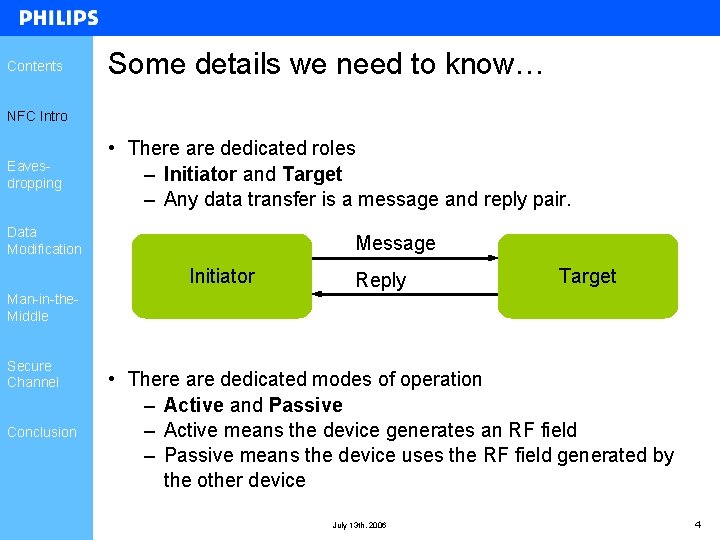
Contents Some details we need to know… NFC Intro Eavesdropping • There are dedicated roles – Initiator and Target – Any data transfer is a message and reply pair. Data Modification Message Initiator Reply Target Man-in-the. Middle Secure Channel Conclusion • There are dedicated modes of operation – Active and Passive – Active means the device generates an RF field – Passive means the device uses the RF field generated by the other device July 13 th, 2006 4
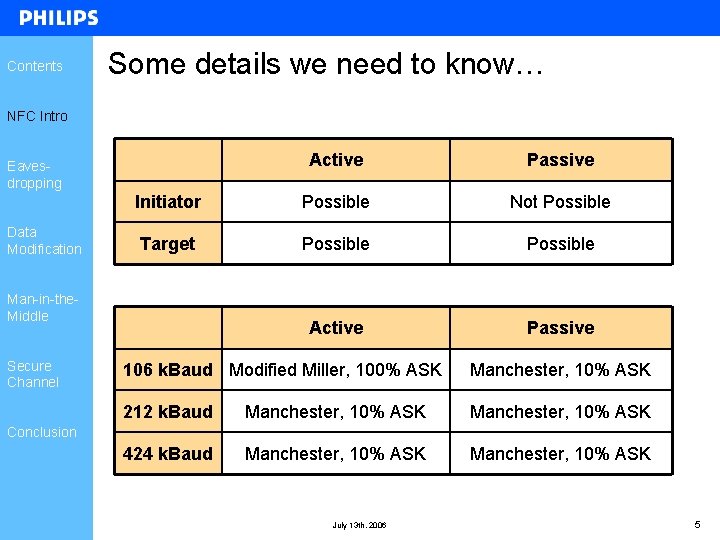
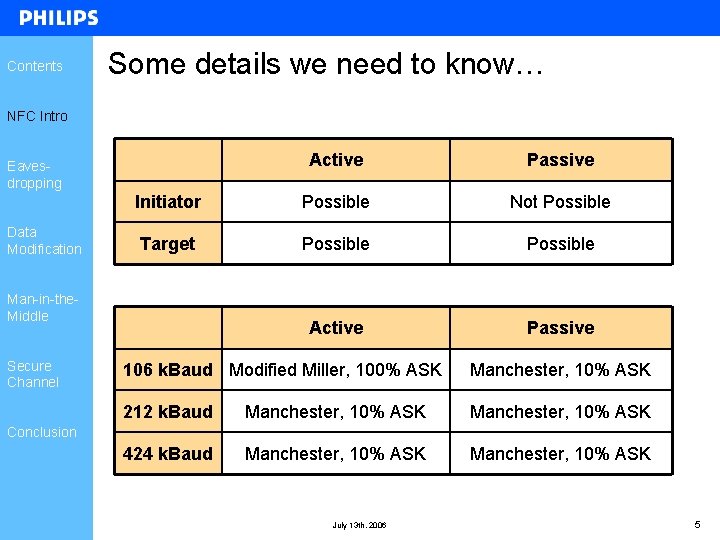
Contents Some details we need to know… NFC Intro Active Passive Initiator Possible Not Possible Target Possible Active Passive Eavesdropping Data Modification Man-in-the. Middle Secure Channel 106 k. Baud Modified Miller, 100% ASK Manchester, 10% ASK 212 k. Baud Manchester, 10% ASK 424 k. Baud Manchester, 10% ASK Conclusion July 13 th, 2006 5
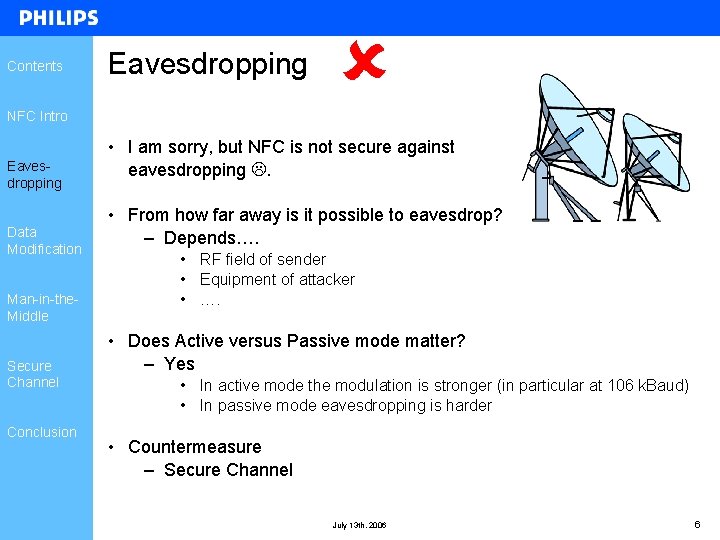
Contents Eavesdropping NFC Intro Eavesdropping Data Modification Man-in-the. Middle Secure Channel Conclusion • I am sorry, but NFC is not secure against eavesdropping . • From how far away is it possible to eavesdrop? – Depends…. • RF field of sender • Equipment of attacker • …. • Does Active versus Passive mode matter? – Yes • In active mode the modulation is stronger (in particular at 106 k. Baud) • In passive mode eavesdropping is harder • Countermeasure – Secure Channel July 13 th, 2006 6
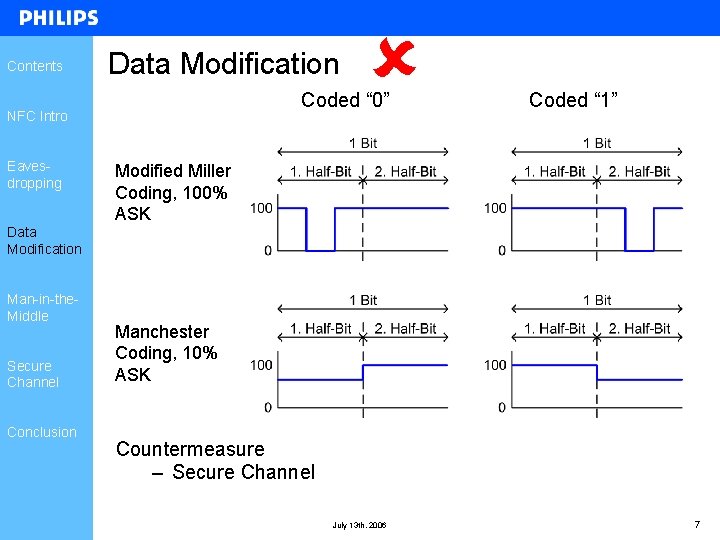
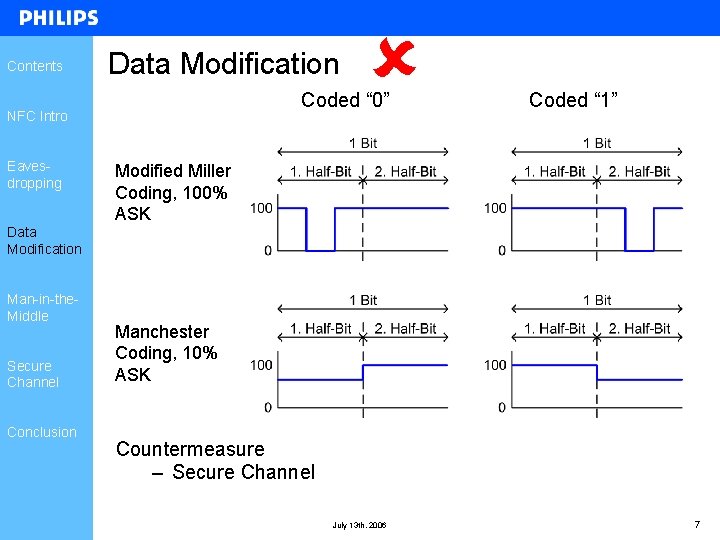
Contents Data Modification Coded “ 0” NFC Intro Eavesdropping Coded “ 1” Modified Miller Coding, 100% ASK Data Modification Man-in-the. Middle Secure Channel Conclusion Manchester Coding, 10% ASK Countermeasure – Secure Channel July 13 th, 2006 7
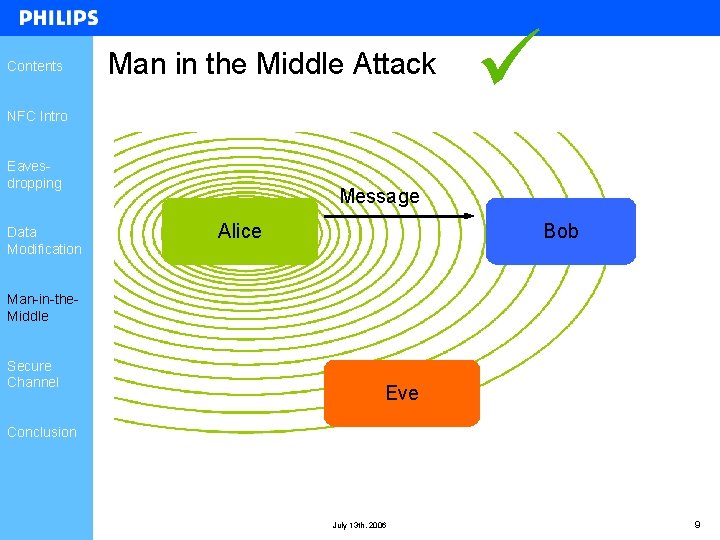
Contents Man in the Middle Attack NFC Intro Eavesdropping Data Modification Alice Bob Man-in-the. Middle Secure Channel Eve Conclusion July 13 th, 2006 8
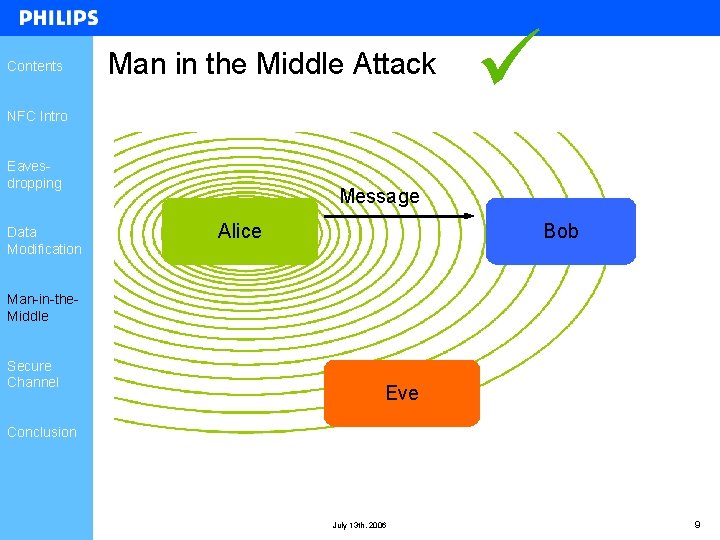
Contents Man in the Middle Attack NFC Intro Eavesdropping Data Modification Message Alice Bob Man-in-the. Middle Secure Channel Eve Conclusion July 13 th, 2006 9
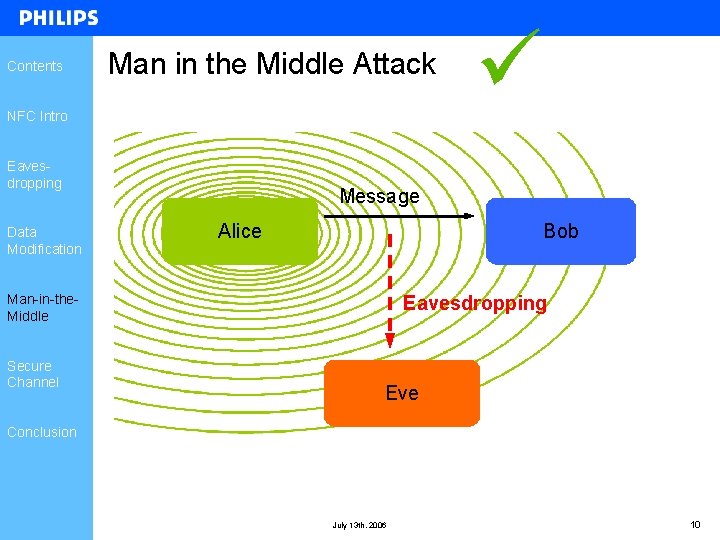
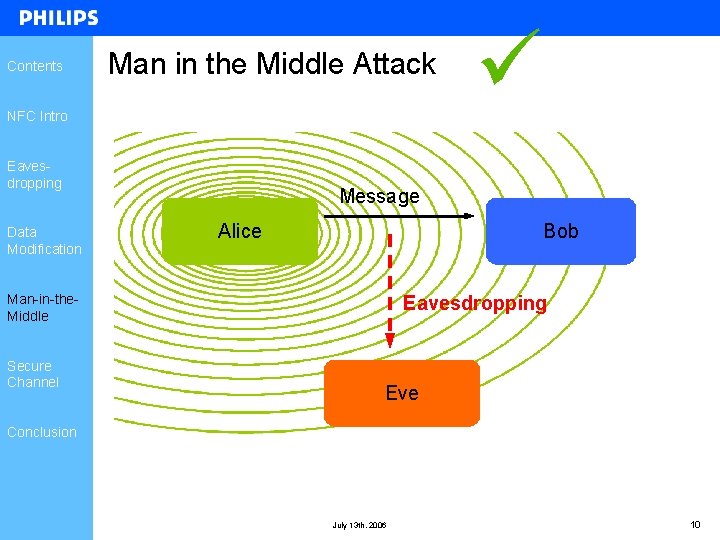
Contents Man in the Middle Attack NFC Intro Eavesdropping Data Modification Message Alice Bob Man-in-the. Middle Secure Channel Eavesdropping Eve Conclusion July 13 th, 2006 10
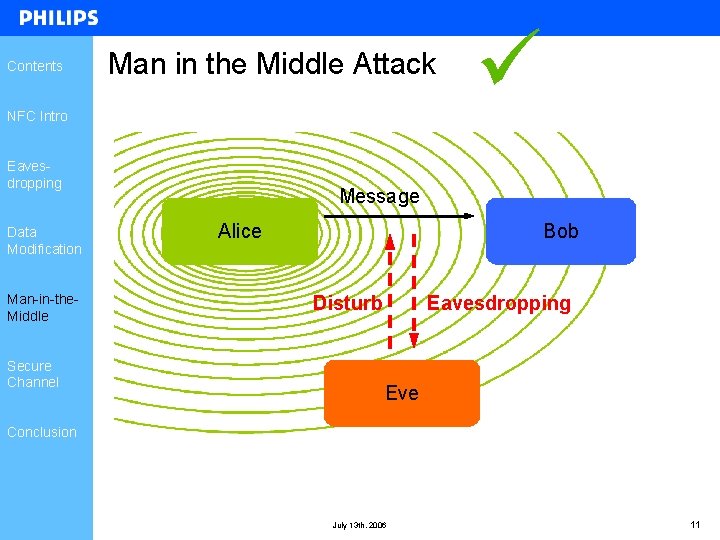
Contents Man in the Middle Attack NFC Intro Eavesdropping Data Modification Man-in-the. Middle Secure Channel Message Alice Bob Eavesdropping Disturb Eve Conclusion July 13 th, 2006 11
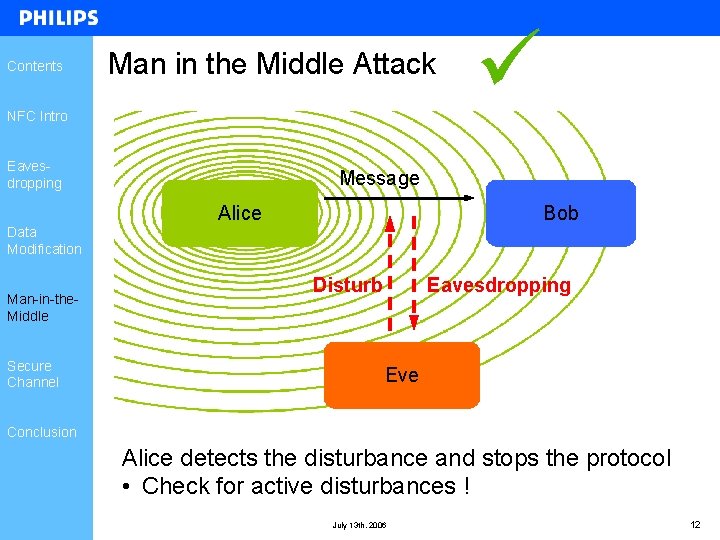
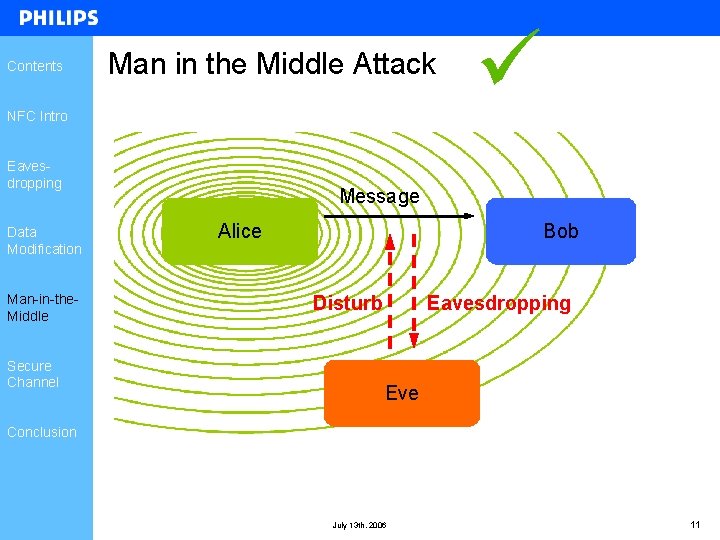
Contents Man in the Middle Attack NFC Intro Eavesdropping Message Alice Bob Data Modification Man-in-the. Middle Secure Channel Eavesdropping Disturb Eve Conclusion Alice detects the disturbance and stops the protocol • Check for active disturbances ! July 13 th, 2006 12
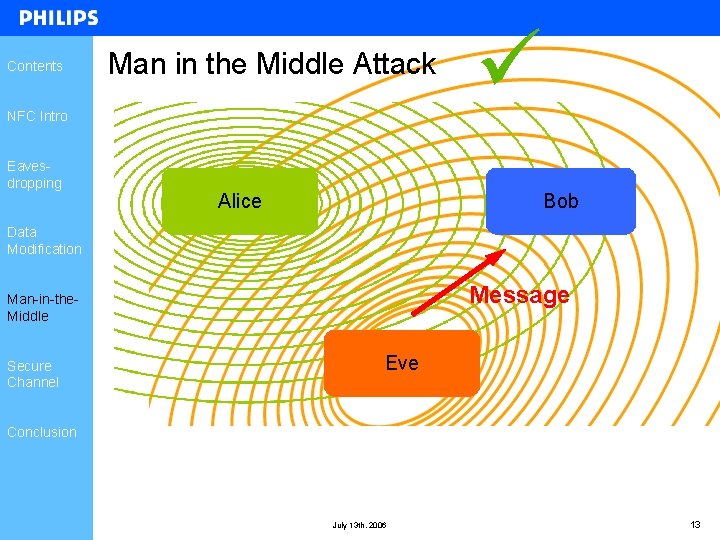
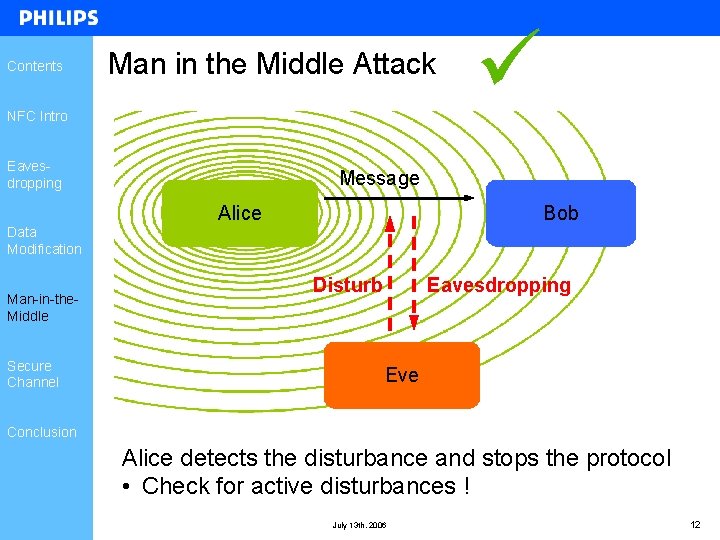
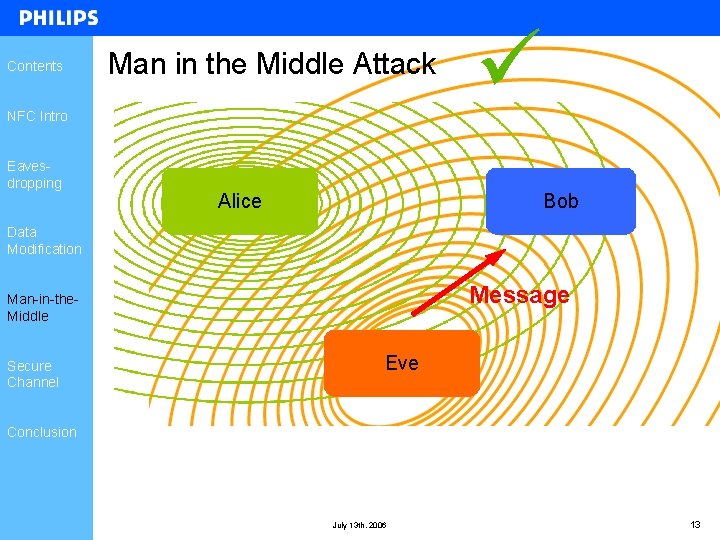
Contents Man in the Middle Attack NFC Intro Eavesdropping Alice Bob Data Modification Message Man-in-the. Middle Secure Channel Eve Conclusion July 13 th, 2006 13
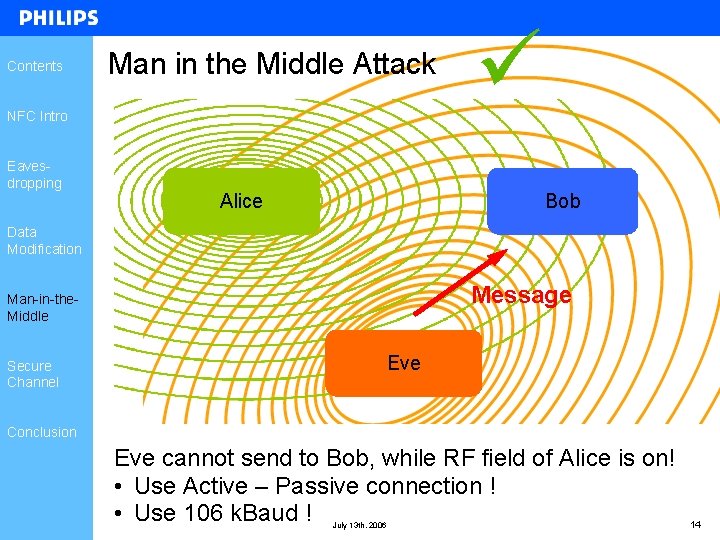
Contents Man in the Middle Attack NFC Intro Eavesdropping Alice Bob Data Modification Message Man-in-the. Middle Secure Channel Eve Conclusion Eve cannot send to Bob, while RF field of Alice is on! • Use Active – Passive connection ! • Use 106 k. Baud ! July 13 th, 2006 14
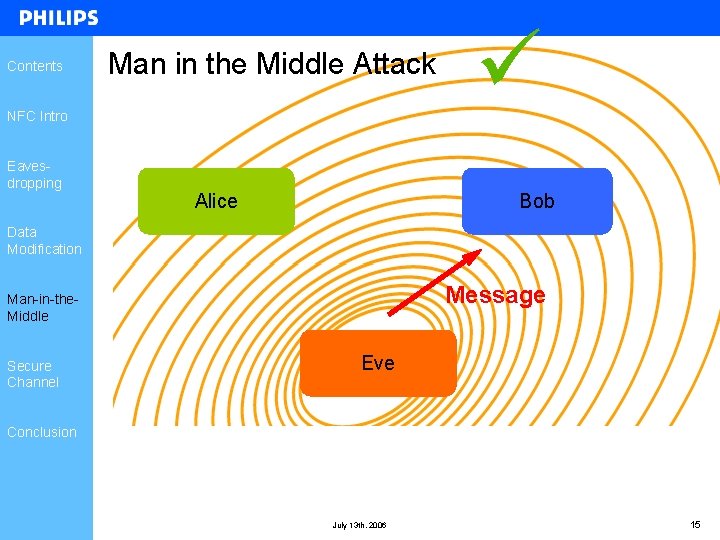
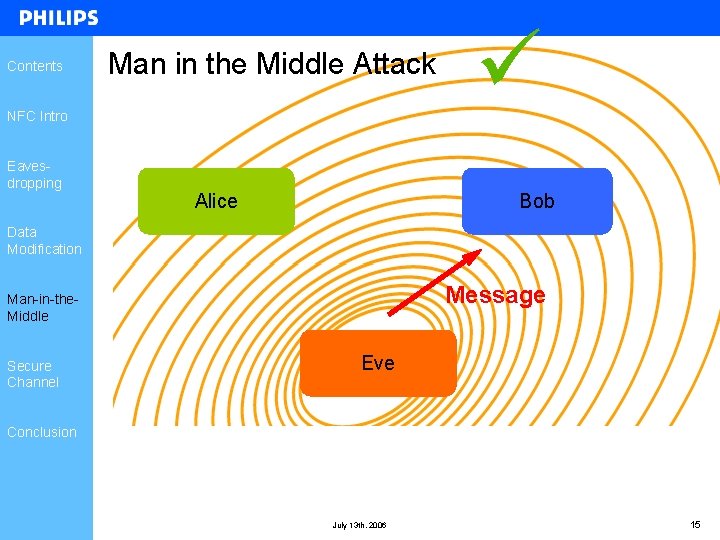
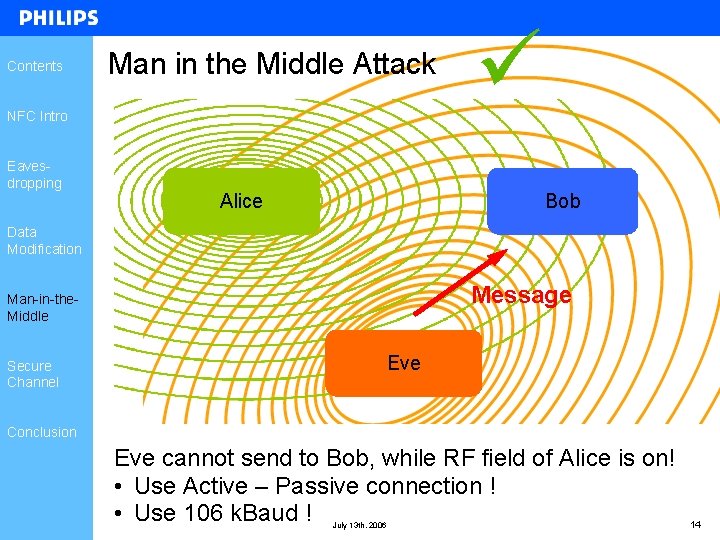
Contents Man in the Middle Attack NFC Intro Eavesdropping Alice Bob Data Modification Message Man-in-the. Middle Secure Channel Eve Conclusion July 13 th, 2006 15
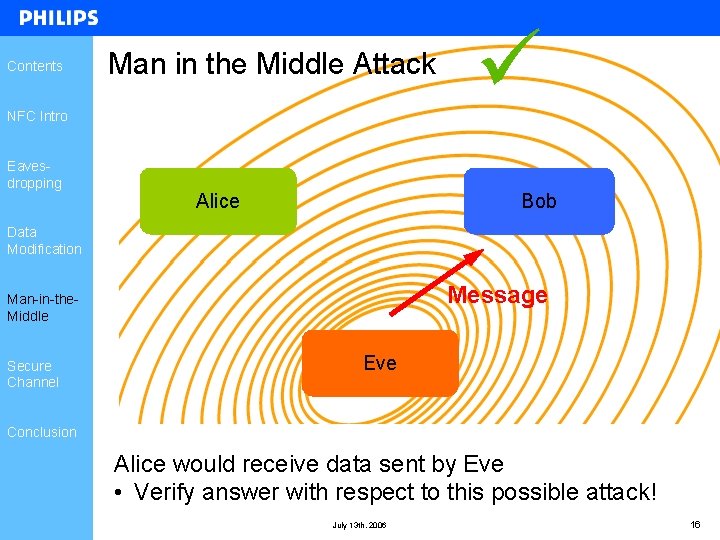
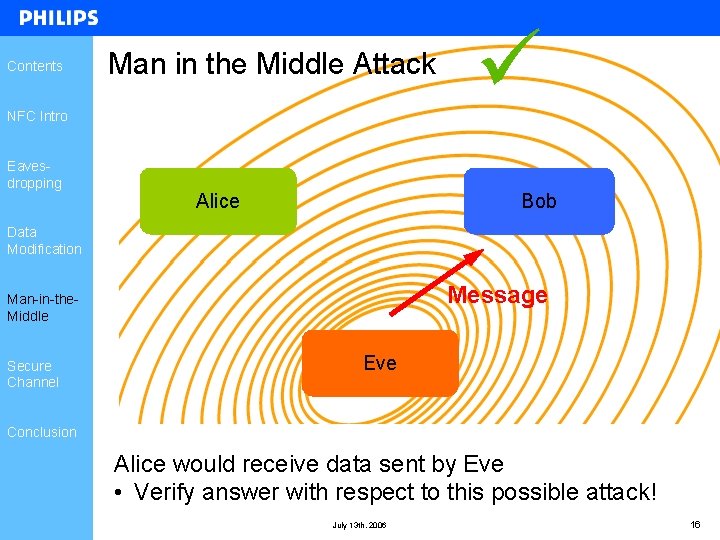
Contents Man in the Middle Attack NFC Intro Eavesdropping Alice Bob Data Modification Message Man-in-the. Middle Secure Channel Eve Conclusion Alice would receive data sent by Eve • Verify answer with respect to this possible attack! July 13 th, 2006 16
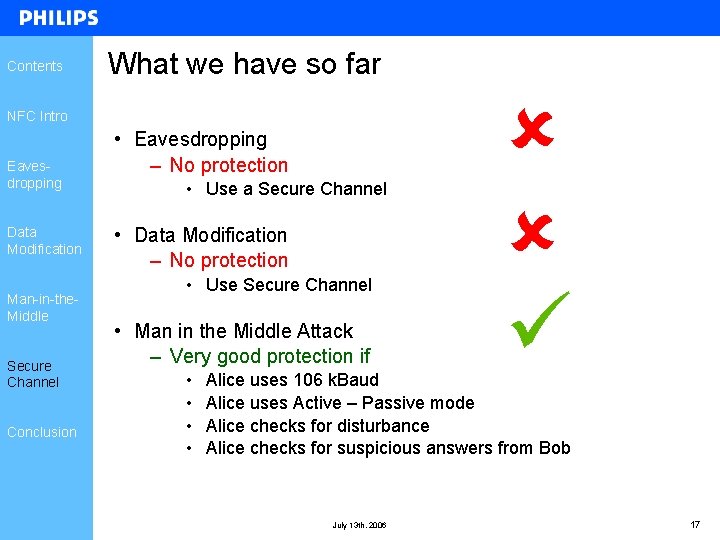
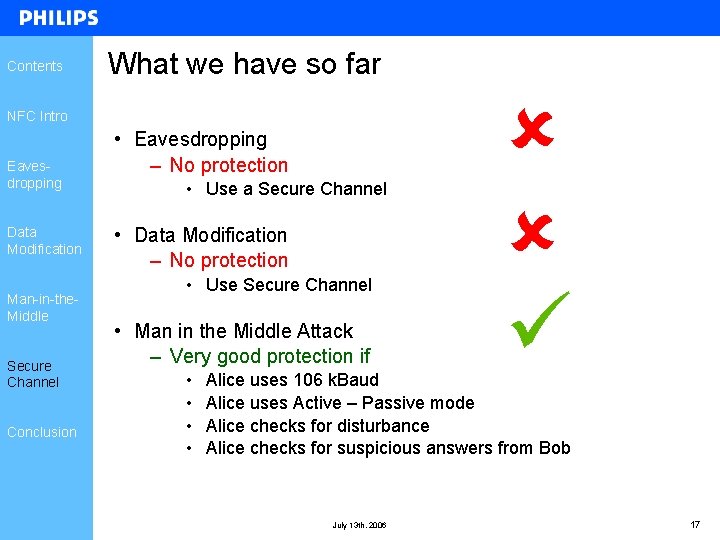
Contents What we have so far NFC Intro Eavesdropping Data Modification Man-in-the. Middle Secure Channel Conclusion • Eavesdropping – No protection • Use a Secure Channel • Data Modification – No protection • Use Secure Channel • Man in the Middle Attack – Very good protection if • • Alice uses 106 k. Baud Alice uses Active – Passive mode Alice checks for disturbance Alice checks for suspicious answers from Bob July 13 th, 2006 17
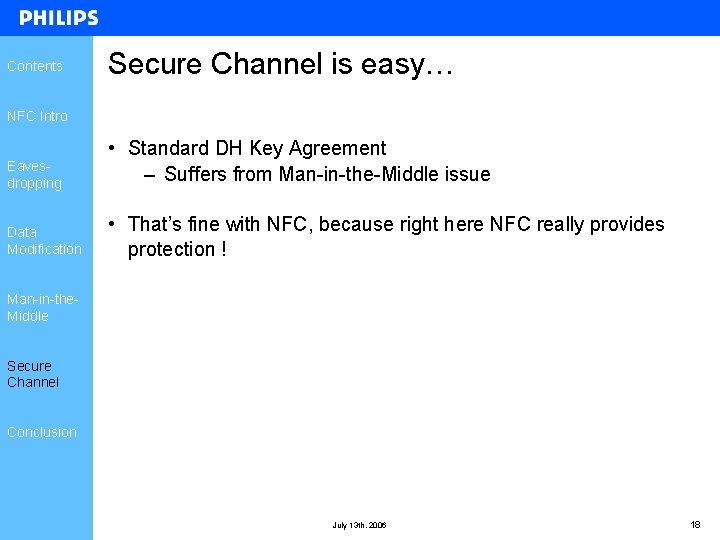
Contents Secure Channel is easy… NFC Intro Eavesdropping • Standard DH Key Agreement – Suffers from Man-in-the-Middle issue Data Modification • That’s fine with NFC, because right here NFC really provides protection ! Man-in-the. Middle Secure Channel Conclusion July 13 th, 2006 18
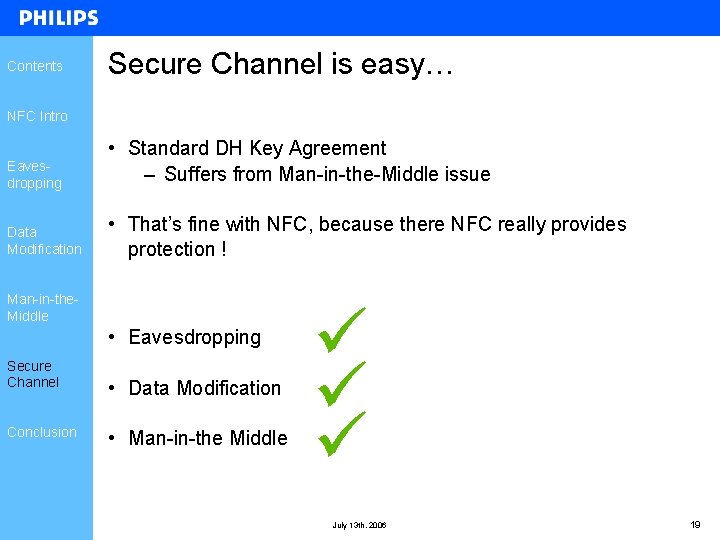
Contents Secure Channel is easy… NFC Intro Eavesdropping • Standard DH Key Agreement – Suffers from Man-in-the-Middle issue Data Modification • That’s fine with NFC, because there NFC really provides protection ! Man-in-the. Middle • Eavesdropping Secure Channel Conclusion • Data Modification • Man-in-the Middle July 13 th, 2006 19
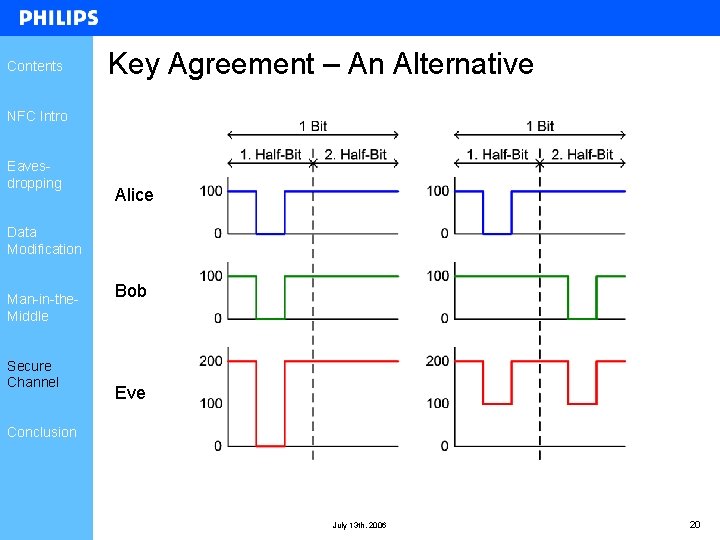
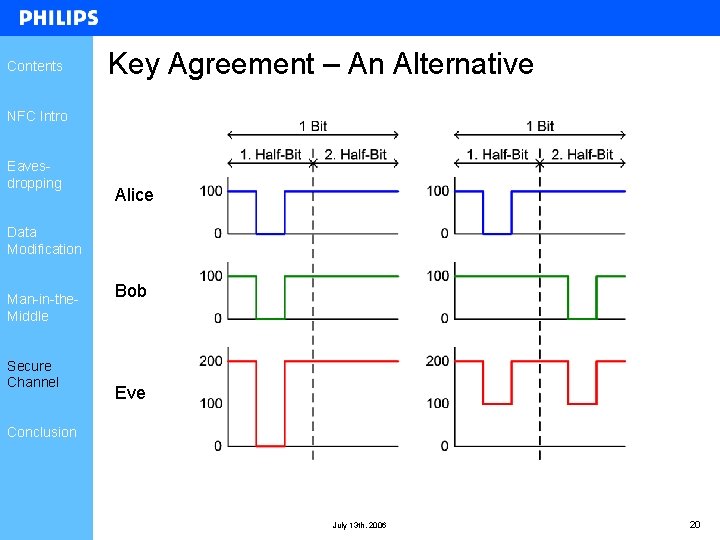
Contents Key Agreement – An Alternative NFC Intro Eavesdropping Alice Data Modification Man-in-the. Middle Secure Channel Bob Eve Conclusion July 13 th, 2006 20
Contents Key Agreement – An Alternative NFC Intro Eavesdropping Data Modification • Perfect in theory – Obvious to see • Needs perfect synchronization between Alice and Bob – Amplitude – Phase • Alice and Bob must actively perform this synchronization Man-in-the. Middle • Security in practice depends on – Synchronization Secure Channel Conclusion – Equipment of attacker • Advantages – Cheap (requires no cryptography) – Extremely fast July 13 th, 2006 21
Contents Conclusion NFC Intro Eavesdropping Data Modification Man-in-the. Middle • NFC does not provide any security by itself • Secure Channel is required • Physical properties of NFC protect against Man-in-the-Middle • Establishing a Secure Channel becomes easy Secure Channel Conclusion July 13 th, 2006 22
