Security Business Process Tommy Yionoulis Security Business Process
Security Business Process Tommy Yionoulis Security Business Process 1
Table of Contents • What is Workflow • What is Security Business Process • Use Cases • Interaction with Security Tools • Available Process Templates and Component packs • Tips for a Successful Workflow Project Security Business Process 2
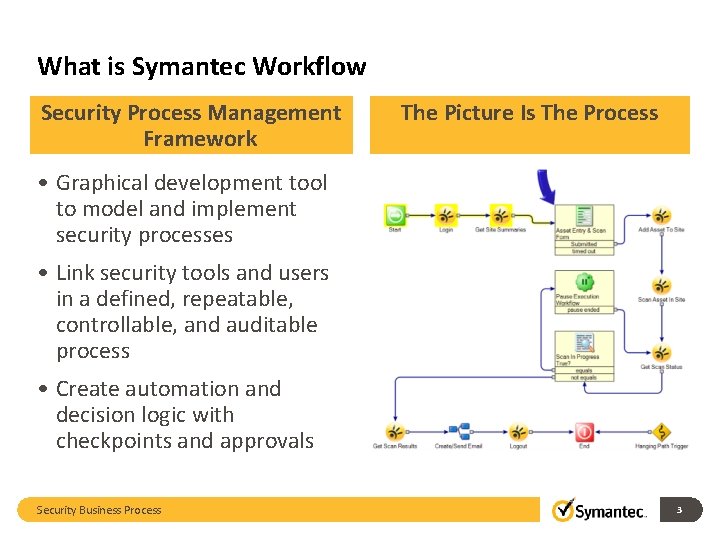
What is Symantec Workflow Security Process Management Framework The Picture Is The Process • Graphical development tool to model and implement security processes • Link security tools and users in a defined, repeatable, controllable, and auditable process • Create automation and decision logic with checkpoints and approvals Security Business Process 3
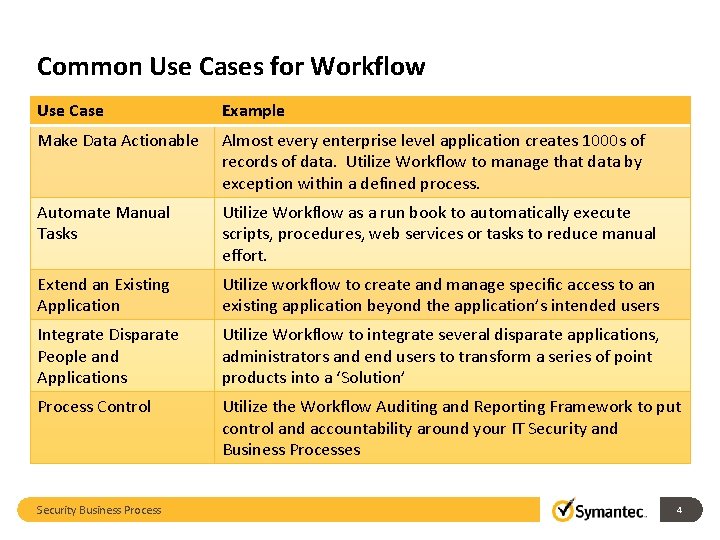
Common Use Cases for Workflow Use Case Example Make Data Actionable Almost every enterprise level application creates 1000 s of records of data. Utilize Workflow to manage that data by exception within a defined process. Automate Manual Tasks Utilize Workflow as a run book to automatically execute scripts, procedures, web services or tasks to reduce manual effort. Extend an Existing Application Utilize workflow to create and manage specific access to an existing application beyond the application’s intended users Integrate Disparate People and Applications Utilize Workflow to integrate several disparate applications, administrators and end users to transform a series of point products into a ‘Solution’ Process Control Utilize the Workflow Auditing and Reporting Framework to put control and accountability around your IT Security and Business Processes Security Business Process 4
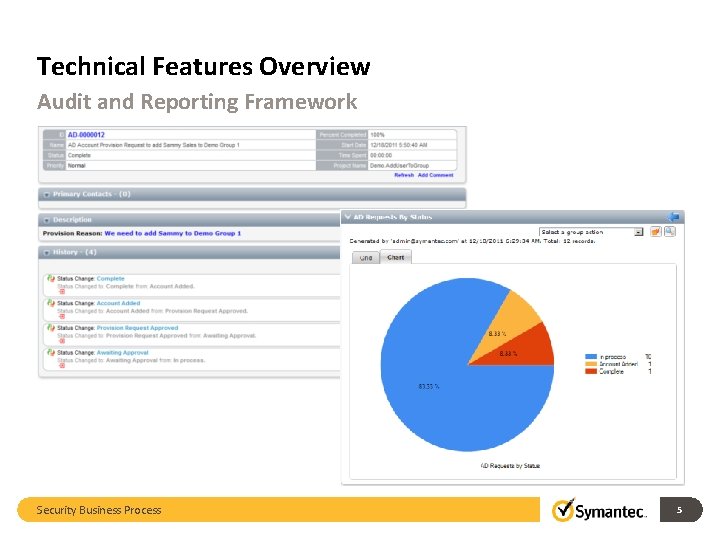
Technical Features Overview Audit and Reporting Framework Security Business Process 5
What is Security Business Process Going from Due Diligence to Due Care Security Business Processes are business processes that link security tools and the people who manage them in a repeatable and auditable way that moves the business from Due Diligence (identifying threats and risks) to Due Care (making risk based decisions to remediate issues). Security Business Process 6
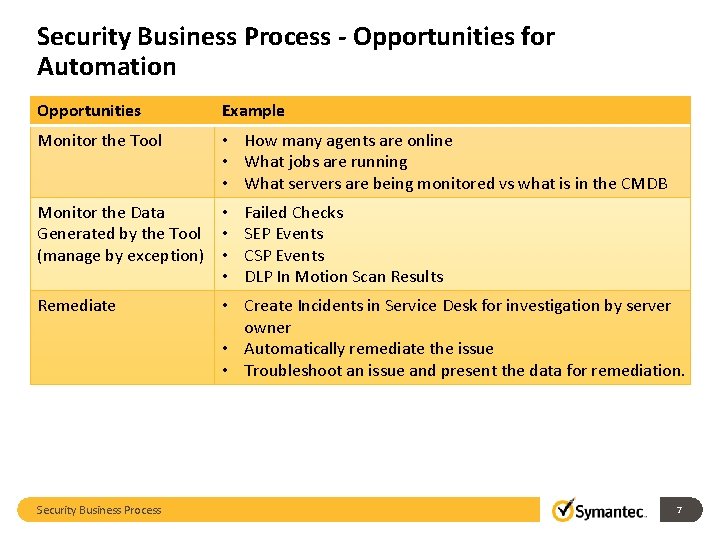
Security Business Process - Opportunities for Automation Opportunities Example Monitor the Tool • How many agents are online • What jobs are running • What servers are being monitored vs what is in the CMDB Monitor the Data • Failed Checks Generated by the Tool • SEP Events (manage by exception) • CSP Events • DLP In Motion Scan Results Remediate Security Business Process • Create Incidents in Service Desk for investigation by server owner • Automatically remediate the issue • Troubleshoot an issue and present the data for remediation. 7
Security Business Process Keys to Success • Automation = Proactivity – Monitoring processes never: go to sleep, get sick, or go on vacation. • Set Thresholds & Priorities – All events are not created equal • Create Human Failsafe Logic – The downside of automated processes is that it works exactly as it was designed to work when a catastrophic event in the network occurs – No one wants to manually close 10, 000 Incidents • Build processes that compliment your other tools – Try to avoid duplicate and redundant notifications • Keep the processes simple – Cheaper and easier to manage Security Business Process 8
Security Business Process Use Cases • CCS – Exception Request • CCS – Agent Health • CSP – File Integrity • CSP – Agent Health • DLP – Data at Rest Encryption • SEP – Event Management • SSIM – Incident Remediation Security Business Process 9
Security Business Process CCS – Exception Request • Owner of a server(s) cannot pass a specific check. • Requests and exception to this standard • Request process goes through several steps and approvers • Request is granted and the CCS Risk Manager is automatically updated. Security Business Process 10

Security Business Process CCS – Agent Health • CCS has attempted to scan a server unsuccessfully for 14 days. • Process checks with Service Desk to see if this server is part of an open Change Management ticket • Process checks with suppression data base to see if the server has active exception from scanning. • If no, process performs basic trouble shooting of server: – Ping, Traceroute, & Telnet to port • Open’s incident and presents trouble shooting results Security Business Process 11
Security Business Process CSP – File Integrity • Process detects a spike in high priority CSP events for a given day based off rolling 60 day average. • Process checks with Service Desk to see if this server is part of an open Change Management ticket • Process checks with suppression data base to see if the server has active exception for spikes above average. • If no, opens Incident for investigation. Security Business Process 12
Security Business Process CSP – Agent Health • CSP detects that an agent has become unresponsive for more then time frame (24 hours). • Process checks with Service Desk to see if this server is part of an open Change Management ticket • Process checks with suppression data base to see if the server has active exception from scanning. • If no, process performs basic trouble shooting of server: – Ping, Traceroute, & Telnet to port • Open’s incident and presents trouble shooting results Security Business Process 13
Security Business Process DLP – Data at Rest with Encryption • DLP detects a file with PCI Data on an unencrypted laptop. • DLP initiates workflow process. • Process quarantines the file and contacts end user giving them a choice to delete the file or encrypt in place. • They choose to encrypt in place and the process triggers a file encryption through PGP. • (can provide an exception request process for people who need to have these types of files on their computers) Security Business Process 14
Security Business Process SEP – Event Management (requires that Host Integrity is installed) • When process detects an unresolved alert in the SEPM console, the process initiates the SEP virus update process and then initiates a targeted scan of endpoint. • If the scan still finds an issue then an incident is created and assigned to the proper group for remediation. Security Business Process 15
Security Business Process SSIM – Incident Remediation • SSIM creates Incident and initiates a call to the Workflow Process. • Process retrieves Incident data and then creates an Incident in the Service Desk for investigation. • Process monitors the Service Desk to see when the Incident has been resolved. • When it has been resolved process closes the SSIM Incident and updates it to reflect the Service Desks Incident #. Security Business Process 16
Security Business Process Integration To Tools – API vs. SQL • If a product has an API you want to use that for the creation and searching of their database. – API’s are supported by the authoring company and will be updated with new releases. – API’s can be slower then straight SQL queries – A high volume of API calls can negatively affect an application’s performance. • If a product doesn’t have an API then you will want to dig into their database to get the data you need. – SQL Schemas can change with releases and this can break your processes. – SQL is the best for heavy lifting and data manipulation – Always do all calculations and data manipulations in your own database and never in the tool database. Security Business Process 17
Security Business Process Solution Center • Solution Center (app store) Q 4 2012 • Process Templates – Will range from simple processes where the integrations are handled for you but you will need to add the logic to full blown processes. – Current place to see workflow templates http: //www. workflowswat. com/process-templates. html Security Business Process 18
Security Business Process Component Packs • Control Compliance Suite: – Regular – Vulnerability Manager – RAM • Critical System Protection: – Event Management • Data Loss Prevention: • • – Getting Incident Data – Jar File how DLP calls Workflow (flex response rule) Mobile Management – Execute anything in the mobile management suite Symantec Endpoint Protection (needs host integrity installed) Symantec Security Information Manager: – Incident Data Symantec Web Gateway – Event Management Amazon EC 2 Cisco UCS (Flex. Pods) Microsoft – AD – Sharepoint – Exchange • VMWare – Vsphere (Actual VM’s) – Vshield (security groups) Security Business Process 19
Successful Workflow Project Keys to Success • Clearly defined process scope – Invest time in documenting the current process and the desired process. – Start with the Key Performance Indicators that you want to track, envision the reports that you will need, work backwards from there. • Best Practice Process Design – Distribute human tasks to the people responsible for remediation use technology to avoid bottlenecks or having one person do everything. – Look for ways to automate out human interactions by developing logic and have the process make decisions based off of the data. – Use Task Management vs. Email because process tasks can have: • SLA’s • Send Reminders • Are auditable – Create an audit table to track the process at it’s key points and to store key data for reporting. Security Business Process 20
Successful Workflow Project Questions to be answered • Internal vs. Consultants – Internal Development: • Invest in training of your resource • 3 rd party support contract with reputable partner – Symantec doesn’t offer Workflow Process Support • Set aside development time for your resource – the only way to become proficient at Workflow is to have the time to develop and learn. – Consultants: • Go with a reputable partner that can provide you with a resume and has done work with Symantec • Make sure they offer post project support • Make sure that you budget time for scoping, documentation, and training. Security Business Process 21
Thank you! Tommy Yionoulis – tommy@wevogroup. com 303 -917 -6333 Copyright © 2011 Symantec Corporation. All rights reserved. Symantec and the Symantec Logo are trademarks or registered trademarks of Symantec Corporation or its affiliates in the U. S. and other countries. Other names may be trademarks of their respective owners. This document is provided for informational purposes only and is not intended as advertising. All warranties relating to the information in this document, either express or implied, are disclaimed to the maximum extent allowed by law. The information in this document is subject to change without notice. Security Business Process 22
- Slides: 22