Security Fabric Salon Med IT 2017 Copyright Fortinet

Security Fabric Salon Med. IT 2017 © Copyright Fortinet Inc. All rights reserved.
Agenda § Three Security Challenges Driving Security Fabric Vision Today § How This Vision is Being Realized § Recap & Discussion 2
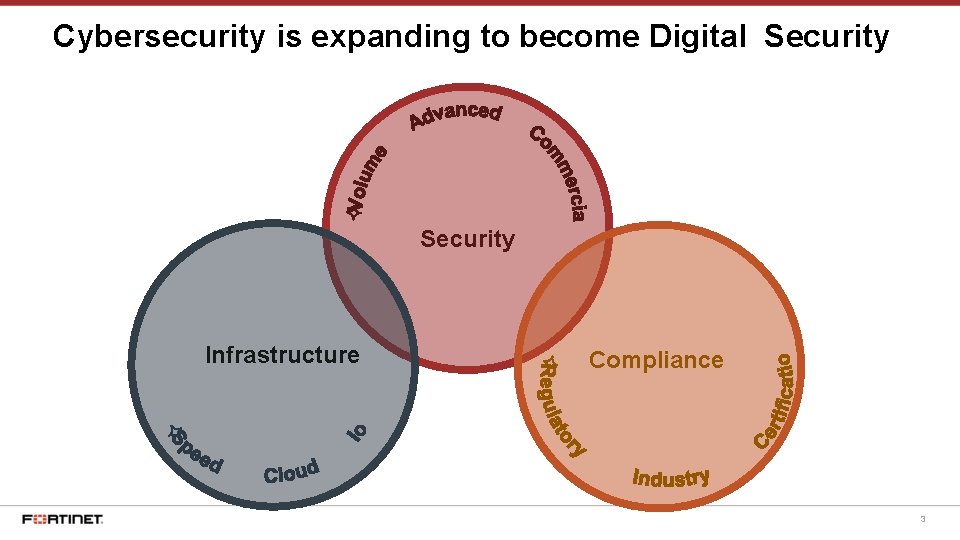
Cybersecurity is expanding to become Digital Security Infrastructure Compliance 3
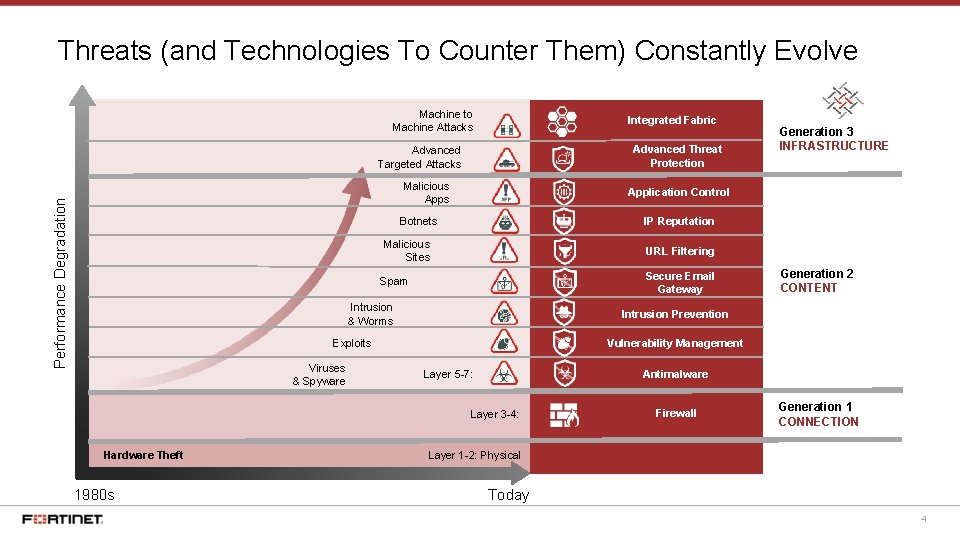
Threats (and Technologies To Counter Them) Constantly Evolve Machine to Machine Attacks Integrated Fabric Advanced Threat Protection Advanced Targeted Attacks Performance Degradation Malicious Application Control IP Reputation Botnets Malicious Sites URL Filtering Secure Email Gateway Spam Intrusion & Worms Vulnerability Management Antimalware Layer 5 -7: Layer 3 -4: Hardware Theft 1980 s Generation 2 CONTENT Intrusion Prevention Exploits Viruses & Spyware Generation 3 INFRASTRUCTURE Firewall Generation 1 CONNECTION Layer 1 -2: Physical Today 4
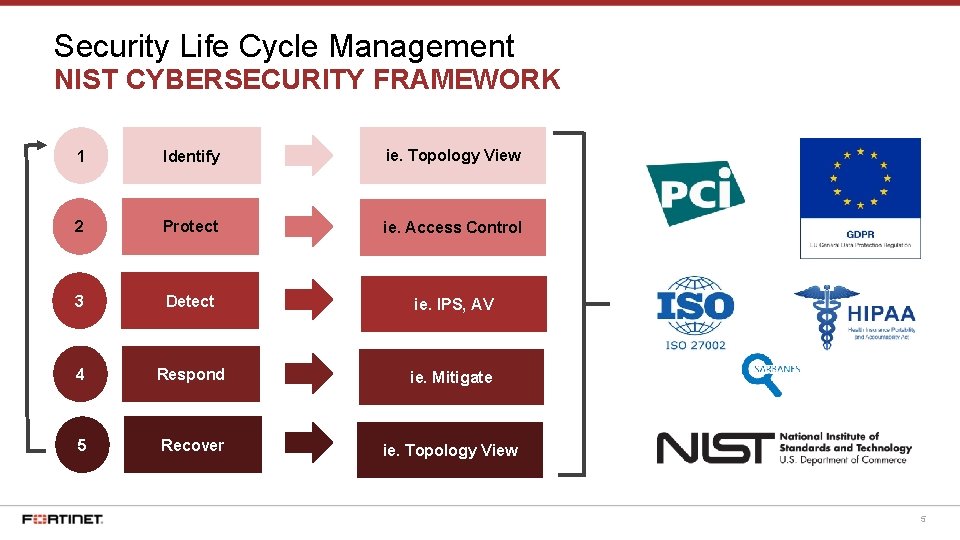
Security Life Cycle Management NIST CYBERSECURITY FRAMEWORK 1 Identify ie. Topology View 2 Protect ie. Access Control 3 Detect ie. IPS, AV 4 Respond ie. Mitigate 5 Recover ie. Topology View 5
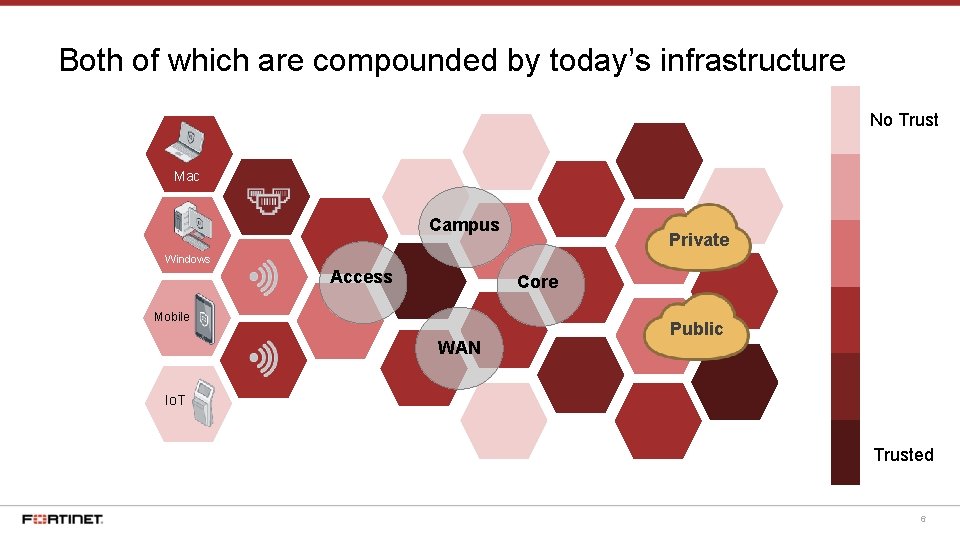
Both of which are compounded by today’s infrastructure No Trust Mac Campus Private Windows Access Core Mobile WAN Public Io. T Trusted 6
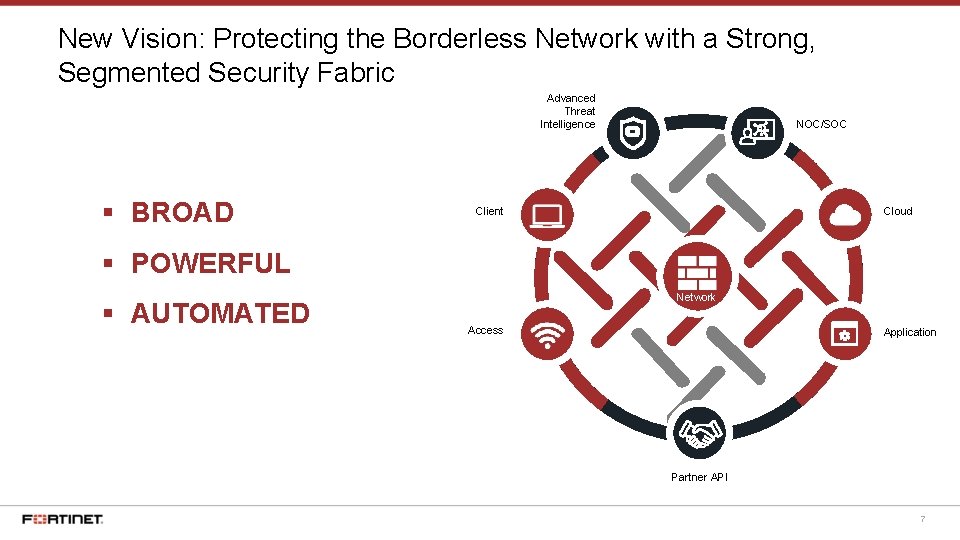
New Vision: Protecting the Borderless Network with a Strong, Segmented Security Fabric Advanced Threat Intelligence § BROAD NOC/SOC Cloud Client § POWERFUL § AUTOMATED Network Access Application Partner API 7
BR BROAD Deeper visibility and control throughout the Security Fabric to reduce the attack surface from Io. T to Cloud OA D
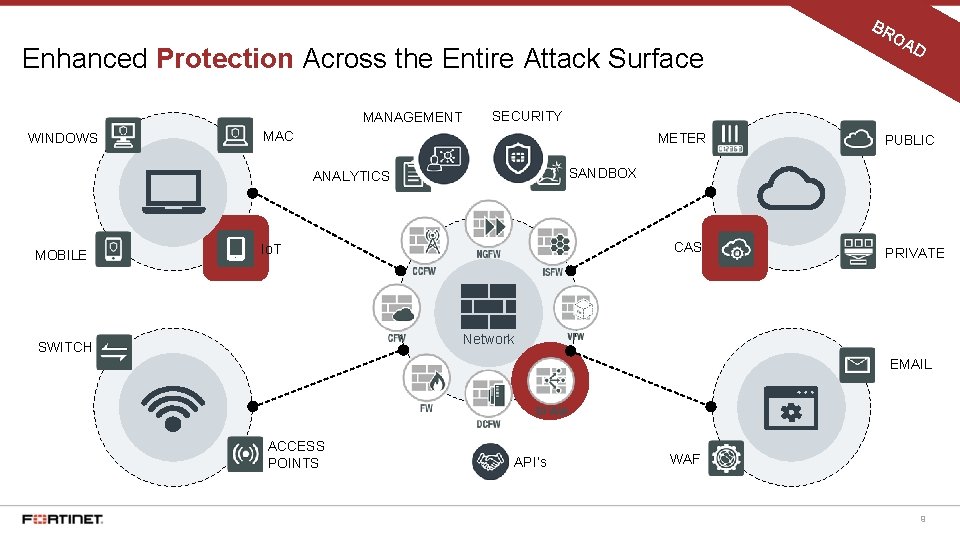
BR Enhanced Protection Across the Entire Attack Surface MANAGEMENT WINDOWS D SECURITY MAC METER PUBLIC SANDBOX ANALYTICS MOBILE OA CASB Io. T PRIVATE Network SWITCH EMAIL ACCESS POINTS API’s WAF 9
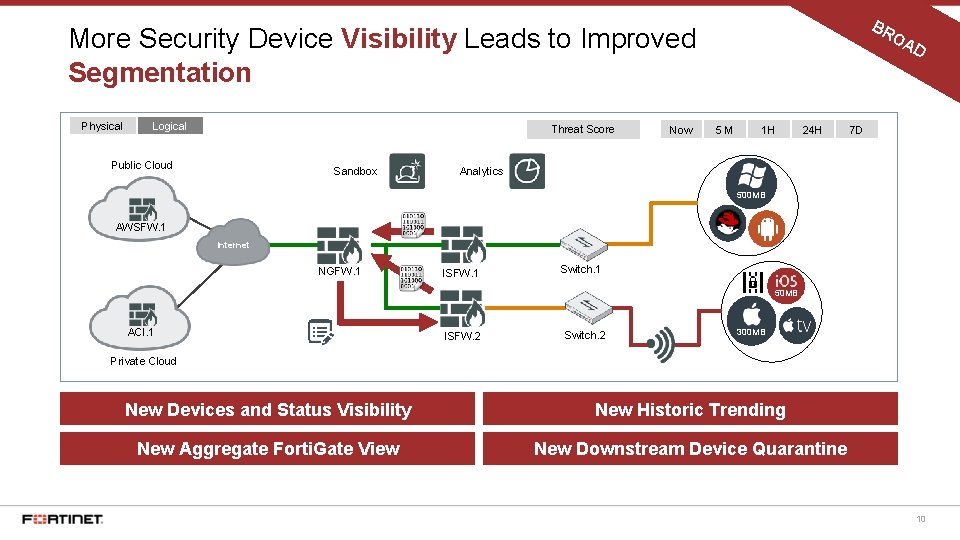
BR More Security Device Visibility Leads to Improved Segmentation Physical Logical Threat Score Public Cloud Sandbox Now 5 M 1 H 24 H OA D 7 D Analytics 500 MB AWSFW. 1 Internet NGFW. 1 ISFW. 1 Switch. 1 50 MB ACI. 1 ISFW. 2 Switch. 2 300 MB Private Cloud New Devices and Status Visibility New Historic Trending New Aggregate Forti. Gate View New Downstream Device Quarantine 10
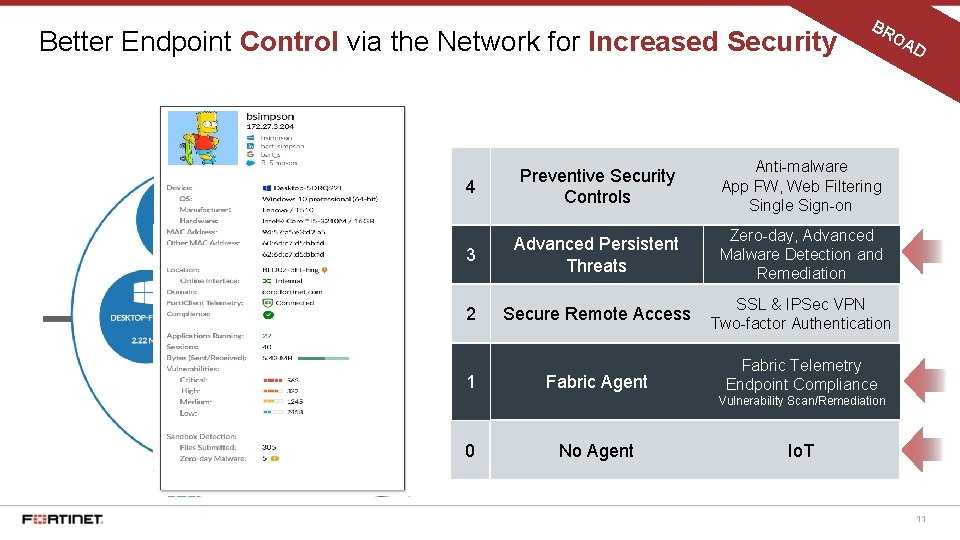
Better Endpoint Control via the Network for Increased Security BR OA 4 Preventive Security Controls Anti-malware App FW, Web Filtering Single Sign-on 3 Advanced Persistent Threats Zero-day, Advanced Malware Detection and Remediation 2 Secure Remote Access SSL & IPSec VPN Two-factor Authentication Fabric Agent Fabric Telemetry Endpoint Compliance 1 D Vulnerability Scan/Remediation 0 No Agent Io. T 11
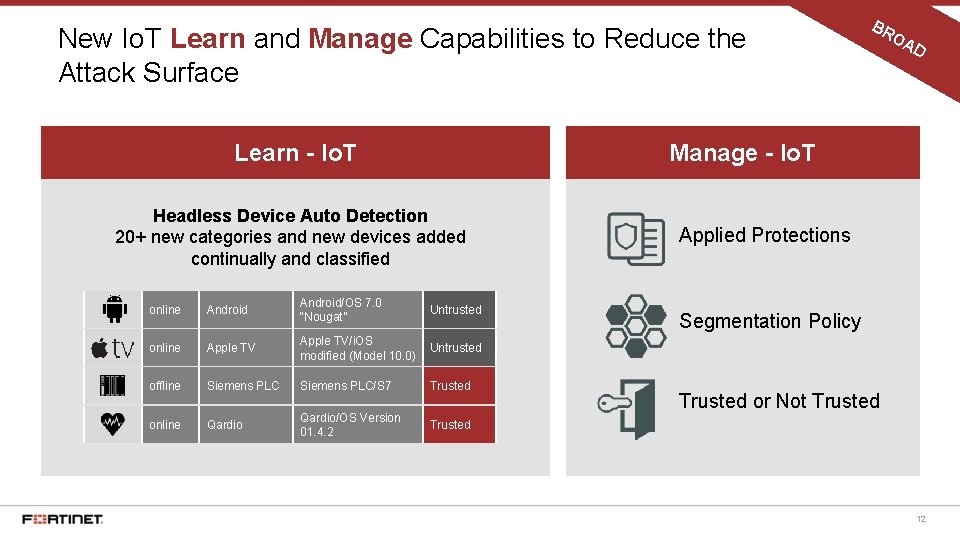
New Io. T Learn and Manage Capabilities to Reduce the Attack Surface Learn - Io. T BR OA D Manage - Io. T Headless Device Auto Detection 20+ new categories and new devices added continually and classified online Android/OS 7. 0 “Nougat” Untrusted online Apple TV/i. OS modified (Model 10. 0) Untrusted offline Siemens PLC/S 7 Trusted online Qardio/OS Version 01. 4. 2 Trusted Applied Protections Segmentation Policy Trusted or Not Trusted 12
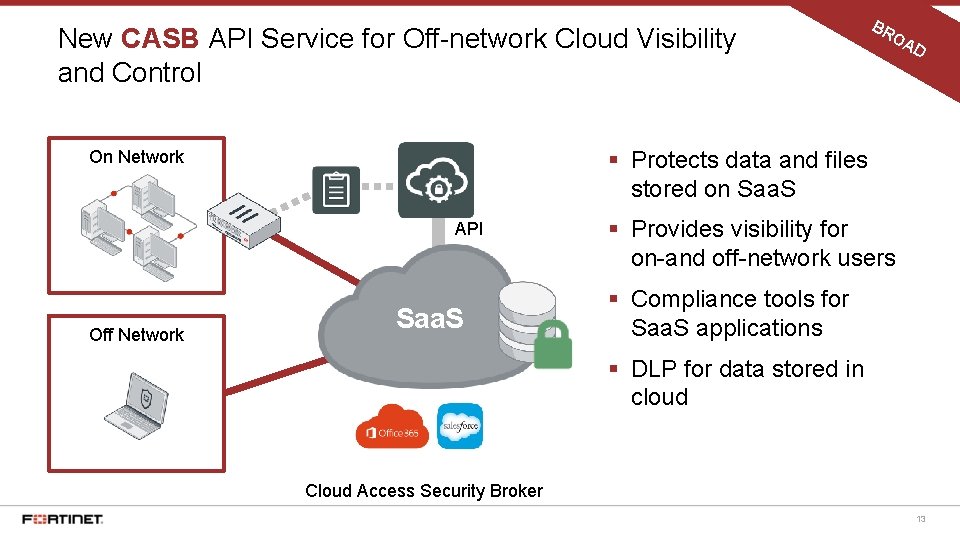
New CASB API Service for Off-network Cloud Visibility and Control OA D § Protects data and files stored on Saa. S On Network API Off Network BR Saa. S § Provides visibility for on-and off-network users § Compliance tools for Saa. S applications § DLP for data stored in cloud Cloud Access Security Broker 13
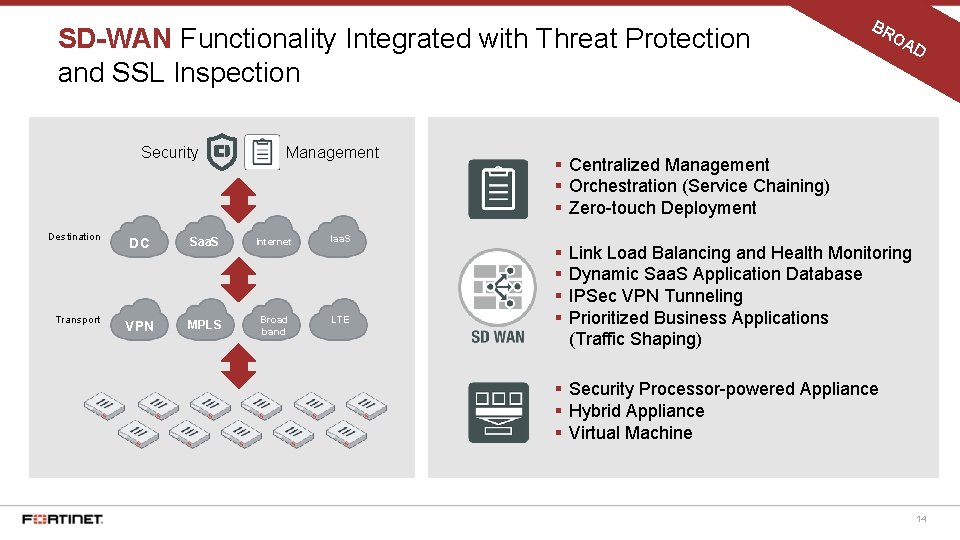
SD-WAN Functionality Integrated with Threat Protection and SSL Inspection Security Destination Transport Management DC Saa. S Internet Iaa. S VPN MPLS Broad band LTE BR OA D § Centralized Management § Orchestration (Service Chaining) § Zero-touch Deployment § § Link Load Balancing and Health Monitoring Dynamic Saa. S Application Database IPSec VPN Tunneling Prioritized Business Applications (Traffic Shaping) § Security Processor-powered Appliance § Hybrid Appliance § Virtual Machine 14
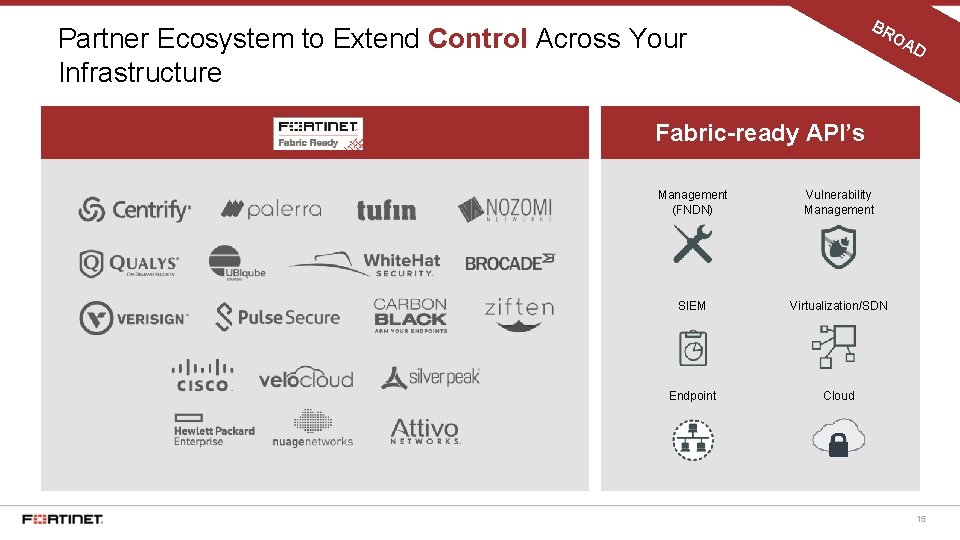
BR Partner Ecosystem to Extend Control Across Your Infrastructure OA D Fabric-ready API’s Management (FNDN) Vulnerability Management SIEM Virtualization/SDN Endpoint Cloud 15

PO WE RF POWERFUL Accelerated cloud-scale and security processor-based appliances with coordinated logging to enable maximum threat protection without affecting performance UL
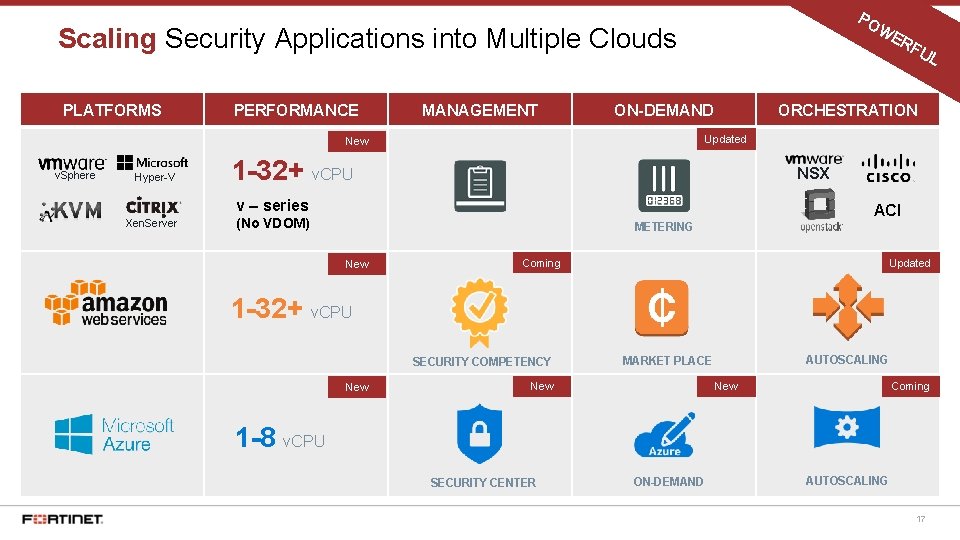
PO WE Scaling Security Applications into Multiple Clouds PLATFORMS PERFORMANCE MANAGEMENT ON-DEMAND Hyper-V ORCHESTRATION 1 -32+ v. CPU NSX v – series Xen. Server UL Updated New v. Sphere RF ACI (No VDOM) METERING New Coming Updated 1 -32+ v. CPU SECURITY COMPETENCY New AUTOSCALING MARKET PLACE New Coming 1 -8 v. CPU SECURITY CENTER ON-DEMAND AUTOSCALING 17
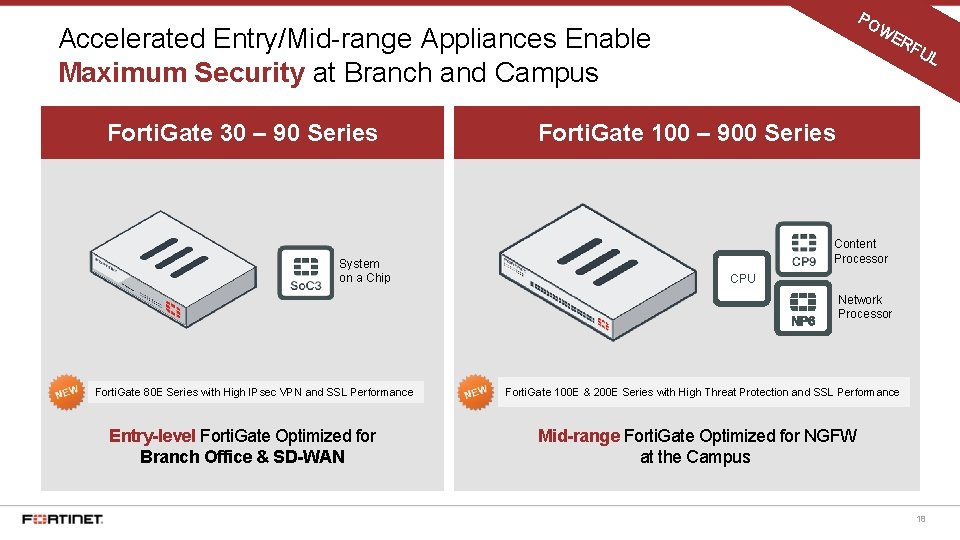
PO WE Accelerated Entry/Mid-range Appliances Enable Maximum Security at Branch and Campus Forti. Gate 30 – 90 Series System on a Chip RF UL Forti. Gate 100 – 900 Series Content Processor CPU Network Processor Forti. Gate 80 E Series with High IPsec VPN and SSL Performance Entry-level Forti. Gate Optimized for Branch Office & SD-WAN Forti. Gate 100 E & 200 E Series with High Threat Protection and SSL Performance Mid-range Forti. Gate Optimized for NGFW at the Campus 18
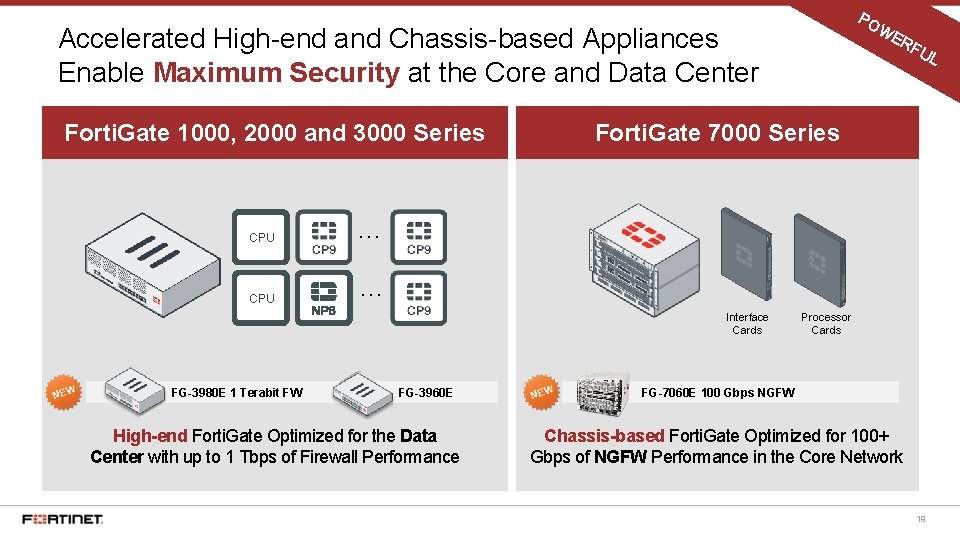
PO WE Accelerated High-end and Chassis-based Appliances Enable Maximum Security at the Core and Data Center Forti. Gate 1000, 2000 and 3000 Series CPU … FG-3960 E High-end Forti. Gate Optimized for the Data Center with up to 1 Tbps of Firewall Performance UL Forti. Gate 7000 Series Interface Cards FG-3980 E 1 Terabit FW RF Processor Cards FG-7060 E 100 Gbps NGFW Chassis-based Forti. Gate Optimized for 100+ Gbps of NGFW Performance in the Core Network 19
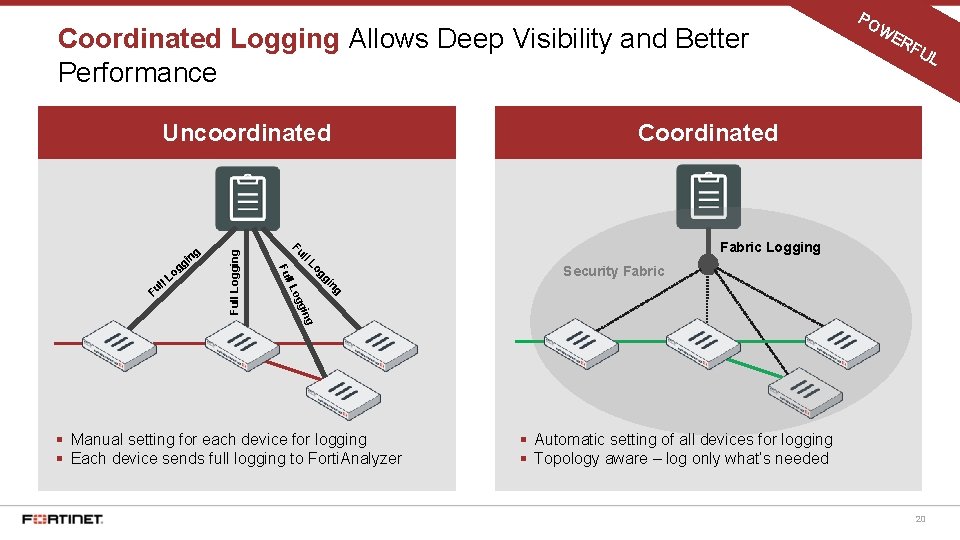
Coordinated Logging Allows Deep Visibility and Better Performance WE RF UL Coordinated Fabric Logging Security Fabric g in ing g og ll L gg Lo ll Fu F l ul Fu Lo g in g g Full Logging Uncoordinated PO § Manual setting for each device for logging § Each device sends full logging to Forti. Analyzer § Automatic setting of all devices for logging § Topology aware – log only what’s needed 20

AU TO MA TE AUTOMATED More efficient operations with new Security Fabric audit/recommendations, intelligence sharing, and NOC views D
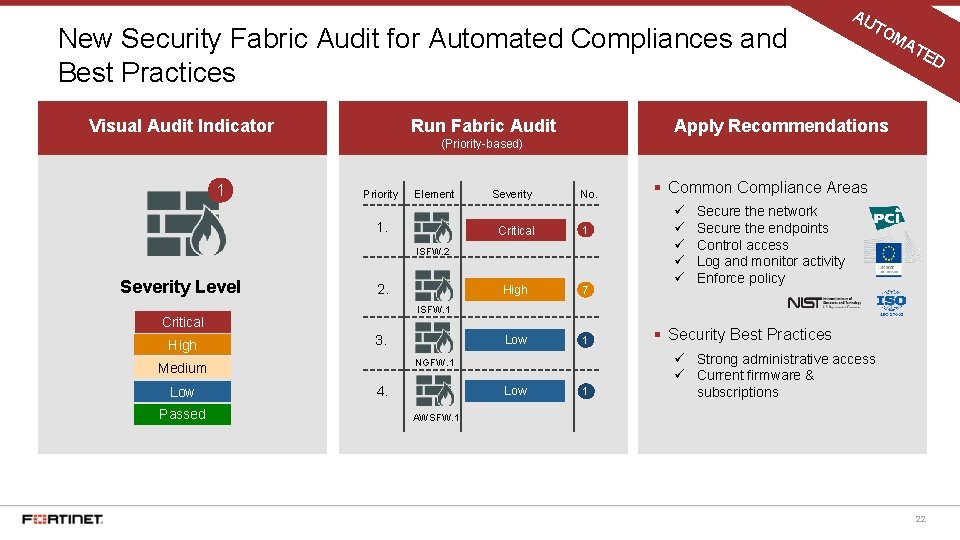
New Security Fabric Audit for Automated Compliances and Best Practices Visual Audit Indicator Run Fabric Audit AU TO MA TE D Apply Recommendations (Priority-based) 1 Priority Element 1. Severity No. Critical 1 High 7 Low 1 ISFW. 2 Severity Level 2. 3. NGFW. 1 Medium Low Passed ü ü ü Secure the network Secure the endpoints Control access Log and monitor activity Enforce policy ISFW. 1 Critical High § Common Compliance Areas 4. Low 1 § Security Best Practices ü Strong administrative access ü Current firmware & subscriptions AWSFW. 1 22
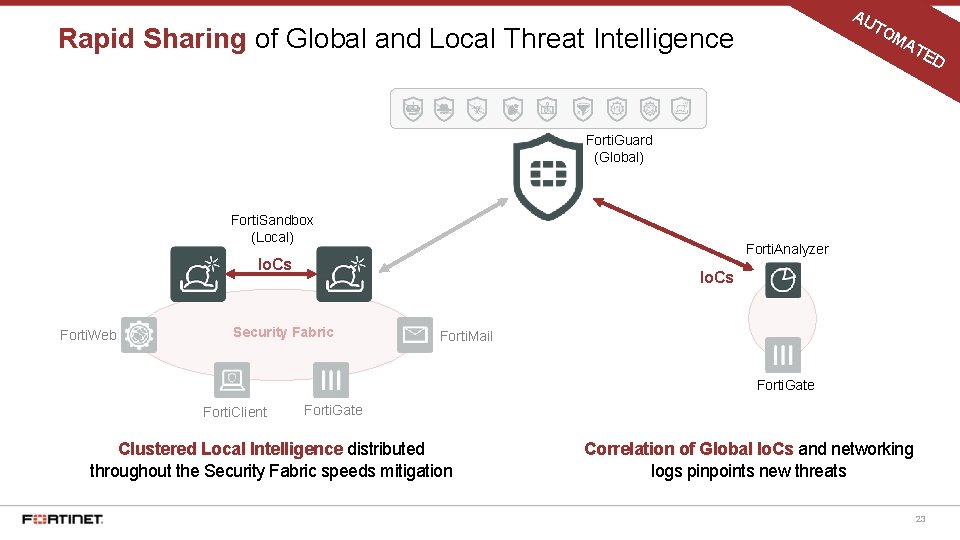
AU TO Rapid Sharing of Global and Local Threat Intelligence MA TE D Forti. Guard (Global) Forti. Sandbox (Local) Forti. Analyzer Io. Cs Forti. Web Io. Cs Security Fabric Forti. Mail Forti. Gate Forti. Client Forti. Gate Clustered Local Intelligence distributed throughout the Security Fabric speeds mitigation Correlation of Global Io. Cs and networking logs pinpoints new threats 23
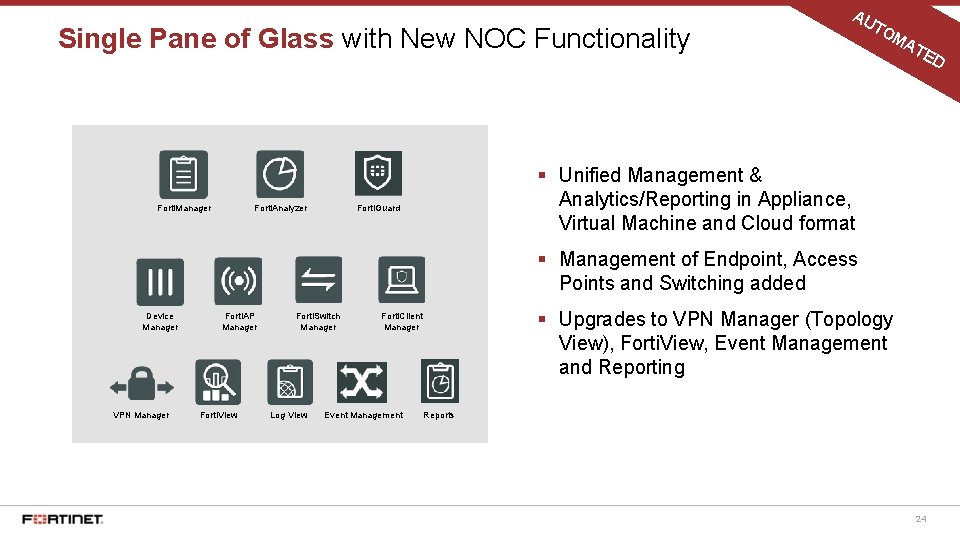
Single Pane of Glass with New NOC Functionality Forti. Manager Forti. Analyzer AU TO MA TE D § Unified Management & Analytics/Reporting in Appliance, Virtual Machine and Cloud format Forti. Guard § Management of Endpoint, Access Points and Switching added Device Manager VPN Manager Forti. AP Manager Forti. View Forti. Switch Manager Log View § Upgrades to VPN Manager (Topology View), Forti. View, Event Management and Reporting Forti. Client Manager Event Management Reports 24
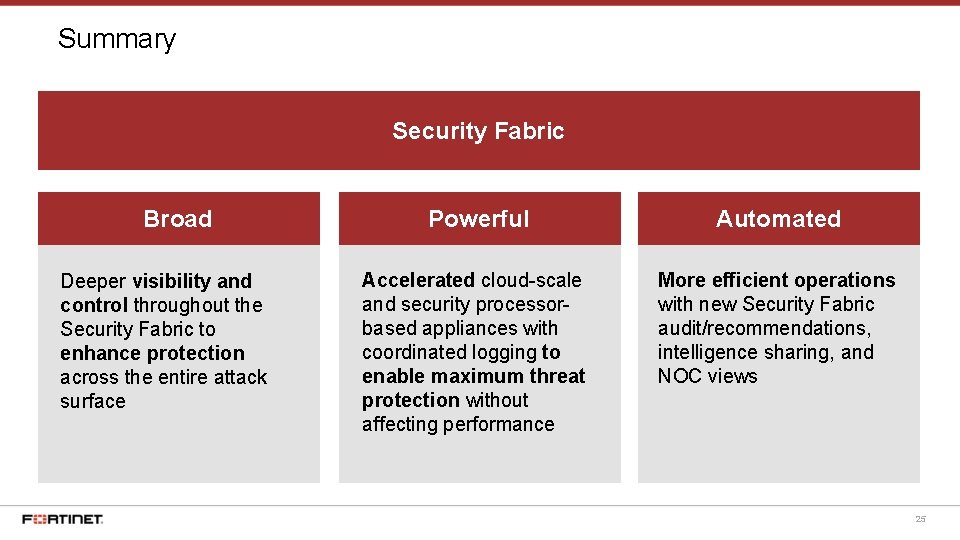
Summary Security Fabric Broad Deeper visibility and control throughout the Security Fabric to enhance protection across the entire attack surface Powerful Automated Accelerated cloud-scale and security processorbased appliances with coordinated logging to enable maximum threat protection without affecting performance More efficient operations with new Security Fabric audit/recommendations, intelligence sharing, and NOC views 25

- Slides: 26