Security Assessment using Office 365 Secure Score Reinventing







- Slides: 23

Security Assessment using Office 365 Secure Score Reinventing Productivity: Trust
Where do I go to enable security features?
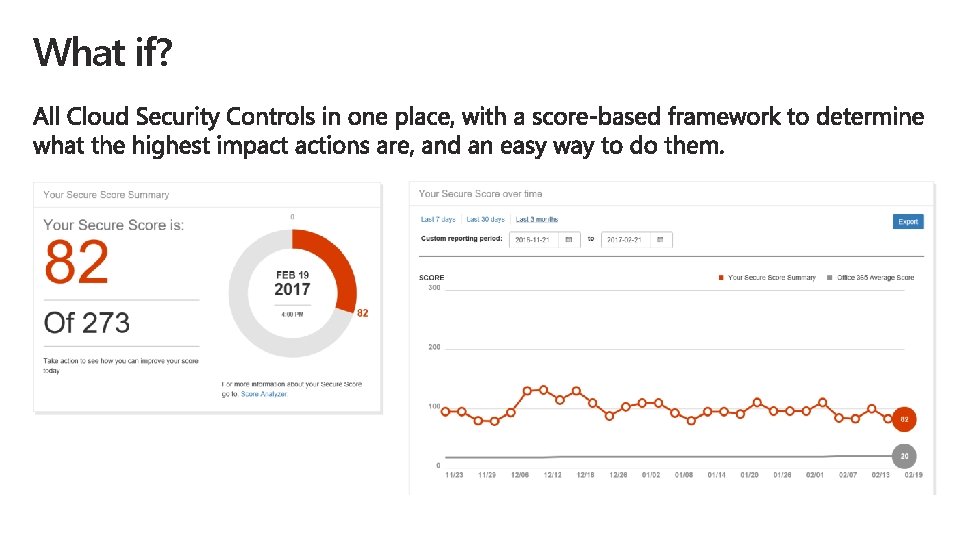
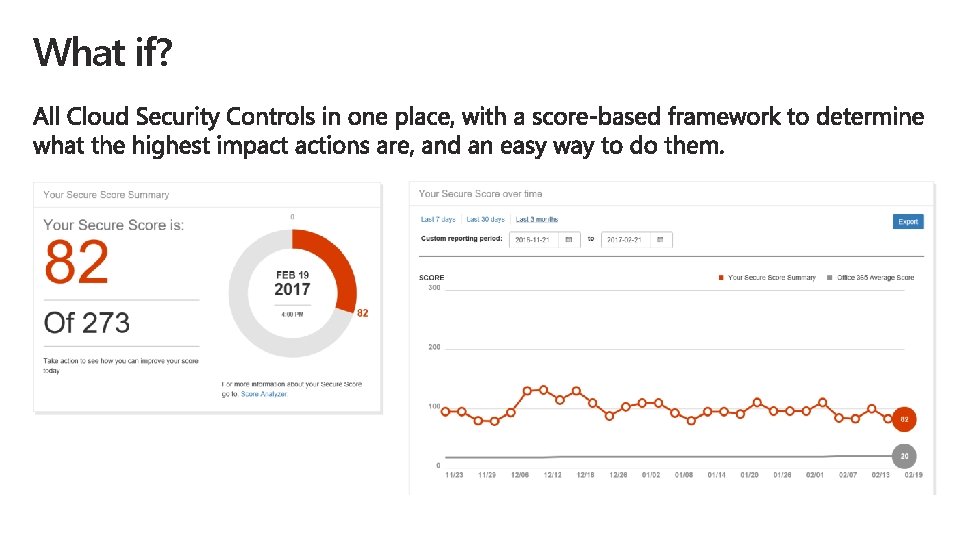
What if?
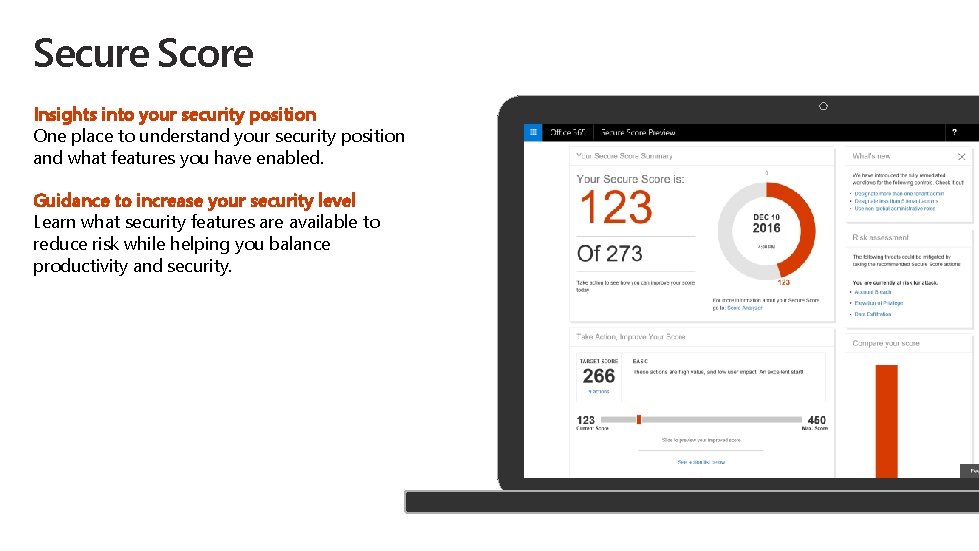
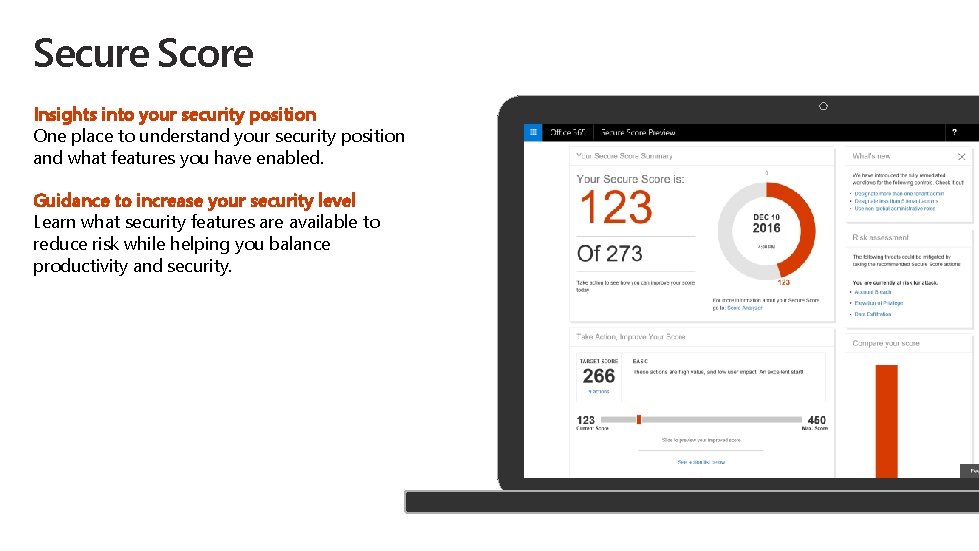
Secure Score Insights into your security position One place to understand your security position and what features you have enabled. Guidance to increase your security level Learn what security features are available to reduce risk while helping you balance productivity and security.

Demo: Office 365 Secure Score
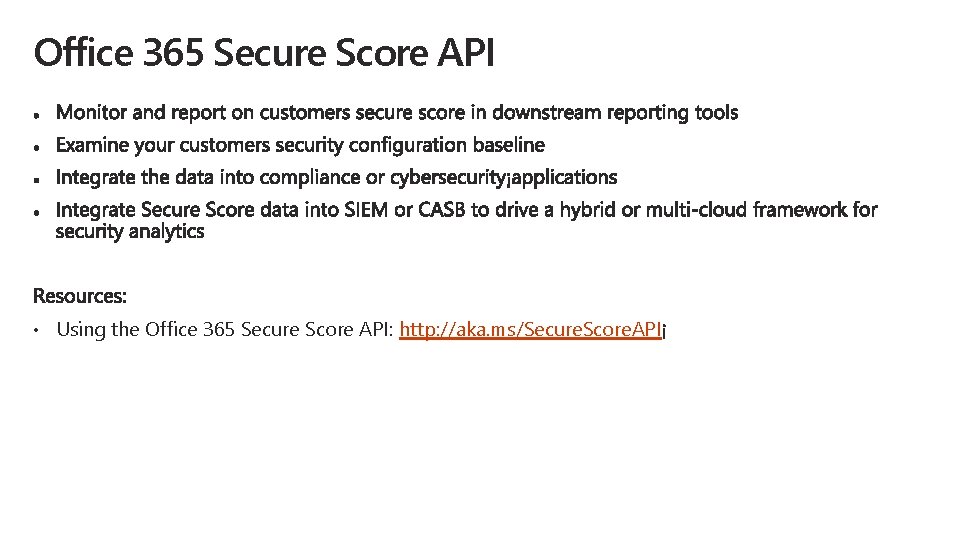
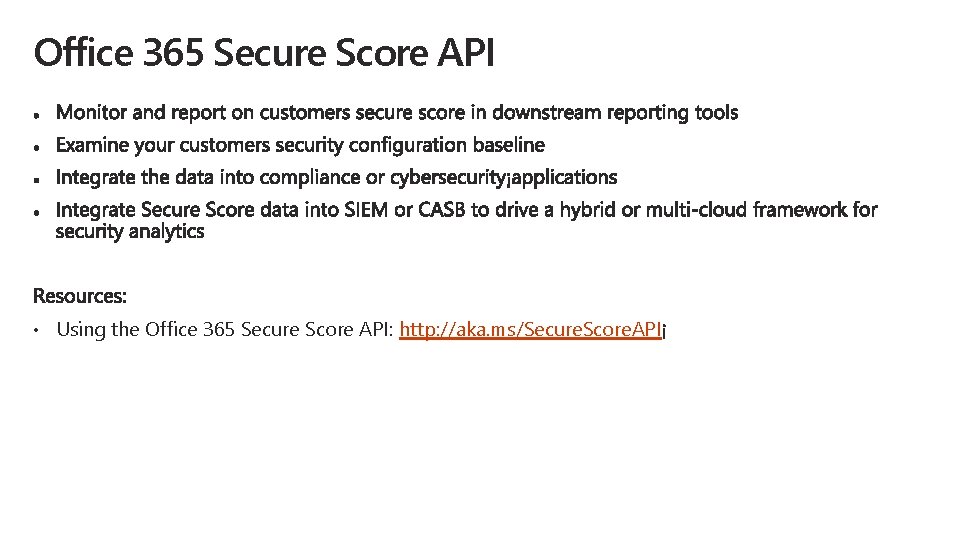
Office 365 Secure Score API • Using the Office 365 Secure Score API: http: //aka. ms/Secure. Score. API

Security Assessments Using Secure Score Security assessment opportunities Introduction to the Security Assessment Workshop (2 day) Assessment methodology Secure score report Customer deliverables
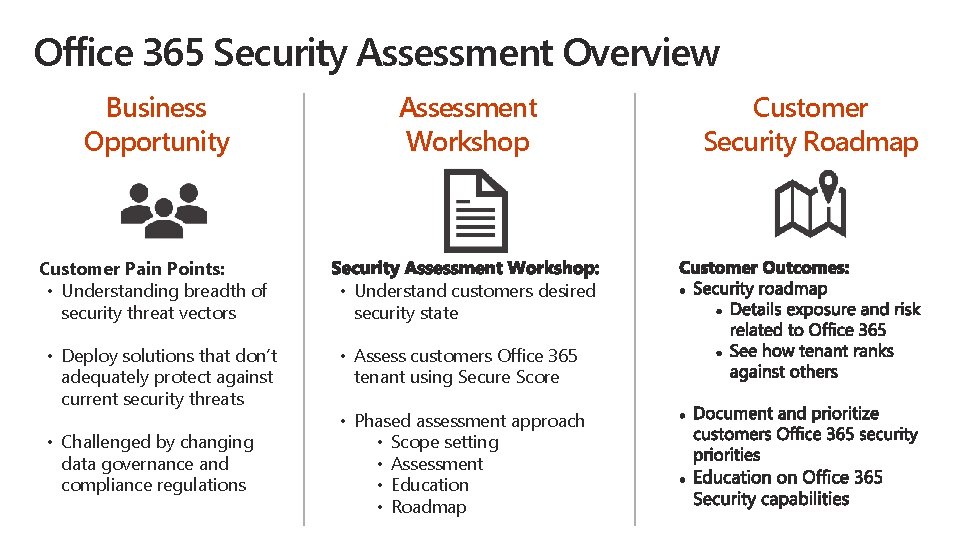
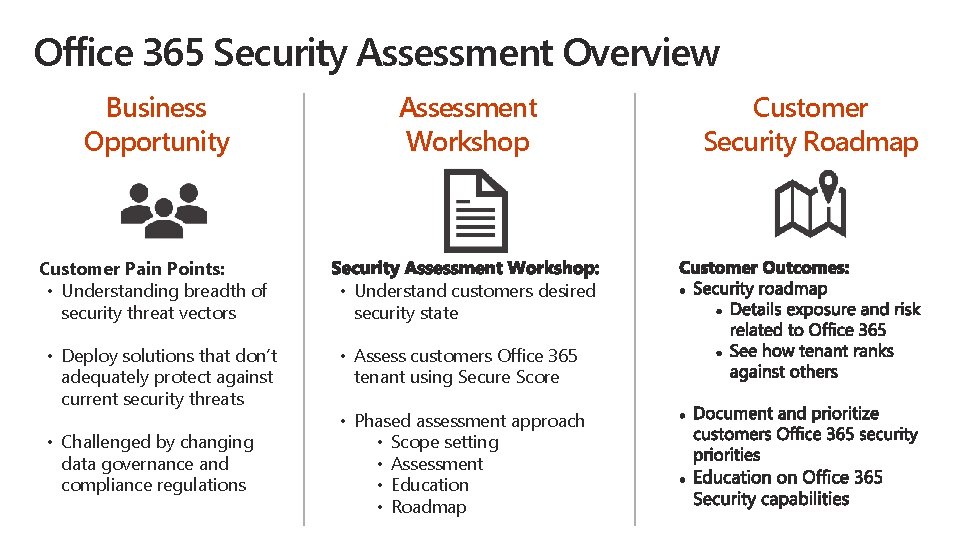
Office 365 Security Assessment Overview Business Opportunity Assessment Workshop Customer Pain Points: • Understanding breadth of security threat vectors • Understand customers desired security state • Deploy solutions that don’t adequately protect against current security threats • Challenged by changing data governance and compliance regulations • Assess customers Office 365 tenant using Secure Score • Phased assessment approach • Scope setting • Assessment • Education • Roadmap Customer Security Roadmap
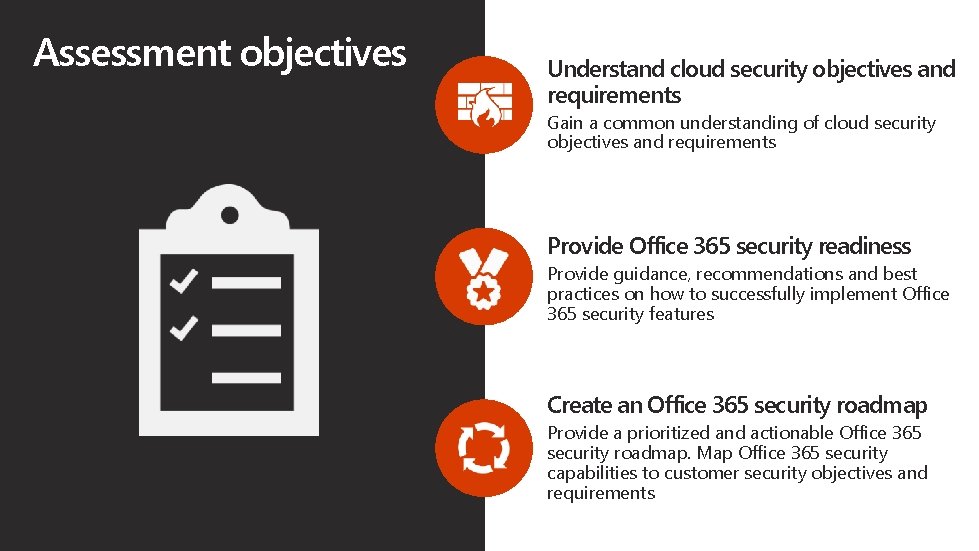
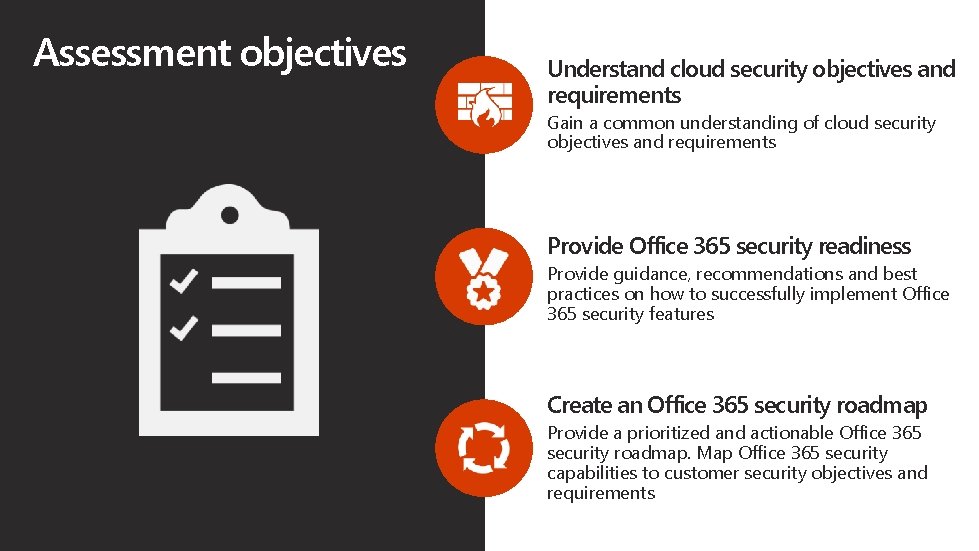
Assessment objectives Understand cloud security objectives and requirements Gain a common understanding of cloud security objectives and requirements Provide Office 365 security readiness Provide guidance, recommendations and best practices on how to successfully implement Office 365 security features Create an Office 365 security roadmap Provide a prioritized and actionable Office 365 security roadmap. Map Office 365 security capabilities to customer security objectives and requirements
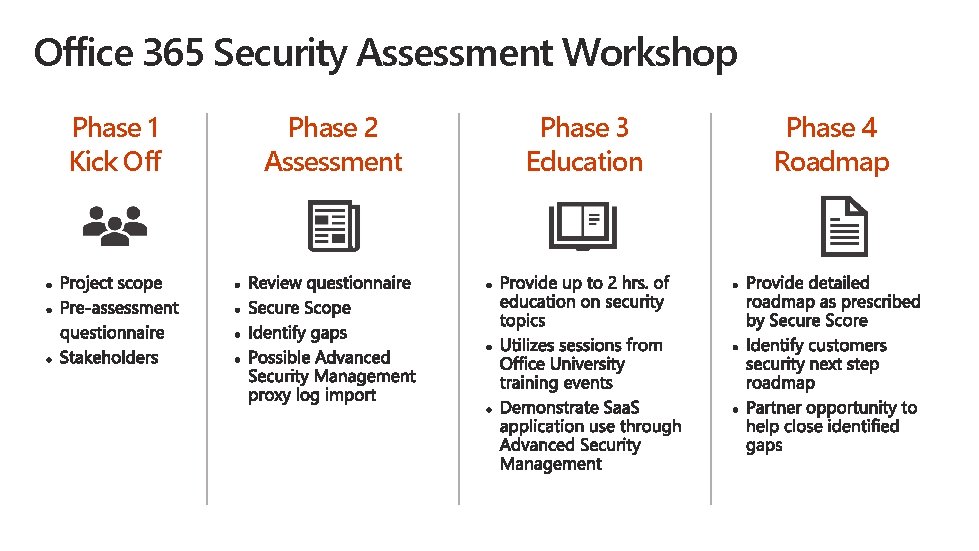
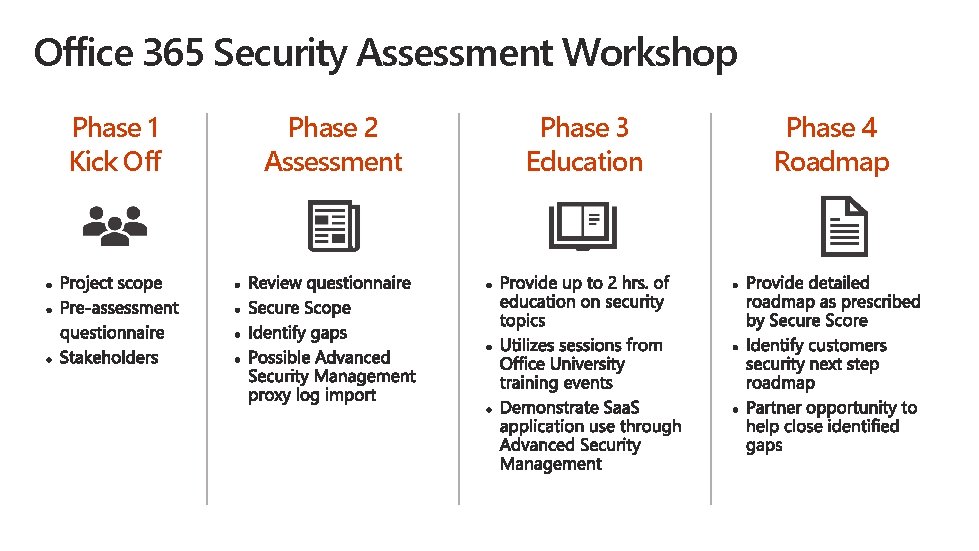
Office 365 Security Assessment Workshop Phase 1 Kick Off Phase 2 Assessment Phase 3 Education Phase 4 Roadmap

What is needed from customers? Complete questionnaire Contains questions about Office 365 usage, plans, security requirements, security objectives, industry regulations Access to teams during the assessment During the on-site phase, multiple workshops will be planned which require the attendance of stakeholders, security teams, cloud and infra teams Provide stakeholder during process A stakeholder/sponsor is required to oversee and own the process from the customer side Office 365 tenant security reports Produce necessary tenant reports such as Secure Score, and proxy logs for ASM demo.

Secure Score report Score-based framework Calculates a security score based on current security settings and behaviours in Office 365 and compares it to a baseline asserted by Microsoft Single dashboard Displays the current security score and a list of prioritized and recommended actions on how to improve the score in a single dashboard Manage Cybersecurity Risk Manage cybersecurity risk by using Secure Score to track and plan incremental improvements over time Available for Business Premium and Enterprise Office 365 tenants Available here: https: //securescore. office. com

Outcomes Conversation from Secure Score report • • Where you are today? Where do you want to go? How will we get there? What does success mean to you? Workshop Outcome • Prioritized, actionable Office 365 security roadmap • Identify key stakeholders • Identify potential constraints • Identify potential disruptive events that can impact the items on the roadmap
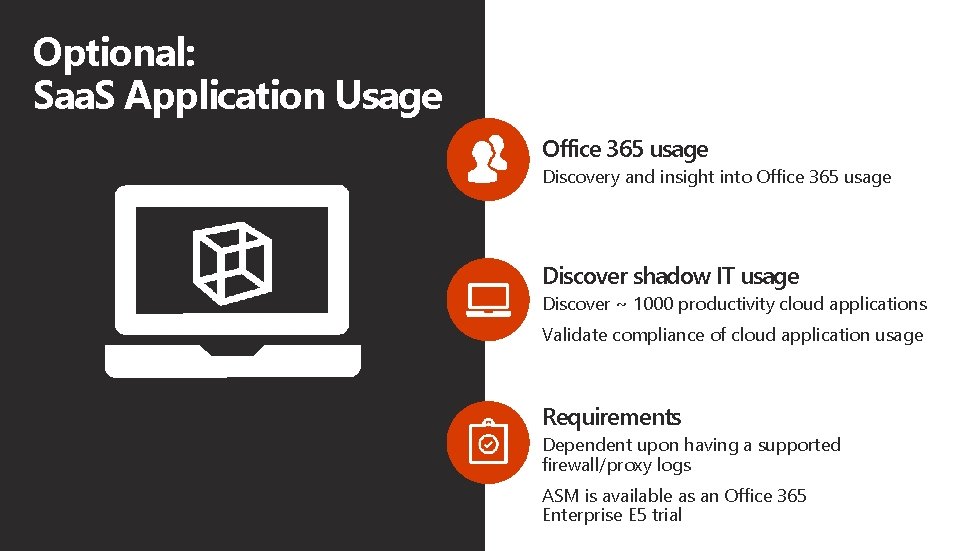
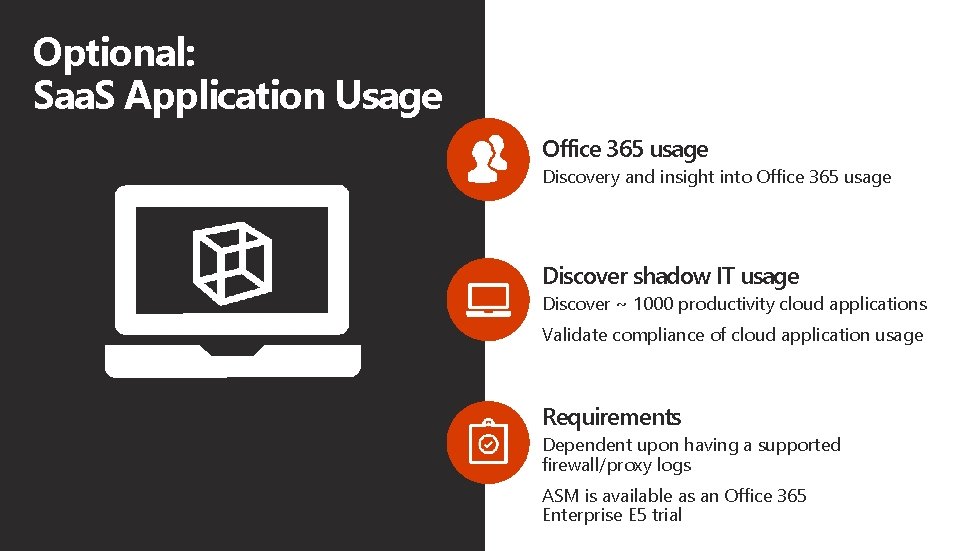
Optional: Saa. S Application Usage Office 365 usage Discovery and insight into Office 365 usage Discover shadow IT usage Discover ~ 1000 productivity cloud applications Validate compliance of cloud application usage Requirements Dependent upon having a supported firewall/proxy logs ASM is available as an Office 365 Enterprise E 5 trial
Out of Scope Technical designs or implementations Implementation or designs beyond the assessment are out of scope but can be part of next steps with customer. Proof of Concepts or Labs Demonstrations will be conducted within the readiness sessions, but proof of concepts and/or labs must be conducted as separate engagements Provide security assessment for hybrid and/or on-premises infrastructure This assessment workshop includes assessing of Office 365 security features as reported by the Office 365 Secure Score tool

Demo: Secure Score Assessment (Offering)
Example Assessment Current state Key recommendations Partner opportunity to help Sample agenda
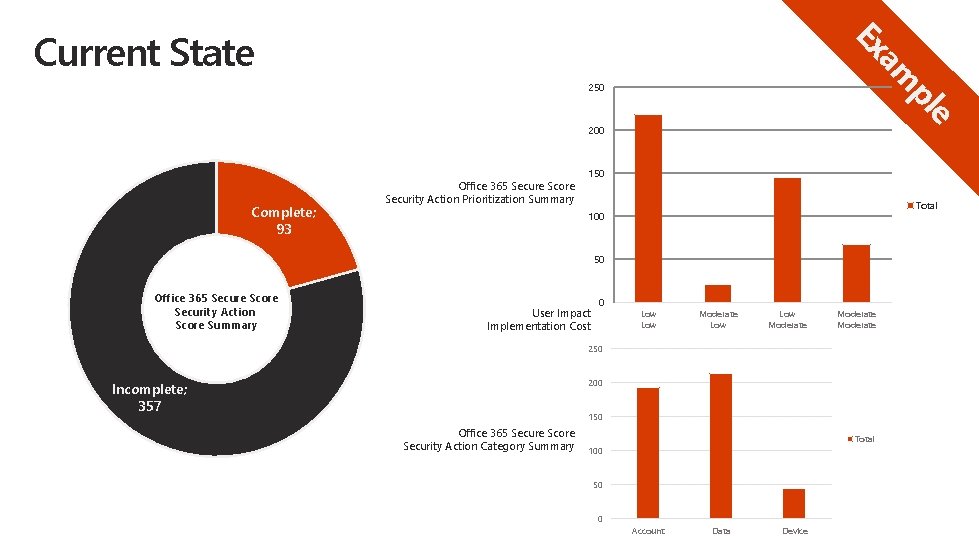
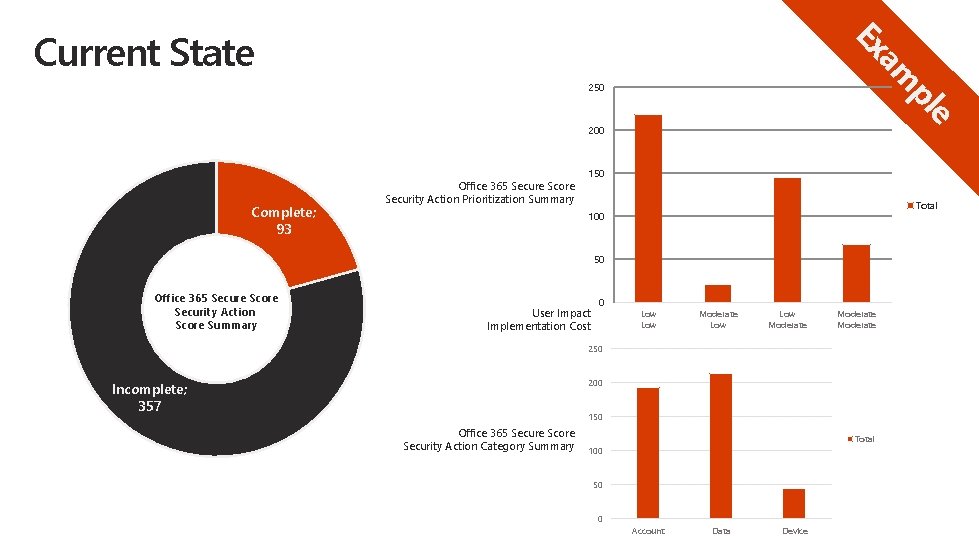
e pl am Ex Current State 250 200 Complete; 93 Office 365 Secure Score Security Action Prioritization Summary 150 Total 100 50 Office 365 Secure Score Security Action Score Summary User Impact Implementation Cost 0 Low Low Moderate 250 200 Incomplete; 357 150 Office 365 Secure Score Security Action Category Summary Total 100 50 0 Account Data Device
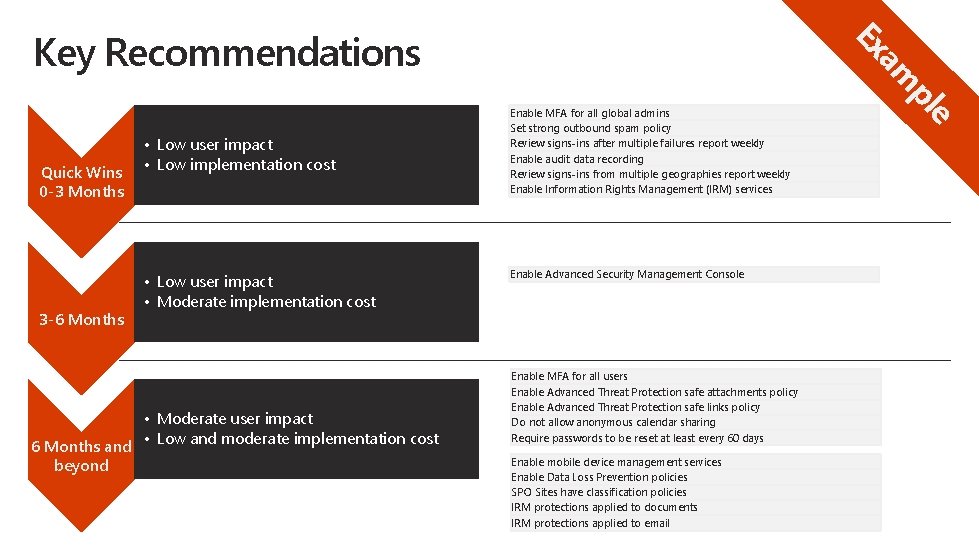
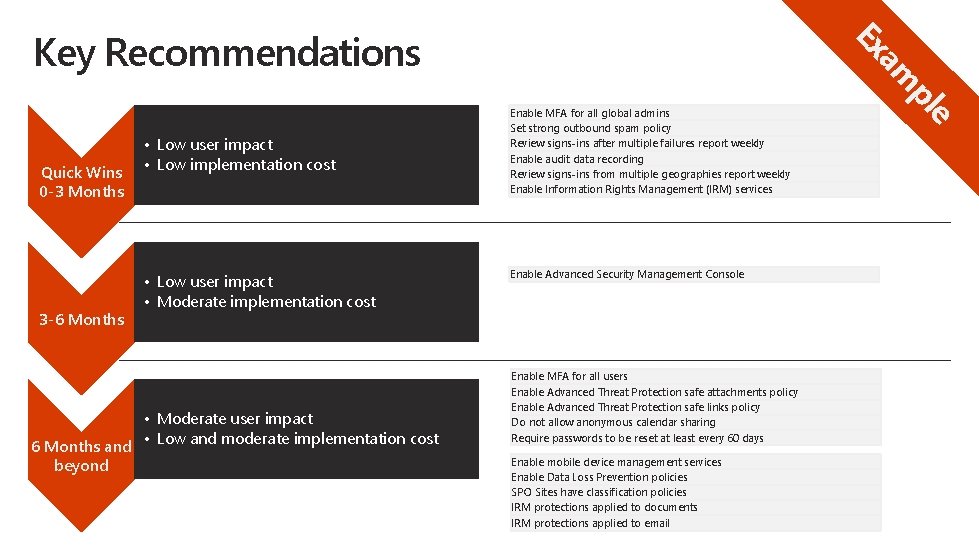
Quick Wins 0 -3 Months 3 -6 Months • Low user impact • Low implementation cost • Low user impact • Moderate implementation cost • Moderate user impact 6 Months and • Low and moderate implementation cost beyond Enable MFA for all global admins Set strong outbound spam policy Review signs-ins after multiple failures report weekly Enable audit data recording Review signs-ins from multiple geographies report weekly Enable Information Rights Management (IRM) services Enable Advanced Security Management Console Enable MFA for all users Enable Advanced Threat Protection safe attachments policy Enable Advanced Threat Protection safe links policy Do not allow anonymous calendar sharing Require passwords to be reset at least every 60 days Enable mobile device management services Enable Data Loss Prevention policies SPO Sites have classification policies IRM protections applied to documents IRM protections applied to email e pl am Ex Key Recommendations
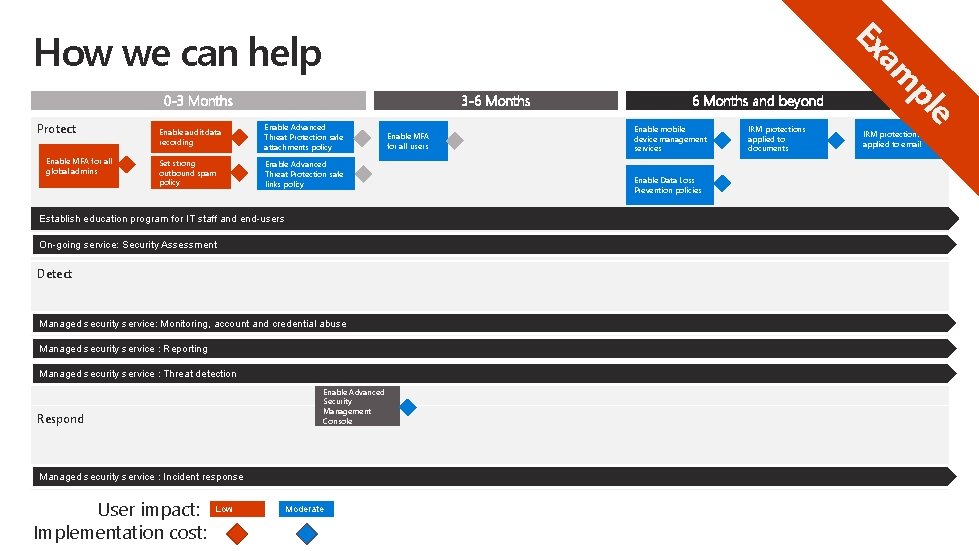
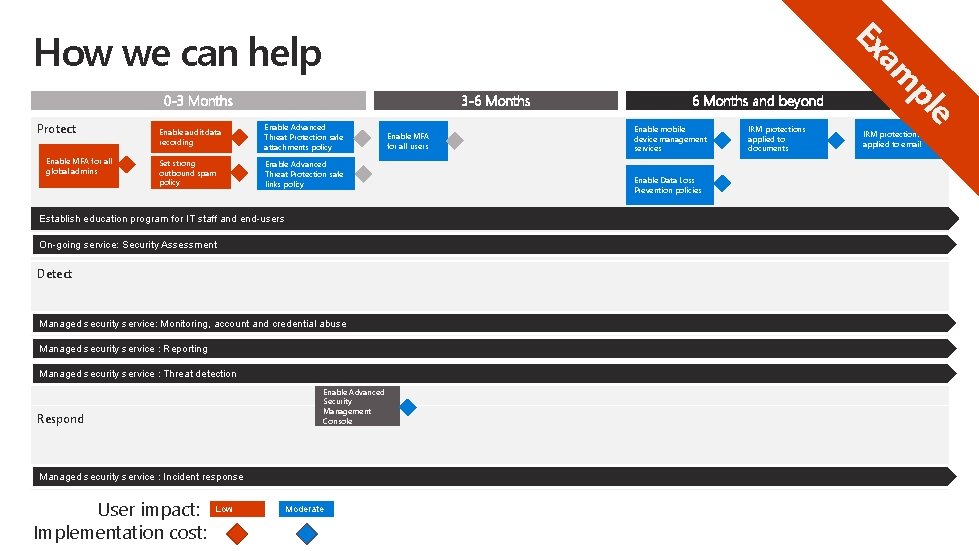
0 -3 Months Protect Enable MFA for all global admins 3 -6 Months Enable audit data recording Enable Advanced Threat Protection safe attachments policy Set strong outbound spam policy Enable Advanced Threat Protection safe links policy Establish education program for IT staff and end-users On-going service: Security Assessment Detect Managed security service: Monitoring, account and credential abuse Managed security service : Reporting Managed security service : Threat detection Enable Advanced Security Management Console Respond Managed security service : Incident response User impact: Implementation cost: Low Moderate Enable MFA for all users 6 Months and beyond Enable mobile device management services Enable Data Loss Prevention policies IRM protections applied to documents e pl am Ex How we can help IRM protections applied to email
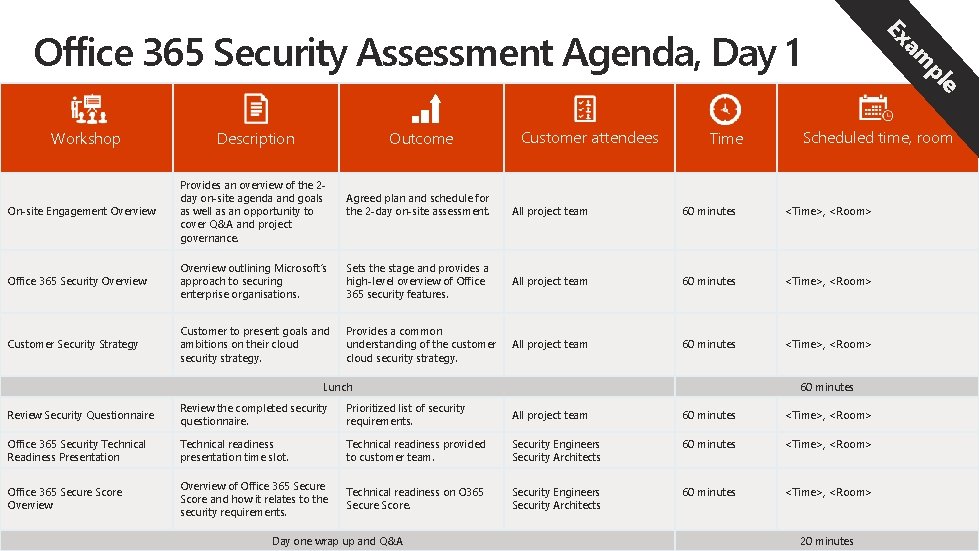
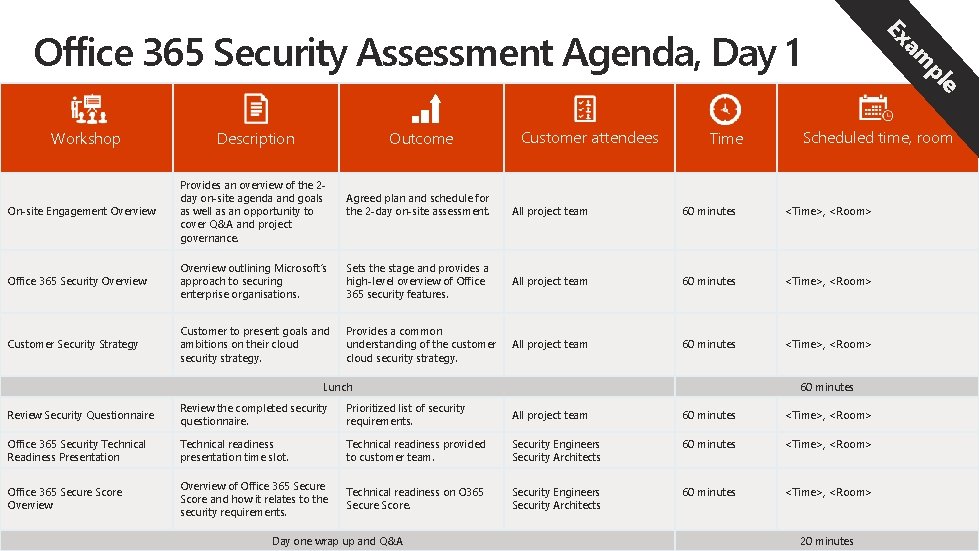
Workshop Description Outcome On-site Engagement Overview Provides an overview of the 2 day on-site agenda and goals as well as an opportunity to cover Q&A and project governance. Office 365 Security Overview outlining Microsoft‘s approach to securing enterprise organisations. Customer Security Strategy Customer to present goals and ambitions on their cloud security strategy. Agreed plan and schedule for the 2 -day on-site assessment. Customer attendees Time e pl am Ex Office 365 Security Assessment Agenda, Day 1 Scheduled time, room All project team 60 minutes <Time>, <Room> Sets the stage and provides a high-level overview of Office 365 security features. All project team 60 minutes <Time>, <Room> Provides a common understanding of the customer cloud security strategy. All project team 60 minutes <Time>, <Room> Lunch 60 minutes Review Security Questionnaire Review the completed security questionnaire. Prioritized list of security requirements. All project team 60 minutes <Time>, <Room> Office 365 Security Technical Readiness Presentation Technical readiness presentation time slot. Technical readiness provided to customer team. Security Engineers Security Architects 60 minutes <Time>, <Room> Office 365 Secure Score Overview of Office 365 Secure Score and how it relates to the security requirements. Technical readiness on O 365 Secure Score. Security Engineers Security Architects 60 minutes <Time>, <Room> Day one wrap up and Q&A 20 minutes
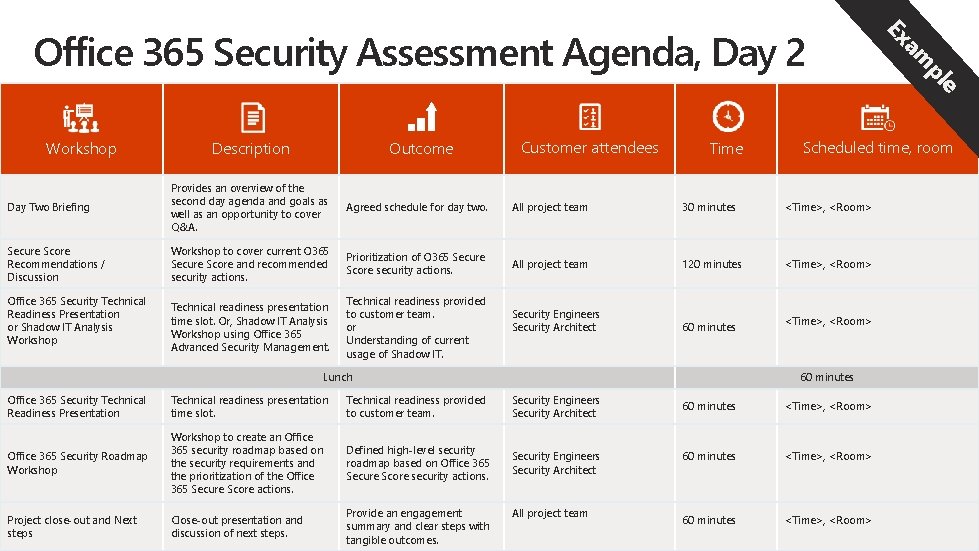
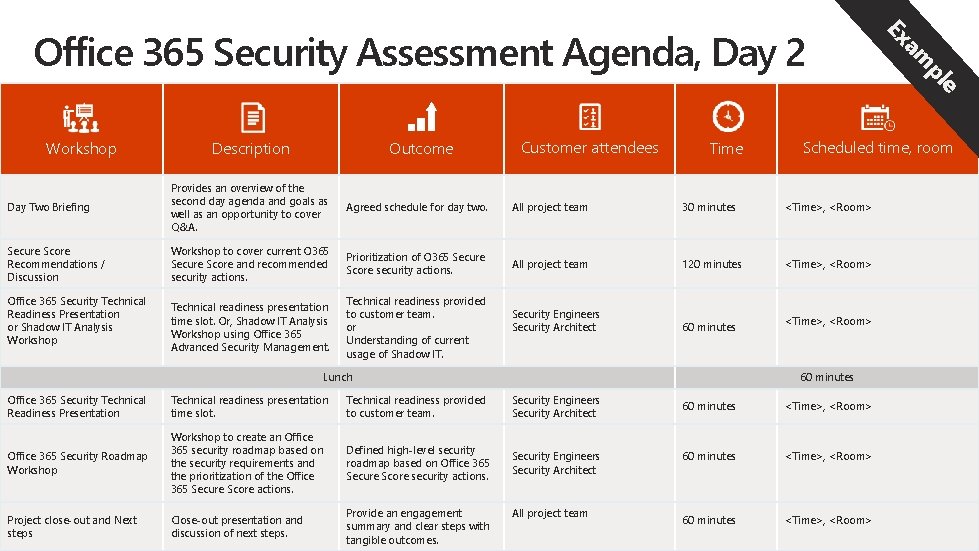
Workshop Description Outcome Customer attendees Time Scheduled time, room Day Two Briefing Provides an overview of the second day agenda and goals as well as an opportunity to cover Q&A. Agreed schedule for day two. All project team 30 minutes <Time>, <Room> Secure Score Recommendations / Discussion Workshop to cover current O 365 Secure Score and recommended security actions. Prioritization of O 365 Secure Score security actions. All project team 120 minutes <Time>, <Room> Technical readiness presentation time slot. Or, Shadow IT Analysis Workshop using Office 365 Advanced Security Management. Technical readiness provided to customer team. or Understanding of current usage of Shadow IT. Security Engineers Security Architect 60 minutes Office 365 Security Technical Readiness Presentation or Shadow IT Analysis Workshop Lunch <Time>, <Room> 60 minutes Office 365 Security Technical Readiness Presentation Technical readiness presentation time slot. Technical readiness provided to customer team. Security Engineers Security Architect Office 365 Security Roadmap Workshop to create an Office 365 security roadmap based on the security requirements and the prioritization of the Office 365 Secure Score actions. Defined high-level security roadmap based on Office 365 Secure Score security actions. Security Engineers Security Architect Project close-out and Next steps Close-out presentation and discussion of next steps. Provide an engagement summary and clear steps with tangible outcomes. All project team e pl am Ex Office 365 Security Assessment Agenda, Day 2 60 minutes <Time>, <Room>
© 2017 Microsoft Corporation. All rights reserved. Microsoft, Windows, and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.