Security Best Practices for Carrier Ethernet Networks and

Security Best Practices for Carrier Ethernet Networks and Services Ralph Santitoro MEF Director and Security Working Group Co-chair Ralph@Santitoro. net
Acknowledgement • Special thanks to Peter Hayman and Steve Holmgren for their significant contributions to the MEF’s Carrier Ethernet security white paper and review comments on this presentation 2
Agenda • MEF Ethernet Service Classification • Security Vulnerability versus Service Flexibility • Service Provider and Enterprise Network Security Environments • Ethernet Threats and Vulnerabilities – Which types of services are affected ? – Best practice mitigation techniques • Carrier Ethernet Security Pillars • Summary 3
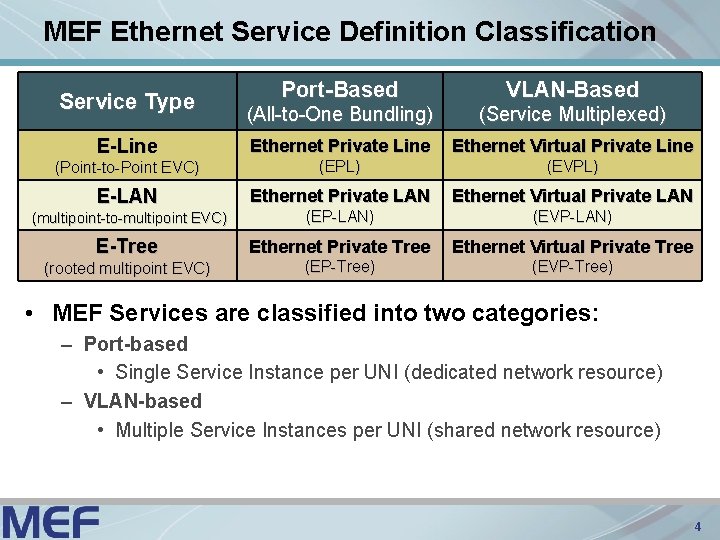
MEF Ethernet Service Definition Classification Port-Based VLAN-Based (All-to-One Bundling) (Service Multiplexed) Ethernet Private Line Ethernet Virtual Private Line (Point-to-Point EVC) (EPL) (EVPL) E-LAN Ethernet Private LAN Ethernet Virtual Private LAN (multipoint-to-multipoint EVC) (EP-LAN) (EVP-LAN) E-Tree Ethernet Private Tree Ethernet Virtual Private Tree (EP-Tree) (EVP-Tree) Service Type E-Line (rooted multipoint EVC) • MEF Services are classified into two categories: – Port-based • Single Service Instance per UNI (dedicated network resource) – VLAN-based • Multiple Service Instances per UNI (shared network resource) 4
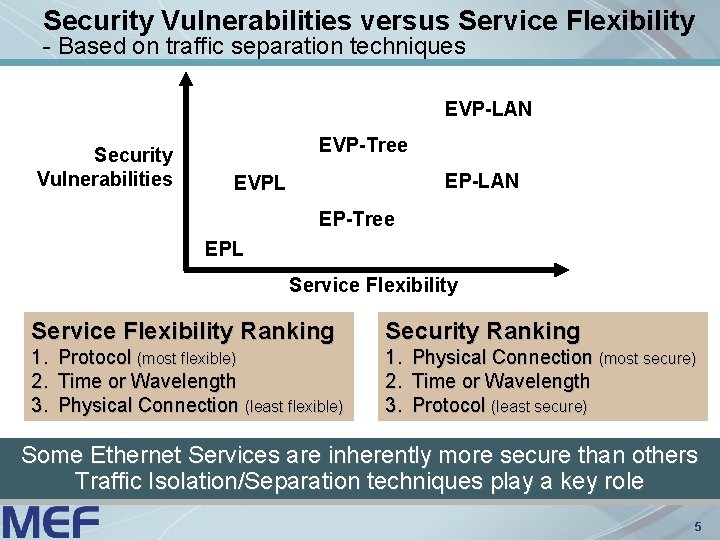
Security Vulnerabilities versus Service Flexibility - Based on traffic separation techniques EVP-LAN Security Vulnerabilities EVP-Tree EP-LAN EVPL EP-Tree EPL Service Flexibility Ranking Security Ranking 1. 2. 3. Protocol (most flexible) Time or Wavelength Physical Connection (least flexible) Physical Connection (most secure) Time or Wavelength Protocol (least secure) Some Ethernet Services are inherently more secure than others Traffic Isolation/Separation techniques play a key role 5
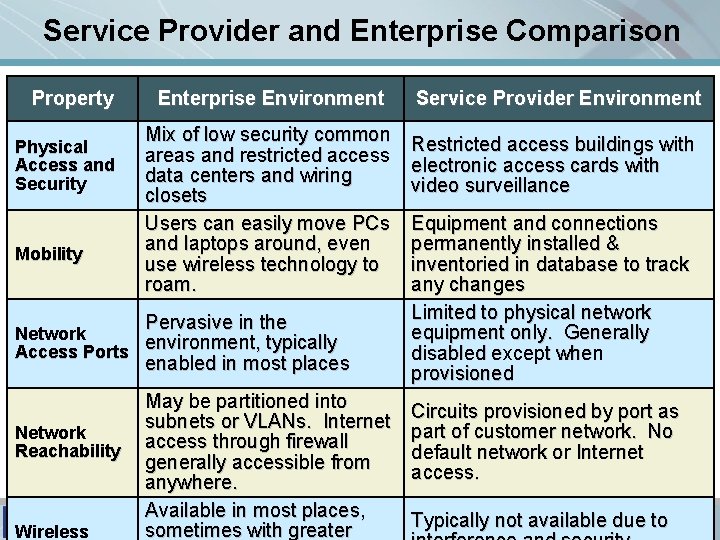
Service Provider and Enterprise Comparison Property Physical Access and Security Mobility Enterprise Environment Mix of low security common areas and restricted access data centers and wiring closets Users can easily move PCs and laptops around, even use wireless technology to roam. Pervasive in the Network Access Ports environment, typically enabled in most places Network Reachability Wireless May be partitioned into subnets or VLANs. Internet access through firewall generally accessible from anywhere. Available in most places, sometimes with greater Service Provider Environment Restricted access buildings with electronic access cards with video surveillance Equipment and connections permanently installed & inventoried in database to track any changes Limited to physical network equipment only. Generally disabled except when provisioned Circuits provisioned by port as part of customer network. No default network or Internet access. Typically not available due to 6
Agenda • MEF Ethernet Service Classification • Security Vulnerability versus Service Flexibility • Service Provider and Enterprise Network Security Environments • Ethernet Threats and Vulnerabilities – Which types of services are affected ? – Best practice mitigation techniques • Carrier Ethernet Security Pillars • Summary 7

Port or VLAN Mirroring and Monitoring - Threat Scenario and Affected Services Customer Site A 1 Port mirroring enabled Customer Site A 2 Eavesdropper • Threat Scenario – Eavesdropper gains control of switch and enables mirroring so subscriber’s traffic can be monitored and copied • Ethernet Services affected – EVPL, EVP-LAN and EVP-Tree • EPL unaffected since transported through dedicated transport, e. g. , SDH 8
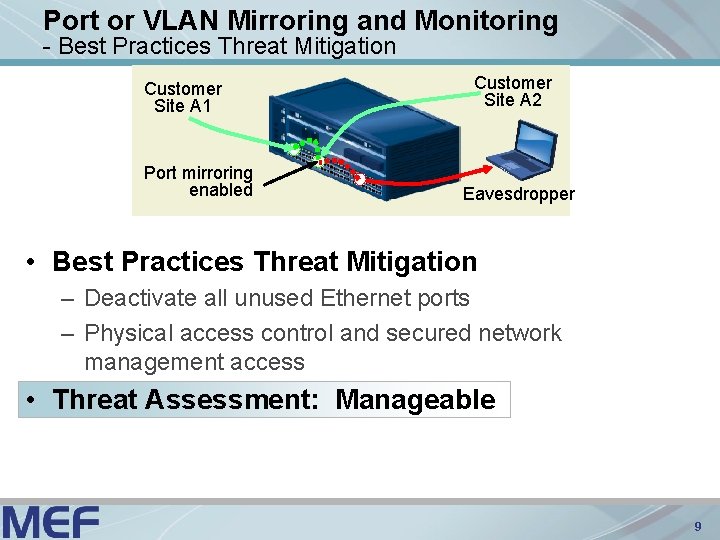
Port or VLAN Mirroring and Monitoring - Best Practices Threat Mitigation Customer Site A 1 Port mirroring enabled Customer Site A 2 Eavesdropper • Best Practices Threat Mitigation – Deactivate all unused Ethernet ports – Physical access control and secured network management access • Threat Assessment: Manageable 9
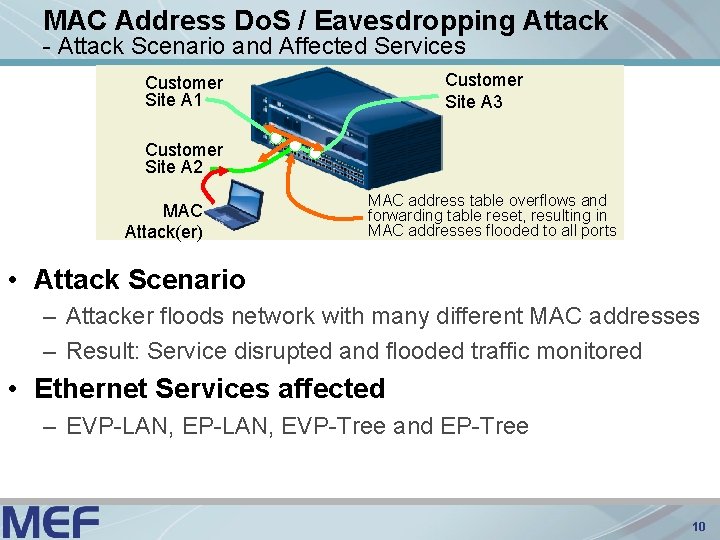
MAC Address Do. S / Eavesdropping Attack - Attack Scenario and Affected Services Customer Site A 3 Customer Site A 1 Customer Site A 2 MAC Attack(er) MAC address table overflows and forwarding table reset, resulting in MAC addresses flooded to all ports • Attack Scenario – Attacker floods network with many different MAC addresses – Result: Service disrupted and flooded traffic monitored • Ethernet Services affected – EVP-LAN, EVP-Tree and EP-Tree 10
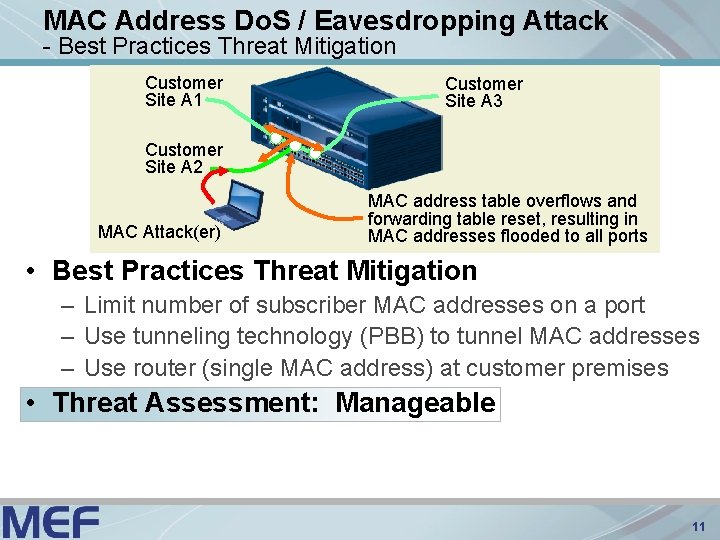
MAC Address Do. S / Eavesdropping Attack - Best Practices Threat Mitigation Customer Site A 1 Customer Site A 3 Customer Site A 2 MAC Attack(er) MAC address table overflows and forwarding table reset, resulting in MAC addresses flooded to all ports • Best Practices Threat Mitigation – Limit number of subscriber MAC addresses on a port – Use tunneling technology (PBB) to tunnel MAC addresses – Use router (single MAC address) at customer premises • Threat Assessment: Manageable 11
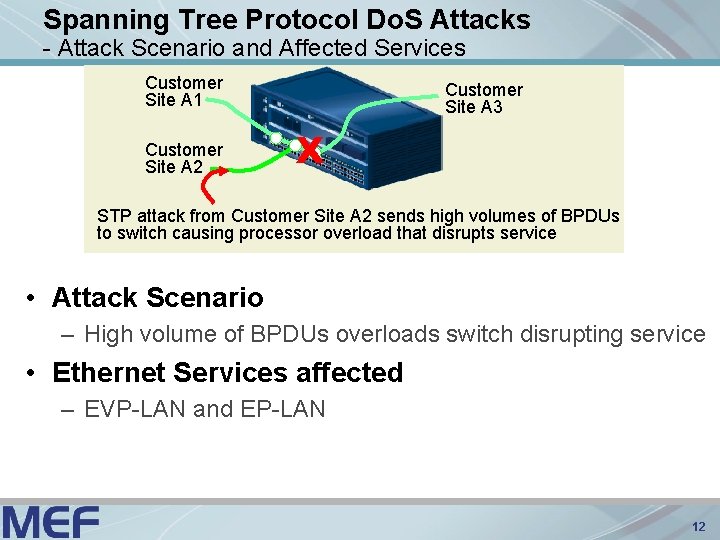
Spanning Tree Protocol Do. S Attacks - Attack Scenario and Affected Services Customer Site A 1 Customer Site A 2 Customer Site A 3 X STP attack from Customer Site A 2 sends high volumes of BPDUs to switch causing processor overload that disrupts service • Attack Scenario – High volume of BPDUs overloads switch disrupting service • Ethernet Services affected – EVP-LAN and EP-LAN 12
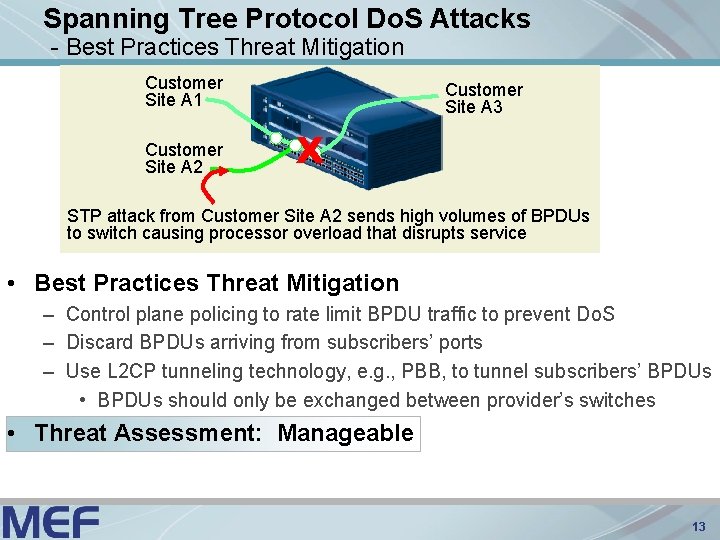
Spanning Tree Protocol Do. S Attacks - Best Practices Threat Mitigation Customer Site A 1 Customer Site A 2 Customer Site A 3 X STP attack from Customer Site A 2 sends high volumes of BPDUs to switch causing processor overload that disrupts service • Best Practices Threat Mitigation – Control plane policing to rate limit BPDU traffic to prevent Do. S – Discard BPDUs arriving from subscribers’ ports – Use L 2 CP tunneling technology, e. g. , PBB, to tunnel subscribers’ BPDUs • BPDUs should only be exchanged between provider’s switches • Threat Assessment: Manageable 13

Agenda • MEF Ethernet Service Classification • Security Vulnerability versus Service Flexibility • Service Provider and Enterprise Network Security Environments • Ethernet Threats and Vulnerabilities – Which types of services are affected ? – Best practice mitigation techniques • Carrier Ethernet Security Pillars • Summary 14
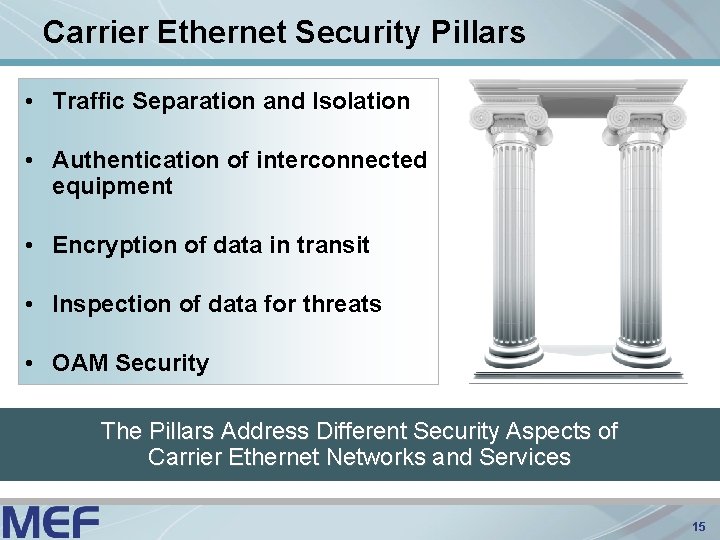
Carrier Ethernet Security Pillars • Traffic Separation and Isolation • Authentication of interconnected equipment • Encryption of data in transit • Inspection of data for threats • OAM Security The Pillars Address Different Security Aspects of Carrier Ethernet Networks and Services 15
Carrier Ethernet Security Pillars - Traffic Separation and Isolation • All customer traffic eventually traverses a shared transport network infrastructure – Subscriber traffic separation and isolation is required • Traffic separation and isolation techniques inherited from transport network – Ethernet over SDH/SONET: TDM channels (temporal separation) – Ethernet over λ: Colors (wavelength separation) – Provider Bridges (IEEE 802. 1 ad): S-VLAN Tag (protocol-based separation) – Provider Backbone Bridges (IEEE 802. 1 ah): Provider MAC Address and VLAN Tag (protocol-based separation) – MPLS Pseudowires: MPLS Label (protocol-based separation) 16
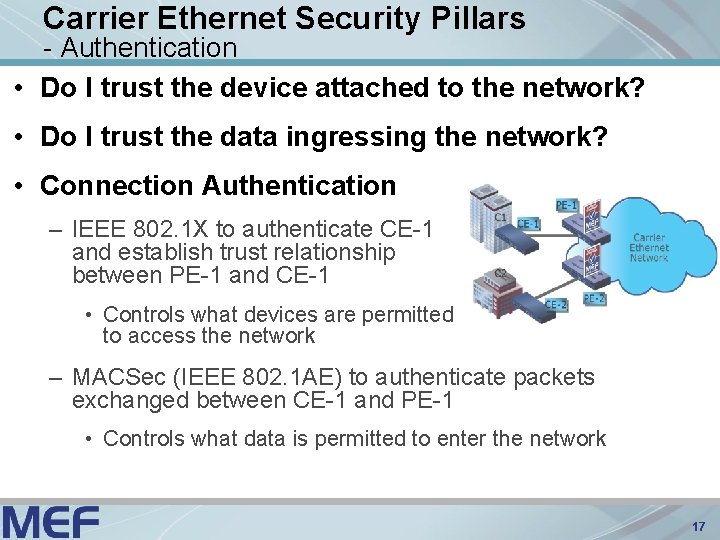
Carrier Ethernet Security Pillars - Authentication • Do I trust the device attached to the network? • Do I trust the data ingressing the network? • Connection Authentication – IEEE 802. 1 X to authenticate CE-1 and establish trust relationship between PE-1 and CE-1 • Controls what devices are permitted to access the network – MACSec (IEEE 802. 1 AE) to authenticate packets exchanged between CE-1 and PE-1 • Controls what data is permitted to enter the network 17

Carrier Ethernet Security Pillars - Encryption • Provides secrecy of sensitive data in transit • Encryption accomplished at different levels – Most commonly provided at IP Layer 3 • Ethernet and IP Encryption Standards – MACSec for Ethernet – IPSec/SSL for IP 18
Carrier Ethernet Security Pillars - Inspection • Enterprise subscribers need stored and in transit data to be monitored to detect and thwart theft of information – Sensitive data such as credit card, bank account, social security and tax identification numbers, and patient health care information – © Copyrighted data such as Music and Movie files • Inspection technologies scan for unwanted traffic (malicious or otherwise) – Optionally allows for blocking or rate limiting the unwanted traffic • Service providers can alert subscribers to threats (part of a managed security service) – and contain (block) the threats before they can become widespread Content inspection typically performed at the application layer 19
Carrier Ethernet Security Pillars - OAM Security • OAM security at Data, Control and Management planes – Ensure subscriber and service provider management frames do not “leak” into or trigger unwanted OAM function in each others’ network • Provider’s management frames must be separated from subscribers’ data using, e. g. , VLANs, SDH DCN, etc. – Limited set of subscribers’ BPDUs appropriate for Ethernet service type acted upon by service provider’s network elements • Certain service types, e. g. , E-LAN, exchange L 2 CPs (L 2 Control Protocols) between provider & subscriber NEs – Limited set of L 2 CPs need to be acted upon • Any L 2 CPs outside this limited set tunneled or discarded per SLA – Suspicious behavior of L 2 CPs requires rate-limiting and alarming 20

Summary • All networking technologies have security threats and vulnerabilities – Through due diligence and Security Best Practices, network operators can effectively manage them • Carrier Ethernet Networks and Services – Are as secure as other networking technologies – Introduce new service flexibilities not possible or practical to deliver with other networking technologies 21

Questions?

For in-depth presentations of Carrier Ethernet for business, Ethernet services, technical overview, certification program etc. , visit: www. metroethernetforum. org/presentations For more information regarding joining the MEF: Visit: Email us at: Call us at: www. metroethernetforum. org manager@metroethernetforum. org +1. 310. 258. 8032 (California, USA)
- Slides: 23