Security Assertion Markup Language A Brief Introduction to
Security Assertion Markup Language A Brief Introduction to SAML Tom Scavo trscavo@ncsa. uiuc. edu NCSA saml-intro-dec 05 1
Overview • • • SAML assertions and statements SAML request/response protocol SAML bindings (e. g. , SOAP binding) SAML profiles (esp. , the browser profiles) SAML attribute exchange Coverage of both SAML 1. x and 2. 0 saml-intro-dec 05 2
SAML Defined • Security Assertion Markup Language (SAML) is an XML standard for exchanging authentication and authorization data between entities • SAML is a product of the OASIS Security Services Technical Committee: http: //www. oasis-open. org/committees/security/ saml-intro-dec 05 3
SAML Versions • SAML 1. 0 was adopted as an OASIS standard in Nov 2002 • SAML 1. 1 was ratified as an OASIS standard in Sep 2003 • SAML 2. 0 became an OASIS standard in Mar 2005 saml-intro-dec 05 4
SAML Standards • SAML is built upon the following technology standards: – Extensible Markup Language (XML) – XML Schema – XML Signature – XML Encryption (SAML 2. 0 only) – Hypertext Transfer Protocol (HTTP) – SOAP saml-intro-dec 05 5
SAML Specification • A SAML specification defines: – Assertions (XML) – Protocols (XML + processing rules) – Bindings (HTTP, SOAP) – Profiles (= Protocols + Bindings) • Assertions and protocols together constitute SAML core (syntactically defined by XML schema) • Profiles define semantics of use cases saml-intro-dec 05 6
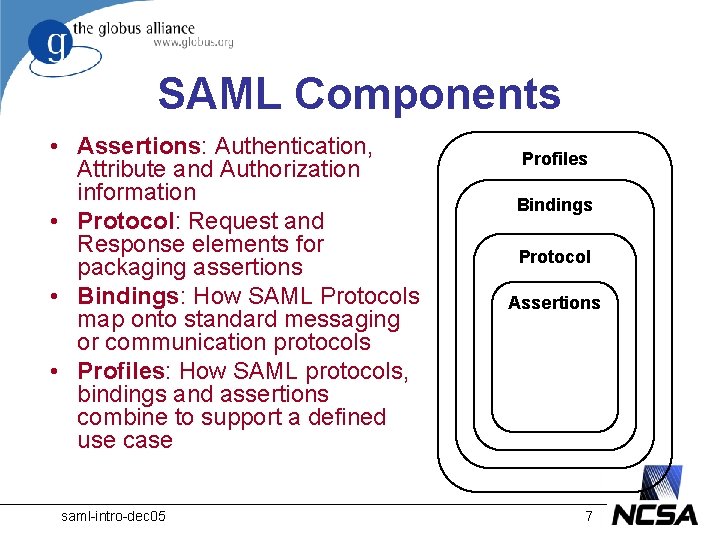
SAML Components • Assertions: Authentication, Attribute and Authorization information • Protocol: Request and Response elements for packaging assertions • Bindings: How SAML Protocols map onto standard messaging or communication protocols • Profiles: How SAML protocols, bindings and assertions combine to support a defined use case saml-intro-dec 05 Profiles Bindings Protocol Assertions 7
SAML Core saml-intro-dec 05 8
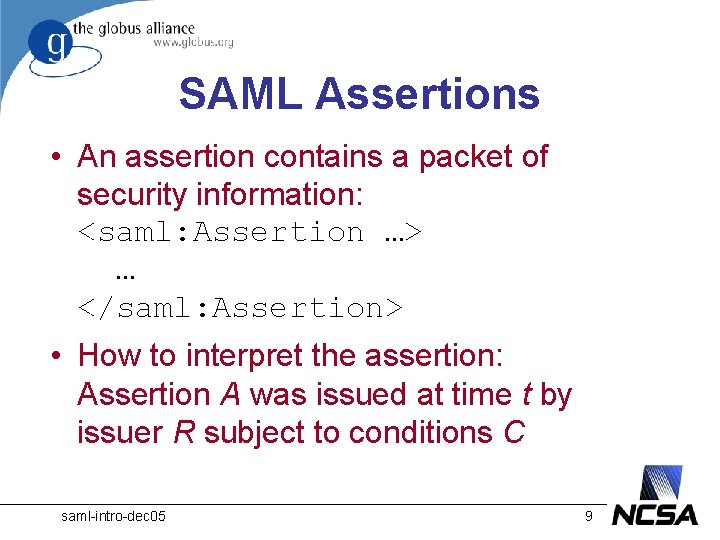
SAML Assertions • An assertion contains a packet of security information: <saml: Assertion …> … </saml: Assertion> • How to interpret the assertion: Assertion A was issued at time t by issuer R subject to conditions C saml-intro-dec 05 9
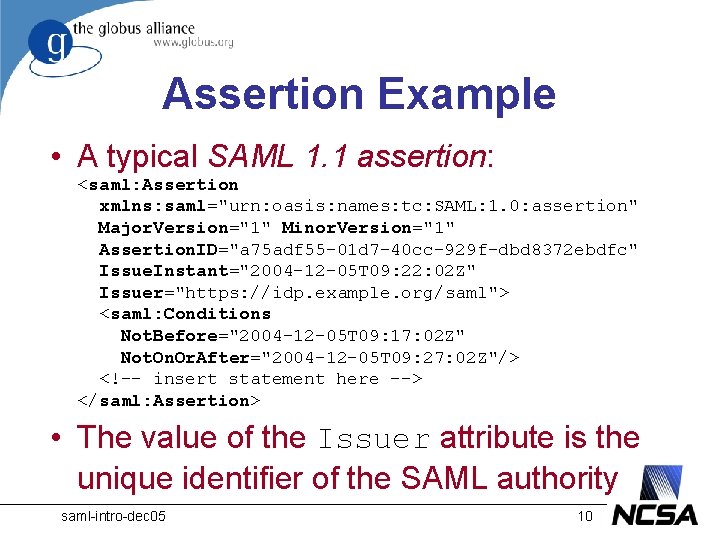
Assertion Example • A typical SAML 1. 1 assertion: <saml: Assertion xmlns: saml="urn: oasis: names: tc: SAML: 1. 0: assertion" Major. Version="1" Minor. Version="1" Assertion. ID="a 75 adf 55 -01 d 7 -40 cc-929 f-dbd 8372 ebdfc" Issue. Instant="2004 -12 -05 T 09: 22: 02 Z" Issuer="https: //idp. example. org/saml"> <saml: Conditions Not. Before="2004 -12 -05 T 09: 17: 02 Z" Not. On. Or. After="2004 -12 -05 T 09: 27: 02 Z"/> <!-- insert statement here --> </saml: Assertion> • The value of the Issuer attribute is the unique identifier of the SAML authority saml-intro-dec 05 10
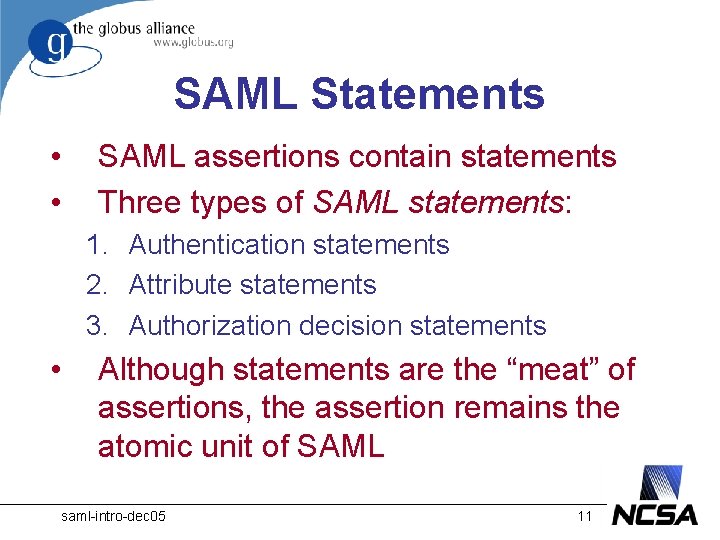
SAML Statements • • SAML assertions contain statements Three types of SAML statements: 1. Authentication statements 2. Attribute statements 3. Authorization decision statements • Although statements are the “meat” of assertions, the assertion remains the atomic unit of SAML saml-intro-dec 05 11
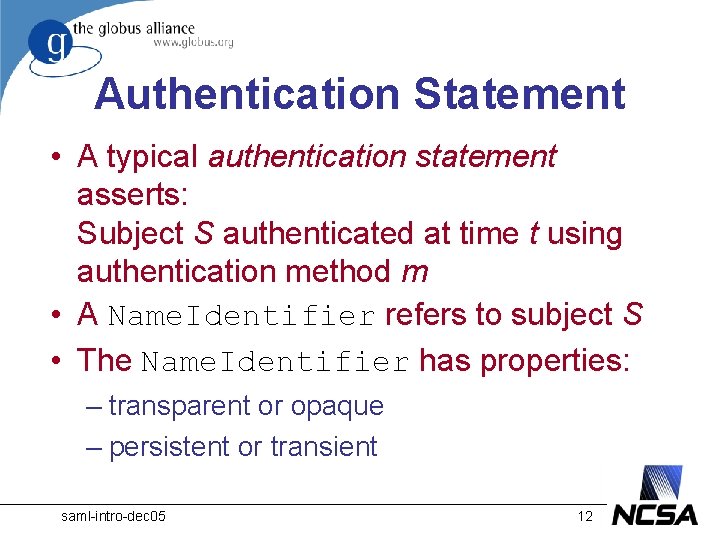
Authentication Statement • A typical authentication statement asserts: Subject S authenticated at time t using authentication method m • A Name. Identifier refers to subject S • The Name. Identifier has properties: – transparent or opaque – persistent or transient saml-intro-dec 05 12
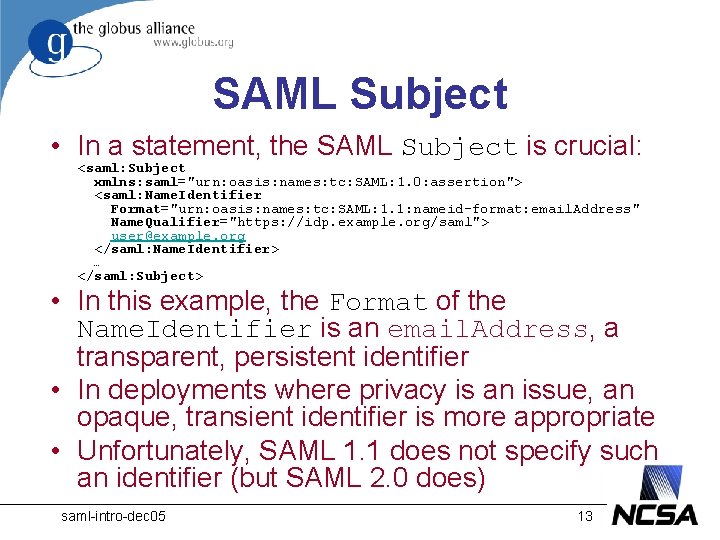
SAML Subject • In a statement, the SAML Subject is crucial: <saml: Subject xmlns: saml="urn: oasis: names: tc: SAML: 1. 0: assertion"> <saml: Name. Identifier Format="urn: oasis: names: tc: SAML: 1. 1: nameid-format: email. Address" Name. Qualifier="https: //idp. example. org/saml"> user@example. org </saml: Name. Identifier> … </saml: Subject> • In this example, the Format of the Name. Identifier is an email. Address, a transparent, persistent identifier • In deployments where privacy is an issue, an opaque, transient identifier is more appropriate • Unfortunately, SAML 1. 1 does not specify such an identifier (but SAML 2. 0 does) saml-intro-dec 05 13
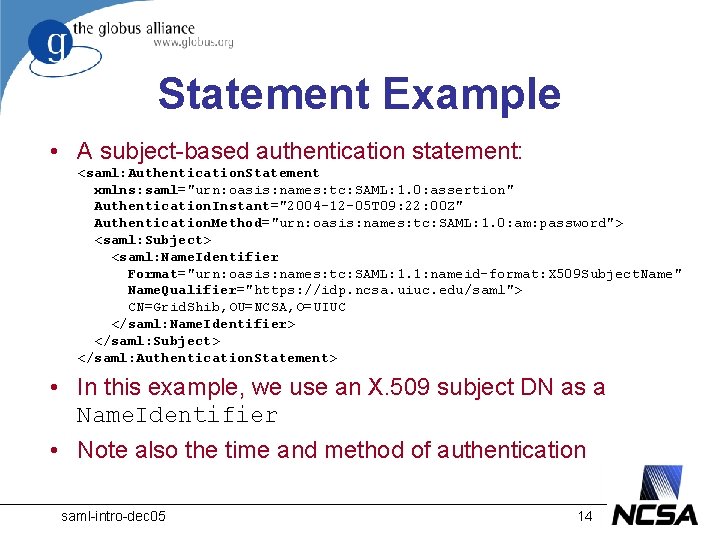
Statement Example • A subject-based authentication statement: <saml: Authentication. Statement xmlns: saml="urn: oasis: names: tc: SAML: 1. 0: assertion" Authentication. Instant="2004 -12 -05 T 09: 22: 00 Z" Authentication. Method="urn: oasis: names: tc: SAML: 1. 0: am: password"> <saml: Subject> <saml: Name. Identifier Format="urn: oasis: names: tc: SAML: 1. 1: nameid-format: X 509 Subject. Name" Name. Qualifier="https: //idp. ncsa. uiuc. edu/saml"> CN=Grid. Shib, OU=NCSA, O=UIUC </saml: Name. Identifier> </saml: Subject> </saml: Authentication. Statement> • In this example, we use an X. 509 subject DN as a Name. Identifier • Note also the time and method of authentication saml-intro-dec 05 14
Attribute Statement • Similarly, an attribute statement asserts: Subject S is associated with attributes A, B, C having values “a”, ”b”, ”c” • Relying parties use attributes to make access control decisions • Standard attribute names with well understood values are of course highly desirable saml-intro-dec 05 15
SAML Protocol • SAML messages are exchanged via a simple request/response protocol • A SAML Request initiates an exchange: <samlp: Request> … </samlp: Request> • A SAML Response often contains one or more assertions saml-intro-dec 05 16
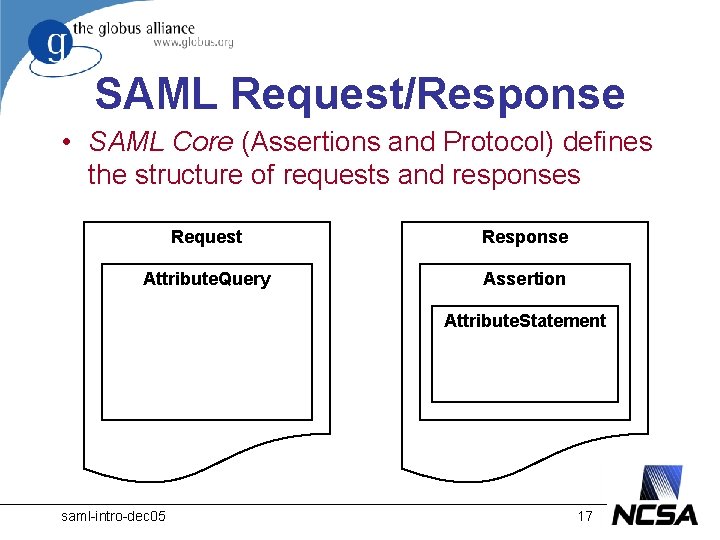
SAML Request/Response • SAML Core (Assertions and Protocol) defines the structure of requests and responses Request Response Attribute. Query Assertion Attribute. Statement saml-intro-dec 05 17
SAML Bindings and Profiles saml-intro-dec 05 18
SAML Bindings • Now we know how to formulate SAML requests and responses, but how do we move them around? • A SAML Binding determines how SAML requests and responses map onto standard messaging or communication protocols • An important (synchronous) binding is SAML over SOAP over HTTP saml-intro-dec 05 19
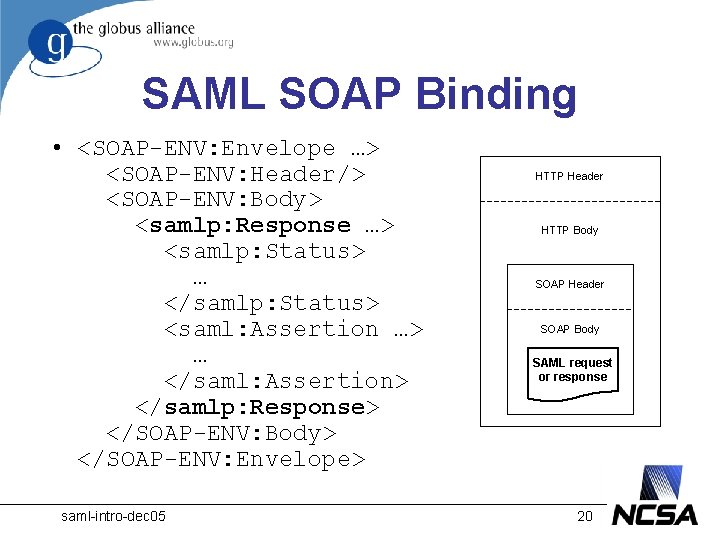
SAML SOAP Binding • <SOAP-ENV: Envelope …> <SOAP-ENV: Header/> <SOAP-ENV: Body> <samlp: Response …> <samlp: Status> … </samlp: Status> <saml: Assertion …> … </saml: Assertion> </samlp: Response> </SOAP-ENV: Body> </SOAP-ENV: Envelope> saml-intro-dec 05 HTTP Header HTTP Body SOAP Header SOAP Body SAML request or response 20
Other SAML Bindings • SAML 1. 1 message bindings: – HTTP POST (special case) – HTTP Artifact (special case) – SOAP • SAML 2. 0 message bindings: – – – HTTP Redirect HTTP POST HTTP Artifact SOAP etc. saml-intro-dec 05 21
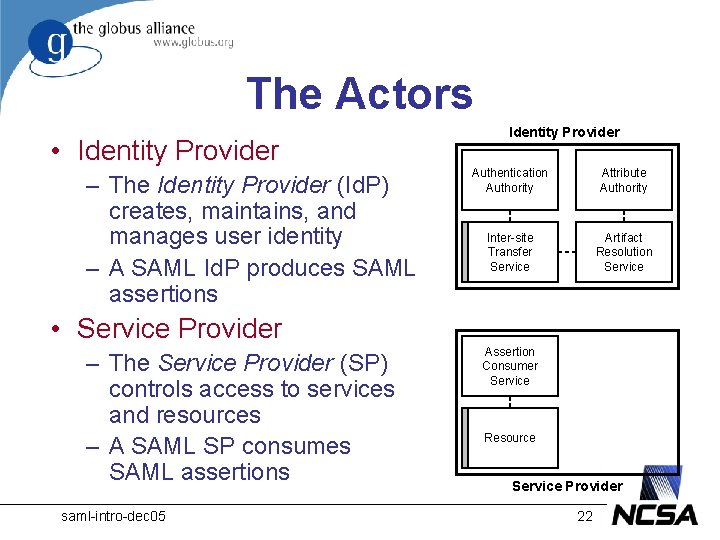
The Actors • Identity Provider – The Identity Provider (Id. P) creates, maintains, and manages user identity – A SAML Id. P produces SAML assertions Identity Provider Authentication Authority Attribute Authority Inter-site Transfer Service Artifact Resolution Service • Service Provider – The Service Provider (SP) controls access to services and resources – A SAML SP consumes SAML assertions saml-intro-dec 05 Assertion Consumer Service Resource Service Provider 22
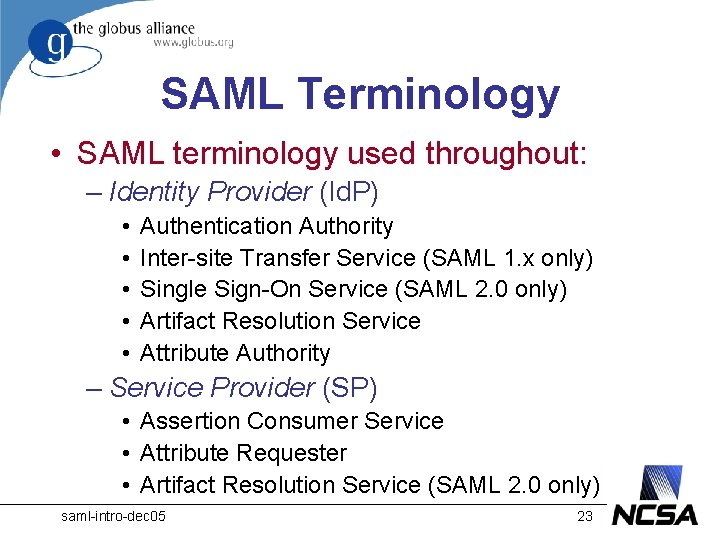
SAML Terminology • SAML terminology used throughout: – Identity Provider (Id. P) • • • Authentication Authority Inter-site Transfer Service (SAML 1. x only) Single Sign-On Service (SAML 2. 0 only) Artifact Resolution Service Attribute Authority – Service Provider (SP) • Assertion Consumer Service • Attribute Requester • Artifact Resolution Service (SAML 2. 0 only) saml-intro-dec 05 23
SAML Use Cases • The most important problem that SAML is trying to solve is the web single signon (SSO) problem • In SAML 1. x, a browser user is requesting the Inter-site Transfer Service via a portal interface at the Id. P • In SAML 2. 0, a browser user is requesting protected resources directly from SPs saml-intro-dec 05 24
Id. P-first or SP-first? • The SAML 1. x browser profiles are Id. Pfirst insofar as they begin with a request to the Id. P • SAML 2. 0 introduces SP-first profiles, which are more complex • In particular, SP-first flows give rise to the Id. P Discovery problem saml-intro-dec 05 25
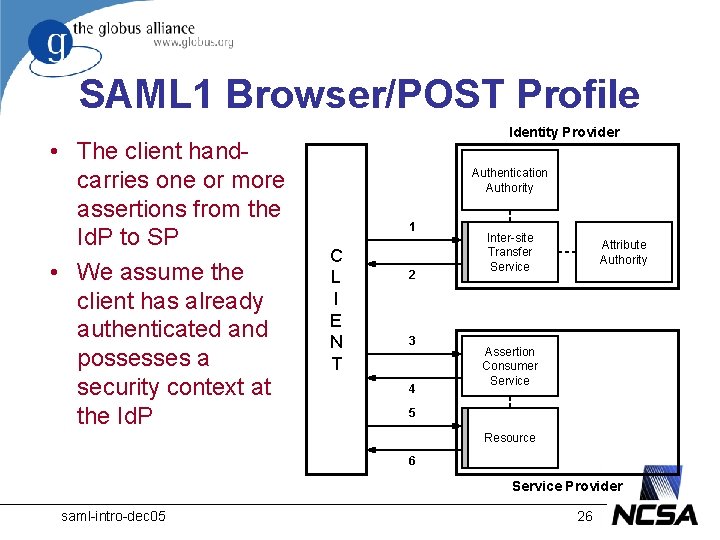
SAML 1 Browser/POST Profile • The client handcarries one or more assertions from the Id. P to SP • We assume the client has already authenticated and possesses a security context at the Id. P Identity Provider Authentication Authority 1 C L I E N T 2 3 4 Inter-site Transfer Service Attribute Authority Assertion Consumer Service 5 Resource 6 Service Provider saml-intro-dec 05 26
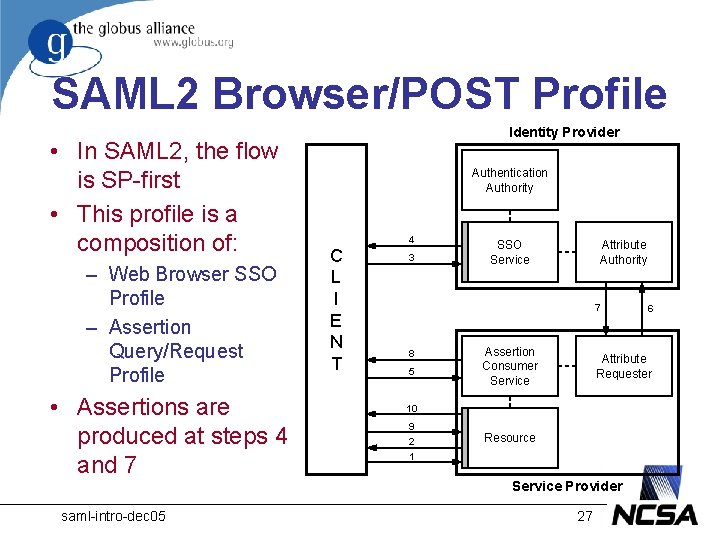
SAML 2 Browser/POST Profile • In SAML 2, the flow is SP-first • This profile is a composition of: – Web Browser SSO Profile – Assertion Query/Request Profile • Assertions are produced at steps 4 and 7 Identity Provider Authentication Authority 4 C L I E N T 3 SSO Service Attribute Authority 7 8 5 Assertion Consumer Service Attribute Requester 10 9 2 1 Resource Service Provider saml-intro-dec 05 6 27
Other SAML Profiles • In SAML 1. x, the browser SSO profiles are the only profiles • In SAML 2. 0, the browser SSO profiles are extended and generalized • SAML 2. 0 introduces many other profiles: – Single Logout Profile – Assertion Query/Request Profile – SAML Attribute Profiles (LDAP, XACML, …) – etc. saml-intro-dec 05 28
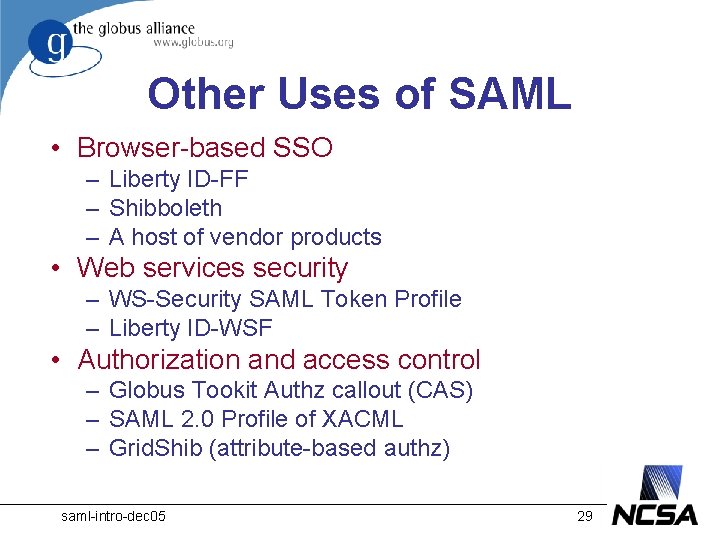
Other Uses of SAML • Browser-based SSO – Liberty ID-FF – Shibboleth – A host of vendor products • Web services security – WS-Security SAML Token Profile – Liberty ID-WSF • Authorization and access control – Globus Tookit Authz callout (CAS) – SAML 2. 0 Profile of XACML – Grid. Shib (attribute-based authz) saml-intro-dec 05 29
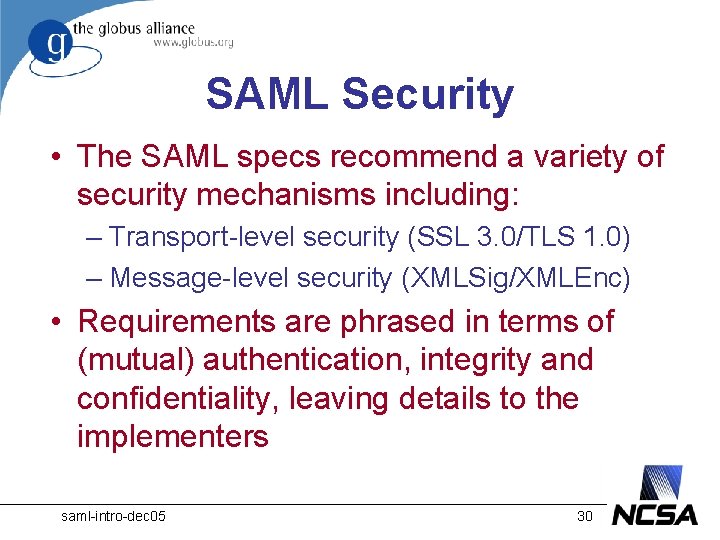
SAML Security • The SAML specs recommend a variety of security mechanisms including: – Transport-level security (SSL 3. 0/TLS 1. 0) – Message-level security (XMLSig/XMLEnc) • Requirements are phrased in terms of (mutual) authentication, integrity and confidentiality, leaving details to the implementers saml-intro-dec 05 30
SAML Miscellania saml-intro-dec 05 31
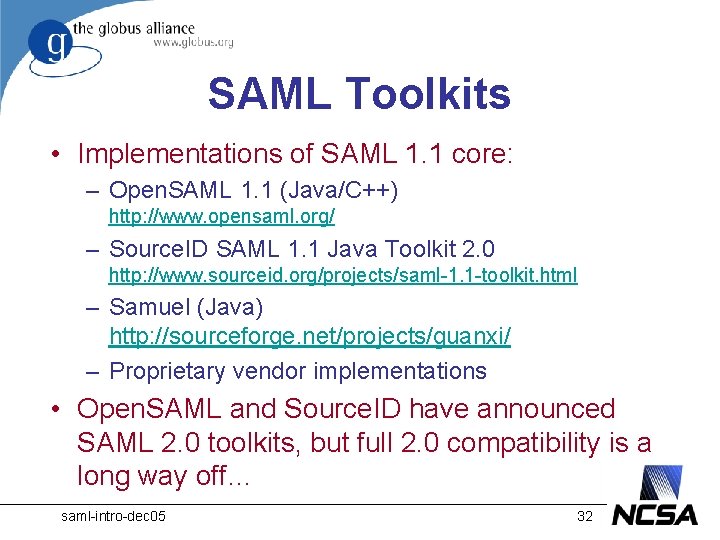
SAML Toolkits • Implementations of SAML 1. 1 core: – Open. SAML 1. 1 (Java/C++) http: //www. opensaml. org/ – Source. ID SAML 1. 1 Java Toolkit 2. 0 http: //www. sourceid. org/projects/saml-1. 1 -toolkit. html – Samuel (Java) http: //sourceforge. net/projects/guanxi/ – Proprietary vendor implementations • Open. SAML and Source. ID have announced SAML 2. 0 toolkits, but full 2. 0 compatibility is a long way off… saml-intro-dec 05 32
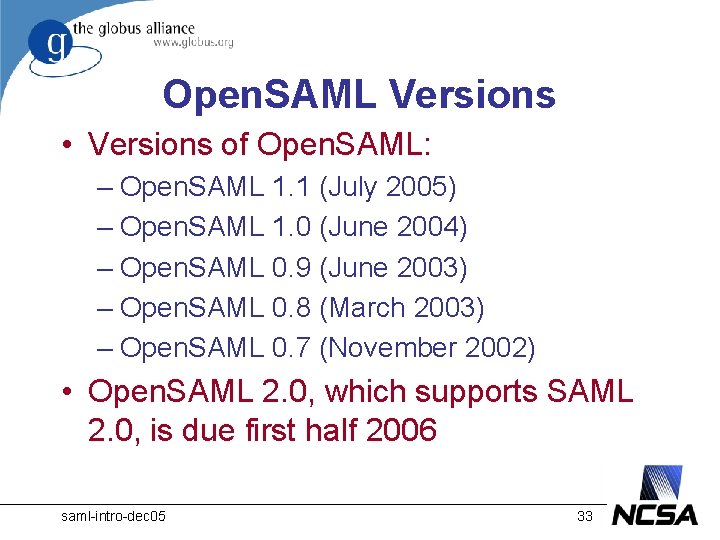
Open. SAML Versions • Versions of Open. SAML: – Open. SAML 1. 1 (July 2005) – Open. SAML 1. 0 (June 2004) – Open. SAML 0. 9 (June 2003) – Open. SAML 0. 8 (March 2003) – Open. SAML 0. 7 (November 2002) • Open. SAML 2. 0, which supports SAML 2. 0, is due first half 2006 saml-intro-dec 05 33
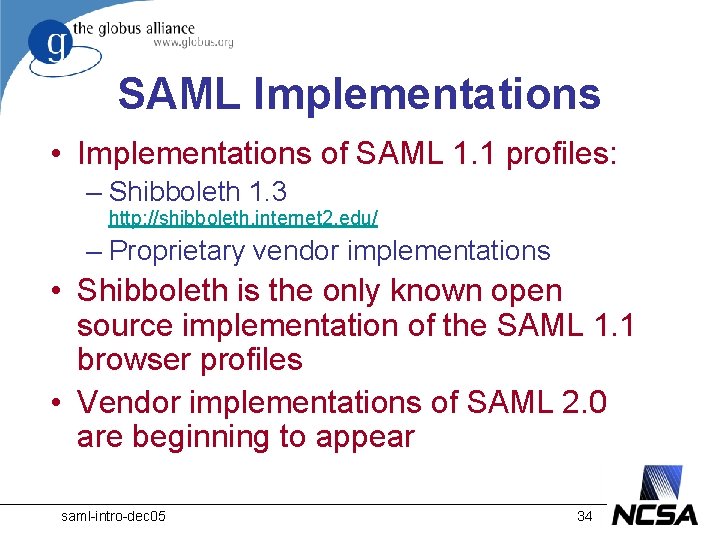
SAML Implementations • Implementations of SAML 1. 1 profiles: – Shibboleth 1. 3 http: //shibboleth. internet 2. edu/ – Proprietary vendor implementations • Shibboleth is the only known open source implementation of the SAML 1. 1 browser profiles • Vendor implementations of SAML 2. 0 are beginning to appear saml-intro-dec 05 34
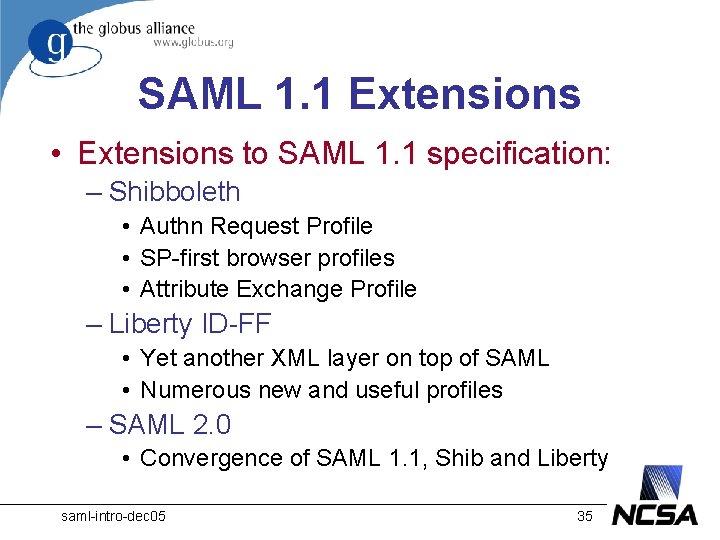
SAML 1. 1 Extensions • Extensions to SAML 1. 1 specification: – Shibboleth • Authn Request Profile • SP-first browser profiles • Attribute Exchange Profile – Liberty ID-FF • Yet another XML layer on top of SAML • Numerous new and useful profiles – SAML 2. 0 • Convergence of SAML 1. 1, Shib and Liberty saml-intro-dec 05 35
SAML Resources • SAML V 1. 1 Technical Overview http: //www. oasisopen. org/committees/download. php/6837/sstc-samltech-overview-1. 1 -cd. pdf • SAML V 2. 0 Technical Overview http: //www. oasisopen. org/committees/download. php/13786/ss tc-saml-tech-overview-2. 0 -draft-07 -diff. pdf • Wikipedia http: //en. wikipedia. org/wiki/SAML saml-intro-dec 05 36
- Slides: 36